CYBER SECURITY CHALLENGES Dr Iftikhar Ahmad Department of
CYBER SECURITY CHALLENGES Dr. Iftikhar Ahmad Department of Information Technology Faculty of Computing and Information Technology, King Abdulaziz University, Saudi Arabia. 1
OUTLINE • • CYBER as a new domain What is cyber security? Cyber security in News Why cyber security is important? Cyber threats evolution Types of cyber threats Cyber security challenges
CYBER: A NEW DOMAIN OF WARFARE
WHAT IS CYBERSECURITY ? Cybersecurity is the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance and technologies that can be used to protect the cyber environment, organization and user’s assets. (International Telecommunication Unit–T X. 1205) The general security objectives comprise the following: • Confidentiality: ensures that the information will be accessed by authorized persons • Reliability: ü Integrity: No any unauthorized person can modify the information ü Authentication: Information belongs to the correct person • Availability: The information will be accessed by authorized users when they need without any interferences

CYBER SECURITY IN NEWS
CYBER ATTACK ON LOCKHEED MARTIN

CYBER ATTACK ON USAF DRONE

CYBER ATTACK ON SAUDI ARAMCO

CYBER ATTACK SHAMOON • Shamoon-1 (Aug 2012) • Saudi Aramco • Ras. GAS • Wiped data from 35000 computers

CYBER ATTACK SHAMOON • Shamoon-2 (Nov 2016) • GACA • Transport Ministry • Saudi Arabian Monetary Authority

CYBER ATTACK SHAMOON • Shamoon-2 (Jan 2017) • Government and private sectors
WHY CYBER SECURITY IS IMPORTANT? • A big challenge is heavy dependency on technology • Think about what happen when you are on the road your smartphone runs out of battery! • If technology fails than this dependency becomes vulnerable. • Some experts predict that by 2020 there will be 200 billion connected things. Cars, planes, homes, cities, and even animals are being connected. • It is very necessary at personal, organizational and national level to protect their private and sensitive assets from cyber attacks. • In today's world, it’s important that technology is available, protected and secure. If not, we will suffer consequences in our daily lives.
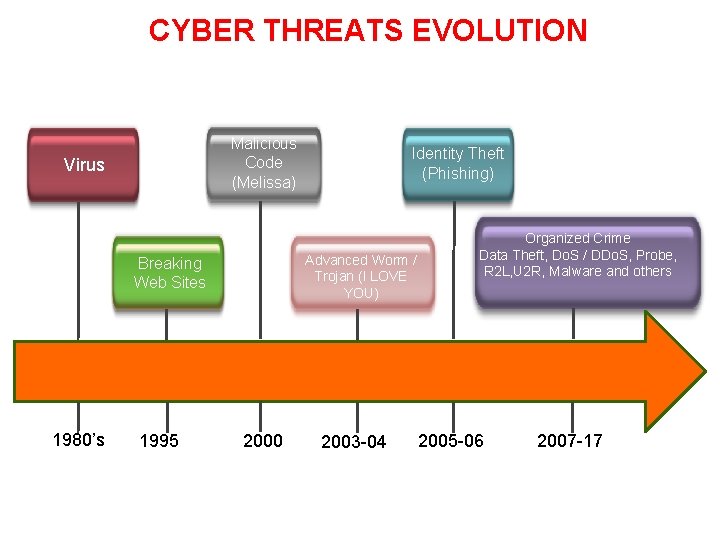
CYBER THREATS EVOLUTION Malicious Code (Melissa) Virus Advanced Worm / Trojan (I LOVE YOU) Breaking Web Sites 1980’s 1995 Identity Theft (Phishing) 2000 2003 -04 Organized Crime Data Theft, Do. S / DDo. S, Probe, R 2 L, U 2 R, Malware and others 2005 -06 2007 -17
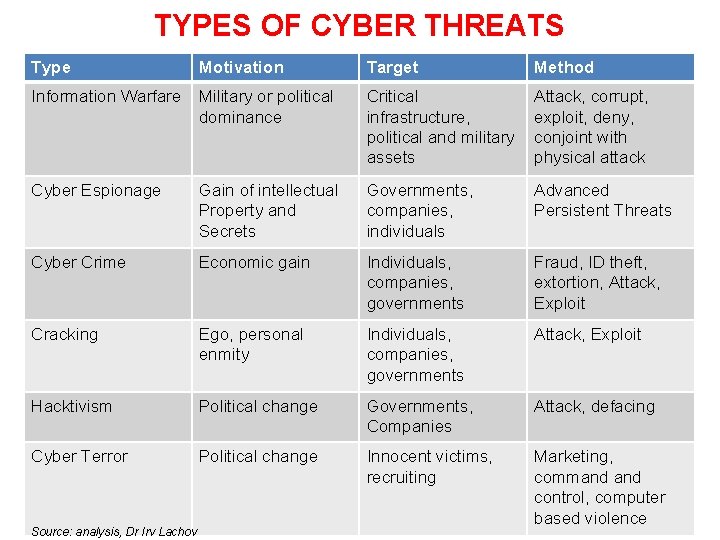
TYPES OF CYBER THREATS Type Motivation Target Method Information Warfare Military or political dominance Critical infrastructure, political and military assets Attack, corrupt, exploit, deny, conjoint with physical attack Cyber Espionage Gain of intellectual Property and Secrets Governments, companies, individuals Advanced Persistent Threats Cyber Crime Economic gain Individuals, companies, governments Fraud, ID theft, extortion, Attack, Exploit Cracking Ego, personal enmity Individuals, companies, governments Attack, Exploit Hacktivism Political change Governments, Companies Attack, defacing Cyber Terror Political change Innocent victims, recruiting Marketing, command control, computer based violence Source: analysis, Dr Irv Lachov

http: //camthao. us/News/332/what-will-the-warrior-guardian-of-the-future-look-like
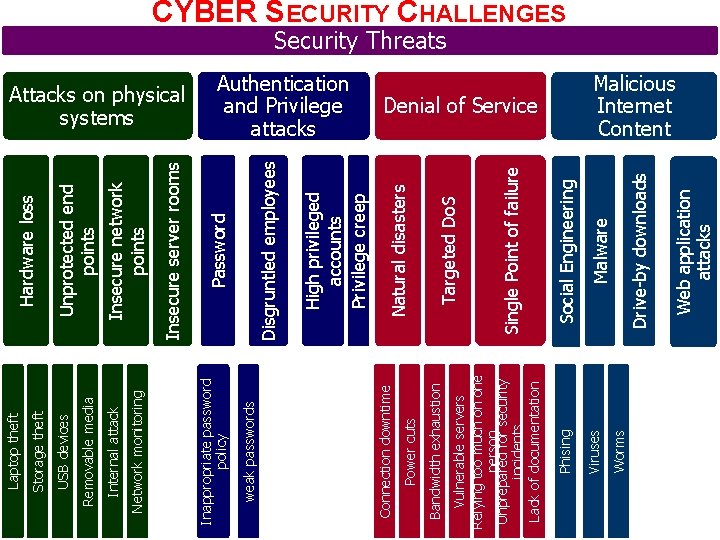
Worms Web application attacks Drive-by downloads Malware Social Engineering Single Point of failure Targeted Do. S Natural disasters Denial of Service Viruses Phising Vulnerable servers Relying too much on one person Unprepared for security incidents Lack of documentation Bandwidth exhaustion Power cuts High privileged accounts Privilege creep Disgruntled employees Authentication and Privilege attacks Connection downtime weak passwords Password Insecure server rooms Insecure network points Unprotected end points Hardware loss Attacks on physical systems Inappropriate password policy Network monitoring Internal attack Removable media USB devices Storage theft Laptop theft CYBER SECURITY CHALLENGES Security Threats Malicious Internet Content
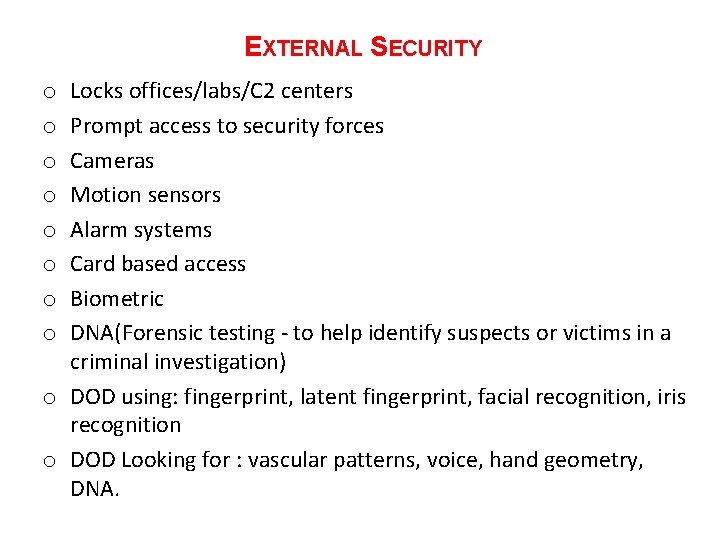
EXTERNAL SECURITY Locks offices/labs/C 2 centers Prompt access to security forces Cameras Motion sensors Alarm systems Card based access Biometric DNA(Forensic testing - to help identify suspects or victims in a criminal investigation) o DOD using: fingerprint, latent fingerprint, facial recognition, iris recognition o DOD Looking for : vascular patterns, voice, hand geometry, DNA. o o o o
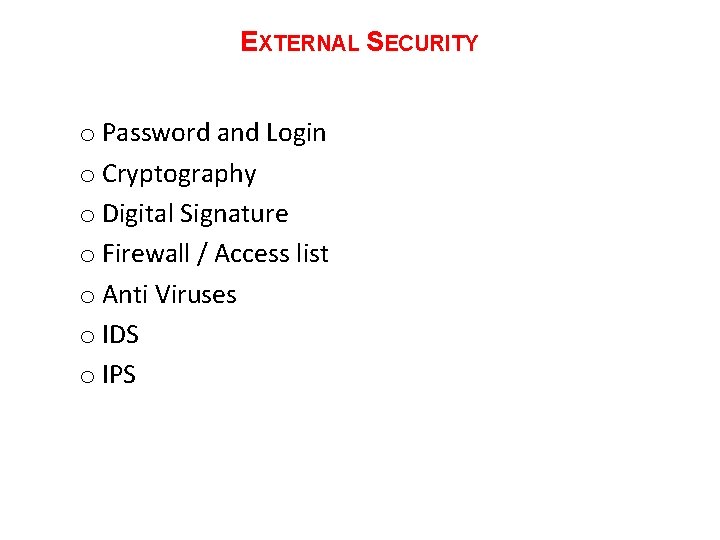
EXTERNAL SECURITY o Password and Login o Cryptography o Digital Signature o Firewall / Access list o Anti Viruses o IDS o IPS
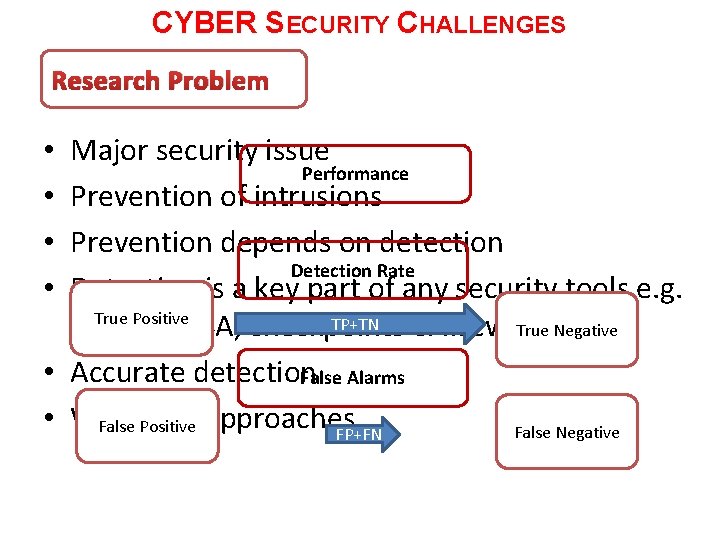
CYBER SECURITY CHALLENGES Research Problem Major security issue Performance Prevention of intrusions Prevention depends on detection Detection Rate Detection is a key part of any security tools e. g. True Positive TP+TN True Negative IDS, IPS, ASA, checkpoints & firewalls. • Accurate detection False Alarms • Variety of approaches False Positive False Negative FP+FN • •
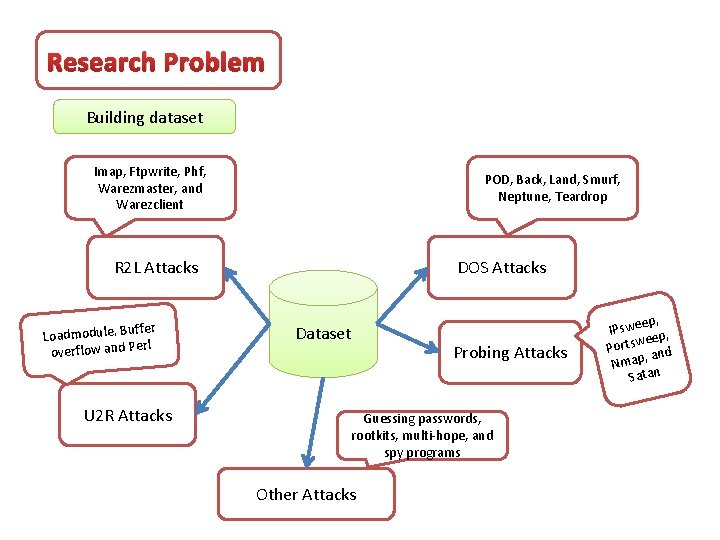
Research Problem Building dataset Imap, Ftpwrite, Phf, Warezmaster, and Warezclient POD, Back, Land, Smurf, Neptune, Teardrop R 2 L Attacks ffer Loadmodule, Bu rl overflow and Pe U 2 R Attacks DOS Attacks Dataset Probing Attacks Guessing passwords, rootkits, multi-hope, and spy programs Other Attacks ep, IPswe p, ee Portsw and , Nmap Satan
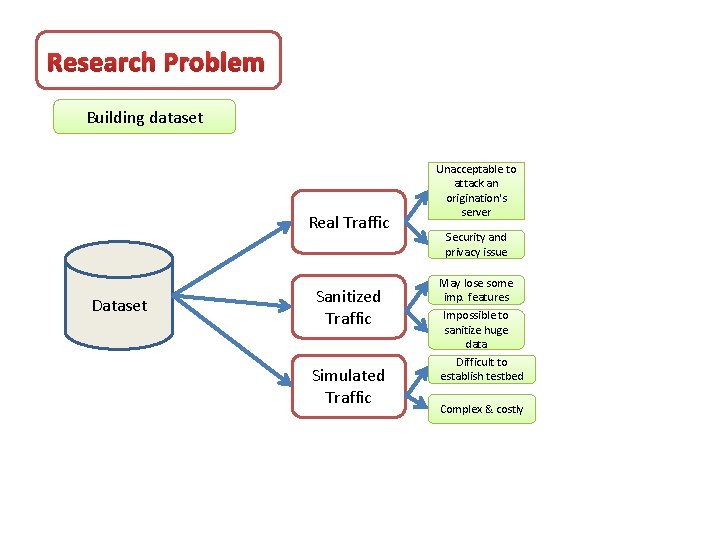
Research Problem Building dataset Real Traffic Dataset Sanitized Traffic Simulated Traffic Unacceptable to attack an origination's server Security and privacy issue May lose some imp. features Impossible to sanitize huge data Difficult to establish testbed Complex & costly
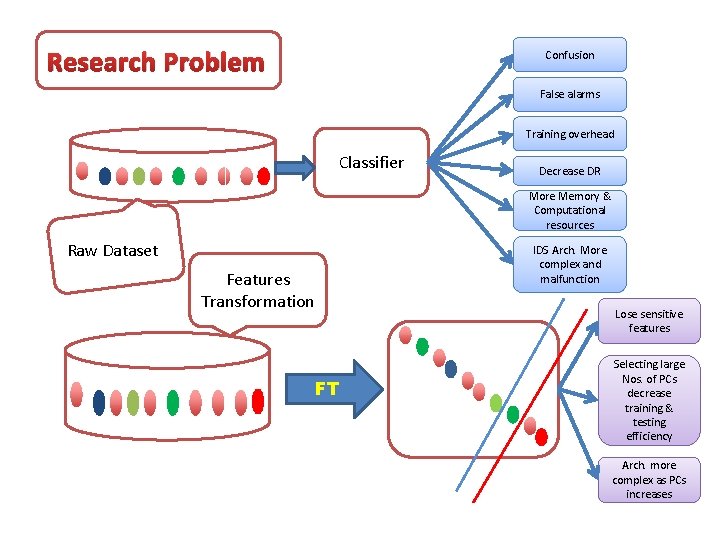
Research Problem Confusion False alarms Training overhead Classifier Decrease DR More Memory & Computational resources Raw Dataset IDS Arch. More complex and malfunction Features Transformation Lose sensitive features FT Selecting large Nos. of PCs decrease training & testing efficiency Arch. more complex as PCs increases
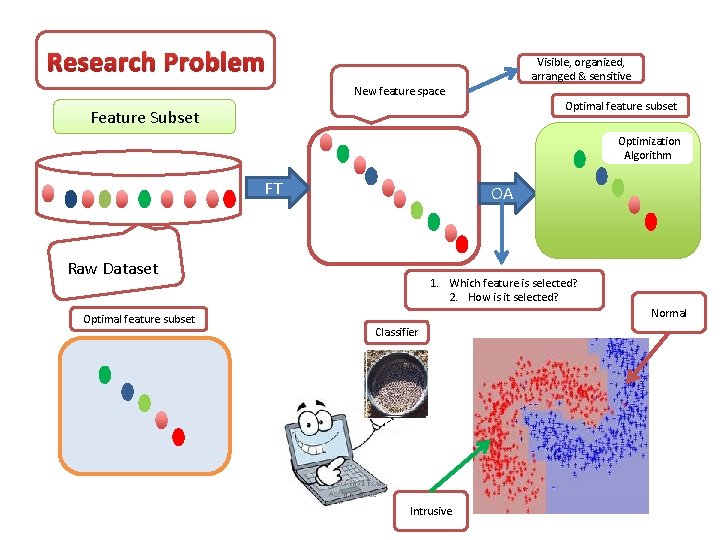
Research Problem Visible, organized, arranged & sensitive New feature space Optimal feature subset Feature Subset Optimization Algorithm FT OA Raw Dataset Optimal feature subset 1. Which feature is selected? 2. How is it selected? Normal Classifier Intrusive
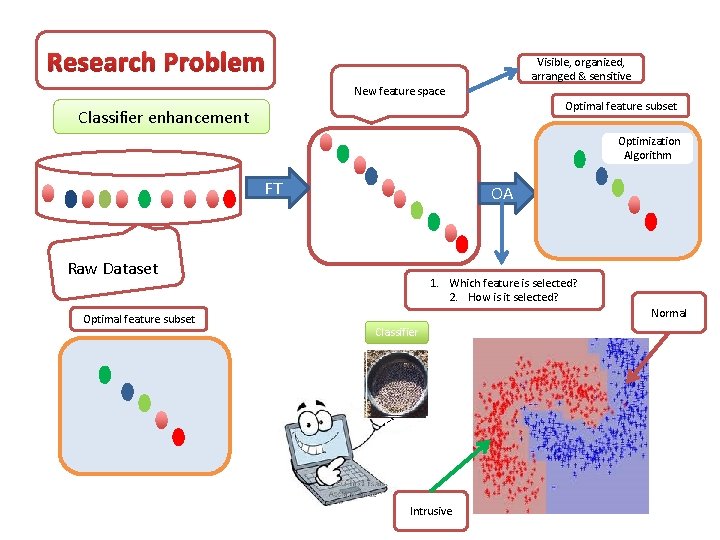
Research Problem Visible, organized, arranged & sensitive New feature space Optimal feature subset Classifier enhancement Optimization Algorithm FT OA Raw Dataset Optimal feature subset 1. Which feature is selected? 2. How is it selected? Normal Classifier Intrusive
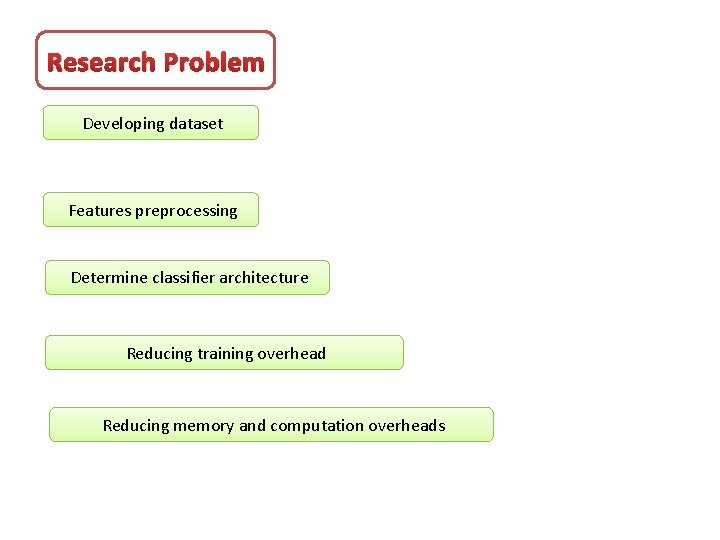
Research Problem Developing dataset Features preprocessing Determine classifier architecture Reducing training overhead Reducing memory and computation overheads

- Slides: 27