Cryptography Block Ciphers Edward J Schwartz Carnegie Mellon
Cryptography: Block Ciphers Edward J. Schwartz Carnegie Mellon University Credits: Slides originally designed by David Brumley. Many other slides are from Dan Boneh’s June 2012 Coursera crypto class.
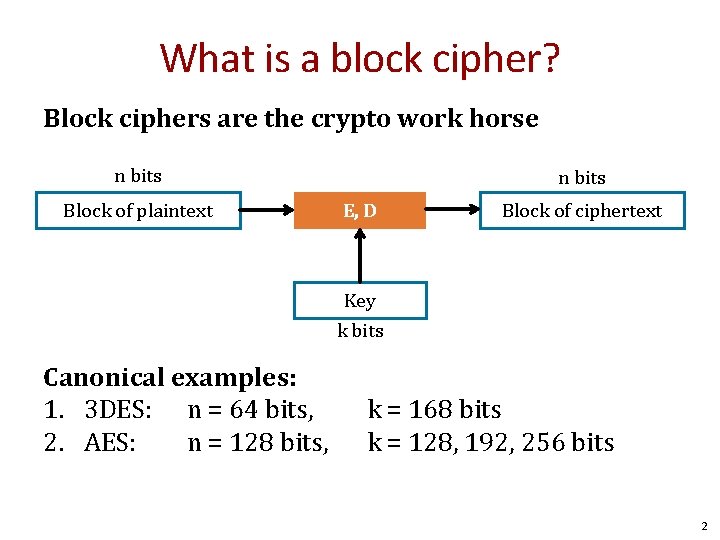
What is a block cipher? Block ciphers are the crypto work horse n bits Block of plaintext n bits E, D Block of ciphertext Key k bits Canonical examples: 1. 3 DES: n = 64 bits, 2. AES: n = 128 bits, k = 168 bits k = 128, 192, 256 bits 2
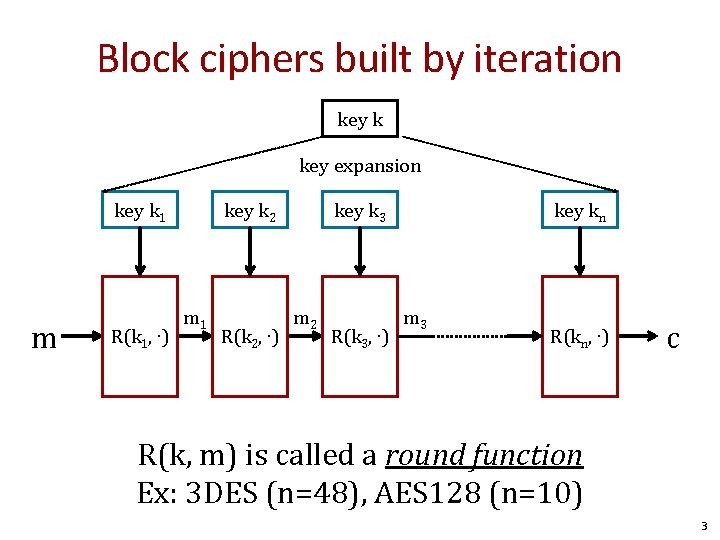
Block ciphers built by iteration key k key expansion key k 1 m m R(k 1, ∙) key k 2 m 1 R(k 2, ∙) key k 3 m 2 R(k 3, ∙) key kn m 3 R(kn, ∙) c R(k, m) is called a round function Ex: 3 DES (n=48), AES 128 (n=10) 3
![Performance: Stream vs. block ciphers Crypto++ 5. 6. 0 [Wei Dai] AMD Opteron, 2. Performance: Stream vs. block ciphers Crypto++ 5. 6. 0 [Wei Dai] AMD Opteron, 2.](http://slidetodoc.com/presentation_image_h/02533d06e9e23388dbc0b0bb87ae38b5/image-4.jpg)
Performance: Stream vs. block ciphers Crypto++ 5. 6. 0 [Wei Dai] AMD Opteron, 2. 2 GHz (Linux) Stream Cipher Block/key size Throughput [MB/s] RC 4 126 Salsa 20/12 643 Sosemanuk 727 Block 3 DES AES 128 64/168 128/128 13 109 4
Block ciphers The Data Encryption Standard (DES) 5
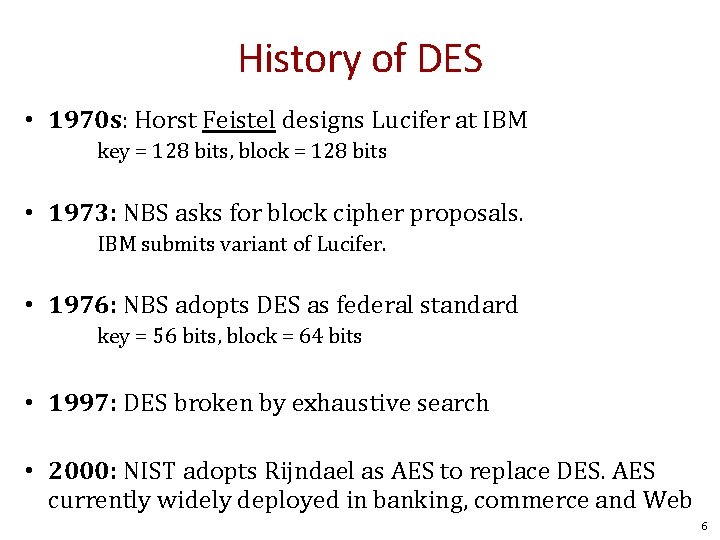
History of DES • 1970 s: Horst Feistel designs Lucifer at IBM key = 128 bits, block = 128 bits • 1973: NBS asks for block cipher proposals. IBM submits variant of Lucifer. • 1976: NBS adopts DES as federal standard key = 56 bits, block = 64 bits • 1997: DES broken by exhaustive search • 2000: NIST adopts Rijndael as AES to replace DES. AES currently widely deployed in banking, commerce and Web 6
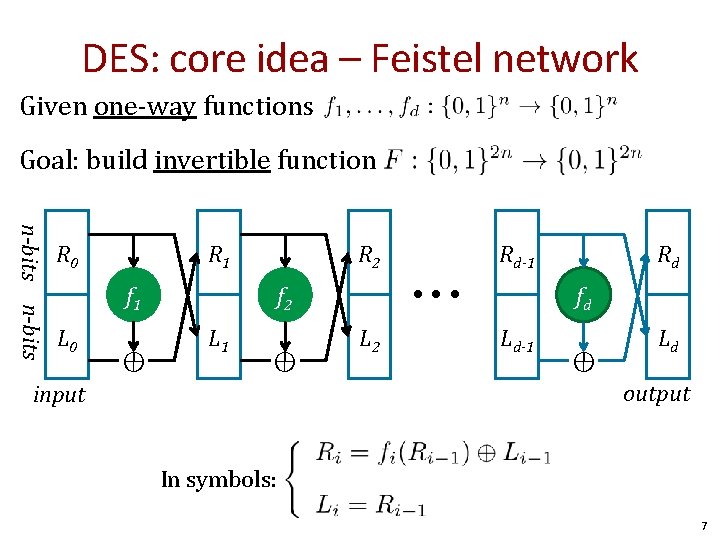
DES: core idea – Feistel network Given one-way functions Goal: build invertible function n-bits R 0 R 1 R 2 f 1 L 0 ⊕ • • • f 2 L 1 ⊕ Rd-1 L 2 Rd fd Ld-1 ⊕ Ld output input In symbols: 7
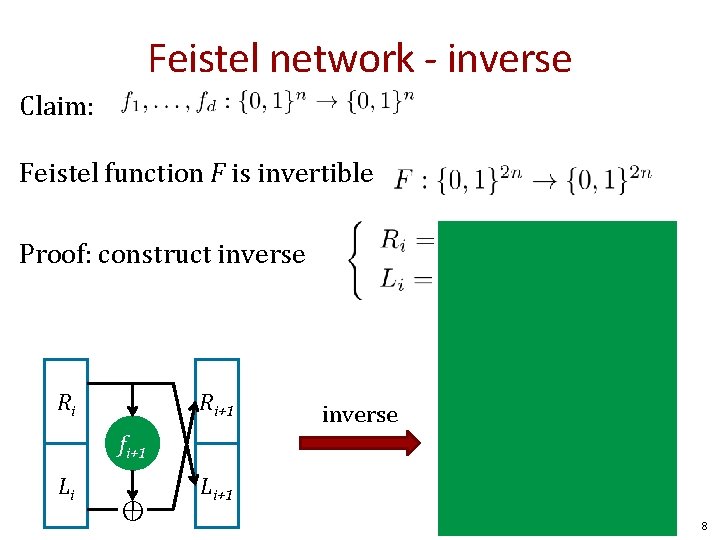
Feistel network - inverse Claim: Feistel function F is invertible Proof: construct inverse Ri+1 fi+1 Li ⊕ ⊕ Ri Ri fi+1 Li+1 Li 8
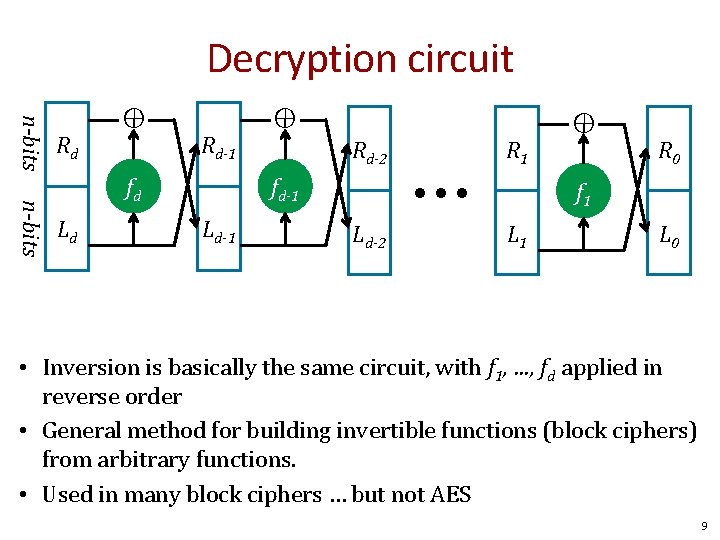
Decryption circuit ⊕ n-bits fd Ld ⊕ Rd-1 Rd-2 • • • fd-1 Ld-1 R 1 Ld-2 ⊕ n-bits Rd R 0 f 1 L 0 • Inversion is basically the same circuit, with f 1, …, fd applied in reverse order • General method for building invertible functions (block ciphers) from arbitrary functions. • Used in many block ciphers … but not AES 9
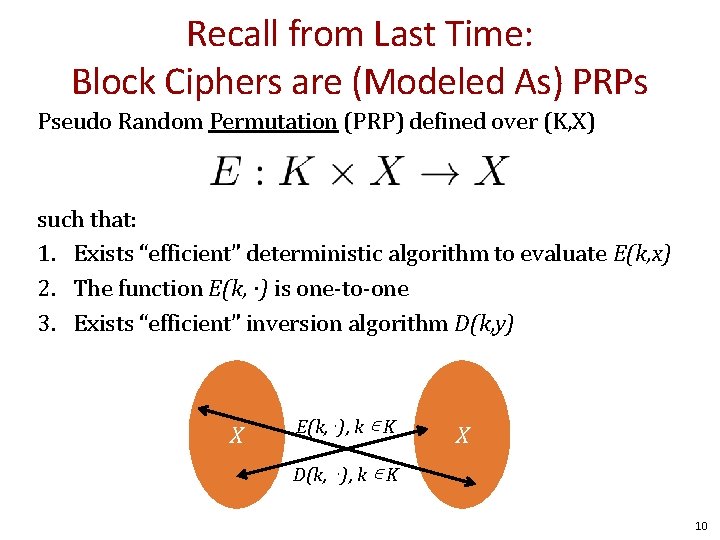
Recall from Last Time: Block Ciphers are (Modeled As) PRPs Pseudo Random Permutation (PRP) defined over (K, X) such that: 1. Exists “efficient” deterministic algorithm to evaluate E(k, x) 2. The function E(k, ∙) is one-to-one 3. Exists “efficient” inversion algorithm D(k, y) X E(k, ⋅), k ∊ K X D(k, ⋅), k ∊ K 10
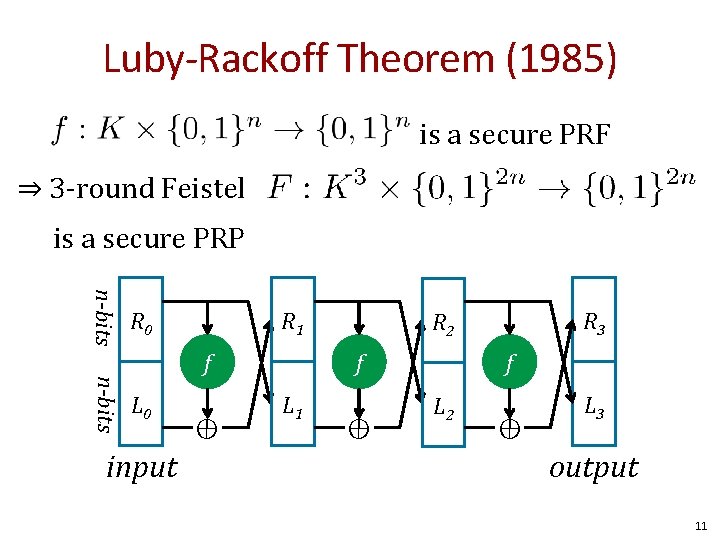
Luby-Rackoff Theorem (1985) is a secure PRF ⇒ 3 -round Feistel is a secure PRP n-bits R 0 R 1 f n-bits L 0 input ⊕ f L 1 R 3 R 2 ⊕ f L 2 ⊕ L 3 output 11
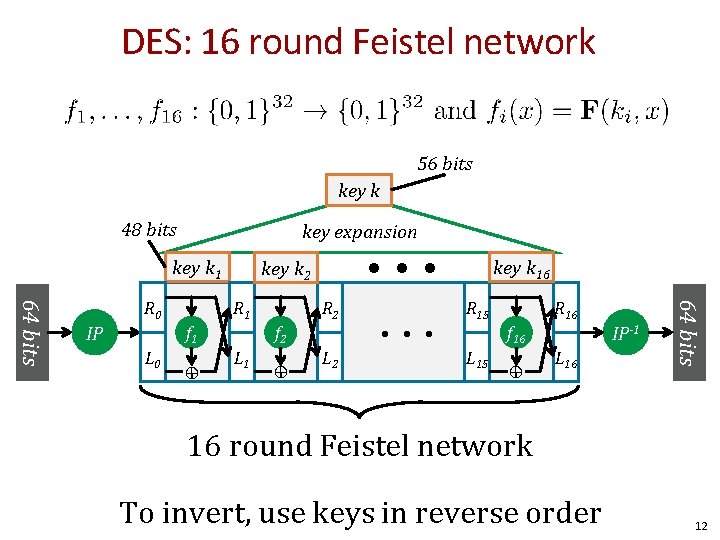
DES: 16 round Feistel network 56 bits key k 48 bits key expansion key k 1 f 2 f 1 L 0 ⊕ R 2 L 1 ⊕ L 2 • • • key k 16 R 15 f 16 L 15 ⊕ L 16 IP-1 64 bits IP R 1 R 0 • • • key k 2 16 round Feistel network To invert, use keys in reverse order 12
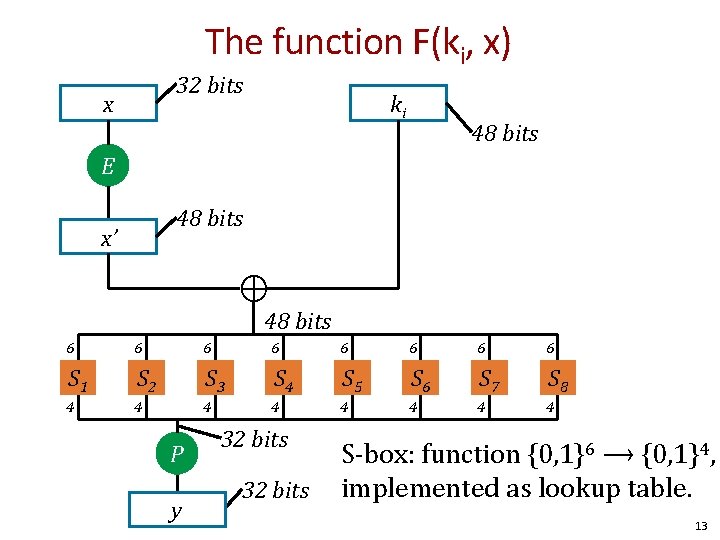
The function F(ki, x) 32 bits x ki 48 bits E 48 bits x’ ⊕ 48 bits 6 6 6 6 S 1 S 2 S 3 S 4 S 5 S 6 S 7 S 8 4 4 4 4 P y 32 bits S-box: function {0, 1}6 ⟶ {0, 1}4, implemented as lookup table. 13
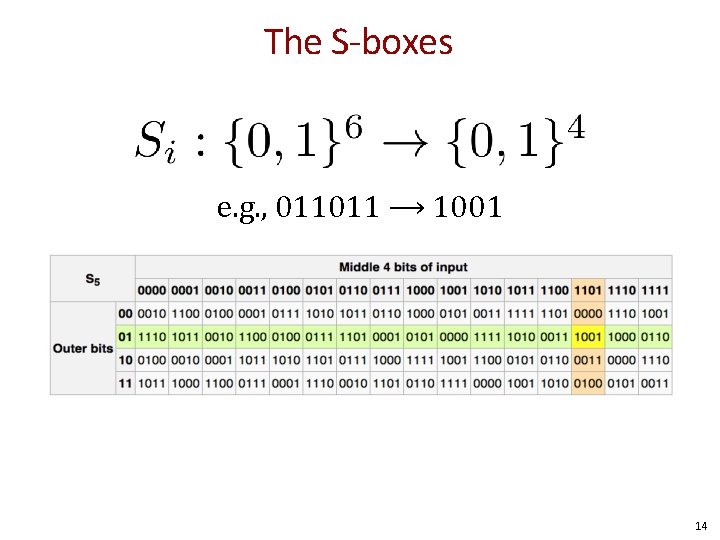
The S-boxes e. g. , 011011 ⟶ 1001 14
The S-boxes • Alan Konheim (one of the designers of DES) commented, "We sent the S-boxes off to Washington. They came back and were all different. “ • 1990: (Re-)Discovery of differential cryptanalysis – DES S-boxes resistant to differential cryptanalysis! – Both IBM and NSA knew of attacks, but they were classified 15
Block cipher attacks 16
Exhaustive Search for block cipher key Goal: given a few input output pairs (mi, ci = E(k, mi)) i=1, . . , n find key k. Attack: Brute force to find the key k. Homework: What is the probability that the key k found with one <m, c> pair is correct? For two pairs? 17
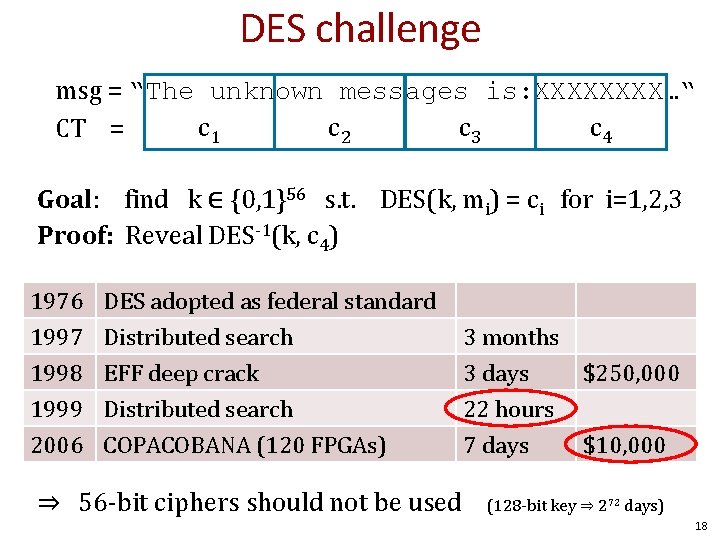
DES challenge msg = “The unknown messages is: XXXX…“ c 1 c 2 c 3 c 4 CT = Goal: find k ∈ {0, 1}56 s. t. DES(k, mi) = ci for i=1, 2, 3 Proof: Reveal DES-1(k, c 4) 1976 1997 1998 1999 DES adopted as federal standard Distributed search EFF deep crack Distributed search 2006 COPACOBANA (120 FPGAs) ⇒ 56 -bit ciphers should not be used 3 months 3 days $250, 000 22 hours 7 days $10, 000 (128 -bit key ⇒ 272 days) 18
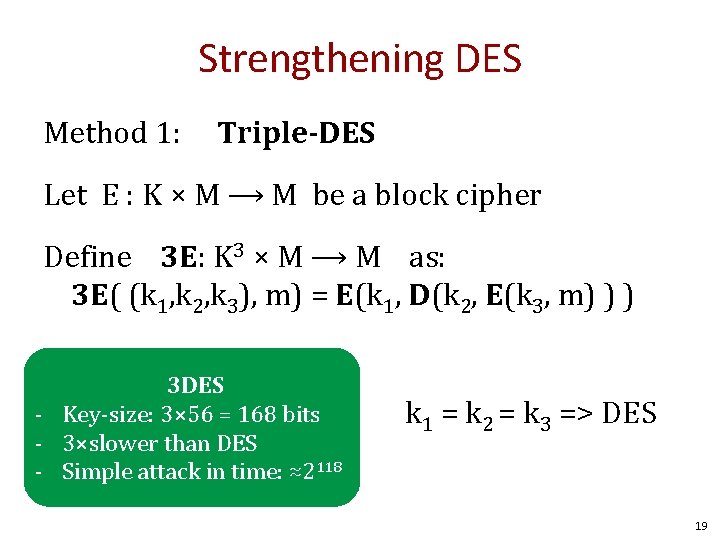
Strengthening DES Method 1: Triple-DES Let E : K × M ⟶ M be a block cipher Define 3 E: K 3 × M ⟶ M as: 3 E( (k 1, k 2, k 3), m) = E(k 1, D(k 2, E(k 3, m) ) ) 3 DES - Key-size: 3× 56 = 168 bits - 3×slower than DES - Simple attack in time: ≈2118 k 1 = k 2 = k 3 => DES 19
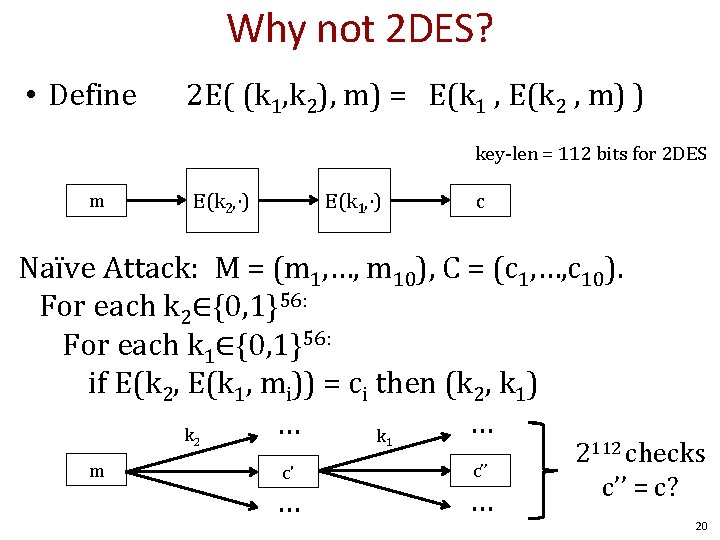
Why not 2 DES? • Define 2 E( (k 1, k 2), m) = E(k 1 , E(k 2 , m) ) key-len = 112 bits for 2 DES m E(k 2, ⋅) E(k 1, ⋅) c Naïve Attack: M = (m 1, …, m 10), C = (c 1, …, c 10). For each k 2∈{0, 1}56: For each k 1∈{0, 1}56: if E(k 2, E(k 1, mi)) = ci then (k 2, k 1) … … k k 2 m 1 c' … c’’ … 2112 checks c’’ = c? 20
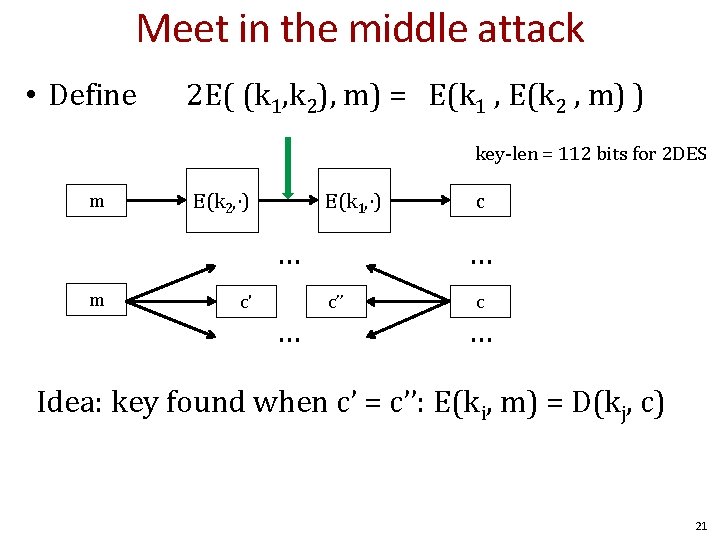
Meet in the middle attack • Define 2 E( (k 1, k 2), m) = E(k 1 , E(k 2 , m) ) key-len = 112 bits for 2 DES m E(k 2, ⋅) E(k 1, ⋅) … m c' … c’’ c … Idea: key found when c’ = c’’: E(ki, m) = D(kj, c) 21
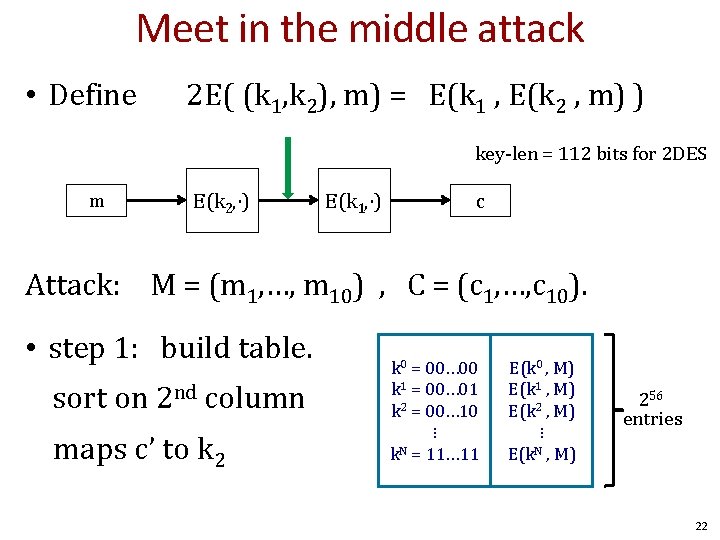
Meet in the middle attack • Define 2 E( (k 1, k 2), m) = E(k 1 , E(k 2 , m) ) key-len = 112 bits for 2 DES m E(k 2, ⋅) E(k 1, ⋅) c Attack: M = (m 1, …, m 10) , C = (c 1, …, c 10). • step 1: build table. sort on 2 nd column maps c’ to k 2 k 0 = 00… 00 k 1 = 00… 01 k 2 = 00… 10 ⋮ k. N = 11… 11 E(k 0 , M) E(k 1 , M) E(k 2 , M) ⋮ E(k. N , M) 256 entries 22
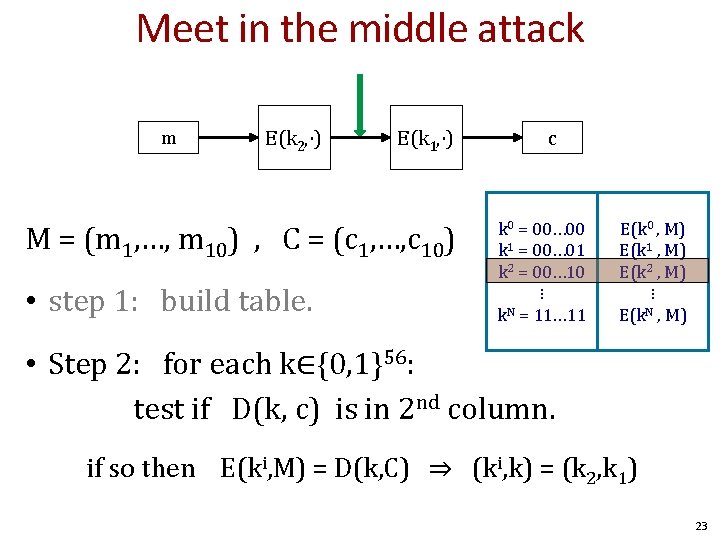
Meet in the middle attack m E(k 2, ⋅) E(k 1, ⋅) M = (m 1, …, m 10) , C = (c 1, …, c 10) • step 1: build table. c k 0 = 00… 00 k 1 = 00… 01 k 2 = 00… 10 ⋮ k. N = 11… 11 E(k 0 , M) E(k 1 , M) E(k 2 , M) ⋮ E(k. N , M) • Step 2: for each k∈{0, 1}56: test if D(k, c) is in 2 nd column. if so then E(ki, M) = D(k, C) ⇒ (ki, k) = (k 2, k 1) 23
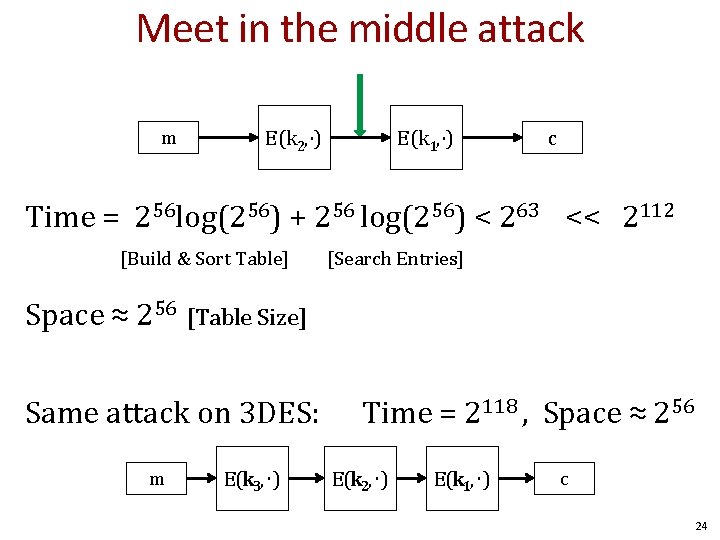
Meet in the middle attack m E(k 2, ⋅) E(k 1, ⋅) c Time = 256 log(256) + 256 log(256) < 263 << 2112 [Build & Sort Table] [Search Entries] Space ≈ 256 [Table Size] Same attack on 3 DES: m E(k 3, ⋅) Time = 2118 , Space ≈ 256 E(k 2, ⋅) E(k 1, ⋅) c 24
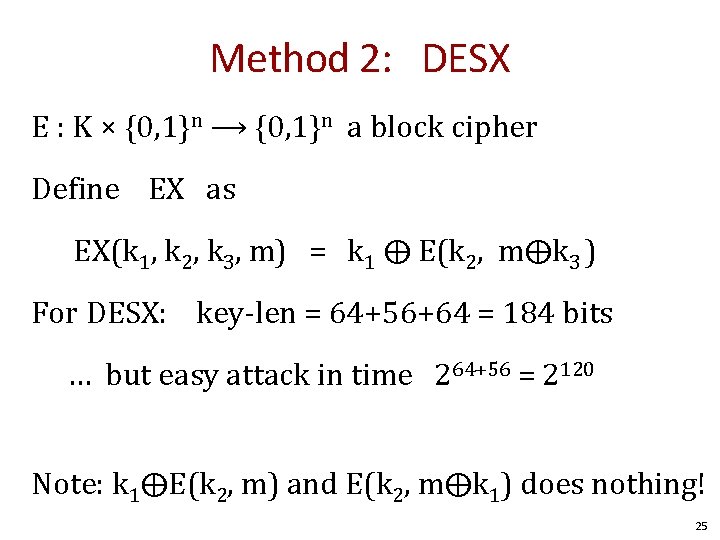
Method 2: DESX E : K × {0, 1}n ⟶ {0, 1}n a block cipher Define EX as EX(k 1, k 2, k 3, m) = k 1 ⨁ E(k 2, m⨁k 3 ) For DESX: key-len = 64+56+64 = 184 bits … but easy attack in time 264+56 = 2120 Note: k 1⨁E(k 2, m) and E(k 2, m⨁k 1) does nothing! 25
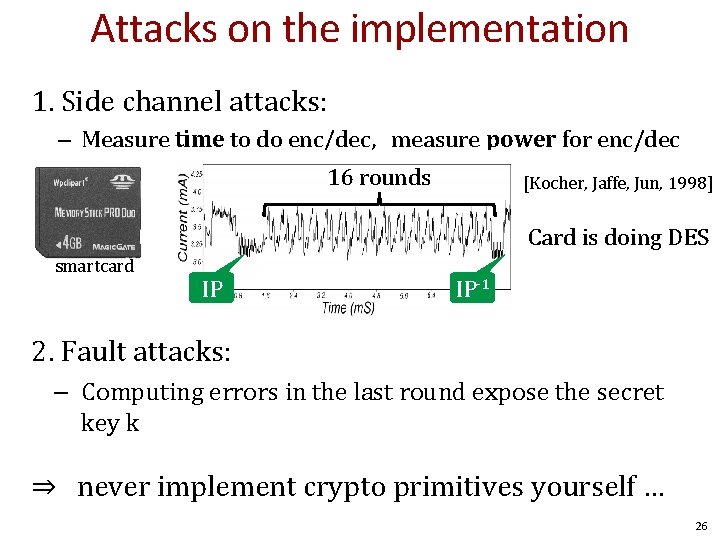
Attacks on the implementation 1. Side channel attacks: – Measure time to do enc/dec, measure power for enc/dec 16 rounds [Kocher, Jaffe, Jun, 1998] Card is doing DES smartcard IP IP-1 2. Fault attacks: – Computing errors in the last round expose the secret key k ⇒ never implement crypto primitives yourself … 26
Block ciphers AES – Advanced encryption standard 27
The AES process • • • 1997: DES broken by exhaustive search 1997: NIST publishes request for proposal 1998: 15 submissions 1999: NIST chooses 5 finalists 2000: NIST chooses Rijndael as AES (developed by Daemen and Rijmen at K. U. Leuven, Belgium) Key sizes: 128, 192, 256 bits Block size: 128 bits 28
AES core idea: Subs-Perm network DES is based on Feistel networks AES is based on the idea of substitution-permutation networks That is, alternating steps of substitution and permutation operations 29
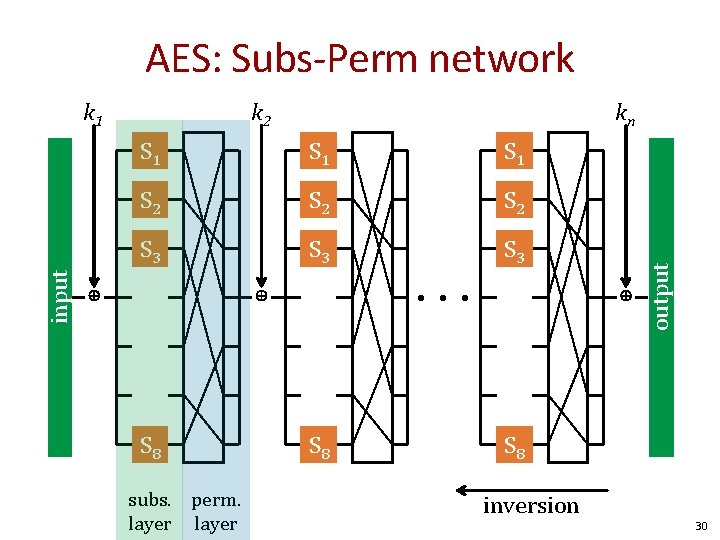
AES: Subs-Perm network k 2 kn S 1 S 1 S 2 S 2 S 3 S 3 ⊕ ⊕ S 8 subs. perm. layer ⊕ • • • S 8 output input k 1 S 8 inversion 30
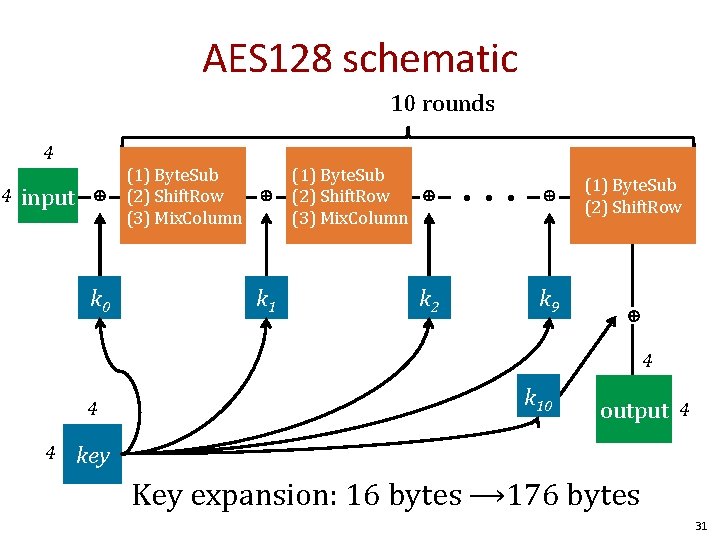
AES 128 schematic 10 rounds 4 4 input ⊕ ⊕ k 1 (1) Byte. Sub (2) Shift. Row (3) Mix. Column ⊕ k 2 • • • ⊕ k 9 (1) Byte. Sub (2) Shift. Row ⊕ k 0 (1) Byte. Sub (2) Shift. Row (3) Mix. Column 4 4 4 k 10 output 4 key Key expansion: 16 bytes ⟶ 176 bytes 31
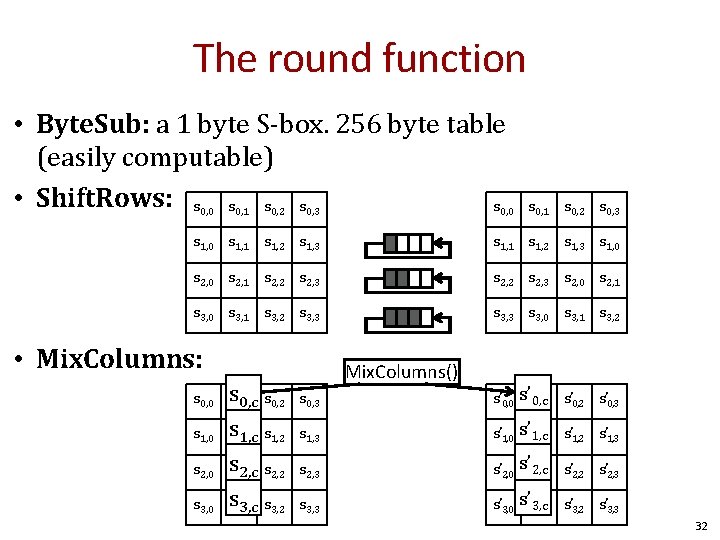
The round function • Byte. Sub: a 1 byte S-box. 256 byte table (easily computable) • Shift. Rows: s s s 0, 0 0, 1 0, 2 0, 3 0, 0 s 0, 1 s 0, 2 s 0, 3 s 1, 0 s 1, 1 s 1, 2 s 1, 3 s 1, 0 s 2, 1 s 2, 2 s 2, 3 s 2, 0 s 2, 1 s 3, 0 s 3, 1 s 3, 2 s 3, 3 s 3, 0 s 3, 1 s 3, 2 • Mix. Columns: s 0, 0 ss 0, 1 0, c s 0, 2 s 0, 3 Mix. Columns() s’ 0, 0 s’s’ 0, c 0, 1 s’ 0, 2 s’ 0, 3 s 1, 0 ss 1, 1 1, c s 1, 2 s 1, 3 s’ 1, 0 s’s’ 1, c 1, 1 s’ 1, 2 s’ 1, 3 s 2, 0 ss 2, 1 2, c s 2, 2 s 2, 3 s’ 2, 0 s’s’ 2, c 2, 1 s’ 2, 2 s’ 2, 3 s 3, 0 ss 3, 1 3, c s 3, 2 s 3, 3 s’ 3, 0 s’s’ 3, c 3, 1 s’ 3, 2 s’ 3, 3 32
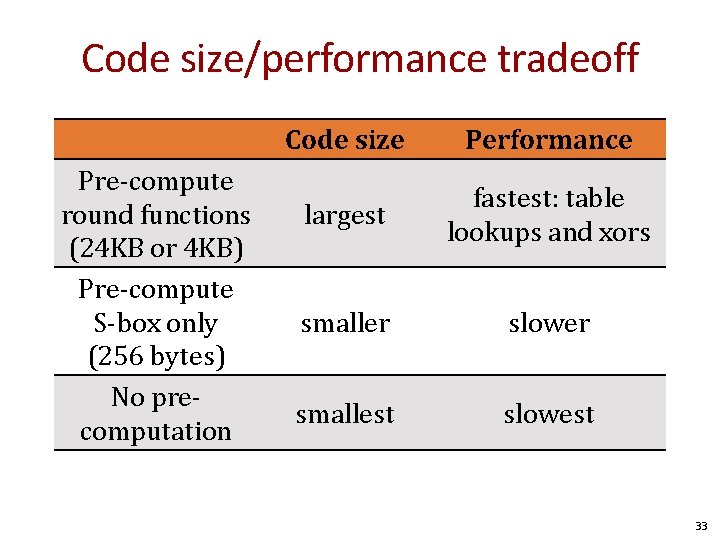
Code size/performance tradeoff Pre-compute round functions (24 KB or 4 KB) Pre-compute S-box only (256 bytes) No precomputation Code size Performance largest fastest: table lookups and xors smaller slower smallest slowest 33
Size + performance (Javascript AES) AES in the browser AES library (6. 4 KB) No pre-computed tables (1) Uncompress code (one time effort) (2) Pre-compute tables (one time effort) (3) Perform encryption using tables Implementation: Stanford Javascript Crypto Library https: //crypto. stanford. edu/sjcl/ 34
Modes of operation 36
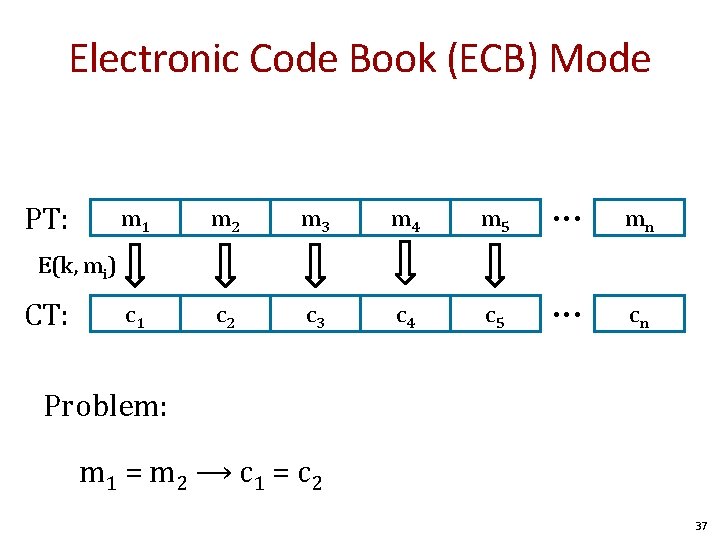
Electronic Code Book (ECB) Mode PT: m 1 m 2 m 3 m 4 m 5 • • • mn c 1 c 2 c 3 c 4 c 5 • • • cn E(k, mi) CT: Problem: m 1 = m 2 ⟶ c 1 = c 2 37
What can possibly go wrong? Plaintext Ciphertext Images from Wikipedia 38
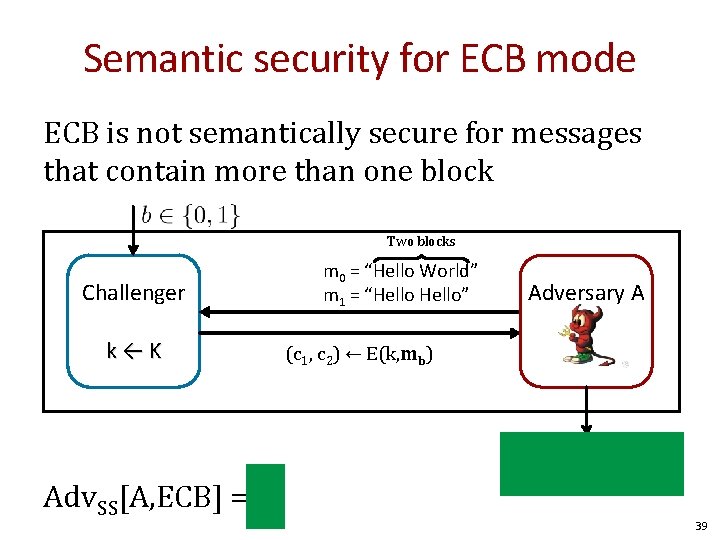
Semantic security for ECB mode ECB is not semantically secure for messages that contain more than one block Two blocks Challenger k←K Adv. SS[A, ECB] = 1 m 0 = “Hello World” m 1 = “Hello” Adversary A (c 1, c 2) ← E(k, mb) if c 1 = c 2 output 1 else output 0 39
![Deterministic counter mode from a PRF F: EDETCTR(k, m) = m[0] m[1] m[2] • Deterministic counter mode from a PRF F: EDETCTR(k, m) = m[0] m[1] m[2] •](http://slidetodoc.com/presentation_image_h/02533d06e9e23388dbc0b0bb87ae38b5/image-39.jpg)
Deterministic counter mode from a PRF F: EDETCTR(k, m) = m[0] m[1] m[2] • • • m[L] F(k, 0) F(k, 1) F(k, 2) • • • F(k, L) c[0] c[1] c[2] • • • c[L] ⊕ Stream cipher built from a PRF (e. g. AES, 3 DES) Better than ECB but only works as long as the key is only used once (one-time-key) 40
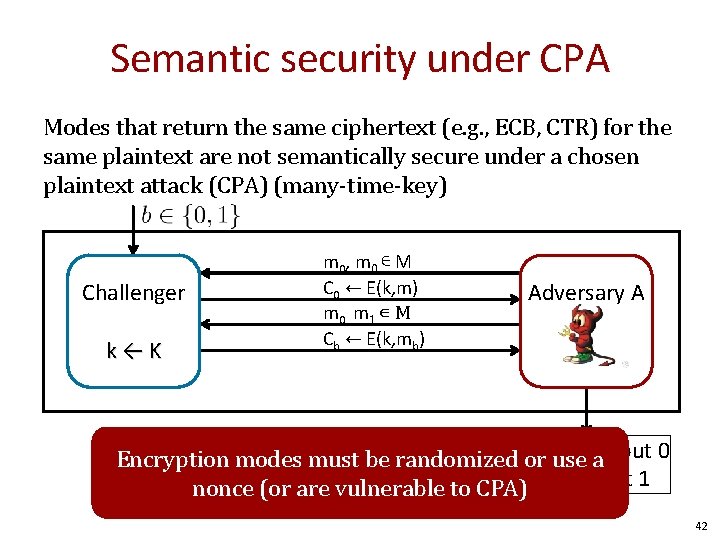
Semantic security under CPA Modes that return the same ciphertext (e. g. , ECB, CTR) for the same plaintext are not semantically secure under a chosen plaintext attack (CPA) (many-time-key) Challenger k←K m 0 , m 0 ∊ M C 0 ← E(k, m) m 0, m 1 ∊ M Cb ← E(k, mb) Adversary A if cor c 0 output 0 b =use Encryption modes must be randomized a nonce (or are vulnerable to CPA)else output 1 42
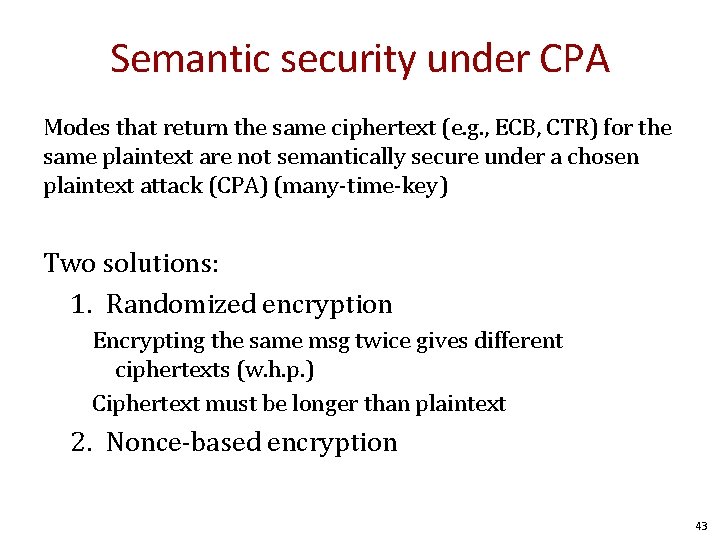
Semantic security under CPA Modes that return the same ciphertext (e. g. , ECB, CTR) for the same plaintext are not semantically secure under a chosen plaintext attack (CPA) (many-time-key) Two solutions: 1. Randomized encryption Encrypting the same msg twice gives different ciphertexts (w. h. p. ) Ciphertext must be longer than plaintext 2. Nonce-based encryption 43
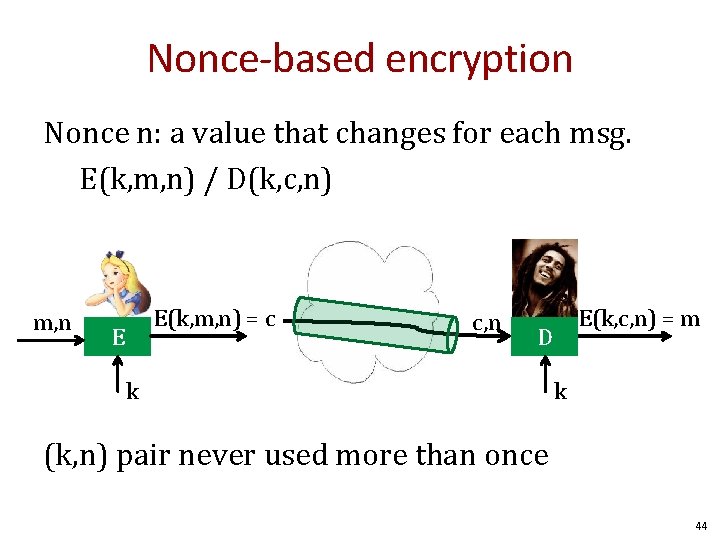
Nonce-based encryption Nonce n: a value that changes for each msg. E(k, m, n) / D(k, c, n) m, n E(k, m, n) = c E c, n E(k, c, n) = m D k k (k, n) pair never used more than once 44
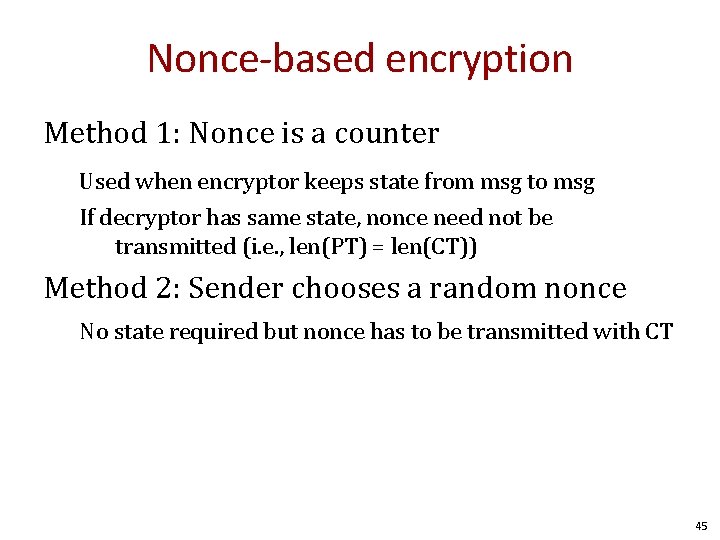
Nonce-based encryption Method 1: Nonce is a counter Used when encryptor keeps state from msg to msg If decryptor has same state, nonce need not be transmitted (i. e. , len(PT) = len(CT)) Method 2: Sender chooses a random nonce No state required but nonce has to be transmitted with CT 45
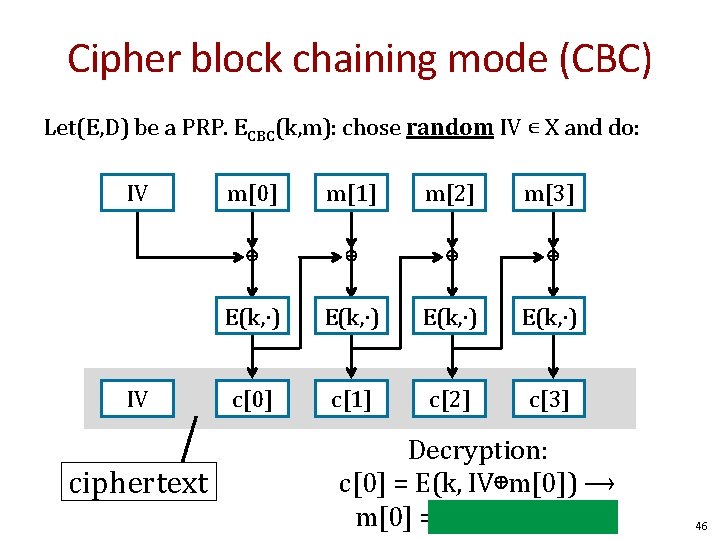
Cipher block chaining mode (CBC) Let(E, D) be a PRP. ECBC(k, m): chose random IV ∊ X and do: IV IV ciphertext m[0] m[1] m[2] m[3] ⊕ ⊕ E(k, ∙) c[0] c[1] c[2] c[3] Decryption: c[0] = E(k, IV⊕m[0]) ⟶ m[0] = D(k, c[0]) ⊕ IV 46
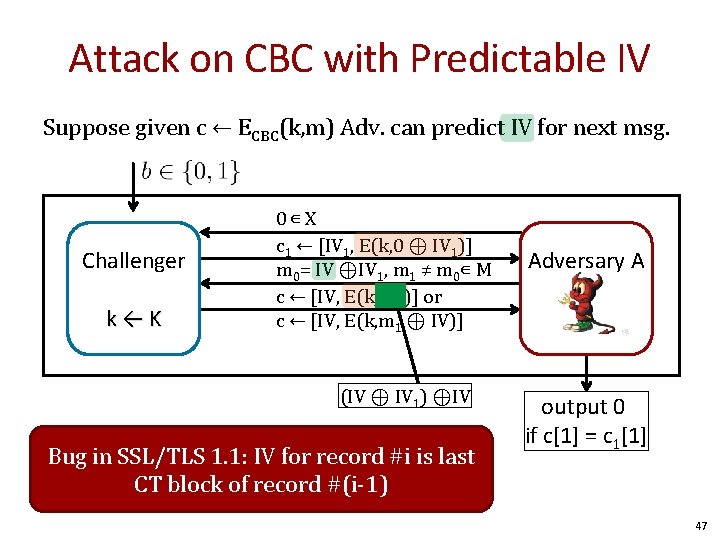
Attack on CBC with Predictable IV Suppose given c ← ECBC(k, m) Adv. can predict IV for next msg. Challenger k←K 0∊ X c 1 ← [IV 1, E(k, 0 ⊕ IV 1)] m 0= IV ⊕IV 1, m 1 ≠ m 0∊ M c ← [IV, E(k, IV 1)] or c ← [IV, E(k, m 1 ⊕ IV)] (IV ⊕ IV 1) ⊕IV Bug in SSL/TLS 1. 1: IV for record #i is last CT block of record #(i-1) Adversary A output 0 if c[1] = c 1[1] 47
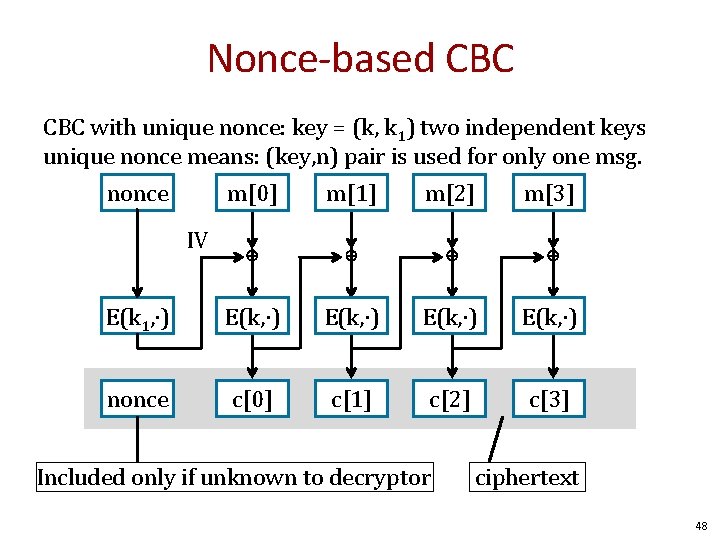
Nonce-based CBC with unique nonce: key = (k, k 1) two independent keys unique nonce means: (key, n) pair is used for only one msg. nonce m[0] m[1] m[2] m[3] ⊕ ⊕ E(k 1, ∙) E(k, ∙) nonce c[0] c[1] c[2] c[3] IV Included only if unknown to decryptor ciphertext 48
![CBC: padding nonce m[0] m[1] m[2] ⊕ ⊕ E(k 1, ∙) E(k, ∙) nonce CBC: padding nonce m[0] m[1] m[2] ⊕ ⊕ E(k 1, ∙) E(k, ∙) nonce](http://slidetodoc.com/presentation_image_h/02533d06e9e23388dbc0b0bb87ae38b5/image-47.jpg)
CBC: padding nonce m[0] m[1] m[2] ⊕ ⊕ E(k 1, ∙) E(k, ∙) nonce c[0] c[1] c[2] c[3] IV TLS: for n > 0 n byte pad is: n n … n If no pad needed, add a dummy block: 16 16 m[3] || pad removed during decryption … 16 Padding oracle side channel attacks 49
Cipher block chaining mode (CBC) Example applications: 1. File system encryption: use the same AES key to encrypt all files (e. g. , loopaes) 2. IPsec: use the same AES key to encrypt multiple packets Problem: If attacker can predict IV, CBC is not CPA-secure 50
Summary Block ciphers – Map fixed length input blocks to same length output blocks – Canonical block ciphers: 3 DES, AES – PRPs are effectively block ciphers – PRPs can be created from arbitrary functions through Feistel networks • 3 DES based on Feistel networks • AES based on substitution-permutation networks 51

Questions? 52
END
![Linear and differential attacks [BS’ 89, M’ 93] Given many inp/out pairs, can recover Linear and differential attacks [BS’ 89, M’ 93] Given many inp/out pairs, can recover](http://slidetodoc.com/presentation_image_h/02533d06e9e23388dbc0b0bb87ae38b5/image-52.jpg)
Linear and differential attacks [BS’ 89, M’ 93] Given many inp/out pairs, can recover key in time less than 256. Linear cryptanalysis (overview) : let c = DES(k, m) Suppose for random k, m : Pr[ m[i 1]⨁⋯⨁m[ir] ⨁ c[jj]⨁⋯⨁c[jv] = k[l 1]⨁⋯⨁k[lu] ] = ½ + ε For some ε. For DES, this exists with ε = 1/221 ≈ 0. 0000000477 54
![Linear attacks Pr[ m[i 1]⨁⋯⨁m[ir] ⨁ c[jj]⨁⋯⨁c[jv] = k[l 1]⨁⋯⨁k[lu] ] = ½ + Linear attacks Pr[ m[i 1]⨁⋯⨁m[ir] ⨁ c[jj]⨁⋯⨁c[jv] = k[l 1]⨁⋯⨁k[lu] ] = ½ +](http://slidetodoc.com/presentation_image_h/02533d06e9e23388dbc0b0bb87ae38b5/image-53.jpg)
Linear attacks Pr[ m[i 1]⨁⋯⨁m[ir] ⨁ c[jj]⨁⋯⨁c[jv] = k[l 1]⨁⋯⨁k[lu] ] = ½ + ε Thm: given 1/ε 2 random (m, c=DES(k, m)) pairs then k[l 1, …, lu] = MAJ [ m[i 1, …, ir] ⨁ c[jj, …, jv] ] with prob. ≥ 97. 7% ⇒ with 1/ε 2 inp/out pairs can find k[l 1, …, lu] in time ≈1/ε 2. 55
Linear attacks For DES, ε = 1/221 ⇒ with 242 inp/out pairs can find k[l 1, …, lu] in time 242 Roughly speaking: can find 14 key “bits” this way in time 242 Brute force remaining 56− 14=42 bits in time 242 Total attack time ≈243 ( << 256 ) with 242 random inp/out pairs 56
Lesson A tiny bit of linearity in S 5 lead to a 242 time attack. ⇒ don’t design ciphers yourself !! 57
Quantum attacks Generic search problem: Let f: X ⟶ {0, 1} be a function. Goal: find x∈X s. t. f(x)=1. Classical computer: best generic algorithm time = O( |X| ) Quantum computer [Grover ’ 96] : time = O( |X|1/2 ) Can quantum computers be built: unknown 58
Quantum exhaustive search Given m, c=E(k, m) define 1 if E(k, m) = c f(k) = 0 otherwise Grover ⇒ quantum computer can find k in time O( |K|1/2 ) DES: time ≈228 , AES-128: time ≈264 quantum computer ⇒ 256 -bits key ciphers (e. g. AES-256) 59
- Slides: 57