CS 5950 Computer Security and Information Assurance Section

- Slides: 25
CS 5950 Computer Security and Information Assurance Section 7: Legal, Privacy, and Ethical Issues in Computer Security Dr. Leszek Lilien Department of Computer Science Western Michigan University Slides based on Security in Computing. Third Edition by Pfleeger and Pfleeger. Using some slides courtesy of: Prof. Aaron Striegel — course taught at U. of Notre Dame Prof. Barbara Endicott-Popovsky and Prof. Deborah Frincke (U. Idaho) — taught at U. Washington Prof. Jussipekka Leiwo — taught at Vrije Universiteit (Free U. ), Amsterdam, The Netherlands Slides not created by the above authors are © 2006 by Leszek T. Lilien Requests to use original slides for non-profit purposes will be gladly granted upon a written request.
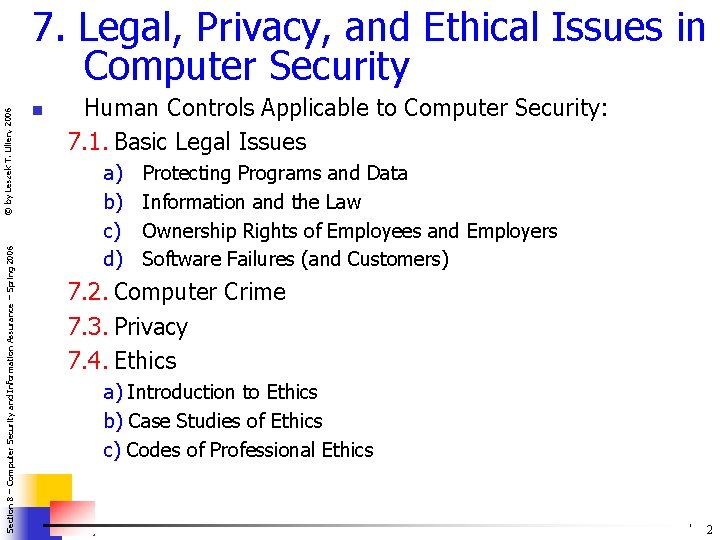
Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 7. Legal, Privacy, and Ethical Issues in Computer Security n Human Controls Applicable to Computer Security: 7. 1. Basic Legal Issues a) b) c) d) Protecting Programs and Data Information and the Law Ownership Rights of Employees and Employers Software Failures (and Customers) 7. 2. Computer Crime 7. 3. Privacy 7. 4. Ethics a) Introduction to Ethics b) Case Studies of Ethics c) Codes of Professional Ethics 2
Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 7. 1. Basic Legal Issues n Outline: a) Protecting Programs and Data b) Information and the Law c) Ownership Rights of Employees and Employers d) Software Failures (and Customers) 3
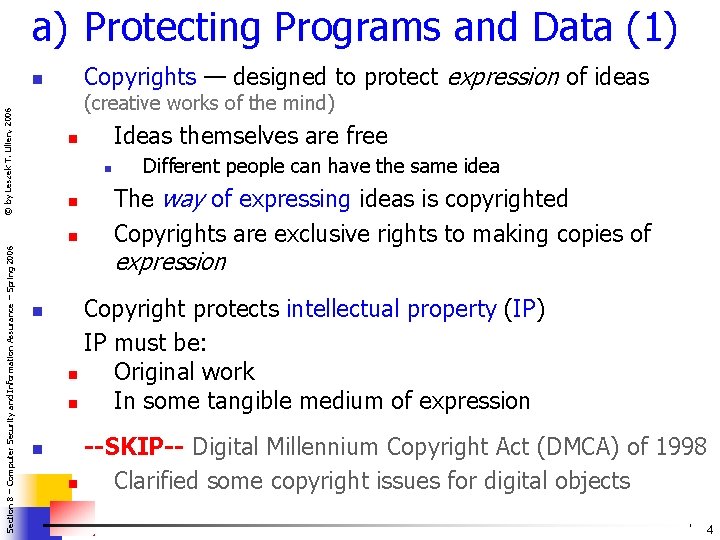
a) Protecting Programs and Data (1) Copyrights — designed to protect expression of ideas n © by Leszek T. Lilien, 2006 (creative works of the mind) n n n Section 8 – Computer Security and Information Assurance – Spring 2006 Ideas themselves are free n Different people can have the same idea The way of expressing ideas is copyrighted Copyrights are exclusive rights to making copies of expression n n Copyright protects intellectual property (IP) IP must be: n Original work n In some tangible medium of expression --SKIP-- Digital Millennium Copyright Act (DMCA) of 1998 n Clarified some copyright issues for digital objects 4
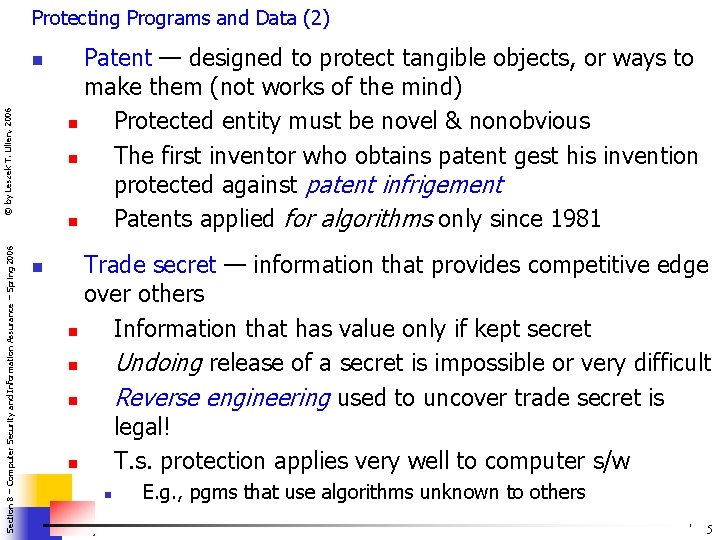
Protecting Programs and Data (2) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n n Patent — designed to protect tangible objects, or ways to make them (not works of the mind) n Protected entity must be novel & nonobvious n The first inventor who obtains patent gest his invention protected against patent infrigement n Patents applied for algorithms only since 1981 Trade secret — information that provides competitive edge over others n Information that has value only if kept secret n Undoing release of a secret is impossible or very difficult n Reverse engineering used to uncover trade secret is legal! n T. s. protection applies very well to computer s/w n E. g. , pgms that use algorithms unknown to others 5
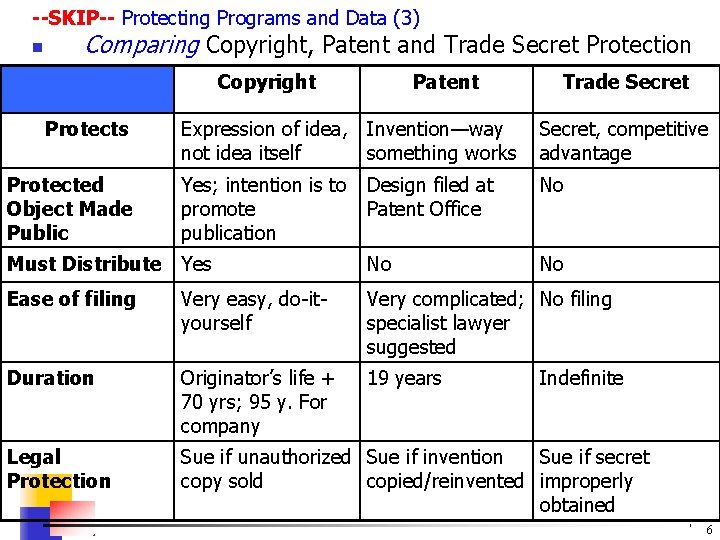
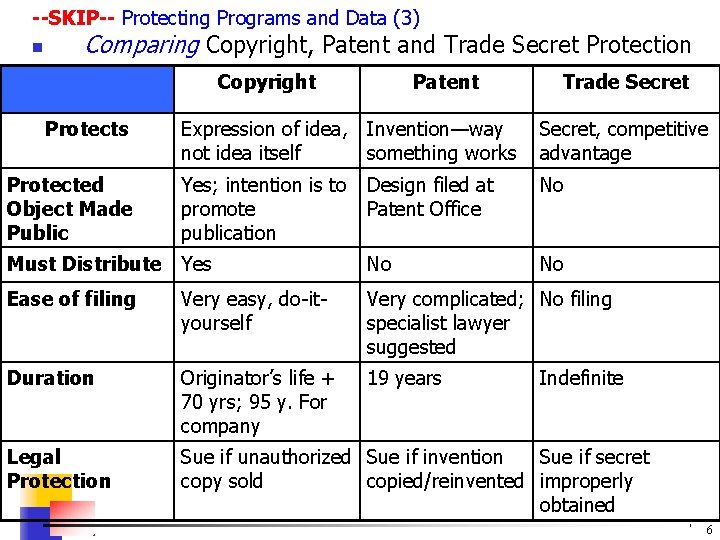
--SKIP-- Protecting Programs and Data (3) n Comparing Copyright, Patent and Trade Secret Protection © by Leszek T. Lilien, 2006 Copyright Protects Patent Trade Secret Expression of idea, Invention—way not idea itself something works Secret, competitive advantage Yes; intention is to promote publication Design filed at Patent Office No Must Distribute Yes No No Ease of filing Very easy, do-ityourself Very complicated; No filing specialist lawyer suggested Duration Originator’s life + 70 yrs; 95 y. For company 19 years Legal Protection Sue if unauthorized Sue if invention Sue if secret copy sold copied/reinvented improperly obtained Section 8 – Computer Security and Information Assurance – Spring 2006 Protected Object Made Public Indefinite 6
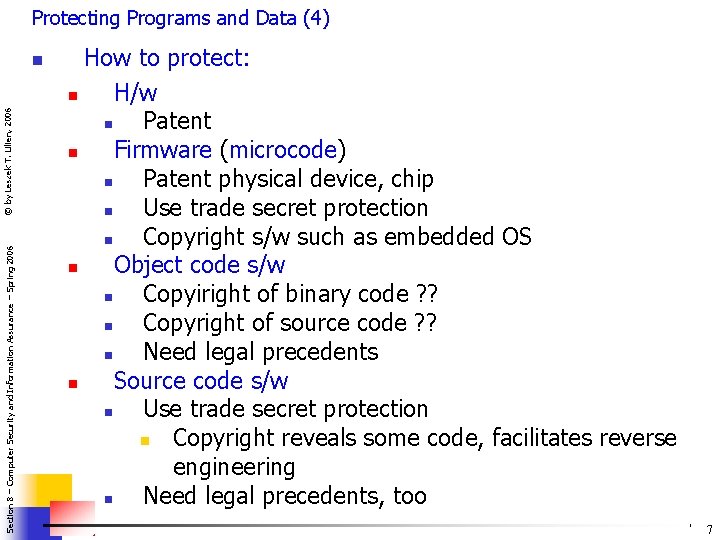
Protecting Programs and Data (4) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n How to protect: n H/w n Patent n Firmware (microcode) n Patent physical device, chip n Use trade secret protection n Copyright s/w such as embedded OS n Object code s/w n Copyiright of binary code ? ? n Copyright of source code ? ? n Need legal precedents n Source code s/w n Use trade secret protection n Copyright reveals some code, facilitates reverse engineering n Need legal precedents, too 7
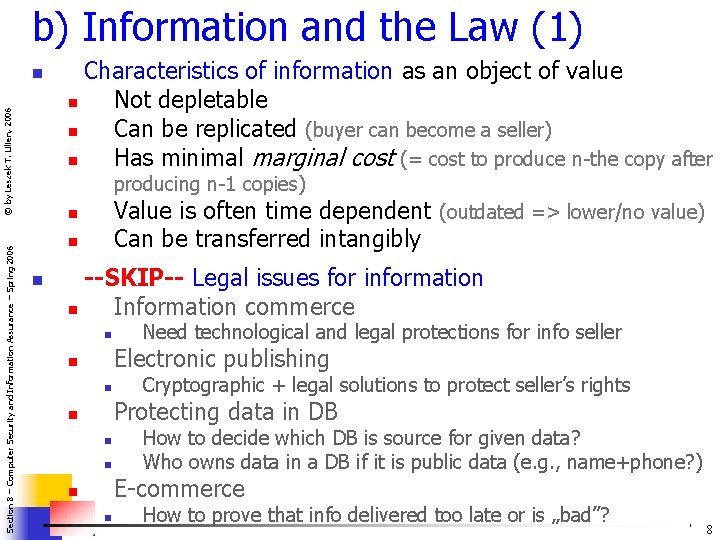
b) Information and the Law (1) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n Characteristics of information as an object of value n Not depletable n Can be replicated (buyer can become a seller) n Has minimal marginal cost (= cost to produce n-the copy after producing n-1 copies) Value is often time dependent (outdated => lower/no value) Can be transferred intangibly n n n --SKIP-- Legal issues for information n Information commerce n Need technological and legal protections for info seller Electronic publishing n n Cryptographic + legal solutions to protect seller’s rights Protecting data in DB n n n How to decide which DB is source for given data? Who owns data in a DB if it is public data (e. g. , name+phone? ) E-commerce n n How to prove that info delivered too late or is „bad”? 8
b) Information and the Law (2) Copyright, patents, trade secrets cover some (not all!) protection needs Remaining protection needs can use law mechanisms discussed below © by Leszek T. Lilien, 2006 n n Section 8 – Computer Security and Information Assurance – Spring 2006 n Building precedents or contributing to legislating new laws Law categories: 1) Criminal Law / Statutory Law 2) Civil Law (I hope I’m right iwith these subcategories) 2 a) Common Law / Tort Law 2 b) Contracts 9
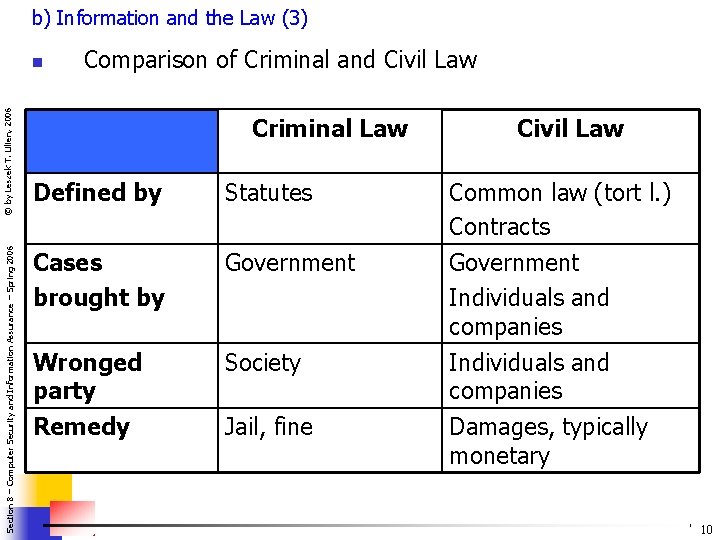
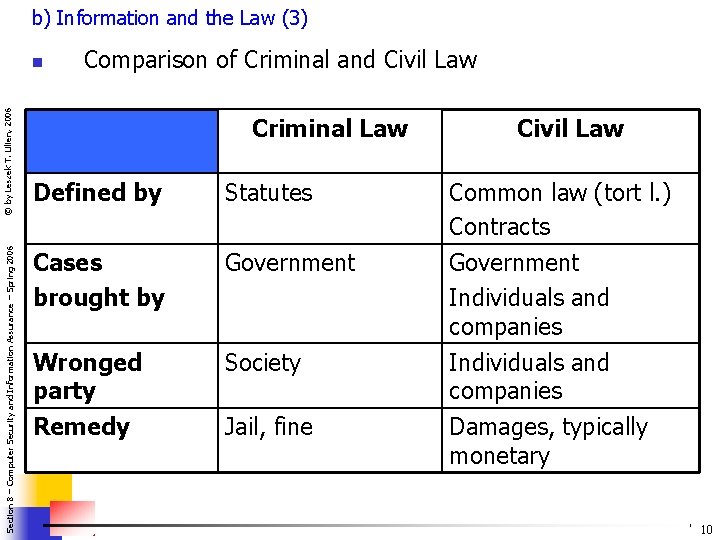
b) Information and the Law (3) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n Comparison of Criminal and Civil Law Criminal Law Civil Law Defined by Statutes Common law (tort l. ) Contracts Cases brought by Government Individuals and companies Wronged party Remedy Society Individuals and companies Damages, typically monetary Jail, fine 10

Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 c) Ownership Rights of Employees and Employers (1) Ownership rights are computer security issue n Concerned with protecting secrecy (confidentiality) and integrity of works produced by employees of an employer n n Ownership issues in emploee/employer relations: n Ownership of products n Products/ideas/inventions developed by employee after hours might still be owned by her employer n Esp. if in the same „line of business” Ownership of patents n n If employer files for patent, employer (not employee—inventor) will own patent Ownership of copyrights n n Similar to patents Trade secret protection n n No registered inventor/author—owner can prosecute for damages 11
Ownership Rights of Employees and Employers (2) Type of employment has ownership consequences n Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n n Work for hire n All work done by employee is owned by employer Employment contracts n Often spell out ownership rights n n Often includes agreement not to compete (for some time after termination) n Non-competition is not always enforceable by law Licenses n Programmer retains full ownership of developed s/w n Grants license for a fee 12
d) Software Failures (& Customers) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 (1) n --SKIP-- Issue 1: Software quality: is it „correct” or not? n If not correct: ask for refund, replacement, fixing n Refund: possible n Replacement: if this copy damaged, or improved in the meantine n Fixing: rarely legally enforced; instead, monetary awards for damages n Correctness of s/w difficult to define/enforce legally n Individual can rarely sue a major s/w vendor n Prohibitive costs for individual 13
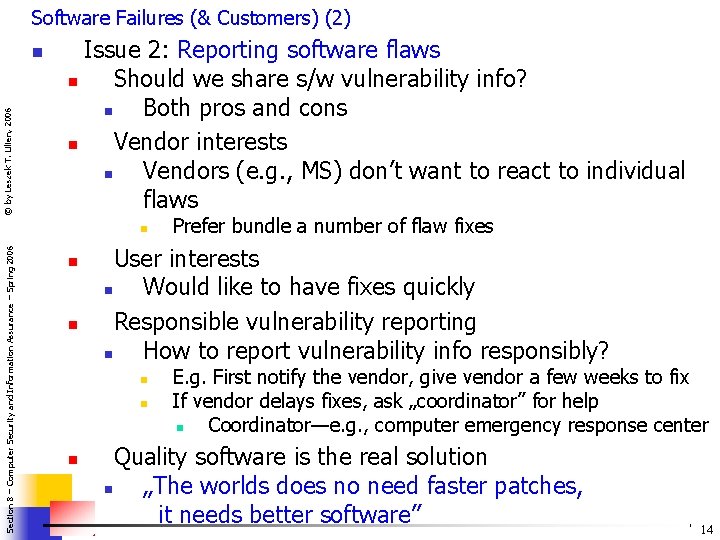
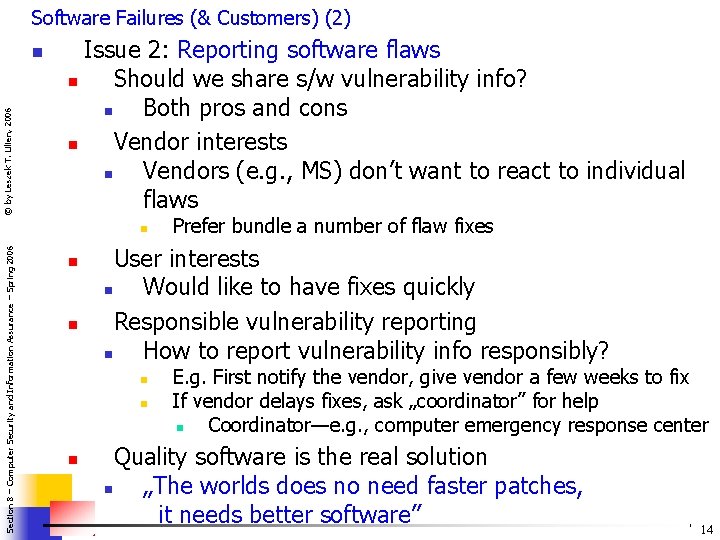
Software Failures (& Customers) (2) © by Leszek T. Lilien, 2006 n Issue 2: Reporting software flaws n Should we share s/w vulnerability info? n Both pros and cons n Vendor interests n Vendors (e. g. , MS) don’t want to react to individual flaws Section 8 – Computer Security and Information Assurance – Spring 2006 n n n User interests n Would like to have fixes quickly Responsible vulnerability reporting n How to report vulnerability info responsibly? n n n Prefer bundle a number of flaw fixes E. g. First notify the vendor, give vendor a few weeks to fix If vendor delays fixes, ask „coordinator” for help n Coordinator—e. g. , computer emergency response center Quality software is the real solution n „The worlds does no need faster patches, it needs better software” 14
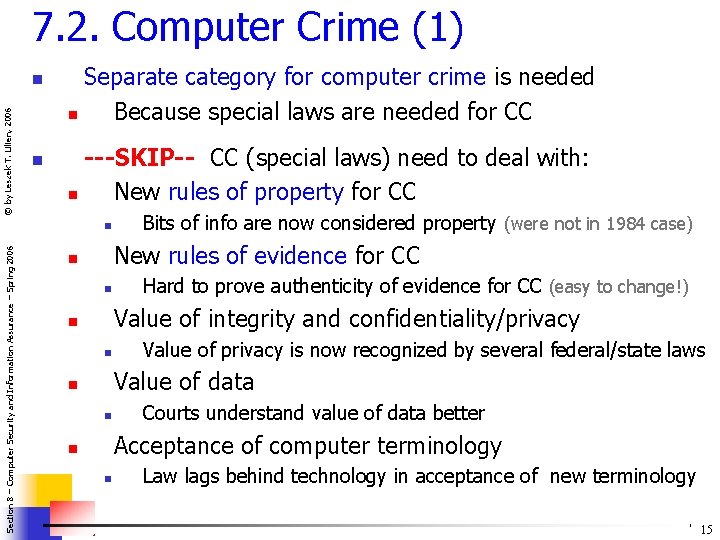
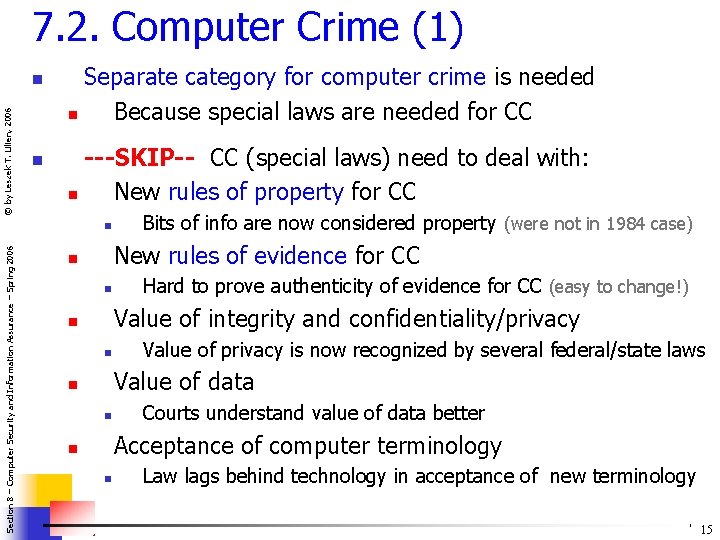
7. 2. Computer Crime (1) © by Leszek T. Lilien, 2006 n n Separate category for computer crime is needed n Because special laws are needed for CC ---SKIP-- CC (special laws) need to deal with: n New rules of property for CC Section 8 – Computer Security and Information Assurance – Spring 2006 n Bits of info are now considered property (were not in 1984 case) New rules of evidence for CC n n Hard to prove authenticity of evidence for CC (easy to change!) Value of integrity and confidentiality/privacy n n Value of privacy is now recognized by several federal/state laws Value of data n n Courts understand value of data better Acceptance of computer terminology n n Law lags behind technology in acceptance of new terminology 15
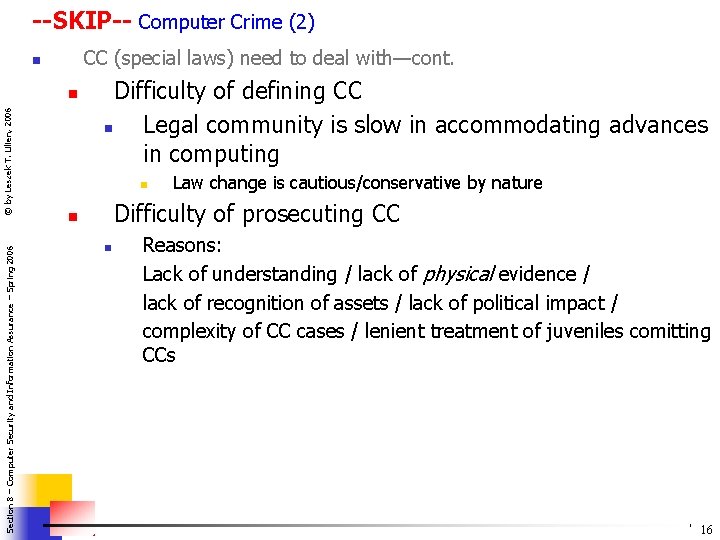
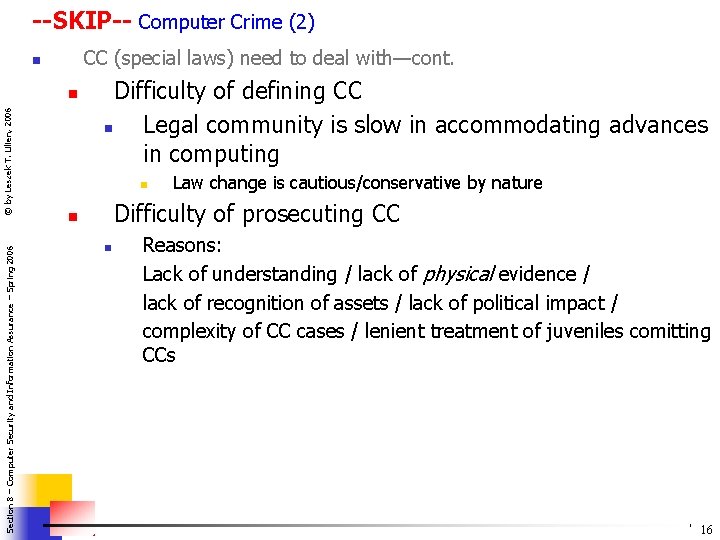
--SKIP-- Computer Crime (2) CC (special laws) need to deal with—cont. n Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n Difficulty of defining CC n Legal community is slow in accommodating advances in computing n Law change is cautious/conservative by nature Difficulty of prosecuting CC n n Reasons: Lack of understanding / lack of physical evidence / lack of recognition of assets / lack of political impact / complexity of CC cases / lenient treatment of juveniles comitting CCs 16
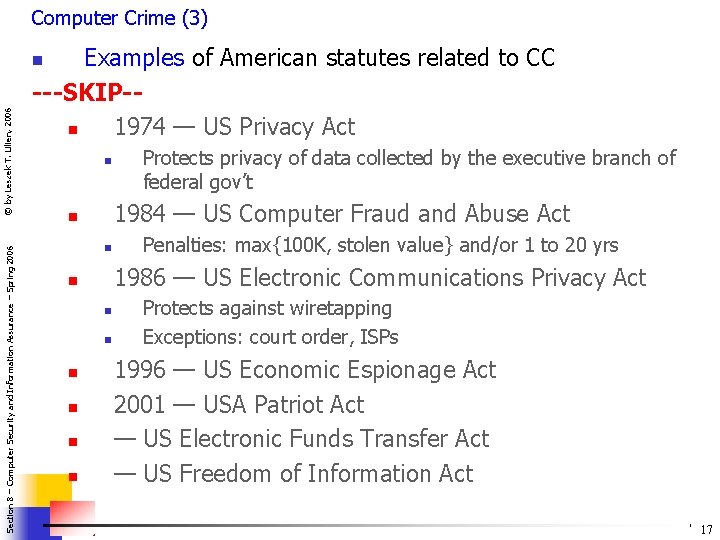
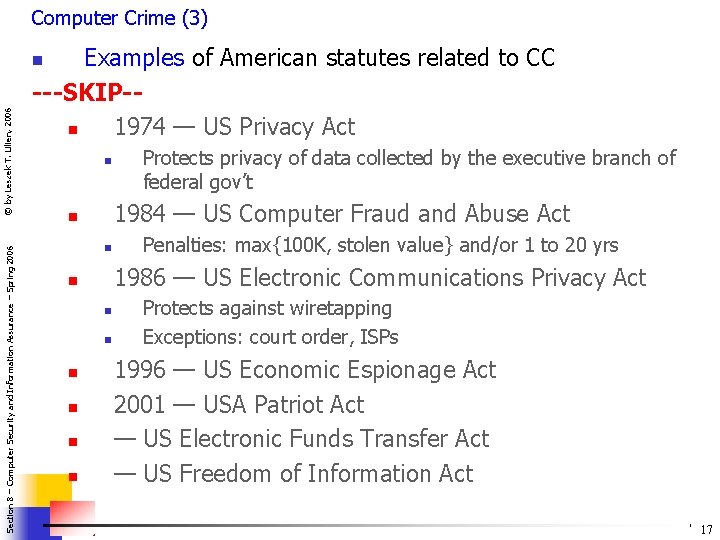
Computer Crime (3) Examples of American statutes related to CC ---SKIP-n 1974 — US Privacy Act Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n n 1984 — US Computer Fraud and Abuse Act n n n n Penalties: max{100 K, stolen value} and/or 1 to 20 yrs 1986 — US Electronic Communications Privacy Act n n Protects privacy of data collected by the executive branch of federal gov’t Protects against wiretapping Exceptions: court order, ISPs 1996 — US Economic Espionage Act 2001 — USA Patriot Act — US Electronic Funds Transfer Act — US Freedom of Information Act 17
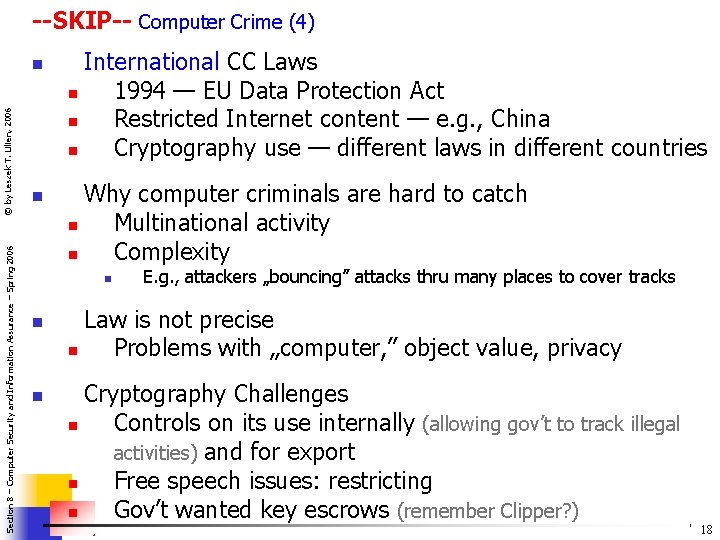
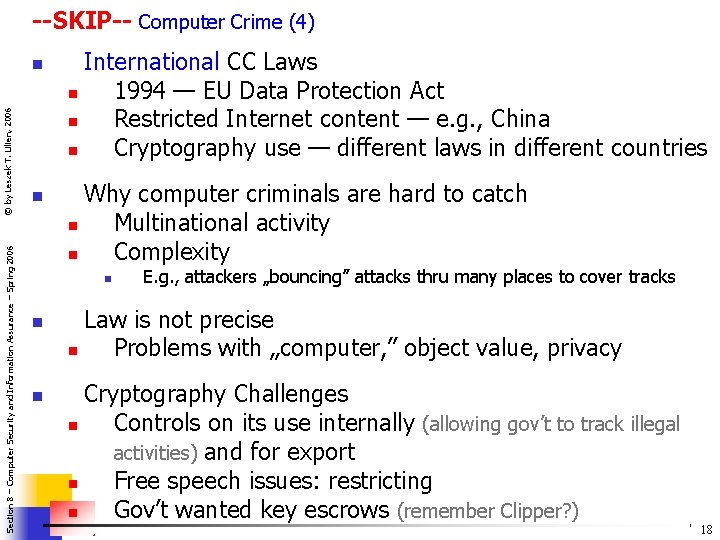
--SKIP-- Computer Crime (4) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n n International CC Laws n 1994 — EU Data Protection Act n Restricted Internet content — e. g. , China n Cryptography use — different laws in different countries Why computer criminals are hard to catch n Multinational activity n Complexity n n n E. g. , attackers „bouncing” attacks thru many places to cover tracks Law is not precise n Problems with „computer, ” object value, privacy Cryptography Challenges n Controls on its use internally (allowing gov’t to track illegal activities) and for export n Free speech issues: restricting n Gov’t wanted key escrows (remember Clipper? ) 18
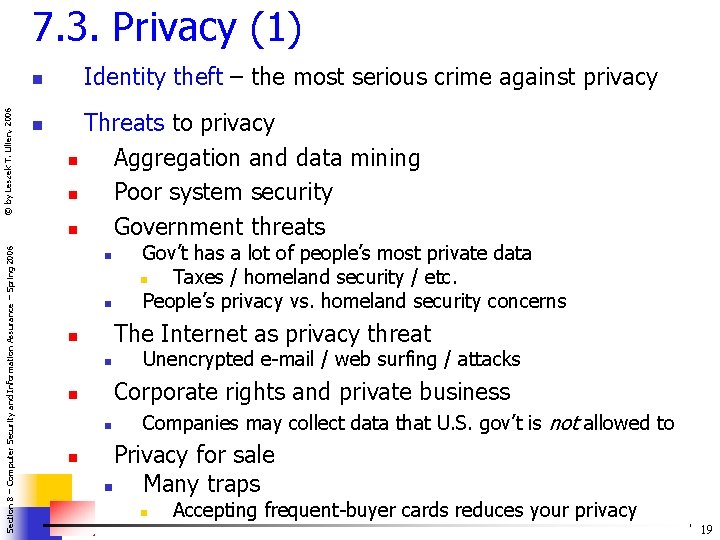
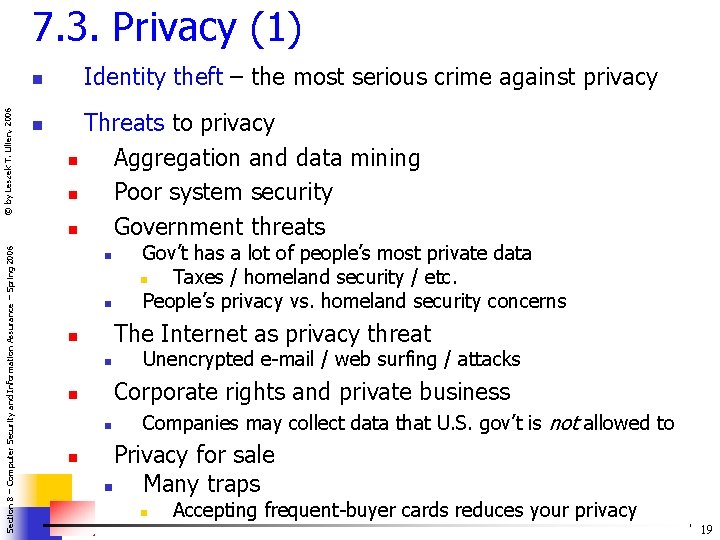
7. 3. Privacy (1) Identity theft – the most serious crime against privacy Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n n Threats to privacy n Aggregation and data mining n Poor system security n Government threats n n The Internet as privacy threat n n Unencrypted e-mail / web surfing / attacks Corporate rights and private business n n n Gov’t has a lot of people’s most private data n Taxes / homeland security / etc. People’s privacy vs. homeland security concerns Companies may collect data that U. S. gov’t is not allowed to Privacy for sale n Many traps n Accepting frequent-buyer cards reduces your privacy 19
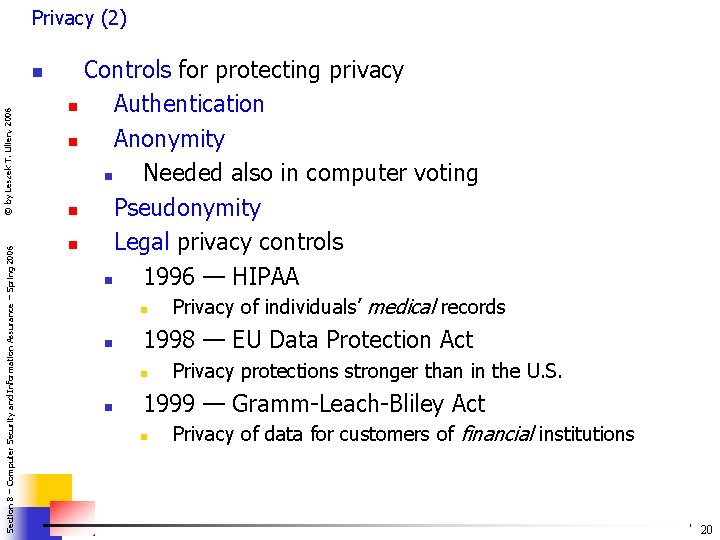
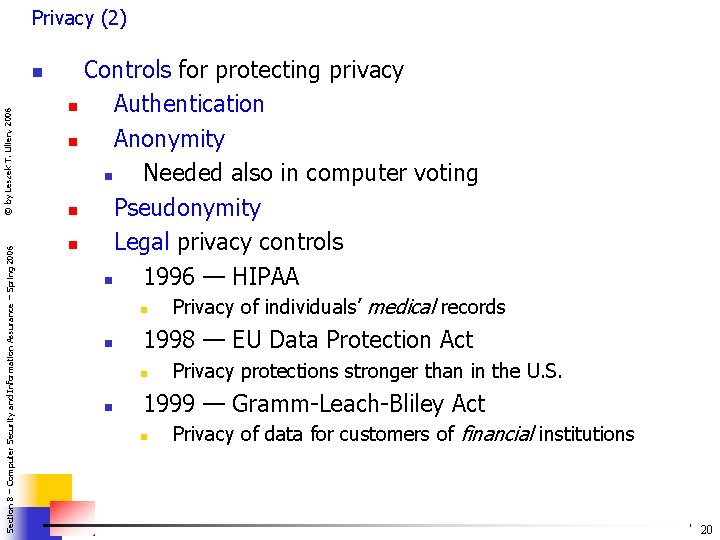
Privacy (2) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n Controls for protecting privacy n Authentication n Anonymity n Needed also in computer voting n Pseudonymity n Legal privacy controls n 1996 — HIPAA n n 1998 — EU Data Protection Act n n Privacy of individuals’ medical records Privacy protections stronger than in the U. S. 1999 — Gramm-Leach-Bliley Act n Privacy of data for customers of financial institutions 20
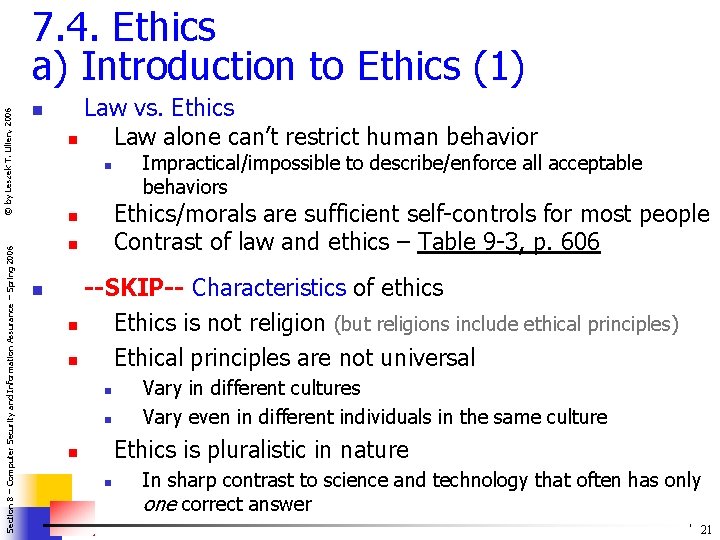
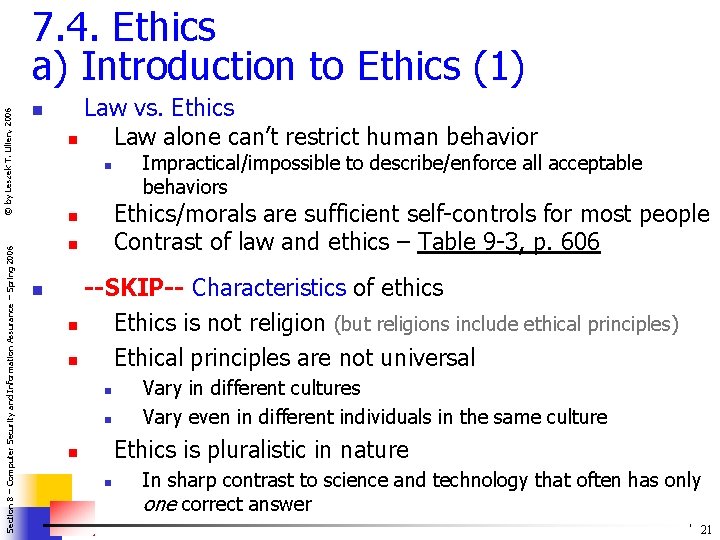
Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 7. 4. Ethics a) Introduction to Ethics (1) n Law vs. Ethics n Law alone can’t restrict human behavior n Ethics/morals are sufficient self-controls for most people Contrast of law and ethics – Table 9 -3, p. 606 n n n Impractical/impossible to describe/enforce all acceptable behaviors --SKIP-- Characteristics of ethics n Ethics is not religion (but religions include ethical principles) n Ethical principles are not universal n n Vary in different cultures Vary even in different individuals in the same culture Ethics is pluralistic in nature n n In sharp contrast to science and technology that often has only one correct answer 21
--SKIP-- Introduction to Ethics (2) Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n Systems of ethics 1) Consequence-based — do what results in greatest good, least harm 1 a) Egoism I do what’s good for me 1 b) Utilitarianism I do what’s brings greatest collective good 2) Rules-based (deontology) — do what is prescribed by certain universal, self-evident, natural rules of proper conduct Could be based on religion on philosophy 22
--SKIP-- Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n b) Case Studies of Ethics Read especially: n Case II: Privacy rights (p. 612) n Case VIII: Ethics of Hacking or Cracking (p. 619) 23
c) Codes of Professional Ethics Different codes of professional ethics Section 8 – Computer Security and Information Assurance – Spring 2006 © by Leszek T. Lilien, 2006 n n Computer Ethics Institute n 10 Commandments of Computer Use – Fig. 9. 3, p. 625 n IEEE – Fig. 9 -1, p. 623 n ACM – Fig. 9 -2, p. 624 24
Section 8 – Computer Security and Information Assurance – Spring 2006 End of Section 7 (Ch. 9) 25 © by Leszek T. Lilien, 2006