Cyber Security Assessment and Management CSAM IT Security
Cyber Security Assessment and Management (CSAM) IT Security Program Purpose: Support Department of Justice Strategic Goals by ensuring Integrity, Confidentiality, and Availability of information and information systems. • Introduction and Overview • • • Highlights and Capabilities Business Readiness Pricing Model Conclusion Q and A’s Comprehensive FISMA Compliance Technology and Support Services Customer Information Day Information System Security Line of Business March 13, 2007 Dennis Heretick Deputy CIO, IT Security Department of Justice Dennis. heretick@usdoj. gov
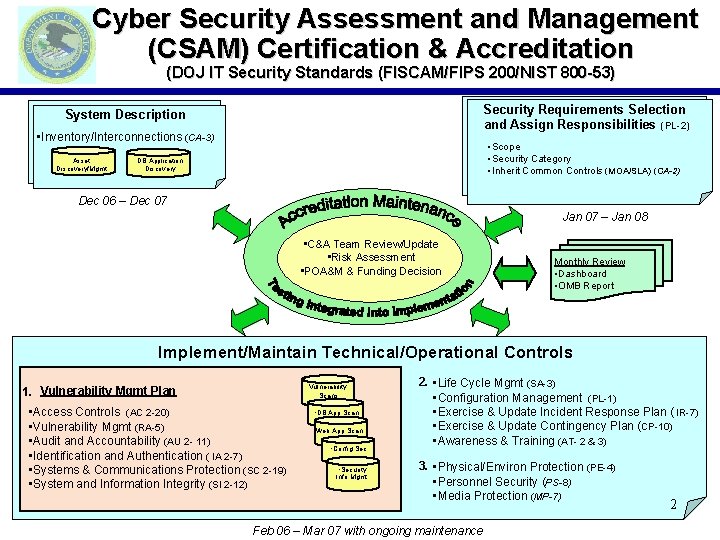
Cyber Security Assessment and Management (CSAM) Certification & Accreditation (DOJ IT Security Standards (FISCAM/FIPS 200/NIST 800 -53) Security Requirements Selection and Assign Responsibilities (PL-2) System Description • Inventory/Interconnections (CA-3) Asset Discovery/Mgmt • Scope • Security Category • Inherit Common Controls (MOA/SLA) (CA-2) DB Application Discovery Dec 06 – Dec 07 Jan 07 – Jan 08 • C&A Team Review/Update • Risk Assessment • POA&M & Funding Decision Monthly Review • Dashboard • OMB Report Implement/Maintain Technical/Operational Controls Vulnerability Scans 1. Vulnerability Mgmt Plan • Access Controls (AC 2 -20) • Vulnerability Mgmt (RA-5) • Audit and Accountability (AU 2 - 11) • Identification and Authentication ( IA 2 -7) • Systems & Communications Protection (SC 2 -19) • System and Information Integrity (SI 2 -12) • DB App Scan • Web App Scan • Config Sec • Security Info Mgmt 2. • Life Cycle Mgmt (SA-3) • Configuration Management (PL-1) • Exercise & Update Incident Response Plan ( IR-7) • Exercise & Update Contingency Plan (CP-10) • Awareness & Training (AT- 2 & 3) 3. • Physical/Environ Protection (PE-4) • Personnel Security (PS-8) • Media Protection (MP-7) Feb 06 – Mar 07 with ongoing maintenance 2
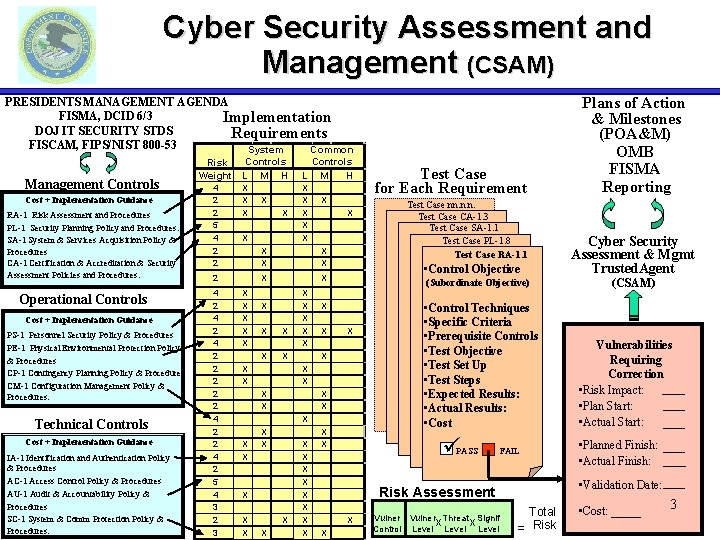
Cyber Security Assessment and Management (CSAM) PRESIDENTS MANAGEMENT AGENDA FISMA, DCID 6/3 Implementation DOJ IT SECURITY STDS Requirements FISCAM, FIPS/NIST 800 -53 System Common Management Controls Cost + Implementation Guidance RA-1 Risk Assessment and Procedures PL-1 Security Planning Policy and Procedures. SA-1 System & Services Acquisition Policy & Procedures CA-1 Certification & Accreditation & Security Assessment Policies and Procedures. Operational Controls Cost + Implementation Guidance PS-1 Personnel Security Policy & Procedures PE-1 Physical Environmental Protection Policy & Procedures CP-1 Contingency Planning Policy & Procedures CM-1 Configuration Management Policy & Procedures. Technical Controls Cost + Implementation Guidance IA-1 Identification and Authentication Policy & Procedures AC-1 Access Control Policy & Procedures AU-1 Audit & Accountability Policy & Procedures SC-1 System & Comm Protection Policy & Procedures. Controls Risk Weight L M H 4 2 2 5 4 2 2 X X X 2 4 2 4 2 2 2 4 2 5 4 3 2 3 X X X L X X X Controls M H X X X X X (Subordinate Objective) X X X X X X X Test Case nn. n. n. Test Case CA-1. 3 Test Case SA-1. 1 Test Case PL-1. 8 Test Case RA-1. 1 • Control Objective X X Test Case for Each Requirement X X • Control Techniques • Specific Criteria • Prerequisite Controls • Test Objective • Test Set Up • Test Steps • Expected Results: • Actual Results: • Cost ü PASS FAIL X Vulner Threat Signif X X Control Level Cyber Security Assessment & Mgmt Trusted. Agent (CSAM) Vulnerabilities Requiring Correction • Risk Impact: • Plan Start: • Actual Start: • Planned Finish: • Actual Finish: • Validation Date: Risk Assessment X Plans of Action & Milestones (POA&M) OMB FISMA Reporting Total = Risk • Cost: _____ 3
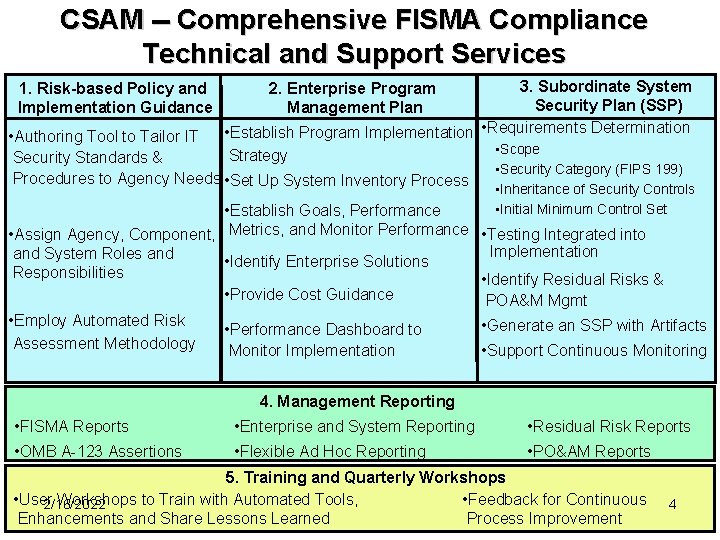
CSAM -- Comprehensive FISMA Compliance Technical and Support Services 1. Risk-based Policy and Implementation Guidance 3. Subordinate System Security Plan (SSP) • Establish Program Implementation • Requirements Determination • Scope Strategy 2. Enterprise Program Management Plan • Authoring Tool to Tailor IT Security Standards & Procedures to Agency Needs • Set Up System Inventory Process • Security Category (FIPS 199) • Inheritance of Security Controls • Initial Minimum Control Set • Establish Goals, Performance • Assign Agency, Component, Metrics, and Monitor Performance • Testing Integrated into Implementation and System Roles and • Identify Enterprise Solutions Responsibilities • Identify Residual Risks & • Provide Cost Guidance POA&M Mgmt • Employ Automated Risk Assessment Methodology • Performance Dashboard to Monitor Implementation • Generate an SSP with Artifacts • Support Continuous Monitoring 4. Management Reporting • FISMA Reports • Enterprise and System Reporting • Residual Risk Reports • OMB A-123 Assertions • Flexible Ad Hoc Reporting • PO&AM Reports 5. Training and Quarterly Workshops • User Workshops to Train with Automated Tools, • Feedback for Continuous 2/16/2022 Enhancements and Share Lessons Learned Process Improvement 4
Business Readiness CSAM Strategy Responsive actions to customer feedback and continuous improvements are key to ensuring satisfied users • Justice has successfully implemented service level agreements and revolving funds to support IT operations • Reliable reimbursement process for managing reimbursable customer contracting support arrangements is in place • Several Justice contracting vehicles are in place • BPA Delivery Orders • ITSS-3 Indefinite Delivery/Indefinite Quantity Contract • GSA Schedule 5
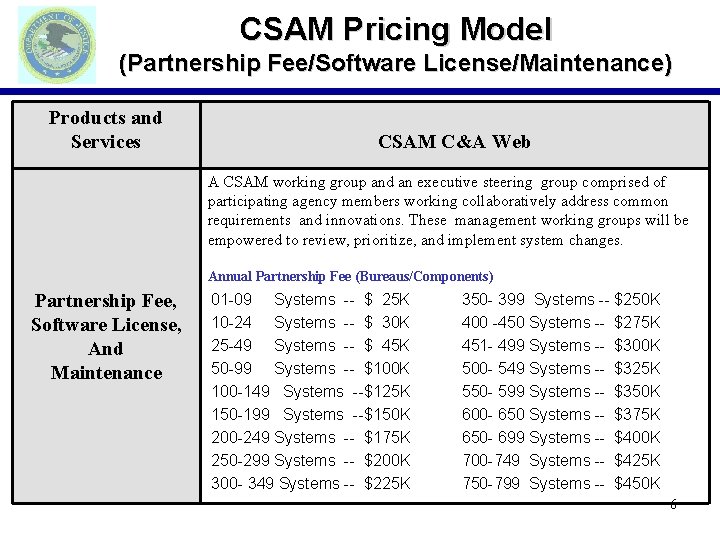
CSAM Pricing Model (Partnership Fee/Software License/Maintenance) Products and Services CSAM C&A Web A CSAM working group and an executive steering group comprised of participating agency members working collaboratively address common requirements and innovations. These management working groups will be empowered to review, prioritize, and implement system changes. Annual Partnership Fee (Bureaus/Components) Partnership Fee, Software License, And Maintenance 01 -09 Systems -- $ 25 K 10 -24 Systems -- $ 30 K 25 -49 Systems -- $ 45 K 50 -99 Systems -- $100 K 100 -149 Systems --$125 K 150 -199 Systems --$150 K 200 -249 Systems -- $175 K 250 -299 Systems -- $200 K 300 - 349 Systems -- $225 K 350 - 399 Systems -- $250 K 400 -450 Systems -- $275 K 451 - 499 Systems -- $300 K 500 - 549 Systems -- $325 K 550 - 599 Systems -- $350 K 600 - 650 Systems -- $375 K 650 - 699 Systems -- $400 K 700 -749 Systems -- $425 K 750 -799 Systems -- $450 K 6
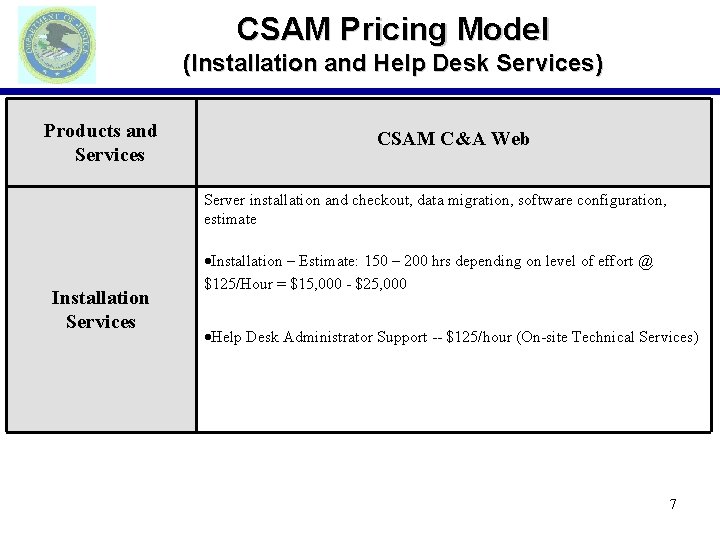
CSAM Pricing Model (Installation and Help Desk Services) Products and Services CSAM C&A Web Server installation and checkout, data migration, software configuration, estimate Installation Services Installation – Estimate: 150 – 200 hrs depending on level of effort @ $125/Hour = $15, 000 - $25, 000 Help Desk Administrator Support -- $125/hour (On-site Technical Services) 7
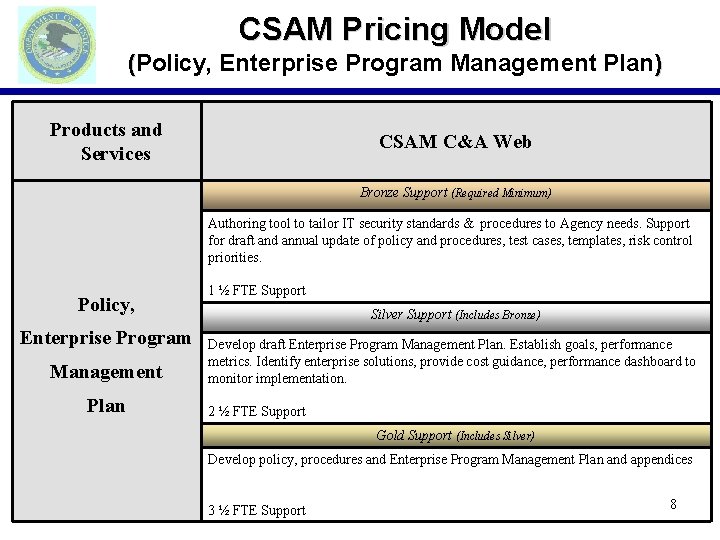
CSAM Pricing Model (Policy, Enterprise Program Management Plan) Products and Services CSAM C&A Web Bronze Support (Required Minimum) Authoring tool to tailor IT security standards & procedures to Agency needs. Support for draft and annual update of policy and procedures, test cases, templates, risk control priorities. Policy, Enterprise Program Management Plan 1 ½ FTE Support Silver Support (Includes Bronze) Develop draft Enterprise Program Management Plan. Establish goals, performance metrics. Identify enterprise solutions, provide cost guidance, performance dashboard to monitor implementation. 2 ½ FTE Support Gold Support (Includes Silver) Develop policy, procedures and Enterprise Program Management Plan and appendices 3 ½ FTE Support 8
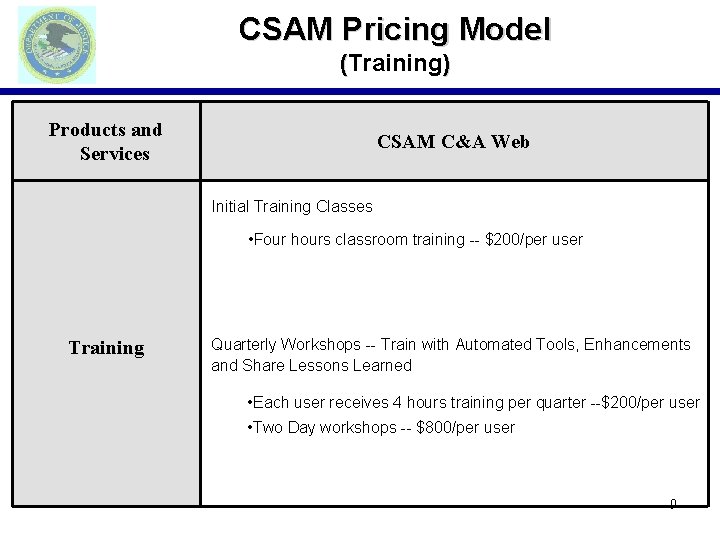
CSAM Pricing Model (Training) Products and Services CSAM C&A Web Initial Training Classes • Four hours classroom training -- $200/per user Training Quarterly Workshops -- Train with Automated Tools, Enhancements and Share Lessons Learned • Each user receives 4 hours training per quarter --$200/per user • Two Day workshops -- $800/per user 9
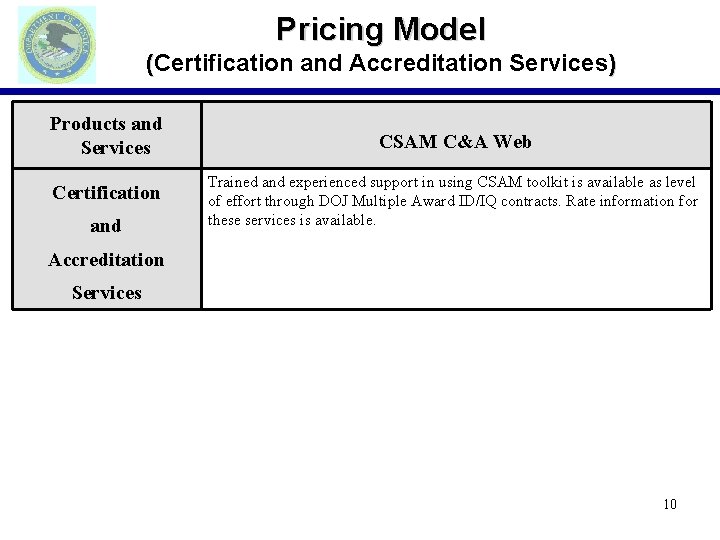
Pricing Model (Certification and Accreditation Services) Products and Services Certification and CSAM C&A Web Trained and experienced support in using CSAM toolkit is available as level of effort through DOJ Multiple Award ID/IQ contracts. Rate information for these services is available. Accreditation Services 10
Conclusion CSAM… Is a comprehensive FISMA compliance Technology and Support Services solution The CSAM solution includes… 1. Risk-based Policy and Implementation Guidance 2. Enterprise Program Management Plan 3. Subordinate System Security Plans 4. Training and Quarterly Workshops 5. Robust Management Reporting For more information or to request a system demonstration, email: DOJLOBCSAM@usdoj. gov or contact: Ken Gandola Jim Leahy 202 -353 -0081 202 -353 -8741 Kenneth. d. gandola@usdoj. gov james. t. leahy@usdoj. gov 11
- Slides: 11