CSL Workshop 6 Basics of Cryptography by Max

CSL Workshop 6 Basics of Cryptography by Max Farrell
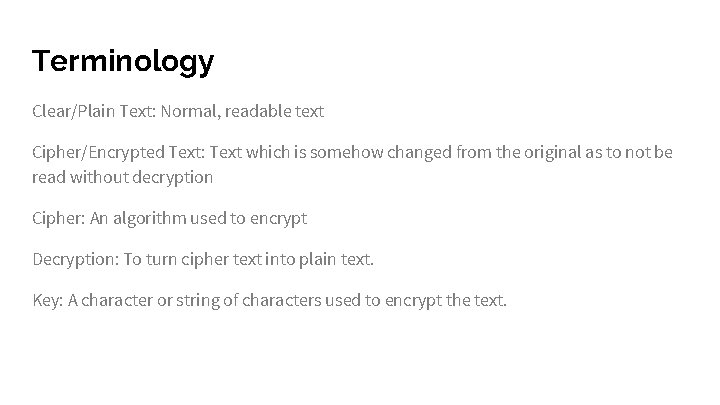
Terminology Clear/Plain Text: Normal, readable text Cipher/Encrypted Text: Text which is somehow changed from the original as to not be read without decryption Cipher: An algorithm used to encrypt Decryption: To turn cipher text into plain text. Key: A character or string of characters used to encrypt the text.
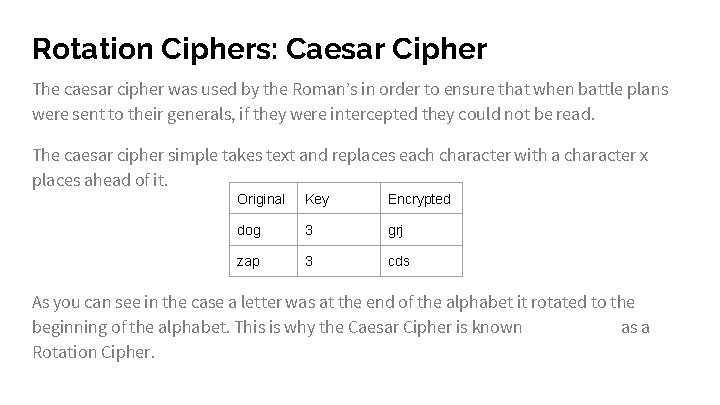
Rotation Ciphers: Caesar Cipher The caesar cipher was used by the Roman’s in order to ensure that when battle plans were sent to their generals, if they were intercepted they could not be read. The caesar cipher simple takes text and replaces each character with a character x places ahead of it. Original Key Encrypted dog 3 grj zap 3 cds As you can see in the case a letter was at the end of the alphabet it rotated to the beginning of the alphabet. This is why the Caesar Cipher is known as a Rotation Cipher.
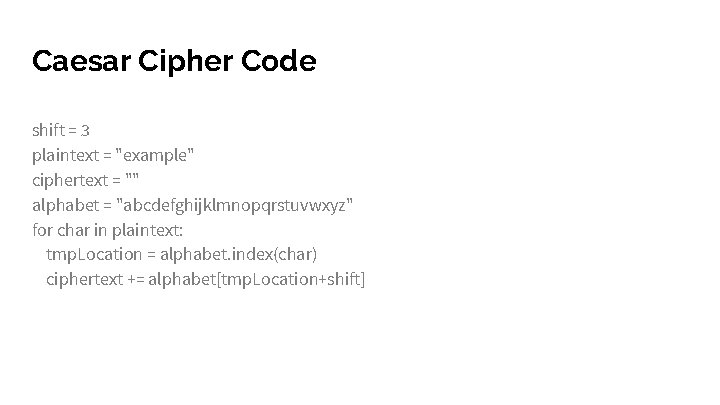
Caesar Cipher Code shift = 3 plaintext = "example" ciphertext = "" alphabet = "abcdefghijklmnopqrstuvwxyz" for char in plaintext: tmp. Location = alphabet. index(char) ciphertext += alphabet[tmp. Location+shift]
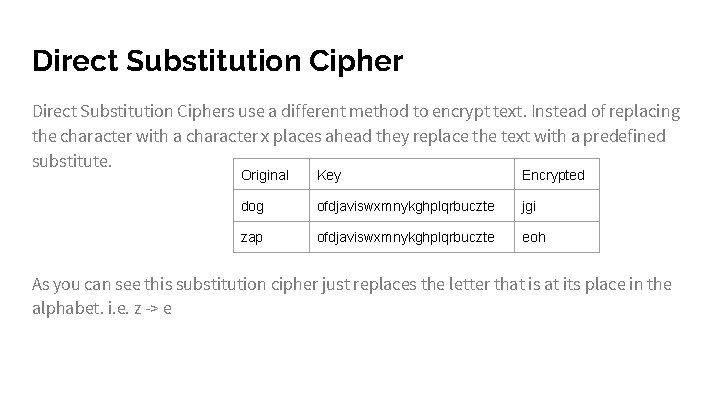
Direct Substitution Ciphers use a different method to encrypt text. Instead of replacing the character with a character x places ahead they replace the text with a predefined substitute. Original Key Encrypted dog ofdjaviswxmnykghplqrbuczte jgi zap ofdjaviswxmnykghplqrbuczte eoh As you can see this substitution cipher just replaces the letter that is at its place in the alphabet. i. e. z -> e

Direct Substitution Code plaintext = "example" ciphertext = "" alphabet = "abcdefghijklmnopqrstuvwxyz" key = "ofdjaviswxmnykghplqrbuczte" for char in plaintext: tmp. Location = alphabet. index(char) ciphertext += key[tmp. Location]
Block Cipher Block ciphers are algorithms which encrypt blocks of data rather than bits. So in the instance of encrypting a text message “Hello”, instead of encrypting H, then e, and so on, first “Hel” is encrypted and then “lo”. Because most block ciphers are built to handle large amounts of data they are generally inefficient for small amounts of data. Some examples of Block Ciphers are Rijndael, Serpent, and Twofish.
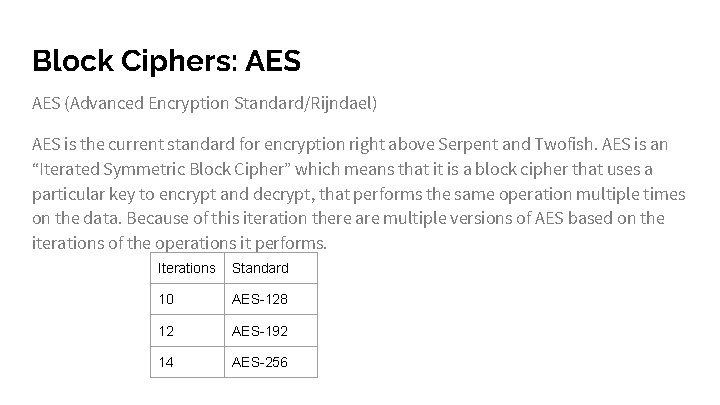
Block Ciphers: AES (Advanced Encryption Standard/Rijndael) AES is the current standard for encryption right above Serpent and Twofish. AES is an “Iterated Symmetric Block Cipher” which means that it is a block cipher that uses a particular key to encrypt and decrypt, that performs the same operation multiple times on the data. Because of this iteration there are multiple versions of AES based on the iterations of the operations it performs. Iterations Standard 10 AES-128 12 AES-192 14 AES-256
AES cont. The steps of the encryption iterations are: Sub. Bytes: Bytes are replaced by bytes from a lookup table Shift. Rows: Shifts the bytes in each row in a cycle Mix. Columns: The columns are mixed using an invertible linear function Add. Round. Key: Get a new round key, a subkey of the main key
Salting While using many modern ciphers salting must be employed. Salting is the practice of adding padding to data in order to make it the fixed size an algorithm requires. AES for instance requires the data be as large as the output i. e. when using AES-256, the data must be 256 bytes.
AES Code Download the AES code from here
Exercise Back to ECorp! Crack the Wi-Fi. Find where ECorp’s forum is hiding and find what they don’t want you to see! (Hint: It’s not as hard as you think)
Best Practices Use the industry standard (AES) Don’t homebrew your crypto (Really. Don’t) Make sure to salt your data Don’t go overboard, encrypting and decrypting can be computationally expensive. Remember that the U. S. Government uses AES-128 for secret documents.
- Slides: 13