CS 716 Advanced Computer Networks By Dr Amir
CS 716 Advanced Computer Networks By Dr. Amir Qayyum 1

Lecture No. 10
Ethernet MAC – CSMA/CD • Multiple access – Nodes send and receive frames over a shared link • Carrier sense – Nodes can distinguish between an idle and busy link • Collision detection – A node listens as it transmits to detect collision 3
CSMA/CD MAC Algorithm • If line is idle (no carrier sensed) – Send immediately – Upper bound message size of ~1500 bytes – Must wait 9. 6µs between back-toback frames 4
CSMA/CD MAC Algorithm • If line is busy (carrier sensed) … – Wait until the line becomes idle and then transmit immediately – Called 1 -persistent (special case of ppersistent) • If collision detected – Stop sending data and jam signal – Try again later 5
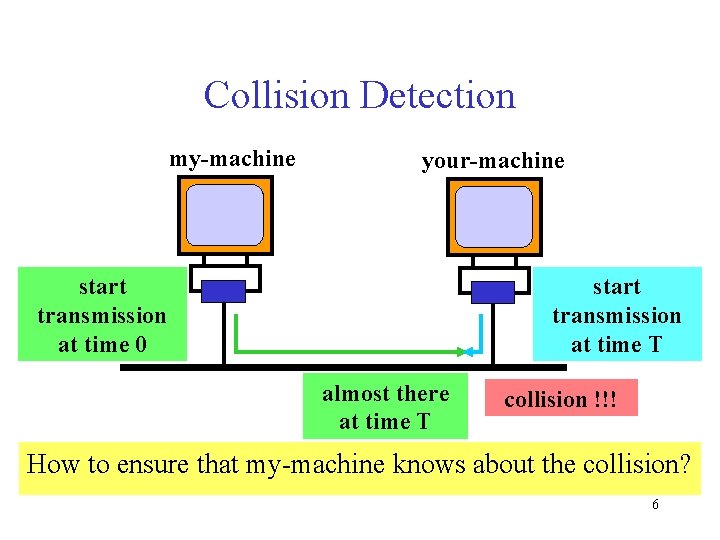
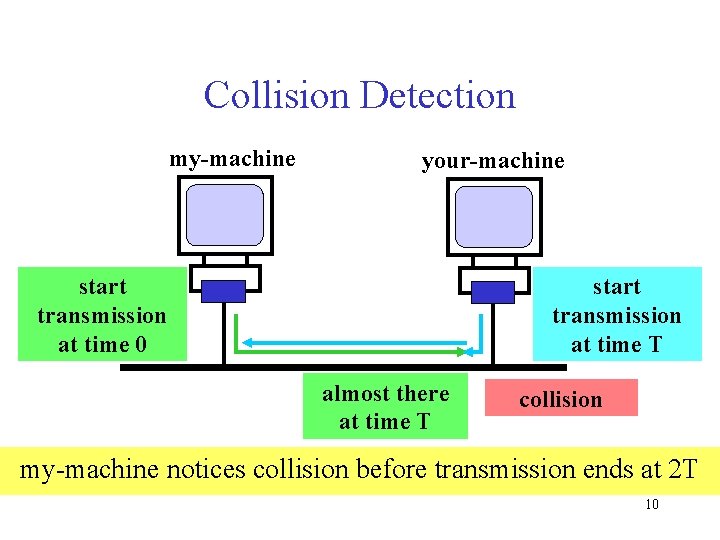
Collision Detection my-machine your-machine start transmission at time 0 start transmission at time T almost there at time T collision !!! How to ensure that my-machine knows about the collision? 6
Constraints on Collision Detection • In our example, consider – my-machine’s message reaches yourmachine at T – your-machine’s message reaches mymachine at 2 T • Thus, my-machine must still be transmitting at 2 T 7
Constraints on Collision Detection • Specifics of IEEE 802. 3 – bounds 2 T to 51. 2 microseconds – packet must be at least 64 B long • Jam after the collision, for 32 bits, then stop transmitting frame (runt frame of 96 bits) – ensures that all hosts notice collision 8
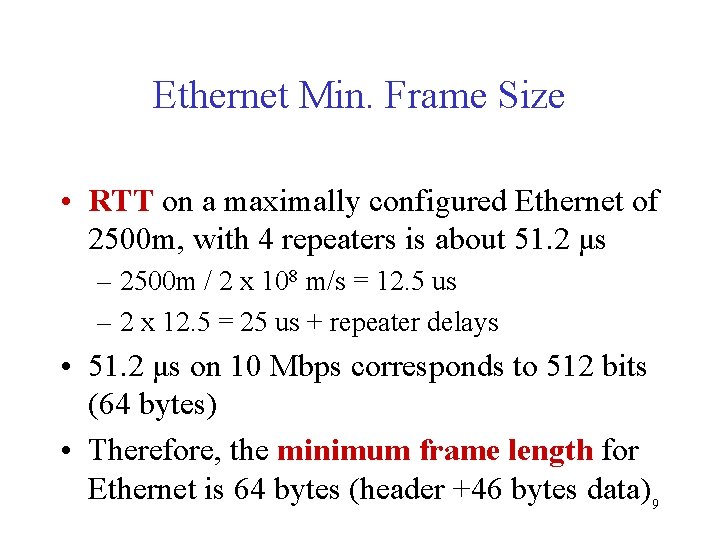
Ethernet Min. Frame Size • RTT on a maximally configured Ethernet of 2500 m, with 4 repeaters is about 51. 2 μs – 2500 m / 2 x 108 m/s = 12. 5 us – 2 x 12. 5 = 25 us + repeater delays • 51. 2 μs on 10 Mbps corresponds to 512 bits (64 bytes) • Therefore, the minimum frame length for Ethernet is 64 bytes (header +46 bytes data) 9
Collision Detection my-machine your-machine start transmission at time 0 start transmission at time T almost there at time T collision my-machine notices collision before transmission ends at 2 T 10
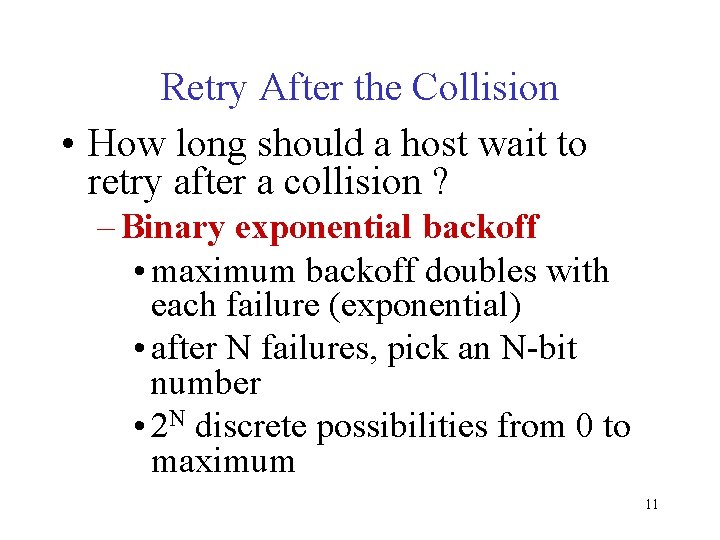
Retry After the Collision • How long should a host wait to retry after a collision ? – Binary exponential backoff • maximum backoff doubles with each failure (exponential) • after N failures, pick an N-bit number • 2 N discrete possibilities from 0 to maximum 11
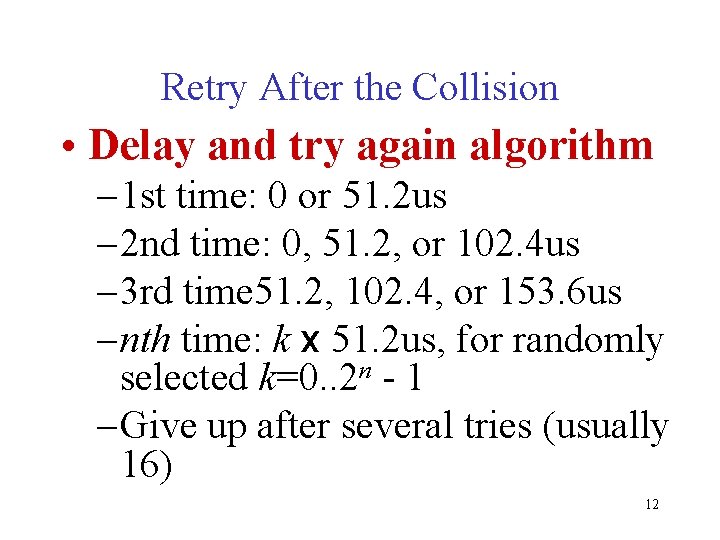
Retry After the Collision • Delay and try again algorithm – 1 st time: 0 or 51. 2 us – 2 nd time: 0, 51. 2, or 102. 4 us – 3 rd time 51. 2, 102. 4, or 153. 6 us – nth time: k x 51. 2 us, for randomly selected k=0. . 2 n - 1 – Give up after several tries (usually 16) 12
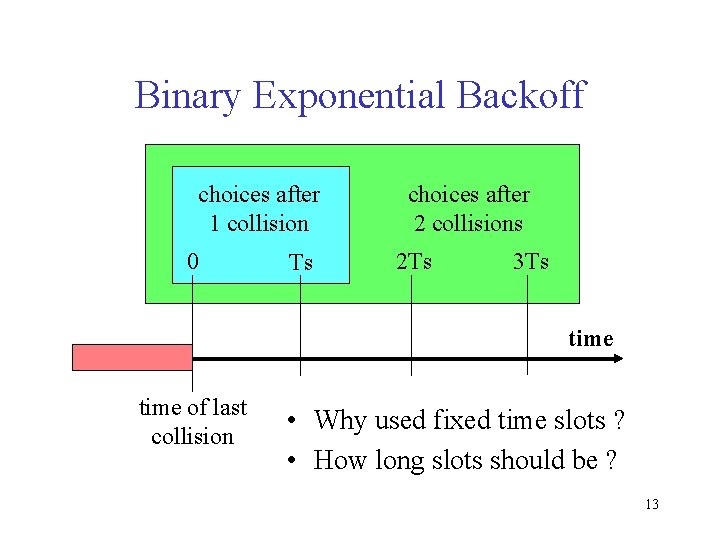
Binary Exponential Backoff choices after 1 collision 0 Ts choices after 2 collisions 2 Ts 3 Ts time of last collision • Why used fixed time slots ? • How long slots should be ? 13
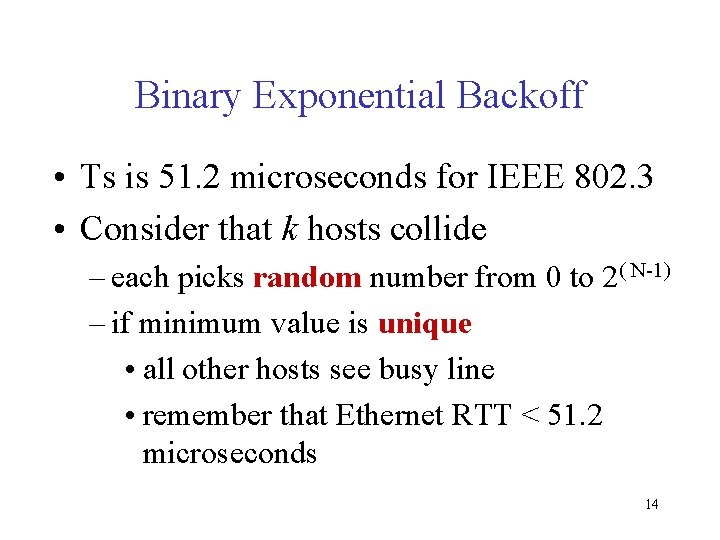
Binary Exponential Backoff • Ts is 51. 2 microseconds for IEEE 802. 3 • Consider that k hosts collide – each picks random number from 0 to 2( N-1) – if minimum value is unique • all other hosts see busy line • remember that Ethernet RTT < 51. 2 microseconds 14
Binary Exponential Backoff • Consider that k hosts collide – if minimum value is not unique • hosts in minimum value slot collide again • following slot idle • consider next smallest backoff value 15
Ethernet Frame Reception • Sender handles all access control • Receiver simply pulls frames from network • Ethernet controller/card – sees all frames – selectively passes frames to host processor 16
Ethernet Frame Reception • Acceptable frames – addressed to host, or; – to multicast address to which host belongs or; – to a broadcast address – anything if in promiscuous mode (packet sniffing and tcpdump requirement) 17
Ethernet Collision Detection • Bus topology Ethernets – Transceiver handles • Carrier detection • Collision detection • Jamming after a collision – Transceiver sees voltage sum • Outgoing signal + Incoming signal – Looks for voltages impossible for local alone • Attenuation can prevent detection • Limits segment length 18
Ethernet Collision Detection • Hub topology Ethernets – Controller/card handles carrier detection – Hub handles • Collision detection • Jamming after a collision – Detect transmission activity on each line – If more than 1 line (host) active • Assert collision to all lines • Continue until no lines active – Attenuation is less critical 19
Experience With Ethernet • Number of hosts limited to 200 in practice, standard allows 1024 • Range much shorter than 2. 5 km limit in standard • Round-trip time is typically 5 or 10 μs, not 50μs 20
Experience With Ethernet • Higher-level flow control (i. e. , TCP) limits load – 30% maximum load recommended – Large packets recommended • Star topologies easier to administer than Bus – Failure isolation, node addition w/o complex topology • (Backwards) Compatibility more important than elegance or raw performance (1 > 0) 21
Token Ring 22
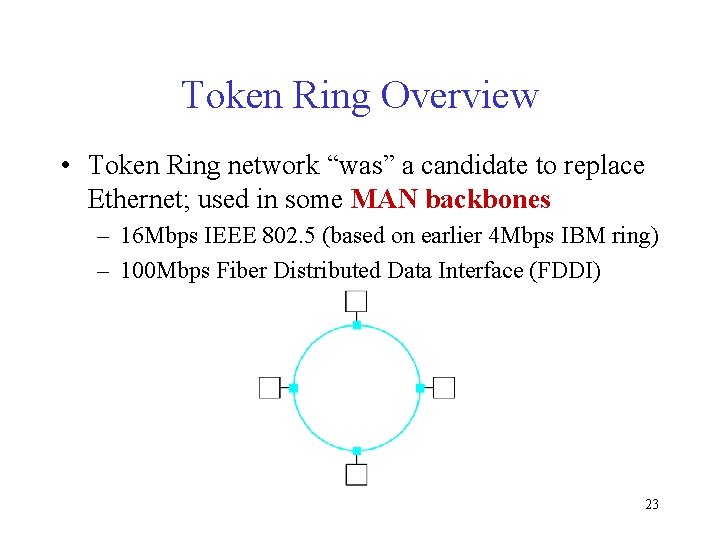
Token Ring Overview • Token Ring network “was” a candidate to replace Ethernet; used in some MAN backbones – 16 Mbps IEEE 802. 5 (based on earlier 4 Mbps IBM ring) – 100 Mbps Fiber Distributed Data Interface (FDDI) 23
Token Ring Rationale • Why emulate a shared medium with pointto-point links? • Why a shared medium? – convenient broadcast capabilities – switches are costly • Why emulation? – simpler MAC algorithm: only have 2 wires – fairer access arbitration – fully digital (802. 3 collision detection requires 24 analog)
IBM Token Ring – IEEE 802. 5 • Data flows in a particular direction – a node receives frames from its upstream neighbor – a node forwards frames to its downstream neighbor 25
IBM Token Ring – IEEE 802. 5 • Ring is viewed as a single shared medium – each node is allowed to transmit according to some distributed algorithm for medium access – all nodes see all frames; destination saves a copy of frame as it flows past • The term “token” indicates the way the access to shared channel is managed 26
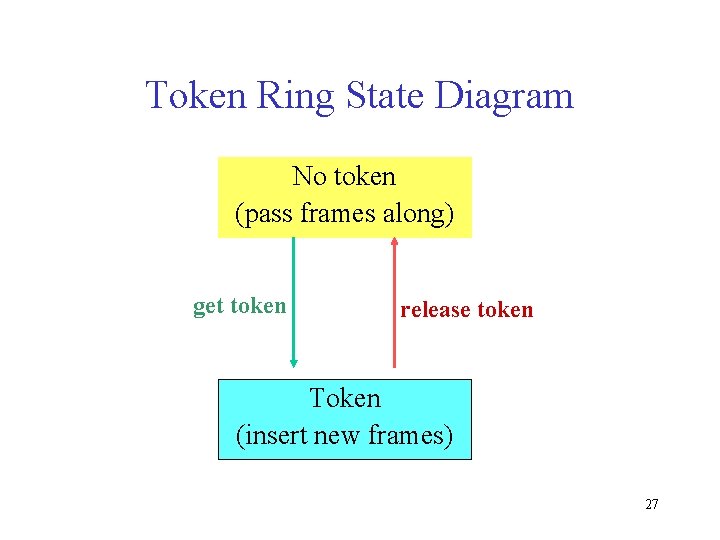
Token Ring State Diagram No token (pass frames along) get token release token Token (insert new frames) 27
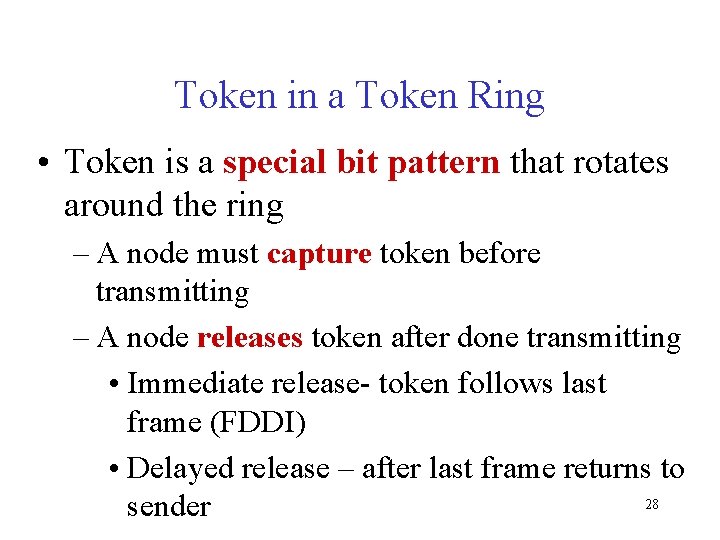
Token in a Token Ring • Token is a special bit pattern that rotates around the ring – A node must capture token before transmitting – A node releases token after done transmitting • Immediate release- token follows last frame (FDDI) • Delayed release – after last frame returns to 28 sender
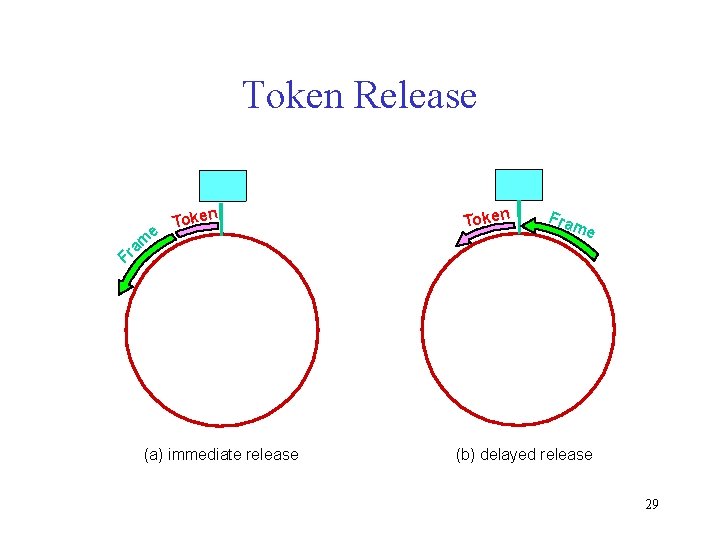
Token Release e Token m a Fr (a) immediate release Token Fra me (b) delayed release 29
Token in a Token Ring • Remove your frame when it comes back around – Transmit another frame or re-insert the token • Stations get round-robin service as the token circulates around the ring 30
Review Lecture 10 • • CSMA/CD MAC algorithm Constraints on collision detection Min frame size – RTT 51. 2 us Retries after collision Binary exp backoff: Min value unique Frame reception: acceptable frames Bus and Hub topology: CD handle Exp: nodes, dist, RTT, 30% load, largeframe 31
Review Lecture 10 • • Token Ring MAN backbone IBM, 802. 5 token ring, FDDI Rationale: emulate shared med p 2 p links Directional data flow Shared med: see all frames, distr MAC algo Token – special bit pattern Capture and release – round robin service 32
- Slides: 32