Cryptanalysis of a MultiServer Password Authenticated Key Agreement
- Slides: 13
Cryptanalysis of a Multi-Server Password Authenticated Key Agreement Scheme Using Smart Cards W. C. Ku, H. M. Chuang, and M. H. Chiang IEICE TRANS. FUNDAMENTALS, VOL. E 88–A, NO. 11, NOV. 2005
Outline n n Introduction Juang’s scheme ¨ W. S. Juang, “Efficient multi-server password authenticated key agreement using smart cards, ” IEEE Trans. Consum. Electron. , vol. 50, no. 1, pp. 251– 255, Feb. 2004 n n n Weaknesses of Juang’s Scheme Conclusions Comments 2
Introduction(1/2) n Authenticated Key Agreement ¨ User authentication and key agreement scheme n Authentication scheme ¨ Single server Multi-server 3
Introduction(2/2) n Criteria for remote authentication and session key agreement schemes using smart cards ¨ C 1: ¨ C 2: ¨ C 3: ¨ C 4: ¨ C 5: ¨ C 6: n No verification table Freely chosen password Low computation and communication cost Mutual authentication Session key agreement Single registration Security criteria for session key agreement ¨ S 1: ¨ S 2: ¨ S 3: Session key security Forward secrecy Known-key security 4
Juang’s scheme n 3 roles: ¨ Users ¨ Servers ¨ Registration n center 3 phases: ¨ The registration phase ¨ The login and session key agreement phase ¨ The shared key inquiry phase 5
Notations 6
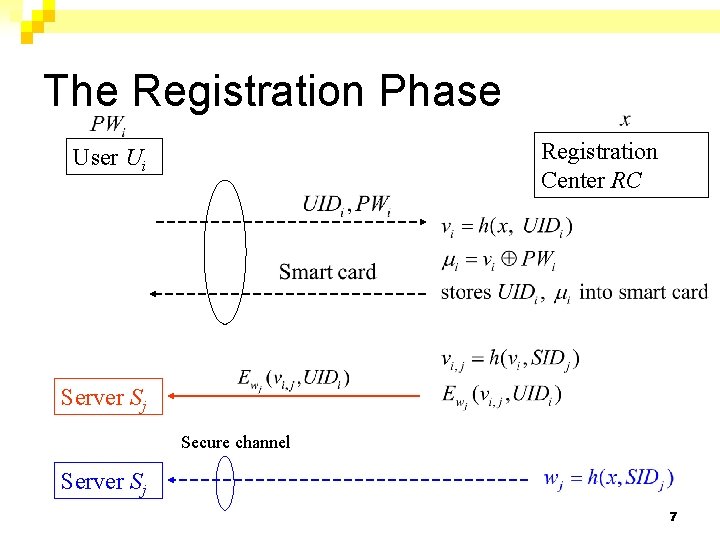
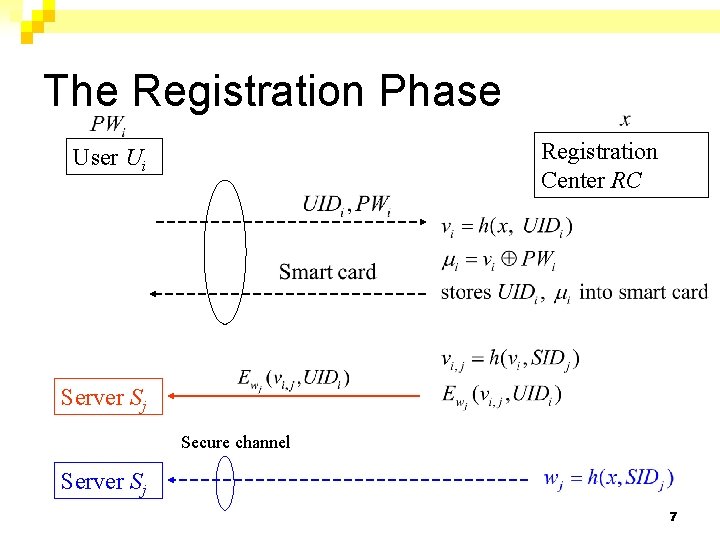
The Registration Phase Registration Center RC User Ui Server Sj Secure channel Server Sj 7
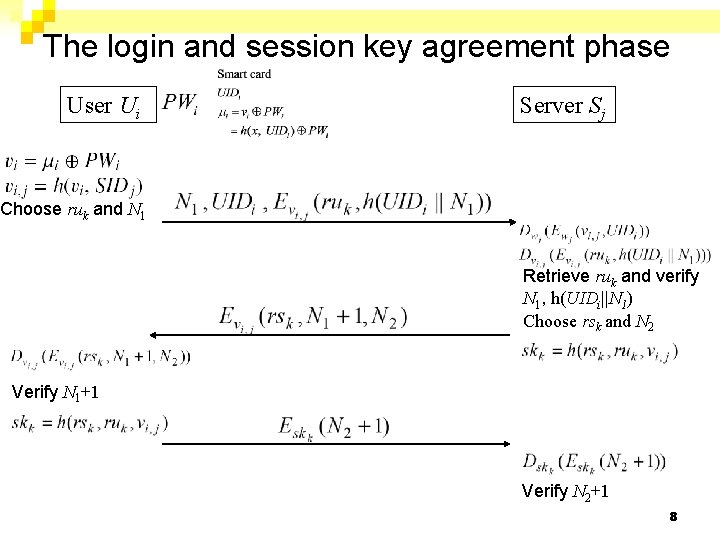
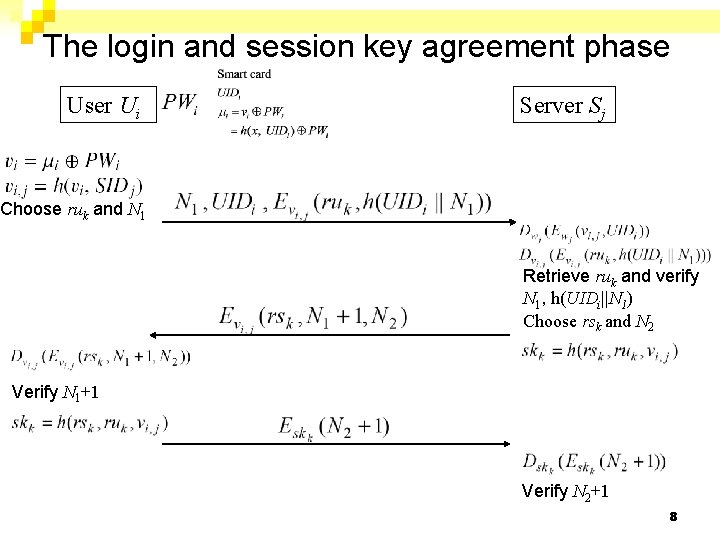
The login and session key agreement phase User Ui Server Sj Choose ruk and N 1 Retrieve ruk and verify N 1, h(UIDi||N 1) Choose rsk and N 2 Verify N 1+1 Verify N 2+1 8
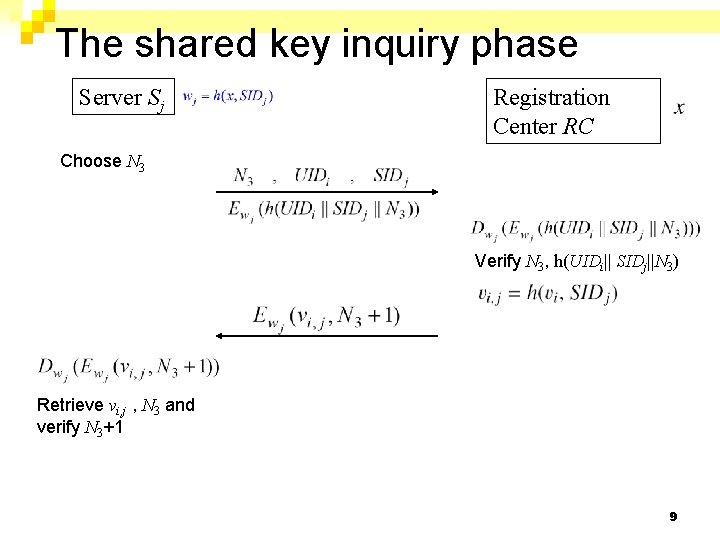
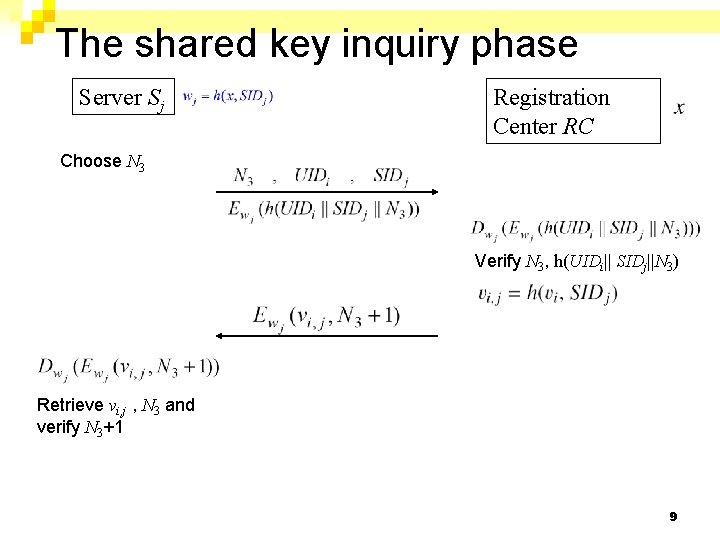
The shared key inquiry phase Server Sj Registration Center RC Choose N 3 Verify N 3, h(UIDi|| SIDj||N 3) Retrieve vi, j , N 3 and verify N 3+1 9
Advantages n n n n Single registration No verification table Freely chosen password The computation and communication cost is very low Mutual authentication Session key agreement Nonce-based scheme 10
Weaknesses n Poor Reparability ¨ n If the smart card is not tamper-resistant Lack of Forward Secrecy If vi, j is compromised ¨ Diffie-Hellman key exchange scheme ¨ n Vulnerability to Privileged Insider’s Attack Ui’s password PWi is revealed to RC. ¨ If the user uses the same password to access several servers ¨ n n No User Eviction Mechanism Misleading Claims 11
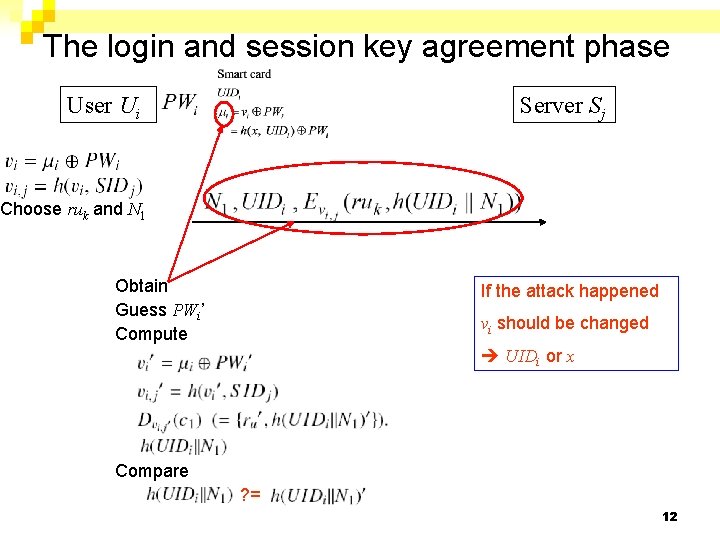
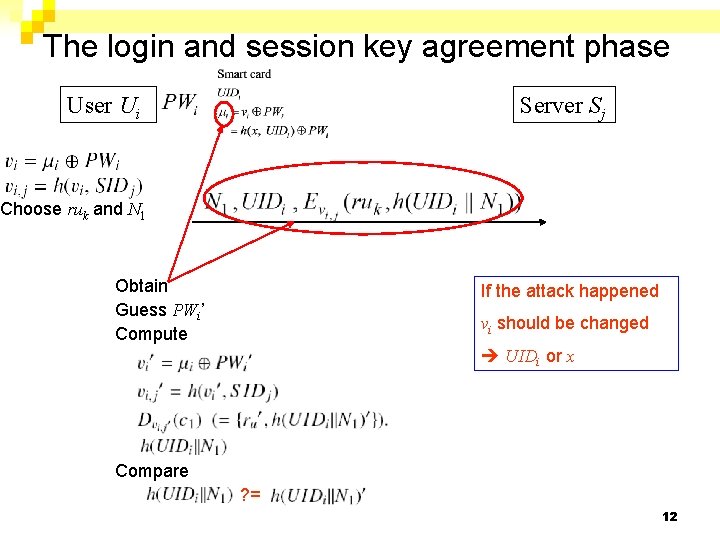
The login and session key agreement phase User Ui Server Sj Choose ruk and N 1 Obtain Guess PWi’ Compute If the attack happened vi should be changed UIDi or x Compare ? = 12
13