CYBER CRIMINALS AND THE POTENTIAL FOR CYBER WAR
CYBER CRIMINALS AND THE POTENTIAL FOR CYBER WAR HOW DO WE PROTECT OURSELVES AND OUR COUNTRY? SHARON ONEAL SHARONONEAL@EMAIL. ARIZONA. EDU 520 -822 -4040
• • • Cyber Crime damage costs to reach $6 trillion annually by 2021 • Every minute 1, 080 hacks occur Human attack surface to reach 6 billion people by 2022 Typical Dwell Time in public Infrastructure networks before Penetration Detection: 128 Days • INTERESTIN G CYBER FACTS • 27 Days to Resolve at an average cost of ~$ 7. 4 M / incident Software Code: 4. 9 Flaws/1000 Lines of Code • 1 to 5% represent a serious vulnerability • Typical Penetration Detector: External Vulnerability Assessment • Currently more than 1. 5 Million Cyber Security Jobs are unfilled (Expected to rise to 3. 5 M by 2021) • • Attacker only needs 0. 0001 Success Rate Most Asset Owners aren’t aware of their Outbound Traffic: • Number of Connections • Length of Connection • Amount of Data • % Encrypted • Destination IP

CYBER THREAT LANDSCAPE Source: https: //www 2. deloitte. com/content/dam/Deloitte/us/Documents/energy-resources/us-er-cyber-risk-protecting-our-critical-

DEPT OF HOMELAND SECURITY (DHS) – 16 CRITICAL INFRASTRUCTURE SECTORS Complex Interactions With Limited Corresponding Government - Industry Expertise & Accountability
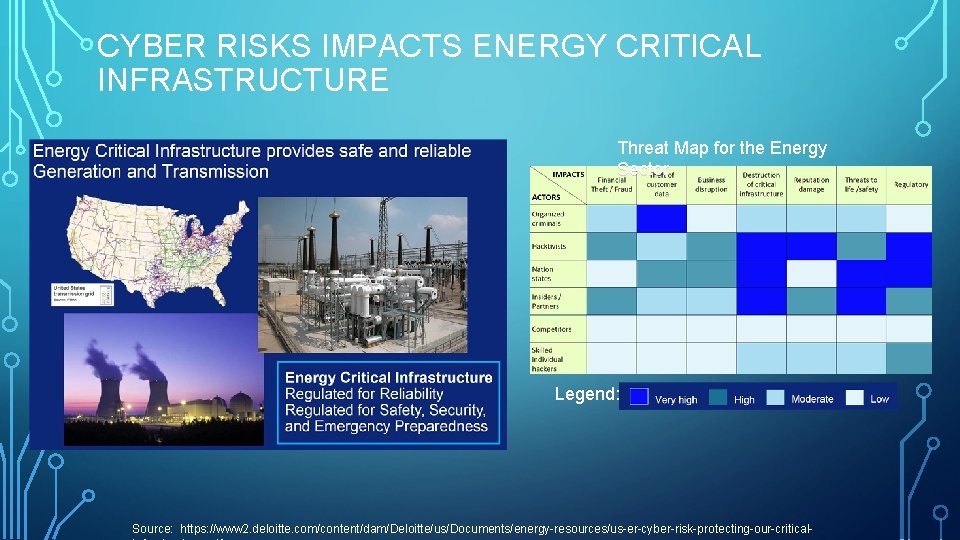
CYBER RISKS IMPACTS ENERGY CRITICAL INFRASTRUCTURE Threat Map for the Energy Sector Legend: Source: https: //www 2. deloitte. com/content/dam/Deloitte/us/Documents/energy-resources/us-er-cyber-risk-protecting-our-critical-
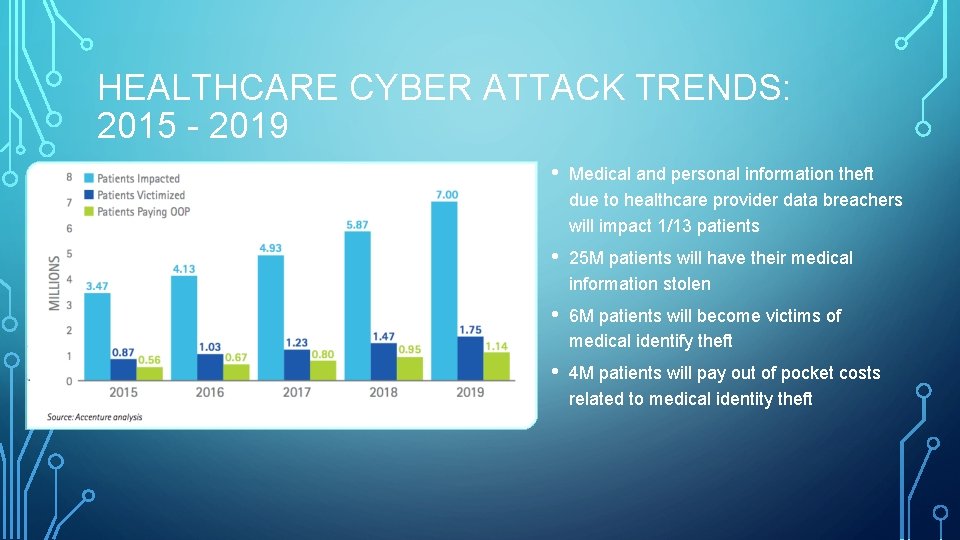
HEALTHCARE CYBER ATTACK TRENDS: 2015 - 2019 • Medical and personal information theft due to healthcare provider data breachers will impact 1/13 patients • 25 M patients will have their medical information stolen • 6 M patients will become victims of medical identify theft • 4 M patients will pay out of pocket costs related to medical identity theft
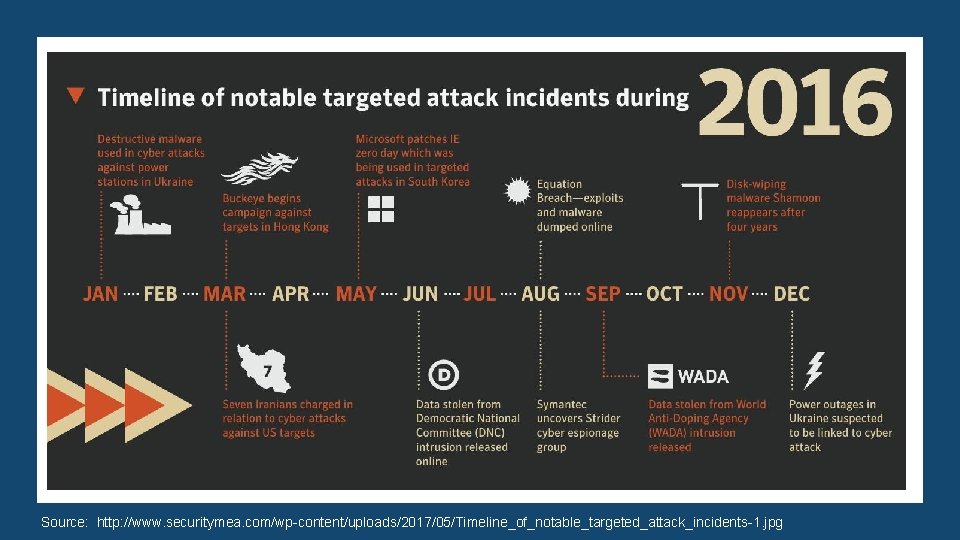
Source: http: //www. securitymea. com/wp-content/uploads/2017/05/Timeline_of_notable_targeted_attack_incidents-1. jpg
DEFENSE DEPARTMENT CYBER SPENDING

STUXNET: ONE OF THE WORLD’S FIRST DIGITAL WEAPONS STUXNET Destroyed Manufacturing Equipment Connected to a Secure, Closed Network
- Slides: 9