Cryptography Enabled RFID and NVRAM Sudhanshu Khanna Ben
Cryptography Enabled RFID and NVRAM Sudhanshu Khanna Ben Calhoun RLP VLSI Group, University of Virginia
Outline n Privacy and Security threats of RFIDs n Technical Challenges in implementing cryptography in RFIDs n Proposed Solutions: NVRAM is key n Chip plans
RFIDs: Widespread and Ubiquitous n Supply Chain Management & Retail q n Wireless Payment Systems q n Wal-Mart, Gillette, Benetton EZ-Pass, Speedpass Building Access Cards, Car Keyless Entry
Privacy & Security Concerns n Tags respond to any reader that queries them n Tags can be queried wirelessly n Tags maintain no record of being queried n Users often don’t know they are using RFID
Adversary Models n Corporate Espionage: q q Gather competitors supply chain data, inventory status Gain access to customer preferences/patterns without their consent Wiping out inventory data Denial of service by spamming RF
Adversary Models n Personal Privacy Threats: q q Tracking an individual using knowledge of the RFID he holds. E. g. People have shown how to track anyone using Nike+, which uses an active RFID tag. Leaking of personal information. E. g. Prescriptions Finding individuals who hold some (valuable) item based on the items RFID tag Cloning a EZ-pass or Building access card
Existing Privacy Features on Tags n Kill command q q n E. g. Kill a tag on checkout But you can’t use the tag anymore…. E. g. your “smartrefrigerator” wont be able to detect that your milk is too old Passwords q q q Tag only responds to a reader that gives the correct password Thus, if all tags use same password, the system becomes to vulnerable. Alternatively use per-tag password Need to maintain extensive tag-password binding
Implementation Challenge n n Main security challenges come from resource constraints. EPC tags ~ 5 cents. Gate count, memory, power, performance, die space, are all tightly constrained Encryption solution should add only a fraction to above resources !
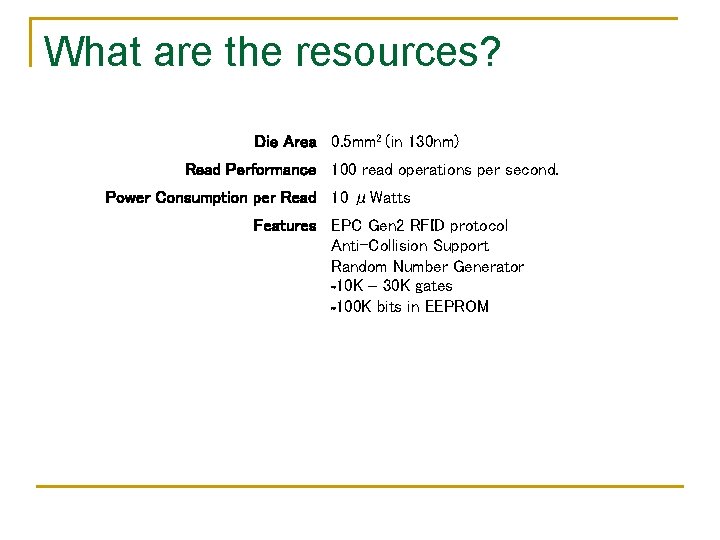
What are the resources? Die Area 0. 5 mm 2 (in 130 nm) Read Performance 100 read operations per second. Power Consumption per Read 10 μWatts Features EPC Gen 2 RFID protocol Anti-Collision Support Random Number Generator ~10 K – 30 K gates ~100 K bits in EEPROM
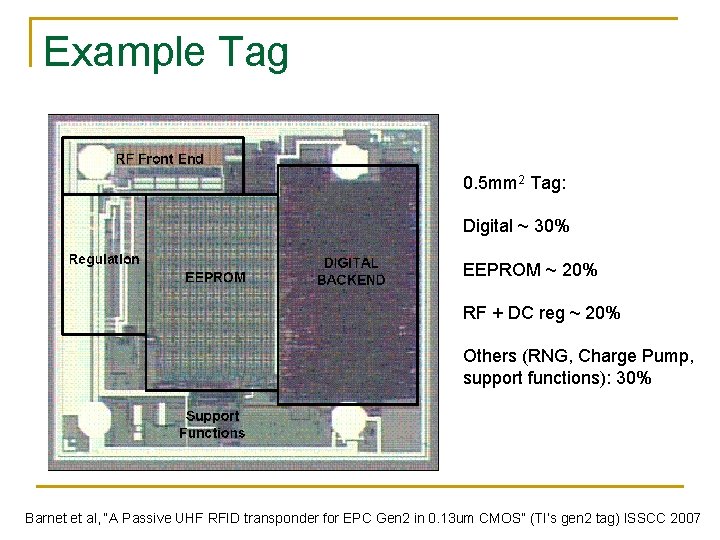
Example Tag 0. 5 mm 2 Tag: Digital ~ 30% EEPROM ~ 20% RF + DC reg ~ 20% Others (RNG, Charge Pump, support functions): 30% Barnet et al, “A Passive UHF RFID transponder for EPC Gen 2 in 0. 13 um CMOS” (TI’s gen 2 tag) ISSCC 2007
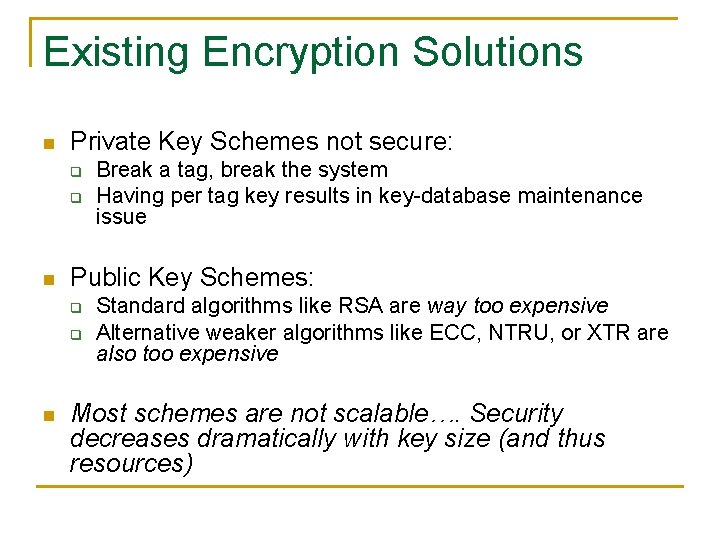
Existing Encryption Solutions n Private Key Schemes not secure: q q n Public Key Schemes: q q n Break a tag, break the system Having per tag key results in key-database maintenance issue Standard algorithms like RSA are way too expensive Alternative weaker algorithms like ECC, NTRU, or XTR are also too expensive Most schemes are not scalable…. Security decreases dramatically with key size (and thus resources)
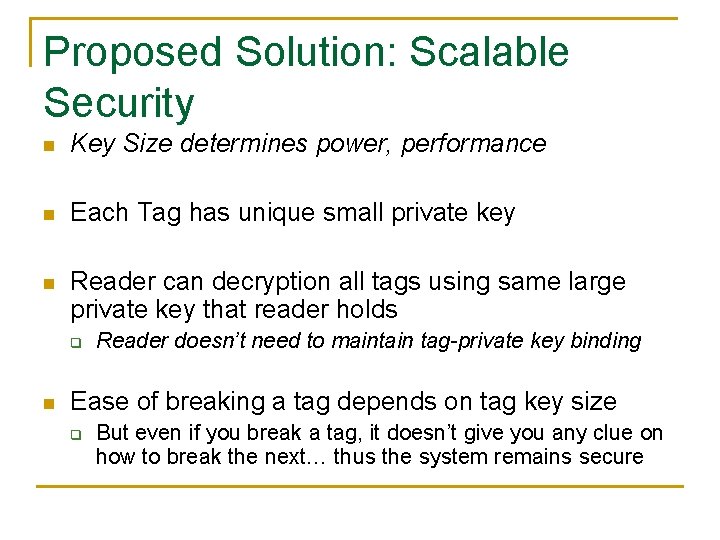
Proposed Solution: Scalable Security n Key Size determines power, performance n Each Tag has unique small private key n Reader can decryption all tags using same large private key that reader holds q n Reader doesn’t need to maintain tag-private key binding Ease of breaking a tag depends on tag key size q But even if you break a tag, it doesn’t give you any clue on how to break the next… thus the system remains secure
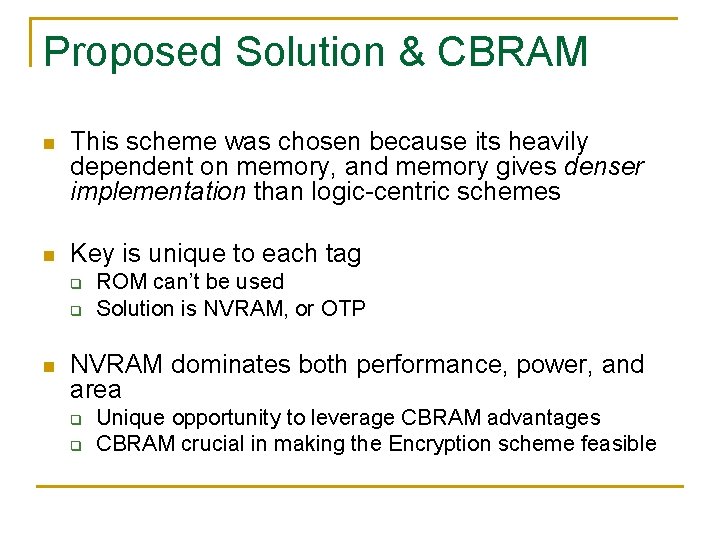
Proposed Solution & CBRAM n This scheme was chosen because its heavily dependent on memory, and memory gives denser implementation than logic-centric schemes n Key is unique to each tag q q n ROM can’t be used Solution is NVRAM, or OTP NVRAM dominates both performance, power, and area q q Unique opportunity to leverage CBRAM advantages CBRAM crucial in making the Encryption scheme feasible
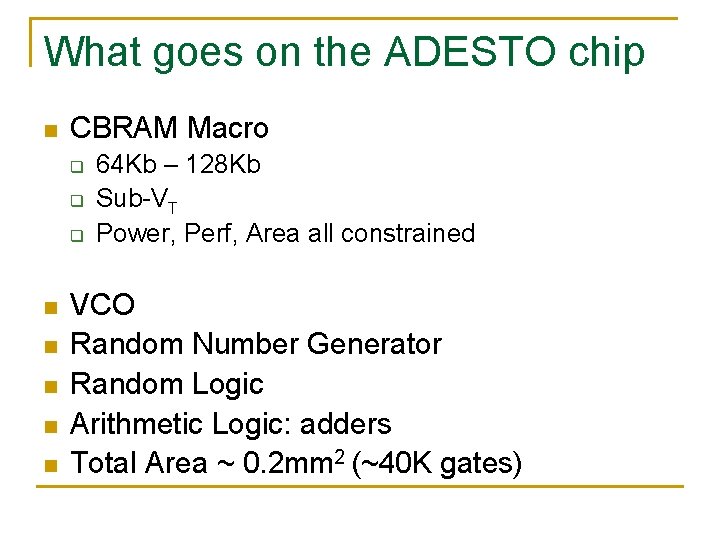
What goes on the ADESTO chip n CBRAM Macro q q q n n n 64 Kb – 128 Kb Sub-VT Power, Perf, Area all constrained VCO Random Number Generator Random Logic Arithmetic Logic: adders Total Area ~ 0. 2 mm 2 (~40 K gates)
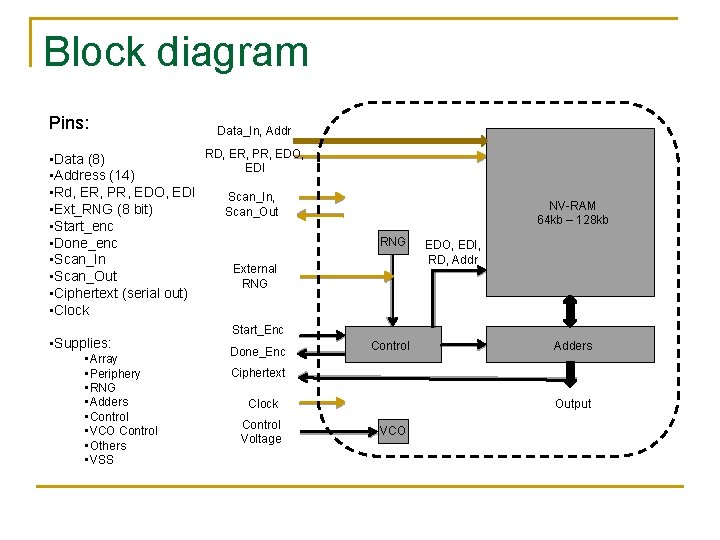
Block diagram Pins: Data_In, Addr RD, ER, PR, EDO, • Data (8) EDI • Address (14) • Rd, ER, PR, EDO, EDI Scan_In, • Ext_RNG (8 bit) Scan_Out • Start_enc • Done_enc • Scan_In External • Scan_Out RNG • Ciphertext (serial out) • Clock • Supplies: • Array • Periphery • RNG • Adders • Control • VCO Control • Others • VSS NV-RAM 64 kb – 128 kb RNG EDO, EDI, RD, Addr Start_Enc Done_Enc Control Adders Ciphertext Clock Control Voltage Output VCO
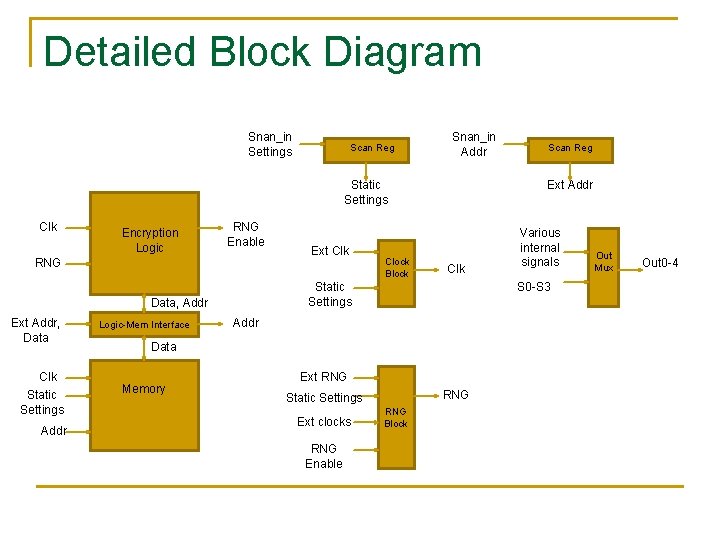
Detailed Block Diagram Snan_in Settings Scan Reg Snan_in Addr Static Settings Clk Encryption Logic RNG Enable RNG Clk Static Settings Addr Logic-Mem Interface Clock Block Ext Addr Clk Static Settings Data, Addr Ext Addr, Data Ext Clk Addr Ext RNG Static Settings Ext clocks RNG Enable Various internal signals S 0 -S 3 Data Memory Scan Reg RNG Block Out Mux Out 0 -4
Goals and Papers n Memory q q q n VCO q n n Energy reduction Performance (SA) Impact of variation ULP, Low phase noise, jitter, drift RNG Logic q Hold time solution
Timeline n May 1 st: Tapeout n April: Layout, P&R n March: Schematic, RTL Design, Ideas n Feb: Generating ideas
Memory Size n Total number of rows not fixed q q q n Number of rows vary from 256 -1024 Data width simultaneously varies from 14 -56 bits Block size simultaneously varies from 12 to 3 Unused blocks may have capability of being switched off
NVRAM Energy-Delay vs. Supply Voltage n What are the most appropriate voltages (VDD, VCC) to read, program, erase? n Setup: q q q All analysis done using 64 kb BLS simulation model No variation in transistor or PMC parameters At all VDD, VCC, the RP and ER pulse widths are set such that PMC RLOW and RHIGH are the same
Read Energy-Delay vs. VDD n VDD is the common periphery supply, going everywhere except the bit-lines during PR, ER n Setup: q q RD (1) – PR – RD (0) sequence is used and read delay and energy are measured. It is ensured that the RD after PR gives ~15% VDD Sweep VDD with WL voltage kept at: n n q VDD for RD Constant 0. 4 V for PR VCC is kept constant at 0. 6 V for PR
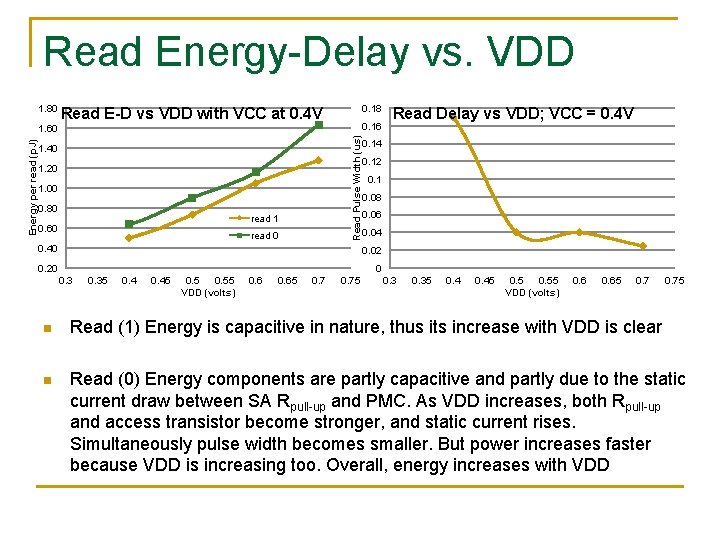
Read Energy-Delay vs. VDD 1. 80 0. 18 Read E-D vs VDD with VCC at 0. 4 V 0. 16 Read Pulse Width (us) Energy per read (p. J) 1. 60 1. 40 1. 20 1. 00 0. 80 read 1 0. 60 read 0 0. 40 Read Delay vs VDD; VCC = 0. 4 V 0. 14 0. 12 0. 1 0. 08 0. 06 0. 04 0. 02 0. 20 0 0. 35 0. 45 0. 55 VDD (volts) 0. 65 0. 75 n Read (1) Energy is capacitive in nature, thus its increase with VDD is clear n Read (0) Energy components are partly capacitive and partly due to the static current draw between SA Rpull-up and PMC. As VDD increases, both Rpull-up and access transistor become stronger, and static current rises. Simultaneously pulse width becomes smaller. But power increases faster because VDD is increasing too. Overall, energy increases with VDD
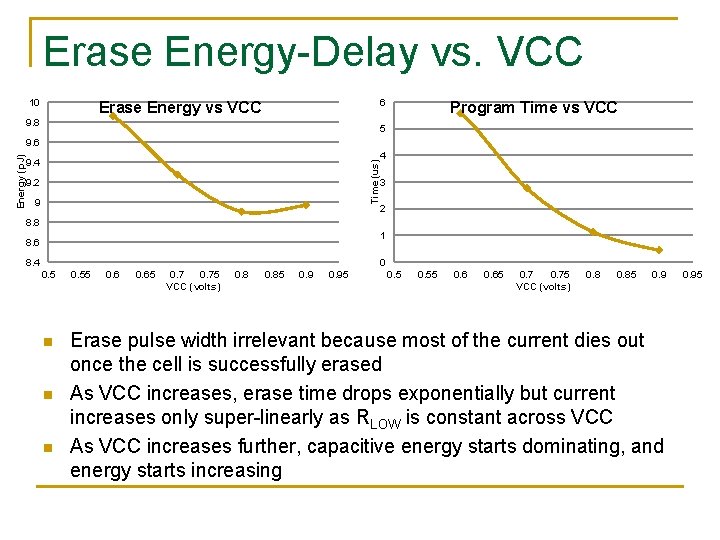
Erase Energy-Delay vs. VCC 10 6 Erase Energy vs VCC 9. 8 Program Time vs VCC 5 9. 4 Time (us) Energy (p. J) 9. 6 9. 2 9 4 3 2 8. 8 1 8. 6 8. 4 0 0. 5 n n n 0. 55 0. 65 0. 75 VCC (volts) 0. 85 0. 95 0. 55 0. 65 0. 75 VCC (volts) 0. 85 0. 9 Erase pulse width irrelevant because most of the current dies out once the cell is successfully erased As VCC increases, erase time drops exponentially but current increases only super-linearly as RLOW is constant across VCC As VCC increases further, capacitive energy starts dominating, and energy starts increasing 0. 95
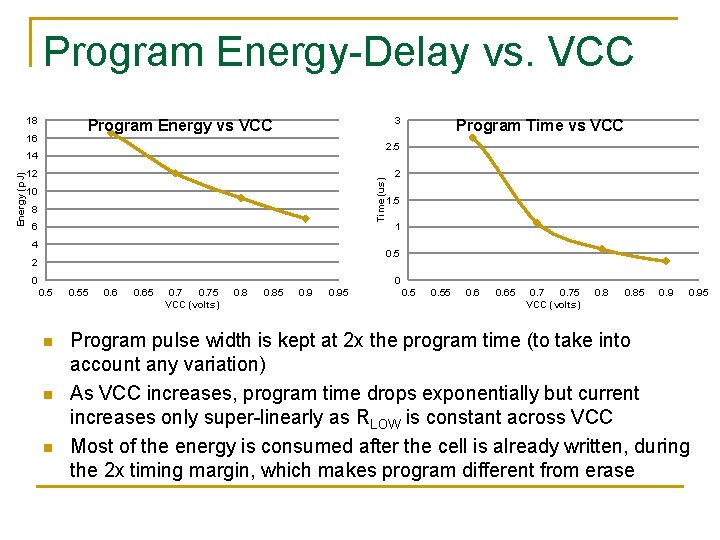
Program Energy-Delay vs. VCC 18 3 Program Energy vs VCC 16 2. 5 14 12 Time (us) Energy (p. J) Program Time vs VCC 10 8 6 4 2 1. 5 1 0. 5 2 0 0 0. 5 n n n 0. 55 0. 65 0. 75 VCC (volts) 0. 85 0. 95 Program pulse width is kept at 2 x the program time (to take into account any variation) As VCC increases, program time drops exponentially but current increases only super-linearly as RLOW is constant across VCC Most of the energy is consumed after the cell is already written, during the 2 x timing margin, which makes program different from erase
Summary
Questions n n Theoretically explain the components of rd pr er energies Specifically: q q Where is the read 1 energy going? ? Why is program delay decreasing sl slowly with VDD? ?
Thanks
- Slides: 27