Covering CWE with Programming Languages and Tools Robert


Covering CWE with Programming Languages and Tools Robert Tice Technical Account Manager
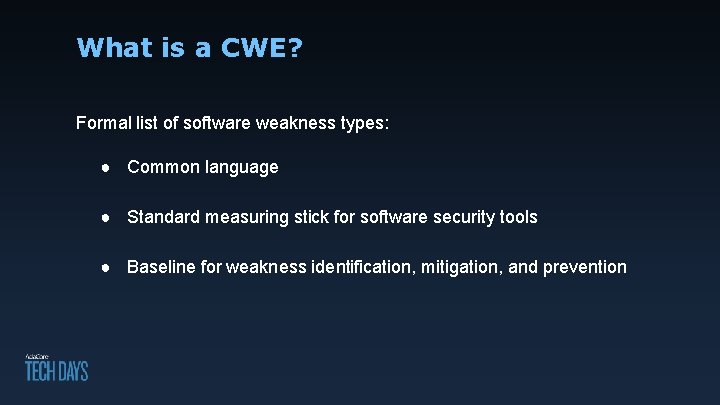
What is a CWE? Formal list of software weakness types: ● Common language ● Standard measuring stick for software security tools ● Baseline for weakness identification, mitigation, and prevention

Prevention vs Mitigation Prevention Entirely absent from application. Mitigation Reduced risk but may exist.
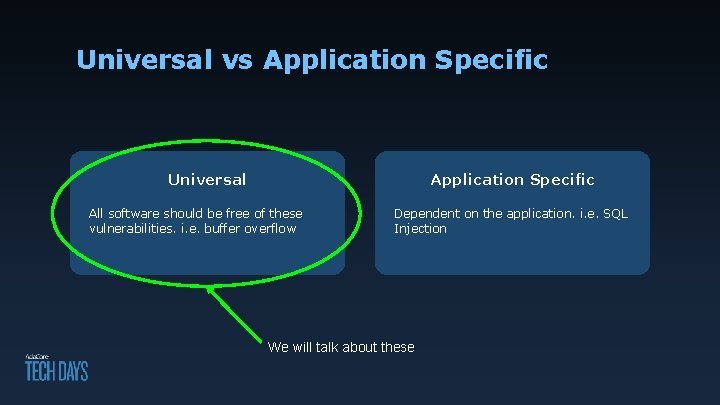
Universal vs Application Specific Universal Application Specific All software should be free of these vulnerabilities. i. e. buffer overflow Dependent on the application. i. e. SQL Injection We will talk about these
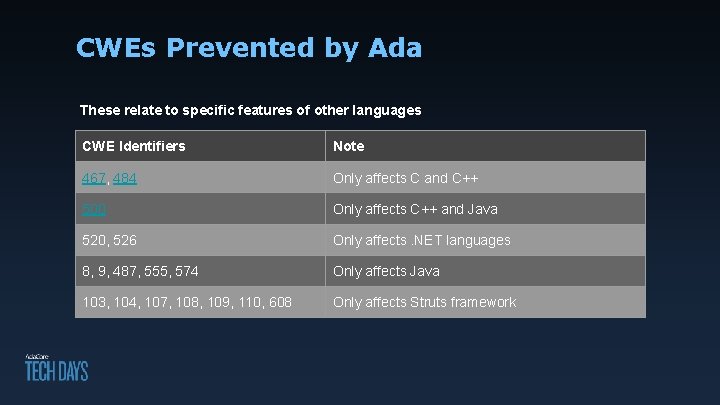
CWEs Prevented by Ada These relate to specific features of other languages CWE Identifiers Note 467, 484 Only affects C and C++ 500 Only affects C++ and Java 520, 526 Only affects. NET languages 8, 9, 487, 555, 574 Only affects Java 103, 104, 107, 108, 109, 110, 608 Only affects Struts framework
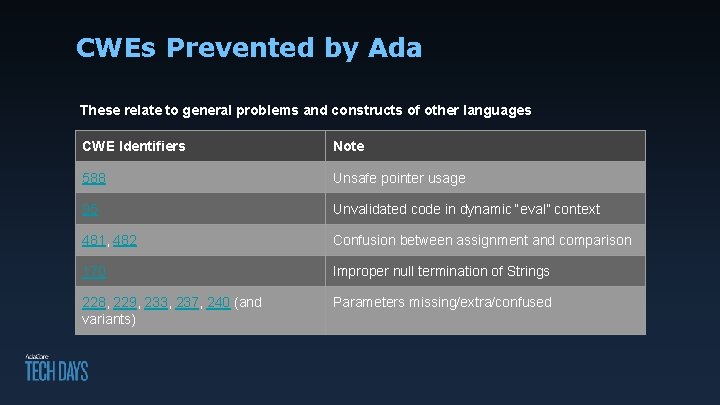
CWEs Prevented by Ada These relate to general problems and constructs of other languages CWE Identifiers Note 588 Unsafe pointer usage 95 Unvalidated code in dynamic “eval” context 481, 482 Confusion between assignment and comparison 170 Improper null termination of Strings 228, 229, 233, 237, 240 (and variants) Parameters missing/extra/confused
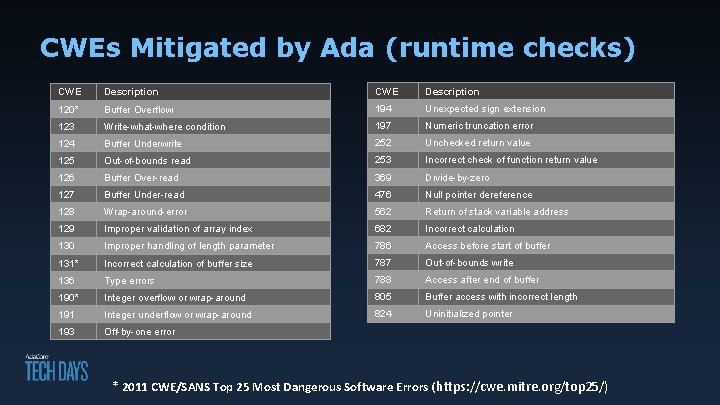
CWEs Mitigated by Ada (runtime checks) CWE Description 120* Buffer Overflow 194 Unexpected sign extension 123 Write-what-where condition 197 Numeric truncation error 124 Buffer Underwrite 252 Unchecked return value 125 Out-of-bounds read 253 Incorrect check of function return value 126 Buffer Over-read 369 Divide-by-zero 127 Buffer Under-read 476 Null pointer dereference 128 Wrap-around-error 562 Return of stack variable address 129 Improper validation of array index 682 Incorrect calculation 130 Improper handling of length parameter 786 Access before start of buffer 131* Incorrect calculation of buffer size 787 Out-of-bounds write 136 Type errors 788 Access after end of buffer 190* Integer overflow or wrap-around 805 Buffer access with incorrect length 191 Integer underflow or wrap-around 824 Uninitialized pointer 193 Off-by-one error * 2011 CWE/SANS Top 25 Most Dangerous Software Errors ( https: //cwe. mitre. org/top 25/)
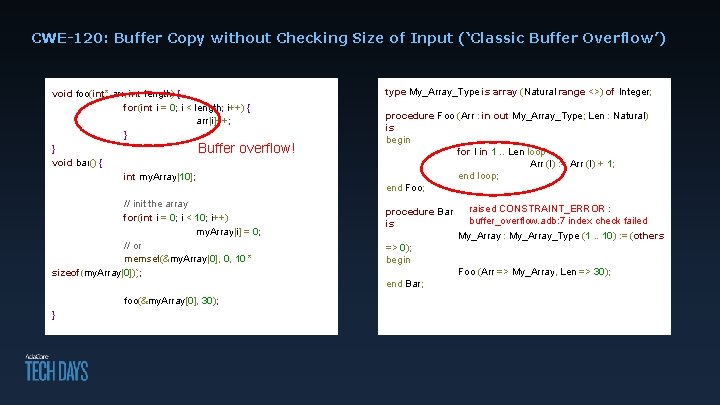
CWE-120: Buffer Copy without Checking Size of Input (‘Classic Buffer Overflow’) void foo(int* arr, int length) { for(int i = 0; i < length; i++) { arr[i]++; } } Buffer overflow! void bar() { int my. Array[10]; // init the array for(int i = 0; i < 10; i++) my. Array[i] = 0; // or memset(&my. Array[0], 0, 10 * sizeof(my. Array[0])); type My_Array_Type array (Natural range <>) of Integer; type My_Array_Type is is array (Natural range <>) of Integer; procedure Foo(Arr My_Array_Type; Len : Natural) procedure Foo : in outout My_Array_Type) is is begin for in. Arr'Range 1. . Len loop for II in loop Arr (I): =: =Arr Arr(I)(I)+ +1; 1; Arr (I) end loop; end Foo; procedure Bar is is => 0); begin end Bar; foo(&my. Array[0], 30); } end Bar; raised CONSTRAINT_ERROR : buffer_overflow. adb: 7 index check failed My_Array : My_Array_Type (1. . 10) : = (others => Foo (Arr => My_Array, Len => 30); -- no accidental length computation -- no accidental buffer overflow because of a typo Foo (Arr => My_Array);
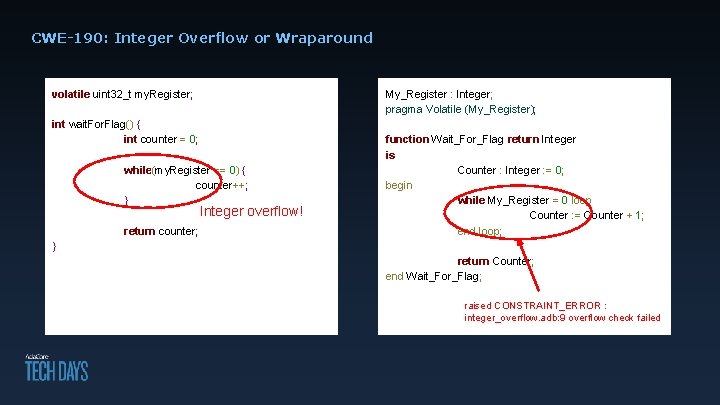
CWE-190: Integer Overflow or Wraparound volatile uint 32_t my. Register; My_Register : Integer; pragma Volatile (My_Register); int wait. For. Flag() { int counter = 0; while(my. Register == 0) { counter++; } Integer overflow! return counter; function Wait_For_Flag return Integer is Counter : Integer : = 0; begin while My_Register = 0 loop Counter : = Counter + 1; end loop; } return Counter; end Wait_For_Flag; raised CONSTRAINT_ERROR : integer_overflow. adb: 9 overflow check failed
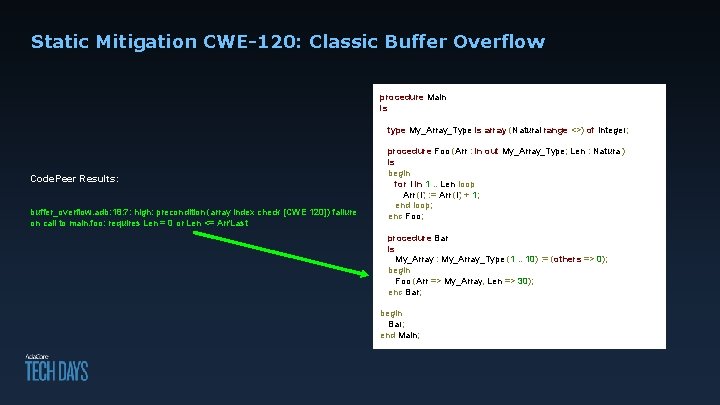
Static Mitigation CWE-120: Classic Buffer Overflow procedure Main is type My_Array_Type is array (Natural range <>) of Integer; Code. Peer Results: buffer_overflow. adb: 18: 7: high: precondition (array index check [CWE 120]) failure on call to main. foo: requires Len = 0 or Len <= Arr'Last procedure Foo (Arr : in out My_Array_Type; Len : Natural) is begin for I in 1. . Len loop Arr (I) : = Arr (I) + 1; end loop; end Foo; procedure Bar is My_Array : My_Array_Type (1. . 10) : = (others => 0); begin Foo (Arr => My_Array, Len => 30); end Bar; begin Bar; end Main;
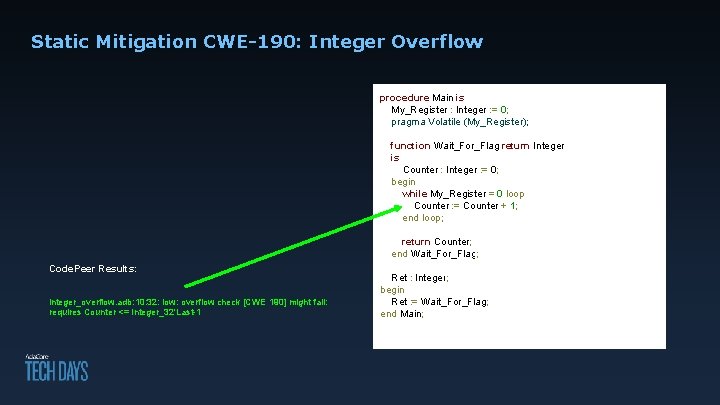
Static Mitigation CWE-190: Integer Overflow procedure Main is My_Register : Integer : = 0; pragma Volatile (My_Register); function Wait_For_Flag return Integer is Counter : Integer : = 0; begin while My_Register = 0 loop Counter : = Counter + 1; end loop; return Counter; end Wait_For_Flag; Code. Peer Results: integer_overflow. adb: 10: 32: low: overflow check [CWE 190] might fail: requires Counter <= Integer_32'Last-1 Ret : Integer; begin Ret : = Wait_For_Flag; end Main;
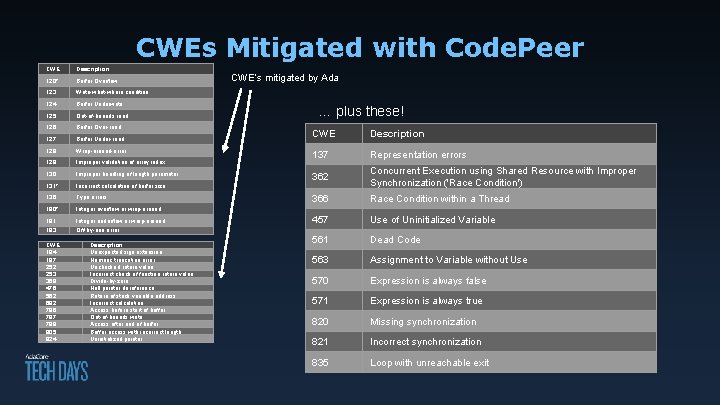
CWEs Mitigated with Code. Peer CWE Description 120* Buffer Overflow 123 Write-what-where condition 124 Buffer Underwrite 125 Out-of-bounds read 126 Buffer Over-read 127 Buffer Under-read 128 Wrap-around-error 129 Improper validation of array index 130 Improper handling of length parameter 131* Incorrect calculation of buffer size 136 Type errors 190* Integer overflow or wrap-around 191 Integer underflow or wrap-around 193 Off-by-one error CWE 194 197 252 253 369 476 562 682 786 787 788 805 824 Description Unexpected sign extension Numeric truncation error Unchecked return value Incorrect check of function return value Divide-by-zero Null pointer dereference Return of stack variable address Incorrect calculation Access before start of buffer Out-of-bounds write Access after end of buffer Buffer access with incorrect length Uninitialized pointer CWE’s mitigated by Ada … plus these! CWE Description 137 Representation errors 362 Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') 366 Race Condition within a Thread 457 Use of Uninitialized Variable 561 Dead Code 563 Assignment to Variable without Use 570 Expression is always false 571 Expression is always true 820 Missing synchronization 821 Incorrect synchronization 835 Loop with unreachable exit
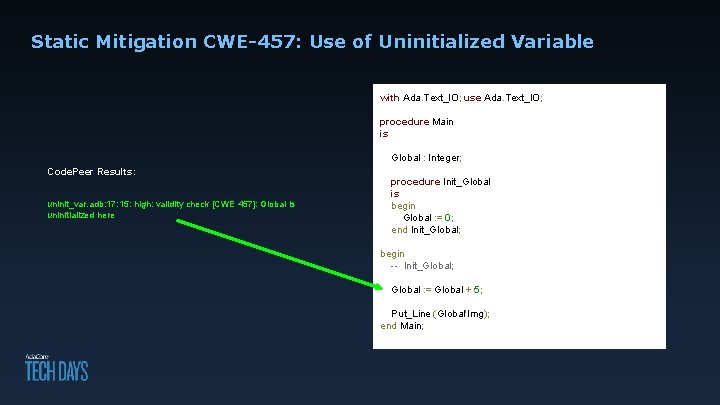
Static Mitigation CWE-457: Use of Uninitialized Variable with Ada. Text_IO; use Ada. Text_IO; procedure Main is Global : Integer; Code. Peer Results: uninit_var. adb: 17: 15: high: validity check [CWE 457]: Global is uninitialized here procedure Init_Global is begin Global : = 0; end Init_Global; begin -- Init_Global; Global : = Global + 5; Put_Line (Global'Img); end Main;
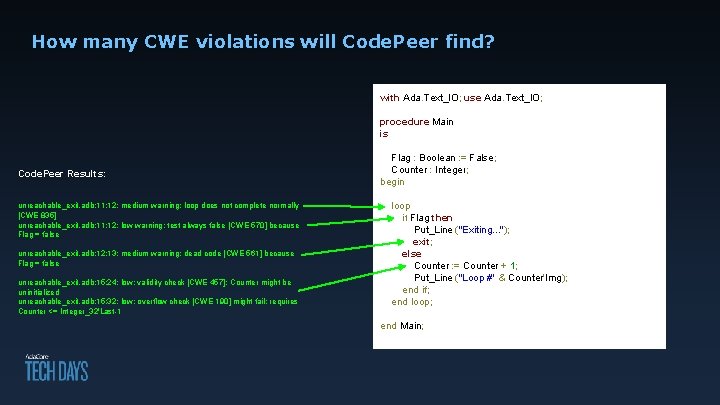
How many CWE violations will Code. Peer find? with Ada. Text_IO; use Ada. Text_IO; procedure Main is Code. Peer Results: unreachable_exit. adb: 11: 12: medium warning: loop does not complete normally [CWE 835] unreachable_exit. adb: 11: 12: low warning: test always false [CWE 570] because Flag = false unreachable_exit. adb: 12: 13: medium warning: dead code [CWE 561] because Flag = false unreachable_exit. adb: 15: 24: low: validity check [CWE 457]: Counter might be uninitialized unreachable_exit. adb: 15: 32: low: overflow check [CWE 190] might fail: requires Counter <= Integer_32'Last-1 Flag : Boolean : = False; Counter : Integer; begin loop if Flag then Put_Line ("Exiting. . . "); exit; else Counter : = Counter + 1; Put_Line ("Loop #" & Counter'Img); end if; end loop; end Main;
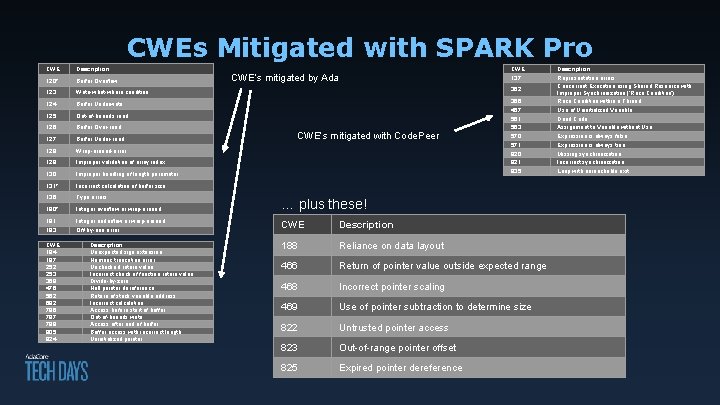
CWEs Mitigated with SPARK Pro CWE Description 120* Buffer Overflow 123 Write-what-where condition 124 Buffer Underwrite 125 Out-of-bounds read 126 Buffer Over-read 127 Buffer Under-read 128 Wrap-around-error 129 Improper validation of array index 130 Improper handling of length parameter 131* Incorrect calculation of buffer size 136 Type errors 190* Integer overflow or wrap-around 191 Integer underflow or wrap-around 193 Off-by-one error CWE 194 197 252 253 369 476 562 682 786 787 788 805 824 Description Unexpected sign extension Numeric truncation error Unchecked return value Incorrect check of function return value Divide-by-zero Null pointer dereference Return of stack variable address Incorrect calculation Access before start of buffer Out-of-bounds write Access after end of buffer Buffer access with incorrect length Uninitialized pointer CWE’s mitigated by Ada CWE 137 362 CWE’s mitigated with Code. Peer 366 457 561 563 570 571 820 821 835 … plus these! CWE Description 188 Reliance on data layout 466 Return of pointer value outside expected range 468 Incorrect pointer scaling 469 Use of pointer subtraction to determine size 822 Untrusted pointer access 823 Out-of-range pointer offset 825 Expired pointer dereference Description Representation errors Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') Race Condition within a Thread Use of Uninitialized Variable Dead Code Assignment to Variable without Use Expression is always false Expression is always true Missing synchronization Incorrect synchronization Loop with unreachable exit
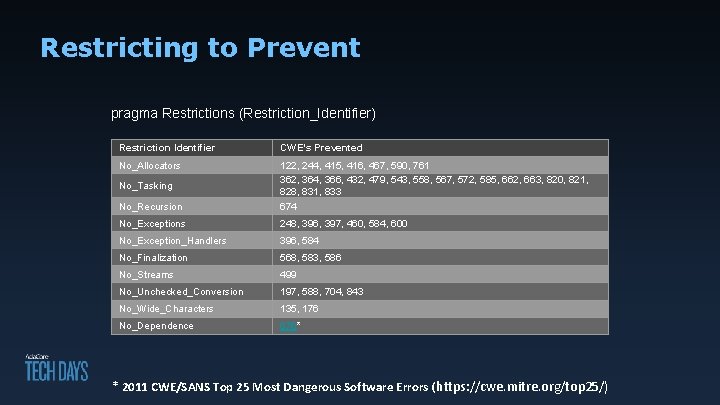
Restricting to Prevent pragma Restrictions (Restriction_Identifier) Restriction Identifier CWE’s Prevented No_Allocators No_Recursion 122, 244, 415, 416, 467, 590, 761 362, 364, 366, 432, 479, 543, 558, 567, 572, 585, 662, 663, 820, 821, 828, 831, 833 674 No_Exceptions 248, 396, 397, 460, 584, 600 No_Exception_Handlers 396, 584 No_Finalization 568, 583, 586 No_Streams 499 No_Unchecked_Conversion 197, 588, 704, 843 No_Wide_Characters 135, 176 No_Dependence 676* No_Tasking * 2011 CWE/SANS Top 25 Most Dangerous Software Errors ( https: //cwe. mitre. org/top 25/)

Reduce risk! Use Ada, SPARK, & Code. Peer Mitre recognized CWE-compatible products!

- Slides: 19