CSE 57349 February 15 th 2006 IPSec Basics
CSE 5/7349 – February 15 th 2006 IPSec
Basics • Stack Level • V 4 vs V 6 • Provides – Authentication – Confidentiality
Architecture & Concepts • • • Placement Mode Security association (SA) ESP AH
IPSec Placement
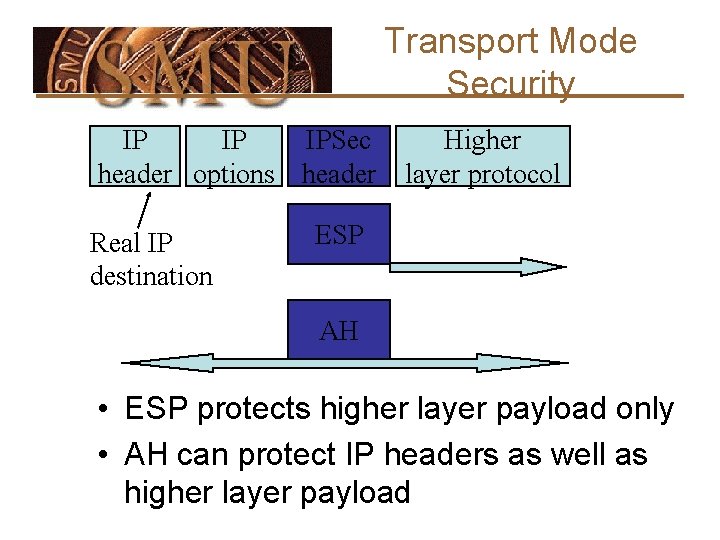
Transport Mode Security IP IP IPSec header options header Real IP destination Higher layer protocol ESP AH • ESP protects higher layer payload only • AH can protect IP headers as well as higher layer payload
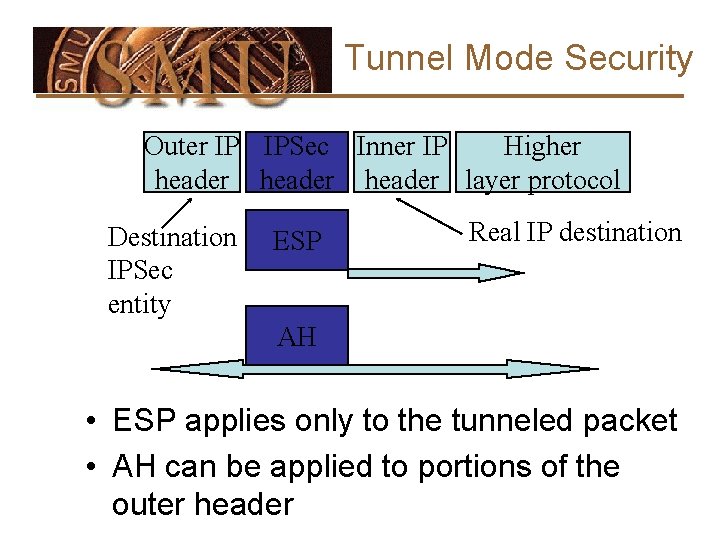
Tunnel Mode Security Outer IP IPSec Inner IP Higher header layer protocol Destination IPSec entity ESP Real IP destination AH • ESP applies only to the tunneled packet • AH can be applied to portions of the outer header
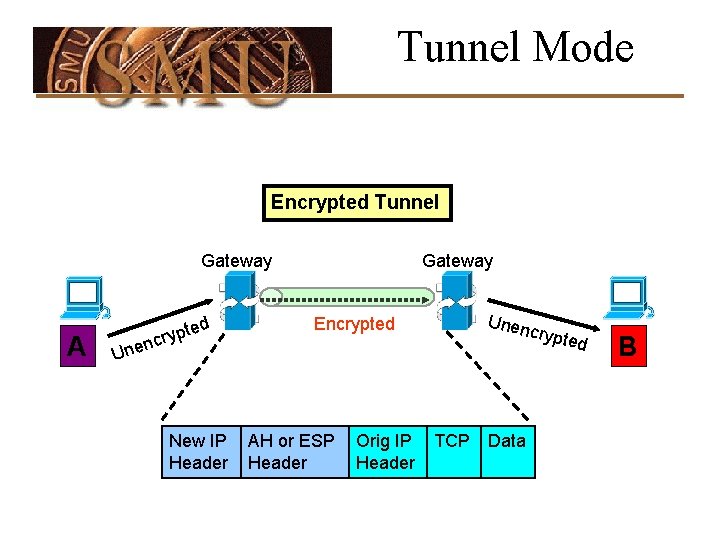
Tunnel Mode Encrypted Tunnel Gateway A ed t p y cr Gateway Unen Encrypted crypt U nen New IP Header AH or ESP Header Orig IP Header TCP Data ed B
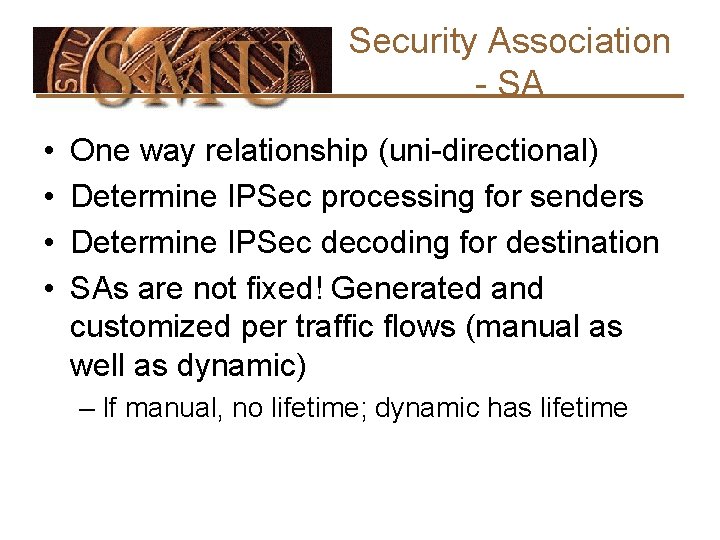
Security Association - SA • • One way relationship (uni-directional) Determine IPSec processing for senders Determine IPSec decoding for destination SAs are not fixed! Generated and customized per traffic flows (manual as well as dynamic) – If manual, no lifetime; dynamic has lifetime
Security Parameters Index - SPI • Can be up to 32 bits large • The SPI allows the destination to select the correct SA under which the received packet will be processed (according to the agreement with the sender) – The SPI is sent with the packet by the sender • SPI + Dest IP address + IPSec Protocol (AH or ESP) uniquely identifies a SA
SA Bundle • More than 1 SA can apply to a packet • Example: ESP does not authenticate new IP header. How to authenticate? – Use SA to apply ESP w/out authentication to original packet – Use 2 nd SA to apply AH
Authenticated Header (AH)
AH Security • Connectionless integrity – Flow/error control left to transport layer – Data integrity • Authentication – Can “trust” IP address source – Use MAC to authenticate • Anti-replay feature • Integrity check value
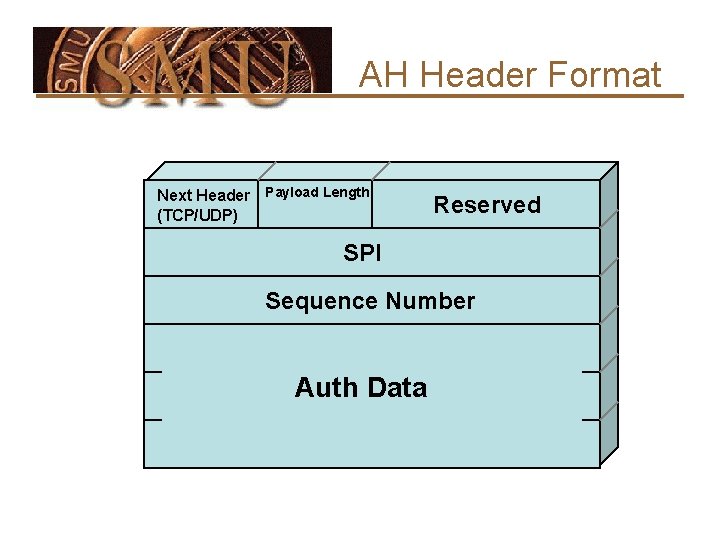
AH Header Format Next Header Payload Length (TCP/UDP) Reserved SPI Sequence Number Auth Data
Anti-Replay • Message authentication code (MAC) calculated over – IP header field that do not change or are predictable – IPSec protocol header minus where the ICV value goes – Upper-level data • Code may be truncated to first 96 bits
Integrity Check Value - ICV • Message authentication code (MAC) calculated over – IP header field that do not change or are predictable – IPSec protocol header minus where the ICV value goes – Upper-level data • Code may be truncated to first 96 bits
AH Modes • Tunnel • Transport • Nested headers – Multiple SAs applied to same message – Nested tunnels
Processing Outbound Messages • • • Insert Next Header and SPI field Compute the sequence no. field If transport mode … If tunnel mode … Compute authentication value
Outbound Processing (cont’d) • If transport mode • If tunnel mode • Compute authentication value
Outbound Processing (cont’d) Fragment the Message • IPSec processing may result in large message which will be fragmented – Transport mode – Tunnel mode
Input Processing • Identify the inbound SA • Replay protection check
Inbound Processing (cont’d) • Verify authentication data • Strip off the AH header and continue IPSec processing for any remaining IPSec headers
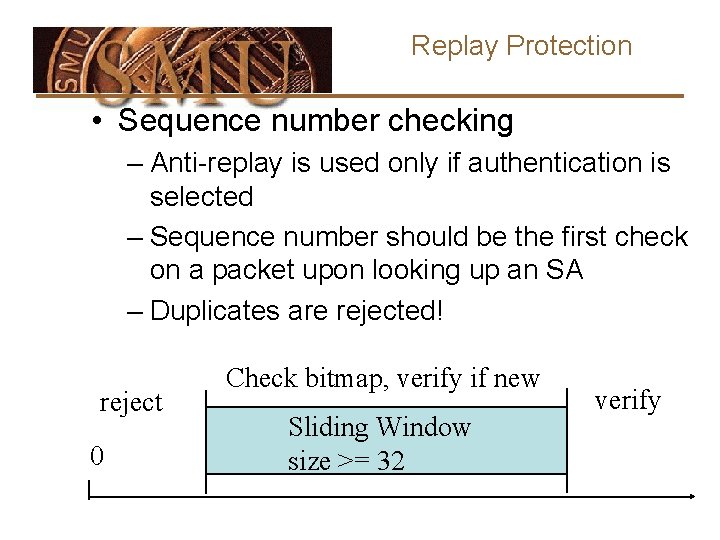
Replay Protection • Sequence number checking – Anti-replay is used only if authentication is selected – Sequence number should be the first check on a packet upon looking up an SA – Duplicates are rejected! reject 0 Check bitmap, verify if new Sliding Window size >= 32 verify
Anti-replay Feature • Sequence number counter - 32 bit for outgoing IPSec packets • Anti-replay window
Internet Key Exchange (IKE)
Key Management • AH and ESP require encryption and authentication keys • Process to negotiate and establish IPSec SA’s between two entities
Manual Key Management • Mandatory • Useful when IPSec developers are debugging • Keys exchanged offline (phone, email, etc. ) • Set up SPI and negotiate parameters • Not scalable
Oakley Key Exchange • Designed to – Leverage advantages of DH – Counter DH weaknesses
Oakley - Major Features
Cookies
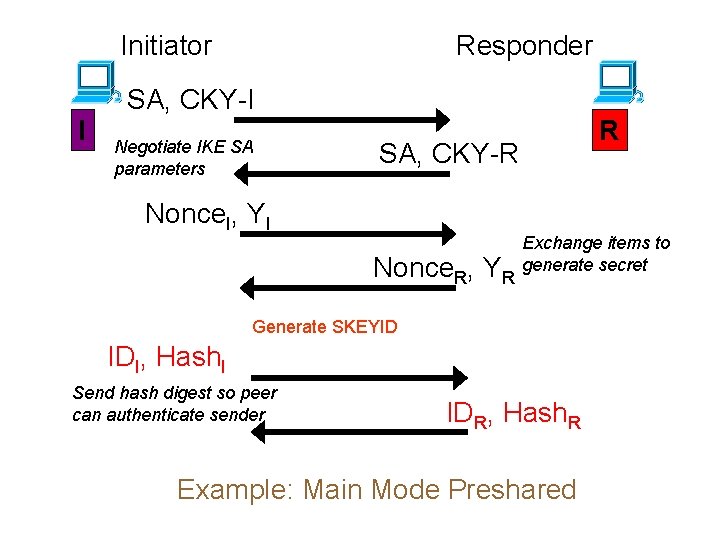
Initiator I Responder SA, CKY-I Negotiate IKE SA parameters R SA, CKY-R Nonce. I, YI Nonce. R, YR Exchange items to generate secret Generate SKEYID IDI, Hash. I Send hash digest so peer can authenticate sender IDR, Hash. R Example: Main Mode Preshared
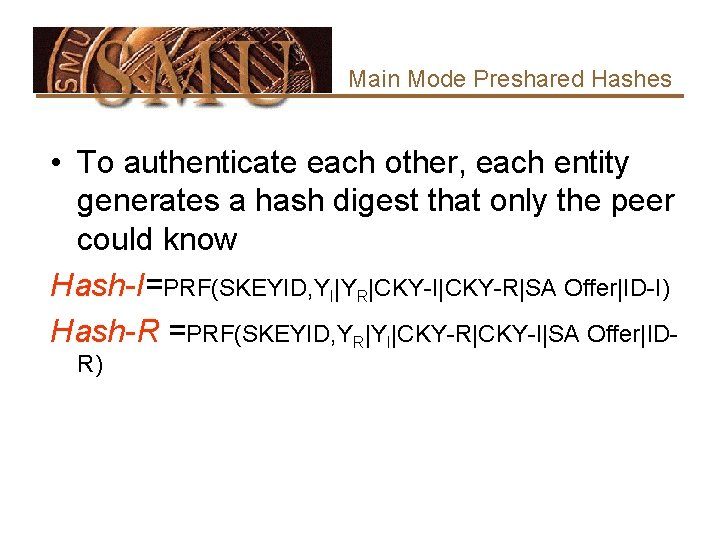
Main Mode Preshared Hashes • To authenticate each other, each entity generates a hash digest that only the peer could know Hash-I=PRF(SKEYID, YI|YR|CKY-I|CKY-R|SA Offer|ID-I) Hash-R =PRF(SKEYID, YR|YI|CKY-R|CKY-I|SA Offer|IDR)
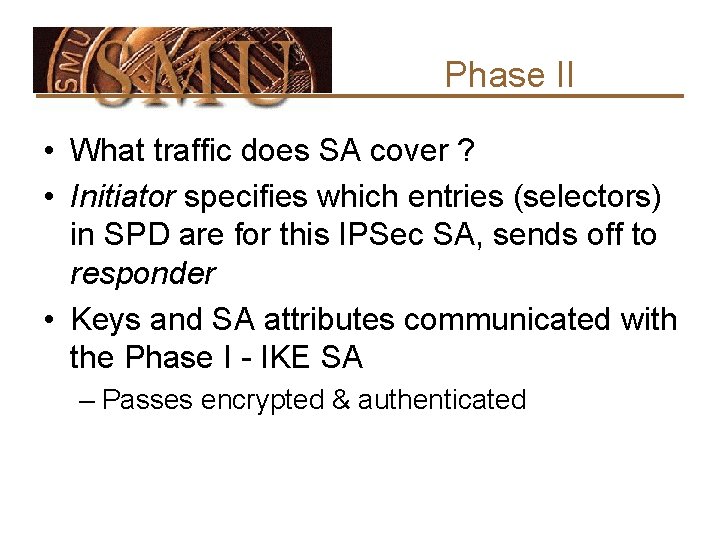
Phase II • What traffic does SA cover ? • Initiator specifies which entries (selectors) in SPD are for this IPSec SA, sends off to responder • Keys and SA attributes communicated with the Phase I - IKE SA – Passes encrypted & authenticated
![Example: Quick Mode Initiator I HASH 1, IPSec SA, Nonce. I, [New K] Negotiate Example: Quick Mode Initiator I HASH 1, IPSec SA, Nonce. I, [New K] Negotiate](http://slidetodoc.com/presentation_image_h2/de5eccdc121f97eff13651936d1dc278/image-33.jpg)
Example: Quick Mode Initiator I HASH 1, IPSec SA, Nonce. I, [New K] Negotiate IPSec SA Parameters, [PFS] HASH 3 Responder R HASH 2, SA, Nonce. R, [New K] ‘Liveness’ proof for Responder
- Slides: 33