CPS 110 Wrapping up memory Landon Cox March
- Slides: 50
CPS 110: Wrapping up memory Landon Cox March 6, 2008
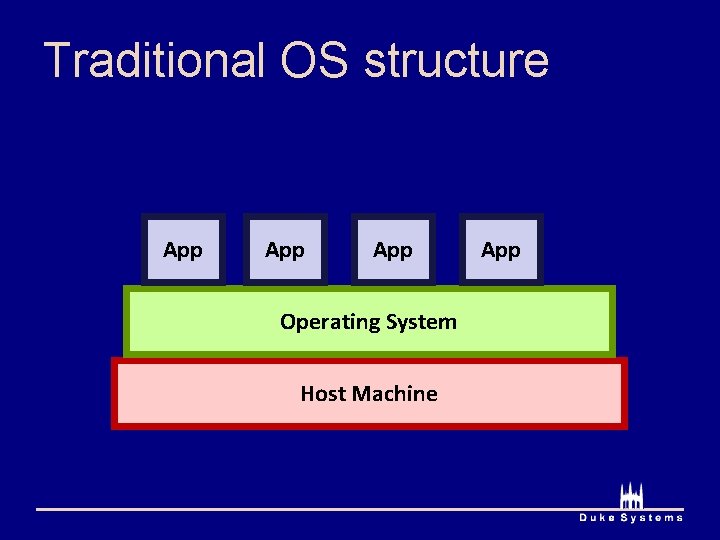
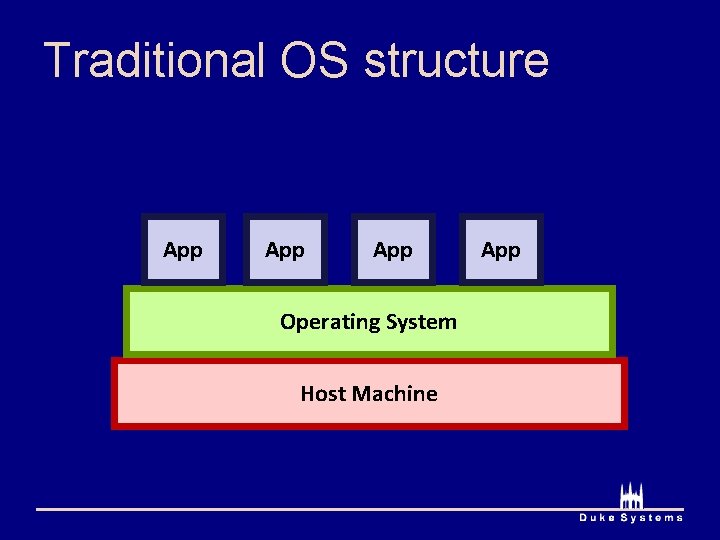
Traditional OS structure App App Operating System Host Machine App
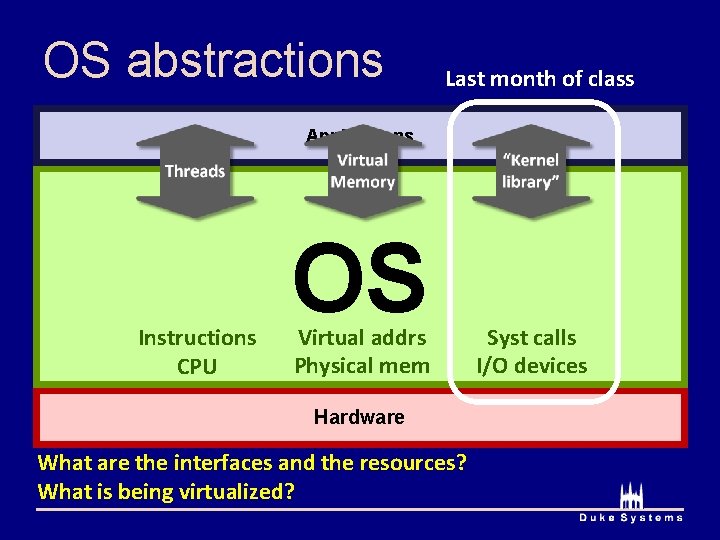
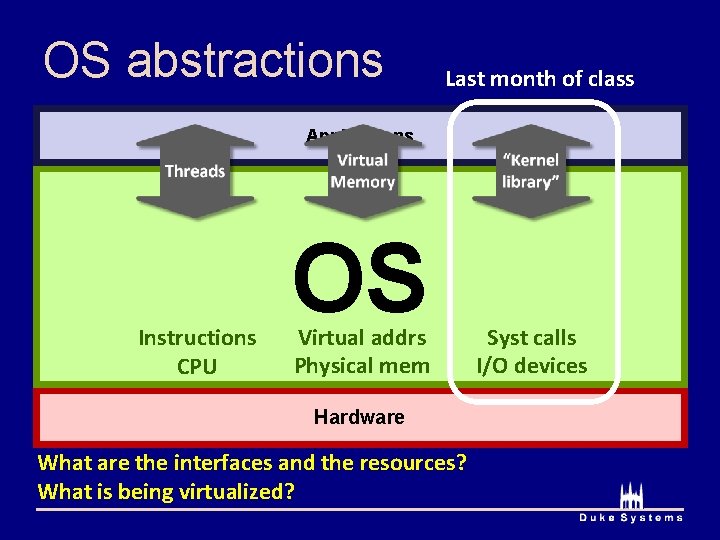
OS abstractions Last month of class Applications Instructions CPU OS Virtual addrs Physical mem Hardware What are the interfaces and the resources? What is being virtualized? Syst calls I/O devices
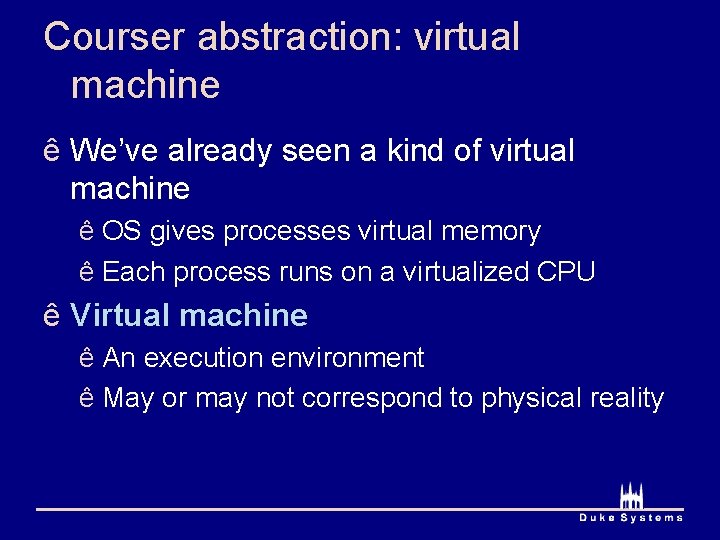
Courser abstraction: virtual machine ê We’ve already seen a kind of virtual machine ê OS gives processes virtual memory ê Each process runs on a virtualized CPU ê Virtual machine ê An execution environment ê May or may not correspond to physical reality
Virtual machine options ê How to implement a virtual machine? 1. Interpreted virtual machines ê Translate every VM instruction ê Kind of like on-the-fly compilation ê VM instruction HW instruction(s) 2. Direct execution ê Execute instructions directly ê Emulate the hard ones
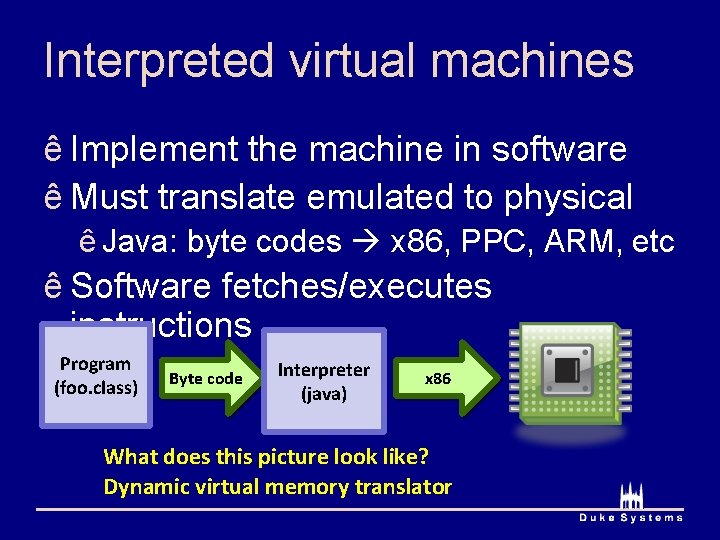
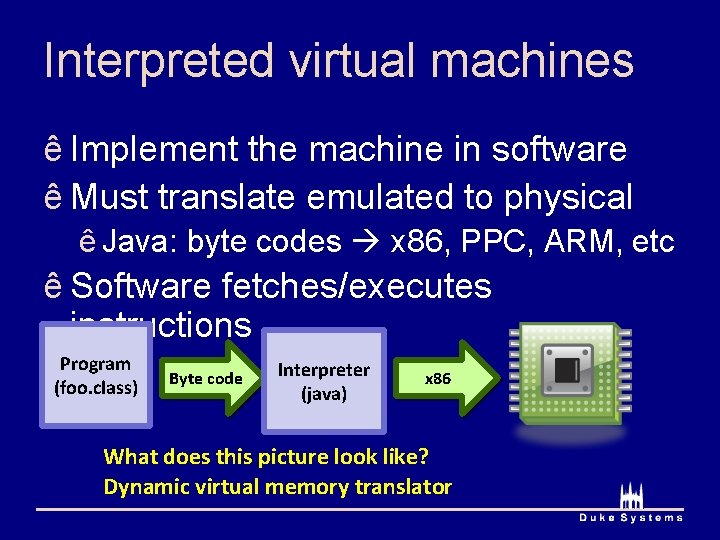
Interpreted virtual machines ê Implement the machine in software ê Must translate emulated to physical ê Java: byte codes x 86, PPC, ARM, etc ê Software fetches/executes instructions Program (foo. class) Byte code Interpreter (java) x 86 What does this picture look like? Dynamic virtual memory translator
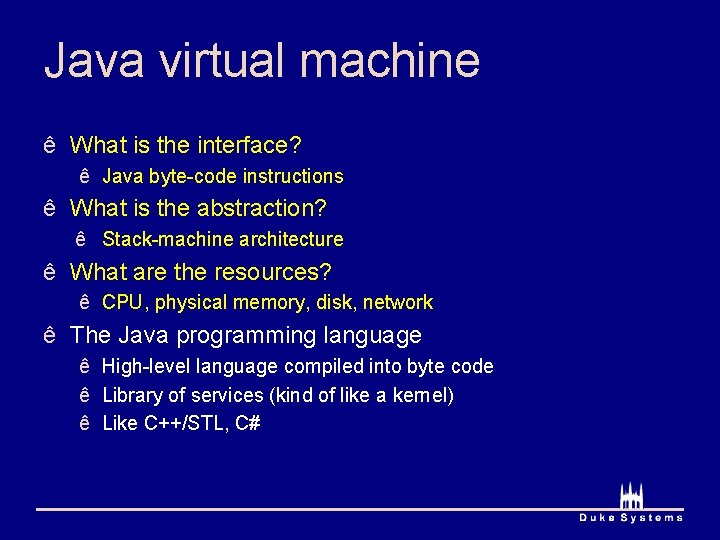
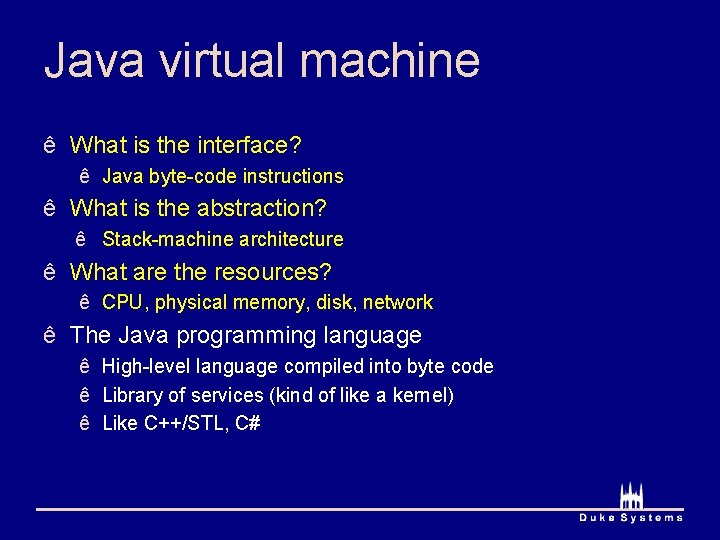
Java virtual machine ê What is the interface? ê Java byte-code instructions ê What is the abstraction? ê Stack-machine architecture ê What are the resources? ê CPU, physical memory, disk, network ê The Java programming language ê High-level language compiled into byte code ê Library of services (kind of like a kernel) ê Like C++/STL, C#
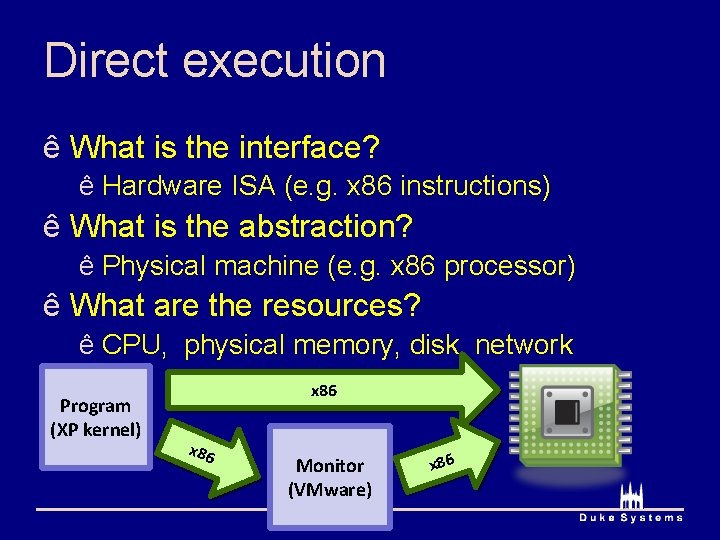
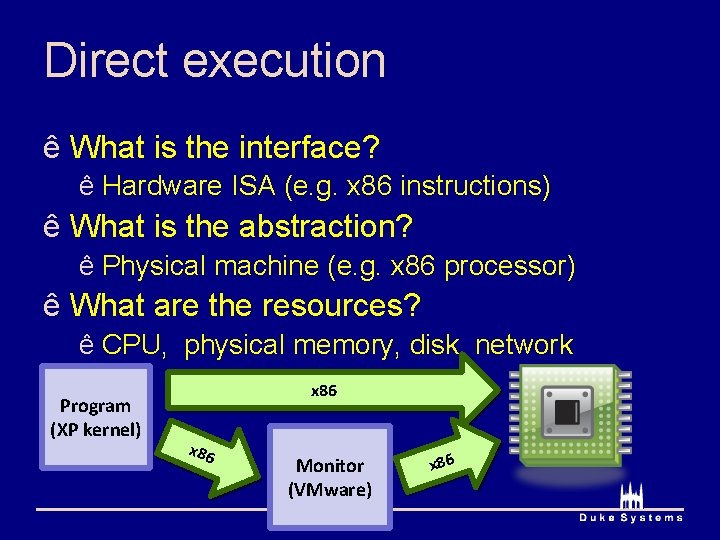
Direct execution ê What is the interface? ê Hardware ISA (e. g. x 86 instructions) ê What is the abstraction? ê Physical machine (e. g. x 86 processor) ê What are the resources? ê CPU, physical memory, disk, network Program (XP kernel) x 86 Monitor (VMware) x 86
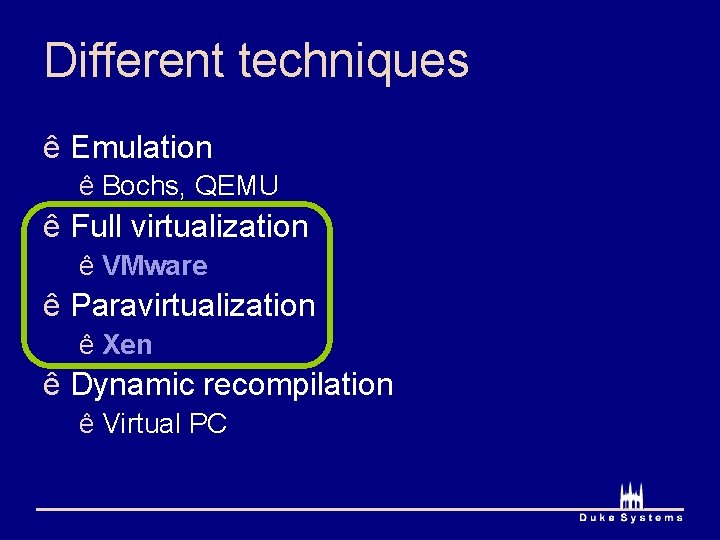
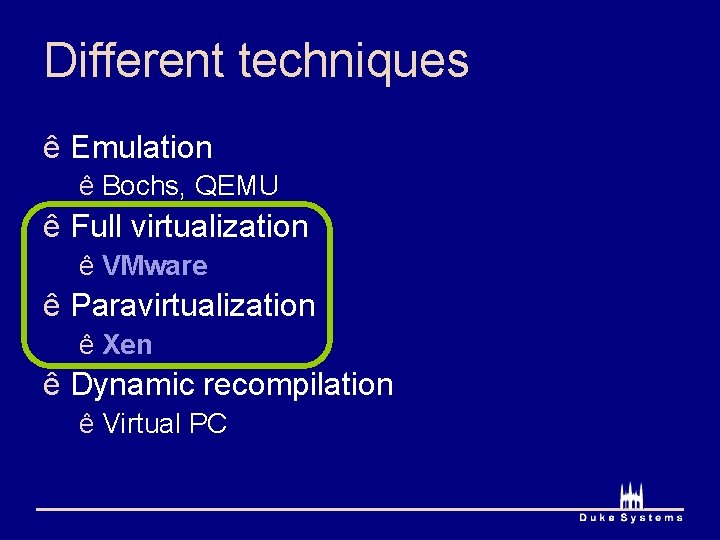
Different techniques ê Emulation ê Bochs, QEMU ê Full virtualization ê VMware ê Paravirtualization ê Xen ê Dynamic recompilation ê Virtual PC
Virtual machines are hot VMware IPO: $19. 1 billion Xen sale: $500 million
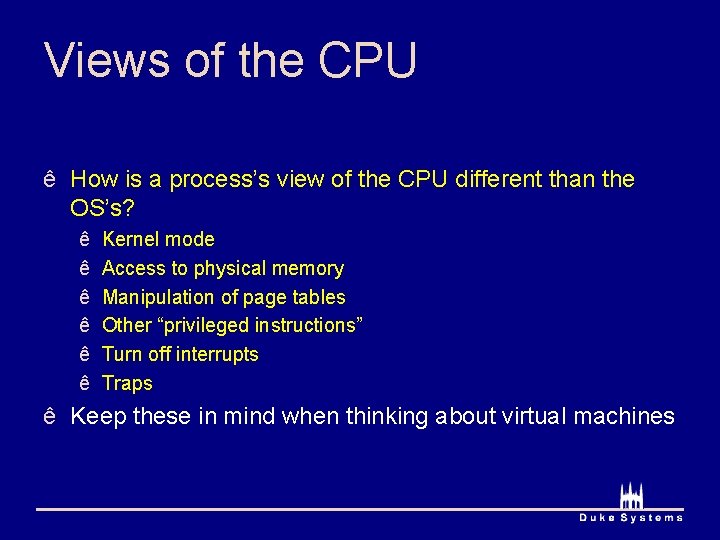
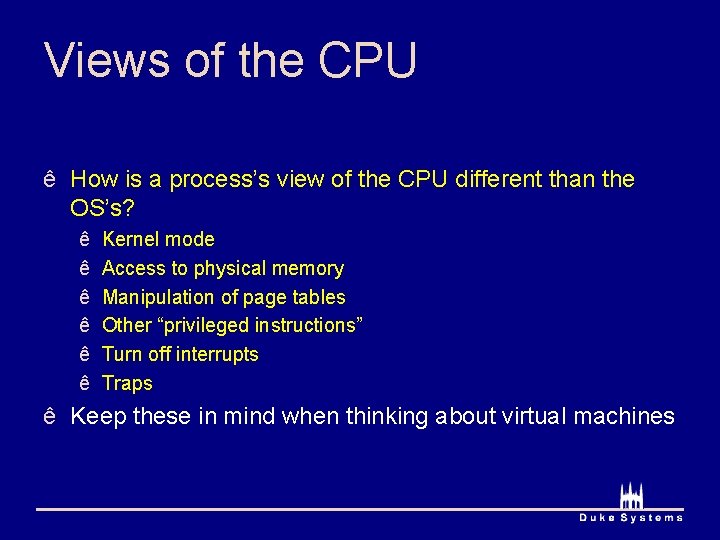
Views of the CPU ê How is a process’s view of the CPU different than the OS’s? ê ê ê Kernel mode Access to physical memory Manipulation of page tables Other “privileged instructions” Turn off interrupts Traps ê Keep these in mind when thinking about virtual machines
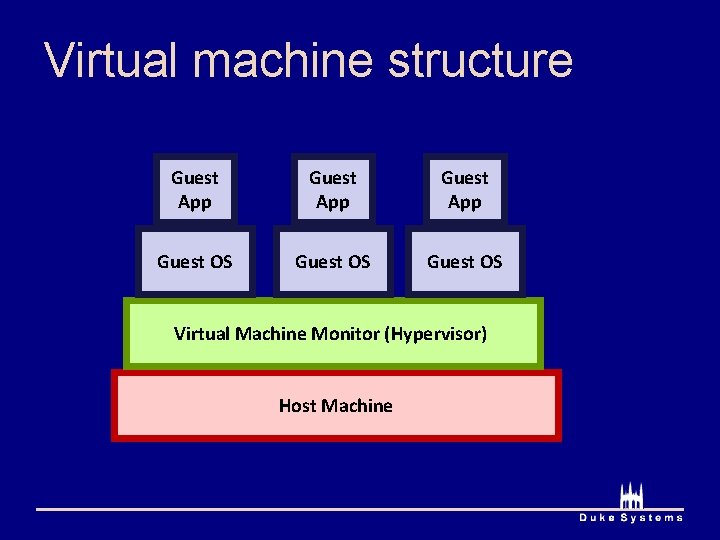
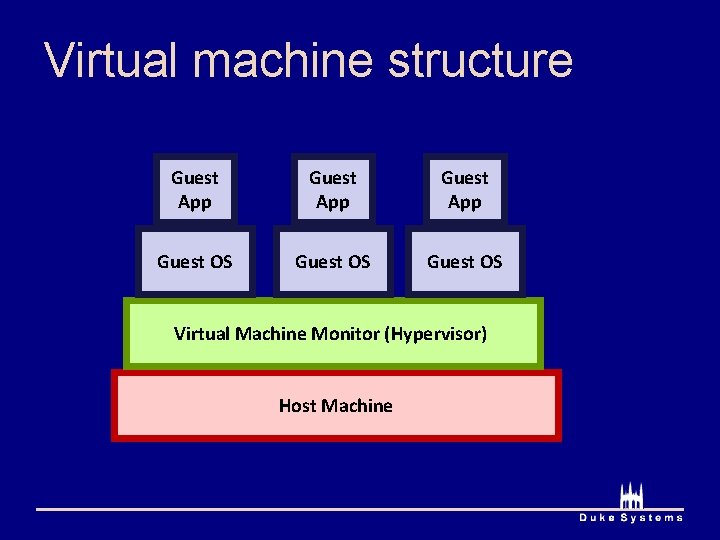
Virtual machine structure Guest App Guest OS Virtual Machine Monitor (Hypervisor) Host Machine
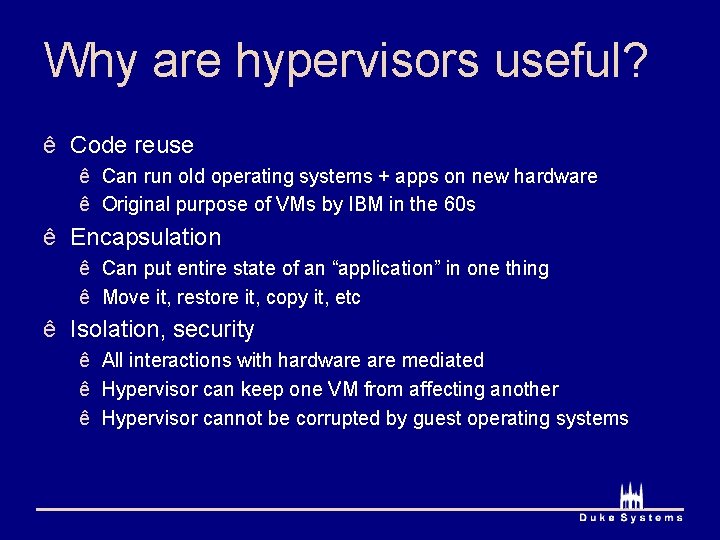
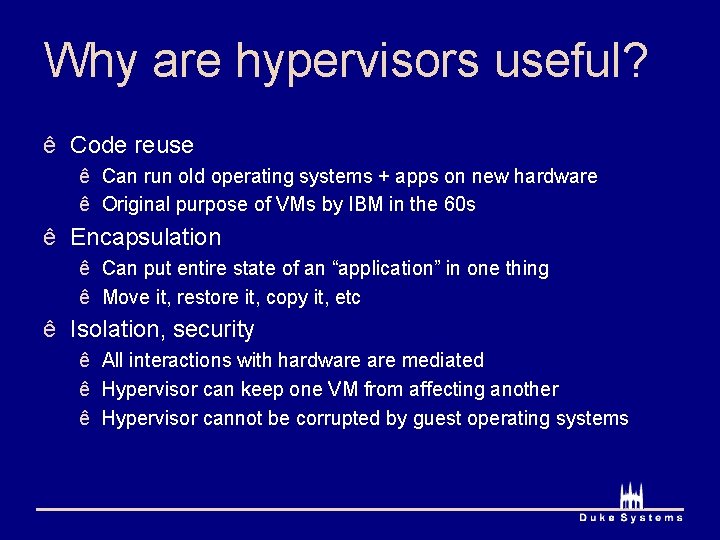
Why are hypervisors useful? ê Code reuse ê Can run old operating systems + apps on new hardware ê Original purpose of VMs by IBM in the 60 s ê Encapsulation ê Can put entire state of an “application” in one thing ê Move it, restore it, copy it, etc ê Isolation, security ê All interactions with hardware mediated ê Hypervisor can keep one VM from affecting another ê Hypervisor cannot be corrupted by guest operating systems
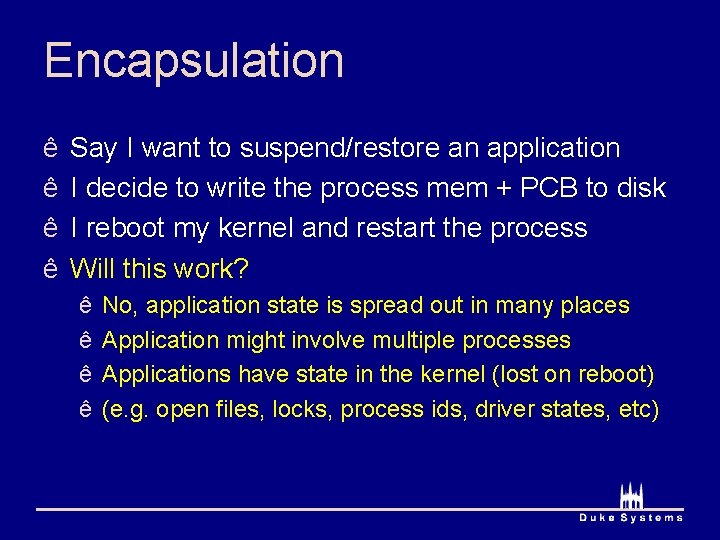
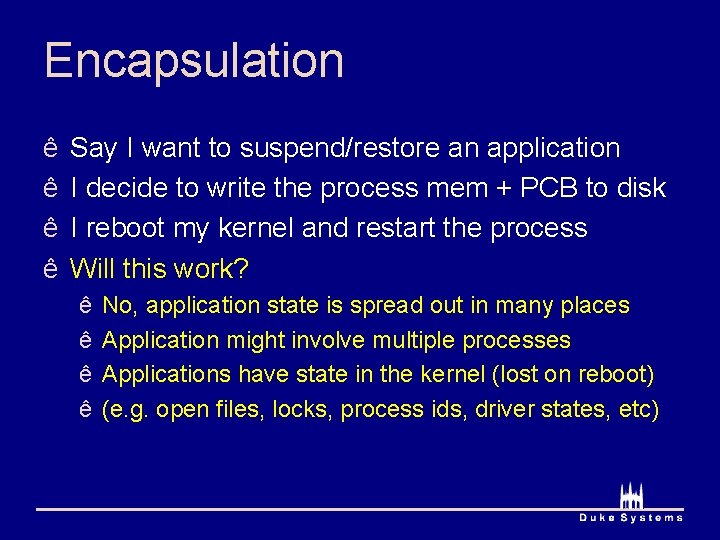
Encapsulation ê ê Say I want to suspend/restore an application I decide to write the process mem + PCB to disk I reboot my kernel and restart the process Will this work? ê ê No, application state is spread out in many places Application might involve multiple processes Applications have state in the kernel (lost on reboot) (e. g. open files, locks, process ids, driver states, etc)
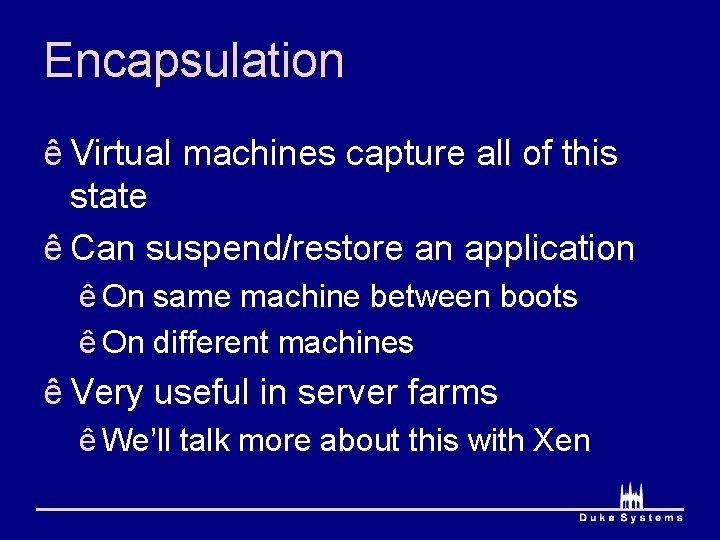
Encapsulation ê Virtual machines capture all of this state ê Can suspend/restore an application ê On same machine between boots ê On different machines ê Very useful in server farms ê We’ll talk more about this with Xen
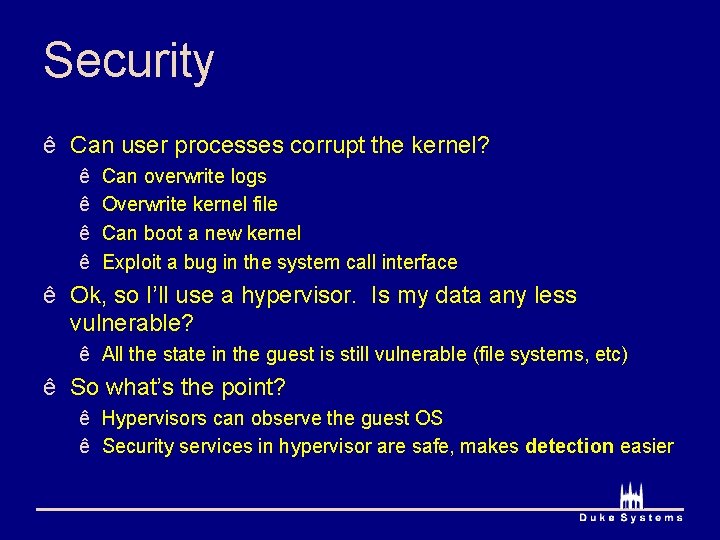
Security ê Can user processes corrupt the kernel? ê ê Can overwrite logs Overwrite kernel file Can boot a new kernel Exploit a bug in the system call interface ê Ok, so I’ll use a hypervisor. Is my data any less vulnerable? ê All the state in the guest is still vulnerable (file systems, etc) ê So what’s the point? ê Hypervisors can observe the guest OS ê Security services in hypervisor are safe, makes detection easier
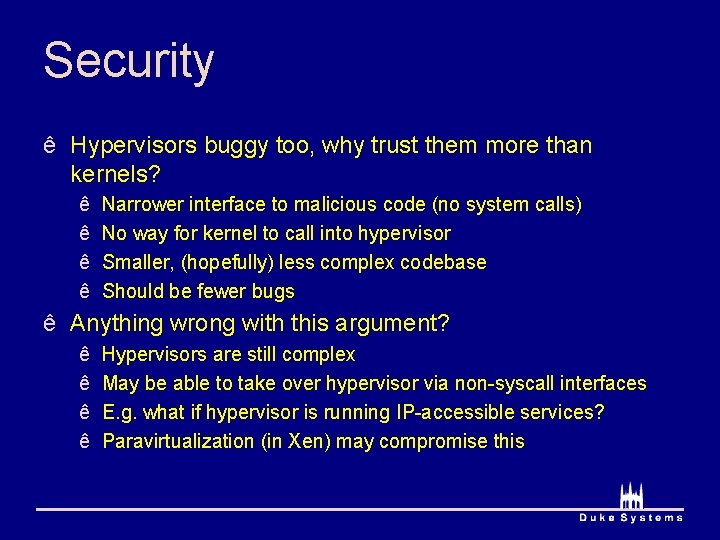
Security ê Hypervisors buggy too, why trust them more than kernels? ê ê Narrower interface to malicious code (no system calls) No way for kernel to call into hypervisor Smaller, (hopefully) less complex codebase Should be fewer bugs ê Anything wrong with this argument? ê ê Hypervisors are still complex May be able to take over hypervisor via non-syscall interfaces E. g. what if hypervisor is running IP-accessible services? Paravirtualization (in Xen) may compromise this
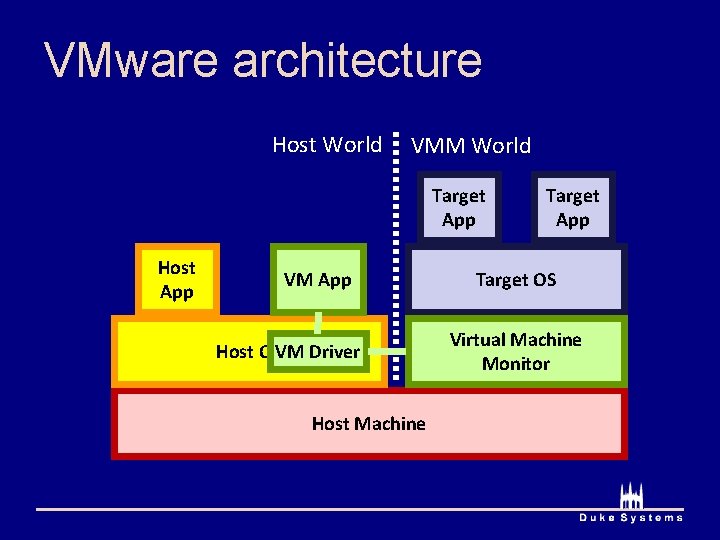
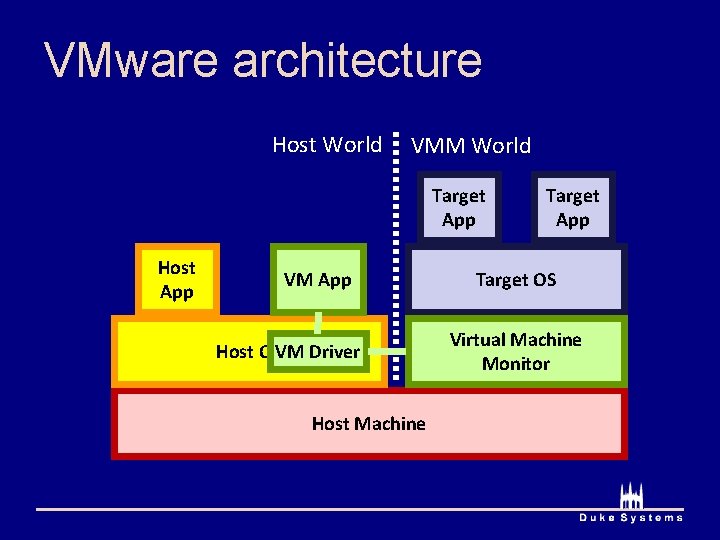
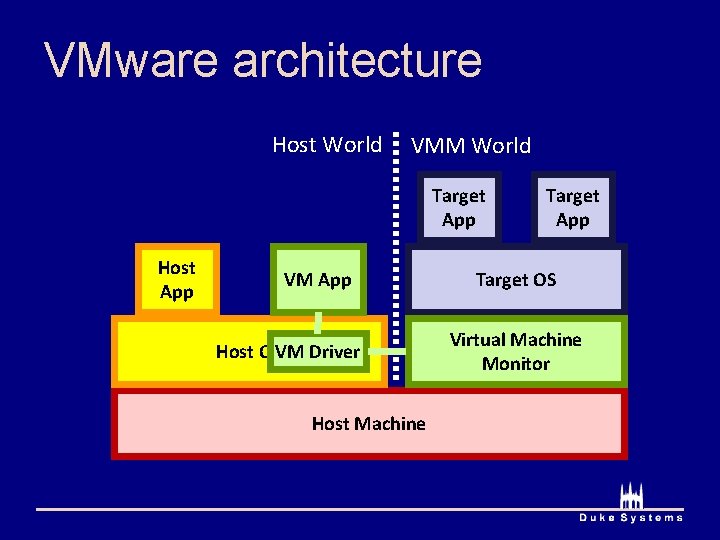
VMware architecture Host World VMM World Target App Host App VM App Host OSVM Driver Host Machine Target App Target OS Virtual Machine Monitor
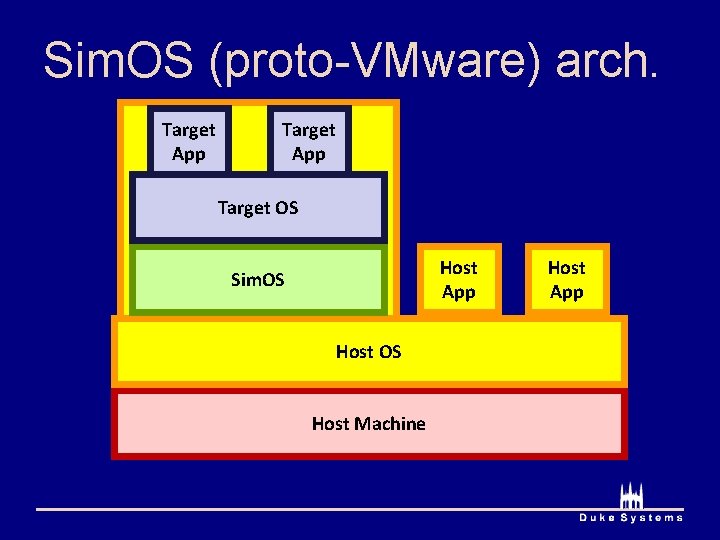
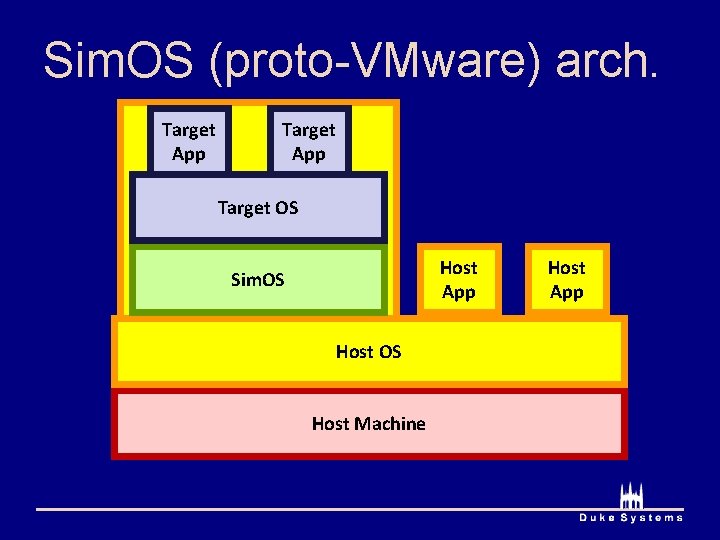
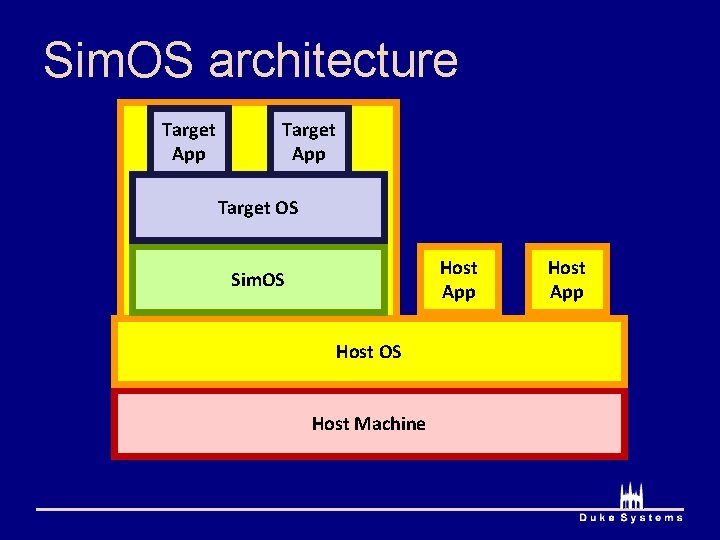
Sim. OS (proto-VMware) arch. Target App Target OS Host App Sim. OS Host Machine Host App
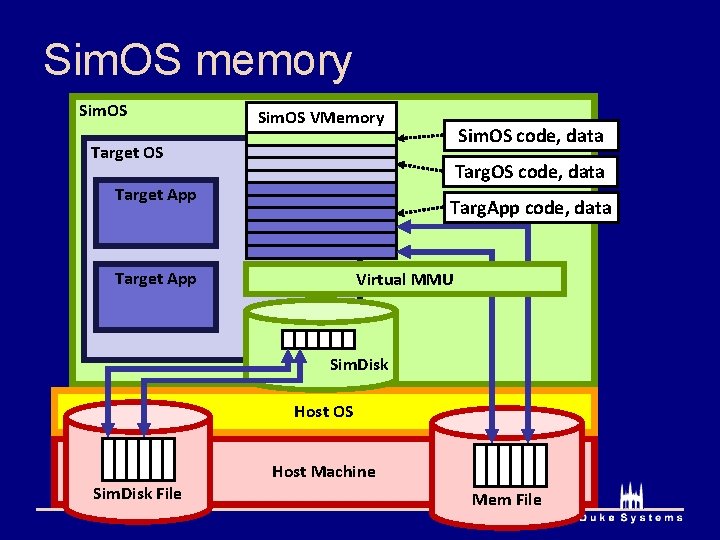
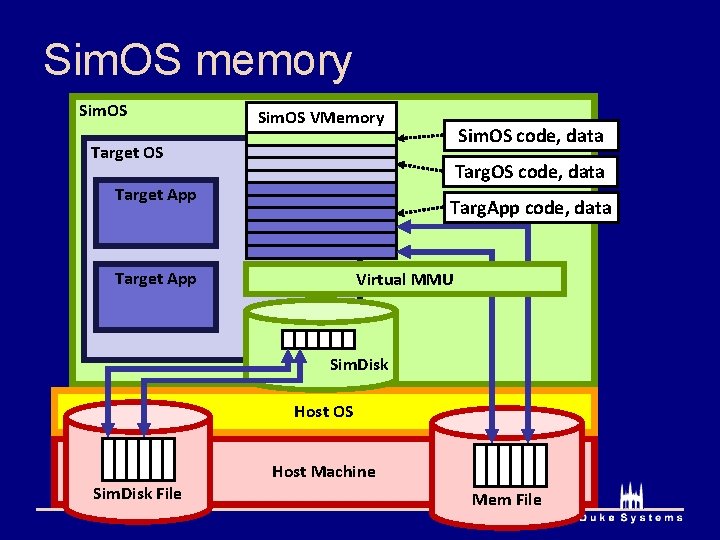
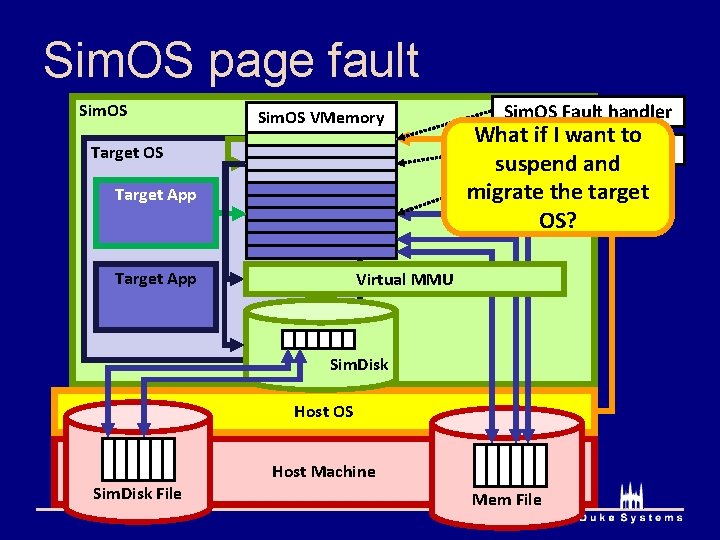
Sim. OS memory Sim. OS VMemory Sim. OS code, data Target OS Targ. OS code, data Target App Targ. App code, data Target App Virtual MMU Sim. Disk Host OS Sim. Disk File Host Machine Mem File
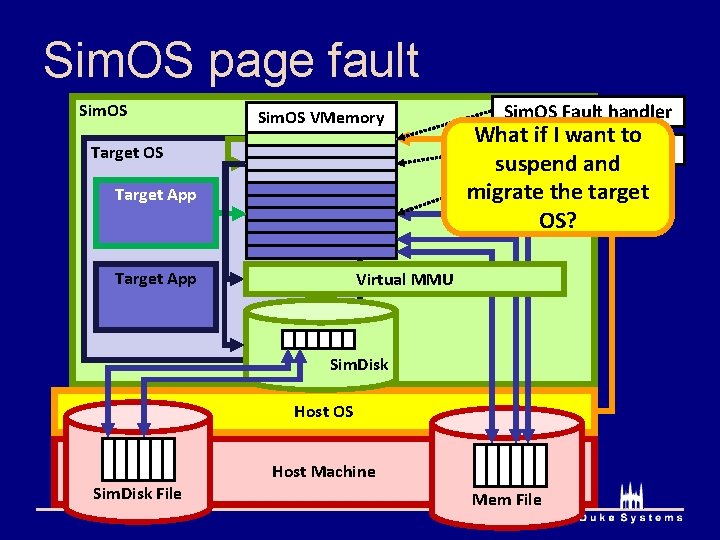
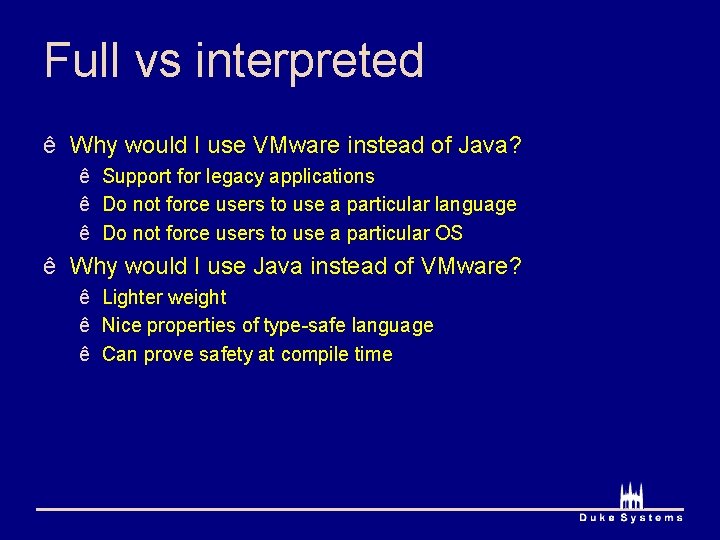
Sim. OS page fault Sim. OS VMemory Target OS Target App Sim. OS Fault handler What if I want to Targ. OS Fault handler suspend and Unmapped addr migrate the target OS? Virtual MMU Sim. Disk Host OS Sim. Disk File Host Machine Mem File
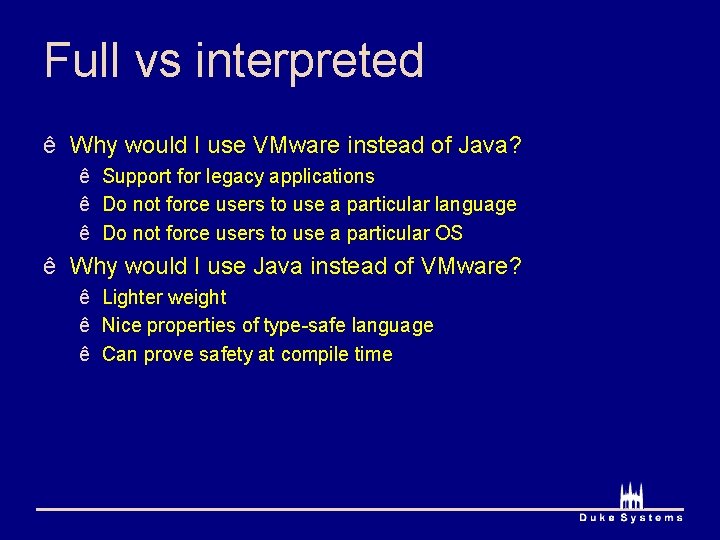
Full vs interpreted ê Why would I use VMware instead of Java? ê Support for legacy applications ê Do not force users to use a particular language ê Do not force users to use a particular OS ê Why would I use Java instead of VMware? ê Lighter weight ê Nice properties of type-safe language ê Can prove safety at compile time
Full vs interpreted ê What about protection? ê What does Java use for protection? VMware? ê Java relies on language features (cannot express unsafe computation) ê VMware relies on the hardware to enforce protection (like an OS) ê What are the trade-offs? Which protection model is better? ê Java gives you stronger (i. e. provable) safety guarantees ê Hardware protection doesn’t constrain programming expressiveness ê What about sharing (kind of the opposite of protection)? ê Sharing among components in Java is easy ê (call a function, compiler makes sure it is safe)
Singularity (could try both)
Virtual machine challenges ê Privilege modes ê Memory management ê Protection ê Performance ê Many more for every architecture…
Course administration ê Multi-process test cases ê Autograder will test your pager with > 1 process ê But don’t submit any to the autograder ê How to write multi-process test cases ê Use vm_yield ê Can quickly open processes in different windows ê Can use sleep (unsigned int seconds) ê Could use fork
Course administration ê Extra office hours after spring break ê Will announce over Blackboard ê Other questions?
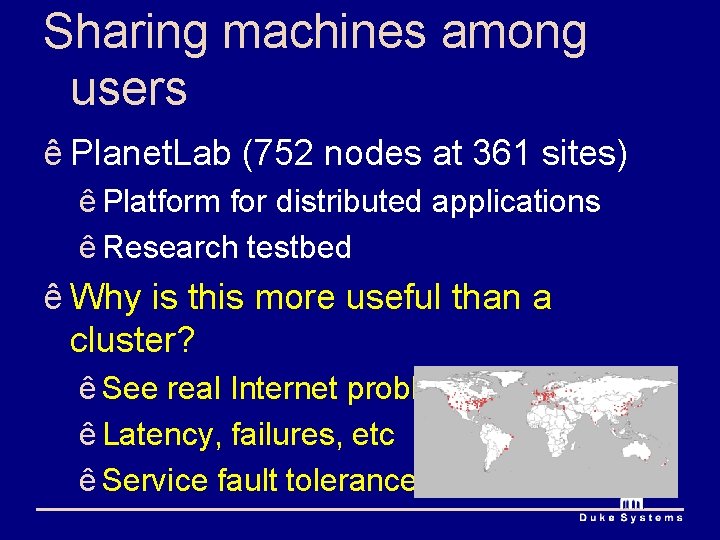
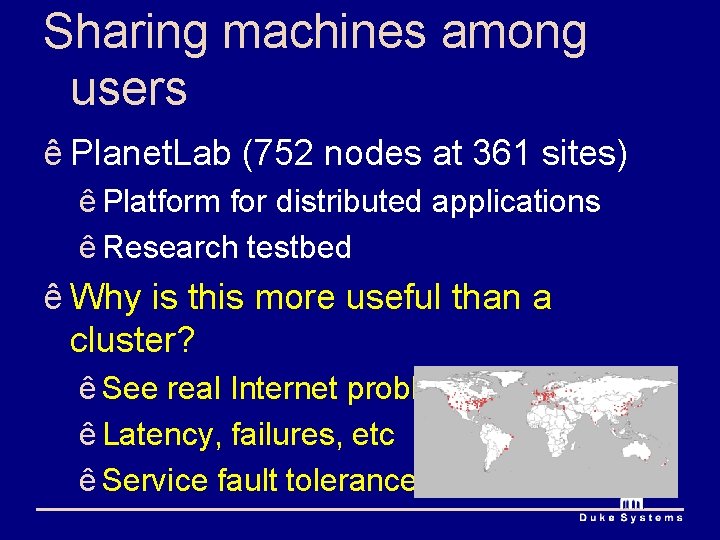
Sharing machines among users ê Planet. Lab (752 nodes at 361 sites) ê Platform for distributed applications ê Research testbed ê Why is this more useful than a cluster? ê See real Internet problems ê Latency, failures, etc ê Service fault tolerance
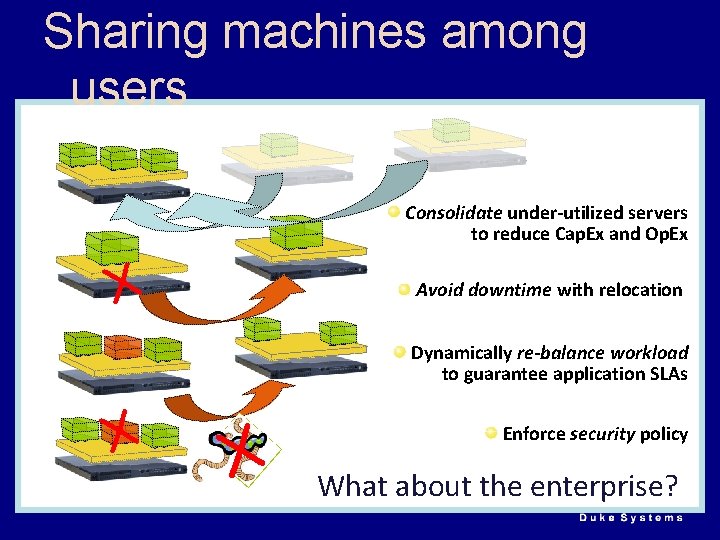
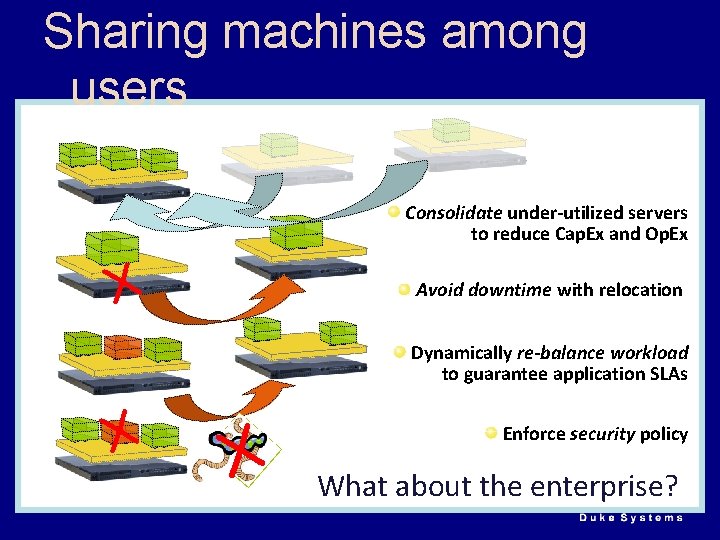
Sharing machines among users Consolidate under-utilized servers to reduce Cap. Ex and Op. Ex X Avoid downtime with relocation Dynamically re-balance workload to guarantee application SLAs X X Enforce security policy What about the enterprise?
Sharing machines among users ê When? ê Planet. Lab (testbeds, distributed services) ê Data centers (three-tier web applications) ê Scientific computing (protein folding, etc) ê What should the interface be?
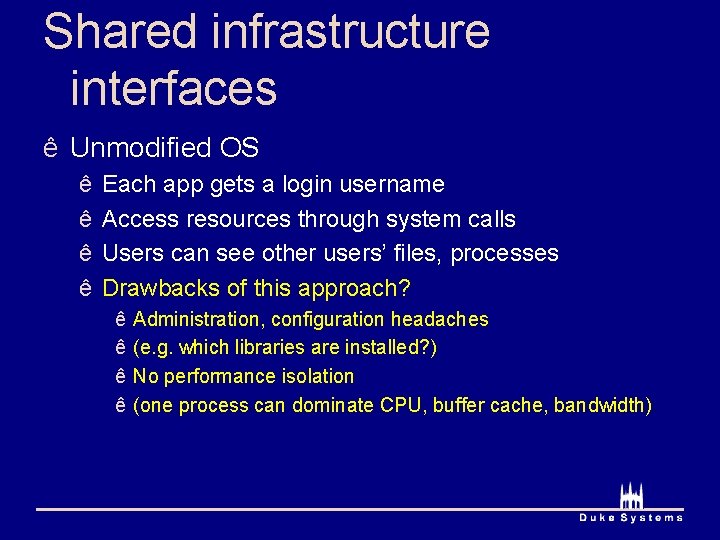
Shared infrastructure interfaces ê Unmodified OS ê ê Each app gets a login username Access resources through system calls Users can see other users’ files, processes Drawbacks of this approach? ê ê Administration, configuration headaches (e. g. which libraries are installed? ) No performance isolation (one process can dominate CPU, buffer cache, bandwidth)
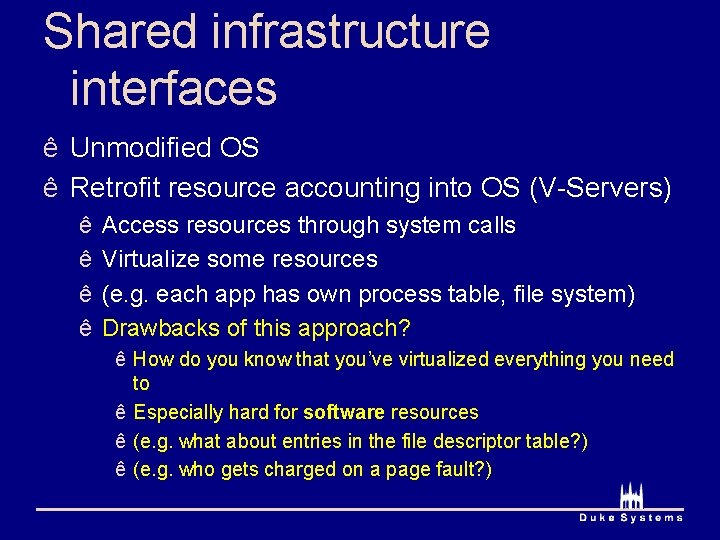
Shared infrastructure interfaces ê Unmodified OS ê Retrofit resource accounting into OS (V-Servers) ê ê Access resources through system calls Virtualize some resources (e. g. each app has own process table, file system) Drawbacks of this approach? ê How do you know that you’ve virtualized everything you need to ê Especially hard for software resources ê (e. g. what about entries in the file descriptor table? ) ê (e. g. who gets charged on a page fault? )
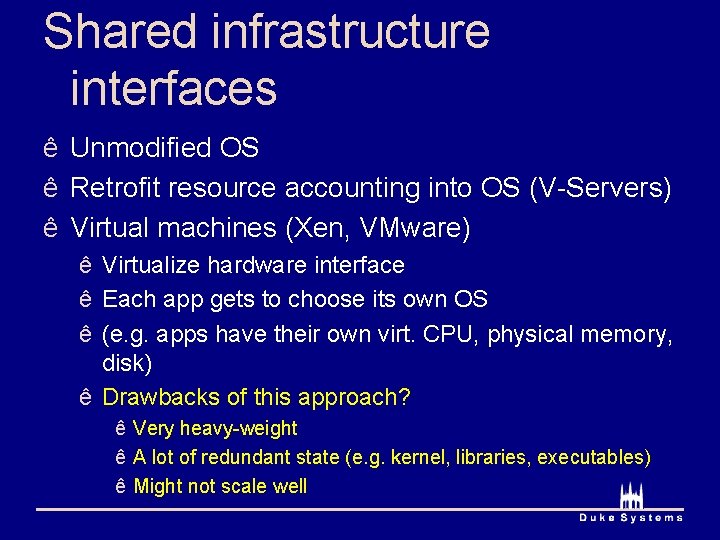
Shared infrastructure interfaces ê Unmodified OS ê Retrofit resource accounting into OS (V-Servers) ê Virtual machines (Xen, VMware) ê Virtualize hardware interface ê Each app gets to choose its own OS ê (e. g. apps have their own virt. CPU, physical memory, disk) ê Drawbacks of this approach? ê Very heavy-weight ê A lot of redundant state (e. g. kernel, libraries, executables) ê Might not scale well
Amazon EC 2 Anyone know what EC 2 uses? Xen
Xen challenges ê Kind of the opposite approach of VServers ê V-Servers: start with OS, virtualize ê Xen: start with VM, “para-virtualize” ê Goals ê Performance isolation ê Support many operating systems ê Reduce performance overhead of virtualization
Para-virtualization ê Full virtualization ê Fool OS into thinking it has access to hardware ê Para-virtualization ê Expose real and virtual resources to OS ê Why do we need para-virtualization? ê Mostly because X 86 makes full virtualization hard
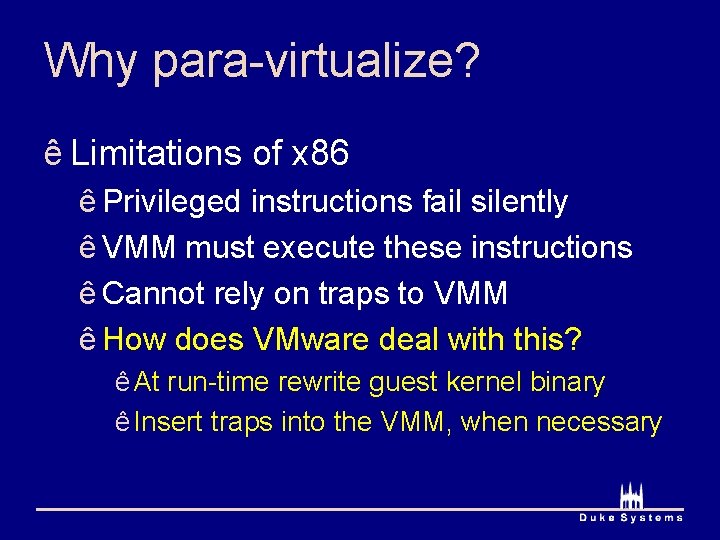
Why para-virtualize? ê Limitations of x 86 ê Privileged instructions fail silently ê VMM must execute these instructions ê Cannot rely on traps to VMM ê How does VMware deal with this? ê At run-time rewrite guest kernel binary ê Insert traps into the VMM, when necessary
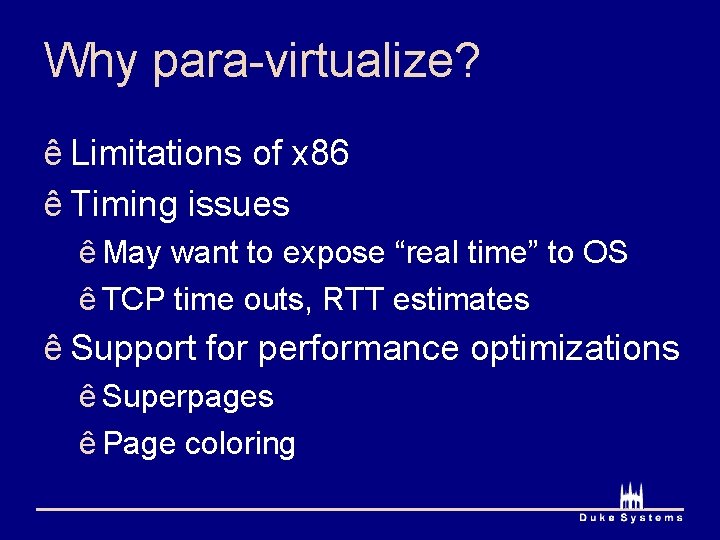
Why para-virtualize? ê Limitations of x 86 ê Timing issues ê May want to expose “real time” to OS ê TCP time outs, RTT estimates ê Support for performance optimizations ê Superpages ê Page coloring
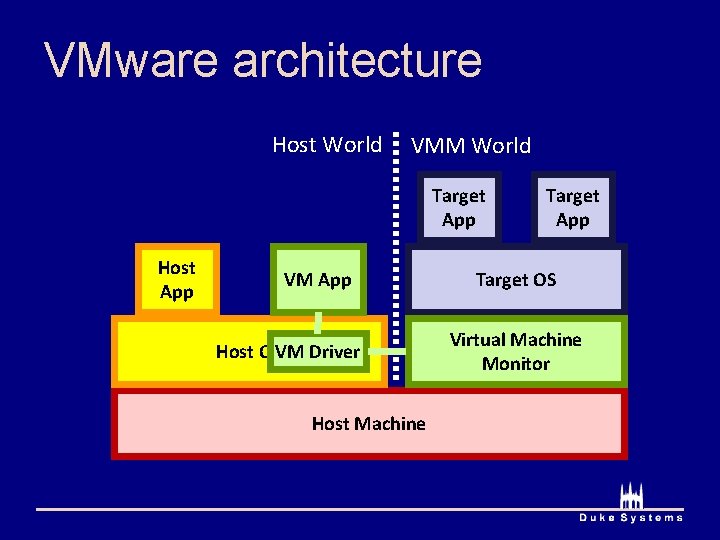
VMware architecture Host World VMM World Target App Host App VM App Host OSVM Driver Host Machine Target App Target OS Virtual Machine Monitor
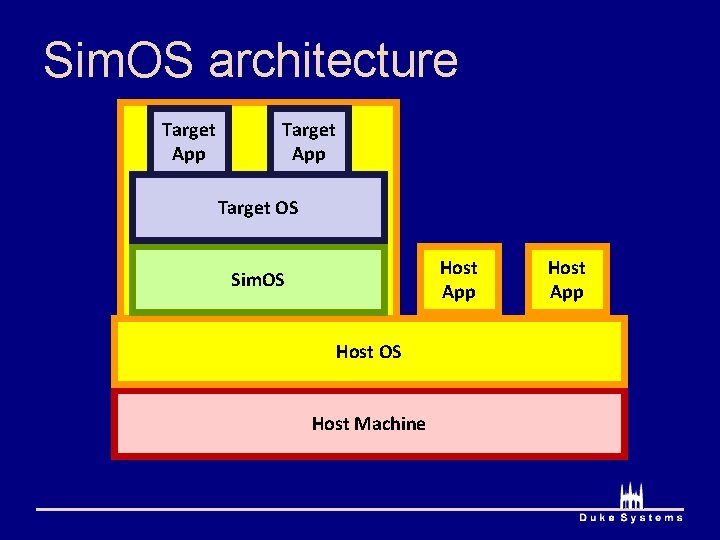
Sim. OS architecture Target App Target OS Host App Sim. OS Host Machine Host App
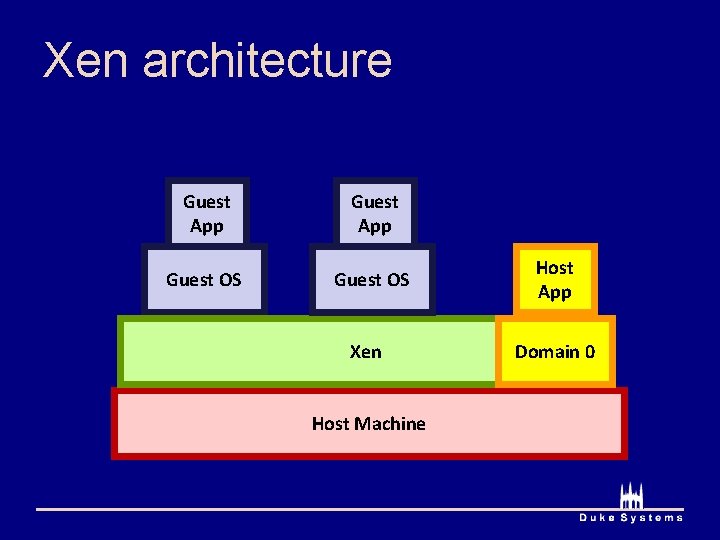
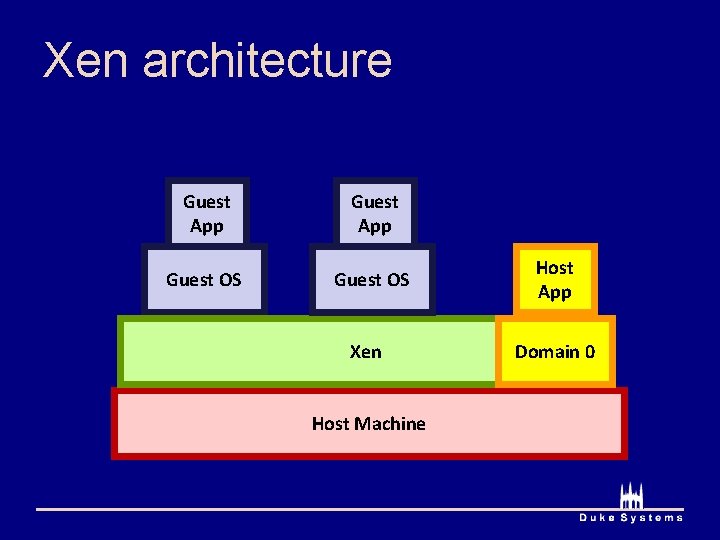
Xen architecture Guest App Guest OS Host App Xen Domain 0 Host Machine
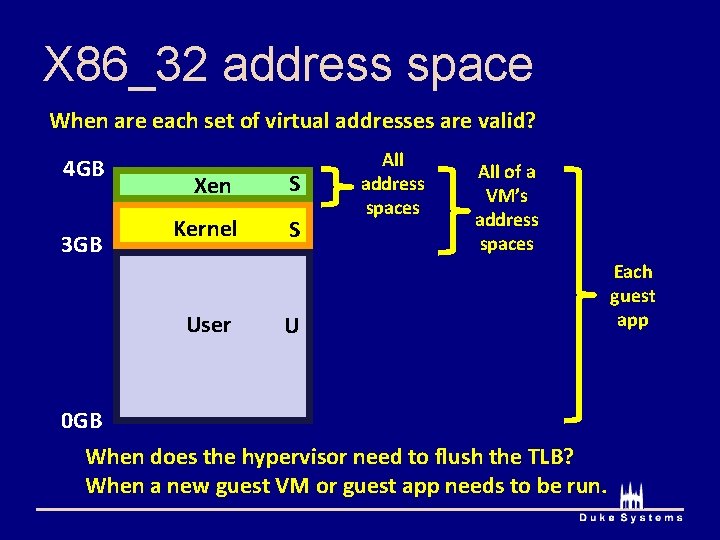
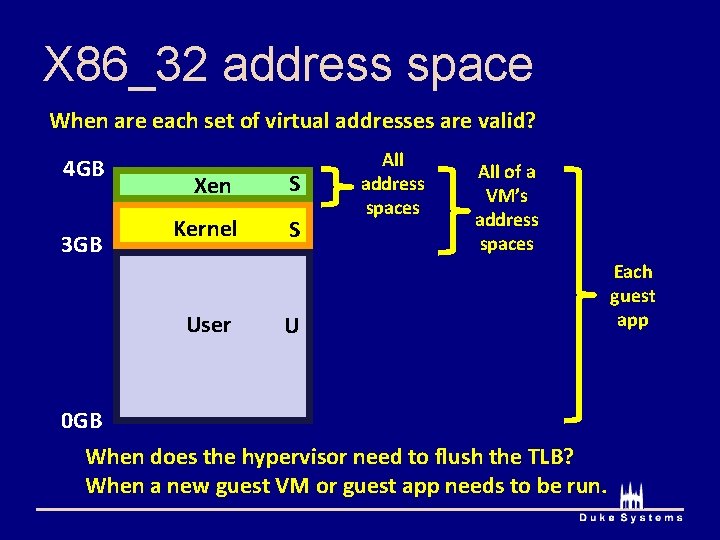
X 86_32 address space When are each set of virtual addresses are valid? 4 GB 3 GB Xen S Kernel S User All address spaces All of a VM’s address spaces U 0 GB When does the hypervisor need to flush the TLB? When a new guest VM or guest app needs to be run. Each guest app
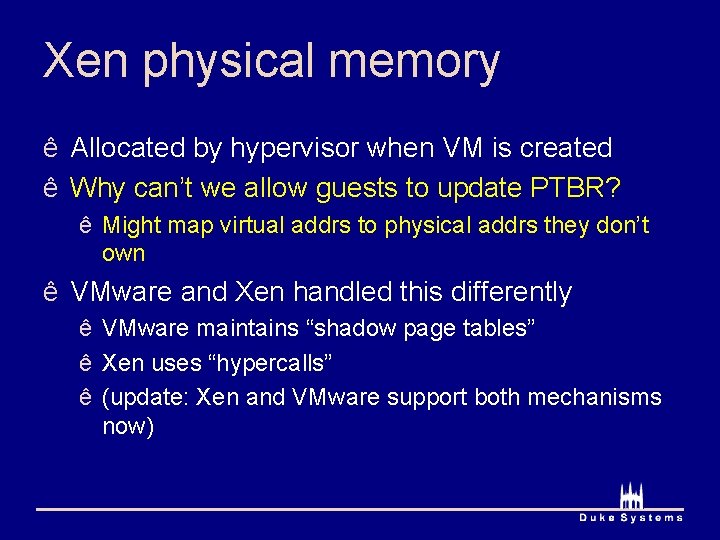
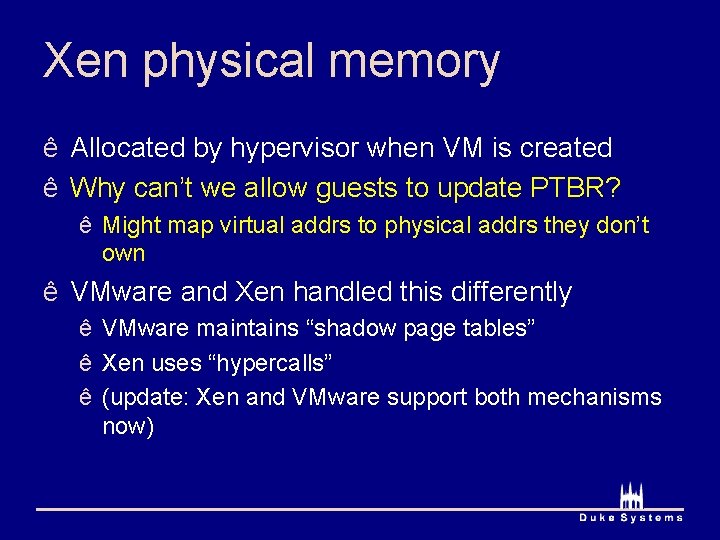
Xen physical memory ê Allocated by hypervisor when VM is created ê Why can’t we allow guests to update PTBR? ê Might map virtual addrs to physical addrs they don’t own ê VMware and Xen handled this differently ê VMware maintains “shadow page tables” ê Xen uses “hypercalls” ê (update: Xen and VMware support both mechanisms now)
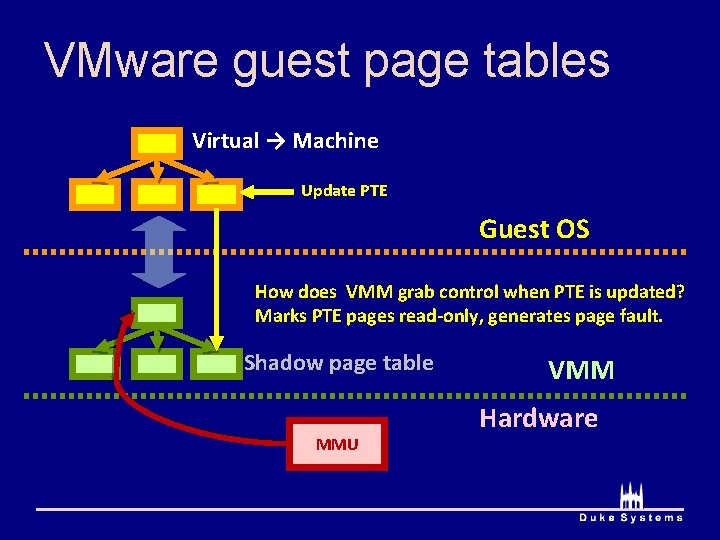
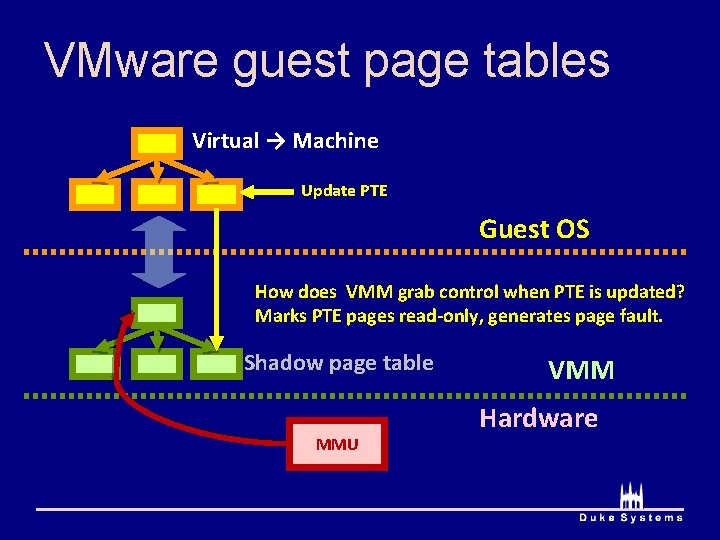
VMware guest page tables Virtual → Machine Update PTE Guest OS How does VMM grab control when PTE is updated? Marks PTE pages read-only, generates page fault. Shadow page table MMU VMM Hardware
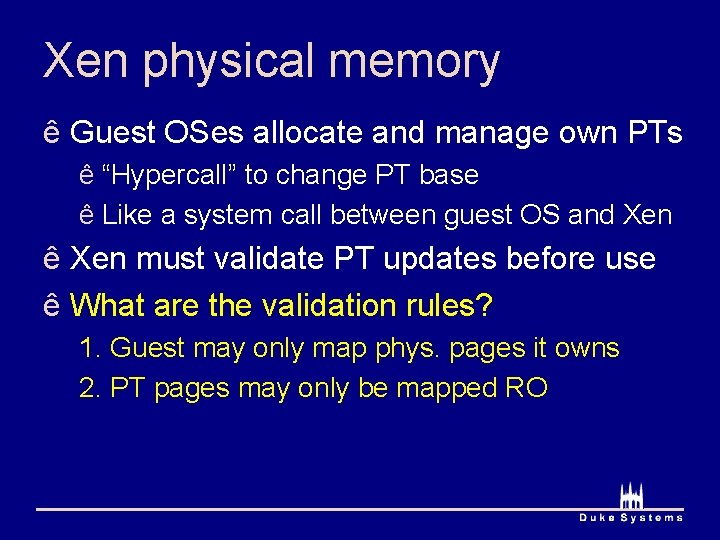
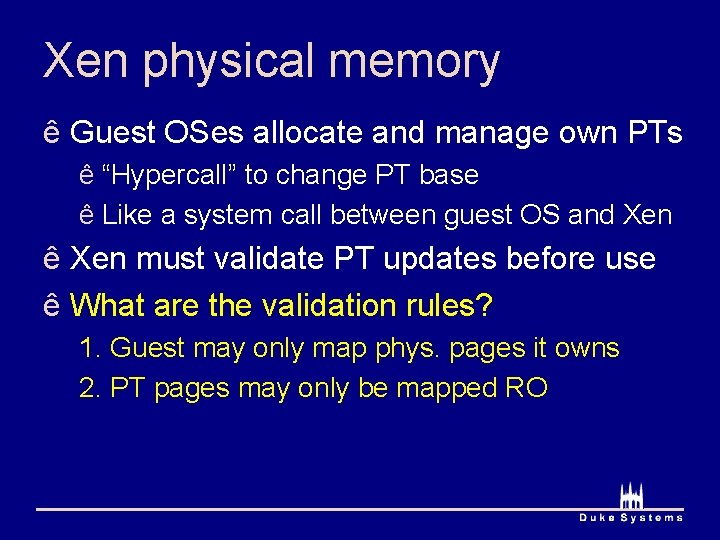
Xen physical memory ê Guest OSes allocate and manage own PTs ê “Hypercall” to change PT base ê Like a system call between guest OS and Xen ê Xen must validate PT updates before use ê What are the validation rules? 1. Guest may only map phys. pages it owns 2. PT pages may only be mapped RO
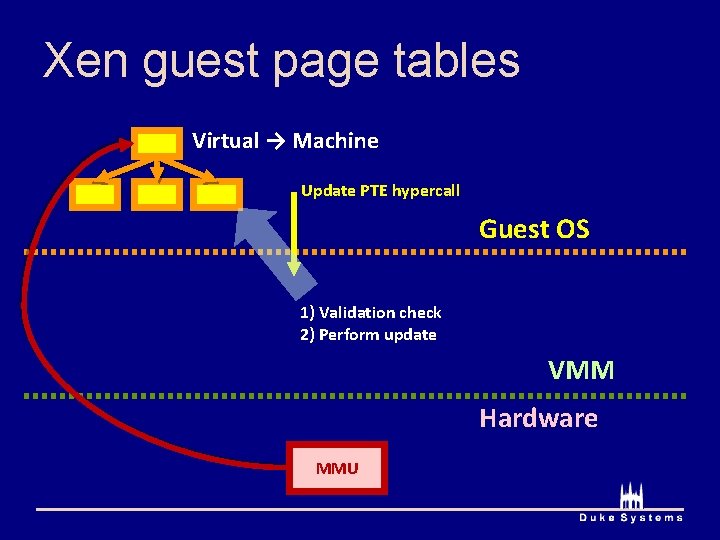
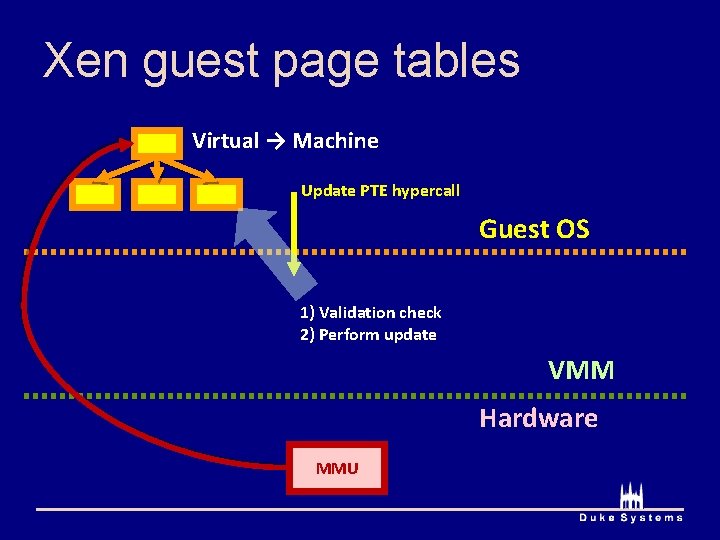
Xen guest page tables Virtual → Machine Update PTE hypercall Guest OS 1) Validation check 2) Perform update VMM Hardware MMU
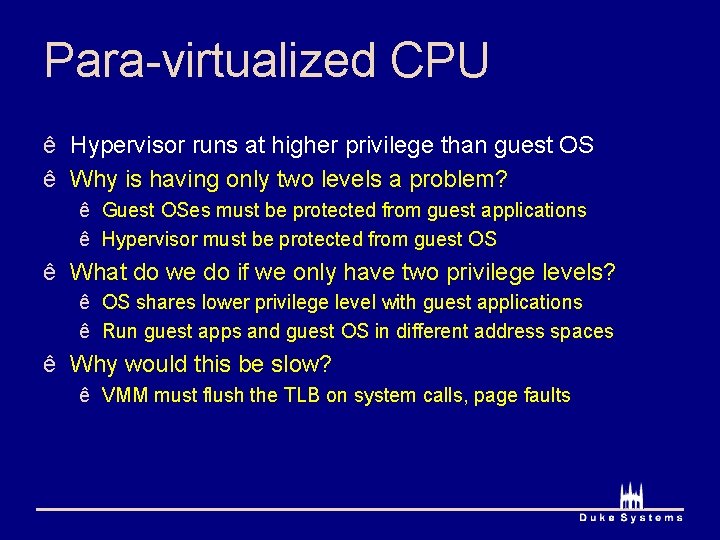
Para-virtualized CPU ê Hypervisor runs at higher privilege than guest OS ê Why is having only two levels a problem? ê Guest OSes must be protected from guest applications ê Hypervisor must be protected from guest OS ê What do we do if we only have two privilege levels? ê OS shares lower privilege level with guest applications ê Run guest apps and guest OS in different address spaces ê Why would this be slow? ê VMM must flush the TLB on system calls, page faults
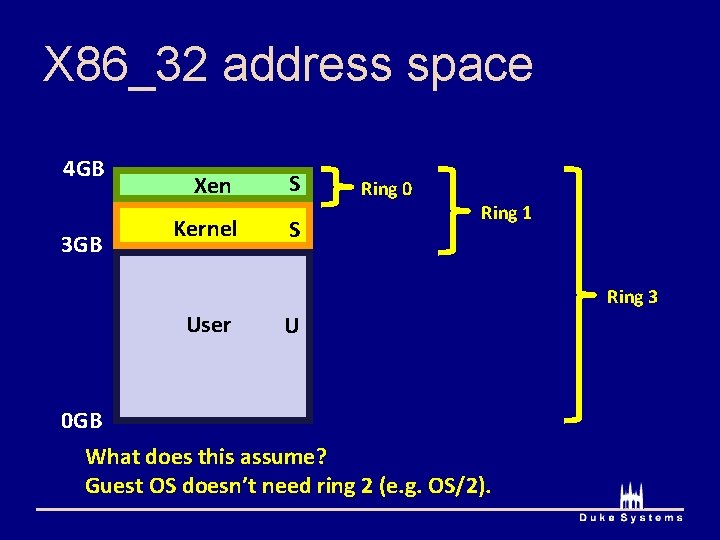
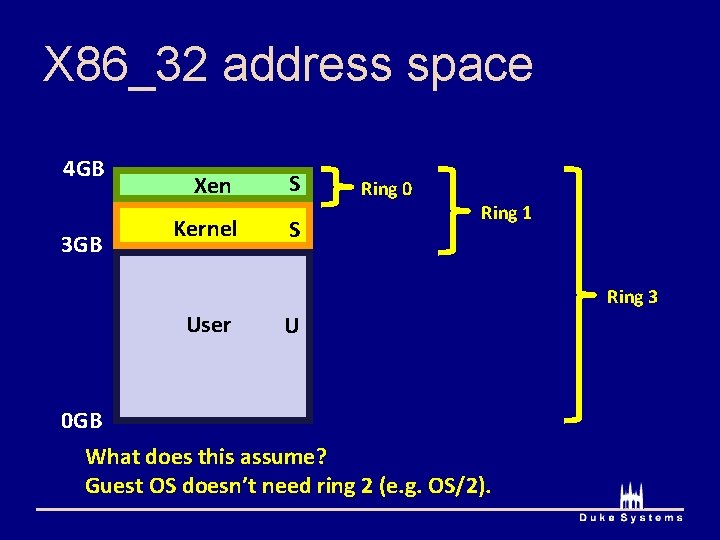
X 86_32 address space 4 GB 3 GB Xen Kernel S S Ring 0 Ring 1 Ring 3 User U 0 GB What does this assume? Guest OS doesn’t need ring 2 (e. g. OS/2).
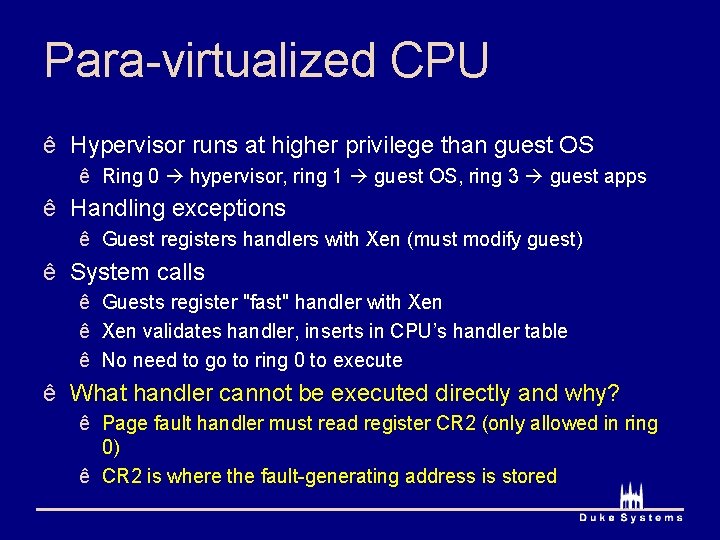
Para-virtualized CPU ê Hypervisor runs at higher privilege than guest OS ê Ring 0 hypervisor, ring 1 guest OS, ring 3 guest apps ê Handling exceptions ê Guest registers handlers with Xen (must modify guest) ê System calls ê Guests register "fast" handler with Xen ê Xen validates handler, inserts in CPU’s handler table ê No need to go to ring 0 to execute ê What handler cannot be executed directly and why? ê Page fault handler must read register CR 2 (only allowed in ring 0) ê CR 2 is where the fault-generating address is stored
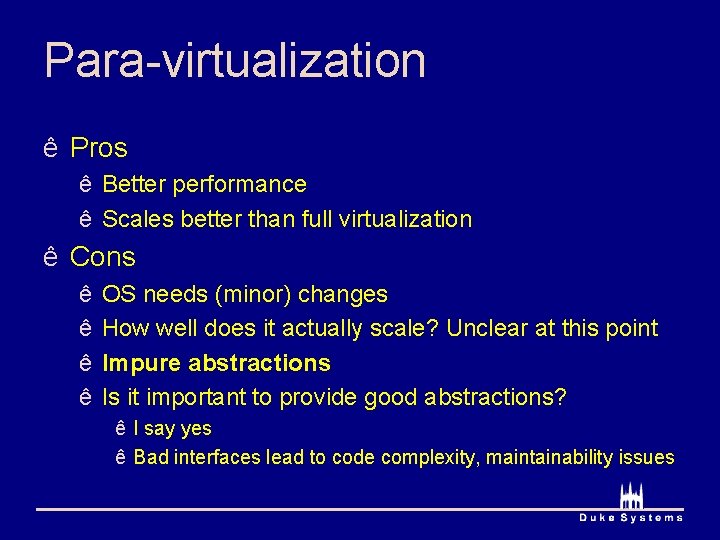
Para-virtualization ê Pros ê Better performance ê Scales better than full virtualization ê Cons ê ê OS needs (minor) changes How well does it actually scale? Unclear at this point Impure abstractions Is it important to provide good abstractions? ê I say yes ê Bad interfaces lead to code complexity, maintainability issues