CWSP Guide to Wireless Security Chapter 6 Enterprise
- Slides: 49
CWSP Guide to Wireless Security Chapter 6 Enterprise Wireless Hardware Security CWSP Guide to Wireless Security
Objectives • List and describe the functions of the different types of wireless LAN hardware used in an enterprise • Tell how access control and protocol filtering can protect a WLAN • Describe the functions of Quality of Service, handoffs, and power features of wireless networking hardware CWSP Guide to Wireless Security 2
Enterprise WLAN Hardware • Wireless hardware – – – Access points Remote wireless bridges Wireless routers Wireless gateways Wireless switches Wireless mesh routers CWSP Guide to Wireless Security 3
Access Point • AP parts – An antenna and a radio transmitter/receiver to send and receive signals – An RJ-45 wired network interface that allows it to connect by cable to a standard wired network – Special bridging software to interface wireless devices to other devices • Basic functions – Acts as the base station for the wireless network – Acts as a bridge between wireless and wired network CWSP Guide to Wireless Security 4
Access Point (continued) • Range of an access point depends on: – Type of wireless network that is supported – Walls, doors, and other solid objects can reduce the distance the signal may travel • Number of wireless clients supported varies – Theoretical: 100 clients – For light traffic: 50 clients – For heavy traffic: 20 clients CWSP Guide to Wireless Security 5
Remote Wireless Bridge • Bridge – Connects two network segments together – Segments can use different types of physical media – Software for transmitting and receiving signals • Remote wireless bridge – Wireless device designed to connect two or more wired or wireless networks – Transmits at higher power than APs – Uses a highly directional or semi-directional antenna CWSP Guide to Wireless Security 6
Remote Wireless Bridge (continued) • Highly directional antennas – Usually concave, dish-shaped devices used for long distance, point-to-point wireless links • Semi-directional antenna – Focuses the energy in one direction – Does not have the high power level of a highly directional antenna – Primarily used for short- and medium-range remote wireless bridge networks CWSP Guide to Wireless Security 7
Remote Wireless Bridge (continued) CWSP Guide to Wireless Security 8
Remote Wireless Bridge (continued) • Delay spread – Minimizes the spread of the signal so that it can reach farther distances • Remote wireless bridges support two types of connections – Point-to-point connections – Point-to-multipoint connections CWSP Guide to Wireless Security 9
Remote Wireless Bridge (continued) CWSP Guide to Wireless Security 10
Remote Wireless Bridge (continued) CWSP Guide to Wireless Security 11
Remote Wireless Bridge (continued) • Remote wireless bridge modes – Access point mode • Standard AP – Root mode • Acts as a root bridge and can communicate only with other non-root bridges – Non-root mode • Can transmit only to a root bridge – Repeater mode • Extends the distance between LAN segments CWSP Guide to Wireless Security 12
Remote Wireless Bridge (continued) CWSP Guide to Wireless Security 13
Remote Wireless Bridge (continued) CWSP Guide to Wireless Security 14
Remote Wireless Bridge (continued) • Remote wireless bridges – Cost-effective alternative to expensive leased wired options for connecting remote buildings – Distance can be up to 29 kilometers (18 miles) transmitting at 11 Mbps • Or up to 40 kilometers (25 miles) transmitting at 2 Mbps CWSP Guide to Wireless Security 15
Wireless Router • Router – Transfers packets between networks – Selects the best link (route) to send packets • Wireless router – Combines an access point with a router – Typically with multiple ports • Advantages – Connects multiple networks – Improves network performance – Shares single IP address CWSP Guide to Wireless Security 16
Wireless Router (continued) CWSP Guide to Wireless Security 17
Wireless Router (continued) CWSP Guide to Wireless Security 18
Wireless Gateway • Gateway – Acts as an entrance to another network • Wireless gateway – Combines an access point, router, network address translation, and other networking features • Enterprise wireless gateway functions – – – Authentication Encryption Intrusion detection and malicious program protection Bandwidth management Centralized network management CWSP Guide to Wireless Security 19
Wireless Switch • Switch – Joins multiple computers within one LAN – Contains more “intelligence” than a hub • Types of switches – Unmanaged switch • Provides no management capabilities of the switch – Managed switch • Provides all of the features of an unmanaged switch along with enhanced management features • Supports both control and monitoring of the network CWSP Guide to Wireless Security 20
Wireless Switch (continued) • One of the challenges of a wireless LAN in an enterprise setting – Integrates management of wired and wireless networks • Wireless switch – Often a rack-mounted unit – Performs user authentication and encryption • Thin access point – Simplified radios with a media converter for the wired network CWSP Guide to Wireless Security 21
Wireless Switch (continued) CWSP Guide to Wireless Security 22
Wireless Switch (continued) • Advantages – Simplified wireless network management – Eliminates handoff procedures • Disadvantages – All thin APs and wireless switches are proprietary – Thin APs do not provide true convergence of the wired and wireless networks • IEEE 802. 1 v protocol – Assists the management of WLAN devices CWSP Guide to Wireless Security 23
Wireless Switch (continued) • IEEE 802. 1 v protocol features – Load balancing – Automatic configuration – Preserves battery life CWSP Guide to Wireless Security 24
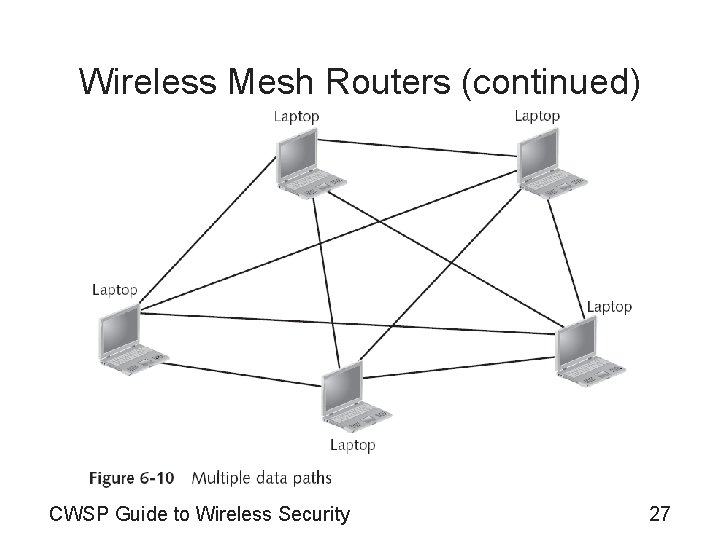
Wireless Mesh Routers • Limitations of connecting APs to a router via the wired network – Placement of APs is limited – APs have a limited range • Mesh networks – Solve these limitations – Provide multiple paths through which data can travel – Best example: the Internet • Wireless mesh network – Allows for multiple paths for wireless transmissions CWSP Guide to Wireless Security 25
Wireless Mesh Routers (continued) CWSP Guide to Wireless Security 26
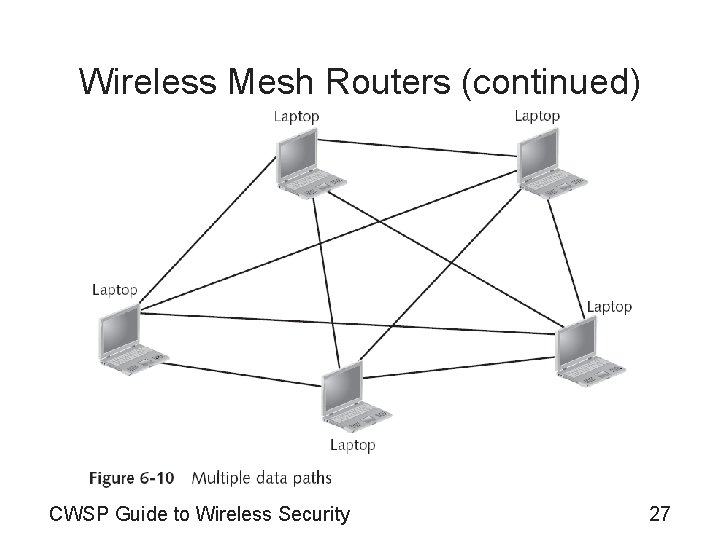
Wireless Mesh Routers (continued) CWSP Guide to Wireless Security 27
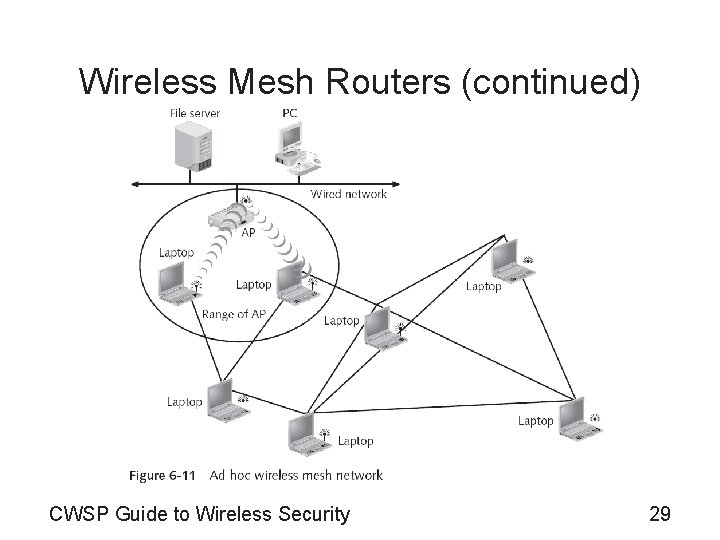
Wireless Mesh Routers (continued) • Wireless mesh network types – Ad hoc wireless mesh network • Allows greater distances away from the access point • Each client device can act as a relay station for signals • Advantages – Decentralized network – Can decrease costs – Can also be reliable CWSP Guide to Wireless Security 28
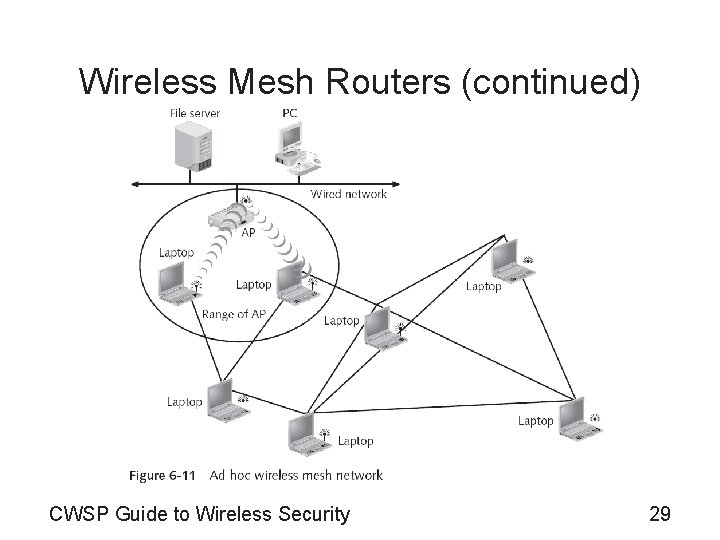
Wireless Mesh Routers (continued) CWSP Guide to Wireless Security 29
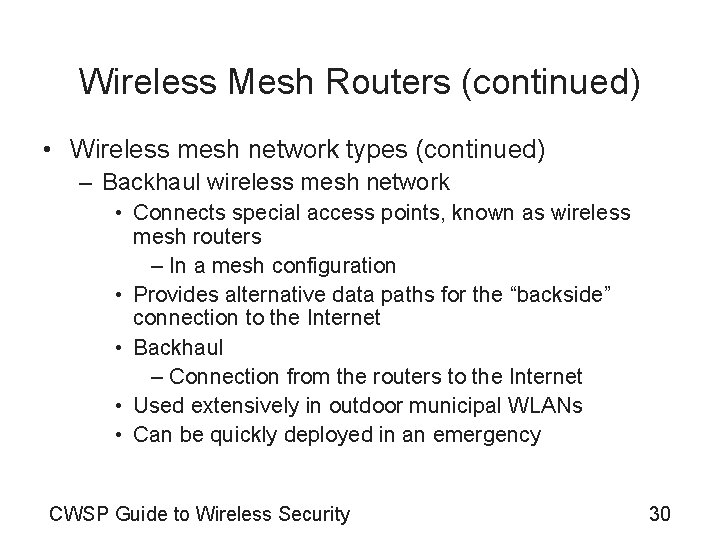
Wireless Mesh Routers (continued) • Wireless mesh network types (continued) – Backhaul wireless mesh network • Connects special access points, known as wireless mesh routers – In a mesh configuration • Provides alternative data paths for the “backside” connection to the Internet • Backhaul – Connection from the routers to the Internet • Used extensively in outdoor municipal WLANs • Can be quickly deployed in an emergency CWSP Guide to Wireless Security 30
Wireless Mesh Routers (continued) CWSP Guide to Wireless Security 31
Wireless Mesh Routers (continued) • No standards exist for wireless mesh networks – IEEE 802. 11 s task group is working on standards • Over 70 different wireless mesh routing protocols – Differ in the following features: • Algorithm • Management data versus transmit data • Number of radios CWSP Guide to Wireless Security 32
Hardware Security Features • Features include: – Controlling access to hardware – Protocol filtering CWSP Guide to Wireless Security 33
Controlling Access to Hardware • Access control – Restricts the user to accessing only the resources essential for the user to do his or her job – Limits access to resources based on the users’ identities and their membership in various groups • Mandatory access control (MAC) – Most restrictive model – User is not allowed to give access to another user to use or access anything on the network – All controls are fixed in place and there is no flexibility – Typically used in military environments CWSP Guide to Wireless Security 34
Controlling Access to Hardware (continued) • Role based access control (RBAC) – Administrator assigns permissions to a position (role) • Assign users and other objects to that role • Discretionary access control (DAC) – Least restrictive model – User can adjust the permissions for other users over network devices – Poses risks in that incorrect permissions may be granted or given CWSP Guide to Wireless Security 35
Controlling Access to Hardware (continued) CWSP Guide to Wireless Security 36
Protocol Filtering • Filtering restricts the traffic on a network based on specific criteria • Types of filtering – Address filtering – Data filtering – Protocol filtering • Some access points can be configured to filter unwanted protocols – From either entering or leaving the wireless network • Can only be used in a few specific situations CWSP Guide to Wireless Security 37
Protocol Filtering (continued) CWSP Guide to Wireless Security 38
Other Hardware Features • Features include: – Quality of service – Fast handoff – Power features CWSP Guide to Wireless Security 39
Quality of Service (IEEE 802. 11 e) • IEEE 802. 11 standard was intended to be “fair” – Not appropriate for real-time traffic • Quality of Service (Qo. S) – Capability to prioritize different types of frames • IEEE 802. 11 e task group has two new modes of operation for the 802. 11 MAC layer – Enhanced Distributed Channel Access (EDCA) – Hybrid Coordination Function Controlled Channel Access (HCCA) CWSP Guide to Wireless Security 40
Quality of Service (IEEE 802. 11 e) (continued) • Enhanced Distributed Channel Access (EDCA) – Contention-based – Supports four different “streams” (types) of traffic • • Voice Video Best effort Background – Provides relative Qo. S but cannot guarantee its service CWSP Guide to Wireless Security 41
Quality of Service (IEEE 802. 11 e) (continued) • Hybrid Coordination Function Controlled Channel Access (HCCA) – Based upon polling – Serves as a centralized scheduling mechanism • Wi-Fi Multimedia (WMM) – Wi-Fi Alliance’s own Qo. S specification – Modeled after a wired network Qo. S prioritization scheme – Subset of IEEE 802. 11 e – Defines new Arbitrary Inter-frame Space Number (AIFSN) and contention window values CWSP Guide to Wireless Security 42
Quality of Service (IEEE 802. 11 e) (continued) CWSP Guide to Wireless Security 43
Handoffs • Inter-Access Point Protocol (IAPP) (IEEE 802. 11 F) – 802. 11 standard did not specify how communications were to take place between access points – 802. 11 F specified information that access points need to exchange to support WLAN roaming • Fast Handoff (IEEE 802. 11 r) – Vo. WLAN mobile phones need fast handoff – Allows a wireless client to determine the Qo. S (and security) being used at a different AP • Before making the transition CWSP Guide to Wireless Security 44
Power Features • Dynamic Frequency and Power Control (IEEE 802. 11 h) – 802. 11 h is designed to enable WLAN devices to share the 5 GHz spectrum – Mechanisms • Dynamic frequency selection (DFS) – Switches the WLAN to another channel if necessary • Transmit power control (TPC) – Designed to reduce interference – Reduces radio transmit power used by devices CWSP Guide to Wireless Security 45
Power Features (continued) • Power over Ethernet (IEEE 802. 3 af) – APs are typically mounted high off the ground • To reduce interference from surrounding objects – Electrical power outlets are generally not found in these locations – Power over Ethernet (Po. E) • Delivers direct current (DC) to the AP through the unused wires in a standard UTP Ethernet cable – End-span • Ethernet switch that has embedded Po. E technology CWSP Guide to Wireless Security 46
Power Features (continued) • Power over Ethernet (IEEE 802. 3 af) (continued) – Failover support • Has duplicate equipment alongside the main equipment – Hot standby CWSP Guide to Wireless Security 47
Summary • Wireless hardware – – – Access points Remote wireless bridges Wireless routers Wireless gateways Wireless switches Wireless mesh routers • Access control limits access to resources – Based on the users’ identities and membership CWSP Guide to Wireless Security 48
Summary (continued) • Some access points can be configured to filter unwanted protocols • The capability to prioritize different types of frames is known as Quality of Service • Inter-Access Point Protocol (used in IEEE 802. 11 F) sets standards for handoffs between access points – Fast handoff is based on the IEEE 802. 11 r standard • Power management types – IEEE 802. 11 h standard – Power over Ethernet (IEEE 802. 3 af) CWSP Guide to Wireless Security 49