CRYPTOLOGY Francesca Bandini IT Ludovica De Barbieri IT
CRYPTOLOGY Francesca Bandini (IT) Ludovica De Barbieri (IT) Ozgur Umut Sener (TR) Mehmet Enes Aktas (TR) Polina Staikova (BG) Sara Kirstine Nicolaisen (DK) Mads Moller Dissing (DK) Teacher: Peer Jesperen
STEGANOGRAPHY Steganography is the art and science of writing hidden messages in a way that no one, apart from the sender and the recipient, suspects the existence of the message. The word comes from Greek words steganos meaning "covered or protected", and grapheiv meaning "writing". The advantage of steganography, over cryptography alone, is that messages do not attract attention. Moreover, while cryptography only protects the contents of a message, steganography can protect both messages and communicating parties.
There are examples of steganography which belong to the Greek world, thousands of years ago. Some of them are told by HERODOTUS in his “Histories”.
THE FİRST ANECDOTE CONCERNS DEMARATOS Demaratos was a Lacedemonian man who lived in the Persian empire. However, he loved his motherland so, as soon as he knew Xerxes wanted to invade it, he communicated it to Lacedemonians, using steganography.
“…he took a folding tablet and scraped off the wax which was upon it, and then he wrote the design of the king upon the wood of the tablet, and having done so he melted the wax and poured it over the writing, so that the tablet (being carried without writing upon it) might not cause any trouble to be given by the keepers of the road. Then when it had arrived at Lacedemon, the Lacedemonians were not able to make conjecture of the matter; until at last, as I am informed, Gorgo, the daughter of Cleomenes and wife of Leonidas, suggested a plan of which she had herself thought, bidding them scrape the wax and they would find writing upon the wood. . . Even the second one is reported by Herodotus and it tells about HISTIAIOS’story. He had been Mileto’s tyrannous before Aristagoras; after he became Emperor Darius’ counsellor but, when Mileto revolted, he supported insurgents so he has been crucified. «…(he) shaved off the hair of the most faithful of his slaves, and having marked his head by pricking it, waited till the hair had grown again; and as soon as it was grown, he sent him away to Miletos, giving him no other charge but this, namely that when he should have arrived at Miletos he should bid Aristagoras shave his hair and look at his head…»
MICRODOT Another interesting example of steganography is a MICRODOT. A is a text or an image reduced in size onto a 1 mm disc to prevent detection by unintended recipients. Microdots are normally circular around one millimetre in diameter but can be made into different shapes and sizes and made from various materials such as polyester. The name comes from the fact that the microdots have often been about the size and shape of a typographical dot, so that they could substitute “i” or “j” dot. Microdots were used mostly during the Franco-Prussian war by Paris and during World War I and II by Germany.
WHAT ABOUT “REAL” CRYPTOGRAPHY? CRYPTOANALYSIS The science of recovering information from ciphers without knowledge of the key CRYPTOSYSTEM A system for encrypting information. DECRYPTION The process of converting the cipher into plaintext. ENCRYPTION The process of converting the plaintext into a cipher
KEY The secret information known only to the transmitter and the receiver which is used to secure the plaintext. MONO-ALPHABETIC SUBSTITUTION A method of encryption where a letter in the plaintext is always replaced by the same letter in the ciphertext. POLY-ALPHABETIC SUBSTITUTION A method of encryption where a letter in the plaintext is not always replaced by the same letter in the ciphertext.
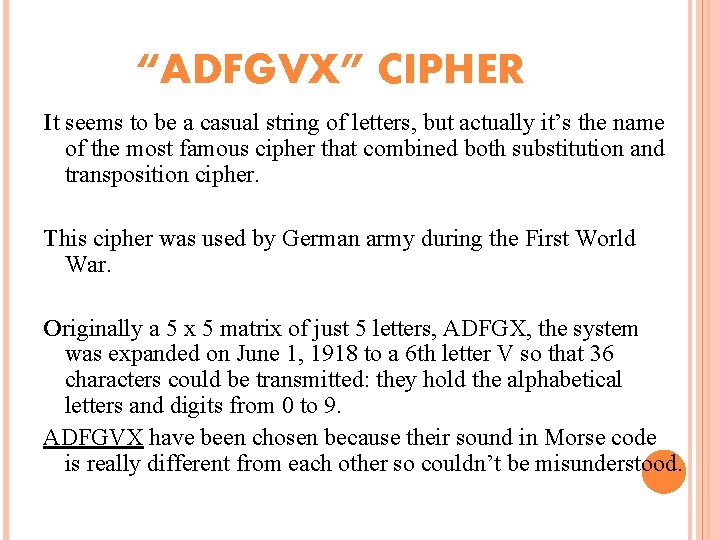
“ADFGVX” CIPHER It seems to be a casual string of letters, but actually it’s the name of the most famous cipher that combined both substitution and transposition cipher. This cipher was used by German army during the First World War. Originally a 5 x 5 matrix of just 5 letters, ADFGX, the system was expanded on June 1, 1918 to a 6 th letter V so that 36 characters could be transmitted: they hold the alphabetical letters and digits from 0 to 9. ADFGVX have been chosen because their sound in Morse code is really different from each other so couldn’t be misunderstood.
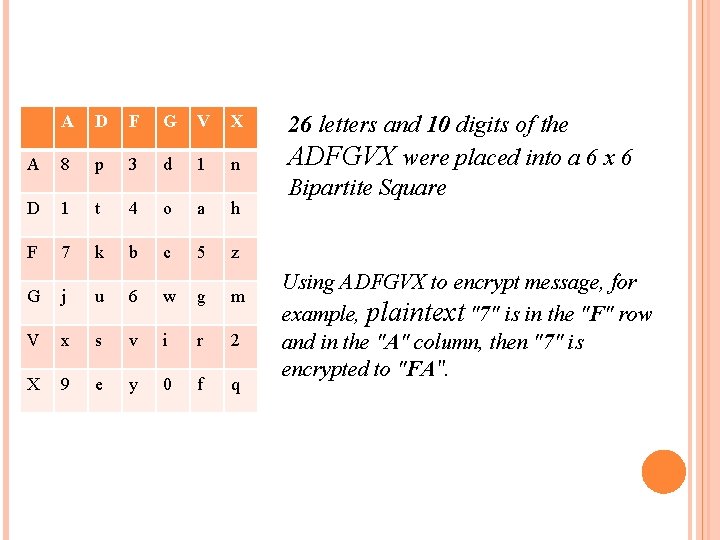
A D F G V X A 8 p 3 d 1 n D 1 t 4 o a h F 7 k b c 5 z G j u 6 w g m V x s v i r 2 X 9 e y 0 f q 26 letters and 10 digits of the ADFGVX were placed into a 6 x 6 Bipartite Square Using ADFGVX to encrypt message, for example, plaintext "7" is in the "F" row and in the "A" column, then "7" is encrypted to "FA".
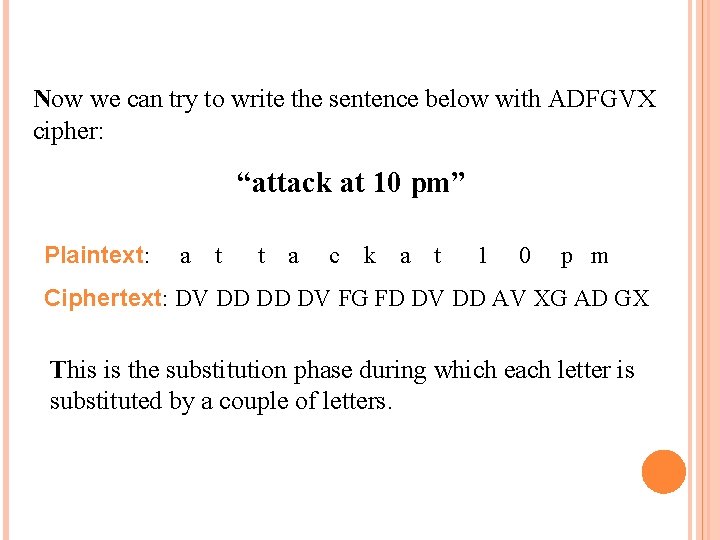
Now we can try to write the sentence below with ADFGVX cipher: “attack at 10 pm” Plaintext: a t t a c k a t 1 0 p m Ciphertext: DV DD DD DV FG FD DV DD AV XG AD GX This is the substitution phase during which each letter is substituted by a couple of letters.
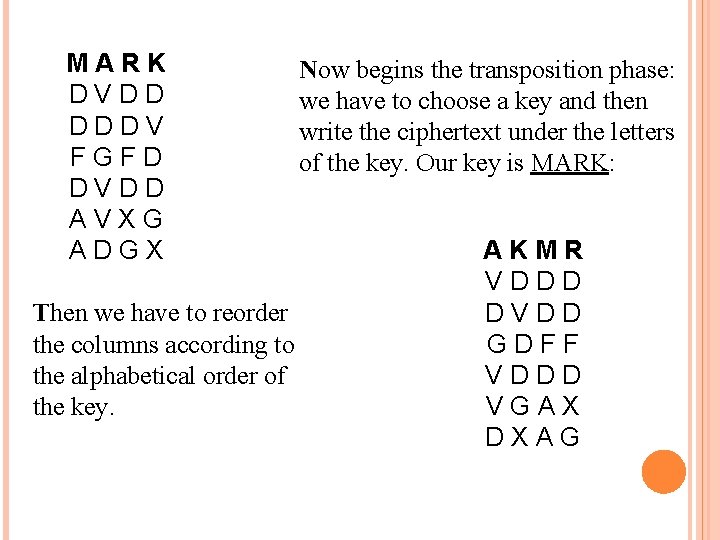
MARK D V D D D V F G F D D V D D A V X G A D G X Now begins the transposition phase: we have to choose a key and then write the ciphertext under the letters of the key. Our key is MARK: Then we have to reorder the columns according to the alphabetical order of the key. A K M R V D D G D F F V D D D V G A X D X A G
Eventually, rewrite the letters by the columns vertically and the result will be: VDGVV DDVDD GXDDF DAADD FDXG (do you remember the original message? ) The first one who was able to break this kind of cipher has been a French cryptanalyst, Painvin, in April 1918. Thanks of his work French army discovered where German army wanted to attack and could stop the offensive.
CAESAR CIPHER Julius Caesar created a cipher in order to protect his military messages. This is attested by Suetonius and from that moment this kind of transposition has been called “Caesar cipher”. Caesar cipher consisted of the shifting of three letters. Even if this is the first recorded cipher, however there’s surely been kind of ciphers even before.
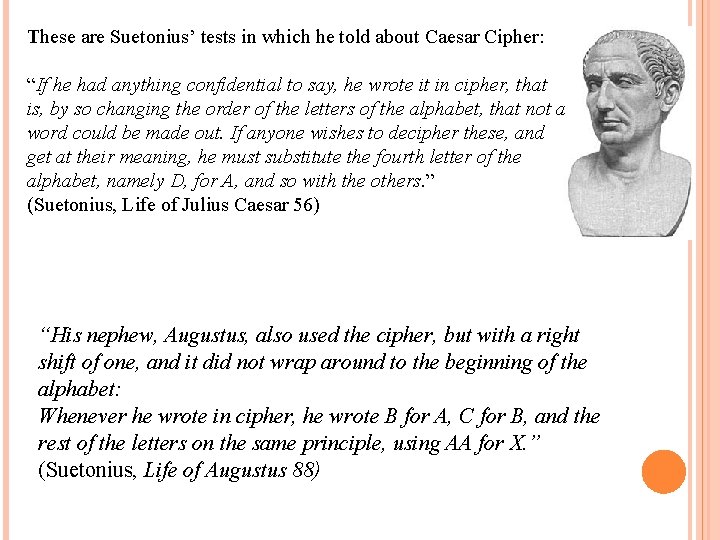
These are Suetonius’ tests in which he told about Caesar Cipher: “If he had anything confidential to say, he wrote it in cipher, that is, by so changing the order of the letters of the alphabet, that not a word could be made out. If anyone wishes to decipher these, and get at their meaning, he must substitute the fourth letter of the alphabet, namely D, for A, and so with the others. ” (Suetonius, Life of Julius Caesar 56) “His nephew, Augustus, also used the cipher, but with a right shift of one, and it did not wrap around to the beginning of the alphabet: Whenever he wrote in cipher, he wrote B for A, C for B, and the rest of the letters on the same principle, using AA for X. ” (Suetonius, Life of Augustus 88)
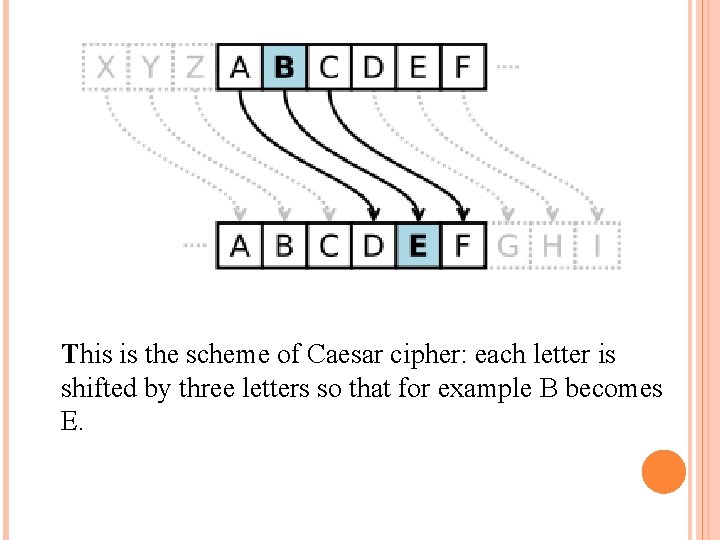
This is the scheme of Caesar cipher: each letter is shifted by three letters so that for example B becomes E.
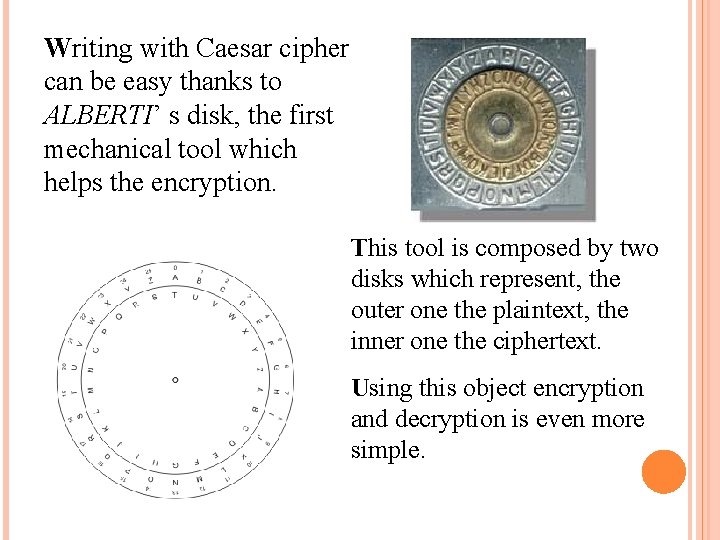
Writing with Caesar cipher can be easy thanks to ALBERTI’ s disk, the first mechanical tool which helps the encryption. This tool is composed by two disks which represent, the outer one the plaintext, the inner one the ciphertext. Using this object encryption and decryption is even more simple.
AFTER CAESAR CIPHER… …VİGENÈRE CİPHER Caesar cipher is one of the simplest kind of cryptography that can be easily decrypted by cryptanalysts. The Vigenère cipher can be considered the evolution of the Caesar one. This cipher is well known because while it is easy to understand implement, it often appears to beginners to be unbreakable; this earned it the definotion of “le chiffre indéchiffrable”. Blaise de Vigenère, 19° century
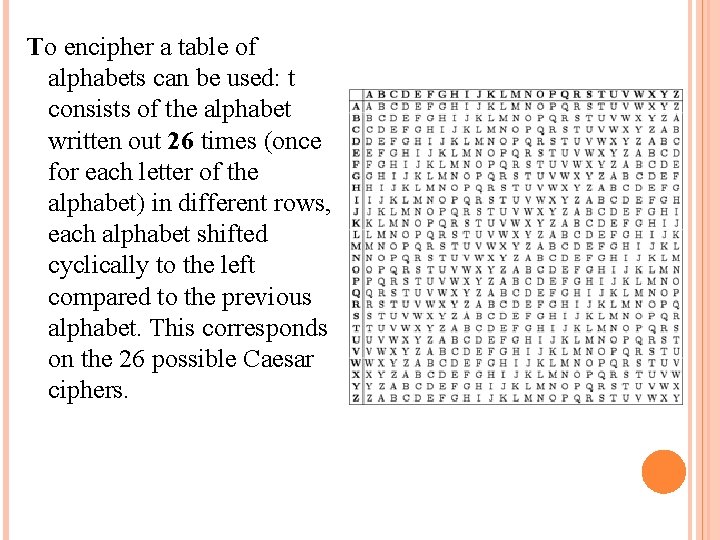
To encipher a table of alphabets can be used: t consists of the alphabet written out 26 times (once for each letter of the alphabet) in different rows, each alphabet shifted cyclically to the left compared to the previous alphabet. This corresponds on the 26 possible Caesar ciphers.
At different points in the encryption process, the cipher uses a different alphabet from one of the rows. The alphabet used at each point depends on a repeating keyword. For example, suppose that the plaintext to be encrypted is: ATTACK AT DAWN The person sending the message chooses a keyword and repeats it until it matches the length of the plaintext, for example, the keyword "LEMON": LEMONLE
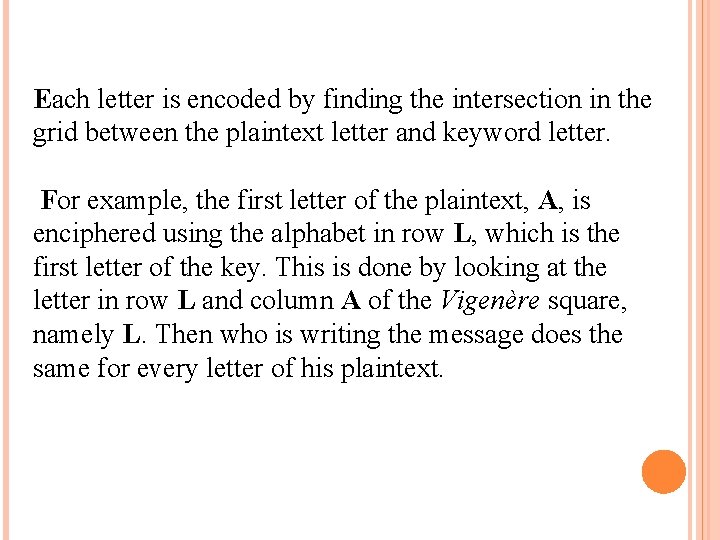
Each letter is encoded by finding the intersection in the grid between the plaintext letter and keyword letter. For example, the first letter of the plaintext, A, is enciphered using the alphabet in row L, which is the first letter of the key. This is done by looking at the letter in row L and column A of the Vigenère square, namely L. Then who is writing the message does the same for every letter of his plaintext.
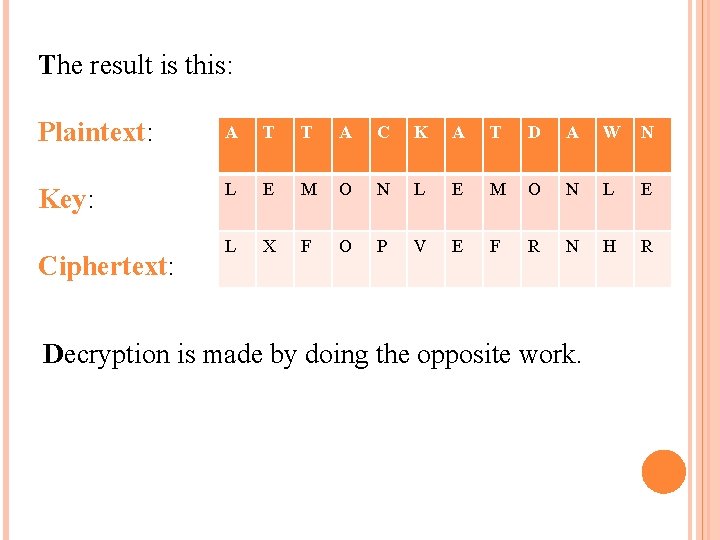
The result is this: Plaintext: A T T A C K A T D A W N Key: L E M O N L E L X F O P V E F R N H R Ciphertext: Decryption is made by doing the opposite work.
PLAYFAİR CİPHER This cipher system was invented by Baron Iyon Fair and it uses 5 x 5 table. English has 26 letters: 5 x 5=25, so a letter must be out of the system. Generally it would be 'Q', because it's a less used word than the others. So, how does it work? 1) Choose a keyword. (For example : PLAYFAIREXAMPLE) 2) Mark repetition words and eliminate those words. (PLAYFIREXM)
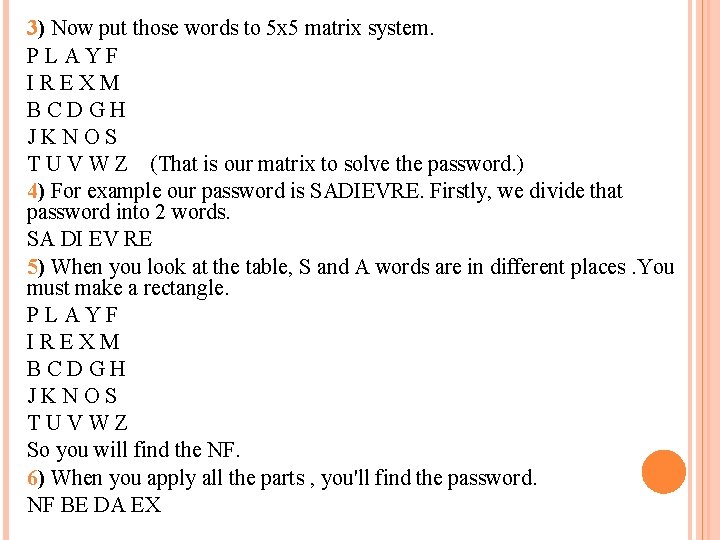
3) Now put those words to 5 x 5 matrix system. P L A Y F I R E X M B C D G H J K N O S T U V W Z (That is our matrix to solve the password. ) 4) For example our password is SADIEVRE. Firstly, we divide that password into 2 words. SA DI EV RE 5) When you look at the table, S and A words are in different places. You must make a rectangle. P L A Y F I R E X M B C D G H J K N O S T U V W Z So you will find the NF. 6) When you apply all the parts , you'll find the password. NF BE DA EX
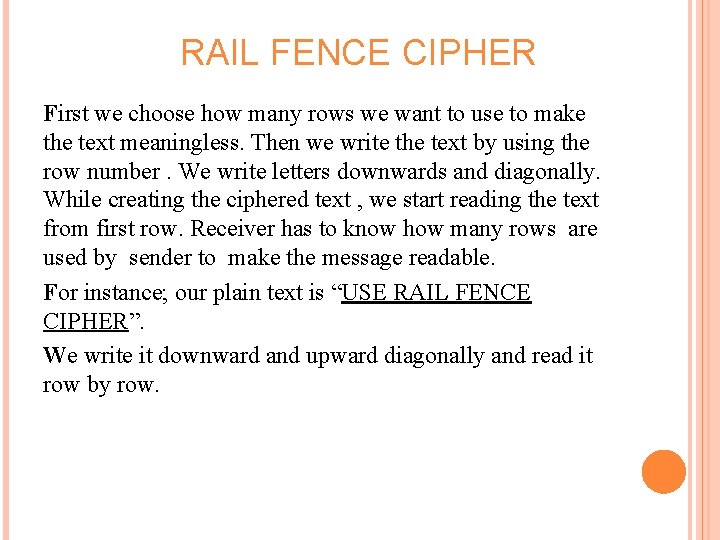
RAIL FENCE CIPHER First we choose how many rows we want to use to make the text meaningless. Then we write the text by using the row number. We write letters downwards and diagonally. While creating the ciphered text , we start reading the text from first row. Receiver has to know how many rows are used by sender to make the message readable. For instance; our plain text is “USE RAIL FENCE CIPHER”. We write it downward and upward diagonally and read it row by row.
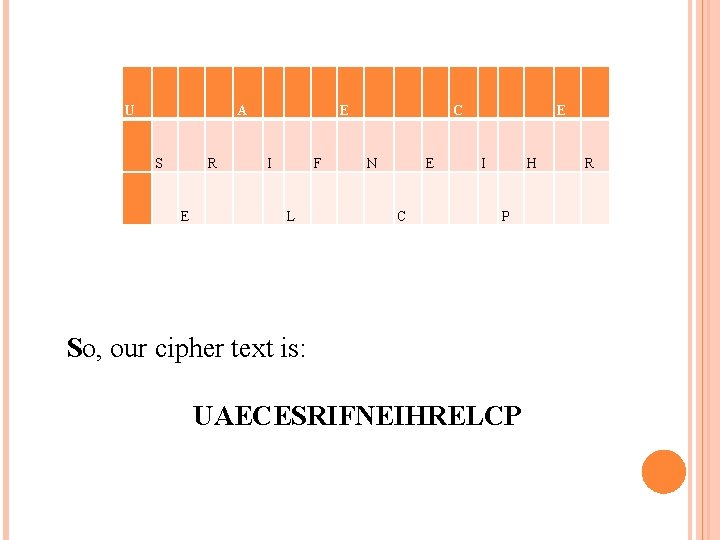
U A E C E S R I F N E I H R E L C P So, our cipher text is: UAECESRIFNEIHRELCP
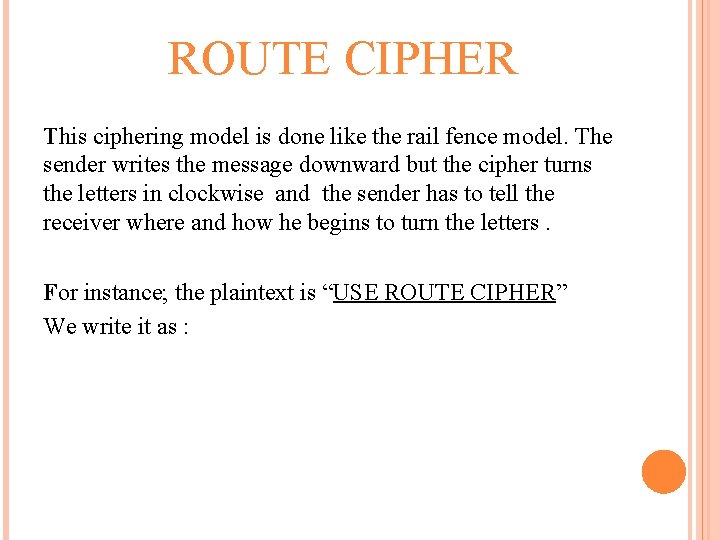
ROUTE CIPHER This ciphering model is done like the rail fence model. The sender writes the message downward but the cipher turns the letters in clockwise and the sender has to tell the receiver where and how he begins to turn the letters. For instance; the plaintext is “USE ROUTE CIPHER” We write it as :
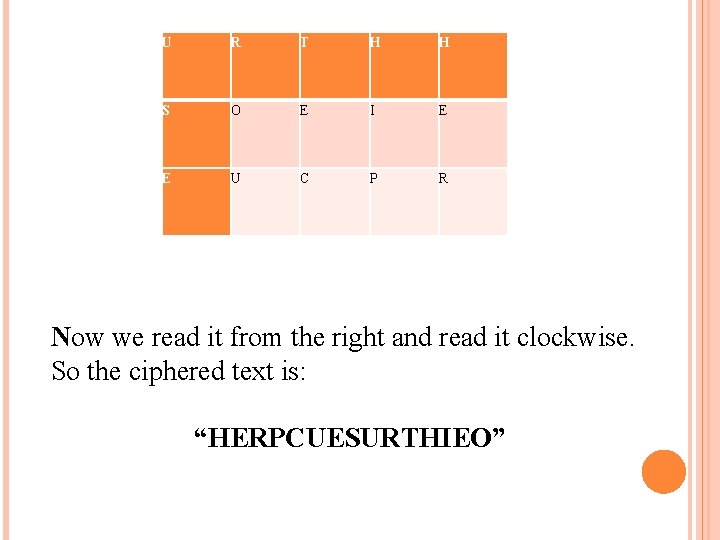
U R T H H S O E I E E U C P R Now we read it from the right and read it clockwise. So the ciphered text is: “HERPCUESURTHIEO”
CODES AND CIPHERS Till now we’ve talked about ciphers but in the history of cryptography, cryptanalysts have found bigger problems with codes. These aren’t created by shifting the letters of the alphabet, but are completely invented by the recipients and are more difficult to be decrypted.
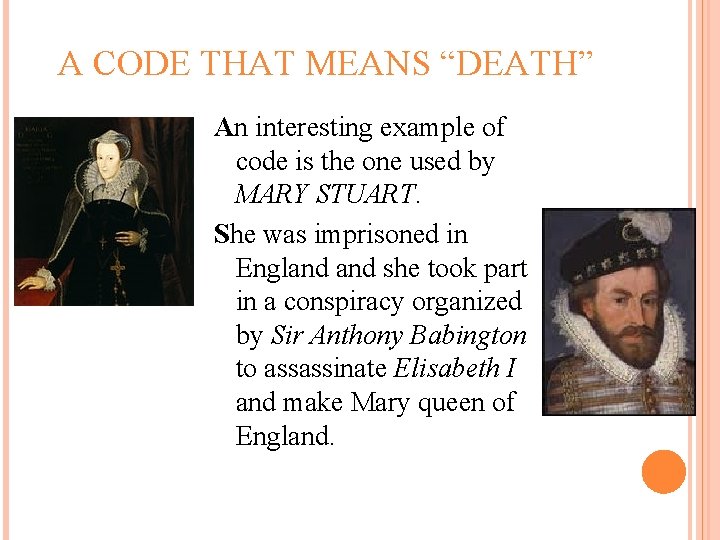
A CODE THAT MEANS “DEATH” An interesting example of code is the one used by MARY STUART. She was imprisoned in England she took part in a conspiracy organized by Sir Anthony Babington to assassinate Elisabeth I and make Mary queen of England.
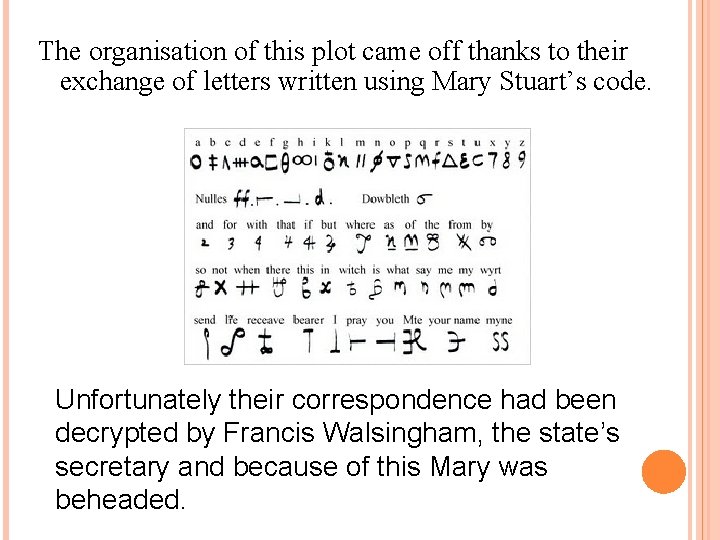
The organisation of this plot came off thanks to their exchange of letters written using Mary Stuart’s code. Unfortunately their correspondence had been decrypted by Francis Walsingham, the state’s secretary and because of this Mary was beheaded.
There are many examples of how cryptography is popular in common communication and it’s impossible to list all the interesting stories based on encryption and decryption of messages. However it’s curious to observe that cryptography is present in literature, too.
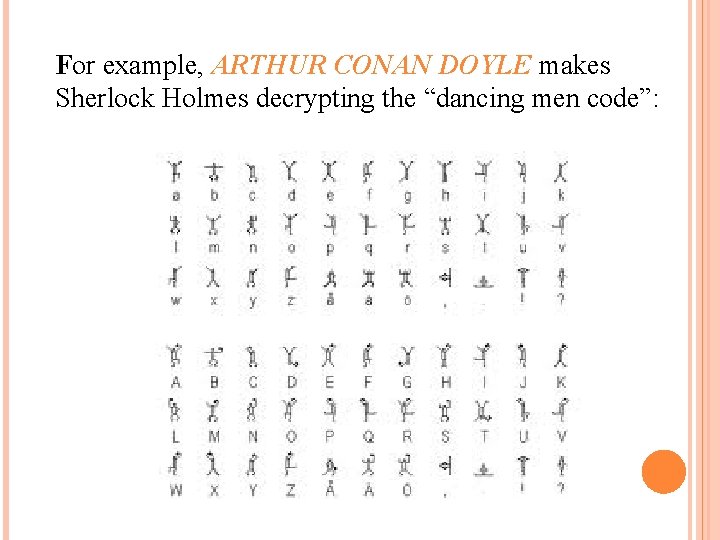
For example, ARTHUR CONAN DOYLE makes Sherlock Holmes decrypting the “dancing men code”:
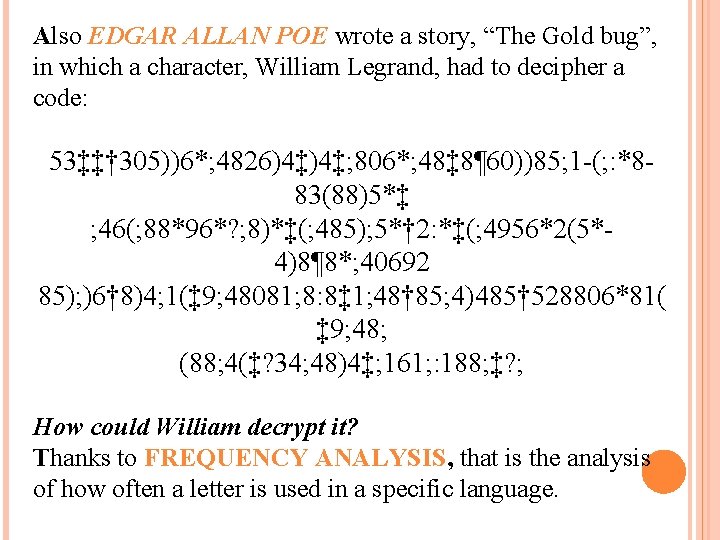
Also EDGAR ALLAN POE wrote a story, “The Gold bug”, in which a character, William Legrand, had to decipher a code: 53‡‡† 305))6*; 4826)4‡)4‡; 806*; 48‡ 8¶ 60))85; 1 -(; : *883(88)5*‡ ; 46(; 88*96*? ; 8)*‡(; 485); 5*† 2: *‡(; 4956*2(5*- 4)8¶ 8*; 40692 85); )6† 8)4; 1(‡ 9; 48081; 8: 8‡ 1; 48† 85; 4)485† 528806*81( ‡ 9; 48; (88; 4(‡? 34; 48)4‡; 161; : 188; ‡? ; How could William decrypt it? Thanks to FREQUENCY ANALYSIS, that is the analysis of how often a letter is used in a specific language.
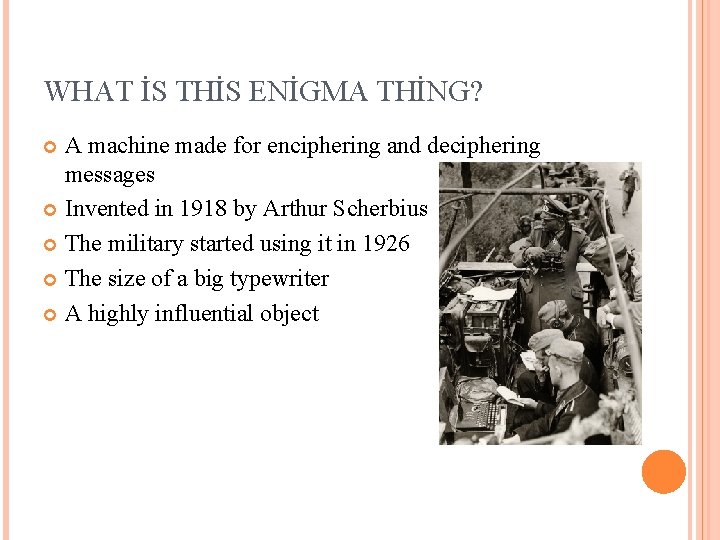
WHAT İS THİS ENİGMA THİNG? A machine made for enciphering and deciphering messages Invented in 1918 by Arthur Scherbius The military started using it in 1926 The size of a big typewriter A highly influential object
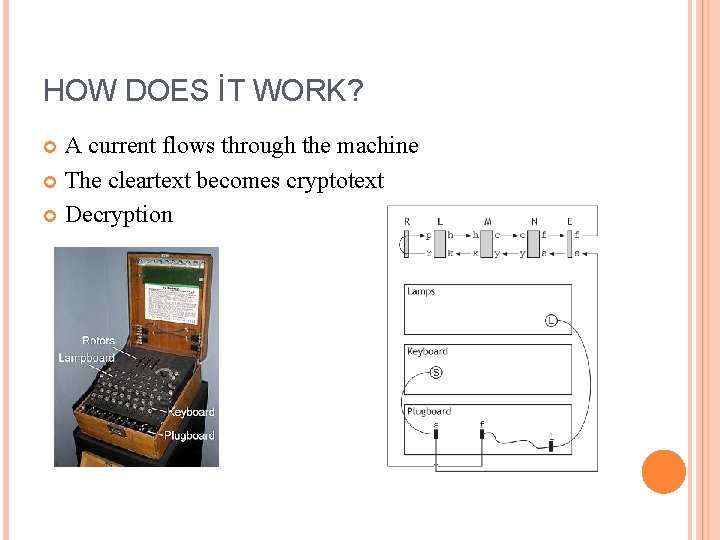
HOW DOES İT WORK? A current flows through the machine The cleartext becomes cryptotext Decryption
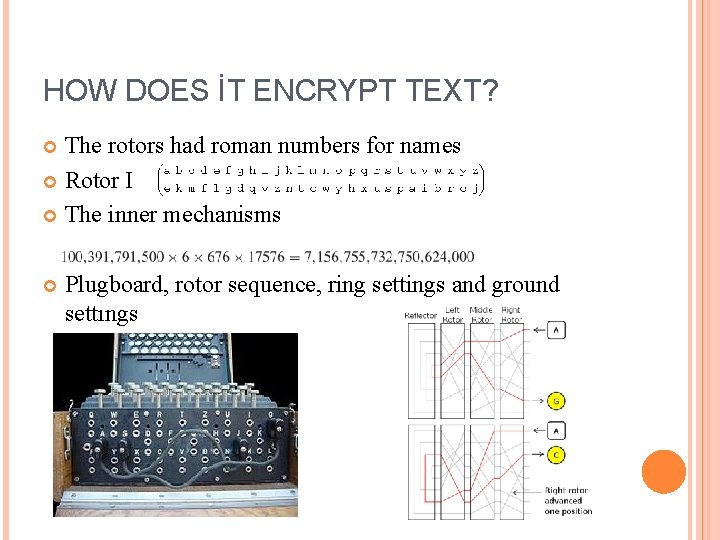
HOW DOES İT ENCRYPT TEXT? The rotors had roman numbers for names Rotor I The inner mechanisms Plugboard, rotor sequence, ring settings and ground settıngs
WHAT MADE ENİGMA SAFE? Around 10114 configurations New settings every day Safe due to the configurations Water soluble ink Different systems for different groups
THE İNFLUENCE ON WWII A betrayers handed the plans for the machine to The Biuro Szyfrów Poland deciphered the code in 1932 Presented the method to the allied forces in 1939 The allied forces found themselves in dilemma "It was thanks to Ultra (the Enigma program) that we won the war. « - Winston Churchill
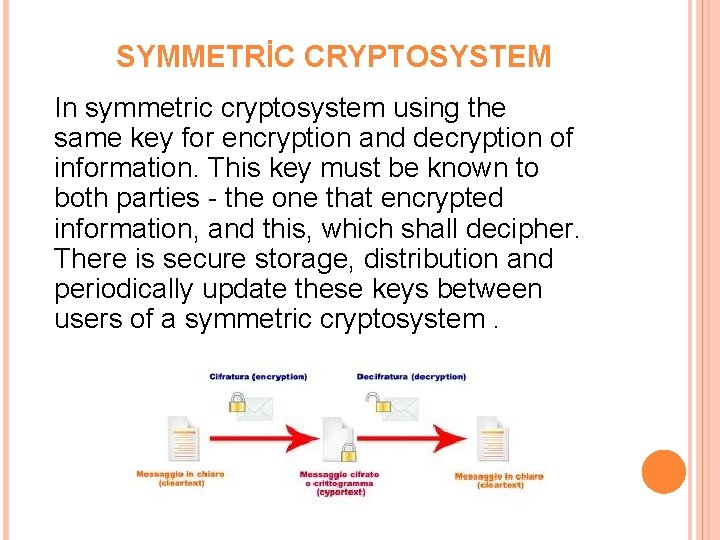
SYMMETRİC CRYPTOSYSTEM In symmetric cryptosystem using the same key for encryption and decryption of information. This key must be known to both parties - the one that encrypted information, and this, which shall decipher. There is secure storage, distribution and periodically update these keys between users of a symmetric cryptosystem.
ASYMMETRİC CRYPTOSYSTEM In an asymmetric cryptosystem need for secure storage of public keys dropped, they are exchanged freely by users or published on Web sites.
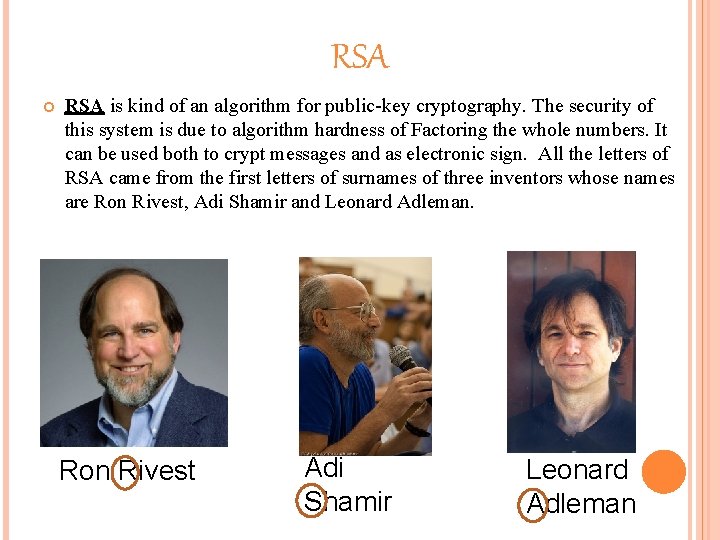
RSA is kind of an algorithm for public-key cryptography. The security of this system is due to algorithm hardness of Factoring the whole numbers. It can be used both to crypt messages and as electronic sign. All the letters of RSA came from the first letters of surnames of three inventors whose names are Ron Rivest, Adi Shamir and Leonard Adleman. Ron Rivest Adi Shamir Leonard Adleman
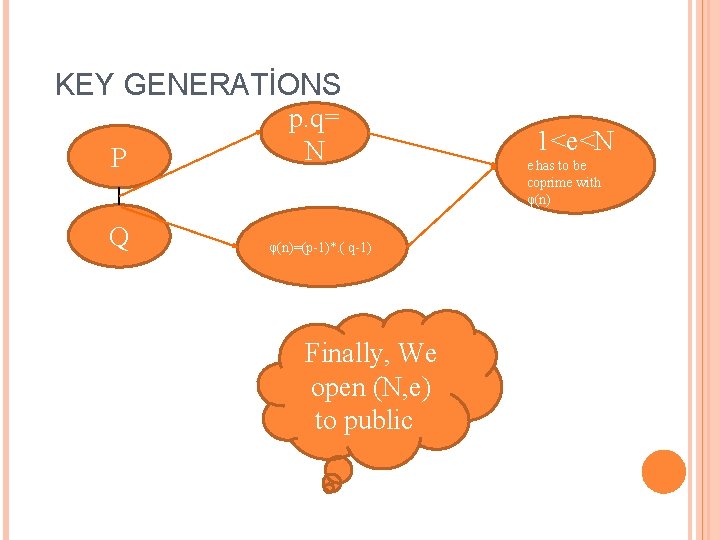
KEY GENERATİONS P Q p. q= N φ(n)=(p-1)*. ( q-1) Finally, We open (N, e) to public 1<e<N e has to be coprime with φ(n)
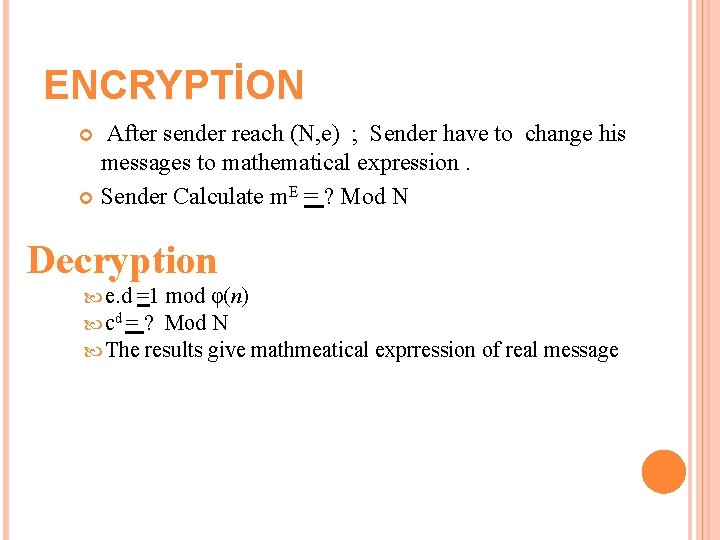
ENCRYPTİON After sender reach (N, e) ; Sender have to change his messages to mathematical expression. Sender Calculate m. E = ? Mod N Decryption e. d =1 mod φ(n) cd = ? Mod N The results give mathmeatical exprression of real message
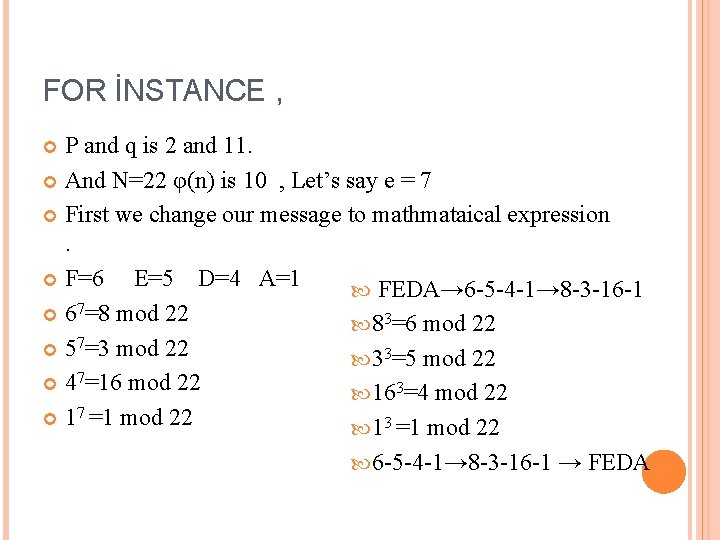
FOR İNSTANCE , P and q is 2 and 11. And N=22 φ(n) is 10 , Let’s say e = 7 First we change our message to mathmataical expression . F=6 E=5 D=4 A=1 FEDA→ 6 -5 -4 -1→ 8 -3 -16 -1 67=8 mod 22 83=6 mod 22 57=3 mod 22 33=5 mod 22 47=16 mod 22 163=4 mod 22 17 =1 mod 22 13 =1 mod 22 6 -5 -4 -1→ 8 -3 -16 -1 → FEDA
ELECTRONİC SİGNATURE SYSTEM Electronic signature algorithm used for encryption, one degree more secure than algorithms using hash function for authentication of the sender. Used asymmetric cryptography key pair - private and public, with one to encrypt and decrypt with the other.
www. jeleznik. org www. google. bg www. wikipedia. org http: //library. thinkquest. org/C 0126342/adfgvx. htm http: //practicalcryptography. com/ciphers/adfgvx-cipher/ http: //illuminations. nctm. org/Lesson. Detail. aspx? id=L 587 http: //cs-exhibitions. uni-klu. ac. at/index. php? id=281 http: //www. braingle. com/brainteasers/codes/vigenere. php http: //www. woodmann. com/crackz/Tutorials/Rsa. htm
- Slides: 47