Cryptography or Smalltalkers 2 Public Key Cryptography Martin
Cryptography or Smalltalkers 2 Public Key Cryptography Martin Kobetic Cincom Smalltalk Development ESUG 2006
Contents l Public Key Algorithms l Encryption (RSA) l Key Establishment (RSA, DH) l Signing – Hashes (SHA, MD 5) – MACs (HMAC, CBC-MAC) – Digital Signatures (RSA, DSA)
Public Key Algorithms l public and private key – hard to compute private from the public – sparse key space => much longer keys l based on “hard” problems – factoring, discrete logarithm l much slower l RSA, DH, El. Gamal l elliptic curves: ECDSA, ECDH, …
Encryption l provides: – confidentiality l symmetric (secret) key ciphers – same (secret) key => encrypt and decrypt – DES, AES, RC 4 l asymmetric (public) key – public key => encrypt – private key => decrypt – RSA, El. Gammal ciphers

RSA (1977) l RSA Security, PKCS #1 modulus n = product of 2 large primes p, q public: e = relatively prime to (p-1)(q-1) private: d = e-1 mod ((p-1)(q-1)) C = Pe mod n [ P < n ] P = Cd mod n l small e => faster encryption
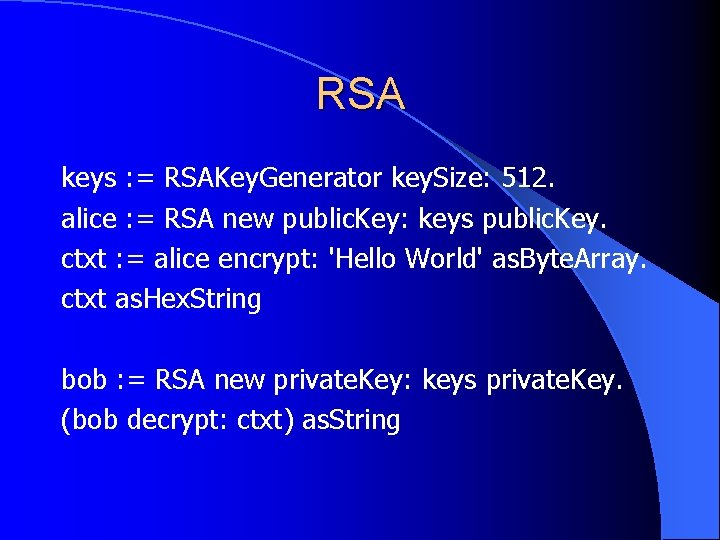
RSA keys : = RSAKey. Generator key. Size: 512. alice : = RSA new public. Key: keys public. Key. ctxt : = alice encrypt: 'Hello World' as. Byte. Array. ctxt as. Hex. String bob : = RSA new private. Key: keys private. Key. (bob decrypt: ctxt) as. String
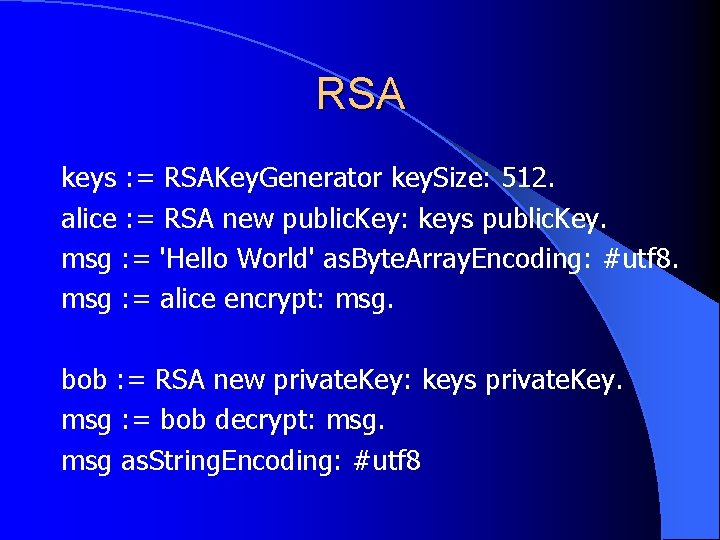
RSA keys : = RSAKey. Generator key. Size: 512. alice : = RSA new public. Key: keys public. Key. msg : = 'Hello World' as. Byte. Array. Encoding: #utf 8. msg : = alice encrypt: msg. bob : = RSA new private. Key: keys private. Key. msg : = bob decrypt: msg as. String. Encoding: #utf 8
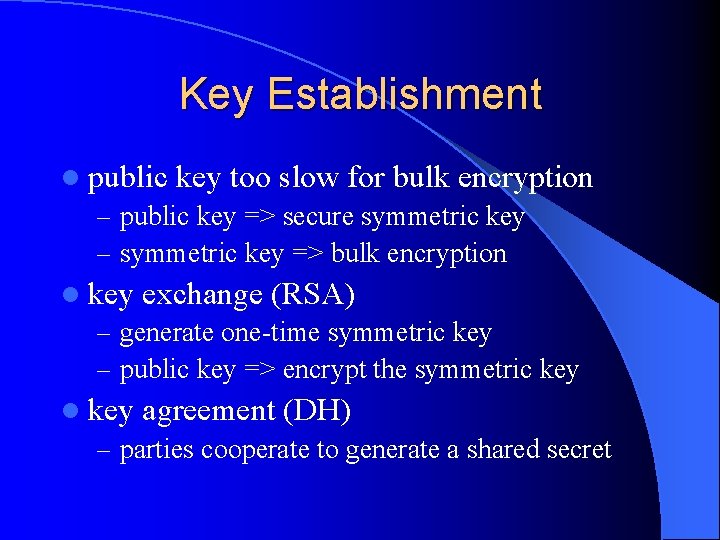
Key Establishment l public key too slow for bulk encryption – public key => secure symmetric key – symmetric key => bulk encryption l key exchange (RSA) – generate one-time symmetric key – public key => encrypt the symmetric key l key agreement (DH) – parties cooperate to generate a shared secret
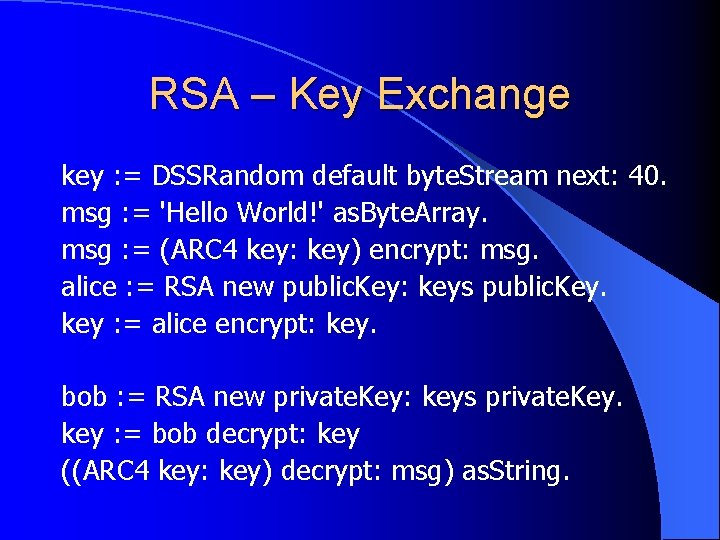
RSA – Key Exchange key : = DSSRandom default byte. Stream next: 40. msg : = 'Hello World!' as. Byte. Array. msg : = (ARC 4 key: key) encrypt: msg. alice : = RSA new public. Key: keys public. Key. key : = alice encrypt: key. bob : = RSA new private. Key: keys private. Key. key : = bob decrypt: key ((ARC 4 key: key) decrypt: msg) as. String.
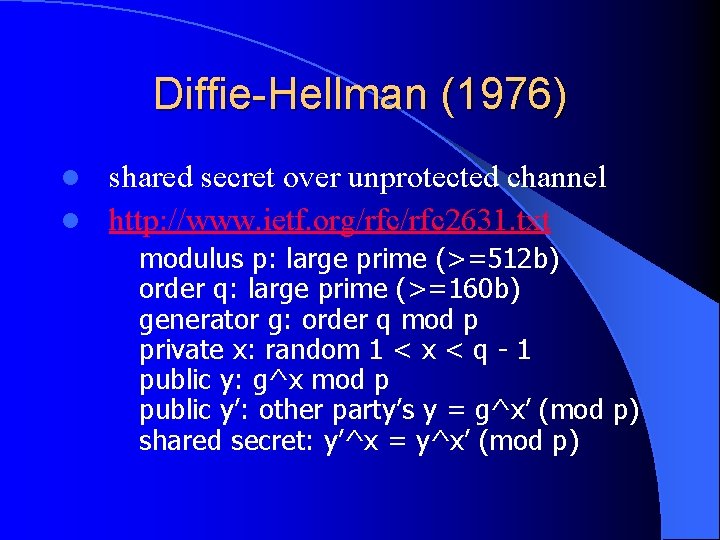
Diffie-Hellman (1976) shared secret over unprotected channel l http: //www. ietf. org/rfc 2631. txt l modulus p: large prime (>=512 b) order q: large prime (>=160 b) generator g: order q mod p private x: random 1 < x < q - 1 public y: g^x mod p public y’: other party’s y = g^x’ (mod p) shared secret: y’^x = y^x’ (mod p)
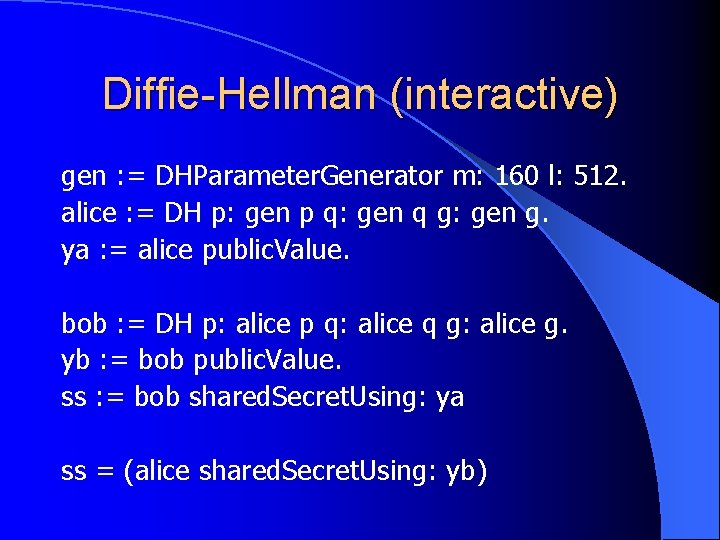
Diffie-Hellman (interactive) gen : = DHParameter. Generator m: 160 l: 512. alice : = DH p: gen p q: gen q g: gen g. ya : = alice public. Value. bob : = DH p: alice p q: alice q g: alice g. yb : = bob public. Value. ss : = bob shared. Secret. Using: ya ss = (alice shared. Secret. Using: yb)
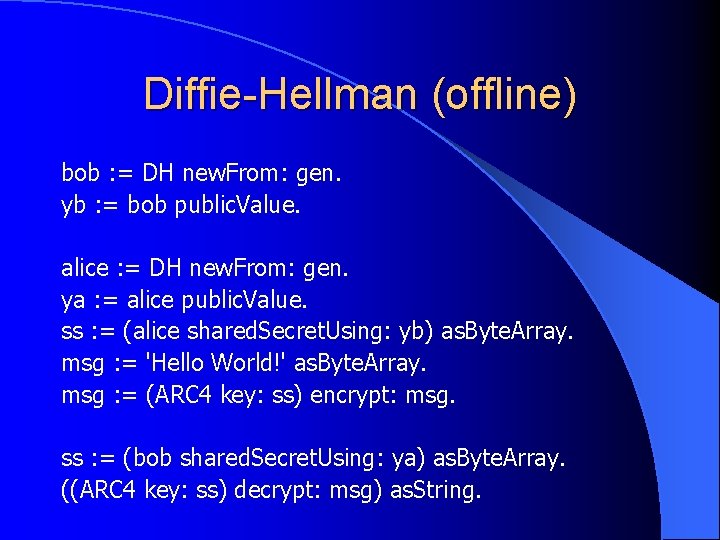
Diffie-Hellman (offline) bob : = DH new. From: gen. yb : = bob public. Value. alice : = DH new. From: gen. ya : = alice public. Value. ss : = (alice shared. Secret. Using: yb) as. Byte. Array. msg : = 'Hello World!' as. Byte. Array. msg : = (ARC 4 key: ss) encrypt: msg. ss : = (bob shared. Secret. Using: ya) as. Byte. Array. ((ARC 4 key: ss) decrypt: msg) as. String.
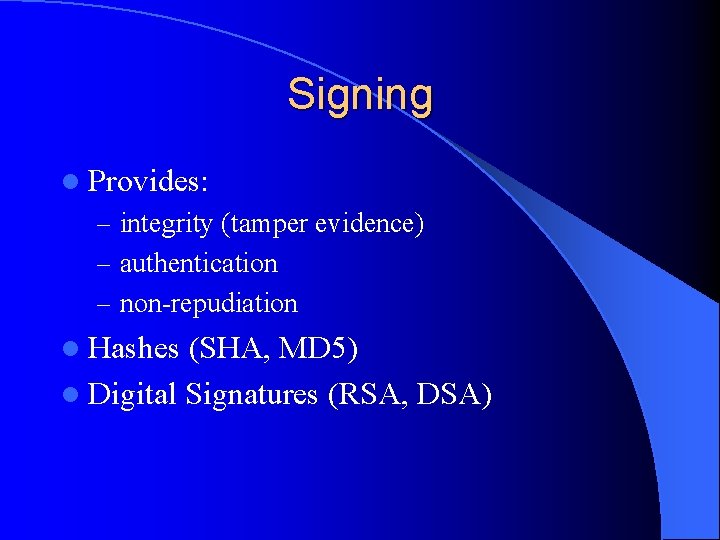
Signing l Provides: – integrity (tamper evidence) – authentication – non-repudiation l Hashes (SHA, MD 5) l Digital Signatures (RSA, DSA)
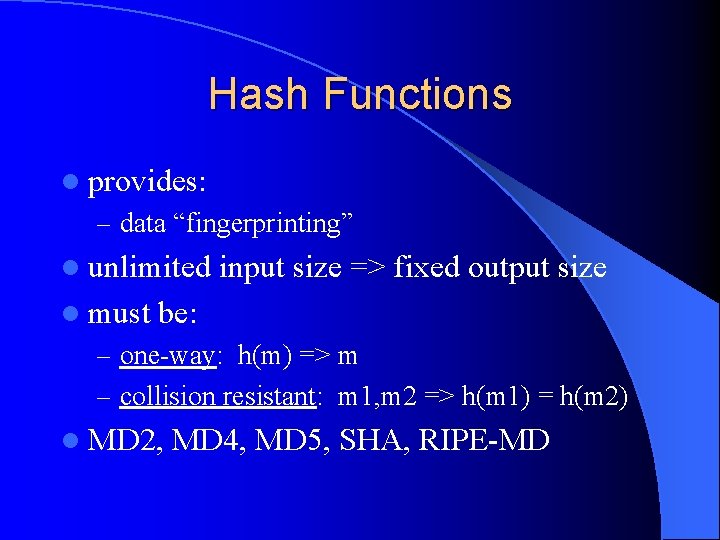
Hash Functions l provides: – data “fingerprinting” l unlimited l must input size => fixed output size be: – one-way: h(m) => m – collision resistant: m 1, m 2 => h(m 1) = h(m 2) l MD 2, MD 4, MD 5, SHA, RIPE-MD
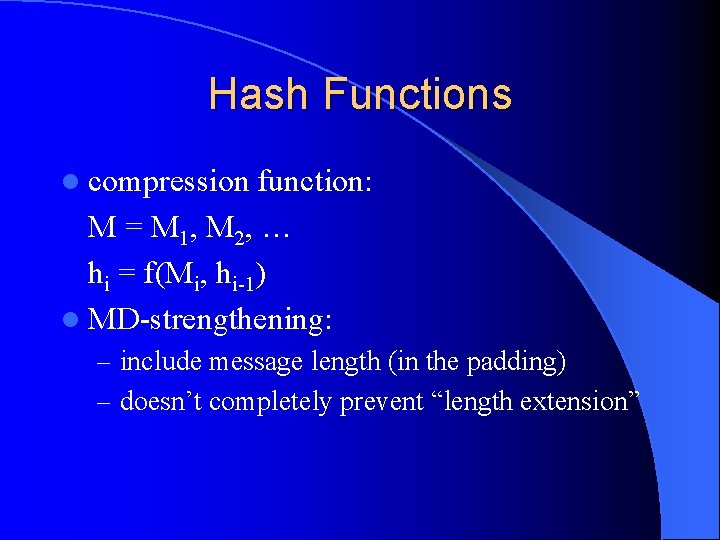
Hash Functions l compression function: M = M 1, M 2, … hi = f(Mi, hi-1) l MD-strengthening: – include message length (in the padding) – doesn’t completely prevent “length extension”
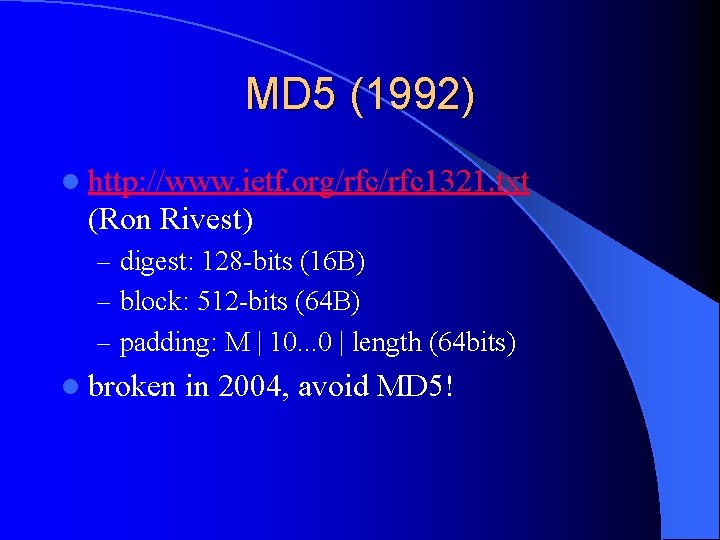
MD 5 (1992) l http: //www. ietf. org/rfc 1321. txt (Ron Rivest) – digest: 128 -bits (16 B) – block: 512 -bits (64 B) – padding: M | 10. . . 0 | length (64 bits) l broken in 2004, avoid MD 5!
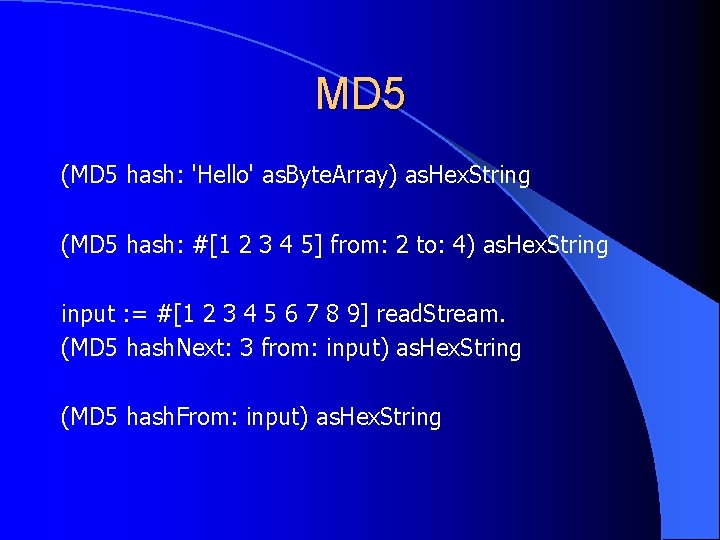
MD 5 (MD 5 hash: 'Hello' as. Byte. Array) as. Hex. String (MD 5 hash: #[1 2 3 4 5] from: 2 to: 4) as. Hex. String input : = #[1 2 3 4 5 6 7 8 9] read. Stream. (MD 5 hash. Next: 3 from: input) as. Hex. String (MD 5 hash. From: input) as. Hex. String
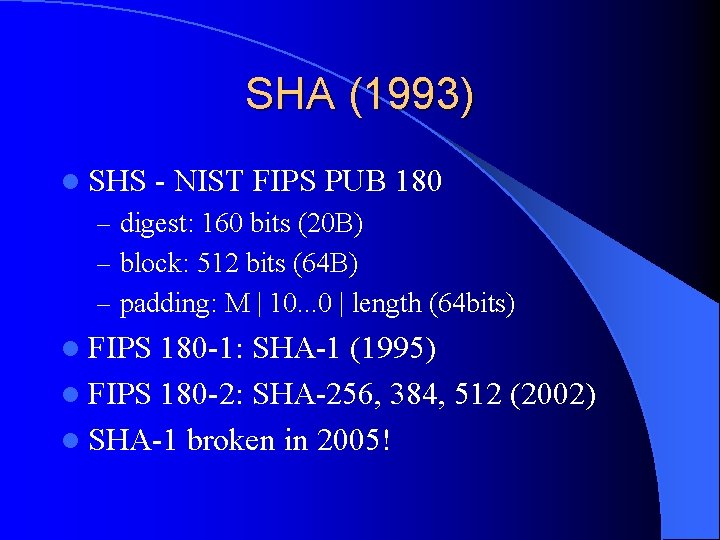
SHA (1993) l SHS - NIST FIPS PUB 180 – digest: 160 bits (20 B) – block: 512 bits (64 B) – padding: M | 10. . . 0 | length (64 bits) l FIPS 180 -1: SHA-1 (1995) l FIPS 180 -2: SHA-256, 384, 512 (2002) l SHA-1 broken in 2005!
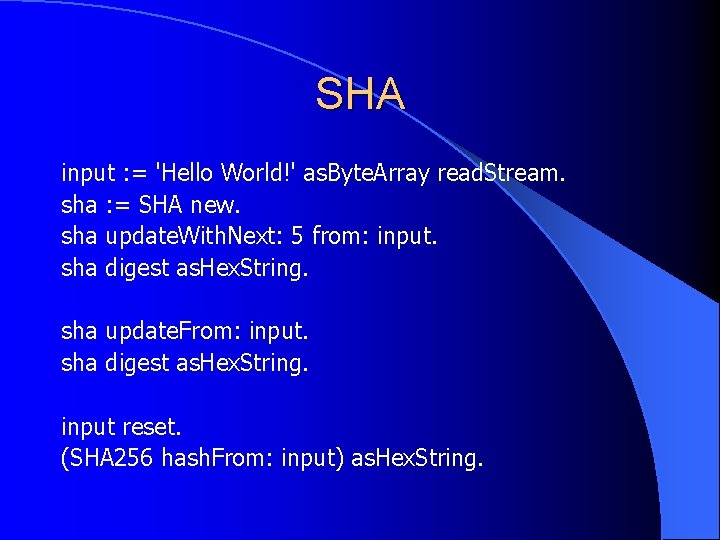
SHA input : = 'Hello World!' as. Byte. Array read. Stream. sha : = SHA new. sha update. With. Next: 5 from: input. sha digest as. Hex. String. sha update. From: input. sha digest as. Hex. String. input reset. (SHA 256 hash. From: input) as. Hex. String.

Digital Signatures authentic, non-reusable, unalterable l signing l – – l uses the private key message, key => signature verification – – uses the public key message, key, signature => true/false
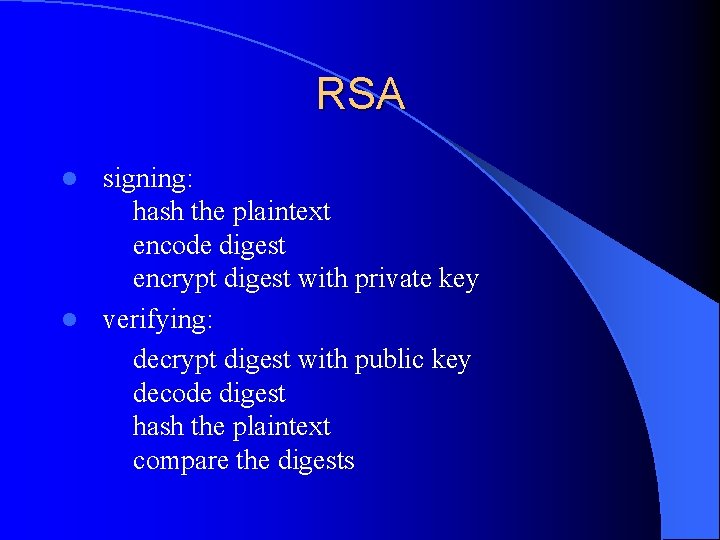
RSA signing: hash the plaintext encode digest encrypt digest with private key l verifying: decrypt digest with public key decode digest hash the plaintext compare the digests l
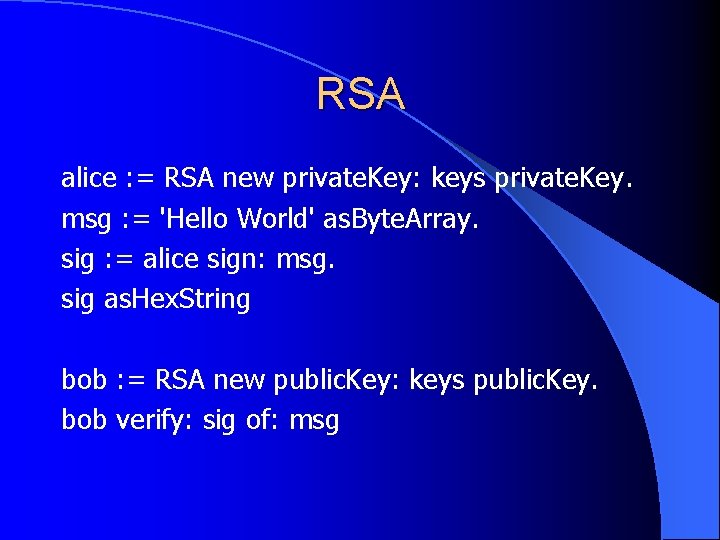
RSA alice : = RSA new private. Key: keys private. Key. msg : = 'Hello World' as. Byte. Array. sig : = alice sign: msg. sig as. Hex. String bob : = RSA new public. Key: keys public. Key. bob verify: sig of: msg
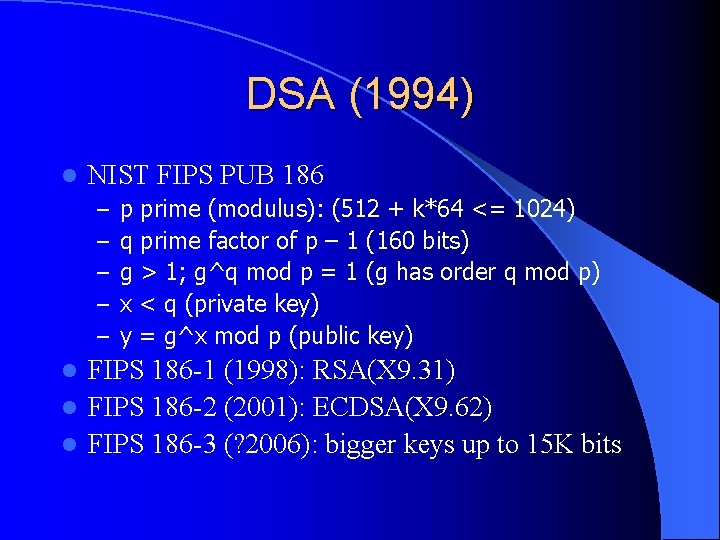
DSA (1994) l NIST FIPS PUB 186 – – – p prime (modulus): (512 + k*64 <= 1024) q prime factor of p – 1 (160 bits) g > 1; g^q mod p = 1 (g has order q mod p) x < q (private key) y = g^x mod p (public key) FIPS 186 -1 (1998): RSA(X 9. 31) l FIPS 186 -2 (2001): ECDSA(X 9. 62) l FIPS 186 -3 (? 2006): bigger keys up to 15 K bits l
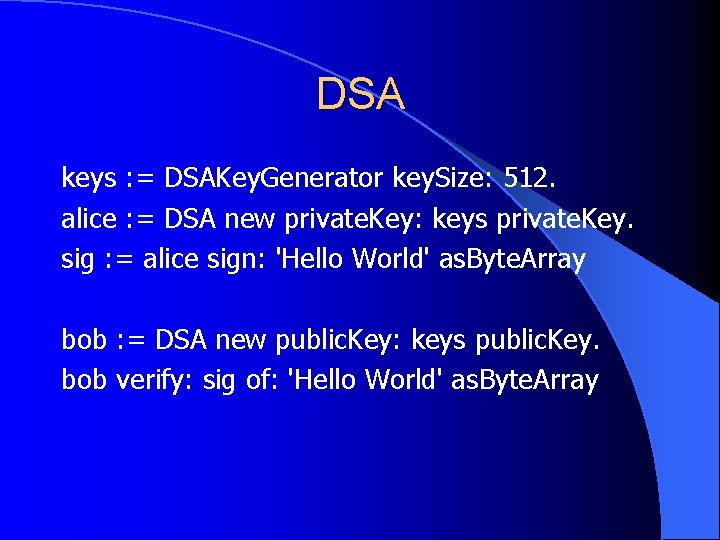
DSA keys : = DSAKey. Generator key. Size: 512. alice : = DSA new private. Key: keys private. Key. sig : = alice sign: 'Hello World' as. Byte. Array bob : = DSA new public. Key: keys public. Key. bob verify: sig of: 'Hello World' as. Byte. Array
![Books l [1] Anderson: Security Engineering l [2] Ferguson, Schneier: Practical Cryptography l [3] Books l [1] Anderson: Security Engineering l [2] Ferguson, Schneier: Practical Cryptography l [3]](http://slidetodoc.com/presentation_image_h/c1541ea7e37a2388b23ba421d2b78420/image-25.jpg)
Books l [1] Anderson: Security Engineering l [2] Ferguson, Schneier: Practical Cryptography l [3] Kahn: The Codebreakers l [4] Menezes, van Oorschot, Vanstone: Handbook of Applied Cryptography l [5] Schneier: Applied Cryptography
- Slides: 25