CS 519419 Cyber Attacks Defense Yeongjin Jang 012318
CS 519/419 Cyber Attacks & Defense Yeongjin Jang 01/23/18
Notice • Week-1 deadline passed • If VM does not works for you, please use the vm-ctf 1 server • Piazza is up • https: //piazza. com/class/jc 9 wsr 9 swhl 1 bf
Project • Project Proposal • Deadline 2/14 Wed - to have enough time (~4 weeks) to finish the project • You can build a team up to 3 members • Please come to the office hour to discuss the topic • Topics • • Bug finding Vulnerability analysis Wargame solving Etc. • You will present the result either on 3/13 or 3/15
Assignment Week-2 • stack-quiz • stack-ovfl • frame-pointer • one-off • weird-main (x 2 points)
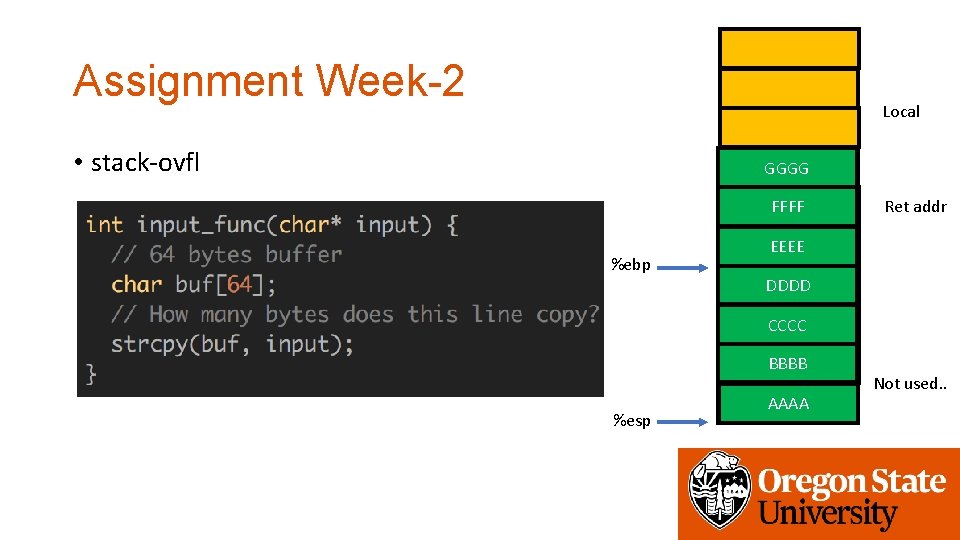
Assignment Week-2 Local • stack-ovfl GGGG FFFF 0 x 80484 e 8 %ebp Ret addr Saved EEEEebp DDDD CCCC BBBB %esp AAAA Not used. .
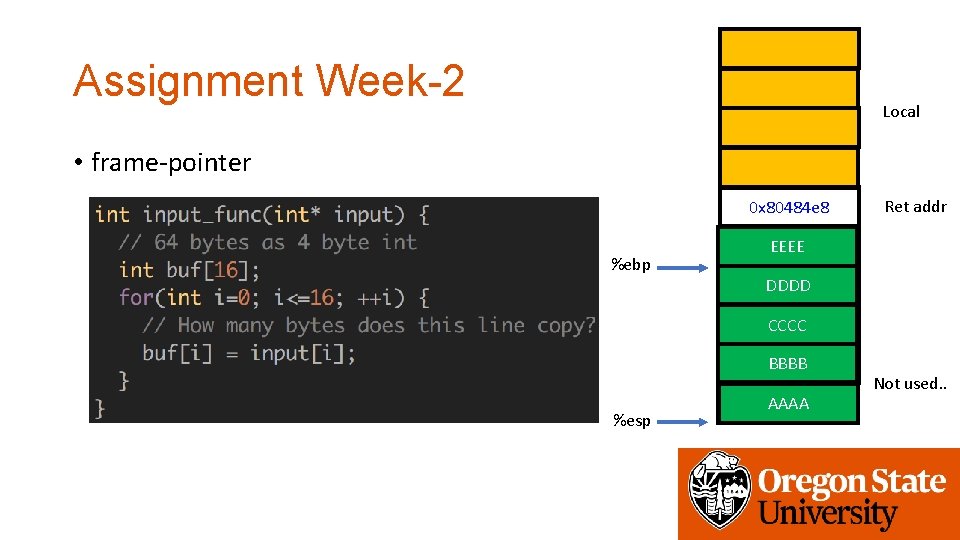
Assignment Week-2 Local • frame-pointer 0 x 80484 e 8 %ebp Ret addr Saved EEEEebp DDDD CCCC BBBB %esp AAAA Not used. .
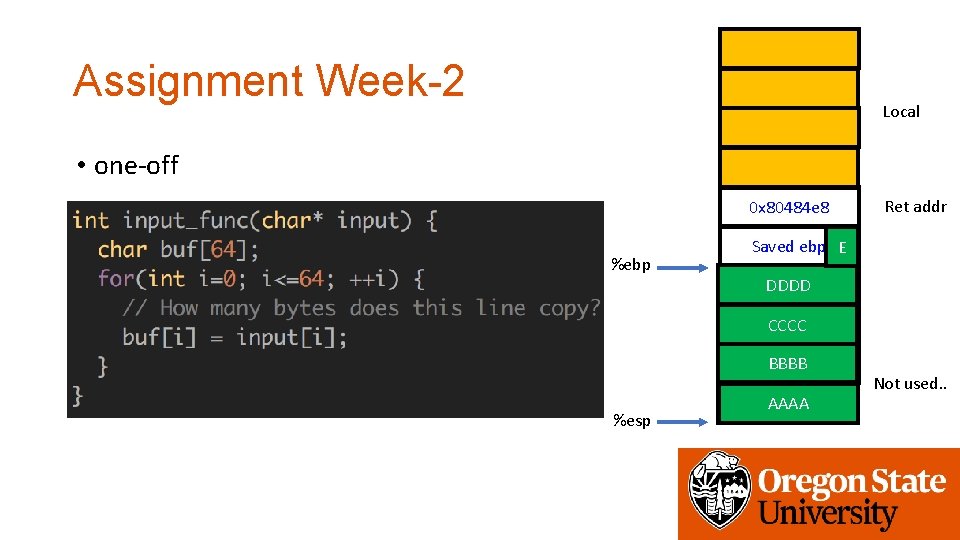
Assignment Week-2 Local • one-off 0 x 80484 e 8 %ebp Ret addr Saved ebp E DDDD CCCC BBBB %esp AAAA Not used. .
Assignment Week-2 Workflow • Overwrite the stack frame • Make the function incorrectly return • Change the return address • execute_me() • Prints the flag
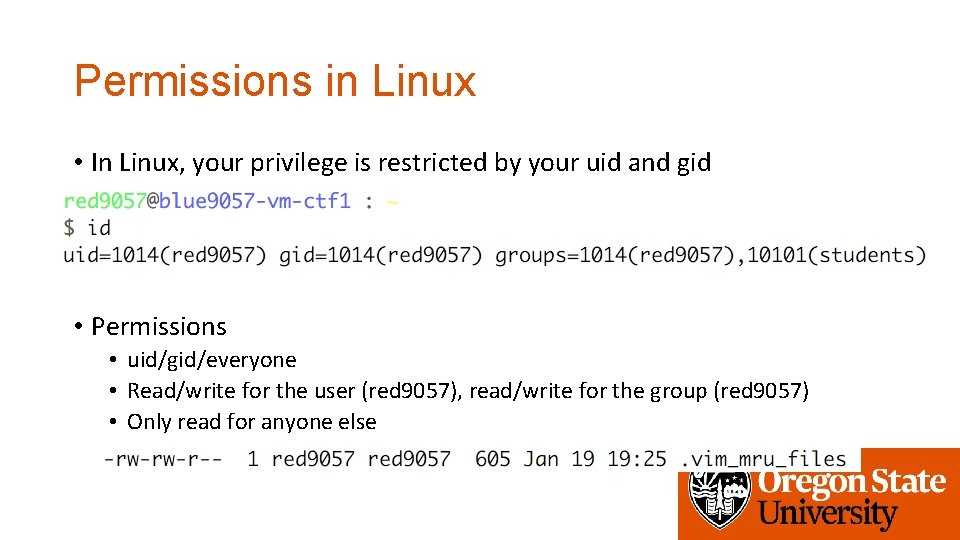
Permissions in Linux • In Linux, your privilege is restricted by your uid and gid • Permissions • uid/gid/everyone • Read/write for the user (red 9057), read/write for the group (red 9057) • Only read for anyone else
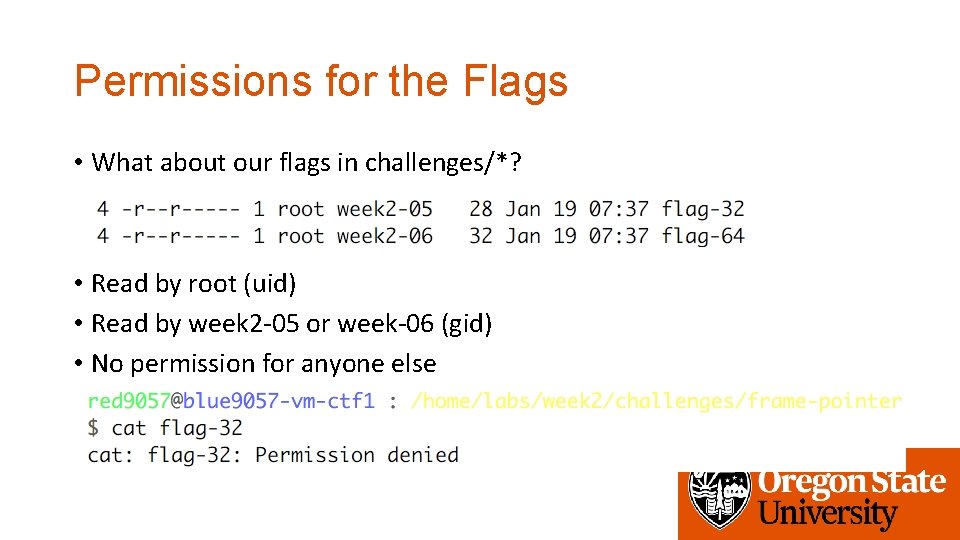
Permissions for the Flags • What about our flags in challenges/*? • Read by root (uid) • Read by week 2 -05 or week-06 (gid) • No permission for anyone else
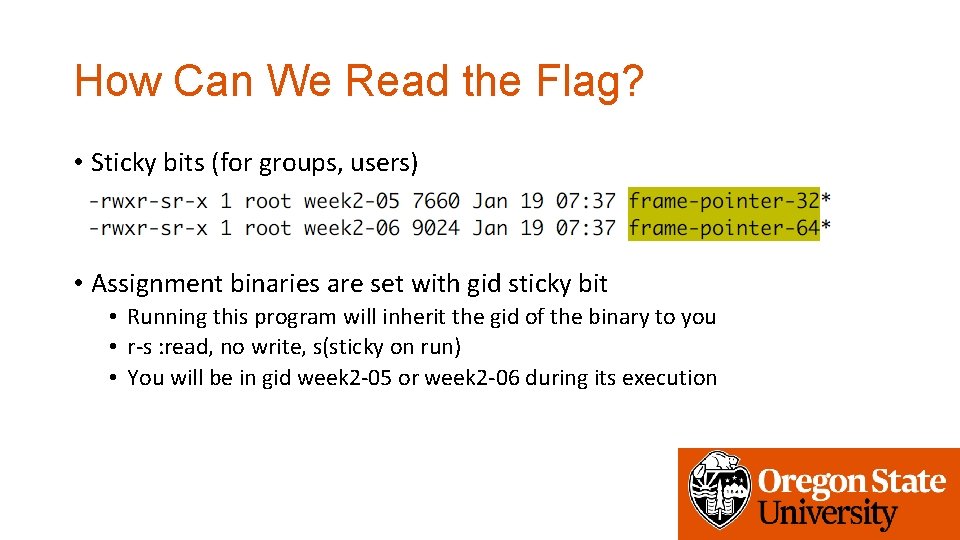
How Can We Read the Flag? • Sticky bits (for groups, users) • Assignment binaries are set with gid sticky bit • Running this program will inherit the gid of the binary to you • r-s : read, no write, s(sticky on run) • You will be in gid week 2 -05 or week 2 -06 during its execution
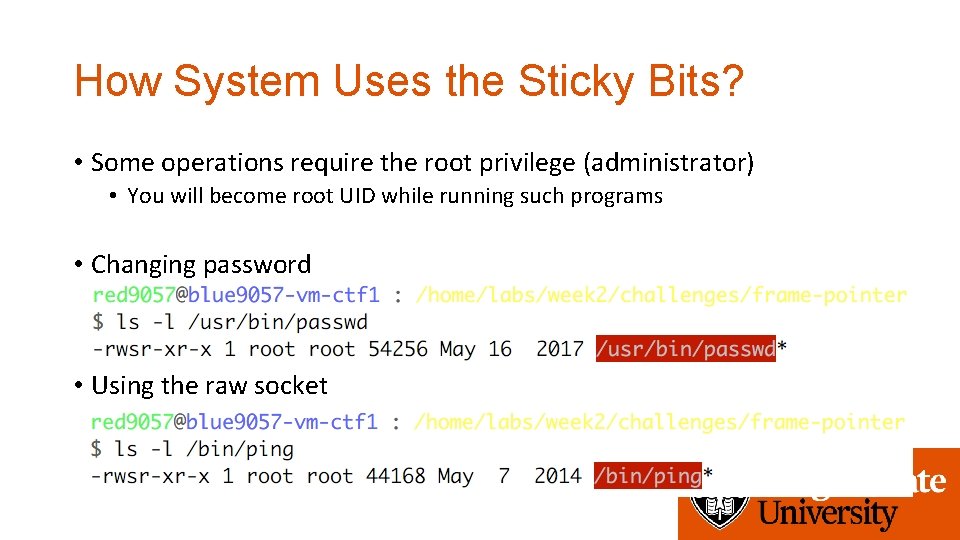
How System Uses the Sticky Bits? • Some operations require the root privilege (administrator) • You will become root UID while running such programs • Changing password • Using the raw socket
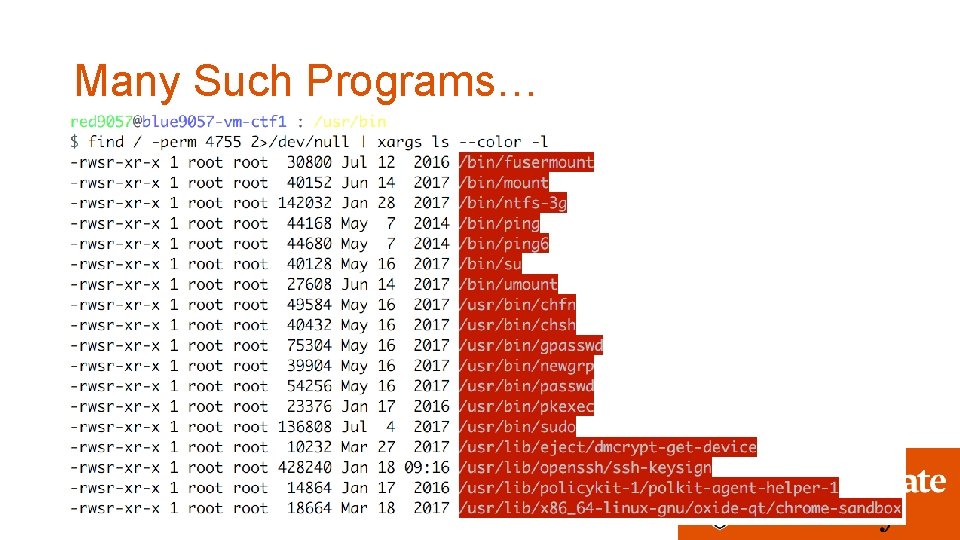
Many Such Programs…
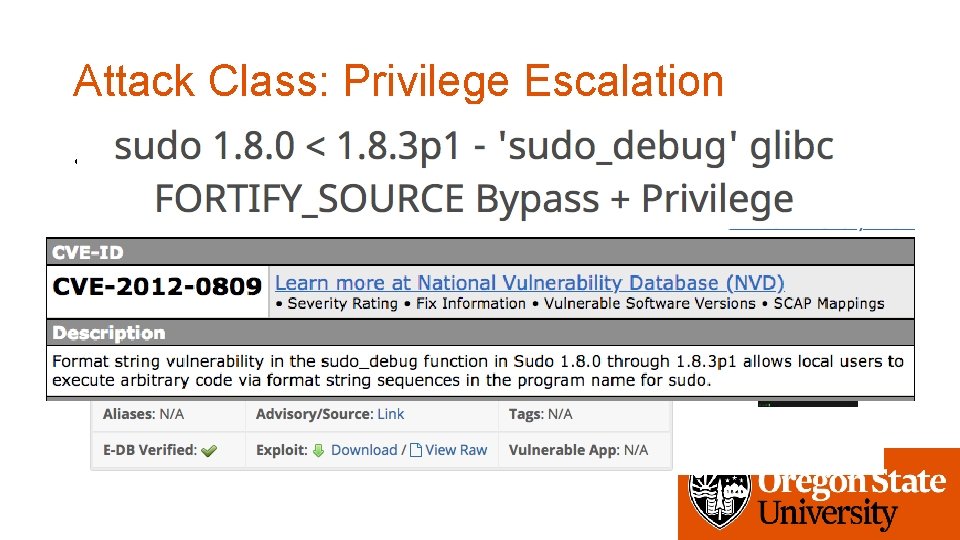
Attack Class: Privilege Escalation • Exploit a vulnerability in a program that run with a higher privilege to do something that is not allowed to you • E. g. , exploit a vulnerability in /usr/bin/sudo to become the root user!
Assignment Week-2 Workflow • Overwrite the stack frame • Make the function incorrectly return • Change the return address • execute_me() • Prints the flag
How Real Attacks Work? • 1. Find a vulnerability that can hijack the control pointer • 2. Change the control to the function that you want to execute • 3. Run with escalated privilege!
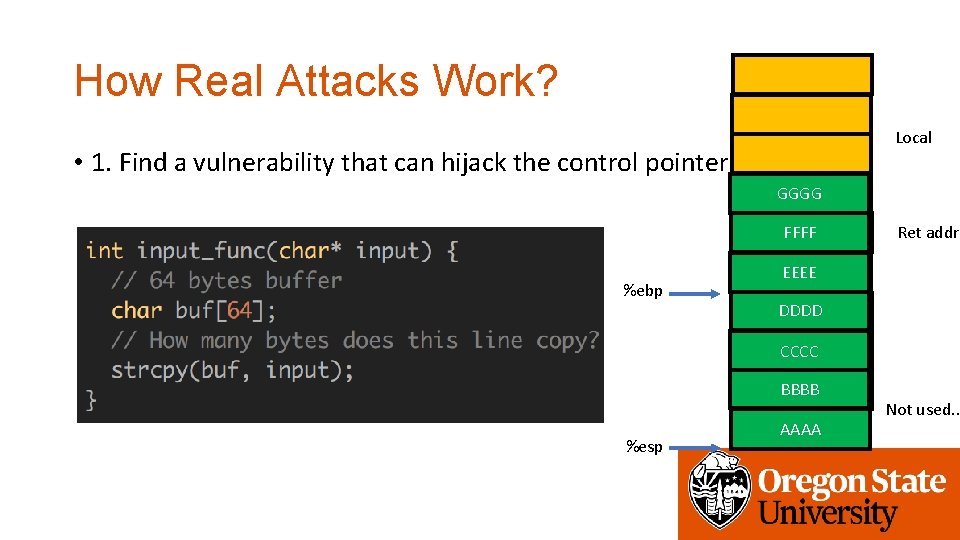
How Real Attacks Work? Local • 1. Find a vulnerability that can hijack the control pointer GGGG FFFF 0 x 80484 e 8 %ebp Ret addr Saved EEEEebp DDDD CCCC BBBB %esp AAAA Not used. .
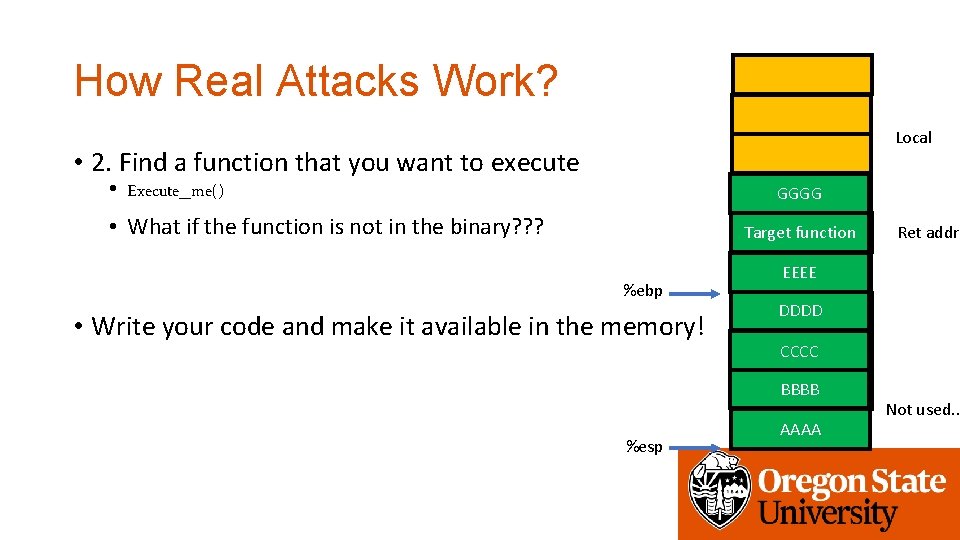
How Real Attacks Work? Local • 2. Find a function that you want to execute • Execute_me() GGGG • What if the function is not in the binary? ? ? Target function 0 x 80484 e 8 %ebp • Write your code and make it available in the memory! Saved EEEEebp DDDD CCCC BBBB %esp Ret addr AAAA Not used. .
Shellcode • A binary code (small piece of program) that runs a shell (i. e. , /bin/sh) • execve(“/bin/sh”, 0, 0) • Why shell? • You can run any command after spawning a shell • $ cat flag-32 • Inheriting the sticky privilege for privilege escalation • setreuid(geteuid(), geteuid()) • setregid(getegid(), getegid())
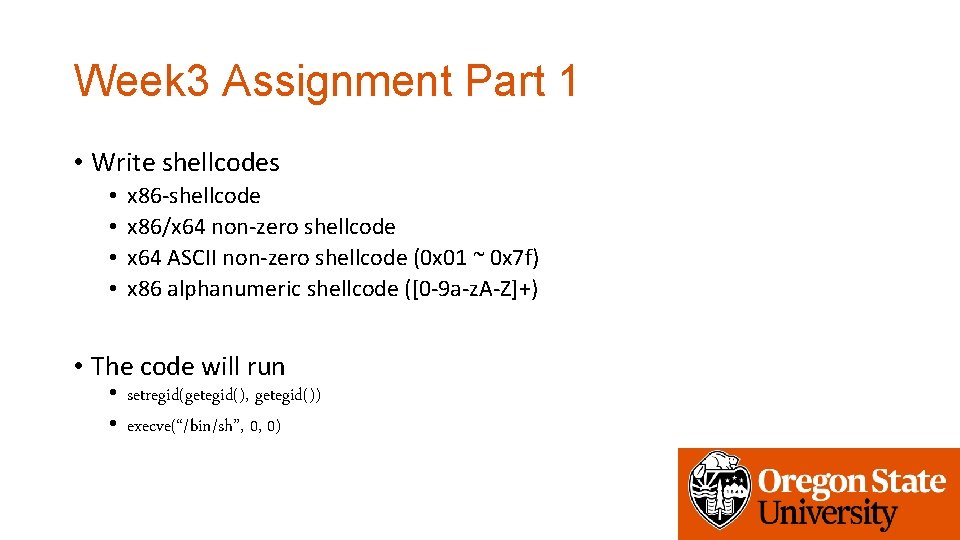
Week 3 Assignment Part 1 • Write shellcodes • • x 86 -shellcode x 86/x 64 non-zero shellcode x 64 ASCII non-zero shellcode (0 x 01 ~ 0 x 7 f) x 86 alphanumeric shellcode ([0 -9 a-z. A-Z]+) • The code will run • setregid(getegid(), getegid()) • execve(“/bin/sh”, 0, 0)
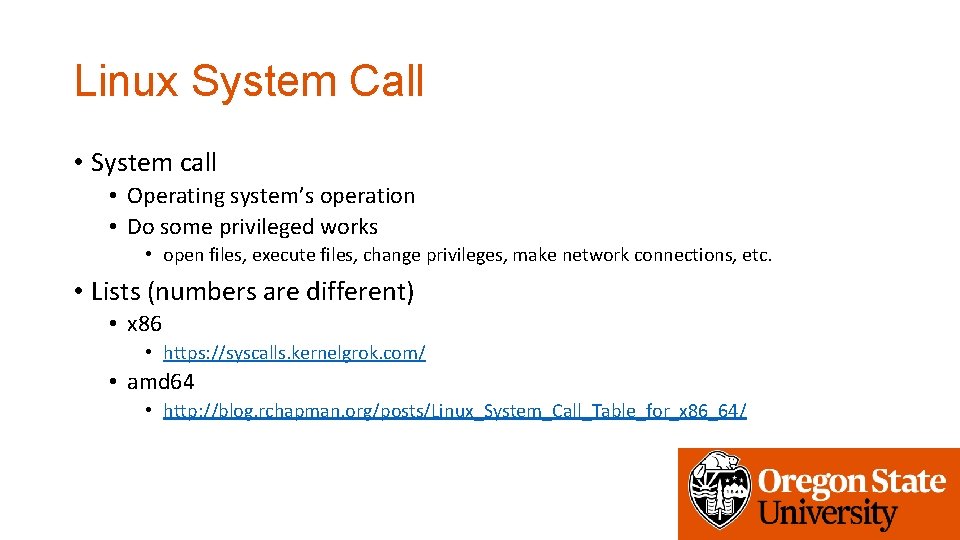
Linux System Call • System call • Operating system’s operation • Do some privileged works • open files, execute files, change privileges, make network connections, etc. • Lists (numbers are different) • x 86 • https: //syscalls. kernelgrok. com/ • amd 64 • http: //blog. rchapman. org/posts/Linux_System_Call_Table_for_x 86_64/
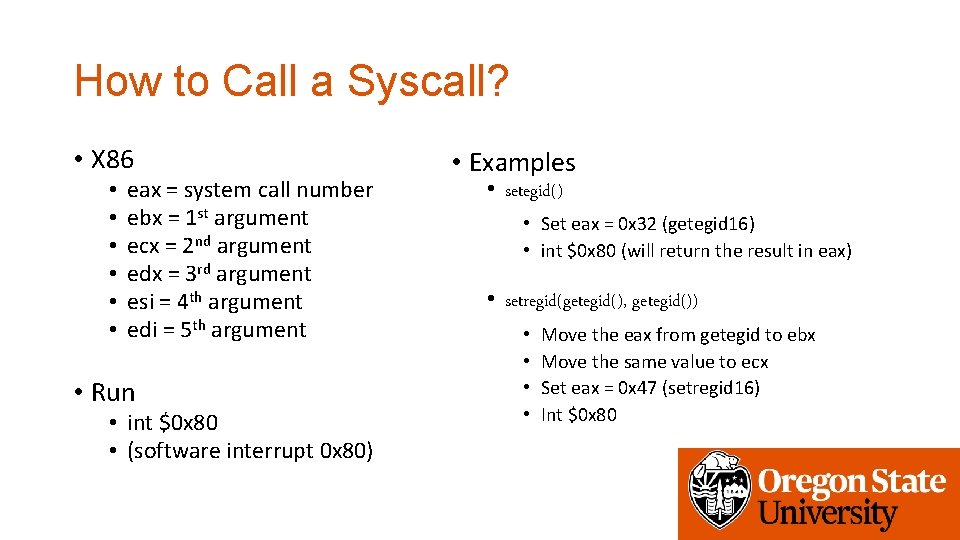
How to Call a Syscall? • X 86 • • • eax = system call number ebx = 1 st argument ecx = 2 nd argument edx = 3 rd argument esi = 4 th argument edi = 5 th argument • Run • int $0 x 80 • (software interrupt 0 x 80) • Examples • setegid() • Set eax = 0 x 32 (getegid 16) • int $0 x 80 (will return the result in eax) • setregid(getegid(), getegid()) • • Move the eax from getegid to ebx Move the same value to ecx Set eax = 0 x 47 (setregid 16) Int $0 x 80
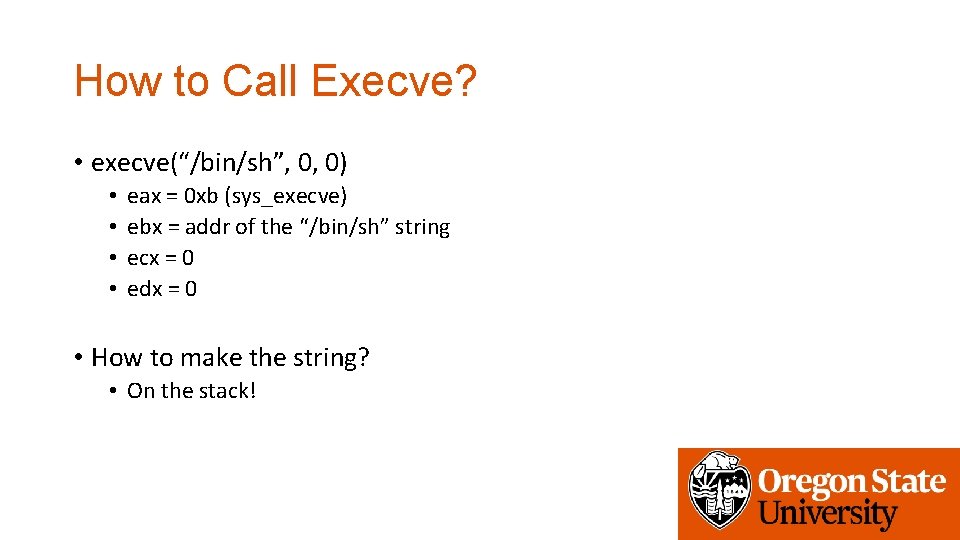
How to Call Execve? • execve(“/bin/sh”, 0, 0) • • eax = 0 xb (sys_execve) ebx = addr of the “/bin/sh” string ecx = 0 edx = 0 • How to make the string? • On the stack!
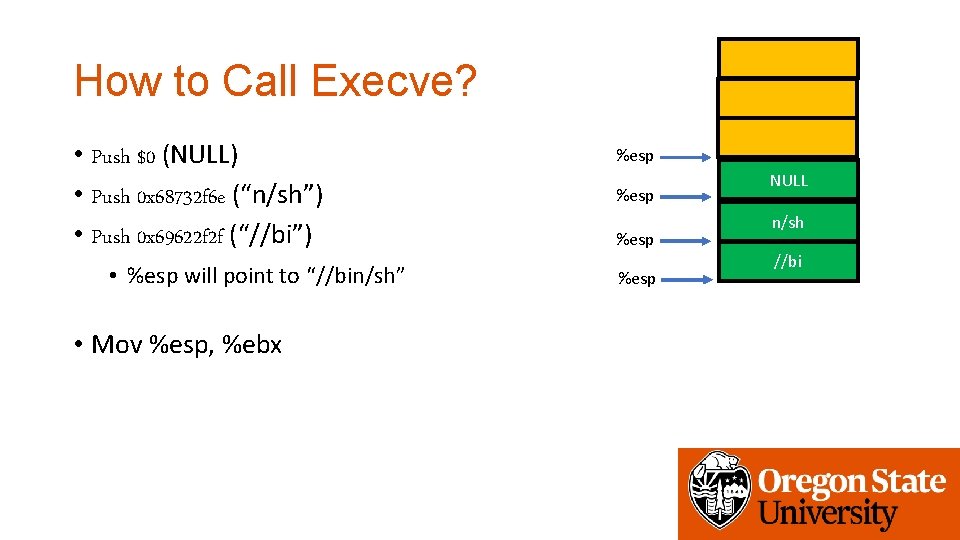
How to Call Execve? • Push $0 (NULL) • Push 0 x 68732 f 6 e (“n/sh”) • Push 0 x 69622 f 2 f (“//bi”) • %esp will point to “//bin/sh” • Mov %esp, %ebx %esp NULL n/sh //bi
How to make Zero without Zero? • xor %ecx, %ecx • mov $0 x 0101, %ecx • sub $0 x 0101, %ecx • push $1 • pop %ecx • dec %ecx
Assignment: Week-3 • Please solve challenges in the /home/labs/week 3 directory • Debug programs in the samples directory • These programs will not give you the flag • Get flags from programs in the challeges directory • Due: 2/6 4: 00 pm
- Slides: 26