Cyber Patriot Training Round 1 results Official Results
Cyber. Patriot Training
Round 1 results • Official Results to be posted Monday • We incurred a time limit deduction • Remember it is how quickly and correctly can we get to 100%?
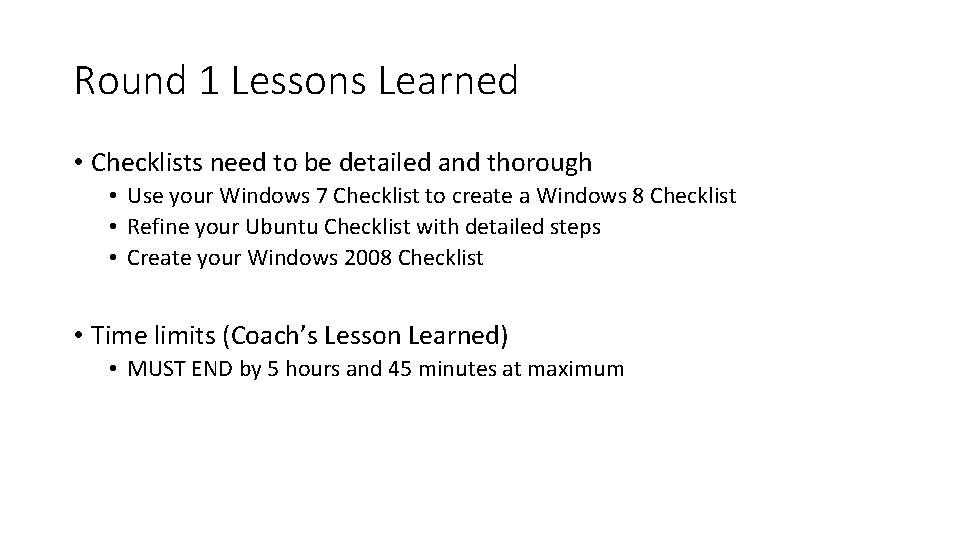
Round 1 Lessons Learned • Checklists need to be detailed and thorough • Use your Windows 7 Checklist to create a Windows 8 Checklist • Refine your Ubuntu Checklist with detailed steps • Create your Windows 2008 Checklist • Time limits (Coach’s Lesson Learned) • MUST END by 5 hours and 45 minutes at maximum
ROUND 2 • Windows 8 • Ubuntu 14. 04 • Windows Server 2008 • Networking Quiz(Modules: 8 -12) • Packet Tracer(Modules: 1 -12)
Lessons from the Server 2008 Introductory Image • Guest account has been secured • How do I find this problem? Securing Guest accounts is a good cybersecurity practice in general. • How do I solve this problem? • Open the Start Menu and access the Control Panel. Click on "User Accounts" -> "Manage another account. " Click on the Guest account. On this page, click the option to "Turn off the guest account. " • Why is fixing this problem important? • Guest accounts allow any individual to log on to a computer anonymously. While someone using this account may not be able to directly access other users' information, he or she may still disrupt the resources of the local computer. The Guest account allows individuals to access the computer more easily, and its anonymity makes it harder to hold them accountable for inappropriate actions.
Lessons from the Server 2008 Introductory Image • A password of at least 8 characters is required • How do I find this problem? • Enforcing use of longer passwords is a good cybersecurity practice in general. • How do I solve this problem? • Open the Start Menu and access the Control Panel. Click "Administrative Tools" -> "Local Security Policy" -> "Account Policies" -> "Password Policy" -> "Minimum password length. " In this window, you can set the number of characters required in a user password to 8. • Why is fixing this problem important? • Setting a password policy ensures that all users on the system have to set a secure password. By setting a password minimum length, IT administrators force users to create more secure passwords.
Lessons from the Server 2008 Introductory Image • Remote Registry has been disabled • How do I find this problem? Disabling Remote Registry is a good cybersecurity practice in general. • How do I solve this problem? • Go to the Startup Menu and type in "services. msc" in the search bar. Hit "Enter" to go to the services window. Scroll down to this list until you find "Remote Registry. " Double-click this service. Change the "Startup Type" to "Disabled" and stop the service. Click "Apply" and close the window. • Why is fixing this problem important? • The Remote Registry service allows users to modify the Windows registry file remotely. This service should be disabled because it creates a potential security vulnerability. If left running, a remote user could modify the system registry to create new security issues or render the system unusable.
Lessons from the Server 2008 Introductory Image • Ophcrack program has been removed • How do I find this problem? • The README file notes that only software for basic office tasks should be on this image. The ophcrack is password cracking software that does not meet these requirements and therefore should be removed. • How do I solve this problem? • Open up Windows Explorer. Click the C: Drive and then access the Program Files folder. Delete the folder called ophcrack. • Why is fixing this problem important? • This software is a violation of the company's security policies. Unknown programs on a computer could contain malware or allow outside individuals access to the computer. It is important to keep only well-known software that is used for a necessary purpose on your computer.
Lessons from the Server 2008 Introductory Image • Remote Desktop has been enabled • How do I find this problem? • The README file notes that Remote Desktop is required for employees who telework. • How do I solve this problem? • From the Start Menu, right click on “Computer” and select “Properties. ” Select “Remote settings” from the left sidebar menu and then select “Allow connections only from computers running Remote Desktop with Network Level Authentication” from the Remote Desktop dialog box and then click “Apply. ” • Why is fixing this problem important? • By enabling this service, employees who telework will be able to complete their work successfully.
Lessons from the Server 2008 Introductory Image • A secure account lockout threshold has been enabled • How do I find this problem? Enabling this feature is a good security practice in general. • How do I solve this problem? • Open the Start Menu and access the Control Panel. Click "Administrative Tools" -> "Local Security Policy" -> "Account Policies" -> "Account Lockout Policy" -> "Account lockout threshold" Change the setting to a value between 3 -10 invalid logon attempts. After setting the value for this setting, you will be prompted to change “Account Lockout Duration” and “Reset account lockout counter after” settings to 30 minutes each. Apply these values. • Why is fixing this problem important? • Setting a secure account lockout threshold is important because it is the number of times that a user can type in their account password incorrectly before getting locked out. An account threshold that is too low will frustrate users who may simply be making a typo and get locked out as a result. An account lockout threshold that is too high is insecure, as an attacker will have more attempts to guess a user’s password and gain unwanted access to their data.
Lessons from the Server 2008 Introductory Image • Former employee account has been removed • How do I find this problem? • One of the first things you should do when starting an image during a competition is check the README file on the desktop. There, you will see the valid users for the image. These are the only users that should have an account. All others should be removed. • How do I solve this problem? • Open the Start Menu and access the Control Panel. Click on "User Accounts" -> "Manage Another Account. " In this window, you can click the users that are not listed on the valid user list in the README file and select the option to "Delete the Account. " Make sure to write down the names of any user you deleted. You may need this information later. You will then be prompted to delete or keep this user's files once you delete them. Select "Delete Files. " • Why is fixing this problem important? • Computer access should be limited to just those who need to use it to complete their tasks. By leaving these user accounts on the image, invalid individuals may be able to log on to the computer and make changes that could affect the safety and security of legitimate users.
Lessons from the Server 2008 Introductory Image • Actions that invoked penalties: • Required software has been removed • From README Fire. Fox and Libre. Office 4 required. • Valid users have been deleted • Account lockout threshold is less than 3 • World Wide Web Publishing service is stopped or disabled
A good checklist item 1. Turn On Firewall a) b) c) d) e) Go to the Control Panel from the Start Menu In the search bar type “Firewall” Click on Windows Firewall On the left side, click on [Turn windows firewall on or off] Select [Turn on windows firewall] for both private and public windows settings f) Click [OK]
Objectives • Today’s practice lets you start your checklists • Work as one team • Be specific • Next practice is not until December 3 rd • Expectation is that teams will work together to produce an amazing checklist to be tested at the December 3 rd training • Round 2 is on December 10 th • Remember we must end at 5 hours and 45 minutes at maximum
- Slides: 14