Cryptography in Mobile Networks Mats Nslund Ericsson Research
Cryptography in Mobile Networks Mats Näslund Ericsson Research mats. naslund@ericsson. com March 4, 2010
Outline • Overview of GSM Cryptography • Some “attacks” on GSM – Lessons to be learnt • Overview of “ 3 G” UMTS Cryptography • The new ”thing”: Cryptography in LTE 2 2010 -03 -04
History • Mobile (wireless) communication has inherent threats – – Eavesdropping Impersonation Connection hijacking. . . • Except early systems (e. g. NMT), use of cryptography has been deemed necessary - Protection of buisness (robust charging of subscribers) - User privacy • Early systems were not perfect and under restrictions. . . 3 2010 -03 -04
GSM Cryptography Overview 4 2010 -03 -04
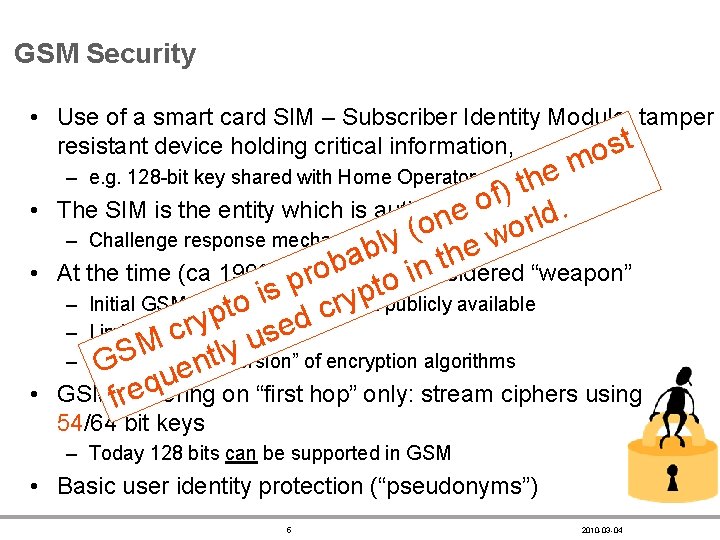
GSM Security • Use of a smart card SIM – Subscriber Identity Module, tamper resistant device holding critical information, ost m e h t ) f o The SIM is the entity which is authenticated. e d l n r o o ( – Challenge response mechanism (one-sided) y he w l b a t b n o At the time (ca 1990) crypto was considered “weapon” i r p o tpublicly available s p i y – Initial GSM algorithms (were) not o d cr t p y rsize e – Limited key c s u M y lversion” S t – Special of encryption algorithms n G “export e u q GSM fciphering on “first hop” only: stream ciphers using re – e. g. 128 -bit key shared with Home Operator • • • 54/64 bit keys – Today 128 bits can be supported in GSM • Basic user identity protection (“pseudonyms”) 5 2010 -03 -04
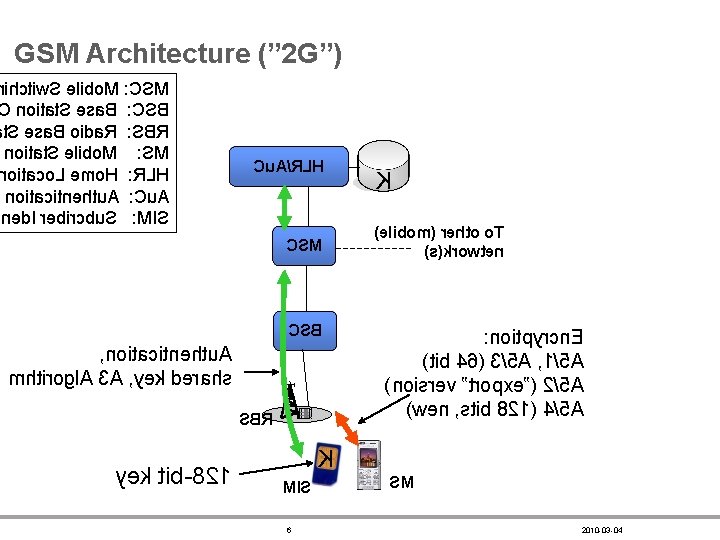
GSM Architecture (” 2 G”) ihctiw. S elibo. M : CSM noitat. S esa. B : CSB t. S esa. B oida. R : SBR noitat. S elibo. M : SM oitaco. L emo. H : RLH noitacitnehtu. A : Cu. A ned. I rebircbu. S : MIS Cu. A/RLH CSM CSB , noitacitnehtu. A mhtirogl. A 3 A , yek derahs SBR yek tib-821 K )elibom( rehto o. T )s(krowten : noitpyrcn. E )tib 46( 3/5 A , 1/5 A )noisrev ”tropxe”( 2/5 A )wen , stib 821( 4/5 A K MIS 6 SM 2010 -03 -04
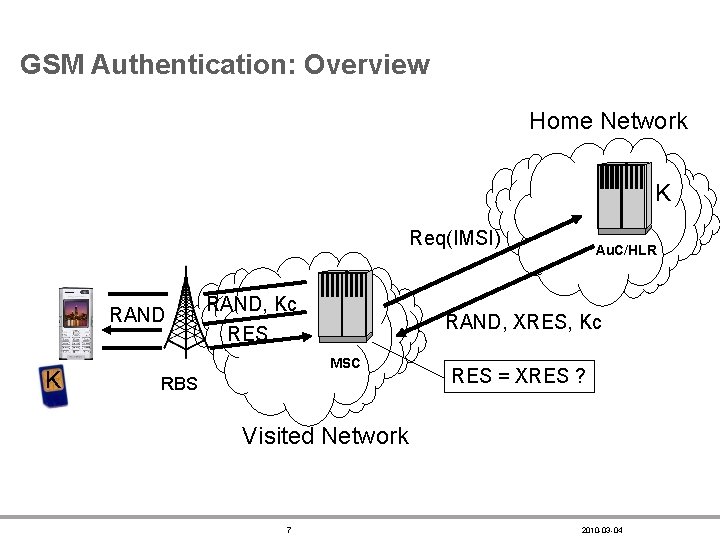
GSM Authentication: Overview Home Network K Req(IMSI) RAND K RAND, Kc RES Au. C/HLR RAND, XRES, Kc MSC RBS RES = XRES ? Visited Network 7 2010 -03 -04

GSM Authentication: Details A 3 and A 8: Authentication and key derivation (proprietary) A 5: encryption (A 5/1 -4, standardized) Note: one-sided authentication Phone SIM Ki (128) A 3 A 8 frame# data/speech RAND (128) RES (32) Kc (64) A 5/x 8 encrypted frame Bit-by-bit, stream cipher 2010 -03 -04
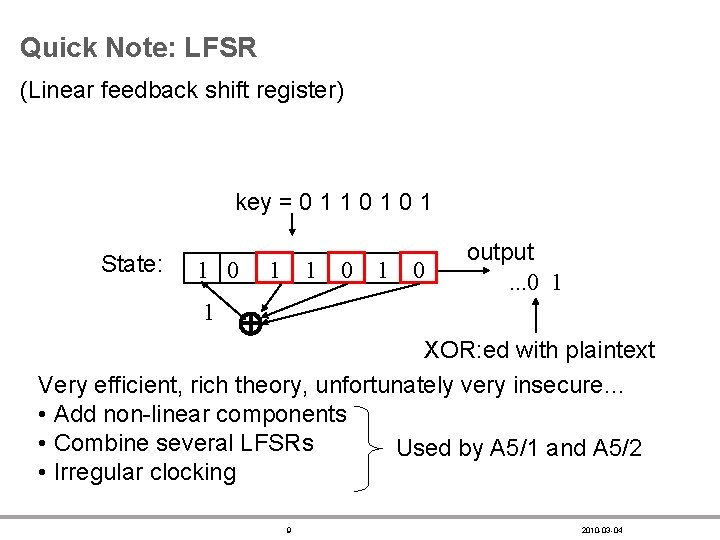
Quick Note: LFSR (Linear feedback shift register) key = 0 1 1 0 1 State: 10 01 1 1 10 01 output. . . 0 1 XOR: ed with plaintext Very efficient, rich theory, unfortunately very insecure… • Add non-linear components • Combine several LFSRs Used by A 5/1 and A 5/2 • Irregular clocking 9 2010 -03 -04
August 2003: Attack on A 5/2 Published 10 2010 -03 -04
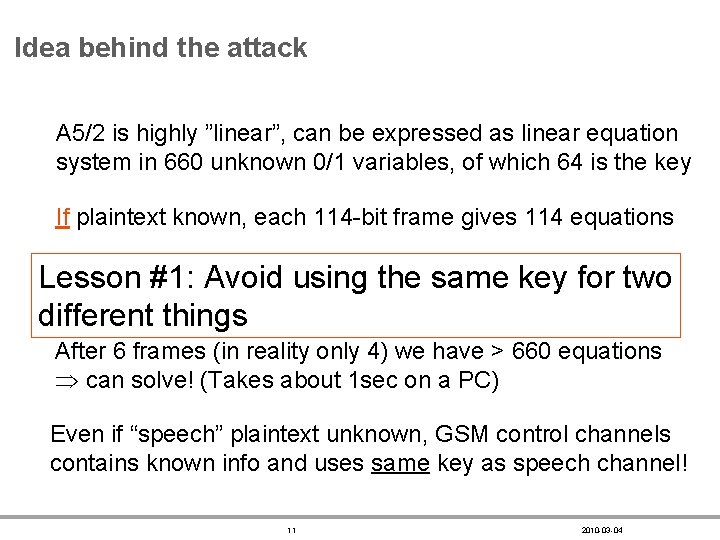
Idea behind the attack A 5/2 is highly ”linear”, can be expressed as linear equation system in 660 unknown 0/1 variables, of which 64 is the key If plaintext known, each 114 -bit frame gives 114 equations Only difference between frames is that frame number Lesson #1: Avoid using the same key for two increases by one. different things After 6 frames (in reality only 4) we have > 660 equations can solve! (Takes about 1 sec on a PC) Even if “speech” plaintext unknown, GSM control channels contains known info and uses same key as speech channel! 11 2010 -03 -04
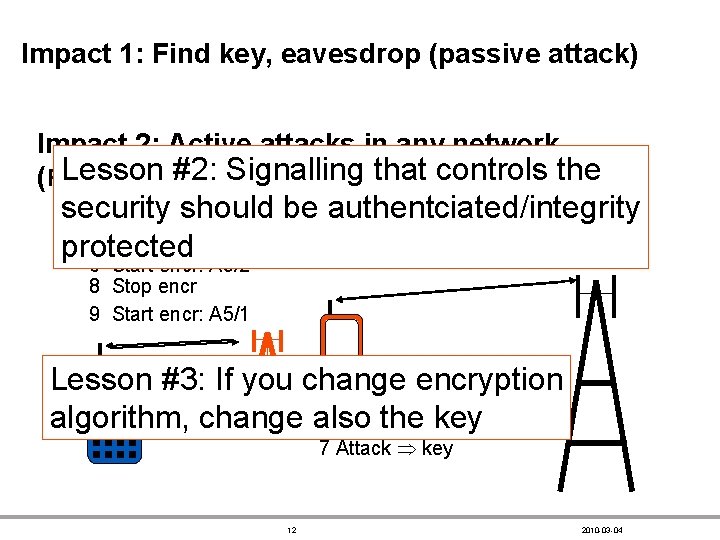
Impact 1: Find key, eavesdrop (passive attack) Impact 2: Active attacks in any network Lesson #2: Signalling that controls (False base-station/man-in-the-middle attacks)the security 1 RAND 2 RAND should be authentciated/integrity 4 RES 3 RES protected 5 Start encr: A 5/1 6 Start encr: A 5/2 8 Stop encr 9 Start encr: A 5/1 Lesson #3: If you change encryption algorithm, change also the key 7 Attack key 12 2010 -03 -04
Note • A 5/2 is an ”export” version, not used in Sweden (or Europe) • Attack does not apply to A 5/1, A 5/3 • Various countermeasures proposed but expensive to upgrade all equipment – Adding integrity, change of keys as proposed on previous slide fall into the ”not-for-free” category • Simple and quite good solution is to phase out A 5/2 - This is in principle done 13 2010 -03 -04
GSM Summary • • GSM was desiged in the ”dark ages” of crypto It addresses the threats that were considered at the time It targeted a 10 -year ”economic lifetime” The best feature of GSM security is that securiy is built-in – as a user, you don’t need to do ”configuration” etc 14 2010 -03 -04
UMTS Security Overview 15 2010 -03 -04
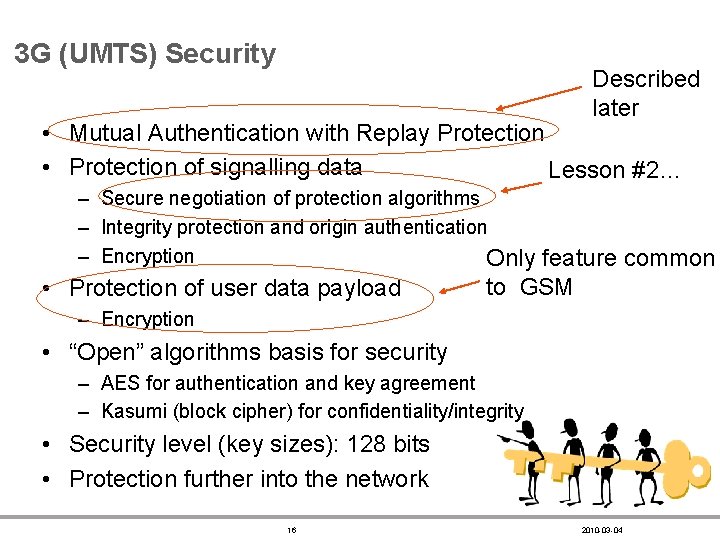
3 G (UMTS) Security Described later • Mutual Authentication with Replay Protection • Protection of signalling data Lesson #2… – Secure negotiation of protection algorithms – Integrity protection and origin authentication – Encryption Only feature common • Protection of user data payload to GSM – Encryption • “Open” algorithms basis for security – AES for authentication and key agreement – Kasumi (block cipher) for confidentiality/integrity • Security level (key sizes): 128 bits • Protection further into the network 16 2010 -03 -04
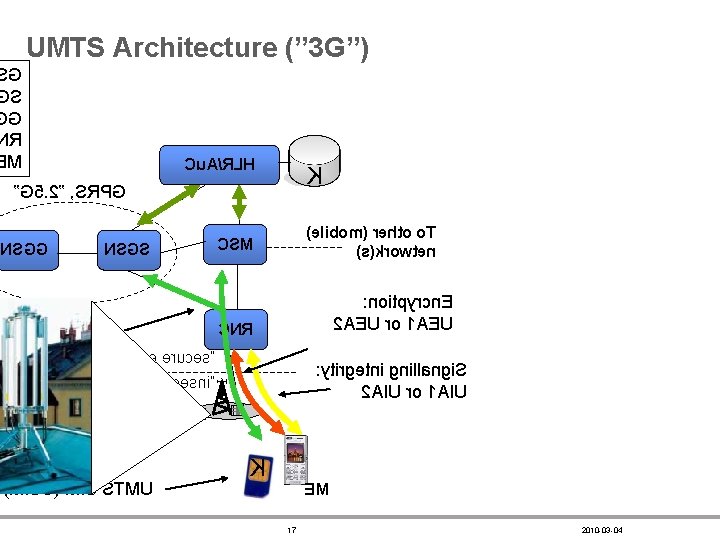
UMTS Architecture (” 3 G”) G S G R M Cu. A/RLH K ”G 5. 2” , SRPG NSGG itnehtu. A eganeli. M )elibom( rehto o. T )s(krowten CSM NSGS : noitpyrcn. E 2 AEU ro 1 AEU CNR ”vne eruces” : ytirgetni gnillangi. S 2 AIU ro 1 AIU ”vne erucesni” Bedo. N )MISU( MIS STMU K EM 17 2010 -03 -04
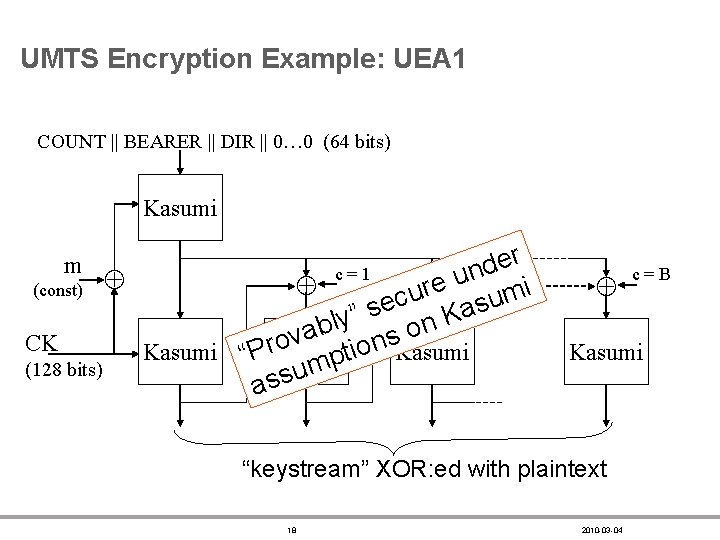
UMTS Encryption Example: UEA 1 COUNT || BEARER || DIR || 0… 0 (64 bits) Kasumi r e d c=1 c= n 2 u e (const) i r u m c u e s s a ” K ly n b o a v s CK o n Kasumi o i Kasumi “Pr. Kasumi t p m (128 bits) u ass m Kasumi “keystream” XOR: ed with plaintext 18 c=B 2010 -03 -04
Note • There are no known security problems with UMTS • HSPA (a. k. a. ”Mobile broadband”, ”Turbo 3 G”, . . . ) is from crypto/security point of view identical to 3 G/UMTS – You can feel safe when using it! 19 2010 -03 -04
LTE: Long Term Evolution

Disclaimer on Notation • ”LTE” refers only to the radio part of the new standard • Also other parts of the mobile network is upgraded – Refered to as EPC, ”Evolved Packet Core” • Will for simplicty use ”LTE” to denote the entire architecture • If you do look at the standards document (3 GPP TS 33. 401) you will not see the same names for keys etc used here 21 2010 -03 -04
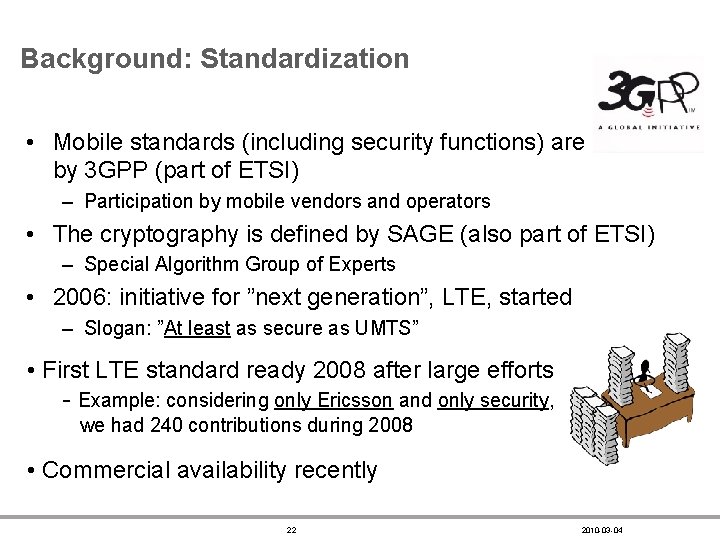
Background: Standardization • Mobile standards (including security functions) are defined by 3 GPP (part of ETSI) – Participation by mobile vendors and operators • The cryptography is defined by SAGE (also part of ETSI) – Special Algorithm Group of Experts • 2006: initiative for ”next generation”, LTE, started – Slogan: ”At least as secure as UMTS” • First LTE standard ready 2008 after large efforts - Example: considering only Ericsson and only security, we had 240 contributions during 2008 • Commercial availability recently 22 2010 -03 -04
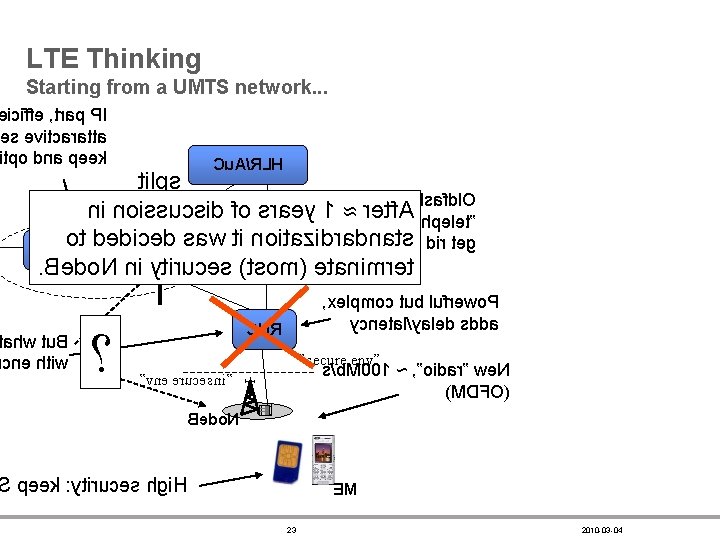
LTE Thinking Starting from a UMTS network. . . iciffe , trap PI es evitcaratta tpo dna peek Cu. A/RLH tilps oihsafdl. O ni noissucsid fo sraey 1 rdee: t”nfy. A nohpelet” ot dedi. Nc. Se. Gd. S saw ti Cn. So. Mitazidradna!ttisfo dir teg NSGG. Bedo. N ni ytiruces )tsom( etanimret ahw tu. B cne htiw ? , xelpmoc tub lufrewo. P ycnetal/yaled sdda CNR ”secure env” s/b. M 001 ~ , ”oidar” we. N )MDFO( ”vne erucesni” Bedo. N peek : ytiruces hgi. H EM 23 2010 -03 -04
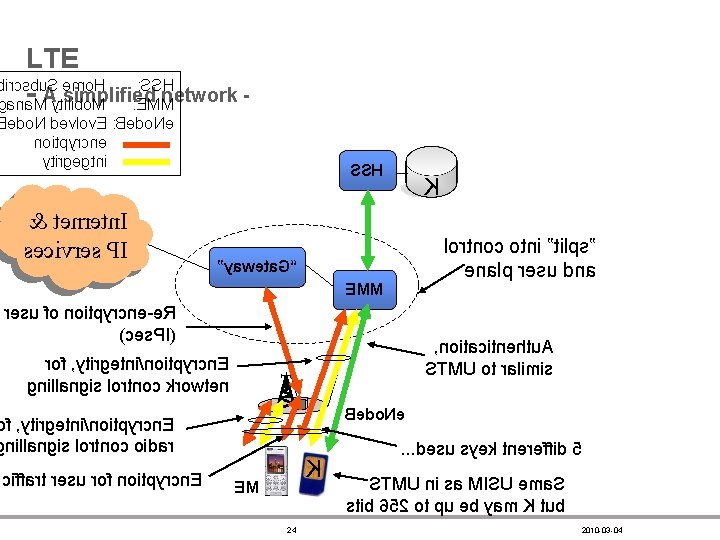
LTE ircsbu. S emo. H : SSH A simplified network ana. M ytilibo. M : EMM edo. N devlov. E : Bedo. Ne noitpyrcne ytirgegtni & tenretn. I secivres PI SSH K lortnoc otni ”tilps” enalp resu dna ”yaweta. G“ EMM resu fo noitpyrcne-e. R )ces. PI( , noitacitnehtu. A STMU ot ralimis rof , ytirgetni/noitpyrcn. E gnillangis lortnoc krowten Bedo. Ne f , ytirgetni/noitpyrcn. E nillangis lortnoc oidar ciffart resu rof noitpyrcn. E K EM 24 . . . desu syek tnereffid 5 STMU ni sa MISU ema. S stib 652 ot pu eb yam K tub 2010 -03 -04
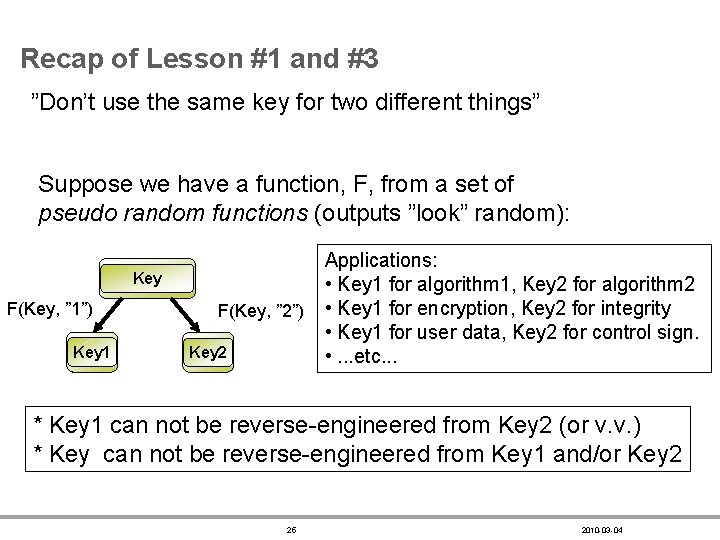
Recap of Lesson #1 and #3 ”Don’t use the same key for two different things” Suppose we have a function, F, from a set of pseudo random functions (outputs ”look” random): Key F(Key, ” 1”) Key 1 F(Key, ” 2”) Key 2 Applications: • Key 1 for algorithm 1, Key 2 for algorithm 2 • Key 1 for encryption, Key 2 for integrity • Key 1 for user data, Key 2 for control sign. • . . . etc. . . * Key 1 can not be reverse-engineered from Key 2 (or v. v. ) * Key can not be reverse-engineered from Key 1 and/or Key 2 25 2010 -03 -04
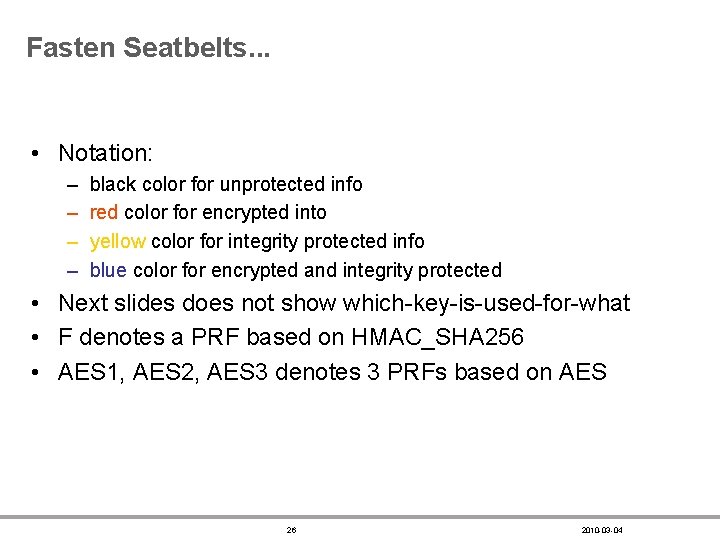
Fasten Seatbelts. . . • Notation: – – black color for unprotected info red color for encrypted into yellow color for integrity protected info blue color for encrypted and integrity protected • Next slides does not show which-key-is-used-for-what • F denotes a PRF based on HMAC_SHA 256 • AES 1, AES 2, AES 3 denotes 3 PRFs based on AES 26 2010 -03 -04
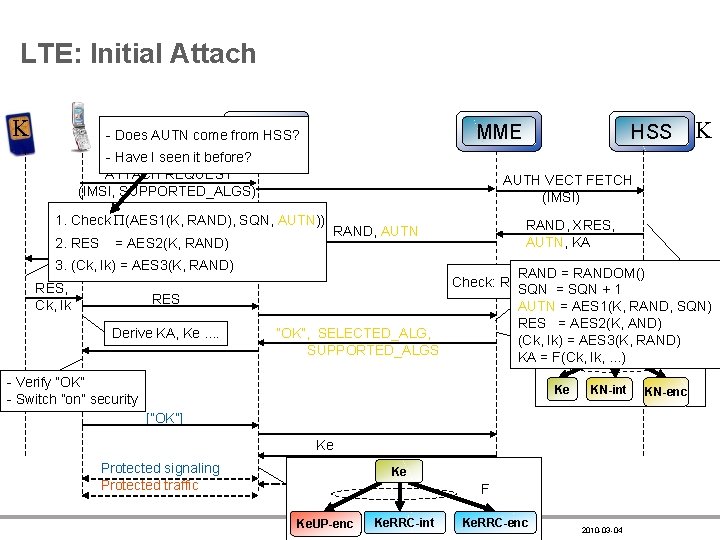
LTE: Initial Attach K e. NB - Does AUTN come from HSS? MME - Have I seen it before? ATTACH REQUEST (IMSI, SUPPORTED_ALGS) = AES 2(K, RAND) 3. (Ck, Ik) = AES 3(K, RAND) RES, Ck, Ik RES Derive KA, Ke. . K AUTH VECT FETCH (IMSI) 1. Check (AES 1(K, RAND), SQN, AUTN)) 2. RES HSS RAND, XRES, AUTN, KA RAND, AUTN RAND = RANDOM() Check: RES == XRES ? ? SQN = SQN + 1 AUTN = AES 1(K, RAND, SQN) RES = AES 2(K, AND) ”OK”, SELECTED_ALG, (Ck, Ik) = AES 3(K, KA RAND) SUPPORTED_ALGS F KA = F(Ck, Ik, . . . ) - Verify ”OK” - Switch ”on” security Ke KN-int [”OK”] Ke Protected signaling Protected traffic Ke F 27 Ke. UP-enc Ke. RRC-int Ke. RRC-enc 2010 -03 -04 KN-enc
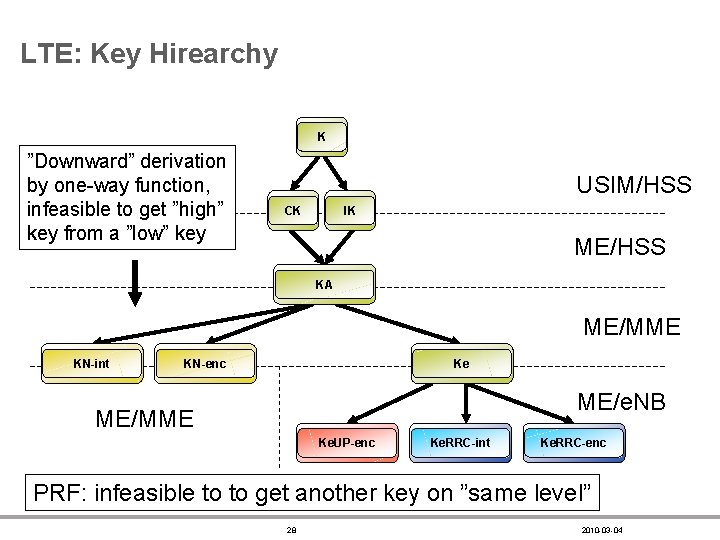
LTE: Key Hirearchy K ”Downward” derivation by one-way function, infeasible to get ”high” key from a ”low” key USIM/HSS CK IK ME/HSS KA ME/MME KN-int KN-enc Ke ME/e. NB ME/MME Ke. UP-enc Ke. RRC-int Ke. RRC-enc PRF: infeasible to to get another key on ”same level” 28 2010 -03 -04
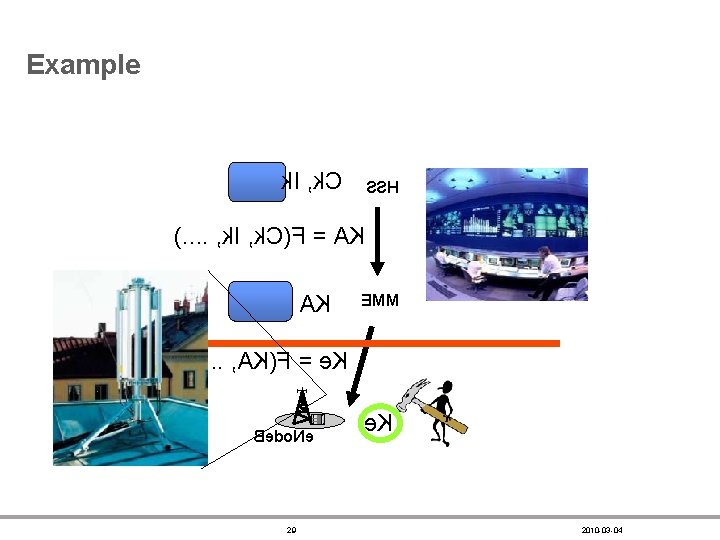
Example k. I , k. C SSH ). . , k. I , k. C(F = AK AK EMM ). . , AK(F = e. K Bedo. Ne 29 e. K 2010 -03 -04
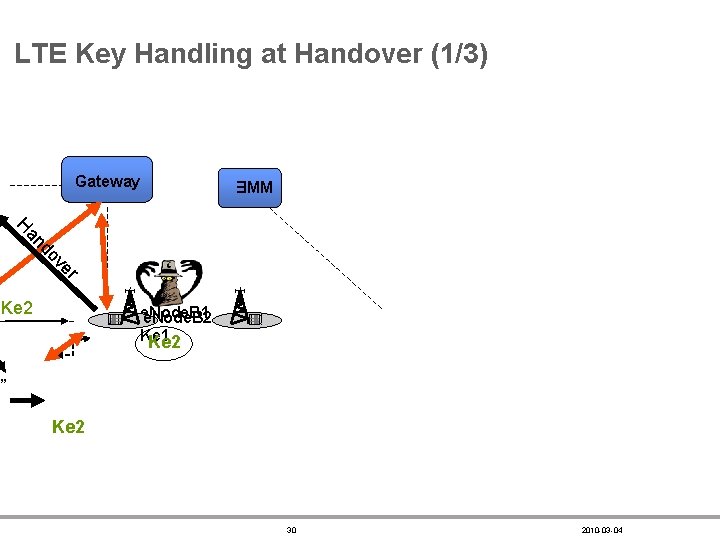
LTE Key Handling at Handover (1/3) Gateway EMM r ve do an H Ke 2 e. Node. B 1 e. Node. B 2 Ke 1 Ke 2 ” Ke 2 30 2010 -03 -04
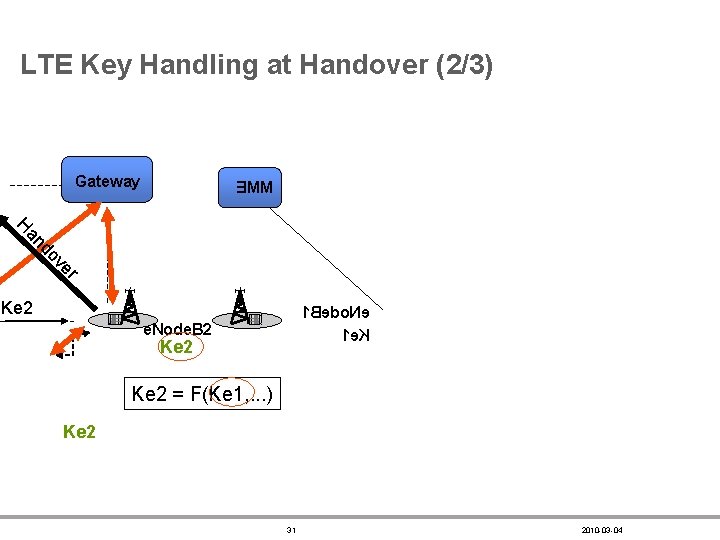
LTE Key Handling at Handover (2/3) Gateway EMM r ve do an H Ke 2 1 Bedo. Ne 1 e. K e. Node. B 2 Ke 2 = F(Ke 1, . . . ) Ke 2 31 2010 -03 -04
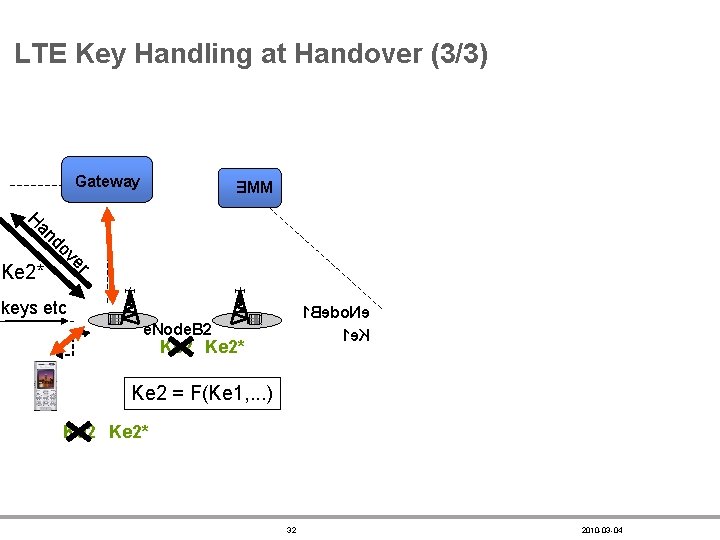
LTE Key Handling at Handover (3/3) Gateway EMM an H r ve do Ke 2* keys etc 1 Bedo. Ne 1 e. K e. Node. B 2 Ke 2* Ke 2 = F(Ke 1, . . . ) Ke 2* 32 2010 -03 -04
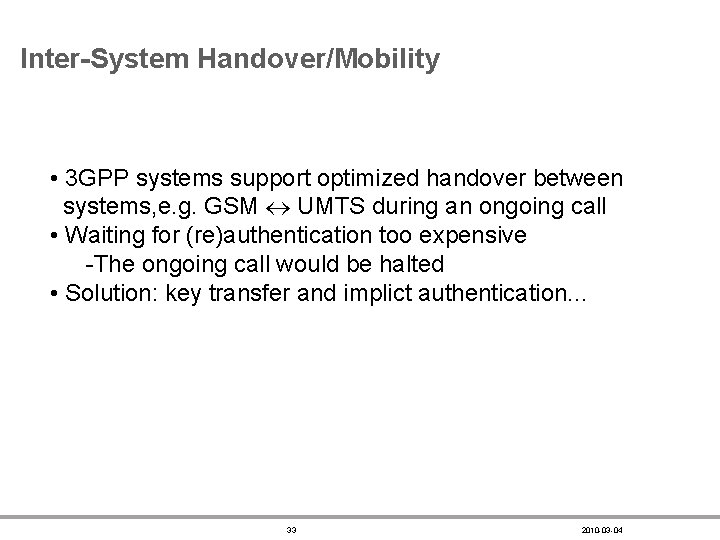
Inter-System Handover/Mobility • 3 GPP systems support optimized handover between systems, e. g. GSM UMTS during an ongoing call • Waiting for (re)authentication too expensive -The ongoing call would be halted • Solution: key transfer and implict authentication. . . 33 2010 -03 -04
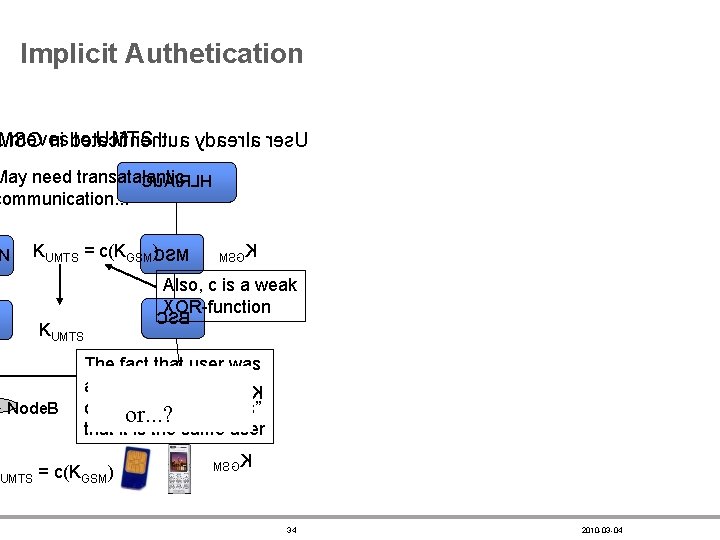
Implicit Authetication . moves SG ni dto et. UMTS acitnehtua ydaerla res. U May need transatalantic Cu. A/RLH communication. . . N KUMTS = c(KGSM)CSM MSGK Also, c is a weak XOR-function KUMTS Node. B CSB The fact that user was able to produce the K MSG correct K ”proves” SB R UMTS or. . . ? that it is the same user UMTS = c(KGSM) MSGK 34 2010 -03 -04
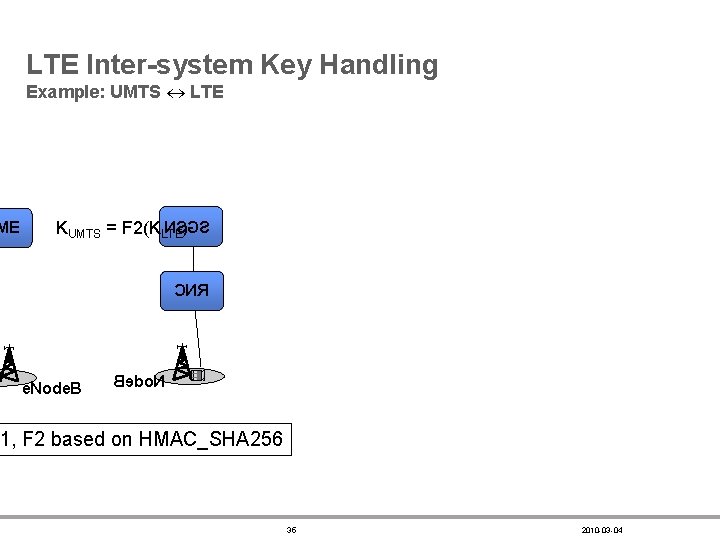
ME LTE Inter-system Key Handling Example: UMTS LTE NS)GS KUMTS = F 2(KLTE CNR e. Node. B Bedo. N 1, F 2 based on HMAC_SHA 256 35 2010 -03 -04
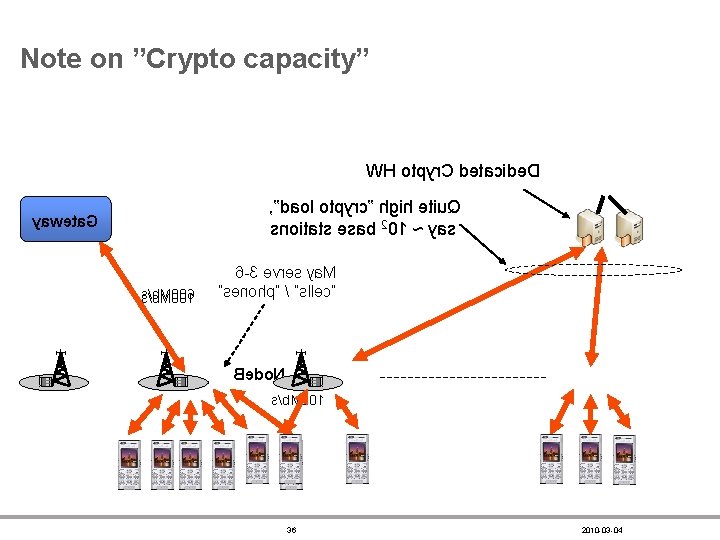
Note on ”Crypto capacity” WH otpyr. C detacide. D , ”daol otpyrc” hgih etiu. Q snoitats esab 201 ~ yas yaweta. G ss//b b. M M 0 00 06 1 6 -3 evres ya. M ”senohp” / ”sllec” Bedo. N s/b. M 001 36 2010 -03 -04
LTE Crypto Algorithms. . . • Key derivation (128 or 256 bits) functions using – AES on the USIM card – HMAC_SHA 256 in ”the phone” • Integrity protection – AES-CMAC – Function based on polynomials over finite fields • Can be ”proven” to be secure • Encryption – AES-Counter. Mode – SNOW 3 G – ”The chineese algorithm” 37 2010 -03 -04
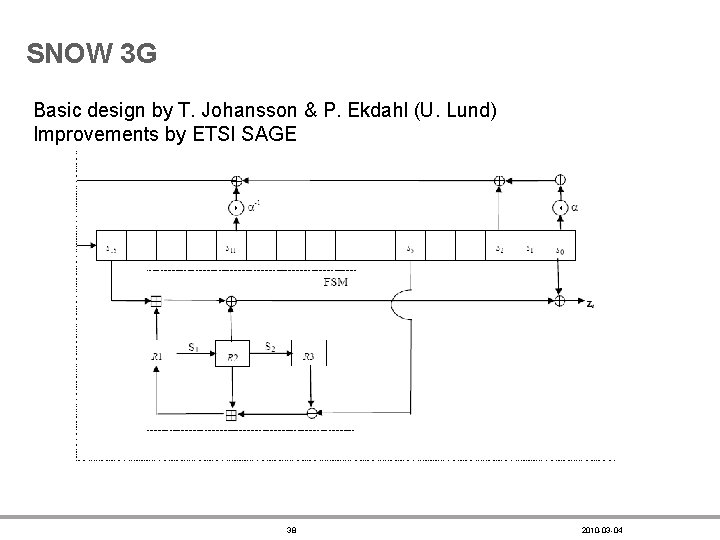
SNOW 3 G Basic design by T. Johansson & P. Ekdahl (U. Lund) Improvements by ETSI SAGE 38 2010 -03 -04
Summary • Despite some attacks on GSM security, the security is so far pretty much a success story Main reason: convenience and invisibility to user • UMTS crypto significantly improved, use with confidence Main reason: free world, longer keys, “open” standard • LTE much more complex, needed to meet “at least as secure as 3 G” Main reason: security “ends” at the base station 39 The End 2010 -03 -04

40 2010 -03 -04
- Slides: 40