CSc 352 Programming Hygiene Saumya Debray Dept of
CSc 352 Programming Hygiene Saumya Debray Dept. of Computer Science The University of Arizona, Tucson debray@cs. arizona. edu
Bugs have consequences 2
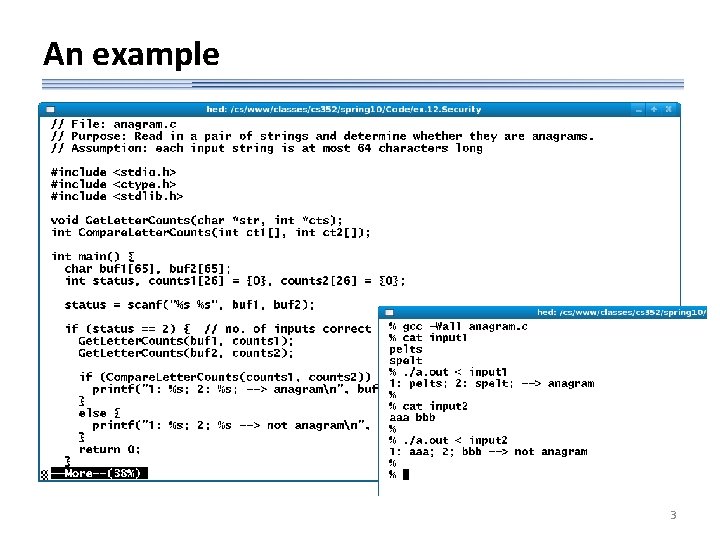
An example 3
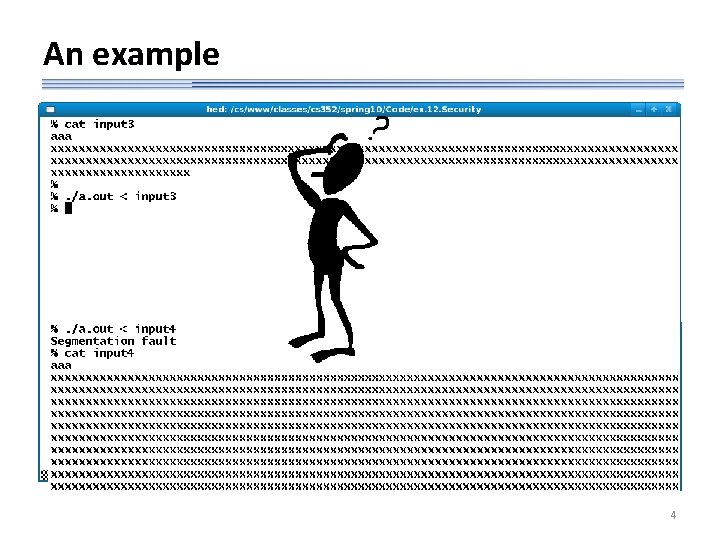
An example 4
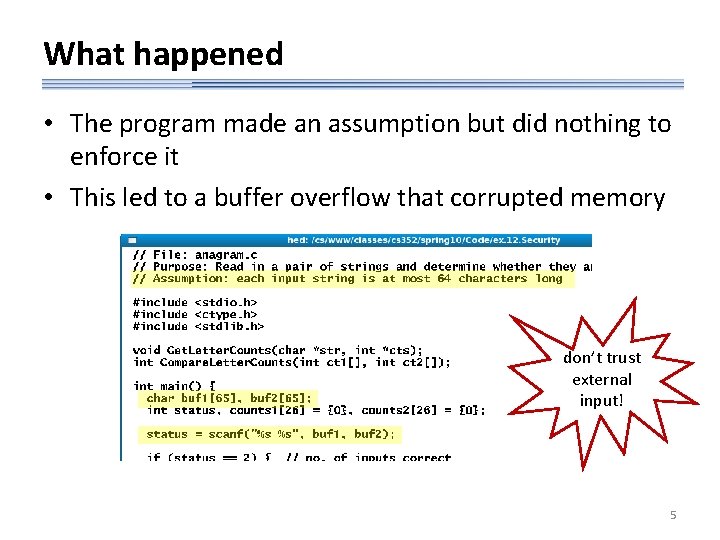
What happened • The program made an assumption but did nothing to enforce it • This led to a buffer overflow that corrupted memory don’t trust external input! 5
Buffer overflows • C does not have array bounds checking – it is possible to write past the end of an array – this has the effect of overwriting other memory locations – depending on what gets corrupted, the program may: • • show no effects compute different results crash let someone else take control of your program (and possibly your computer) 6
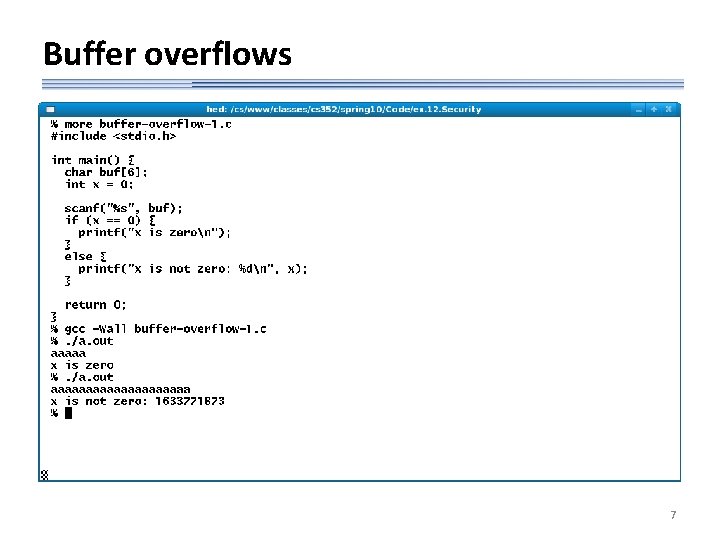
Buffer overflows 7
Some examples of buffer overflows 8
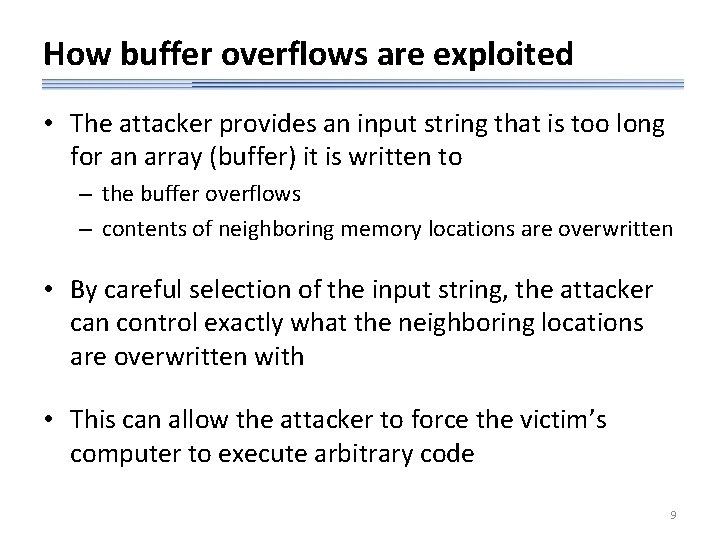
How buffer overflows are exploited • The attacker provides an input string that is too long for an array (buffer) it is written to – the buffer overflows – contents of neighboring memory locations are overwritten • By careful selection of the input string, the attacker can control exactly what the neighboring locations are overwritten with • This can allow the attacker to force the victim’s computer to execute arbitrary code 9
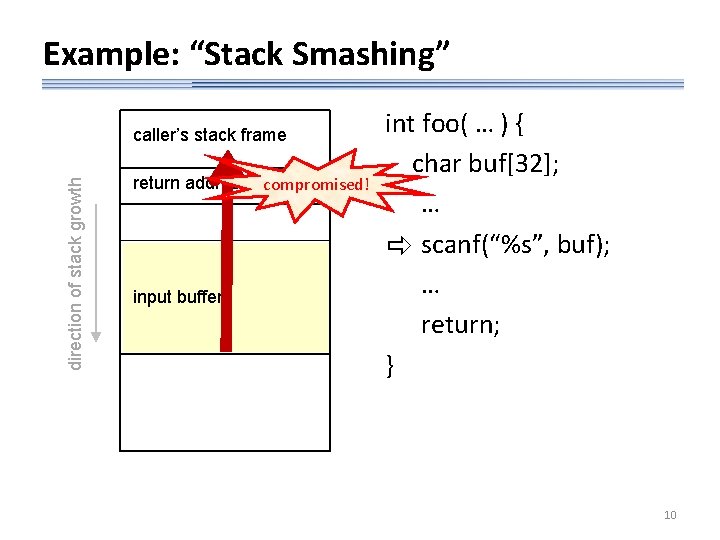
Example: “Stack Smashing” direction of stack growth caller’s stack frame return address compromised! input buffer int foo( … ) { char buf[32]; … scanf(“%s”, buf); … return; } 10
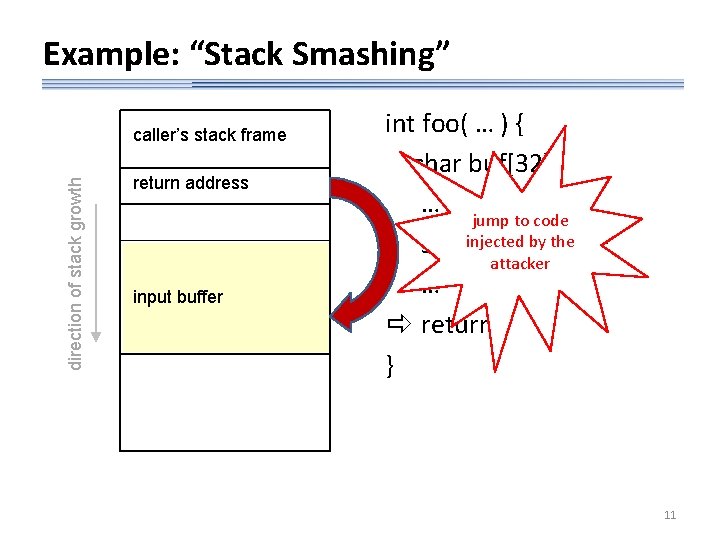
Example: “Stack Smashing” direction of stack growth caller’s stack frame return address Compromised! input buffer int foo( … ) { char buf[32]; … jump to code injected by the scanf(“%s”, buf); attacker … return; } 11
![Controlling amount of input read • [f]scanf lets you specify a maximum field width Controlling amount of input read • [f]scanf lets you specify a maximum field width](http://slidetodoc.com/presentation_image_h2/4d5d6116b12080160bd153cfd835e424/image-12.jpg)
Controlling amount of input read • [f]scanf lets you specify a maximum field width before the conversion specifier – max. field width: optional decimal integer – if specified: reading of characters stops when this width is reached – for strings: field width does not include terminating ‘�’ 12
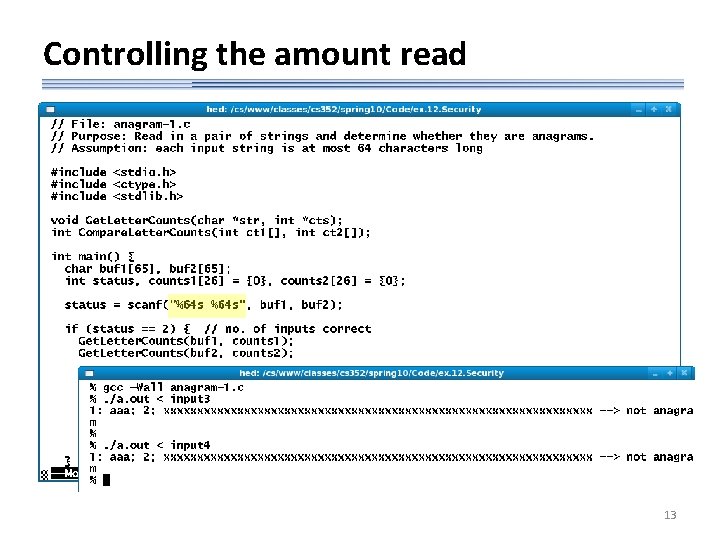
Controlling the amount read 13
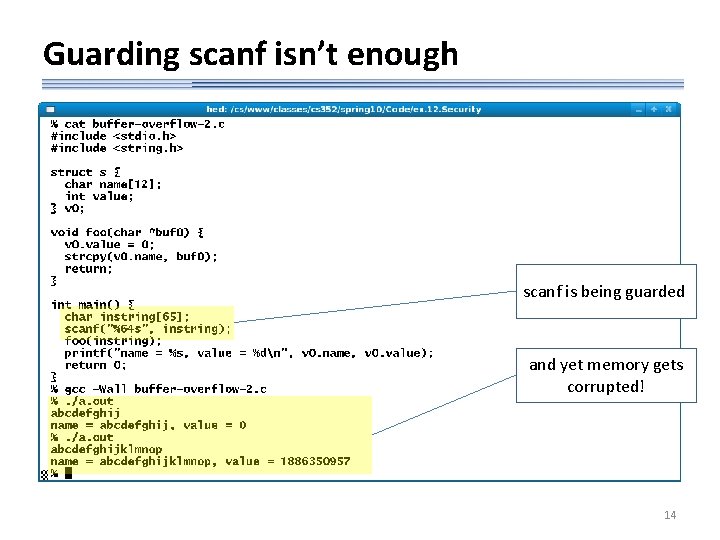
Guarding scanf isn’t enough scanf is being guarded and yet memory gets corrupted! 14
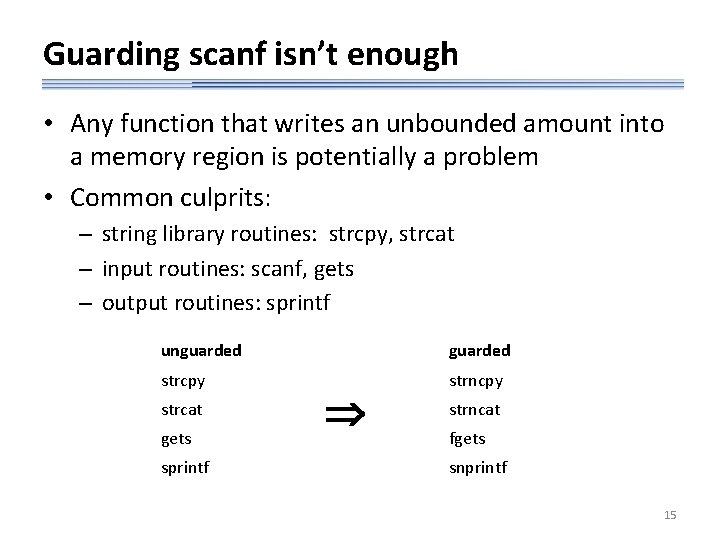
Guarding scanf isn’t enough • Any function that writes an unbounded amount into a memory region is potentially a problem • Common culprits: – string library routines: strcpy, strcat – input routines: scanf, gets – output routines: sprintf unguarded strcpy strncpy strcat gets sprintf strncat fgets snprintf 15
Example: strcpy vs. strncpy 16
![It’s easy to get careless str 0[ ], name[ ] are the same size: It’s easy to get careless str 0[ ], name[ ] are the same size:](http://slidetodoc.com/presentation_image_h2/4d5d6116b12080160bd153cfd835e424/image-17.jpg)
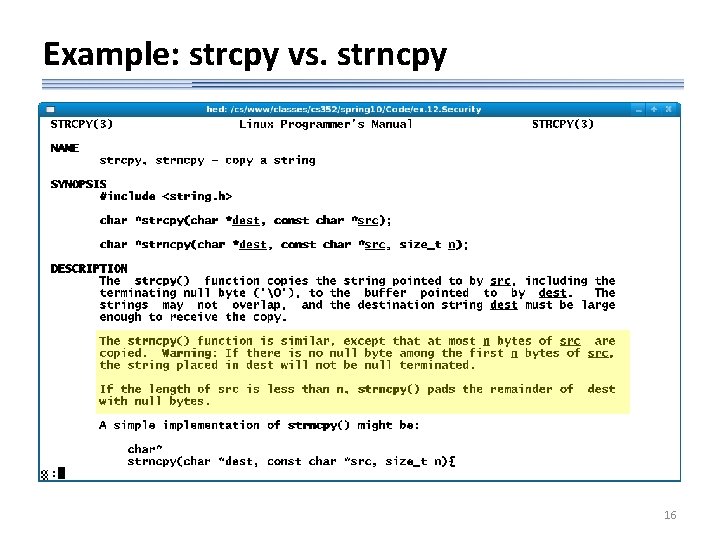
It’s easy to get careless str 0[ ], name[ ] are the same size: 4 bytes we’ve made sure we copied at most 4 bytes into str 0 therefore it’s OK to use just strcpy() to copy str 0 into v 0. name right? 17
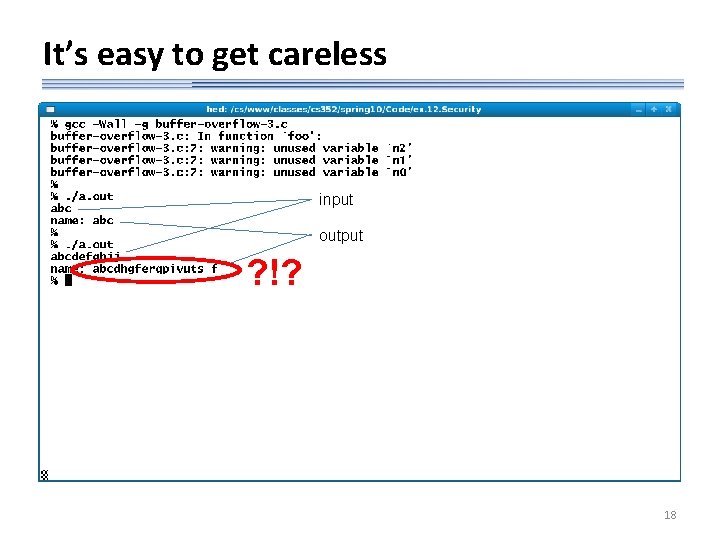
It’s easy to get careless input output ? !? 18
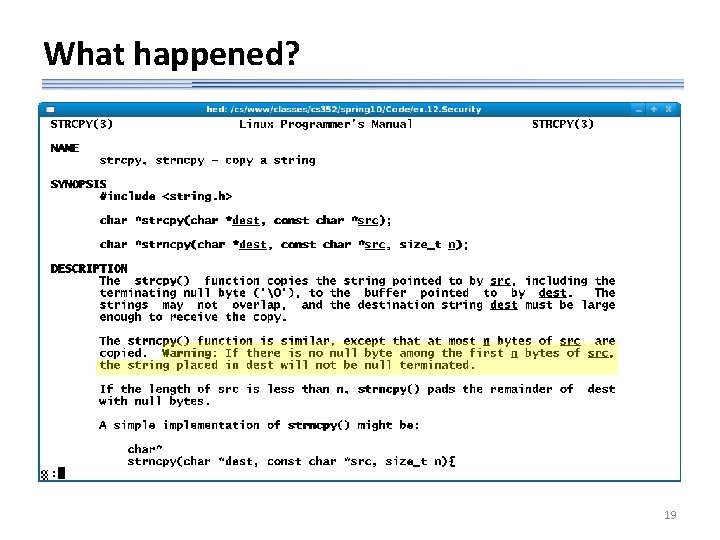
What happened? 19
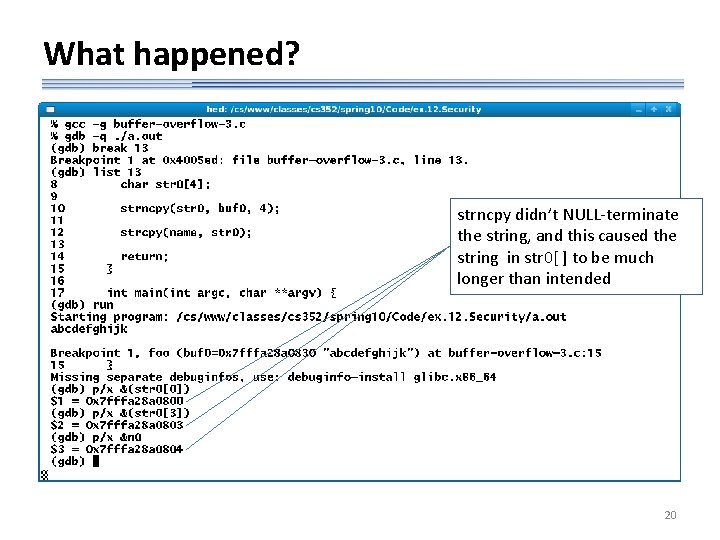
What happened? strncpy didn’t NULL-terminate the string, and this caused the string in str 0[ ] to be much longer than intended 20
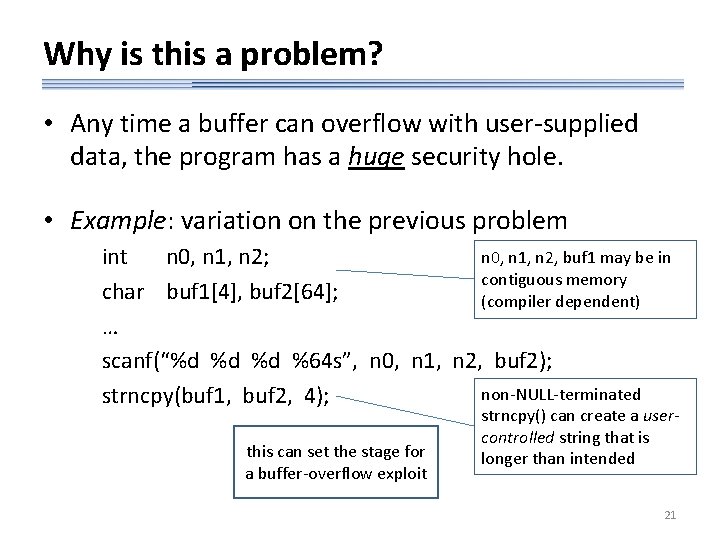
Why is this a problem? • Any time a buffer can overflow with user-supplied data, the program has a huge security hole. • Example: variation on the previous problem n 0, n 1, n 2, buf 1 may be in int n 0, n 1, n 2; contiguous memory char buf 1[4], buf 2[64]; (compiler dependent) … scanf(“%d %d %d %64 s”, n 0, n 1, n 2, buf 2); non-NULL-terminated strncpy(buf 1, buf 2, 4); this can set the stage for a buffer-overflow exploit strncpy() can create a usercontrolled string that is longer than intended 21
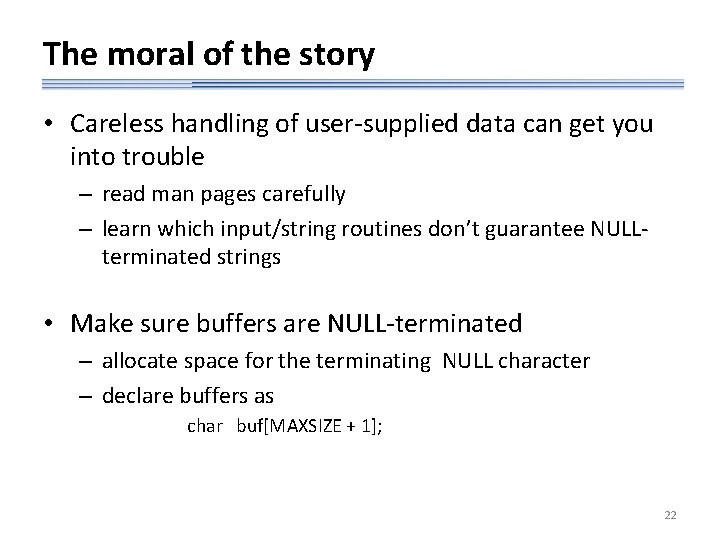
The moral of the story • Careless handling of user-supplied data can get you into trouble – read man pages carefully – learn which input/string routines don’t guarantee NULLterminated strings • Make sure buffers are NULL-terminated – allocate space for the terminating NULL character – declare buffers as char buf[MAXSIZE + 1]; 22
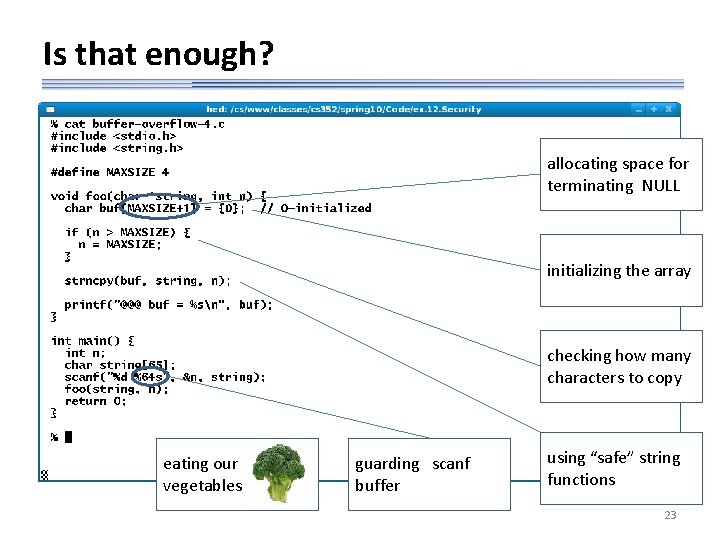
Is that enough? allocating space for terminating NULL initializing the array checking how many characters to copy eating our vegetables guarding scanf buffer using “safe” string functions 23
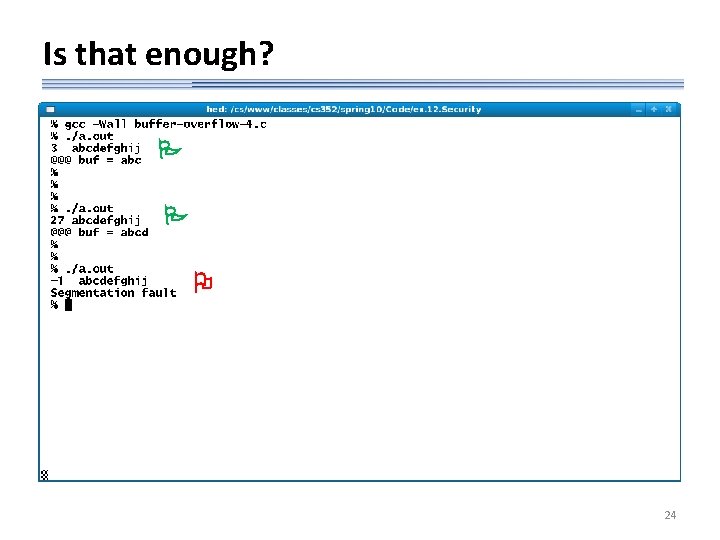
Is that enough? 24
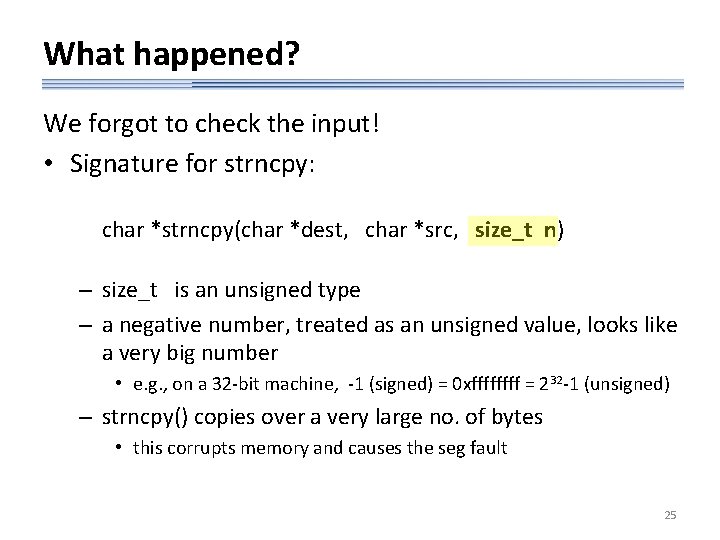
What happened? We forgot to check the input! • Signature for strncpy: char *strncpy(char *dest, char *src, size_t n) – size_t is an unsigned type – a negative number, treated as an unsigned value, looks like a very big number • e. g. , on a 32 -bit machine, -1 (signed) = 0 xffff = 232 -1 (unsigned) – strncpy() copies over a very large no. of bytes • this corrupts memory and causes the seg fault 25
- Slides: 25