Course Overview January 17 2006 Usable Privacy and
Course Overview January 17, 2006 Usable Privacy and Security • Carnegie Mellon University • Spring 2006 • Cranor/Hong/Reiter • http: //cups. cmu. edu/courses/ups-sp 06/ 1
Outline n Introduction to usable privacy and security n Review syllabus and course policies • Distribute survey n Faculty research overview n Introduce students Usable Privacy and Security • Carnegie Mellon University • Spring 2006 • Cranor/Hong/Reiter • http: //cups. cmu. edu/courses/ups-sp 06/ 2
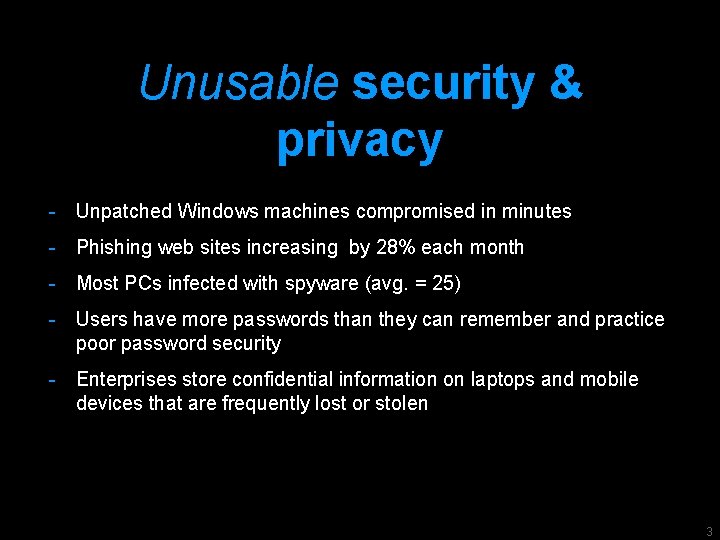
Unusable security & privacy - Unpatched Windows machines compromised in minutes - Phishing web sites increasing by 28% each month - Most PCs infected with spyware (avg. = 25) - Users have more passwords than they can remember and practice poor password security - Enterprises store confidential information on laptops and mobile devices that are frequently lost or stolen 3
Grand Challenge “Give end-users security controls they can understand privacy they can control for the dynamic, pervasive computing environments of the future. ” - Computing Research Association 2003 4
Just work
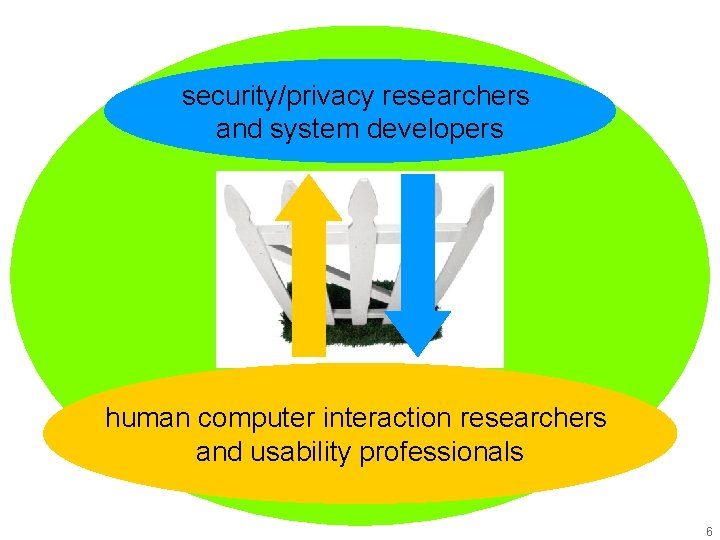
security/privacy researchers and system developers human computer interaction researchers and usability professionals 6
r a d n e al c r u o y 6 k 0 r 20 Ma S P U U O S M C r fo at 6 1 4 1 y l Ju Symposium On Usable Privacy and Security (SOUPS) July 6 -8, 2005 Pittsburgh, PA USA http: //cups. cmu. edu/soups/ 7
A preview of some topics we’ll cover in this course 1. Problems and approaches 2. Passwords 3. Symbols & metaphors 4. Rethinking cookies 5. Making Web privacy visible 8
Problems and approaches 1.
How do you stay safe online? 10

Experts recommend…
POP! 12

After installing all that security and privacy software 13
Do you have any time left to get any work done? 14
Secondary tasks
Approaches to usable security - Make it “just work” - Invisible security - Make security/privacy understandable - Make it visible - Make it intuitive - Use metaphors that users can relate to - Train the user 16
Make decisions - Developers should not expect users to make decisions they themselves can’t make 17
Present choices, not dilemmas - Chris Nodder (in charge of user experience for XP SP 2)
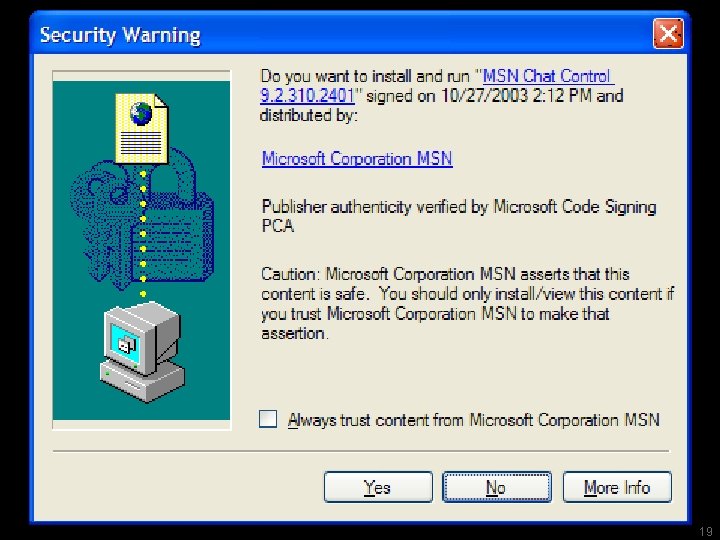
19
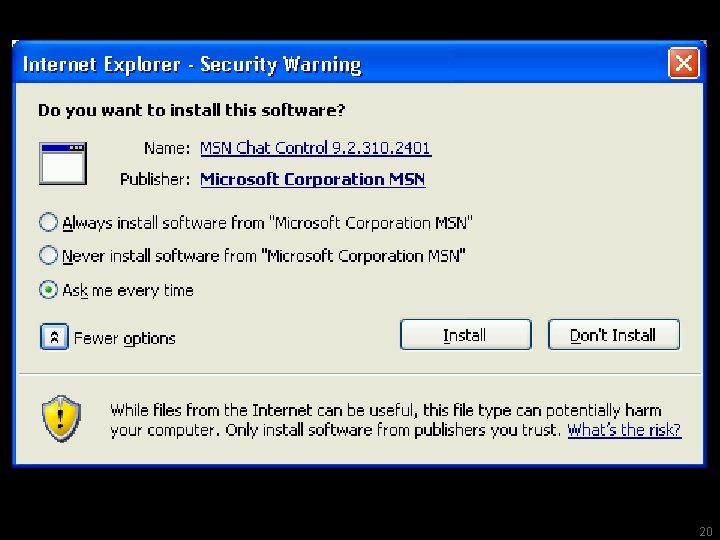
20
Passwords 2.
Typical advice - Pick a hard to guess password - Don’t use it anywhere else - Change it often - Don’t write it down 22
What do users do when every web site wants a password?
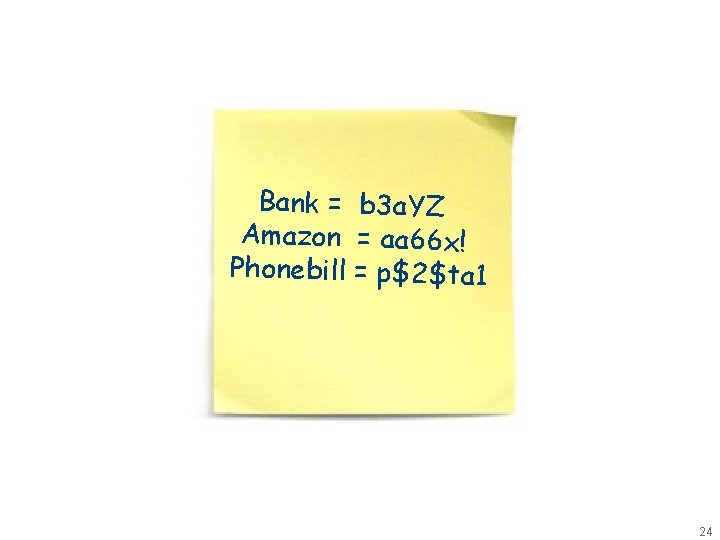
Bank = b 3 a. YZ Amazon = aa 66 x! Phonebill = p$2$ta 1 24
25
Symbols & Metaphors 3.
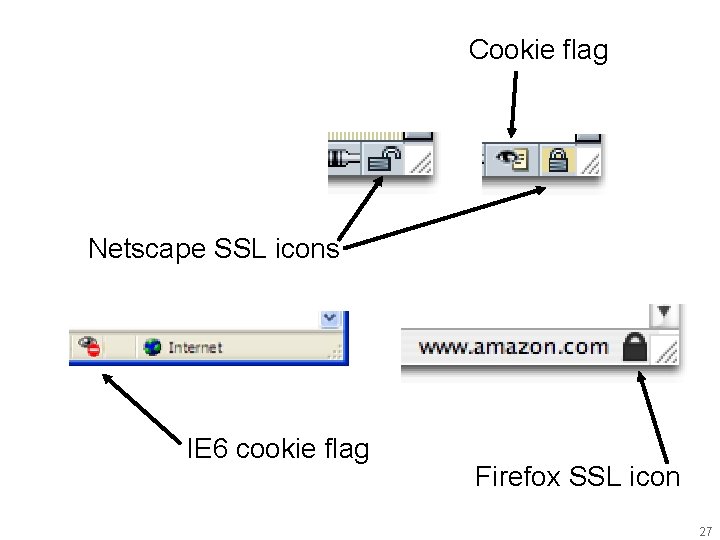
Cookie flag Netscape SSL icons IE 6 cookie flag Firefox SSL icon 27
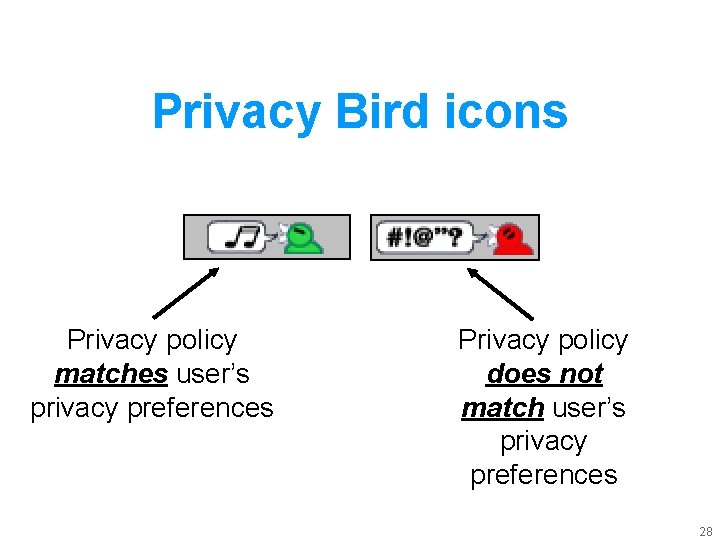
Privacy Bird icons Privacy policy matches user’s privacy preferences Privacy policy does not match user’s privacy preferences 28
Rethinking cookies 4.
30

31

Making Web privacy visible 5.
Web site privacy policies - Many posted - Few read 33
What if your browser could read privacy policies for you?
Platform for Privacy Preferences (P 3 P) - 2002 W 3 C Recommendation - XML format for Web privacy policies - Protocol enables clients to locate and fetch policies from servers 35
Privacy Bird - P 3 P user agent - Free download http: //privacybird. com/ - Compares user preferences with P 3 P policies 36
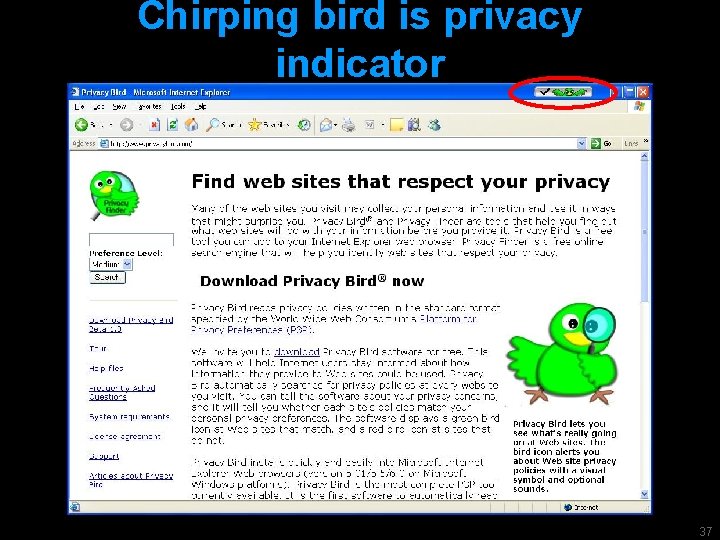
Chirping bird is privacy indicator 37
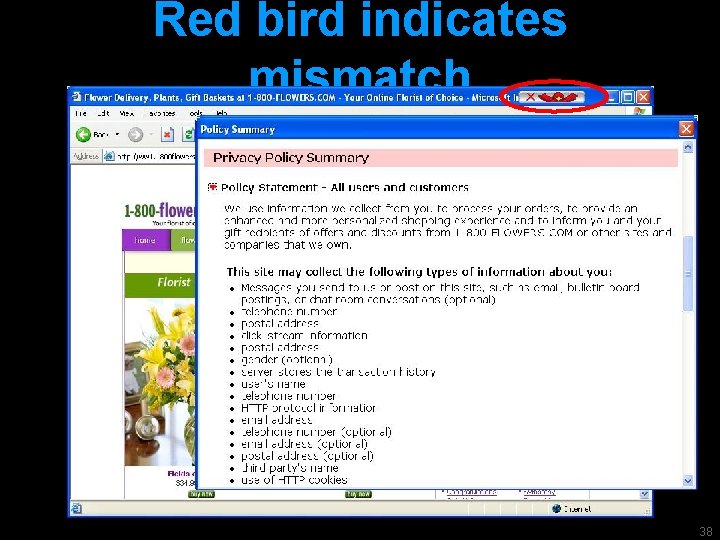
Red bird indicates mismatch 38
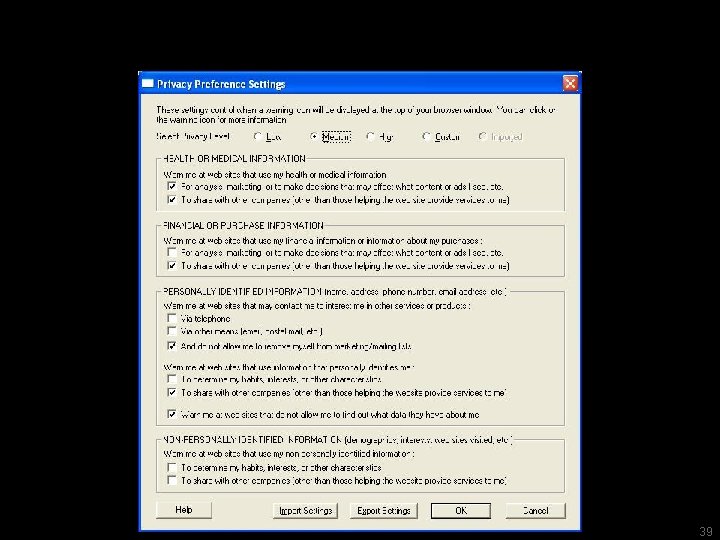
Privacy settings 39
Example: Sending flowers
41
42
Wireless privacy - Many users unaware that communications over wireless computer networks are not private 43
Wall of sheep
Defcon 2001 Photo credit: Kyoorius @ techfreakz. org http: //www. techfreakz. org/defcon 10/? slide=38 45
Defcon 2004 Photo credit: http: //www. timekiller. org/gallery/Defcon. XII/photo 0003 46
Peripheral display - Help users form more accurate expectations of privacy - Without making the problem worse 47
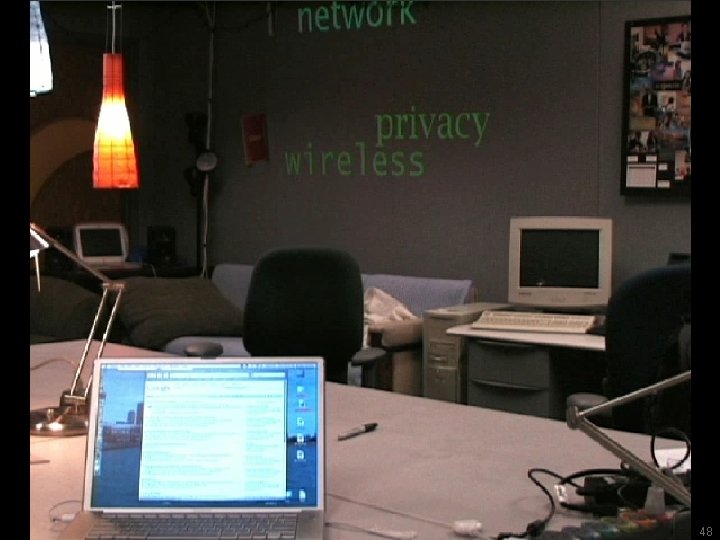
48
Experimental trial - 11 subjects in student workspace - Data collected by survey and traffic analysis - Did they refine their expectations of privacy? 49
Results - No change in behavior - Peripheral display raised privacy awareness in student workspace - But they didn’t really get it 50
Privacy awareness increased “I feel like my information /activity / privacy are not being protected …. seems like someone can monitor or get my information from my computer, or even publish them. ” 51
![But only while the display was on “Now that words [projected on the wall] But only while the display was on “Now that words [projected on the wall]](http://slidetodoc.com/presentation_image_h2/0e2a3a7f6c078f7890715ea00c90e2df/image-52.jpg)
But only while the display was on “Now that words [projected on the wall] are gone, I'll go back to the same. ” 52
Questions to ask about a security or privacy cue - Do users notice it? - Do they know what it means? - Do they know what they are supposed to do when they see it? - Will they actually do it? - Will they keep doing it? 53
Syllabus n http: //cups. cmu. edu/courses/ups-sp 06/ n Homework (25%) n Lecture (25%) n Project (50%) n Textbook and readings n Schedule Usable Privacy and Security • Carnegie Mellon University • Spring 2006 • Cranor/Hong/Reiter • http: //cups. cmu. edu/courses/ups-sp 06/ 54
Survey n Please fill out course survey and bring it with you to class on Thursday Usable Privacy and Security • Carnegie Mellon University • Spring 2006 • Cranor/Hong/Reiter • http: //cups. cmu. edu/courses/ups-sp 06/ 55

Faculty research overview Lorrie Cranor Michael Reiter Jason Hong Usable Privacy and Security • Carnegie Mellon University • Spring 2006 • Cranor/Hong/Reiter • http: //cups. cmu. edu/courses/ups-sp 06/ 56
Student introductions n Introduce yourself to your neighbor and tell them your background. Tell them why you’re taking the course and what you want to get out of the course n Form a group of ~4 and repeat n Form a group of ~8 and repeat n Pick someone to stand up in front of the class, introduce your group members, and summarize the reasons people in your group are taking the course and what you want to get out of the course Usable Privacy and Security • Carnegie Mellon University • Spring 2006 • Cranor/Hong/Reiter • http: //cups. cmu. edu/courses/ups-sp 06/ 57
- Slides: 57