CS 519419 Cyber Attacks Defense Yeongjin Jang 092718
CS 519/419 Cyber Attacks & Defense Yeongjin Jang 09/27/18
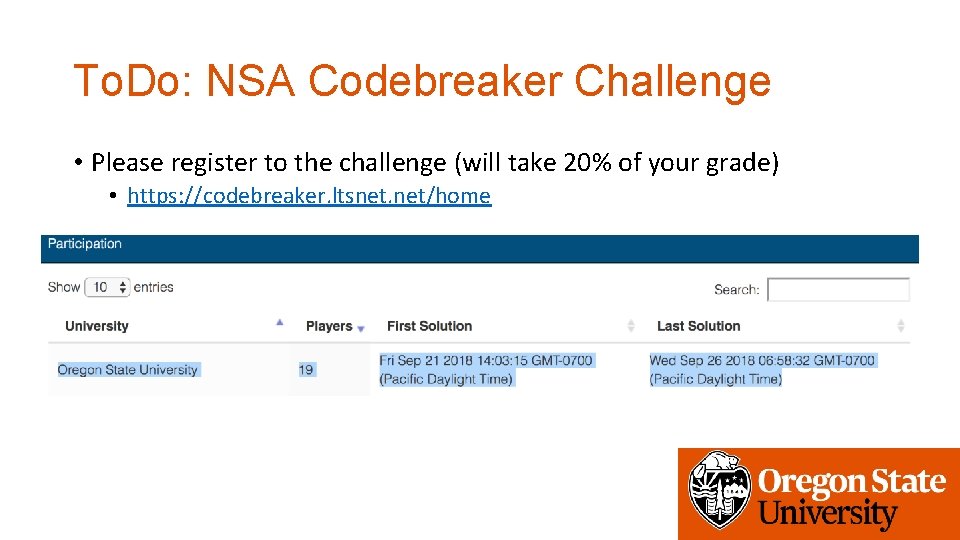
To. Do: NSA Codebreaker Challenge • Please register to the challenge (will take 20% of your grade) • https: //codebreaker. ltsnet. net/home
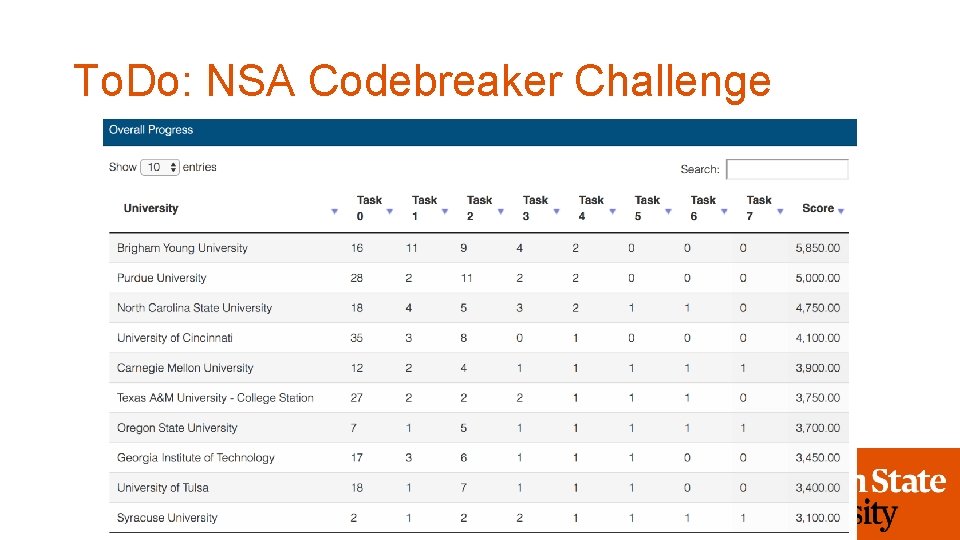
To. Do: NSA Codebreaker Challenge
To. DO: NSA Codebreaker Challenge • For those who do not wish to participate this challenge: • Please let me know before 10/09 • No later than this date. • You will get a set of five additional challenges for 20% credits
Updated Challenge Descriptions
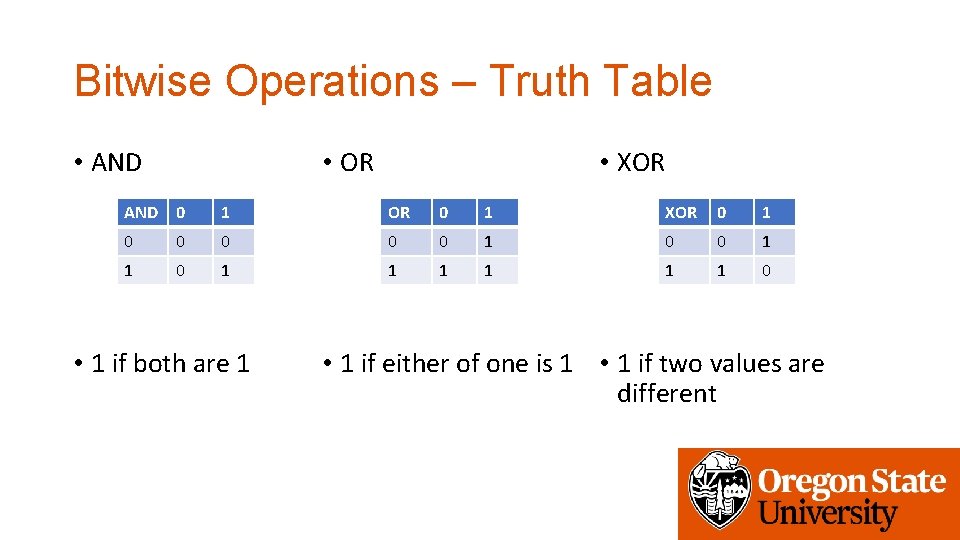
Bitwise Operations – Truth Table • AND • OR • XOR AND 0 1 OR 0 1 XOR 0 1 0 0 1 1 1 1 0 • 1 if both are 1 • 1 if either of one is 1 • 1 if two values are different
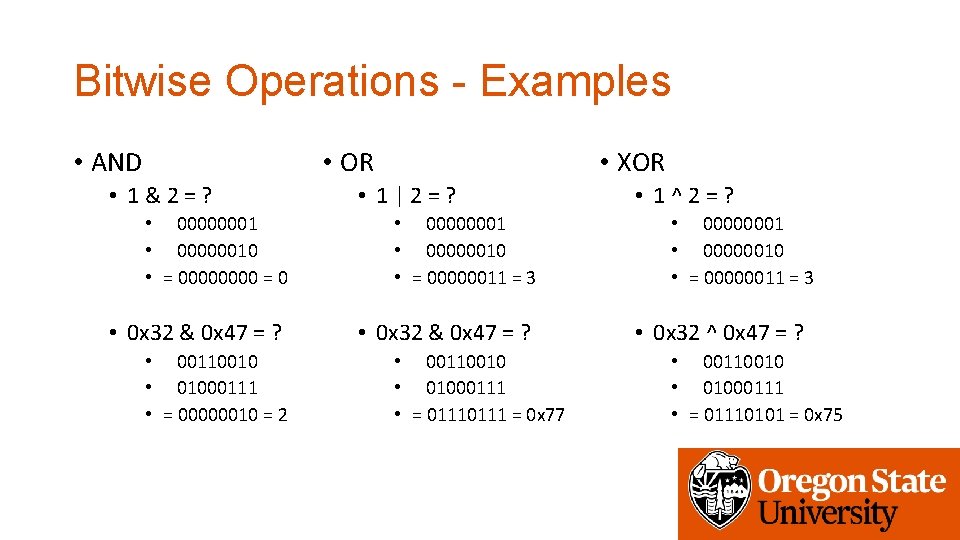
Bitwise Operations - Examples • AND • OR • 1&2=? • XOR • 1|2=? • 00000001 • 00000010 • = 0000 = 0 • 00000001 • 00000010 • = 00000011 = 3 • 0 x 32 & 0 x 47 = ? • 00110010 • 01000111 • = 00000010 = 2 • 00110010 • 01000111 • = 0111 = 0 x 77 • 1^2=? • 00000001 • 00000010 • = 00000011 = 3 • 0 x 32 ^ 0 x 47 = ? • 00110010 • 01000111 • = 01110101 = 0 x 75
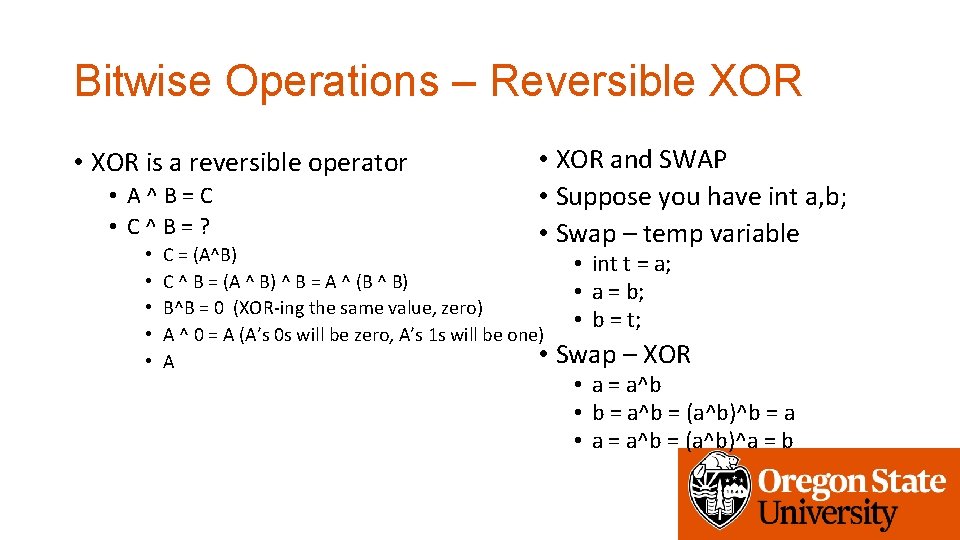
Bitwise Operations – Reversible XOR • XOR is a reversible operator • A^B=C • C^B=? • • • XOR and SWAP • Suppose you have int a, b; • Swap – temp variable C = (A^B) C ^ B = (A ^ B) ^ B = A ^ (B ^ B) B^B = 0 (XOR-ing the same value, zero) A ^ 0 = A (A’s 0 s will be zero, A’s 1 s will be one) • A • int t = a; • a = b; • b = t; Swap – XOR • a = a^b • b = a^b = (a^b)^b = a • a = a^b = (a^b)^a = b
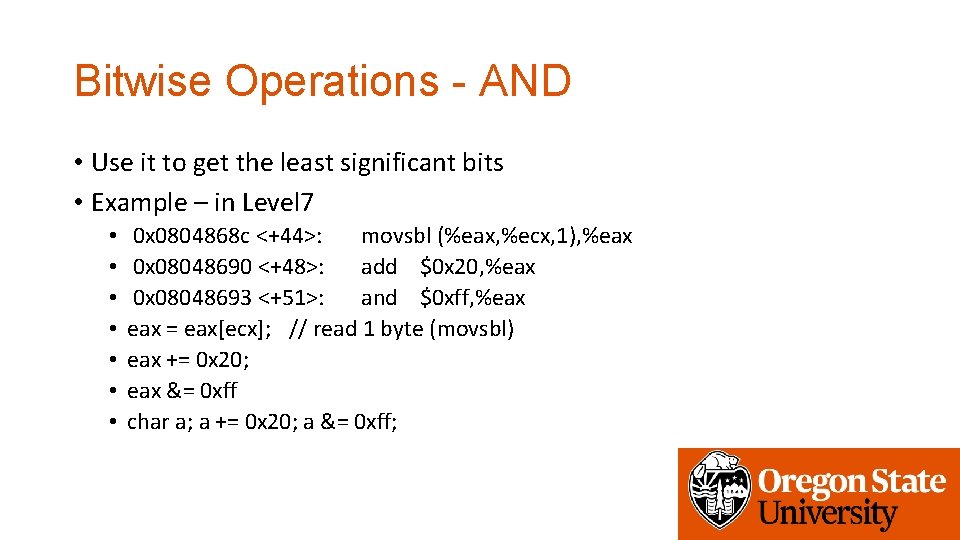
Bitwise Operations - AND • Use it to get the least significant bits • Example – in Level 7 • • 0 x 0804868 c <+44>: movsbl (%eax, %ecx, 1), %eax 0 x 08048690 <+48>: add $0 x 20, %eax 0 x 08048693 <+51>: and $0 xff, %eax = eax[ecx]; // read 1 byte (movsbl) eax += 0 x 20; eax &= 0 xff char a; a += 0 x 20; a &= 0 xff;
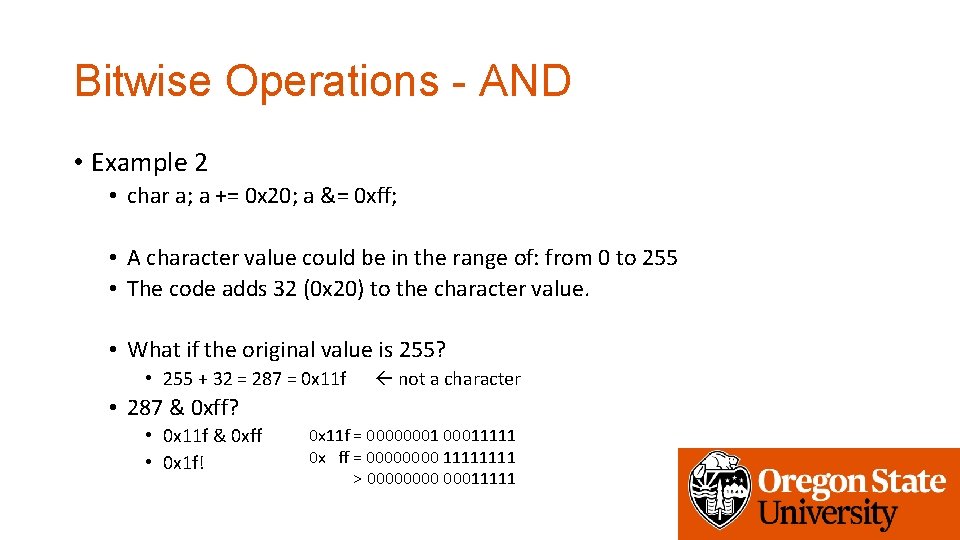
Bitwise Operations - AND • Example 2 • char a; a += 0 x 20; a &= 0 xff; • A character value could be in the range of: from 0 to 255 • The code adds 32 (0 x 20) to the character value. • What if the original value is 255? • 255 + 32 = 287 = 0 x 11 f not a character • 287 & 0 xff? • 0 x 11 f & 0 xff • 0 x 1 f! 0 x 11 f = 000000011111 0 x ff = 0000 1111 > 0000 00011111
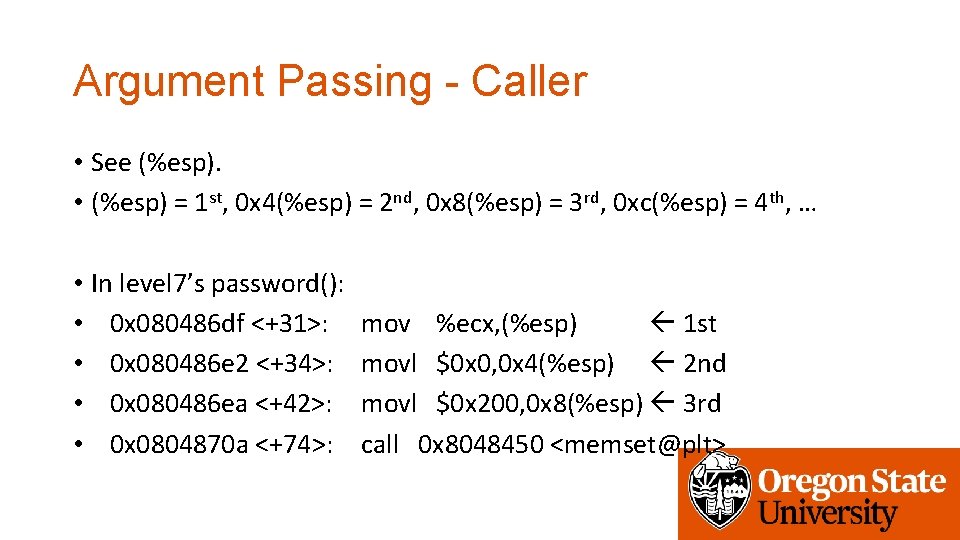
Argument Passing - Caller • See (%esp). • (%esp) = 1 st, 0 x 4(%esp) = 2 nd, 0 x 8(%esp) = 3 rd, 0 xc(%esp) = 4 th, … • In level 7’s password(): • 0 x 080486 df <+31>: • 0 x 080486 e 2 <+34>: • 0 x 080486 ea <+42>: • 0 x 0804870 a <+74>: mov %ecx, (%esp) 1 st movl $0 x 0, 0 x 4(%esp) 2 nd movl $0 x 200, 0 x 8(%esp) 3 rd call 0 x 8048450 <memset@plt>
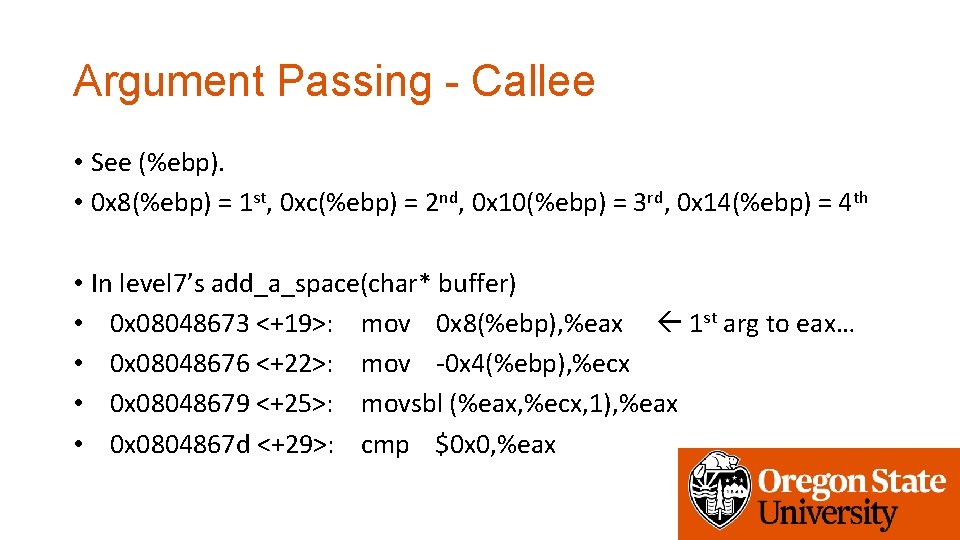
Argument Passing - Callee • See (%ebp). • 0 x 8(%ebp) = 1 st, 0 xc(%ebp) = 2 nd, 0 x 10(%ebp) = 3 rd, 0 x 14(%ebp) = 4 th • In level 7’s add_a_space(char* buffer) • 0 x 08048673 <+19>: mov 0 x 8(%ebp), %eax 1 st arg to eax… • 0 x 08048676 <+22>: mov -0 x 4(%ebp), %ecx • 0 x 08048679 <+25>: movsbl (%eax, %ecx, 1), %eax • 0 x 0804867 d <+29>: cmp $0 x 0, %eax
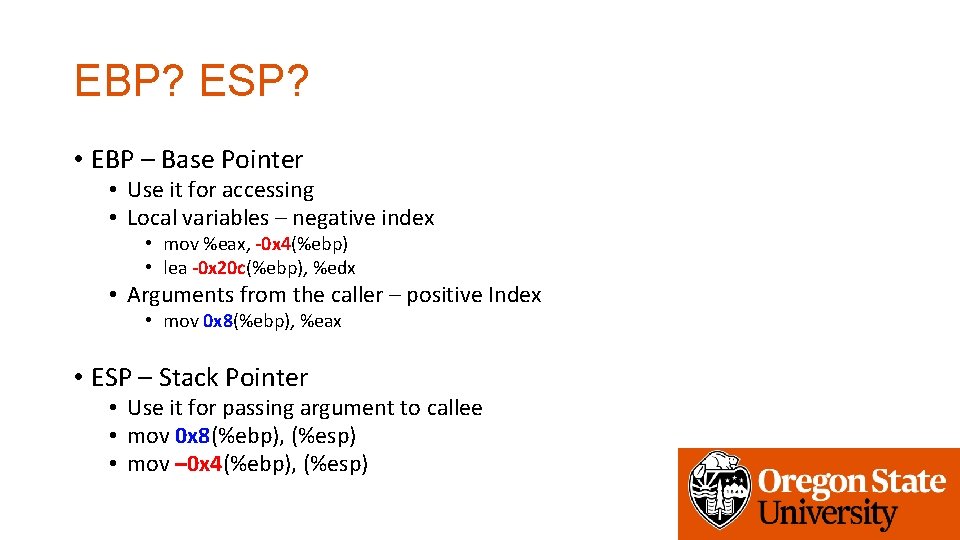
EBP? ESP? • EBP – Base Pointer • Use it for accessing • Local variables – negative index • mov %eax, -0 x 4(%ebp) • lea -0 x 20 c(%ebp), %edx • Arguments from the caller – positive Index • mov 0 x 8(%ebp), %eax • ESP – Stack Pointer • Use it for passing argument to callee • mov 0 x 8(%ebp), (%esp) • mov – 0 x 4(%ebp), (%esp)
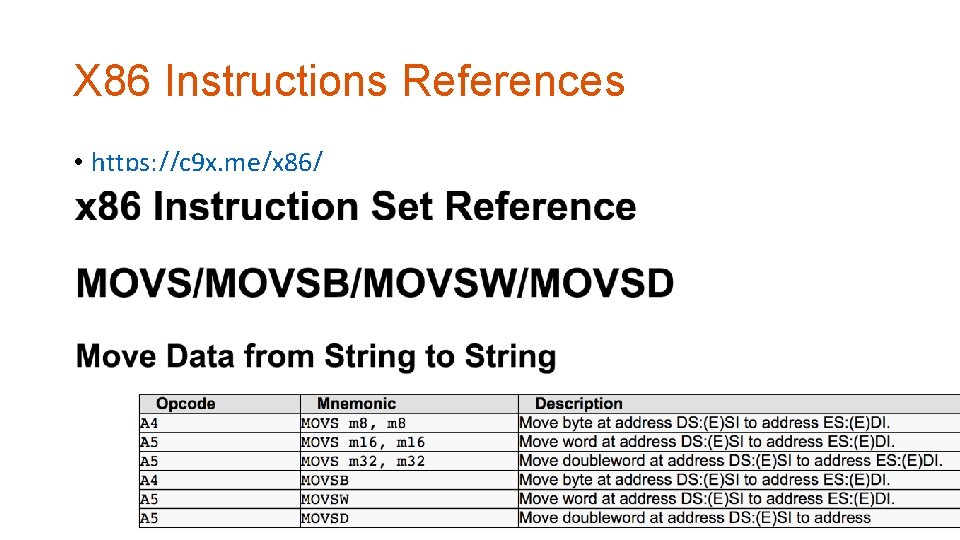
X 86 Instructions References • https: //c 9 x. me/x 86/
![Integer Division Operation • idiv [value] • • Use 64 bit integer (EDX: EAX) Integer Division Operation • idiv [value] • • Use 64 bit integer (EDX: EAX)](http://slidetodoc.com/presentation_image_h2/7b23030bb77a06933c54c77087481dea/image-15.jpg)
Integer Division Operation • idiv [value] • • Use 64 bit integer (EDX: EAX) Calls cdq / cltd instruction first (asserting using EDX: EAX as one 64 bit integer) Divide EDX: EAX with [value] Store Quotient at EAX, Remainter in EDX
![Integer Division Operation • idiv [value] • • Use 64 bit integer (EDX: EAX) Integer Division Operation • idiv [value] • • Use 64 bit integer (EDX: EAX)](http://slidetodoc.com/presentation_image_h2/7b23030bb77a06933c54c77087481dea/image-16.jpg)
Integer Division Operation • idiv [value] • • Use 64 bit integer (EDX: EAX) Calls cdq / cltd instruction first (asserting using EDX: EAX as one 64 bit integer) Divide EDX: EAX with [value] Store Quotient at EAX, Remainder in EDX • Example – in level 9, check(int value) • • • 0 x 08048670 <+32>: 0 x 08048673 <+35>: 0 x 08048676 <+38>: 0 x 08048677 <+39>: 0 x 0804867 e <+46>: mov cltd idivl cmp 0 x 8(%ebp), %eax -0 x 8(%ebp), %ecx 0 x 804 a 02 c(, %ecx, 4) $0 x 0, %edx eax is arg 1 ecx is loop index use edx: eax, int 64 divide array[ecx]/eax Remainder… • Comparing the remainder of array[i] / value to zero… • if(array[i] % value == 0)
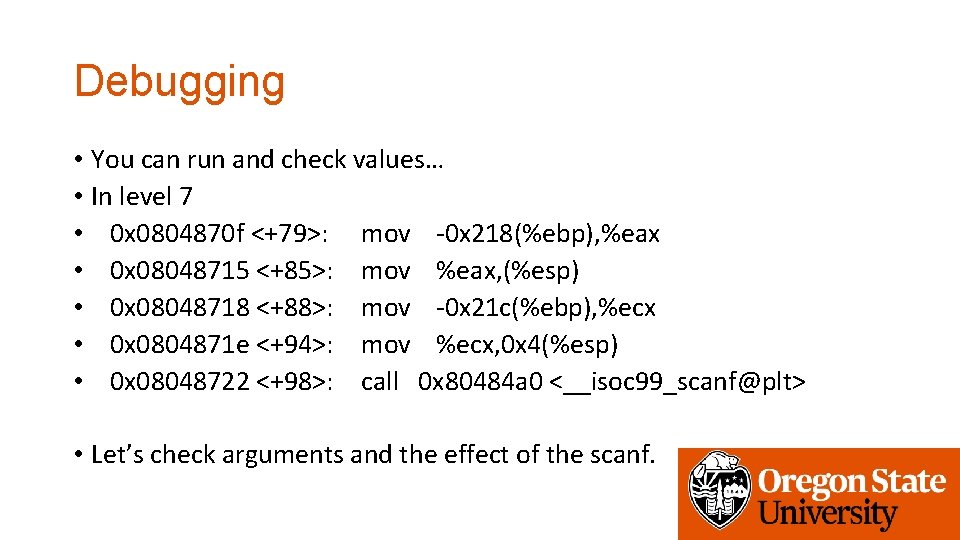
Debugging • You can run and check values… • In level 7 • 0 x 0804870 f <+79>: mov -0 x 218(%ebp), %eax • 0 x 08048715 <+85>: mov %eax, (%esp) • 0 x 08048718 <+88>: mov -0 x 21 c(%ebp), %ecx • 0 x 0804871 e <+94>: mov %ecx, 0 x 4(%esp) • 0 x 08048722 <+98>: call 0 x 80484 a 0 <__isoc 99_scanf@plt> • Let’s check arguments and the effect of the scanf.
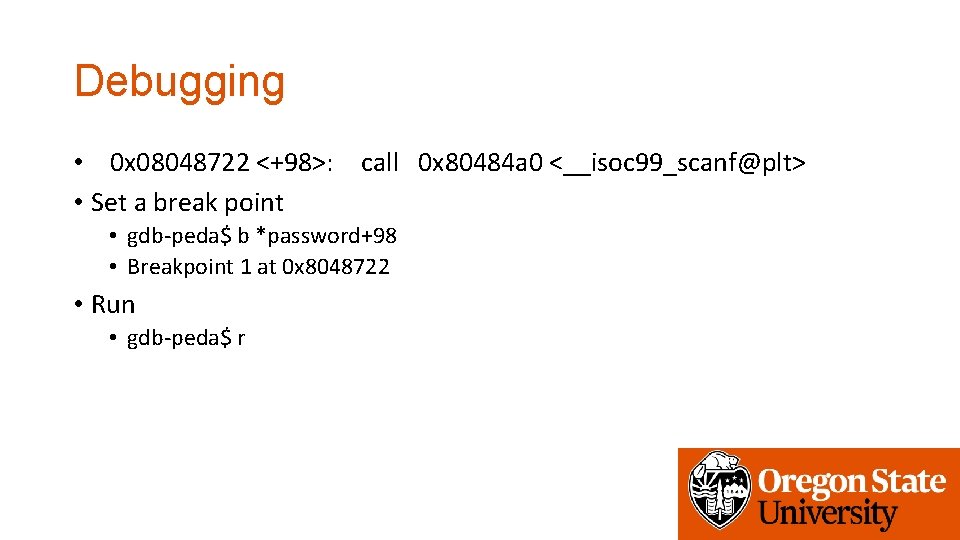
Debugging • 0 x 08048722 <+98>: call 0 x 80484 a 0 <__isoc 99_scanf@plt> • Set a break point • gdb-peda$ b *password+98 • Breakpoint 1 at 0 x 8048722 • Run • gdb-peda$ r
Debug You can also see regs. Values. . Stopped before the call 1 st arg 2 nd arg
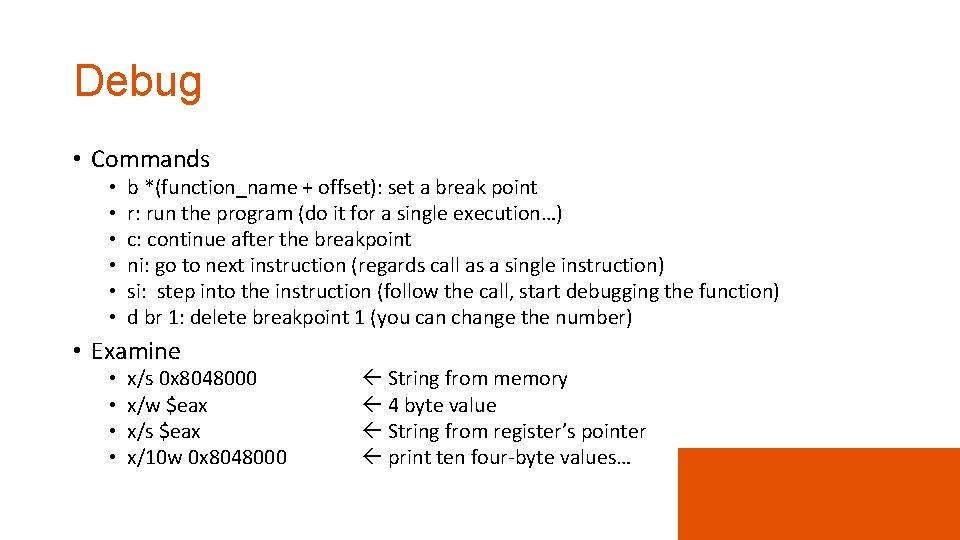
Debug • Commands • • • b *(function_name + offset): set a break point r: run the program (do it for a single execution…) c: continue after the breakpoint ni: go to next instruction (regards call as a single instruction) si: step into the instruction (follow the call, start debugging the function) d br 1: delete breakpoint 1 (you can change the number) • Examine • • x/s 0 x 8048000 x/w $eax x/s $eax x/10 w 0 x 8048000 String from memory 4 byte value String from register’s pointer print ten four-byte values…
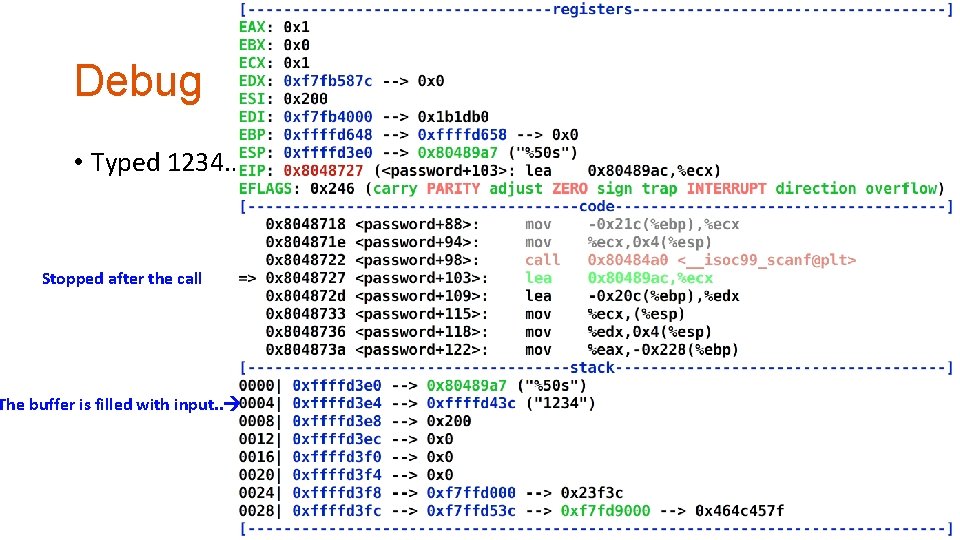
Debug • Typed 1234. . Stopped after the call The buffer is filled with input. .
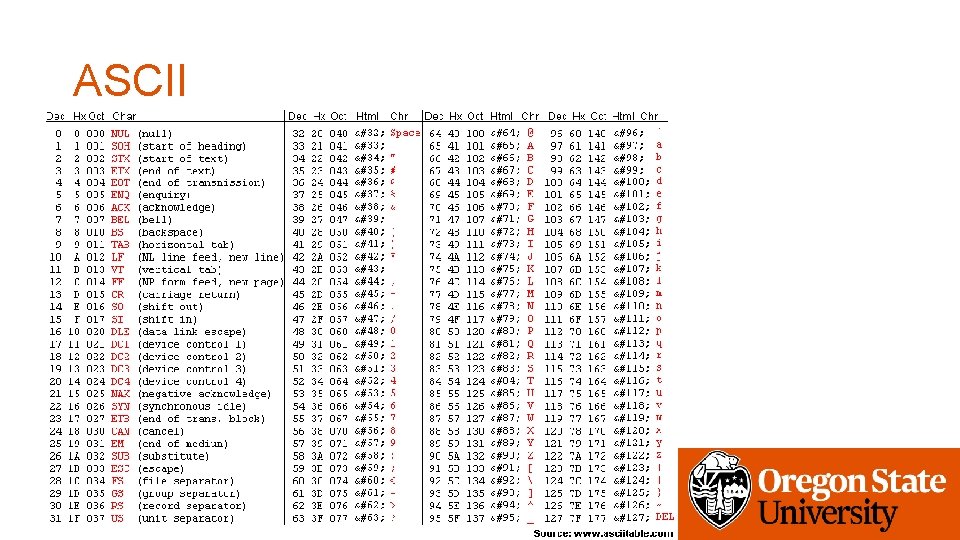
ASCII
- Slides: 22