CS 285 Network Security Fall 2008 Yuan Xue
![Books and References Textbook n [WS] Cryptography and Network Security: Principles and Practice (4 Books and References Textbook n [WS] Cryptography and Network Security: Principles and Practice (4](https://slidetodoc.com/presentation_image_h2/d8b58693c38bc2a34b123cd34710a34f/image-3.jpg)
- Slides: 23
CS 285 Network Security Fall 2008 @Yuan Xue (yuan. xue@vanderbilt. edu )
Course Information When and Where n n Tuesday/Thursday 11 am-12: 15 pm 209 Featheringill Hall Instructor: Yuan Xue (yuan. xue@vanderbilt. edu) n n Office: 383 Jacobs Hall, Phone: 615 -322 -2926 Office hours: Monday/Thursday 2 pm-3 pm or by appointment. Web: http: //vanets. vuse. vanderbilt. edu/~xue/cs 285 fall 08/index. html @Yuan Xue (yuan. xue@vanderbilt. edu )
![Books and References Textbook n WS Cryptography and Network Security Principles and Practice 4 Books and References Textbook n [WS] Cryptography and Network Security: Principles and Practice (4](https://slidetodoc.com/presentation_image_h2/d8b58693c38bc2a34b123cd34710a34f/image-3.jpg)
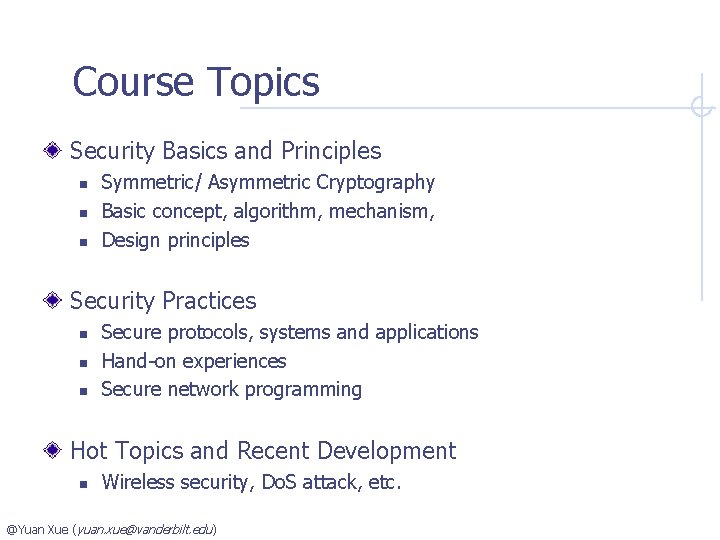
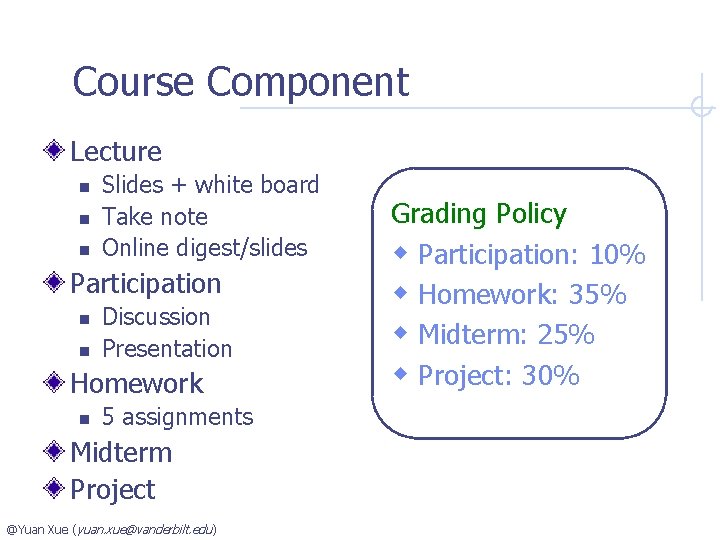
Books and References Textbook n [WS] Cryptography and Network Security: Principles and Practice (4 th Edition) by William Stallings Reference books n n n [KPS] Network Security: Private Communication in a Public World (2 nd Edition), by Charlie Kaufman, Radia Perlman, Mike Speciner [CSP] Security in Computing (3 rd Edition), by Charles P. Pfleeger, Shari Lawrence Pfleeger [MB] Computer Security: Art and Science, by Matthew A. Bishop @Yuan Xue (yuan. xue@vanderbilt. edu )
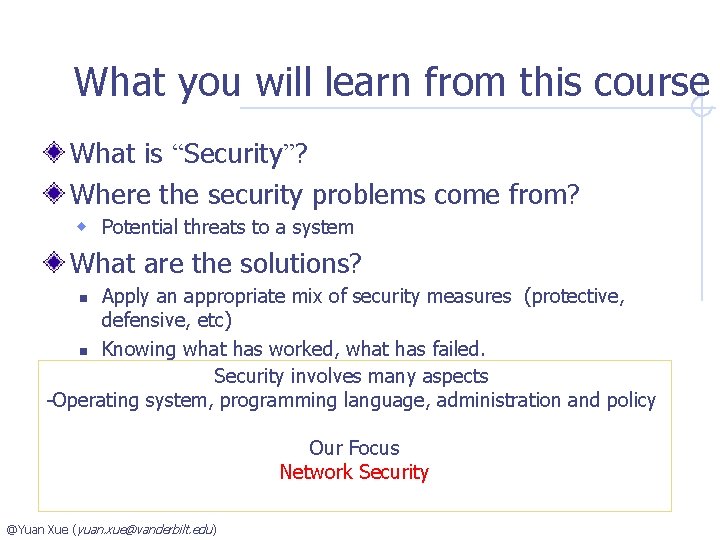
Course Component Lecture n n n Slides + white board Take note Online digest/slides Participation n n Discussion Presentation Homework n 5 assignments Midterm Project @Yuan Xue (yuan. xue@vanderbilt. edu ) Grading Policy w Participation: 10% w Homework: 35% w Midterm: 25% w Project: 30%
What you will learn from this course What is “Security”? Where the security problems come from? w Potential threats to a system What are the solutions? Apply an appropriate mix of security measures (protective, defensive, etc) n Knowing what has worked, what has failed. Security involves many aspects -Operating system, programming language, administration and policy n Our Focus Network Security @Yuan Xue (yuan. xue@vanderbilt. edu )
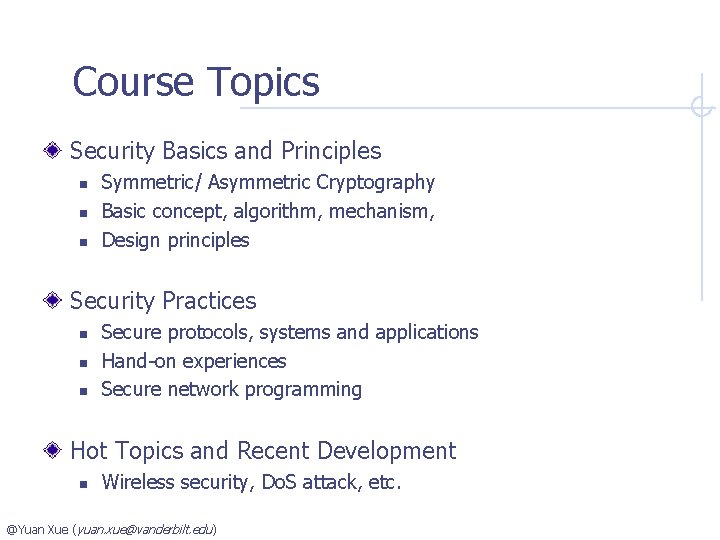
Course Topics Security Basics and Principles n n n Symmetric/ Asymmetric Cryptography Basic concept, algorithm, mechanism, Design principles Security Practices n n n Secure protocols, systems and applications Hand-on experiences Secure network programming Hot Topics and Recent Development n Wireless security, Do. S attack, etc. @Yuan Xue (yuan. xue@vanderbilt. edu )
Survey and Feedback Your input is important n Online Survey w http: //www. zoomerang. com/Survey/? p=WEB 22873 V 62 YWQ n Feedback @Yuan Xue (yuan. xue@vanderbilt. edu )
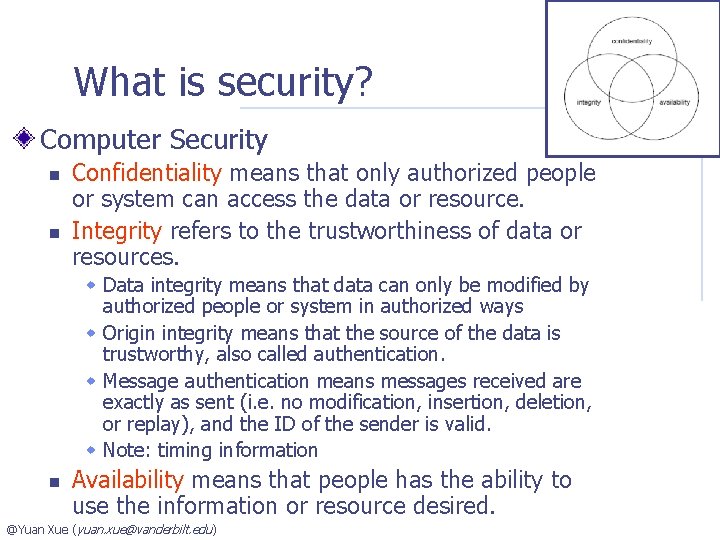
What is security? In general, security is the condition of being protected against danger or loss. (Wikipedia) In computer security and network security n What are the subjects that need to be protected? Let’s start with some terms n System w computer, network, application, data, resource n Principal: an entity that participate in a system w user, person @Yuan Xue (yuan. xue@vanderbilt. edu )
What is security? Computer Security n n Confidentiality means that only authorized people or system can access the data or resource. Integrity refers to the trustworthiness of data or resources. w Data integrity means that data can only be modified by authorized people or system in authorized ways w Origin integrity means that the source of the data is trustworthy, also called authentication. w Message authentication means messages received are exactly as sent (i. e. no modification, insertion, deletion, or replay), and the ID of the sender is valid. w Note: timing information n Availability means that people has the ability to use the information or resource desired. @Yuan Xue (yuan. xue@vanderbilt. edu )
Where the security problem comes from? Let’s look at some example systems: Bank n Bookkeeping w Core operations n customer account, journals recording the transactions w Who has the access to the information? n Bank’s own staff – what if they cheat? n ATM w Authenticate users based on card and ID number n Let’s go Internet w The user – how do we know they are the “real” (authenticate) user? w Protect web servers and bookkeeping database @Yuan Xue (yuan. xue@vanderbilt. edu )
Where the security problem comes from? Hospital n Patient record system w Who can access the record? – n Many parties – insurance company, care giver, researcher, etc n Complicated -- role can change n Privacy issue – HIPPA n Anonymize the record for research w Is it sufficient? n Show me all records of 59 -year-old males who were treated for a broken collarbone on September 15, 1966 n n Drug management Let’s go to Web w …. @Yuan Xue (yuan. xue@vanderbilt. edu )
Issues that will be addressed in this class @Yuan Xue (yuan. xue@vanderbilt. edu )
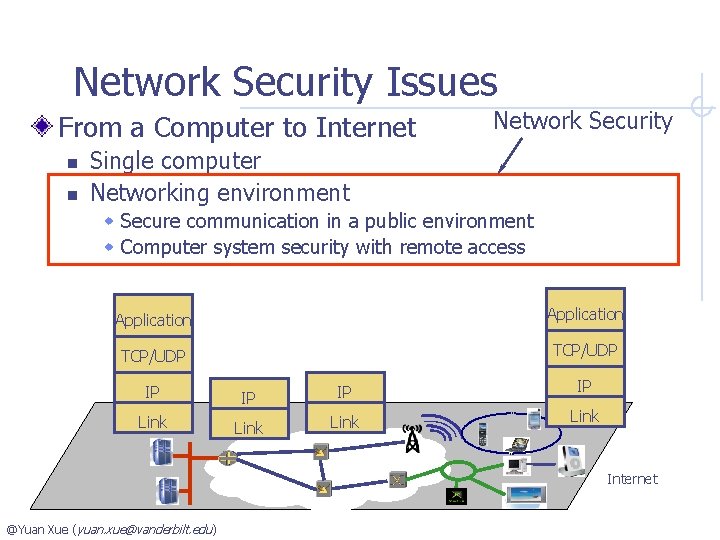
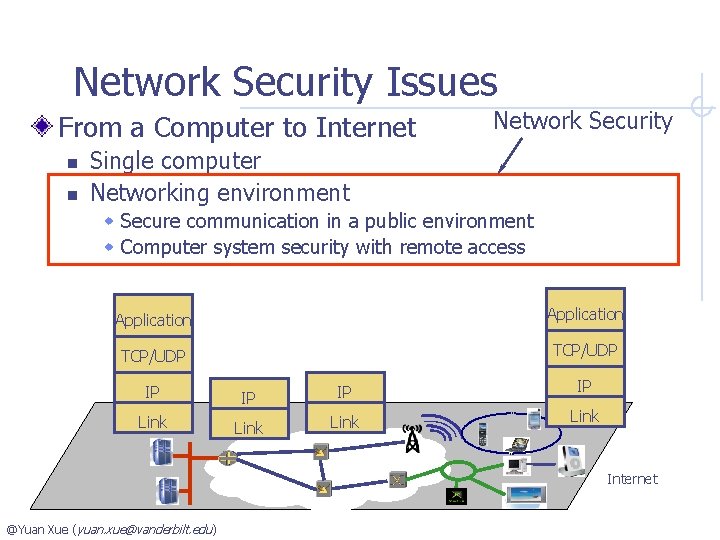
Network Security Issues From a Computer to Internet n n Network Security Single computer Networking environment w Secure communication in a public environment w Computer system security with remote access Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
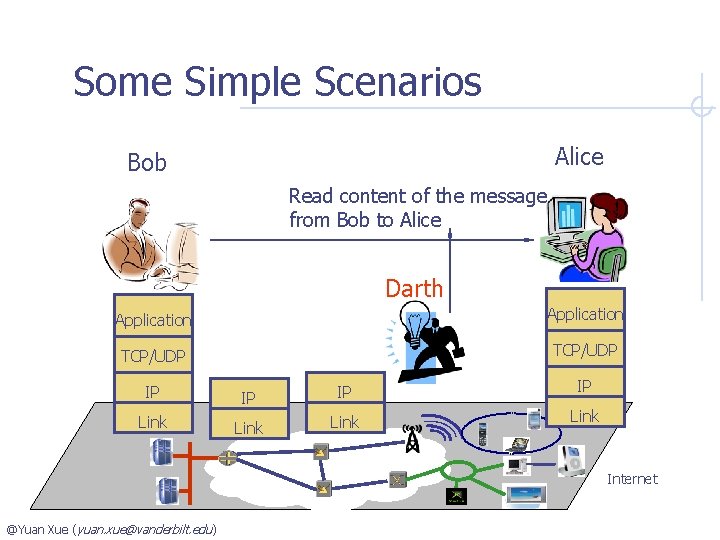
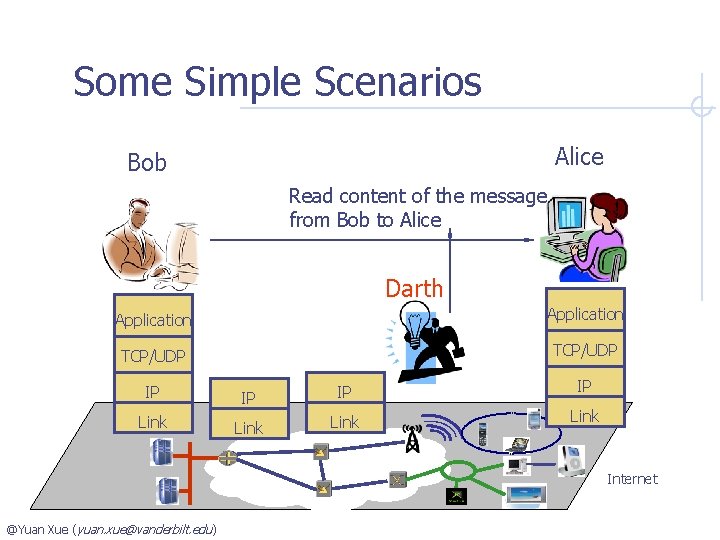
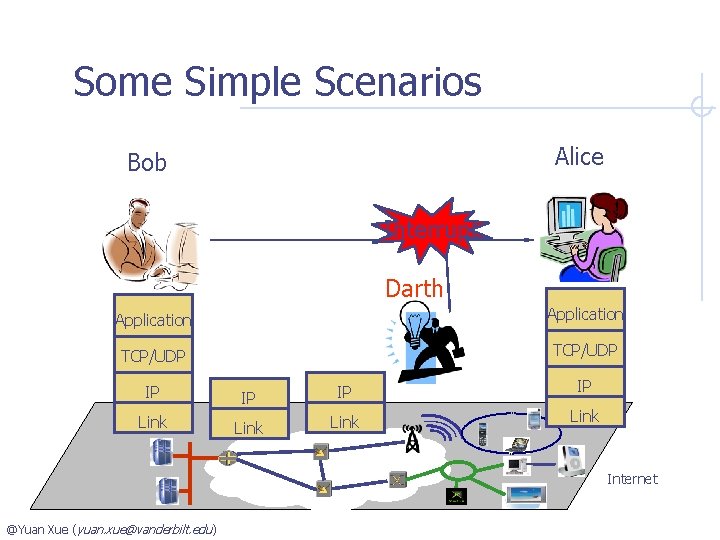
Some Simple Scenarios Alice Bob Read content of the message from Bob to Alice Darth Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
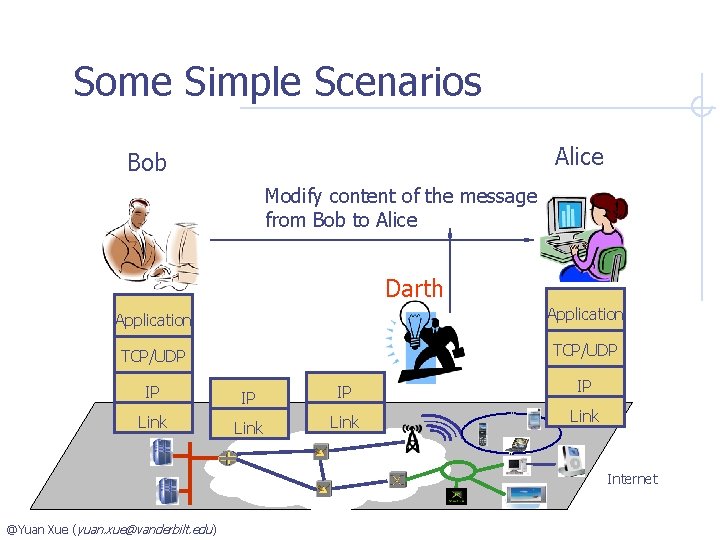
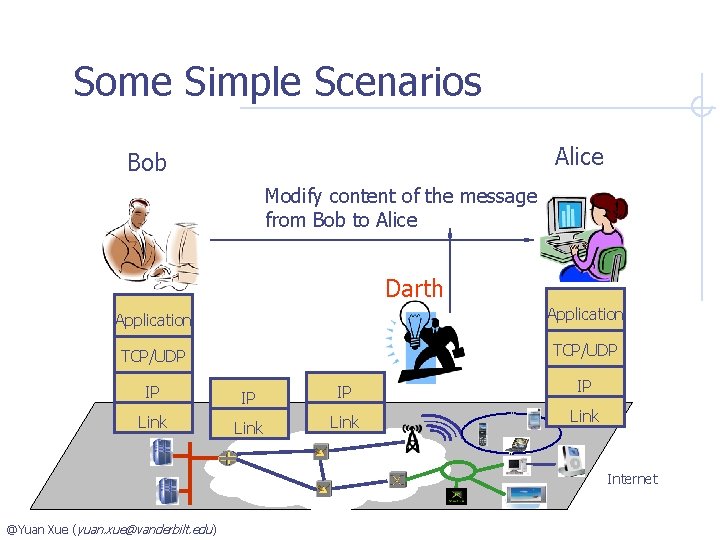
Some Simple Scenarios Alice Bob Modify content of the message from Bob to Alice Darth Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
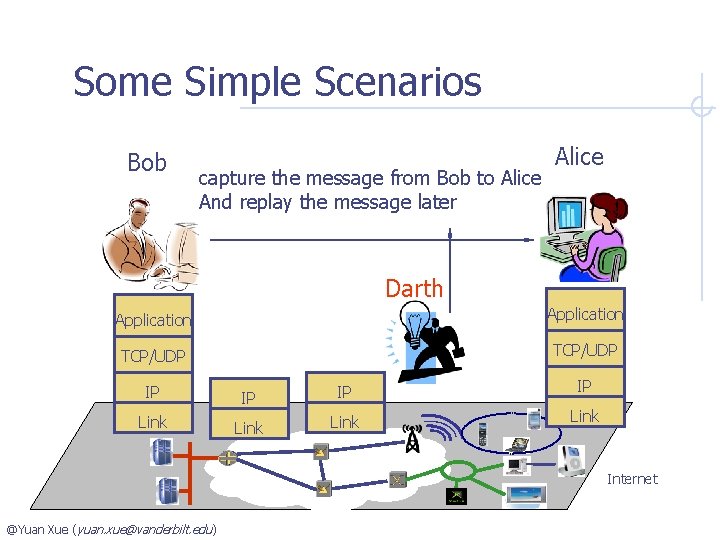
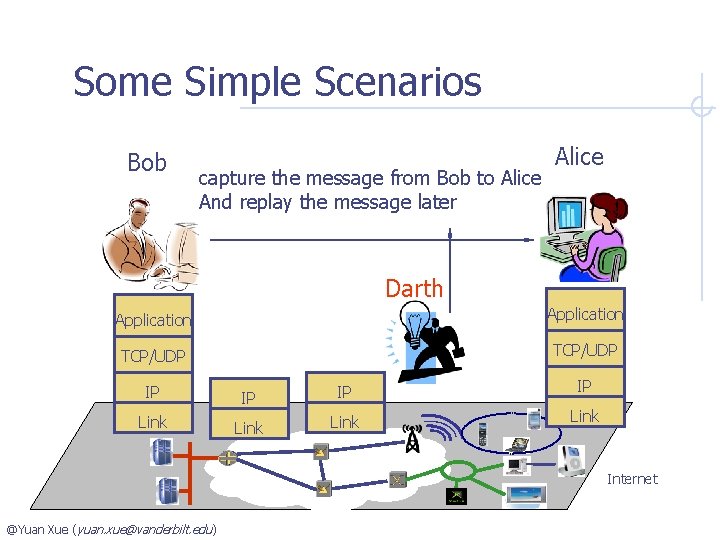
Some Simple Scenarios Bob capture the message from Bob to Alice And replay the message later Alice Darth Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
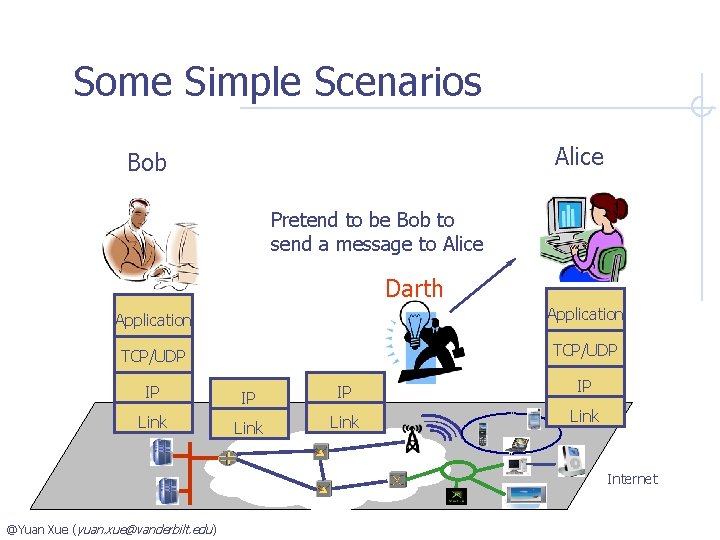
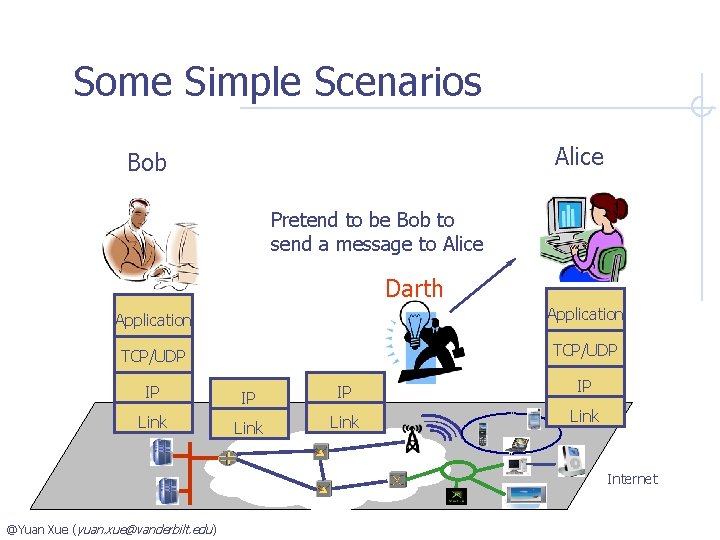
Some Simple Scenarios Alice Bob Pretend to be Bob to send a message to Alice Darth Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
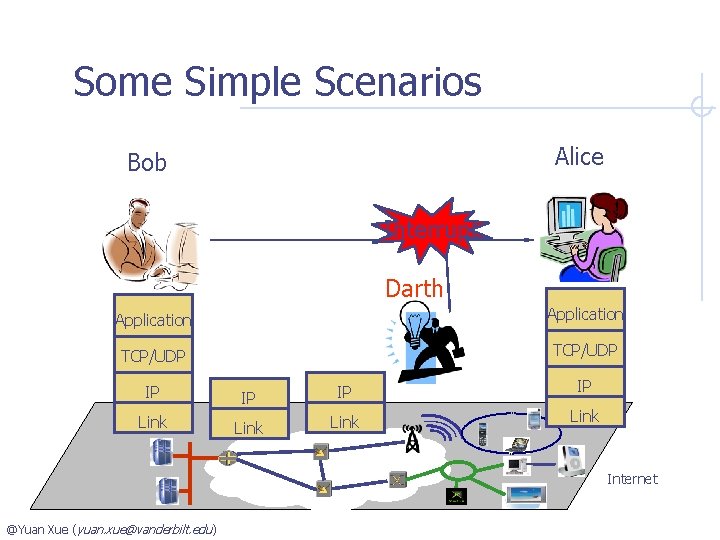
Some Simple Scenarios Alice Bob Interrupt Darth Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
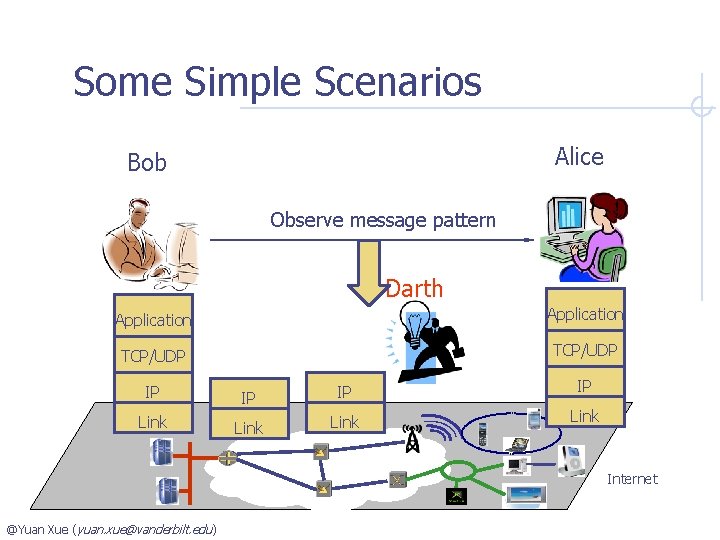
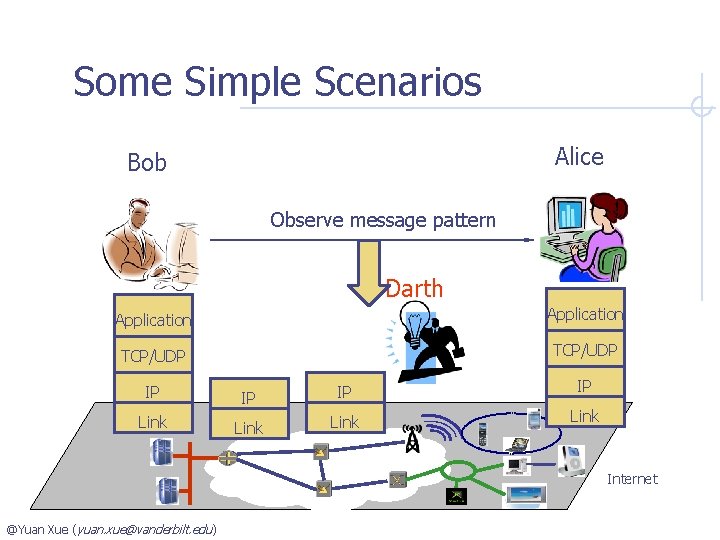
Some Simple Scenarios Alice Bob Observe message pattern Darth Application TCP/UDP IP IP Link Internet @Yuan Xue (yuan. xue@vanderbilt. edu )
What are the solutions? @Yuan Xue (yuan. xue@vanderbilt. edu )
Why many solutions fail? Protect wrong things Protect right things in the wrong way @Yuan Xue (yuan. xue@vanderbilt. edu )
What are the solutions? Security Basics and Principles n n Symmetric/ Asymmetric Cryptography Basic concept, algorithm, mechanism, Security Practices n n Secure protocol designs Secure systems and applications @Yuan Xue (yuan. xue@vanderbilt. edu )
How to study network security? Principle of Easiest Penetration n n An intruder are expected to use any available means of penetration. Computer security specialists must consider all possible means of penetration. Learning methodology n n examine all possible vulnerabilities of the system consider available countermeasures. @Yuan Xue (yuan. xue@vanderbilt. edu )