Cyber Security Awareness Halloween Horror Film Matinee Presented
Cyber Security Awareness Halloween Horror Film Matinee Presented by Mc. Gill IT Services

Cyber Security Awareness Halloween Horror Film Matinee 30 October 2017
today’s terrifying Program Passwords Featuring Spaceballs! Phishing Featuring Night of the Living Dead! Social Media & Privacy Featuring Scream!

Passwords

Spaceballs (1987)
The good ol’ days Face to face tr ansactions ty i t n e d i l Physica ts n e m u c do
The good ol’ days Crooks h ad to do it in perso n
The good ol’ days Criminals actually looked like bankers

Today’s world
Today’s world Do you know how many passwords you have?

What are the dangers? Identity theft Financial fraud Extortion Revenge

What are the dangers? Ransomware Data theft Industrial espionage Financial losses

Know your enemy Dictionary Brute-force Social engineering phishing
Dictionary Attack Tries all possibilities from a list Tries most likely possibilities first List can come from dictionaries or other sources (like leaked passwords)
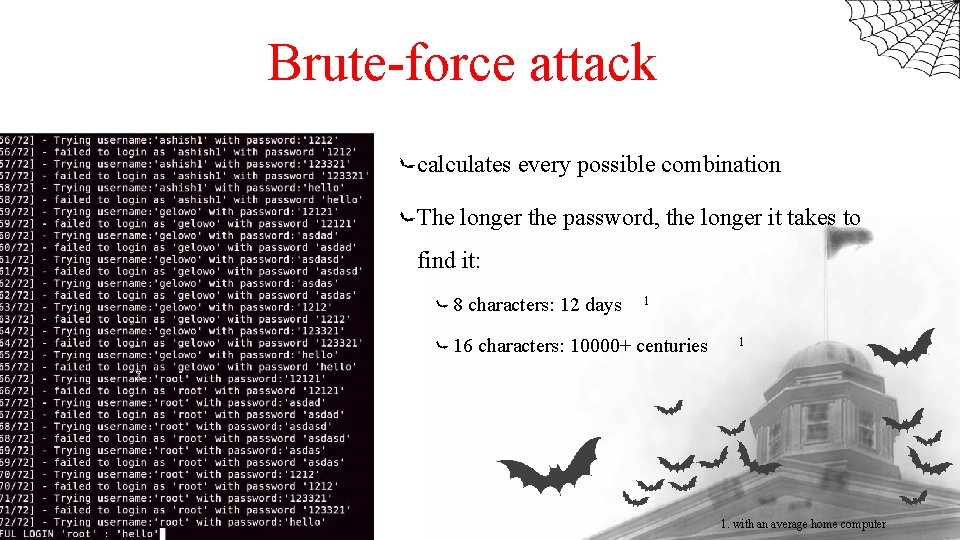
Brute-force attack calculates every possible combination The longer the password, the longer it takes to find it: 8 characters: 12 days 1 16 characters: 10000+ centuries 1 1. with an average home computer
Social Engineering Psychological manipulation defraud a person after gaining their confidence Used to gather information Example: “Nigerian Prince” Shoulder surfing
Phishing Induces individuals to reveal personal information disguises as a trustworthy entity in an electronic communication More on this later…

Common mistakes Too short Too common Too old Easy to guess Default

Common mistakes Reused Poorly stored Unsecured Device shared
How you can protect yourself Toothbrush test: Choose a good one Don’t share it Replace it often Don’t recycle an old one
How you can protect yourself Use a long password: 12 characters or more Use a combination of: Lowercase letters Uppercase letters Numbers Symbols don’t use a common password: Remember Spaceballs?
How you can protect yourself don’t base it on personal information: Social security number Name of a relative/pet Favorite things (book, team, etc. ) Change the Default
How you can protect yourself Never reuse a password Store it securely: Don’t write it down Secure your Device Never share a password
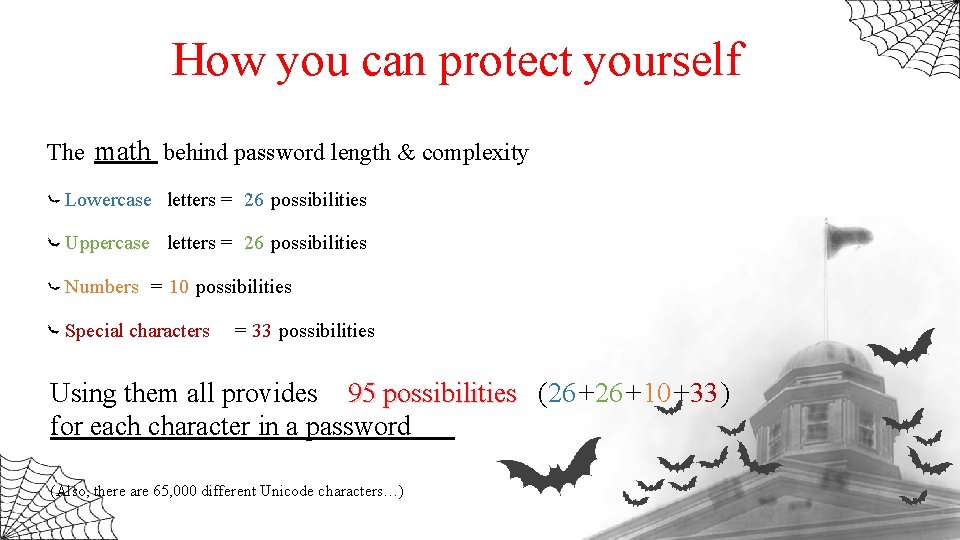
How you can protect yourself The math behind password length & complexity Lowercase letters = 26 possibilities Uppercase letters = 26 possibilities Numbers = 10 possibilities Special characters = 33 possibilities Using them all provides 95 possibilities (26 +10 +33 ) for each character in a password (Also, there are 65, 000 different Unicode characters…)
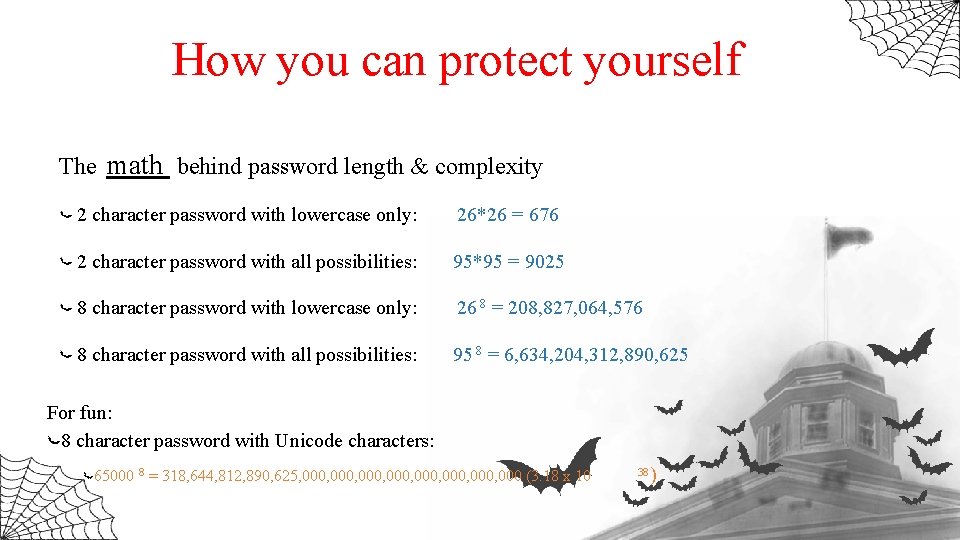
How you can protect yourself The math behind password length & complexity 2 character password with lowercase only: 26*26 = 676 2 character password with all possibilities: 95*95 = 9025 8 character password with lowercase only: 26 8 = 208, 827, 064, 576 8 character password with all possibilities: 95 8 = 6, 634, 204, 312, 890, 625 For fun: 8 character password with Unicode characters: 65000 8 = 318, 644, 812, 890, 625, 000, 000, 000 (3. 18 x 10 38 )
How you can protect yourself Test your password https: //password. kaspersky. com http : //www. passwordmeter. com / / https: // www. grc. com/haystack. htm …OR just Google “password tester”

How you can protect yourself Use a password manager Helps generating secure passwords No need to remember them all Work across platforms Cloud based or desktop Many are free
Phishing
Phishing Return of the Living Dead – Paramedics scene https: //www. youtube. com/watch? v=l. Rcle-Jgn. FA
PHISHING Cyber criminals are lurking everywhere, hoping you’ll take their bait and give up your personal information.
What is phishing? Attempt to obtain sensitive information (username, password, credit card – ultimately $$) Criminal Masquerades as a trustworthy entity (University, Bank, Canadian Government) Via email, instant message, other electronic comm. (via email, instant message, other electronic communication)
How does it Work? Email/text looks legitimate (contains valid-looking signature, may include graphics) Asks you to click on a link (e. g. , verify account, or take some action) Link goes to fake website You enter your credentials (and other info) Attachments Can install malware, such as key logger or virus IM from mobile device Your mobile contains information about where you are…
Watch out for. . . • Fake URLs – Links that look close to legit sites, e. g. "payapl. com" • Urgent / immediate action required – Your account will expire, etc. • Official sounding Name/Signature e. g. "Mc. Gill University Admin" • Logo – Easy to copy from real corporate/institutional websites • Prize / recognition e. g. you have been selected for … • Content sharing apps e. g. , One. Drive, Google Drive
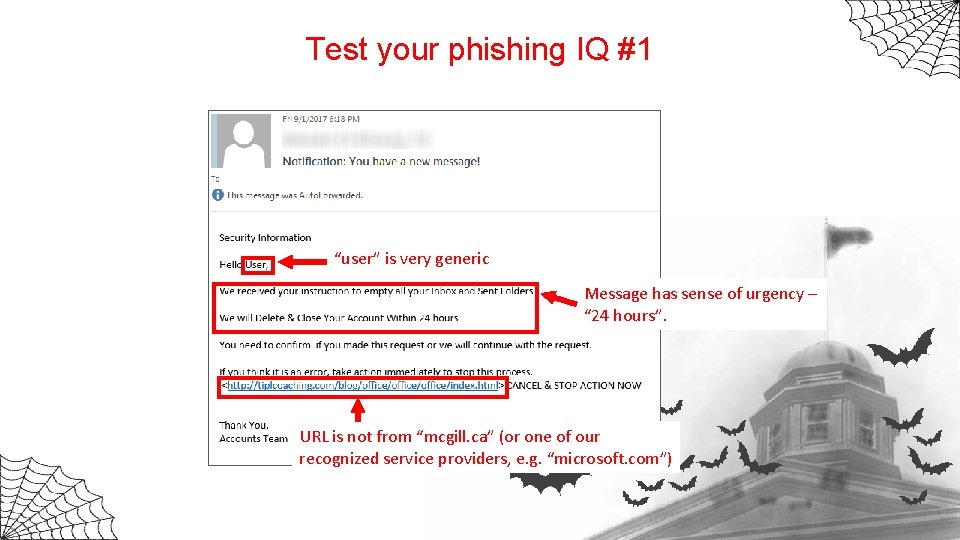
Test your phishing IQ #1 “user” is very generic Message has sense of urgency – “ 24 hours”. URL is not from “mcgill. ca” (or one of our recognized service providers, e. g. “microsoft. com”)
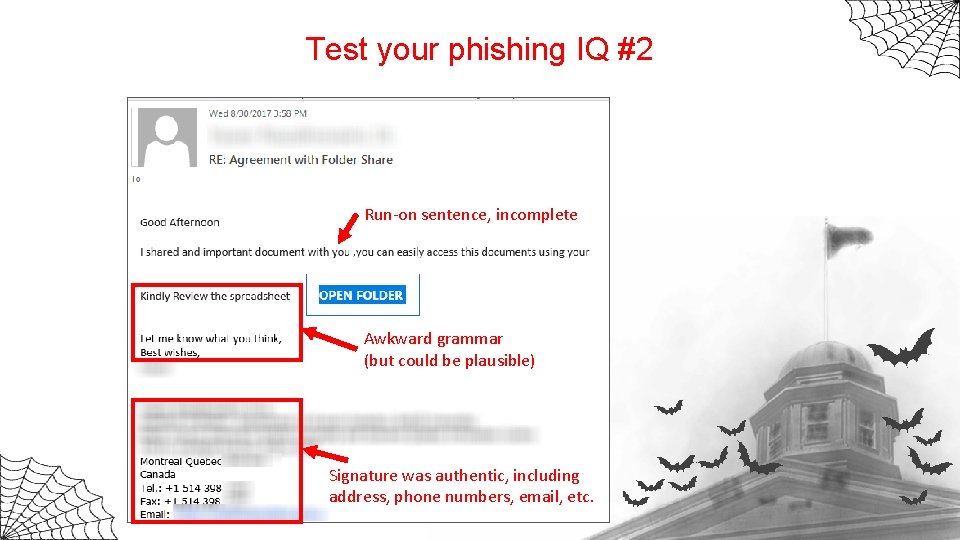
Test your phishing IQ #2 Run-on sentence, incomplete Awkward grammar (but could be plausible) Signature was authentic, including address, phone numbers, email, etc.
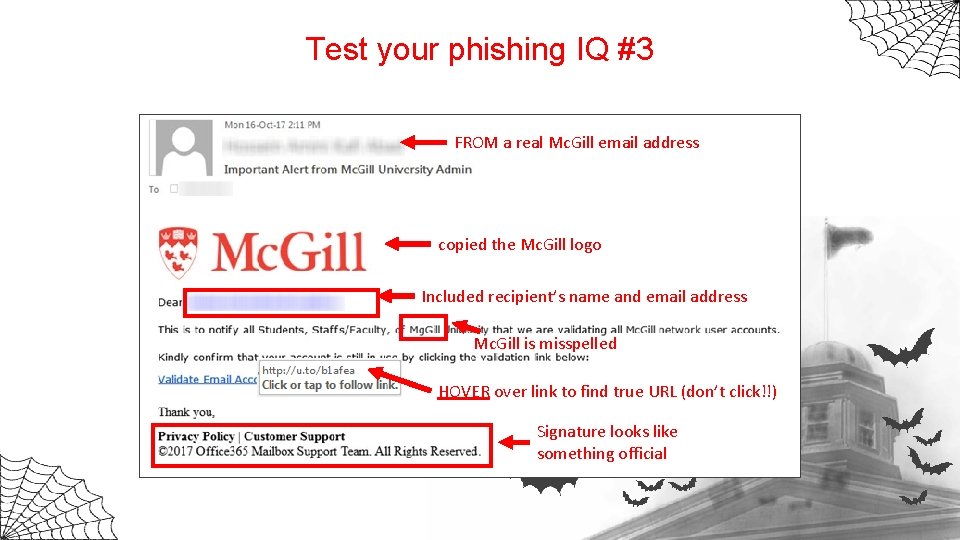
Test your phishing IQ #3 FROM a real Mc. Gill email address copied the Mc. Gill logo Included recipient’s name and email address Mc. Gill is misspelled HOVER over link to find true URL (don’t click!!) Signature looks like something official
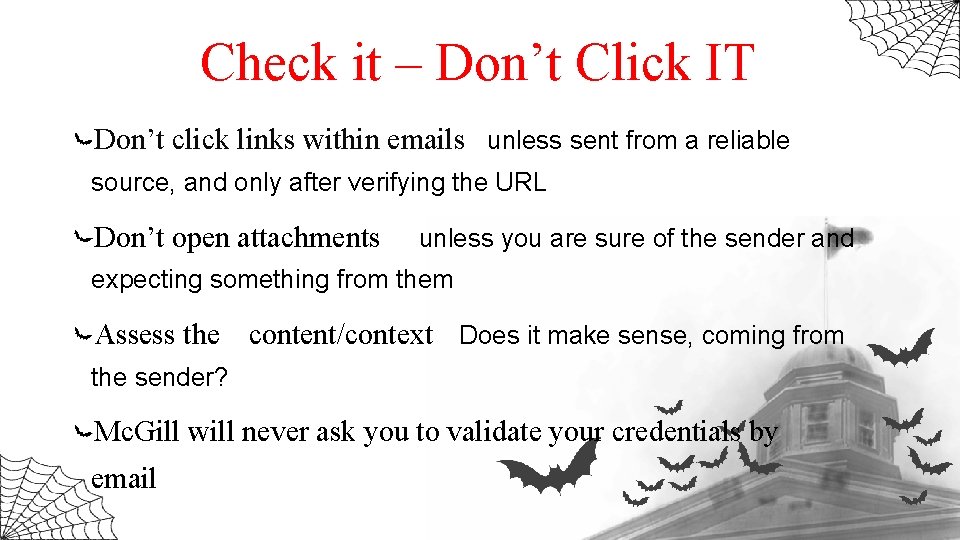
Check it – Don’t Click IT Don’t click links within emails unless sent from a reliable source, and only after verifying the URL Don’t open attachments unless you are sure of the sender and expecting something from them Assess the content/context Does it make sense, coming from the sender? Mc. Gill will never ask you to validate your credentials by email
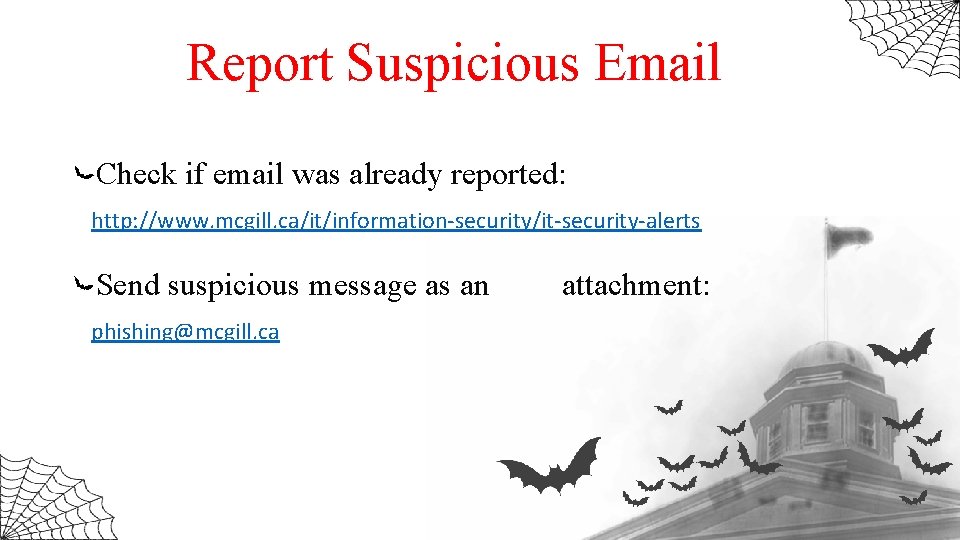
Report Suspicious Email Check if email was already reported: http: //www. mcgill. ca/it/information-security/it-security-alerts Send suspicious message as an phishing@mcgill. ca attachment:

Privacy & Social Media
Scream (1996) https: //youtu. be/LWx. SBb. BX 4 fs? t=1 s

Today The good ol’ days Vs
What are the dangers? Identity theft Location tracking & sharing apps Social Engineering Phishing
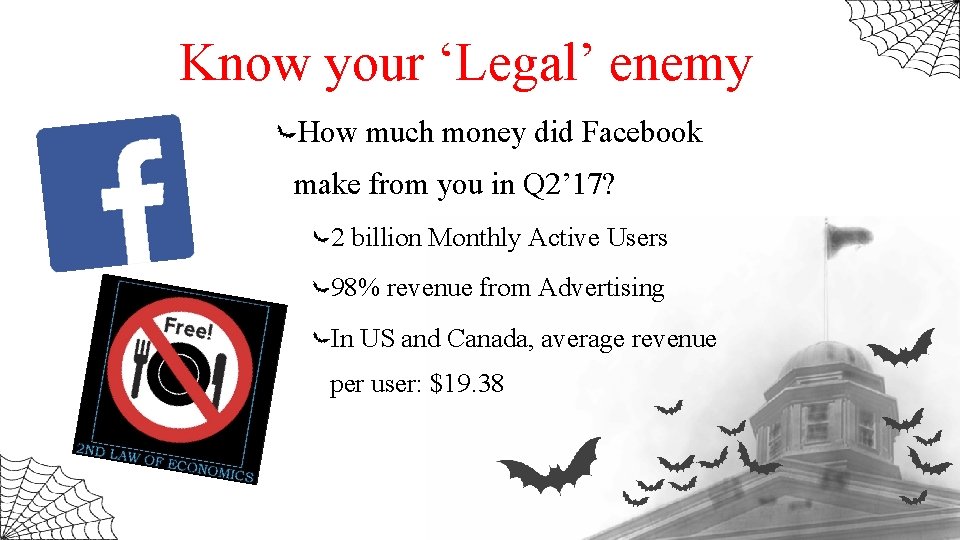
Know your ‘Legal’ enemy How much money did Facebook make from you in Q 2’ 17? 2 billion Monthly Active Users 98% revenue from Advertising In US and Canada, average revenue per user: $19. 38
Common mistakes Provide your personal info Post when you aren’t home Ignore privacy settings Use easy-to-guess password

Common mistakes Answering ‘ Who’s this’?
How you can protect yourself You Be mindful about what you share Think twice before clicking links & installing apps Don’t accept unknown connection / friend requests
How you can protect yourself Your account(s) Check your privacy settings Practice password hygiene Secure with two-Factor Authentication https : //twofactorauth. org/
How you can protect yourself Your device(s) Lock it Keep OS, browser & software updated Antivirus
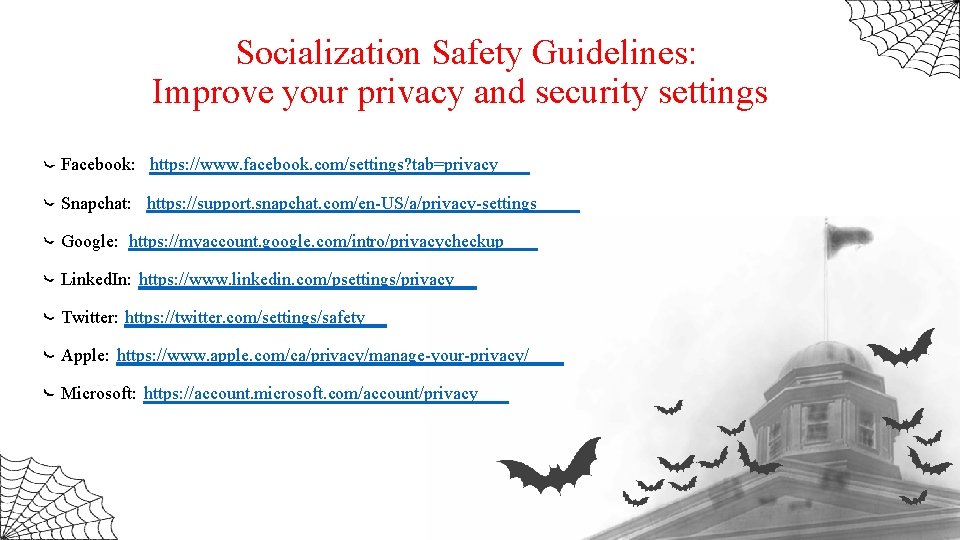
Socialization Safety Guidelines: Improve your privacy and security settings Facebook: https: //www. facebook. com/settings? tab=privacy Snapchat: https: //support. snapchat. com/en-US/a/privacy-settings Google: https: //myaccount. google. com/intro/privacycheckup Linked. In: https: //www. linkedin. com/psettings/privacy Twitter: https: //twitter. com/settings/safety Apple: https: //www. apple. com/ca/privacy/manage-your-privacy/ Microsoft: https: //account. microsoft. com/account/privacy

Thank you
- Slides: 50