CSC 382582 Computer Security Web Security CSC 382582
CSC 382/582: Computer Security Web Security CSC 382/582: Computer Security 1
Topics 1. 2. 3. 4. 5. 6. 7. 8. HTTP Web Input Canonicalization Authentication SQL Injection Cross-Site Scripting Client-side Attacks Finding Web Vulnerabilities CSC 382/582: Computer Security 2
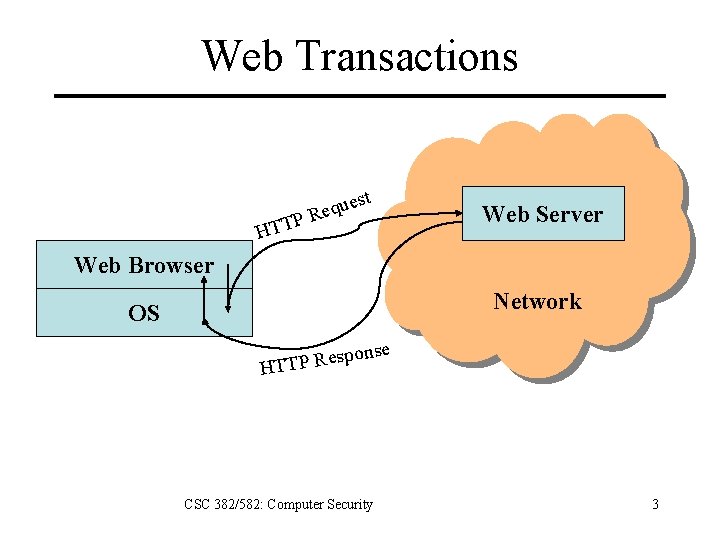
Web Transactions t es u q e PR Web Server HTT Web Browser Network OS e pons s e R P T HT CSC 382/582: Computer Security 3
HTTP: Hyper. Text Transfer Protocol • Simple request/respond protocol – Request methods: GET, POST, HEAD, etc. – Protocol versions: 1. 0, 1. 1 • Stateless – Each request independent of previous requests, i. e. request #2 doesn’t know you auth’d in #1. – Applications responsible for handling state. CSC 382/582: Computer Security 4
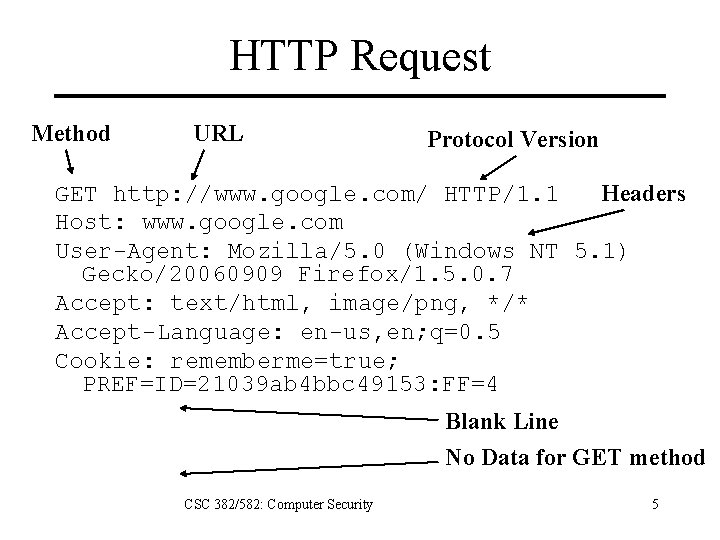
HTTP Request Method URL Protocol Version GET http: //www. google. com/ HTTP/1. 1 Headers Host: www. google. com User-Agent: Mozilla/5. 0 (Windows NT 5. 1) Gecko/20060909 Firefox/1. 5. 0. 7 Accept: text/html, image/png, */* Accept-Language: en-us, en; q=0. 5 Cookie: rememberme=true; PREF=ID=21039 ab 4 bbc 49153: FF=4 Blank Line No Data for GET method CSC 382/582: Computer Security 5
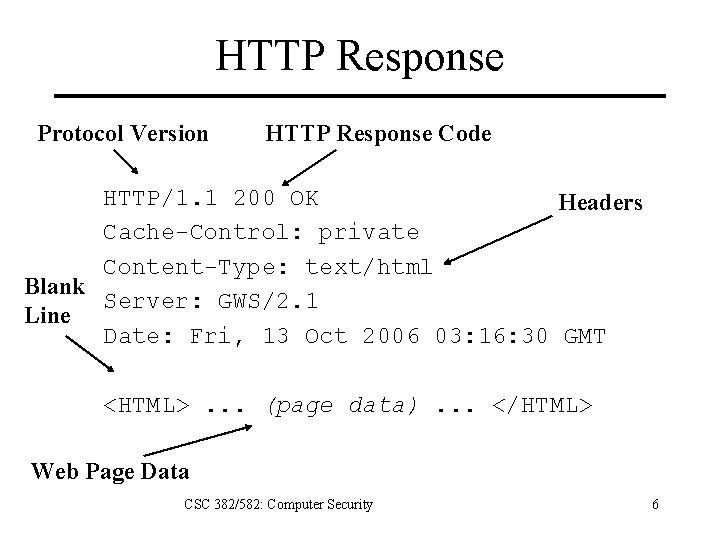
HTTP Response Protocol Version HTTP Response Code HTTP/1. 1 200 OK Headers Cache-Control: private Content-Type: text/html Blank Server: GWS/2. 1 Line Date: Fri, 13 Oct 2006 03: 16: 30 GMT <HTML>. . . (page data). . . </HTML> Web Page Data CSC 382/582: Computer Security 6
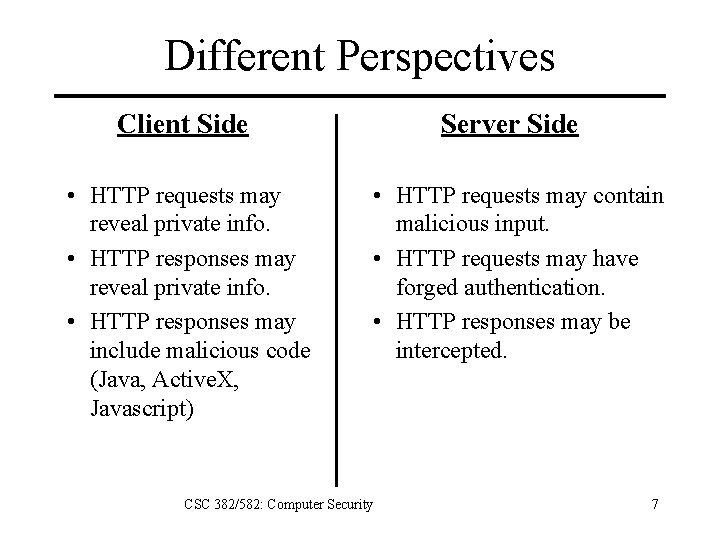
Different Perspectives Client Side • HTTP requests may reveal private info. • HTTP responses may include malicious code (Java, Active. X, Javascript) Server Side • HTTP requests may contain malicious input. • HTTP requests may have forged authentication. • HTTP responses may be intercepted. CSC 382/582: Computer Security 7
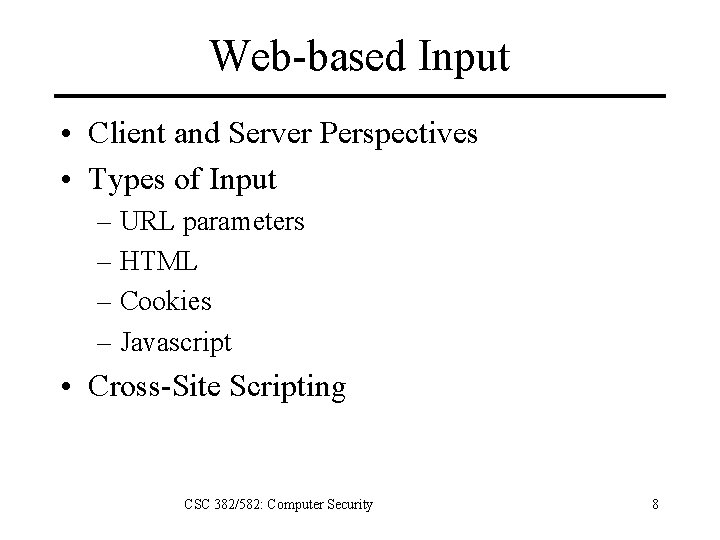
Web-based Input • Client and Server Perspectives • Types of Input – URL parameters – HTML – Cookies – Javascript • Cross-Site Scripting CSC 382/582: Computer Security 8
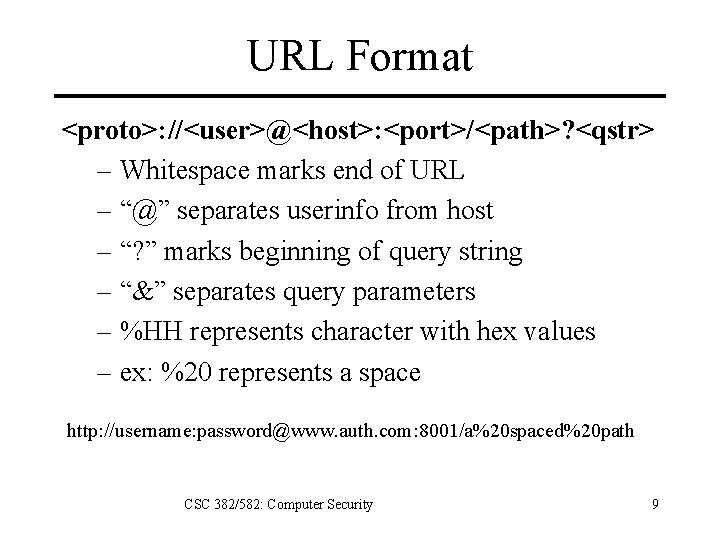
URL Format <proto>: //<user>@<host>: <port>/<path>? <qstr> – Whitespace marks end of URL – “@” separates userinfo from host – “? ” marks beginning of query string – “&” separates query parameters – %HH represents character with hex values – ex: %20 represents a space http: //username: password@www. auth. com: 8001/a%20 spaced%20 path CSC 382/582: Computer Security 9
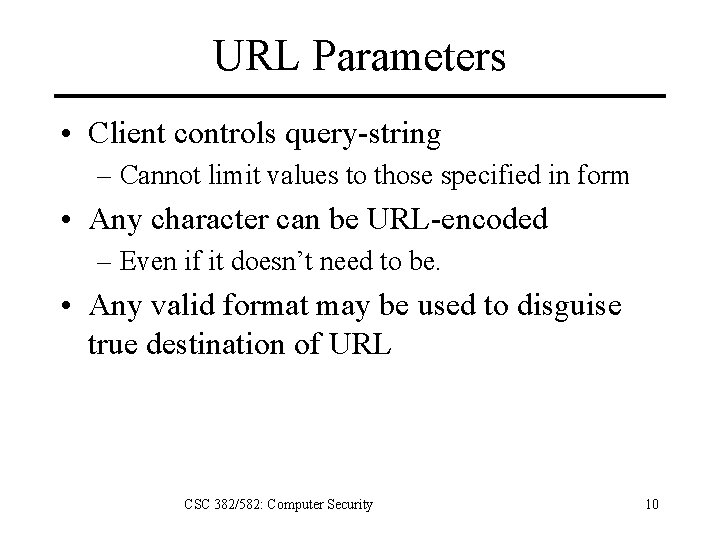
URL Parameters • Client controls query-string – Cannot limit values to those specified in form • Any character can be URL-encoded – Even if it doesn’t need to be. • Any valid format may be used to disguise true destination of URL CSC 382/582: Computer Security 10
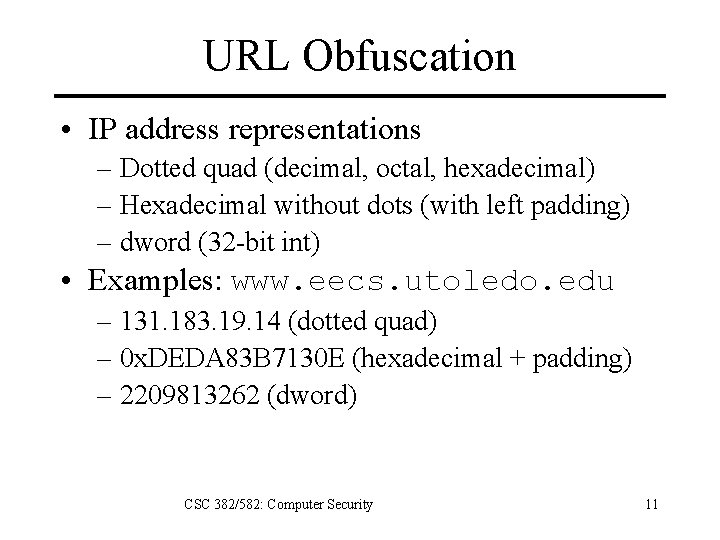
URL Obfuscation • IP address representations – Dotted quad (decimal, octal, hexadecimal) – Hexadecimal without dots (with left padding) – dword (32 -bit int) • Examples: www. eecs. utoledo. edu – 131. 183. 19. 14 (dotted quad) – 0 x. DEDA 83 B 7130 E (hexadecimal + padding) – 2209813262 (dword) CSC 382/582: Computer Security 11
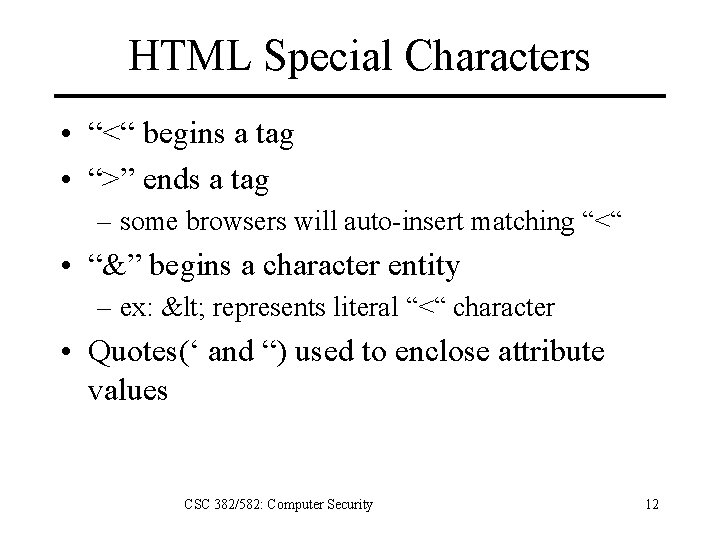
HTML Special Characters • “<“ begins a tag • “>” ends a tag – some browsers will auto-insert matching “<“ • “&” begins a character entity – ex: < represents literal “<“ character • Quotes(‘ and “) used to enclose attribute values CSC 382/582: Computer Security 12
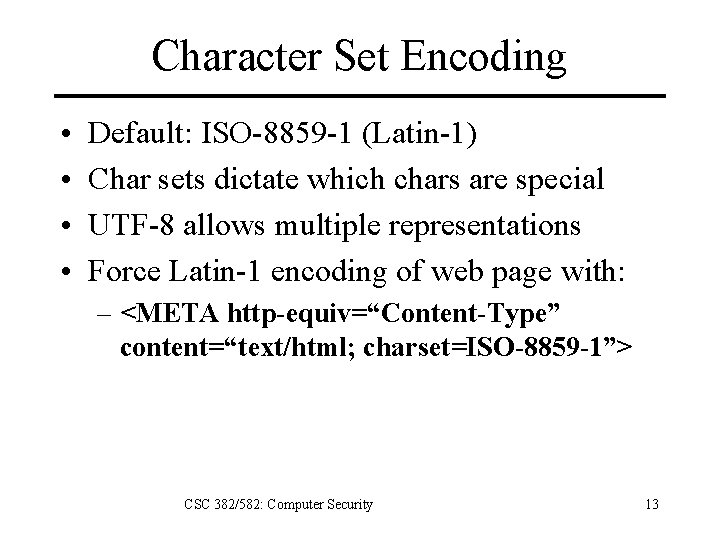
Character Set Encoding • • Default: ISO-8859 -1 (Latin-1) Char sets dictate which chars are special UTF-8 allows multiple representations Force Latin-1 encoding of web page with: – <META http-equiv=“Content-Type” content=“text/html; charset=ISO-8859 -1”> CSC 382/582: Computer Security 13
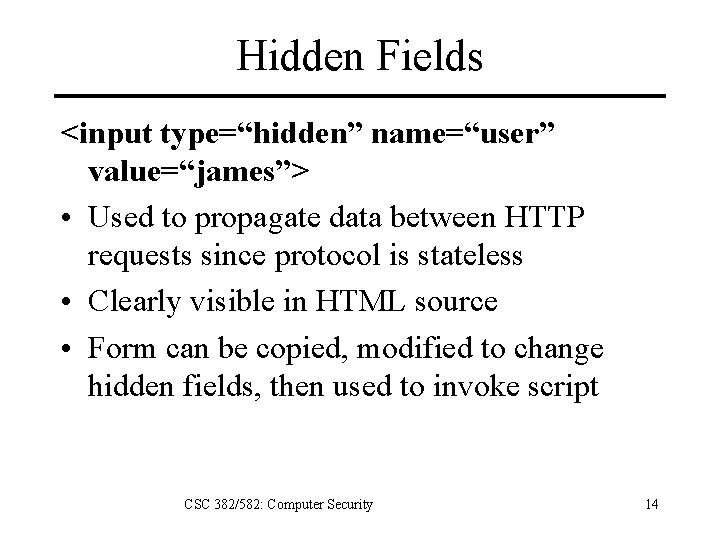
Hidden Fields <input type=“hidden” name=“user” value=“james”> • Used to propagate data between HTTP requests since protocol is stateless • Clearly visible in HTML source • Form can be copied, modified to change hidden fields, then used to invoke script CSC 382/582: Computer Security 14
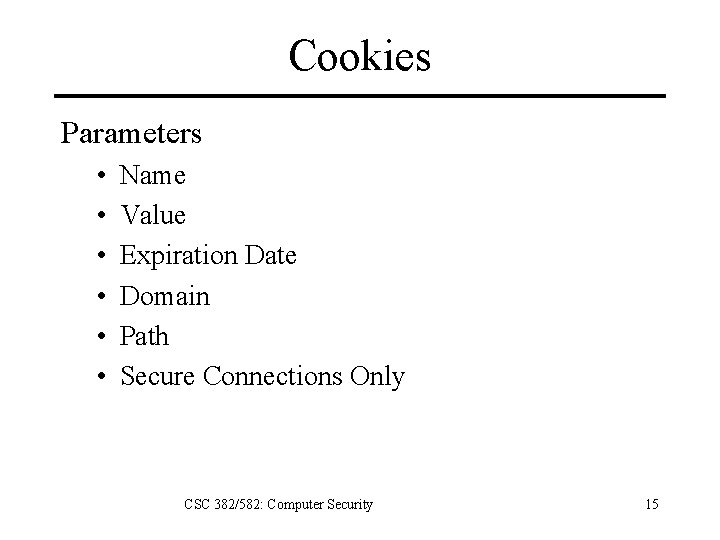
Cookies Parameters • • • Name Value Expiration Date Domain Path Secure Connections Only CSC 382/582: Computer Security 15
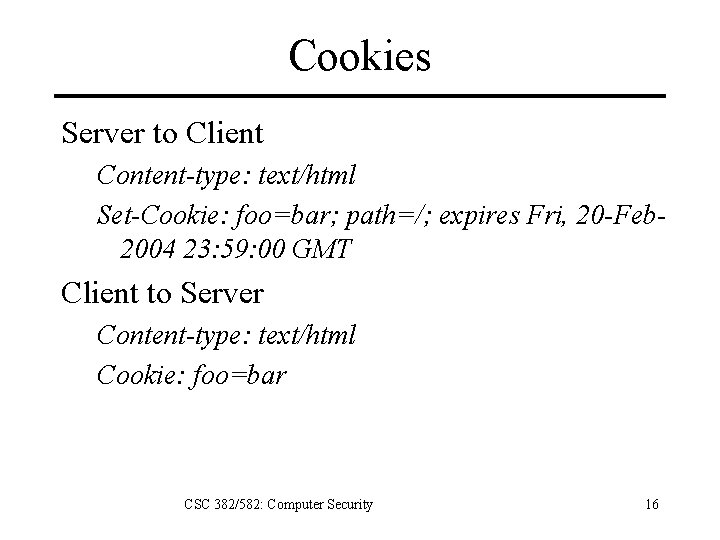
Cookies Server to Client Content-type: text/html Set-Cookie: foo=bar; path=/; expires Fri, 20 -Feb 2004 23: 59: 00 GMT Client to Server Content-type: text/html Cookie: foo=bar CSC 382/582: Computer Security 16
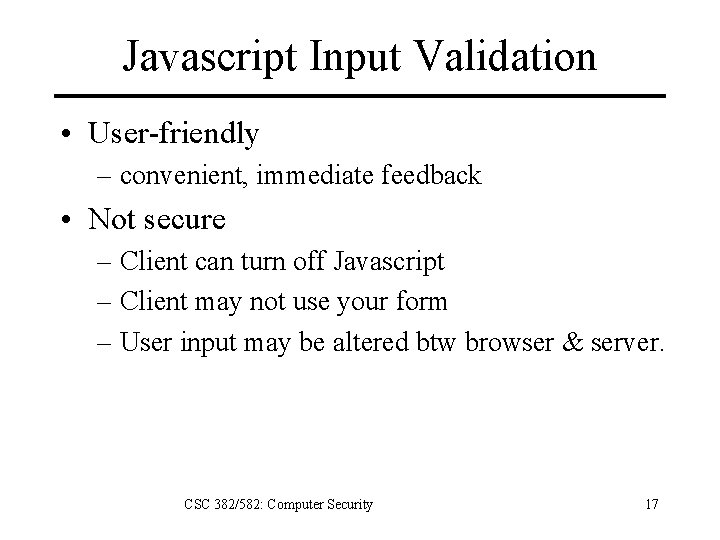
Javascript Input Validation • User-friendly – convenient, immediate feedback • Not secure – Client can turn off Javascript – Client may not use your form – User input may be altered btw browser & server. CSC 382/582: Computer Security 17
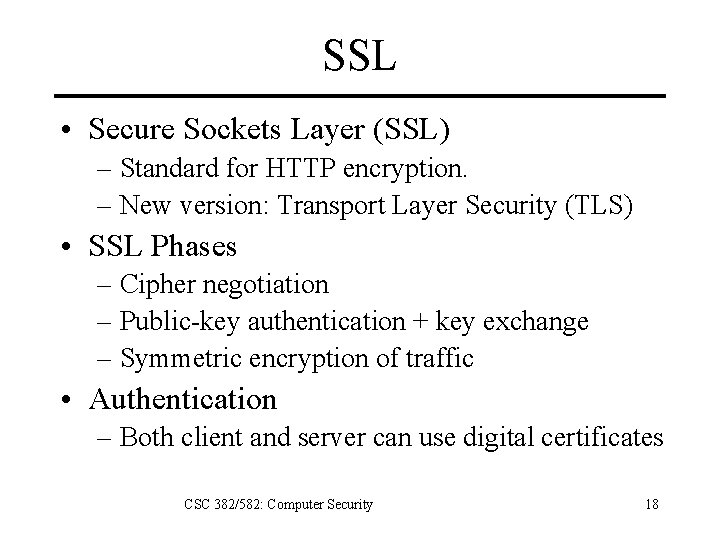
SSL • Secure Sockets Layer (SSL) – Standard for HTTP encryption. – New version: Transport Layer Security (TLS) • SSL Phases – Cipher negotiation – Public-key authentication + key exchange – Symmetric encryption of traffic • Authentication – Both client and server can use digital certificates CSC 382/582: Computer Security 18
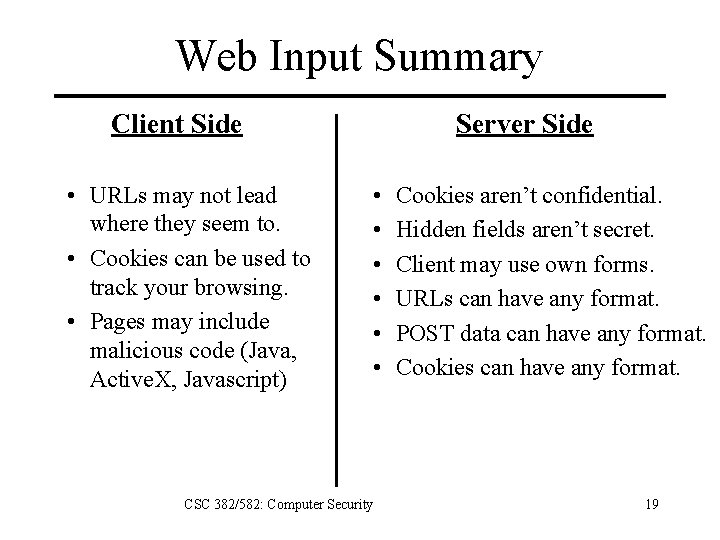
Web Input Summary Client Side • URLs may not lead where they seem to. • Cookies can be used to track your browsing. • Pages may include malicious code (Java, Active. X, Javascript) Server Side • • • CSC 382/582: Computer Security Cookies aren’t confidential. Hidden fields aren’t secret. Client may use own forms. URLs can have any format. POST data can have any format. Cookies can have any format. 19
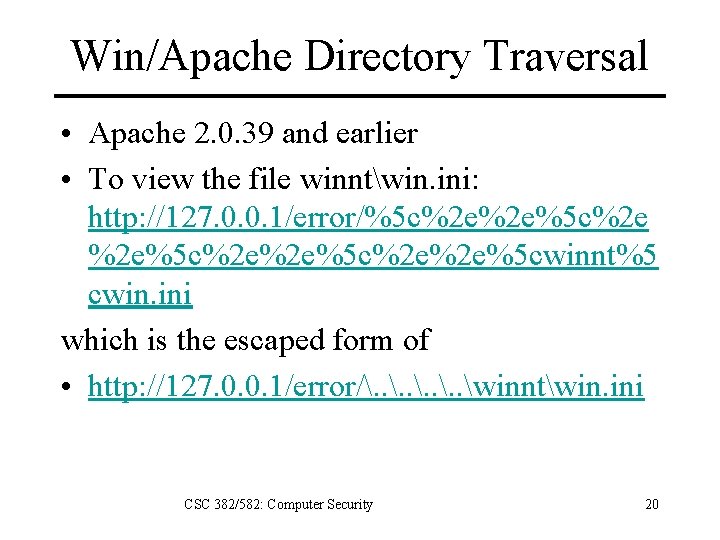
Win/Apache Directory Traversal • Apache 2. 0. 39 and earlier • To view the file winntwin. ini: http: //127. 0. 0. 1/error/%5 c%2 e%2 e%5 c%2 e%2 e%5 cwinnt%5 cwin. ini which is the escaped form of • http: //127. 0. 0. 1/error/. . winntwin. ini CSC 382/582: Computer Security 20
Naïve Solution to Name Issues Remove or check for known insecure elements in original pathname, i. e. “. . ” “/cgi-bin” or other protected directories “. exe” or other special filename extensions Trailing “. ” or “” URI-escaped characters CSC 382/582: Computer Security 21
IIS Directory Traversal • MS Internet Information Server 4 + 5 • Execute shell command: http: //127. 0. 0. 1/scripts/. . %c 0%af. . /winnt/system 32/cmd. exe where %c 0%af is 2 -byte UTF-8 encoding “/” • Problem: Too many ways to encode paths. CSC 382/582: Computer Security 22
Canonicalization • Resolve all names to canonical name using operating system functions. – Use standard OS function where available. • Do access control using canonical name. CSC 382/582: Computer Security 23
Web Authentication • Initial authentication by password. • How does web app remember authentication? – Cookies – Hidden form fields – URL paths • Problem: client can tamper with all three. CSC 382/582: Computer Security 24
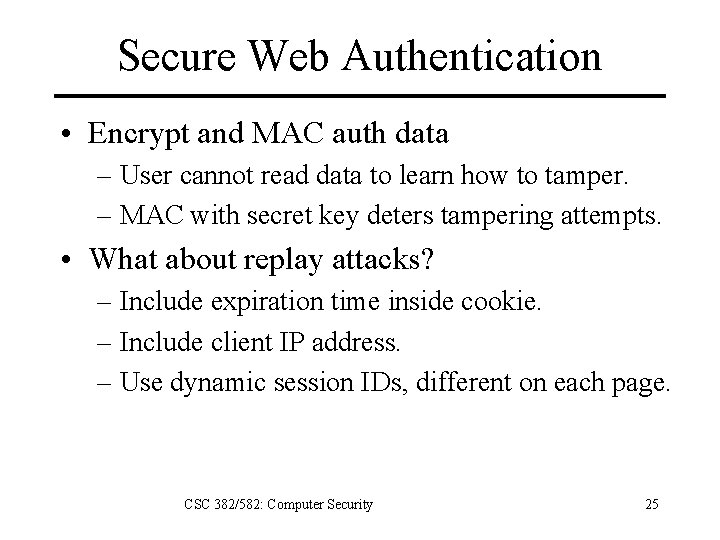
Secure Web Authentication • Encrypt and MAC auth data – User cannot read data to learn how to tamper. – MAC with secret key deters tampering attempts. • What about replay attacks? – Include expiration time inside cookie. – Include client IP address. – Use dynamic session IDs, different on each page. CSC 382/582: Computer Security 25
CSC 382/582: Computer Security 26
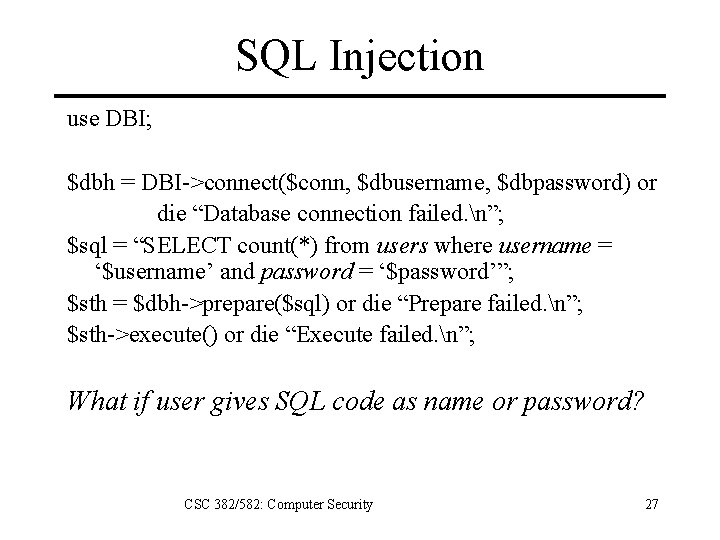
SQL Injection use DBI; $dbh = DBI->connect($conn, $dbusername, $dbpassword) or die “Database connection failed. n”; $sql = “SELECT count(*) from users where username = ‘$username’ and password = ‘$password’”; $sth = $dbh->prepare($sql) or die “Prepare failed. n”; $sth->execute() or die “Execute failed. n”; What if user gives SQL code as name or password? CSC 382/582: Computer Security 27
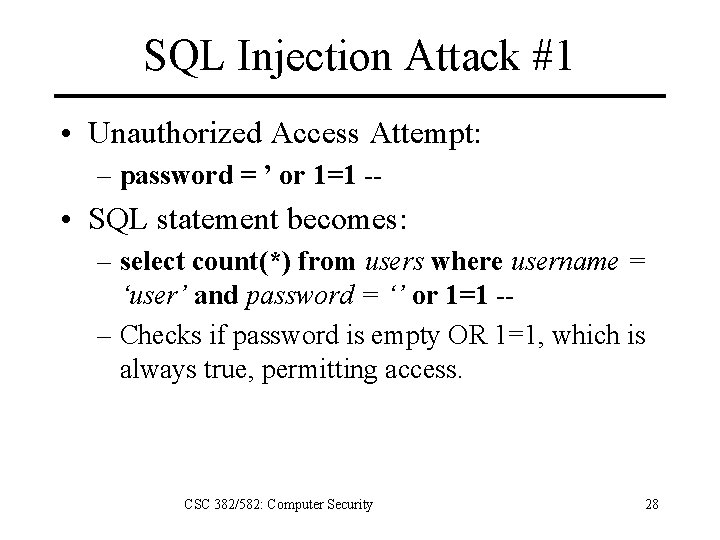
SQL Injection Attack #1 • Unauthorized Access Attempt: – password = ’ or 1=1 -- • SQL statement becomes: – select count(*) from users where username = ‘user’ and password = ‘’ or 1=1 -– Checks if password is empty OR 1=1, which is always true, permitting access. CSC 382/582: Computer Security 28
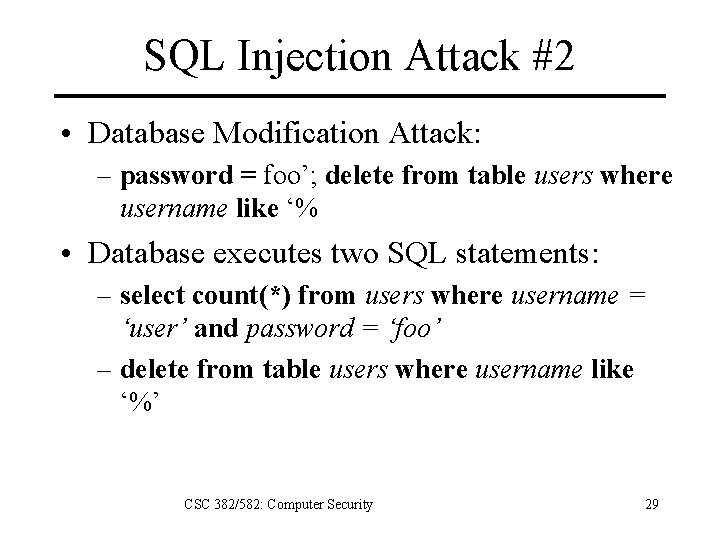
SQL Injection Attack #2 • Database Modification Attack: – password = foo’; delete from table users where username like ‘% • Database executes two SQL statements: – select count(*) from users where username = ‘user’ and password = ‘foo’ – delete from table users where username like ‘%’ CSC 382/582: Computer Security 29
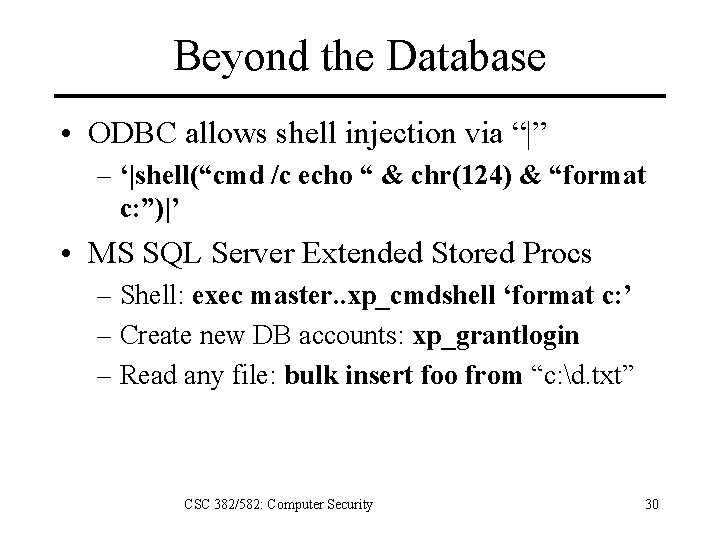
Beyond the Database • ODBC allows shell injection via “|” – ‘|shell(“cmd /c echo “ & chr(124) & “format c: ”)|’ • MS SQL Server Extended Stored Procs – Shell: exec master. . xp_cmdshell ‘format c: ’ – Create new DB accounts: xp_grantlogin – Read any file: bulk insert foo from “c: d. txt” CSC 382/582: Computer Security 30
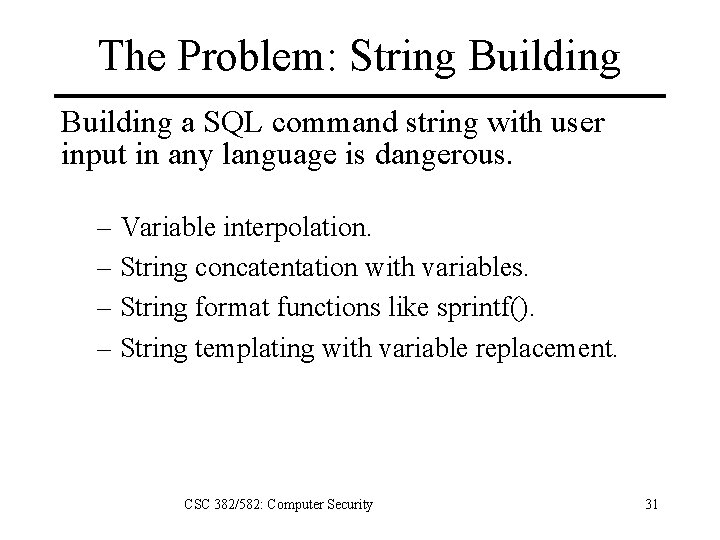
The Problem: String Building a SQL command string with user input in any language is dangerous. – Variable interpolation. – String concatentation with variables. – String format functions like sprintf(). – String templating with variable replacement. CSC 382/582: Computer Security 31
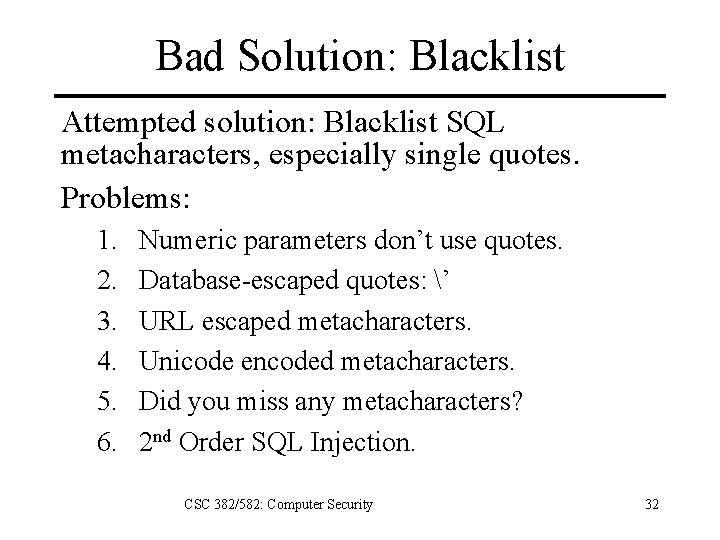
Bad Solution: Blacklist Attempted solution: Blacklist SQL metacharacters, especially single quotes. Problems: 1. 2. 3. 4. 5. 6. Numeric parameters don’t use quotes. Database-escaped quotes: ’ URL escaped metacharacters. Unicode encoded metacharacters. Did you miss any metacharacters? 2 nd Order SQL Injection. CSC 382/582: Computer Security 32
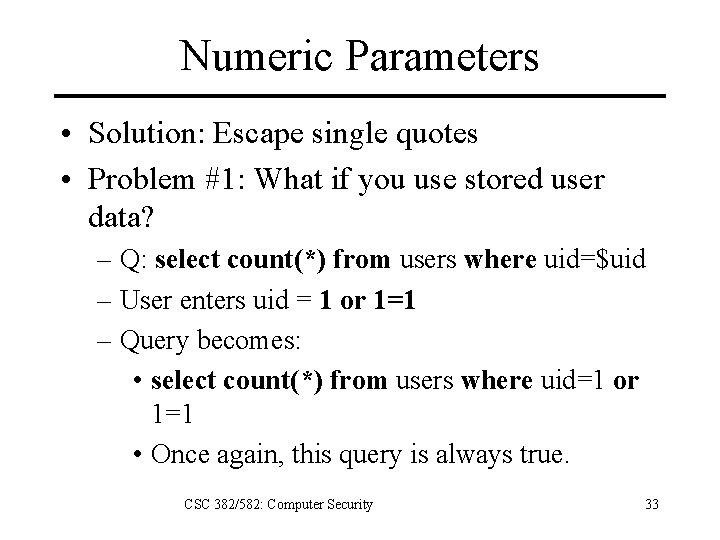
Numeric Parameters • Solution: Escape single quotes • Problem #1: What if you use stored user data? – Q: select count(*) from users where uid=$uid – User enters uid = 1 or 1=1 – Query becomes: • select count(*) from users where uid=1 or 1=1 • Once again, this query is always true. CSC 382/582: Computer Security 33
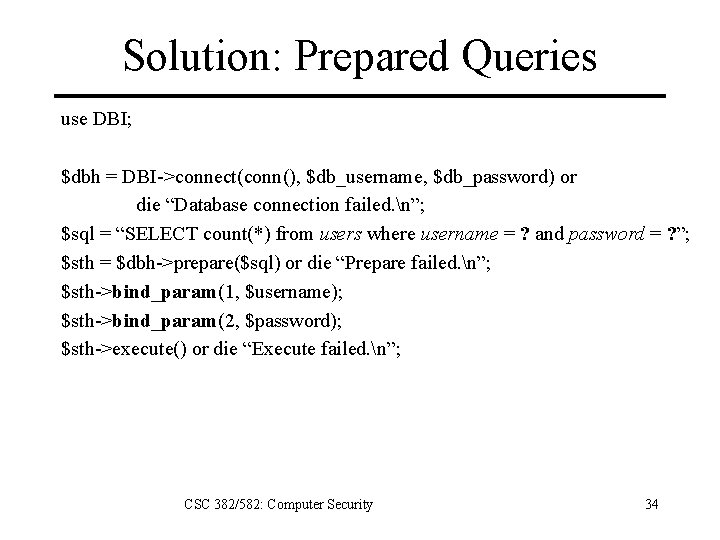
Solution: Prepared Queries use DBI; $dbh = DBI->connect(conn(), $db_username, $db_password) or die “Database connection failed. n”; $sql = “SELECT count(*) from users where username = ? and password = ? ”; $sth = $dbh->prepare($sql) or die “Prepare failed. n”; $sth->bind_param(1, $username); $sth->bind_param(2, $password); $sth->execute() or die “Execute failed. n”; CSC 382/582: Computer Security 34
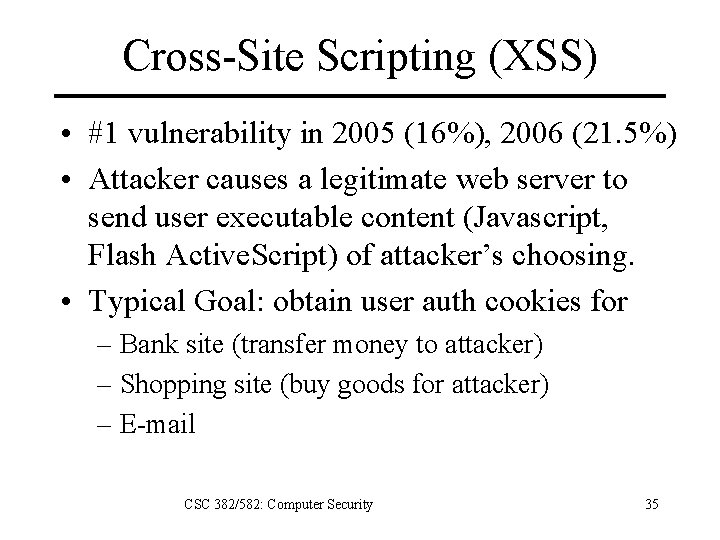
Cross-Site Scripting (XSS) • #1 vulnerability in 2005 (16%), 2006 (21. 5%) • Attacker causes a legitimate web server to send user executable content (Javascript, Flash Active. Script) of attacker’s choosing. • Typical Goal: obtain user auth cookies for – Bank site (transfer money to attacker) – Shopping site (buy goods for attacker) – E-mail CSC 382/582: Computer Security 35
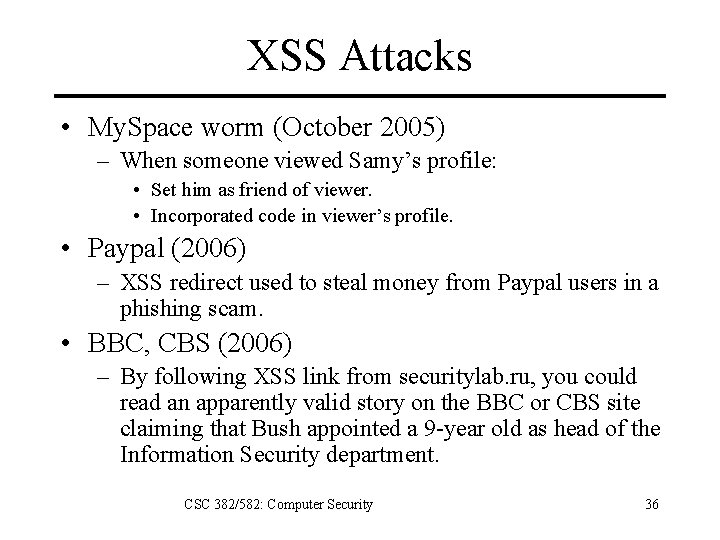
XSS Attacks • My. Space worm (October 2005) – When someone viewed Samy’s profile: • Set him as friend of viewer. • Incorporated code in viewer’s profile. • Paypal (2006) – XSS redirect used to steal money from Paypal users in a phishing scam. • BBC, CBS (2006) – By following XSS link from securitylab. ru, you could read an apparently valid story on the BBC or CBS site claiming that Bush appointed a 9 -year old as head of the Information Security department. CSC 382/582: Computer Security 36
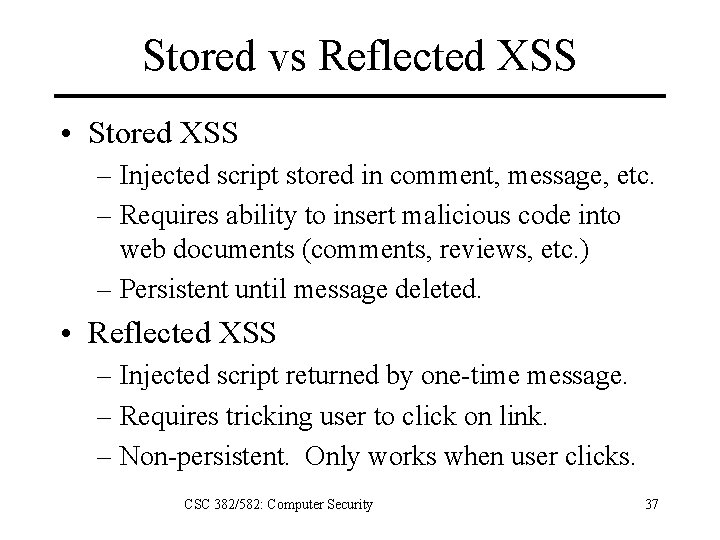
Stored vs Reflected XSS • Stored XSS – Injected script stored in comment, message, etc. – Requires ability to insert malicious code into web documents (comments, reviews, etc. ) – Persistent until message deleted. • Reflected XSS – Injected script returned by one-time message. – Requires tricking user to click on link. – Non-persistent. Only works when user clicks. CSC 382/582: Computer Security 37
Why does XSS Work? • Same-Origin Policy – Browser only allows Javascript from site X to access cookies and other data from site X. – Attacker needs to make attack come from site X. • Vulnerable Server Program – Any program that returns user input without filtering out dangerous code. CSC 382/582: Computer Security 38
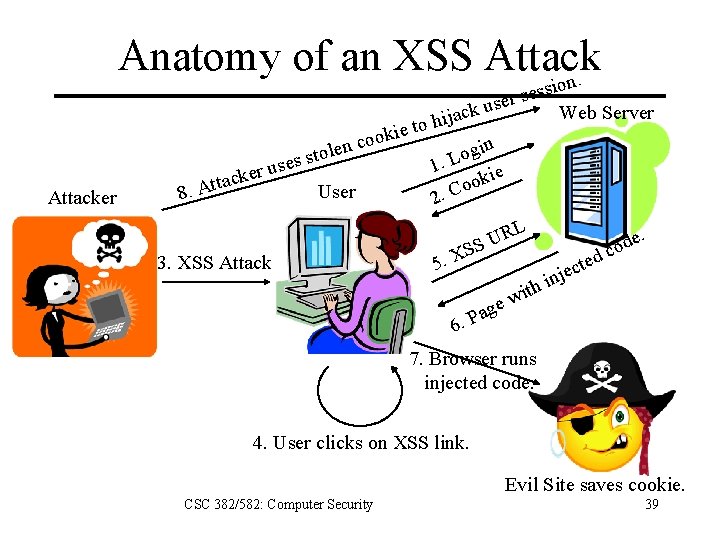
Anatomy of an XSS Attack on. Attacker se r e s ck u a j i h to e i k o co n in e l g o o t s. L es s 1 u r ie ke k c a o t t o User 8. A 2. C RL U SS X. 3. XSS Attack 5 h it ew g a P 6. ssi Web Server ted c e inj e. d o c 7. Browser runs injected code. 4. User clicks on XSS link. Evil Site saves cookie. CSC 382/582: Computer Security 39
Anatomy of an XSS Attack 1. 2. 3. 4. 5. 6. 7. 8. 9. User logs into legitimate site. Site sends user authentication cookie. Attacker sends user XSS attack containing injected code. User clicks on XSS link in email, web, IM. Browser contacts vulnerable URL at legitimate site with cookie in URL. Legitimate site returns injected code in web page. Browser runs injected code, which accesses evil site with cookie in URL. Evil site records user cookie. Attacker uses cookie to authenticate to legitimate site as user. CSC 382/582: Computer Security 40
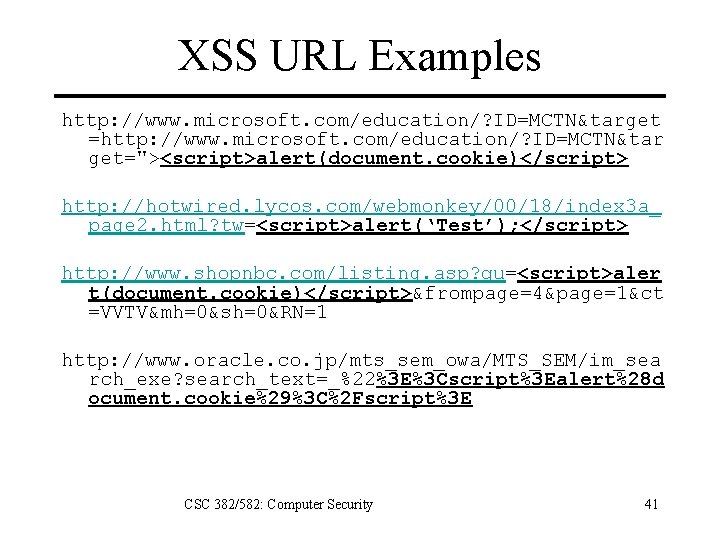
XSS URL Examples http: //www. microsoft. com/education/? ID=MCTN&target =http: //www. microsoft. com/education/? ID=MCTN&tar get="><script>alert(document. cookie)</script> http: //hotwired. lycos. com/webmonkey/00/18/index 3 a_ page 2. html? tw=<script>alert(‘Test’); </script> http: //www. shopnbc. com/listing. asp? qu=<script>aler t(document. cookie)</script>&frompage=4&page=1&ct =VVTV&mh=0&sh=0&RN=1 http: //www. oracle. co. jp/mts_sem_owa/MTS_SEM/im_sea rch_exe? search_text=_%22%3 E%3 Cscript%3 Ealert%28 d ocument. cookie%29%3 C%2 Fscript%3 E CSC 382/582: Computer Security 41
Preventing XSS • Client: Disable scripting – Use No. Script to permit some sites to use scripts. • Server: Disallow HTML input – Reject any input with HTML – Replace HTML special characters • ex: replace < with < and > with > • also replace (, ), #, & • Server: Allow only safe HTML tags – Escape all HTML tags except whitelisted ones • Server: tagged cookies – Include IP address in cookie and only allow access to original IP address that cookie was created for. CSC 382/582: Computer Security 42
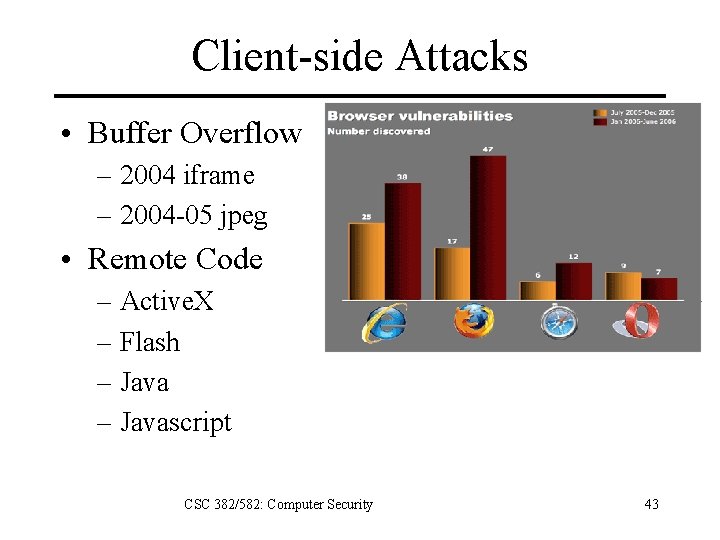
Client-side Attacks • Buffer Overflow – 2004 iframe – 2004 -05 jpeg • Remote Code – Active. X – Flash – Javascript CSC 382/582: Computer Security 43
Active. X Executable code downloaded from server – Activated by HTML object tag. – Native code binary format. Security model – Digital signature authentication – Zone-based access control – No control once execution starts CSC 382/582: Computer Security 44
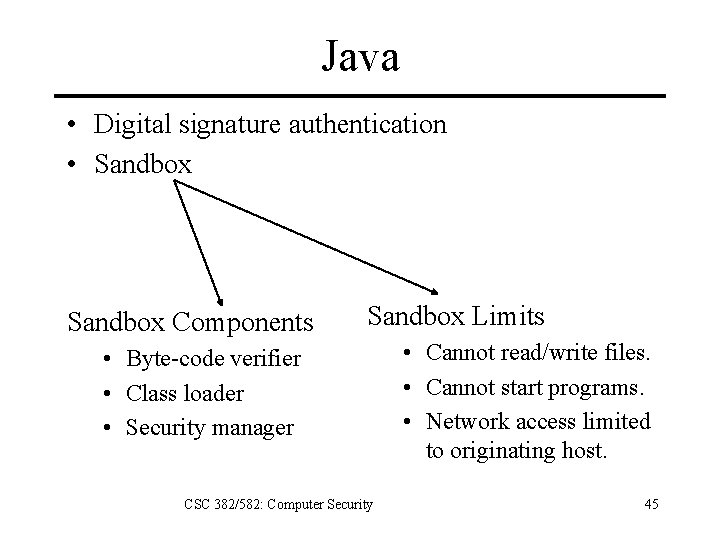
Java • Digital signature authentication • Sandbox Components Sandbox Limits • Byte-code verifier • Class loader • Security manager CSC 382/582: Computer Security • Cannot read/write files. • Cannot start programs. • Network access limited to originating host. 45
Client Protection • Disable Active. X and Java. • Run browser with least privilege. • Use a browser sandbox: – VMWare Virtual Browser Appliance – Protected Mode IE (Windows Vista) • • Goto sites directly instead of using links. Use plain text e-mail instead of HTML. Patch your browser regularly. Use a personal firewall. CSC 382/582: Computer Security 46
Web Reconnaissance • Google Hacking – “Index of” +passwd – “Index of” +password. txt – filetype: htaccess user – allinurl: _vti_bin shtml. exe • Web Crawling Santy Worm used Google to find vulnerable servers. – wget --mirror http: //www. w 3. org/ -o /mirror/w 3 CSC 382/582: Computer Security 47
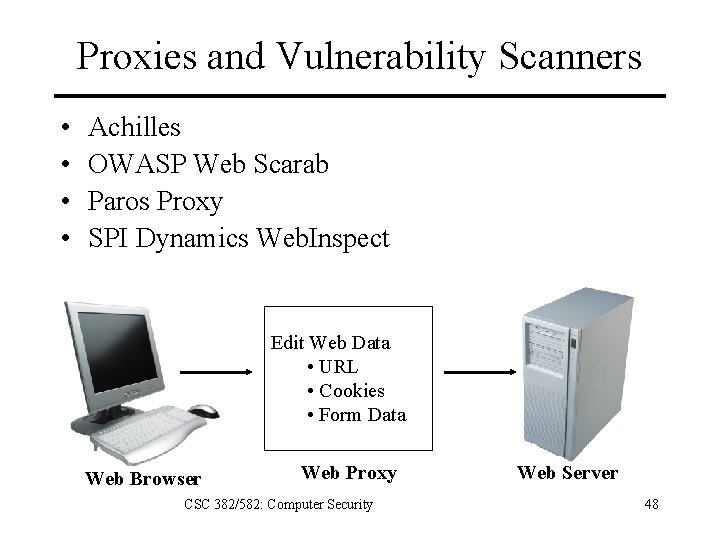
Proxies and Vulnerability Scanners • • Achilles OWASP Web Scarab Paros Proxy SPI Dynamics Web. Inspect Edit Web Data • URL • Cookies • Form Data Web Browser Web Proxy CSC 382/582: Computer Security Web Server 48
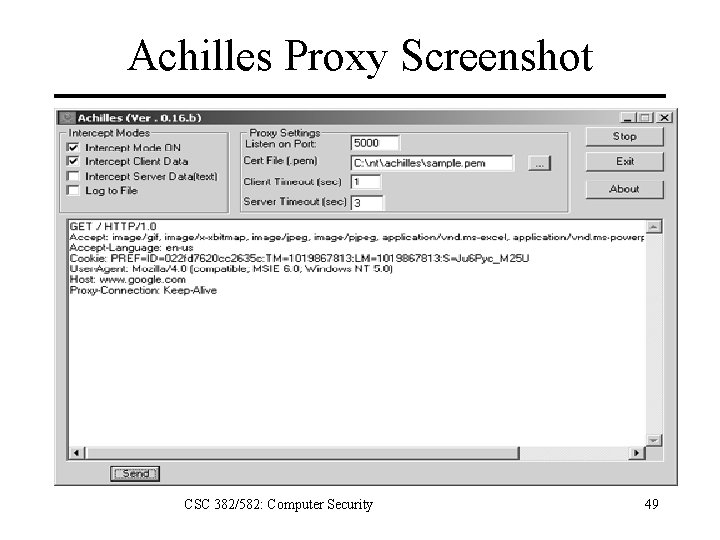
Achilles Proxy Screenshot CSC 382/582: Computer Security 49
Key Points • All input can be dangerous – URLs, Cookies, Executable content • Consider both client and server security. • SSL is not a panacea – Confidentiality + integrity of data in transit. – Input-based attacks can be delivered via SSL. • Top Vulnerabilities – Cross-Site Scripting – SQL Injection CSC 382/582: Computer Security 50
References 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 16. Chris Anley, “Advanced SQL Injection In SQL Server Applications, ” http: //www. nextgenss. com/papers/advanced_sql_injection. pdf, 2002. CERT, “Understanding Malicious Content Mitigation for Web Developers, ” http: //www. cert. org/tech_tips/malicious_code_mitigation. html, Feb. 2000 David Endler, “The Evolution of Cross-Site Scripting Attacks, ” http: //www. cgisecurity. com/development/xss. shtml, 2002. Joris Evers, “Paypal fixes Phishing hole, ” http: //news. com/Pay. Pal+fixes+phishing+hole/21007349_3 -6084974. html, 2006. Stephen J. Friedl, “SQL Injection Attacks by Example, ” http: //www. unixwiz. net/techtips/sqlinjection. html, 2005. Michael Howard, David Le. Blanc, and John Viega, 19 Deadly Sins of Software Security, Mc. Graw-Hill Osborne, 2005. Johnny Long, Google Hacking for Penetration Testers, Syngress, 2004. Johnny Long, Google Hacking Database, http: //johnny. ihackstuff. com, 2006. Nate Mook, “Cross-Site Scripting Worm Hits My. Space, ” http: //www. betanews. com/article/Cross. Site_Scripting_Worm_Hits_My. Space/1129232391, 2005. Gunter Ollman, “HTML Code Injection and Cross-Site Scripting, ” http: //www. technicalinfo. net/papers/CSS. html, 2002. Samy, “My. Space Worm Explanation, ” http: //namb. la/popular/tech. html, 2005. Stuart Mc. Clure, Joel Scambray, and George Kurtz, Hacking Exposed, 5/e, Mc. Graw-Hill, 2005. Stuart Mc. Clure, Saumil Shah and Shreeraj Shah, Web Hacking: Attacks and Defense, Addison-Wesley, 2002. Joel Scambray, Mike Shema, Caleb Sima, Hacking Exposed Web Applications, Second Edition, Mc. Graw-Hill, 2006. Ed Skoudis, Counter Hack Reloaded, Prentice Hall, 2006. SK, “SQL Injection Walkthrough, ” http: //www. securiteam. com/securityreviews/5 DP 0 N 1 P 76 E. html, CSC 382/582: Computer Security 51 2002.
- Slides: 51