CW BRAINPORT ONLINE SESSION HACKER V S VICTIM

CW BRAINPORT – ONLINE SESSION HACKER V. S. VICTIM

Introduction
Topics for today • Looking at tools used by an attacker from the perspective of the attacker and the perspective of the victim. • Focus on RAT (remote access tooling) and Ransomware.
Online ways of working
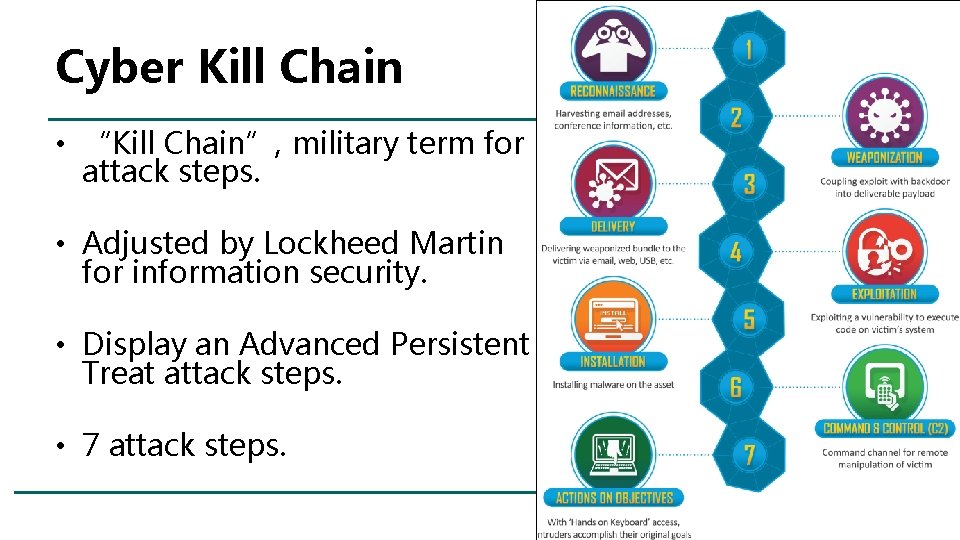
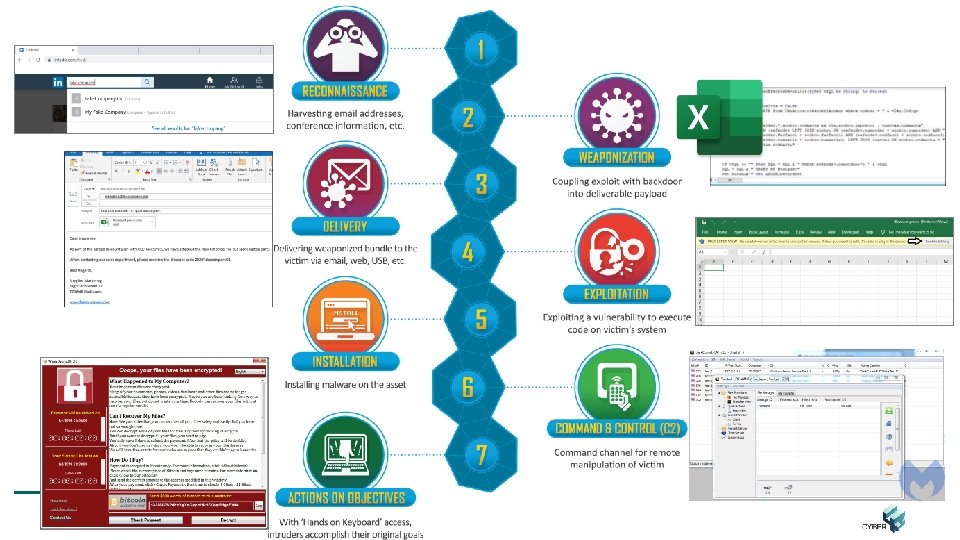
Cyber Kill Chain • “Kill Chain”, military term for attack steps. • Adjusted by Lockheed Martin for information security. • Display an Advanced Persistent Treat attack steps. • 7 attack steps.
RAT (Remote Access Tooling) • Case: I want to install software that allows me to control your system. – I need your “permission” to install. – I don’t want you to see that it is installed. – I don’t want you to notice it remains after you reboot.
Controls to detect RAT • • • Awareness / Phishing Logging, especially FW logs AV / AM IDS / IPS E-mail security gateway
Malware Types • Ransomware is een vorm van malware (malicious software). • Kunnen jullie nog andere types noemen?
Malware Types • • • Ransomware Fileless malware Spyware Adware Trojans • • • Worms Rootkits Keyloggers Bots Mobile Malware Source: https: //www. crowdstrike. com/epp-101/types-of-malware/
Ransomware • Starts with an e-mail (or other entry point) • Good reading material – Paper from University of Maastricht – Sophoslabs Ransomware behaviour report – Nomoreransom. org
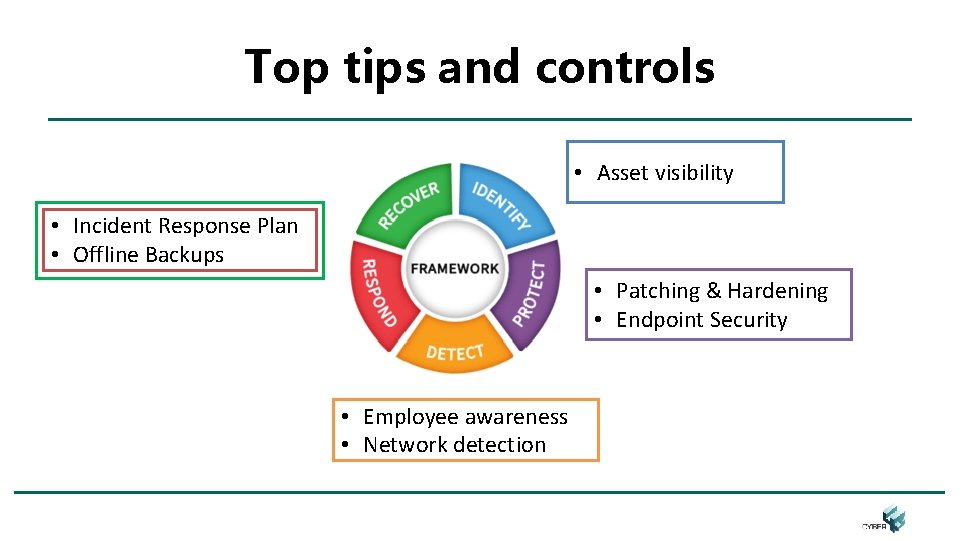
Top tips and controls • Asset visibility • Incident Response Plan • Offline Backups • Patching & Hardening • Endpoint Security • Employee awareness • Network detection
Thank you! Feel free to ask questions Feel free to propose other topics
- Slides: 13