Cyber Insurance What You Need to Know CanTech
Cyber Insurance: What You Need to Know Can-Tech 2019 Technology Law Spring Forum Panel Moderator: Steve Tenai (Aird & Berlis LLP) Erin Flett Professional Liability & Cyber Supervisor, Financial Lines Chubb Canada Jonathan Weekes Vice President, Marsh Canada National Cyber Practice Marsh Canada Andrea Fisher Senior Claims Specialist Financial Lines Chubb Canada June 17, 2019 This presentation may contain general comments on legal issues of concern to organizations and individuals. These comments are not intended to be, nor should they be construed as, legal advice. Please consult a legal professional on the particular issues that concern you.
Insurance Lines What are the typical insurance policies for a business enterprise?
Common Forms of Insurance for Businesses • • • General Liability Business Interruption Commercial Crime Professional Liability D&O Liability Kidnap, Ransom & Extortion Insurance Evolution of the Cyber product Technology E&O (Third Party Liability) + Media Liability (Third Party Liability) + Financial Institutions Fidelity Bond (First Party Direct Expense) • = Today’s Hybrid Cyber Contract © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
Cyber Insurance • What is Cyber? http: //editorialcartoonists. com/cartoon/display. cfm? cartoonist=Cox. A © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
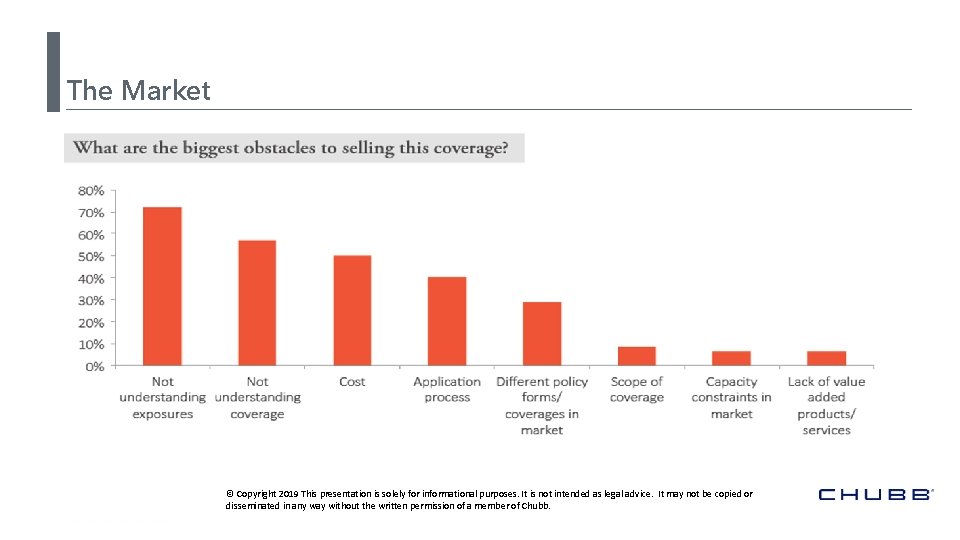
The Market © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.

Cyber Breach Losses Understanding the Full Spectrum of Potential Losses
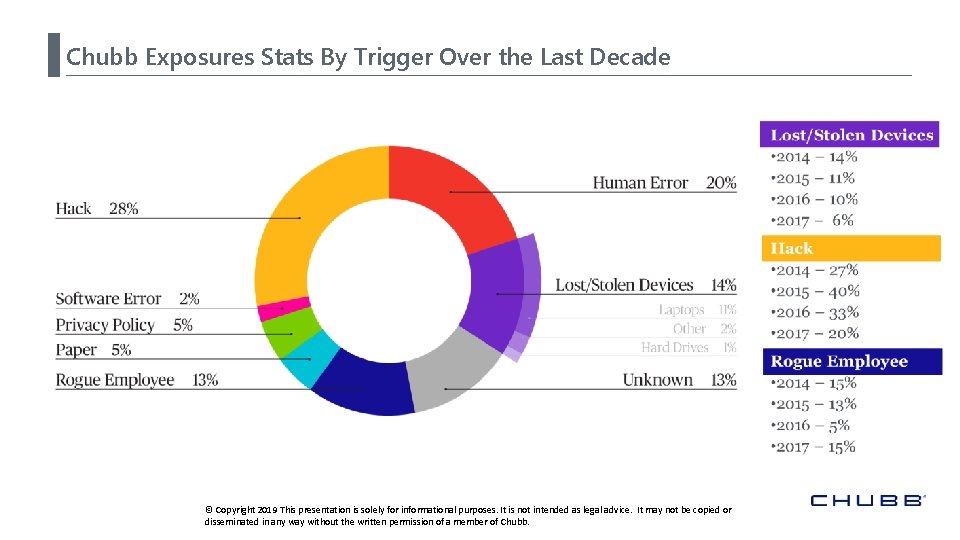
Chubb Exposures Stats By Trigger Over the Last Decade © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
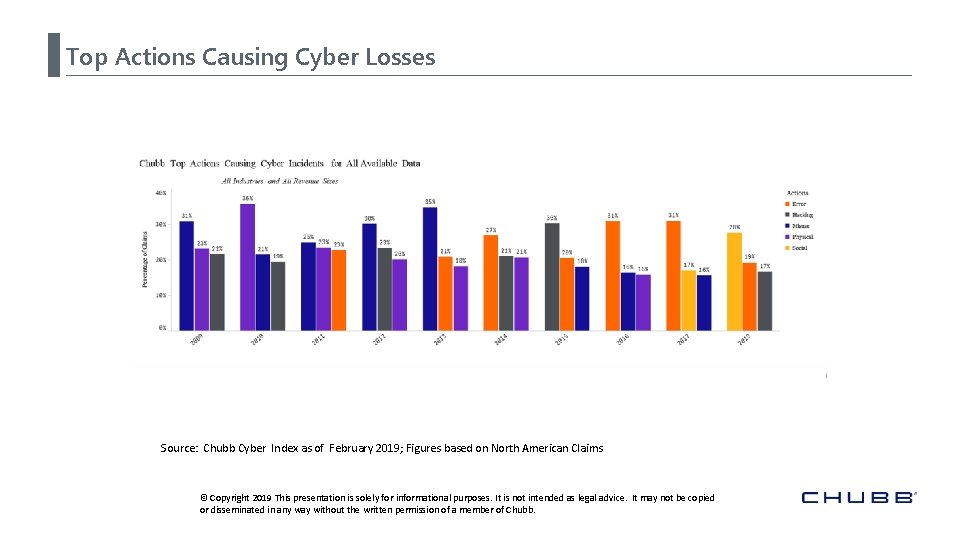
Top Actions Causing Cyber Losses Source: Chubb Cyber Index as of February 2019; Figures based on North American Claims © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
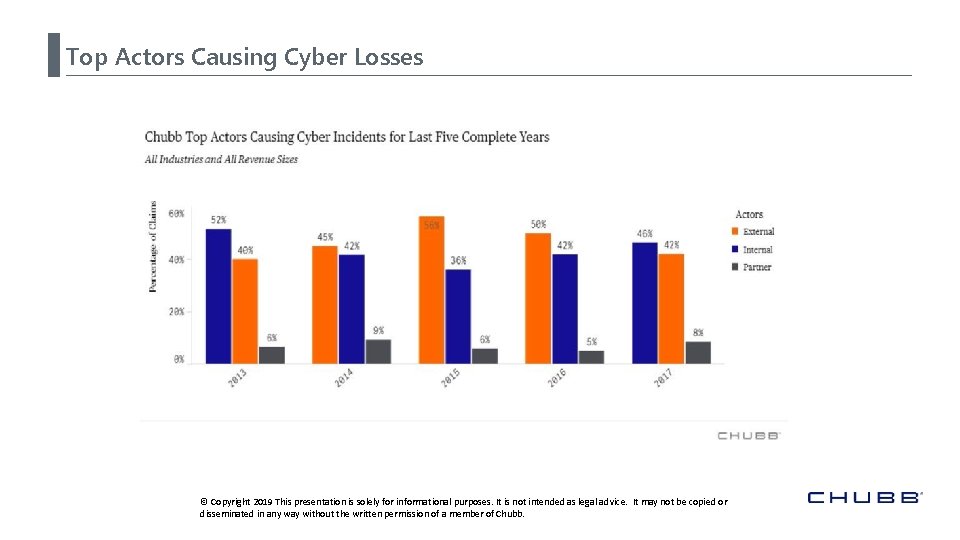
Top Actors Causing Cyber Losses © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
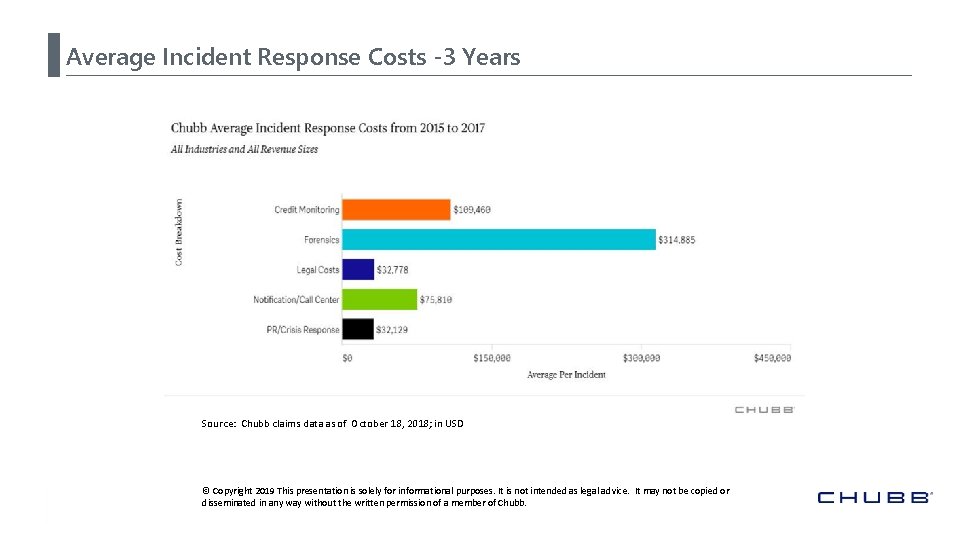
Average Incident Response Costs -3 Years Source: Chubb claims data as of October 18, 2018; in USD © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
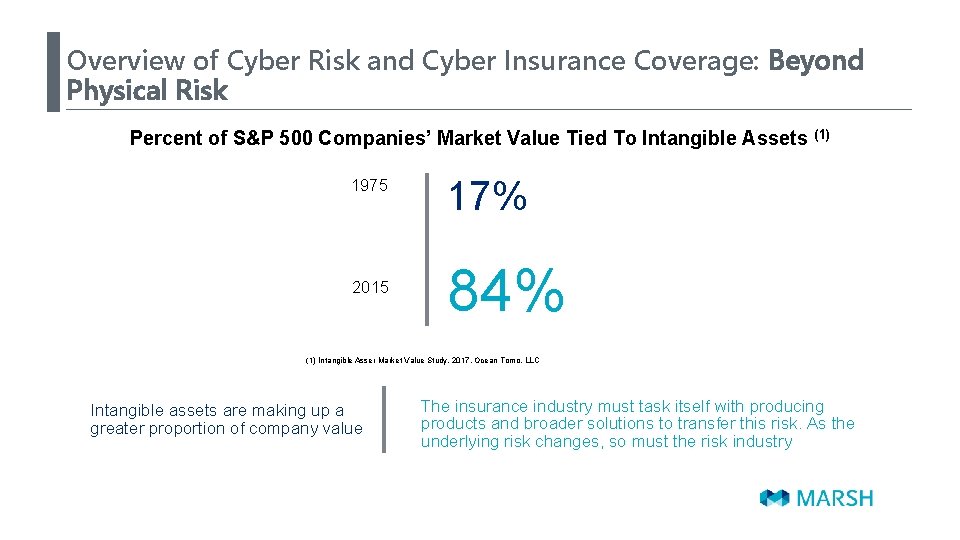
Overview of Cyber Risk and Cyber Insurance Coverage: Beyond Physical Risk Percent of S&P 500 Companies’ Market Value Tied To Intangible Assets 1975 2015 (1) 17% 84% (1) Intangible Asser Market Value Study, 2017, Ocean Tomo, LLC Intangible assets are making up a greater proportion of company value The insurance industry must task itself with producing products and broader solutions to transfer this risk. As the underlying risk changes, so must the risk industry
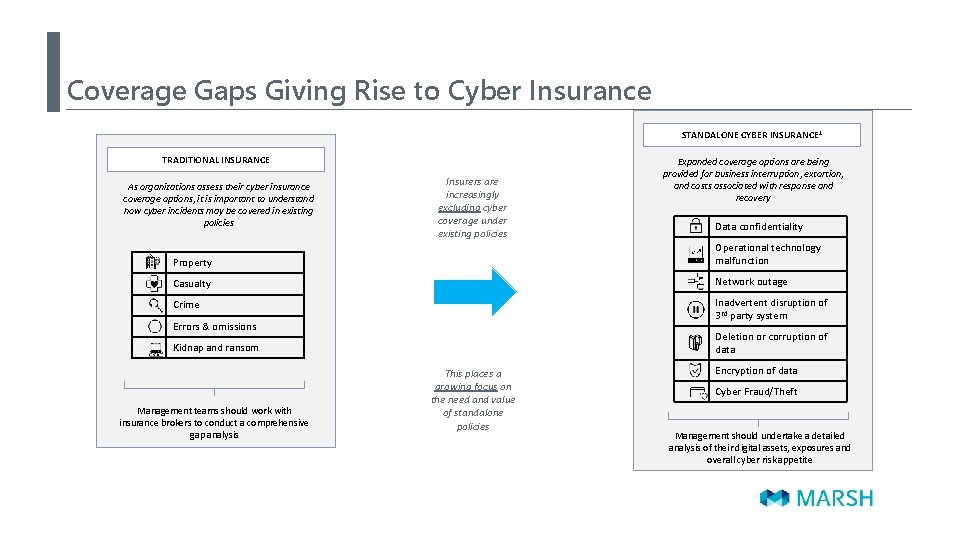
Coverage Gaps Giving Rise to Cyber Insurance STANDALONE CYBER INSURANCE 1 TRADITIONAL INSURANCE As organizations assess their cyber insurance coverage options, it is important to understand how cyber incidents may be covered in existing policies Insurers are increasingly excluding cyber coverage under existing policies Expanded coverage options are being provided for business interruption, extortion, and costs associated with response and recovery Data confidentiality Property Operational technology malfunction Casualty Network outage Crime Inadvertent disruption of 3 rd party system Errors & omissions Deletion or corruption of data Kidnap and ransom Management teams should work with insurance brokers to conduct a comprehensive gap analysis This places a growing focus on the need and value of standalone policies Encryption of data Cyber Fraud/Theft Management should undertake a detailed analysis of their digital assets, exposures and overall cyber risk appetite
Covered Cyber Events • Events typically covered by Cyber Insurance: - Ransomware attacks - Phishing attacks - Human error (e. g. lost/stolen laptop, PII)
What Have We Paid Lately-Chubb Business Interruption Claim • Insured was the victim of a denial of service attack from an unknown source • The attack caused a 22 -hour outage to the company’s website and a continued degradation of service for an additional 4 days • The incident resulted in the company’s inability to sell subscriptions to customers through its website • This event resulted in $750, 000 in business interruption losses and an additional $40, 000 was spent on forensic accounting services © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.

Buying Cyber Insurance What Are the Key Consideration in Selecting the Right Coverage?
Key Consideration in Selecting the Right Coverage Privacy Based Exposure Areas of Focus Should Be: • Privacy Breach Liability • Incident Response/Notification Costs • Regulatory Defense, Fines & Penalties Operational Disruption Exposure Areas of Focus Should Be: • Business Interruption • Contingent Business Interruption • Data Asset Restoration Costs • Cyber Extortion

• UNDERSTAND your security and privacy risk management policies and procedures are the most important and first line of defense • MEASURE and quantify the security and privacy exposures that are most relevant to your organization • Determine which security and privacy exposures/risks your organization is comfortable accepting and which exposures/risks your organization may consider transferring through insurance • Analyze your organization’s current portfolio of insurance products to see if you already have some from of security and privacy coverage • If, after considering the items above, your organization feels that cyber insurance would be helpful as a second line of defense in MANAGING your cyber risk, reach out to your broker to discuss further.
Key Cyber Insurance Clauses What Are the Key Clauses to a Cyber Insurance Policy?
Key Cyber Insurance Clauses: First Party Coverage Business Interruption (BI) / Extra Expense and Contingent Business Interruption Digital Asset Replacement Incident Response Costs / Event Management Cyber Extortion
Key Cyber Insurance Clauses: Third Party Coverage Privacy Liability Network Security Liability Media Liability Privacy Regulatory Defense Costs
Buying Cyber Insurance What Will You Be Required to Demonstrate and Represent?

What Insurance Covers What For Cyber Losses? Why Do Businesses Need Cyber Insurance?
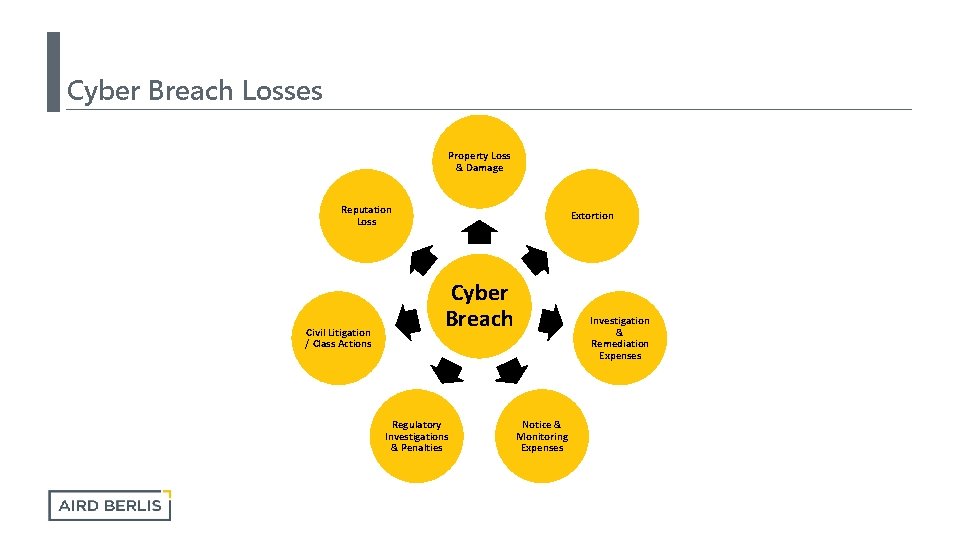
Cyber Breach Losses Property Loss & Damage Reputation Loss Civil Litigation / Class Actions Extortion Cyber Breach Regulatory Investigations & Penalties Investigation & Remediation Expenses Notice & Monitoring Expenses
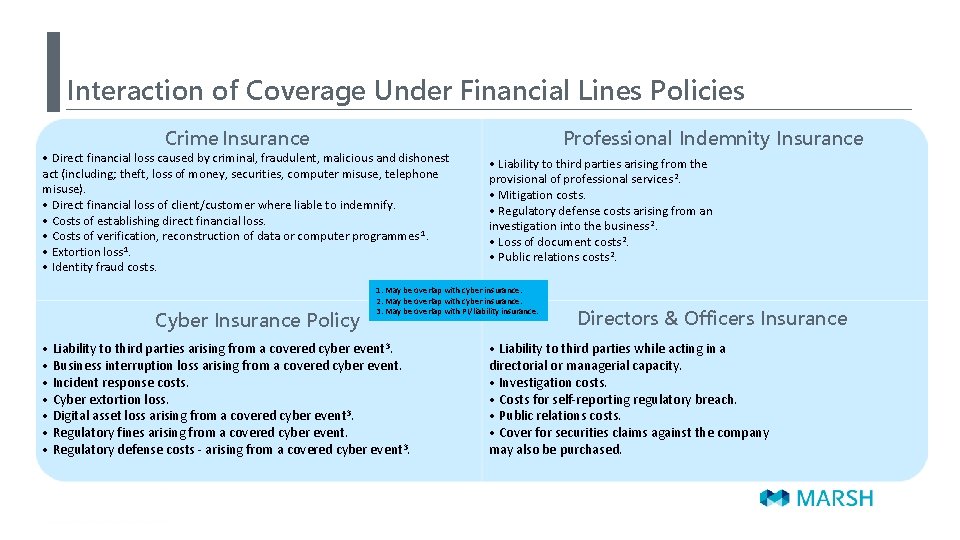
Interaction of Coverage Under Financial Lines Policies Professional Indemnity Insurance Crime Insurance • Direct financial loss caused by criminal, fraudulent, malicious and dishonest act (including; theft, loss of money, securities, computer misuse, telephone misuse). • Direct financial loss of client/customer where liable to indemnify. • Costs of establishing direct financial loss. • Costs of verification, reconstruction of data or computer programmes 1. • Extortion loss 1. • Identity fraud costs. Cyber Insurance Policy • Liability to third parties arising from the provisional of professional services 2. • Mitigation costs. • Regulatory defense costs arising from an investigation into the business 2. • Loss of document costs 2. • Public relations costs 2. 1. May be overlap with cyber insurance. 2. May be overlap with cyber insurance. 3. May be overlap with PI/liability insurance. • Liability to third parties arising from a covered cyber event 3. • Business interruption loss arising from a covered cyber event. • Incident response costs. • Cyber extortion loss. • Digital asset loss arising from a covered cyber event 3. • Regulatory fines arising from a covered cyber event. • Regulatory defense costs - arising from a covered cyber event 3. Directors & Officers Insurance • Liability to third parties while acting in a directorial or managerial capacity. • Investigation costs. • Costs for self-reporting regulatory breach. • Public relations costs. • Cover for securities claims against the company may also be purchased.
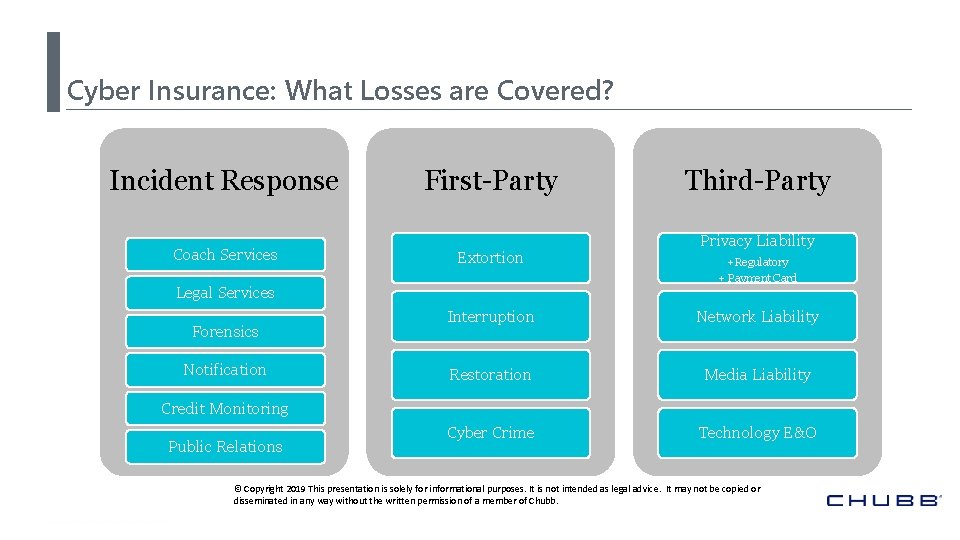
Cyber Insurance: What Losses are Covered? Incident Response Coach Services First-Party Extortion Legal Services Forensics Notification Third-Party Privacy Liability +Regulatory + Payment Card Interruption Network Liability Restoration Media Liability Cyber Crime Technology E&O Credit Monitoring Public Relations © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
Cyber Insurance What Losses Are Not Covered: • Cyber Insurance typically does not include coverage for: • Traditional Insurance Coverage: - General Liability, Commercial Crime, Professional Liability, D&O Liability, Kidnap, Ransom and Extortion Coverage • Loss of money or property due to computer fraud, phishing or social engineering (ever changing) • Professional Services • Bodily Injury and Property Damage • Pollution Coverage • Proprietary trade secrets • System Upgrade post breach • Loss of goodwill, valuation © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
You Suspect a Cyber Breach Now What?
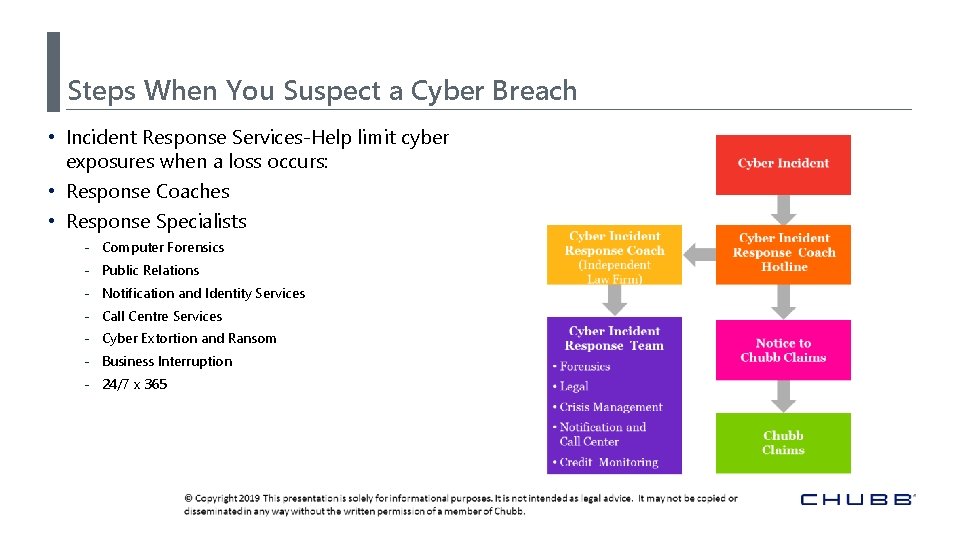
Steps When You Suspect a Cyber Breach • Incident Response Services-Help limit cyber exposures when a loss occurs: • Response Coaches • Response Specialists - Computer Forensics - Public Relations - Notification and Identity Services - Call Centre Services - Cyber Extortion and Ransom - Business Interruption - 24/7 x 365
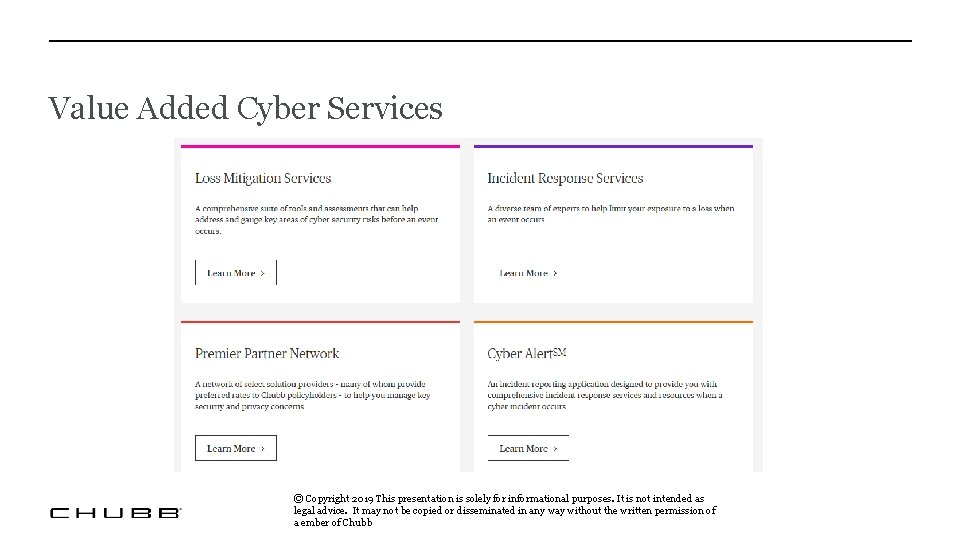
Value Added Cyber Services © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a ember of Chubb
Respond with Chubb Cyber Alert. TM • Live specialists are available 24 X 7 to report an incident (not claim reporting) • Attach photos to help in the assessment of an incident (e. g. , phishing emails, ransomware) • Incident logging and history with real time status updates • For more information: www. chubbcyberalert. com • Chubb Cyber Alert can be downloaded from the App Store or Google Play Store
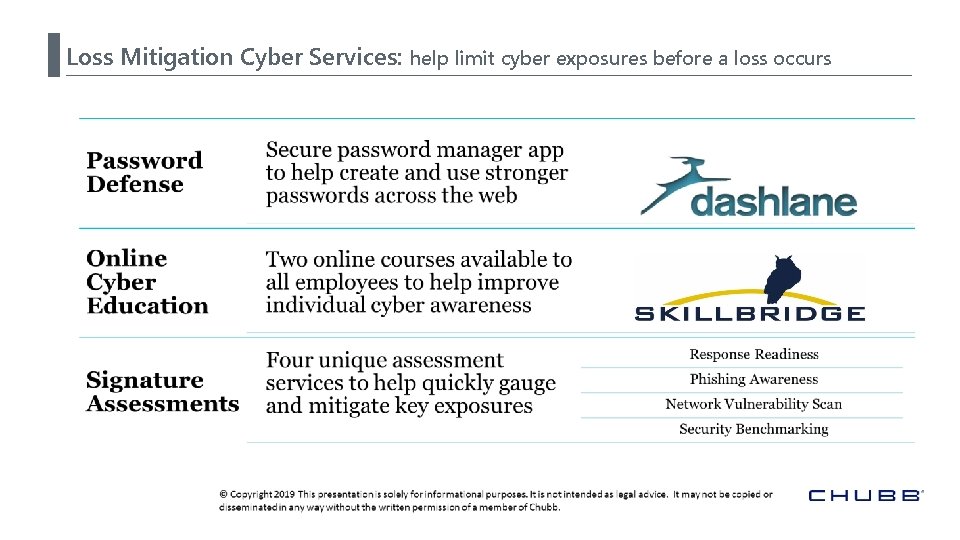
Loss Mitigation Cyber Services: help limit cyber exposures before a loss occurs
You Suspect a Cyber Breach What Mistakes In How You Respond Can Put Coverage at Risk?
Common Mistakes in Response • • Working in silos Late reporting Failing to involve a breach coach Use of non-panel vendors

Questions Aird & Berlis LLP | Lawyers Brookfield Place, 181 Bay Street, Suite 1800, Toronto, Canada M 5 J 2 T 9 T 416. 863. 1500 F 416. 863. 1515 | airdberlis. com
Disclaimer Chubb The material presented in this presentation is not intended to provide legal or other expert advice as to any of the subjects mentioned, but rather is presented for general information only. You should consult knowledgeable legal counsel or other knowledgeable experts as to any legal or technical questions you may have. Further, the insurance discussed is a product summary only. For actual terms and conditions of any insurance product, please refer to the policy. © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
Disclaimer Marsh This document and any recommendations, analysis, or advice provided by Marsh (collectively, the “Marsh Analysis”) are intended solely for the entity identified as the recipient herein (“you”). This document contains proprietary, confidential information of Marsh and may not be shared with any third party, including other insurance producers, without Marsh’s prior written consent. Any statements concerning actuarial, tax, accounting, or legal matters are based solely on our experience as insurance brokers and risk consultants and are not to be relied upon as actuarial, accounting, tax, or legal advice, for which you should consult your own professional advisors. Any modeling, analytics, or projections are subject to inherent uncertainty, and the Marsh Analysis could be materially affected if any underlying assumptions, conditions, information, or factors are inaccurate or incomplete or should change. The information contained herein is based on sources we believe reliable, but we make no representation or warranty as to its accuracy. Except as may be set forth in an agreement between you and Marsh, Marsh shall have no obligation to update the Marsh Analysis and shall have no liability to you or any other party with regard to the Marsh Analysis or to any services provided by a third party to you or Marsh makes no representation or warranty concerning the application of policy wordings or the financial condition or solvency of insurers or reinsurers. Marsh makes no assurances regarding the availability, cost, or terms of insurance coverage. Marsh is one of the Marsh & Mc. Lennan Companies, together with Guy Carpenter, Mercer, and Oliver Wyman. Copyright © 2019 Marsh Canada Limited and its licensors. All rights reserved © Copyright 2019 This presentation is solely for informational purposes. It is not intended as legal advice. It may not be copied or disseminated in any way without the written permission of a member of Chubb.
- Slides: 36