CSE 466 Cryptology and NW Security Dr M
- Slides: 21
CSE 466 Cryptology and NW Security Dr M. Sakalli Marmara University
So much material cluttering information channels, I’ll keep it lean, so that you can digest the main concepts and the materials. M. Sakalli As quoted in the lecture slides by Lawrie Brown, and site: http: //williamstallings. com/Crypto 3 e. html, in chapter 1 of Introduction The art of war teaches us to rely not on the likelihood of the enemy's not coming, but on our own readiness to receive him; not on the chance of his not attacking, but rather on the fact that we have made our position unassailable. —The Art of War, Sun Tzu
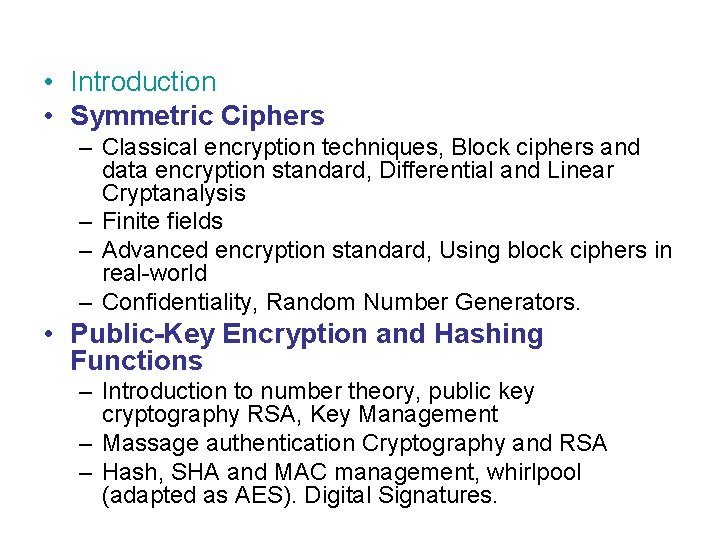
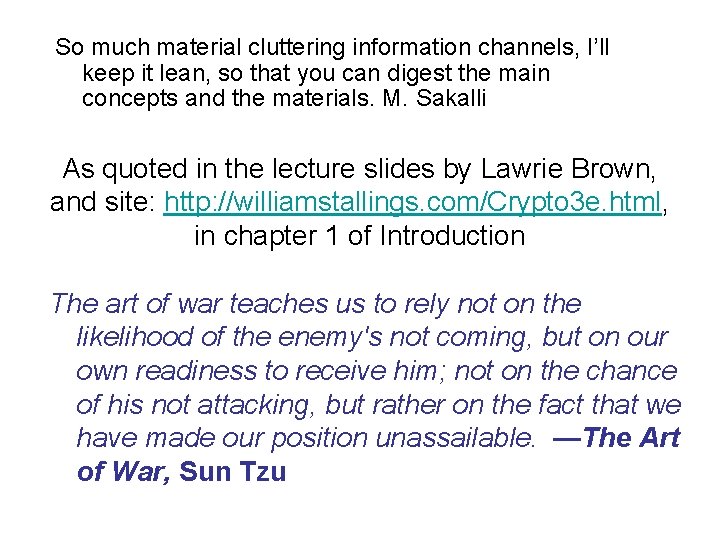
• Introduction • Symmetric Ciphers – Classical encryption techniques, Block ciphers and data encryption standard, Differential and Linear Cryptanalysis – Finite fields – Advanced encryption standard, Using block ciphers in real-world – Confidentiality, Random Number Generators. • Public-Key Encryption and Hashing Functions – Introduction to number theory, public key cryptography RSA, Key Management – Massage authentication Cryptography and RSA – Hash, SHA and MAC management, whirlpool (adapted as AES). Digital Signatures.
Part 3 -4 Applications • NW Security – Kerberos, X. 509, – Email, PGP: signatures, certifying mail, privacy (via encryption), S/MIME, – IP Security, Web security SSL, TSL • System Security – – – System security. Intrusion detection, Malicious software. DOS. Firewalls. IEEE 802. 11 Wireless LAN Security (WEP) 4
Grading plan • Midterm exam I: 30% (Friday, Oct. 24) • Final exam: 40% (Tue, Dec. 9, 1: 30 pm) • Assignments: 30% • The later you submit your homework, the lower you will be marked. 6
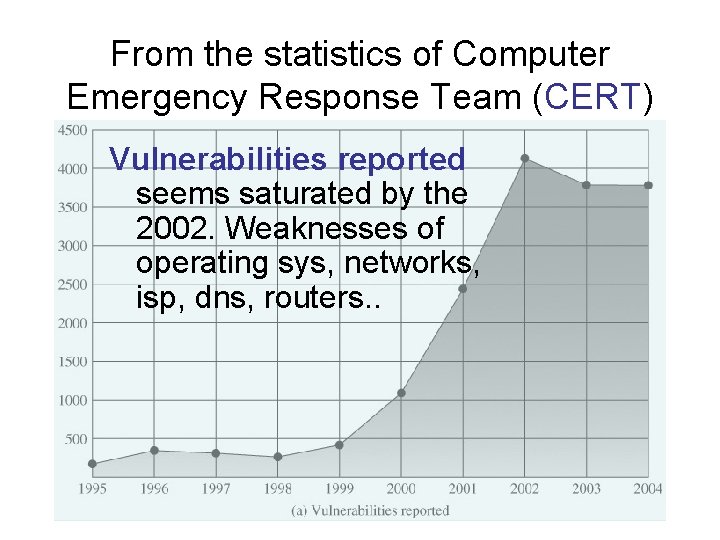
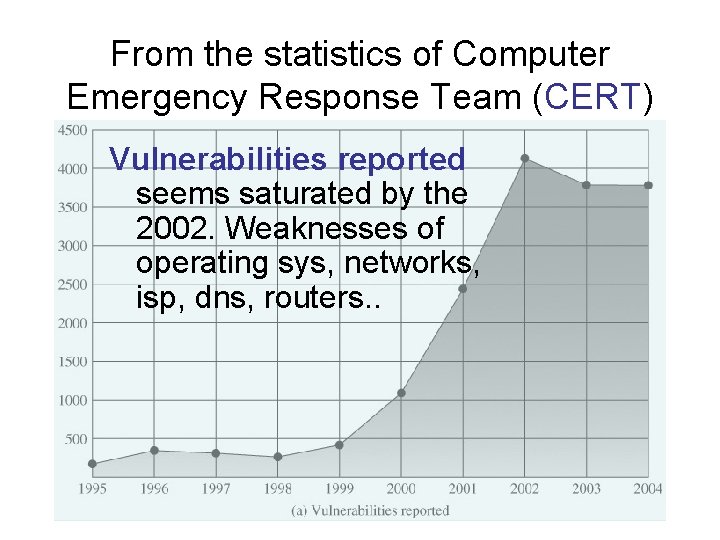
From the statistics of Computer Emergency Response Team (CERT) Vulnerabilities reported seems saturated by the 2002. Weaknesses of operating sys, networks, isp, dns, routers. .
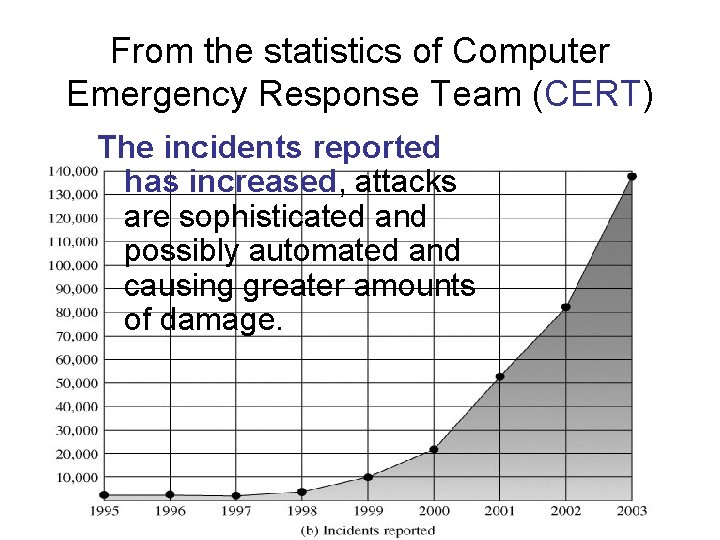
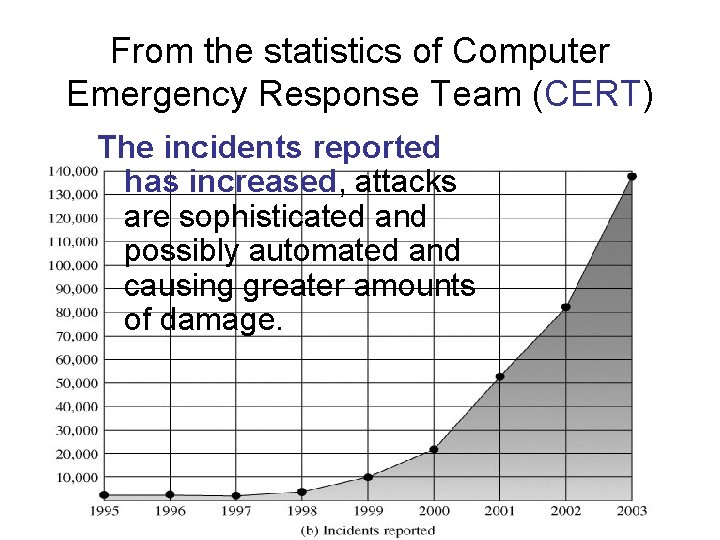
From the statistics of Computer Emergency Response Team (CERT) The incidents reported has increased, attacks are sophisticated and possibly automated and causing greater amounts of damage.
The OSI architecture • The systematic approach of OSI security architecture, compromises security in three stages: Attack mechanisms and defence mechanisms and the services implemented complement each other hand to hand. • RFC 2828: Threats are the possibilities of the breaching security rules, and an attack is an assault and/or a deliberate action to inflict damage on the other side.
Security Mechanisms (X. 800) • OSI specific security mechanisms: – encipherment, digital signatures, access controls, data integrity, authentication exchange, traffic padding, routing control, notarization • Non OSI pervasive security mechanisms: – trusted functionality, security labels, event detection, security audit trails, security recovery
Internet standards and RFCs • The Internet society – Internet Architecture Board (IAB) – Internet Engineering Task Force (IETF) – Internet Engineering Steering Group (IESG)
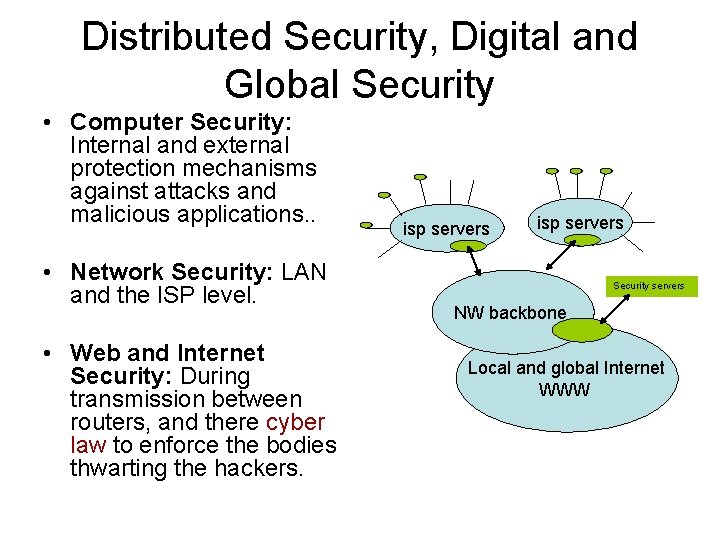
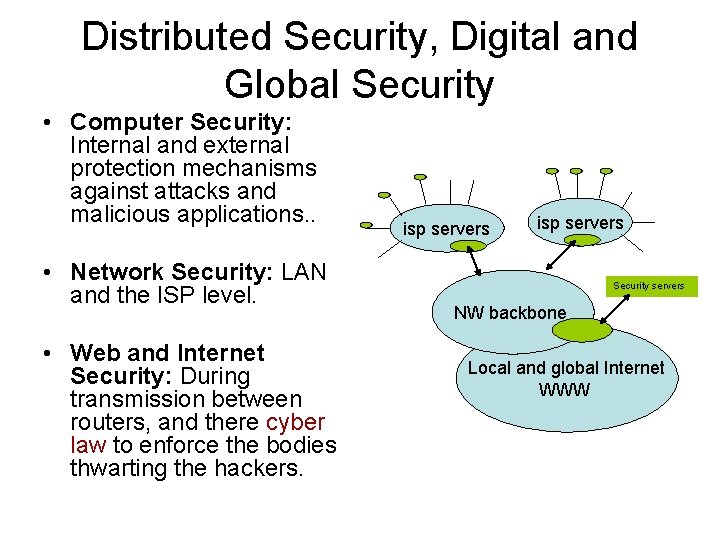
Distributed Security, Digital and Global Security • Computer Security: Internal and external protection mechanisms against attacks and malicious applications. . • Network Security: LAN and the ISP level. • Web and Internet Security: During transmission between routers, and there cyber law to enforce the bodies thwarting the hackers. isp servers Security servers NW backbone Local and global Internet WWW
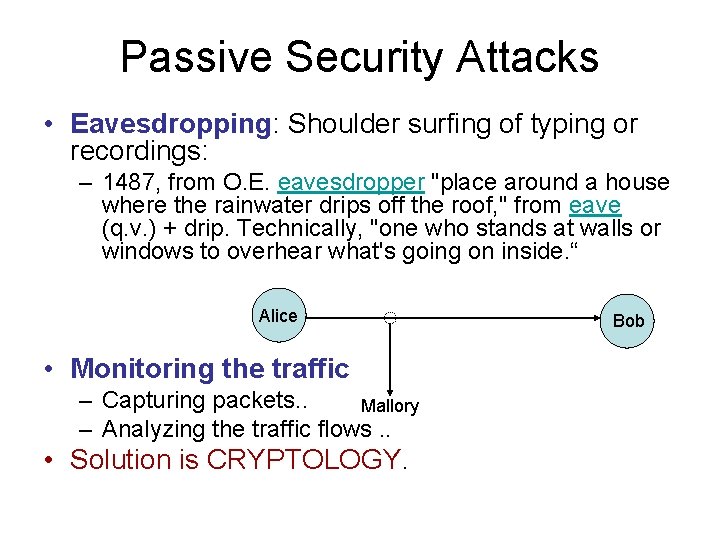
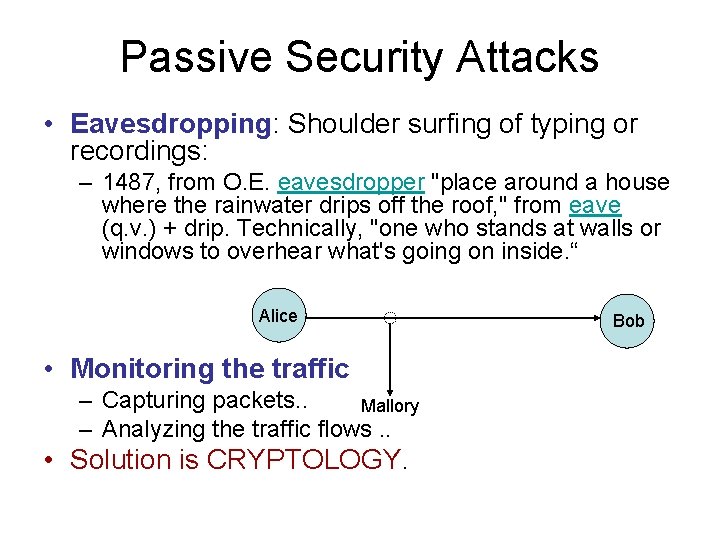
Passive Security Attacks • Eavesdropping: Shoulder surfing of typing or recordings: – 1487, from O. E. eavesdropper "place around a house where the rainwater drips off the roof, " from eave (q. v. ) + drip. Technically, "one who stands at walls or windows to overhear what's going on inside. “ Alice • Monitoring the traffic – Capturing packets. . Mallory – Analyzing the traffic flows. . • Solution is CRYPTOLOGY. Bob
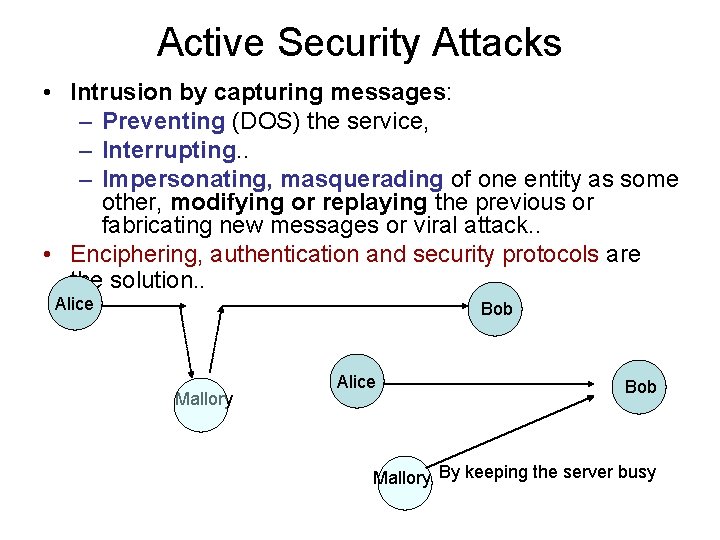
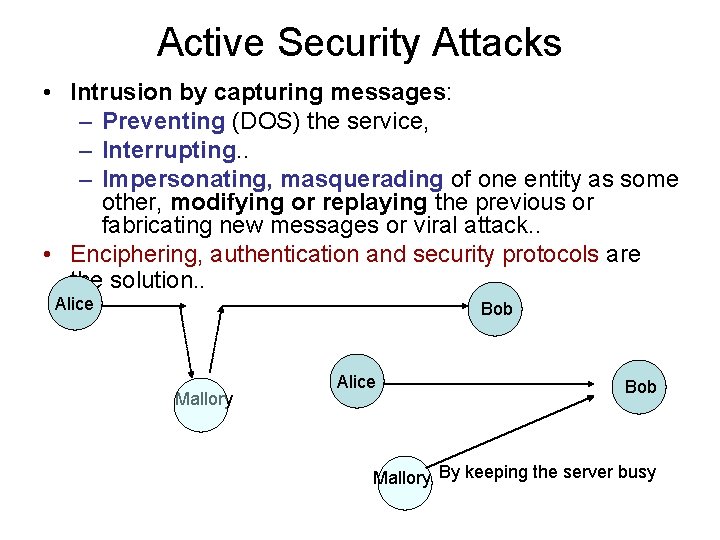
Active Security Attacks • Intrusion by capturing messages: – Preventing (DOS) the service, – Interrupting. . – Impersonating, masquerading of one entity as some other, modifying or replaying the previous or fabricating new messages or viral attack. . • Enciphering, authentication and security protocols are the solution. . Alice Bob Mallory By keeping the server busy
• The main reason for cryptology is to hide for surviving: protecting privacy, preventing intrusion. – Secrecy, masking the message traffic can be visible, in the case of data confidentiality evading passive attacks. – Authentication, 1 - Identity check of the peer entities, 2 - data origin auth, prevent interference and masquerading, not preclude passive attacks. Certificates – Integrity of the message: In connectionless service (assuring that message is not altered), MACs, CRC. . – Nonrepudiation (undeniable producer or receiver). • 1412, "repudiation, " from L. L. repulsionem, noun of action from repellere (see repel), . – Oblivious transfer = without leaving any trace of inf transferred, – Zero knowledge proofs = Prove possession of certain information without conveying an ID. . • https… - "s" is for SSL
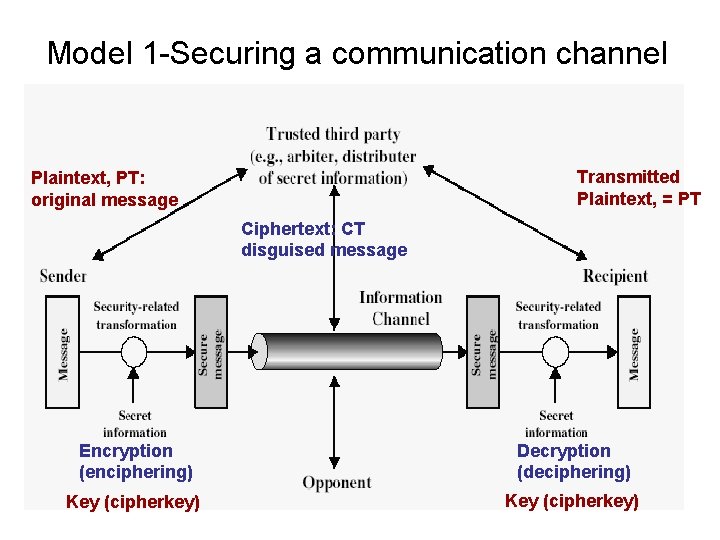
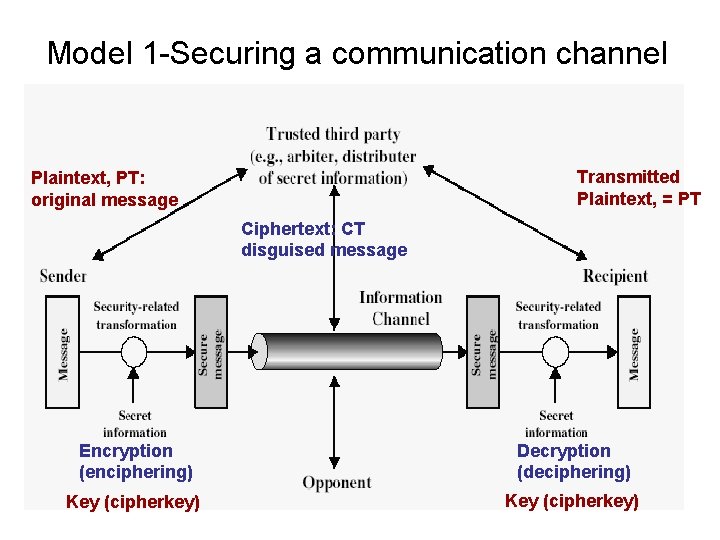
Model 1 -Securing a communication channel Transmitted Plaintext, = PT Plaintext, PT: original message Ciphertext: CT disguised message Encryption (enciphering) Key (cipherkey) Decryption (deciphering) Possible PT Key (cipherkey)
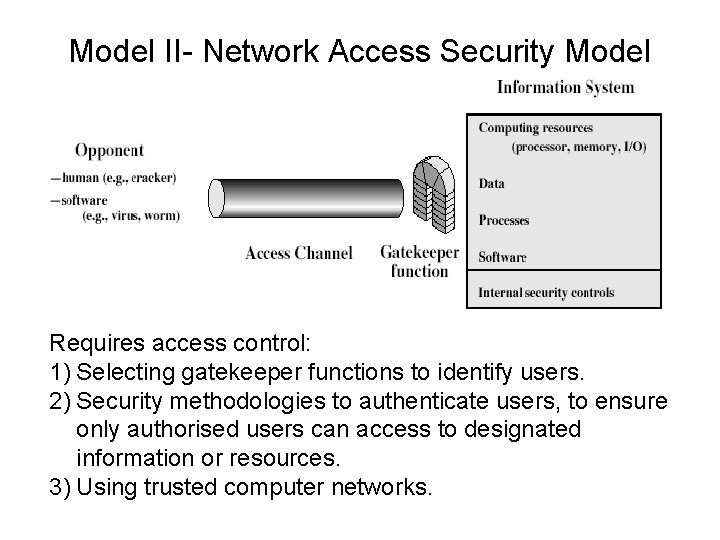
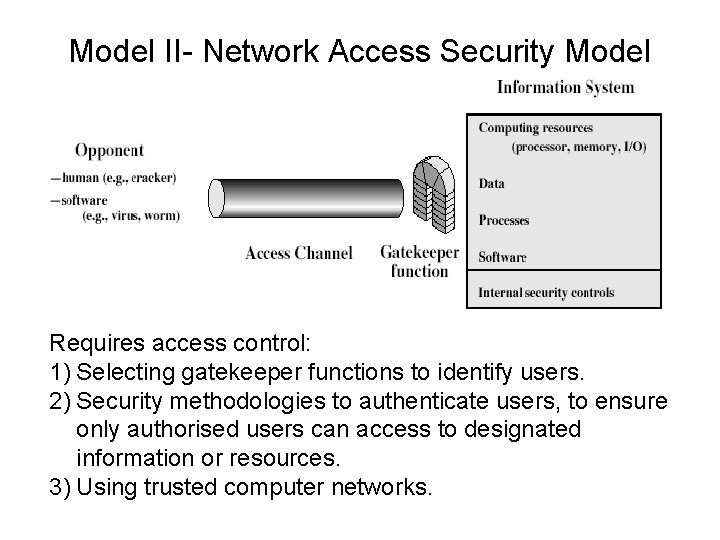
Model II- Network Access Security Model Requires access control: 1) Selecting gatekeeper functions to identify users. 2) Security methodologies to authenticate users, to ensure only authorised users can access to designated information or resources. 3) Using trusted computer networks.
• Cryptology is the mathematics of concealing messages by scrambling under some constraints applied open cipher that are. . – Applicable duration of the cipher. . – Space, physical environment. Communications, Storage area. . – Complexity, vs simplicity, human factor. . – The cost. .
• if both the encryption and decryption keys are the same, then the method employed is symmetric. . . Otherwise asymmetric. • "Crypto graphy" = both Greek 'krypte graphic' meaning hidden (or vault) + writing • Cryptanalysis (cryptanalyst, cryptoanalyst) is the art of cracking the codes. • An adversary, eavesdropper, hacker, imposter. . • Cryptology = Cryptography + cryptanalysis. . • Cryptograms are roughly divided into Ciphers and Codes. • Perfect security and entropic security. (Shannon), an adversary does not have any information at all about the secret which is equivalent to saying that the random variable constituting the secret and the random variable modeling the adversary’s knowledge must be independent. H(x)=H(X|Y) for adversary, H(X|YK)=0 for recipient.
Steganography and cryptography • Histiaeus detained in Sasu island eagerly wanted to send a message to his regent to revolt against to Persians. The only way he found was to shave the head of his messenger, and (tattoo) write the message on his scalp, and then waited for the hair to regrow. On reaching his destination the messenger, was instructed to shave his head, so that Aristogoras the mayor of Miletus could read the message. Herodotus. • an alternative to encryption • hides existence of message – using only a subset of letters/words in a longer message marked in some way – using invisible ink – hiding in LSB in graphic image or sound file • has drawbacks – high overhead to hide relatively few info bits
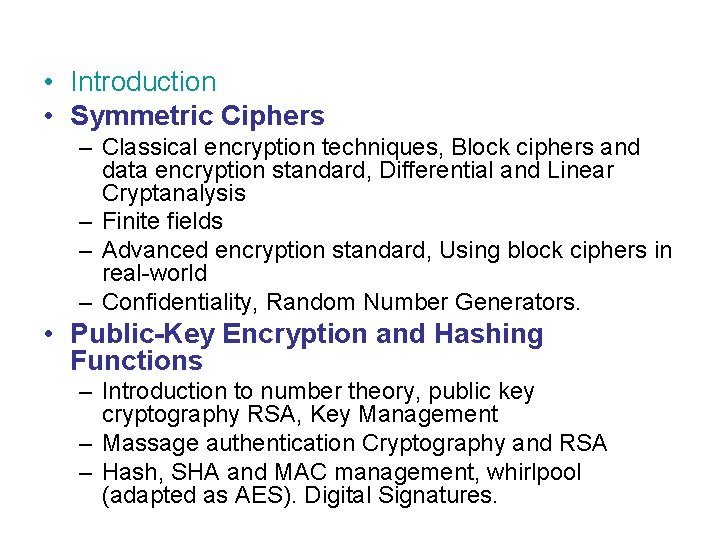
A very brief history • Substitution cipher is the oldest cipher • Secret key K is a table lookup: A --> C • Breaking: Some single letter for example substituted for E, will have the same frequency if the message is not too short, then it’ll be easy to figure out which letter is substituted for E, (or such), which is the occurring as frequent as. E, etc. Abu al-Kindi's "A Manuscript on Deciphering Cryptographic Messages“. . • Vigenère (1523 - 1570) • Rotor (1800 - 1950): WWII Enigma machine • 1974: DES developed by IBM, 1 st good cipher • 1977: Diffie Hellman, public key crypto • Symmetric ciphers: info theoretic approach (Shannon) • -- privacy against eavesdropping • -- make substitution cipher secure • -- one-time pad: very fast, key as long as message; why is this secure?