Counter Braids A Novel Counter Architecture for PerFlow
Counter Braids: A Novel Counter Architecture for Per-Flow Measurement Author: Yi Lu, Andrea Montanari, Balaji Prabhakar, Sarang Dharmapurikar, Abdul Kabbani Publisher: SIGMETRICS’ 08 Presenter: Yun-Yan Chang Date: 2011/04/27 1
Outline � Introduction � Counter Braids ◦ Random mapping ◦ Encoding (update algorithm) ◦ Message passing decoder (reconstruction) � Performance 2
Introduction � Present a counter architecture called Counter Braids (CB). ◦ Goals: To solve main problems �Compacting counter space �Flow-to-counter association rule ◦ Solution methodology �Use a small number of hash functions �Braid the counters �Reconstruct by a linear-complexity message-passing algorithm 3
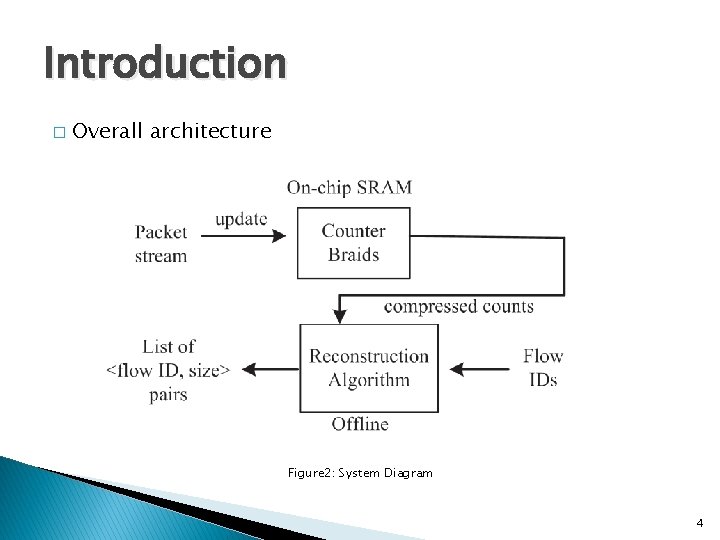
Introduction � Overall architecture Figure 2: System Diagram 4
Counter Braids (CB) � Hierarchy architecture. � Minimize counter space with incremental compression. � Solve flow-to-counter association problem by random graphs. � Decoding algorithm reconstructs information from compressed counts with zero error. 5
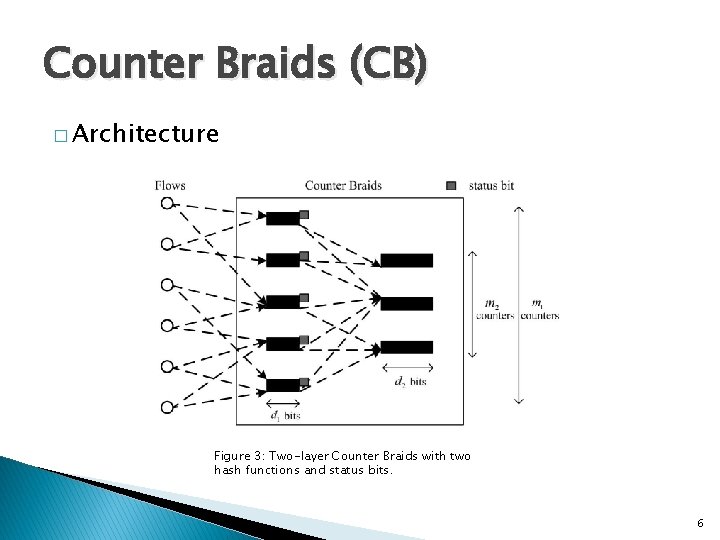
Counter Braids (CB) � Architecture Figure 3: Two-layer Counter Braids with two hash functions and status bits. 6
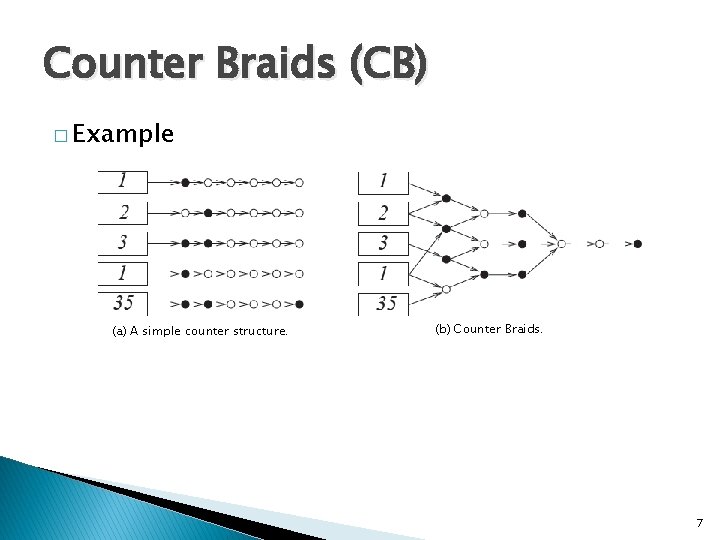
Counter Braids (CB) � Example (a) A simple counter structure. (b) Counter Braids. 7
Random (Hash) mappings � To solve flow-to-counter association. � Use the same random mapping: ◦ Between flows and the 1 st-layer counters. ◦ Between two consecutive layers of counters. ◦ For each flow ID, apply k pseudo-random hash functions with range {0, … , ml-1}. �ml: number of counters in layer l 8
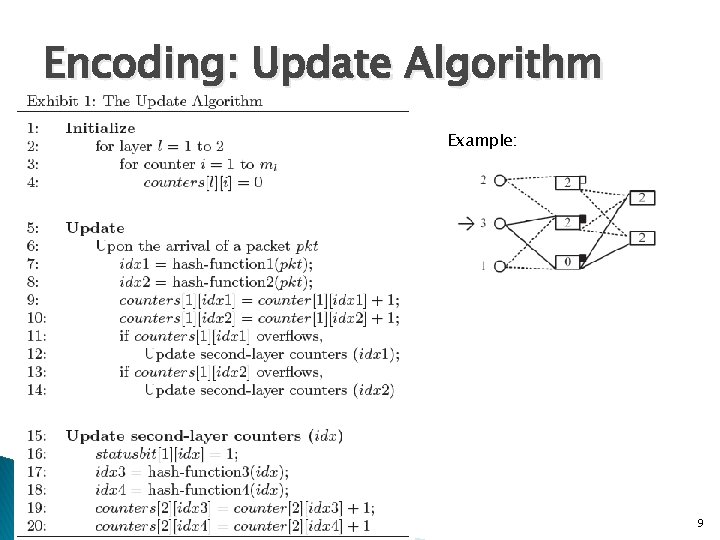
Encoding: Update Algorithm Example: 9
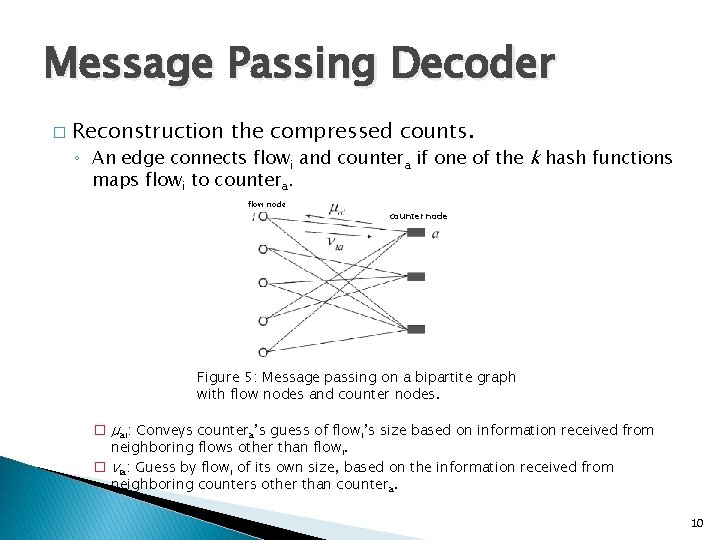
Message Passing Decoder � Reconstruction the compressed counts. ◦ An edge connects flowi and countera if one of the k hash functions maps flowi to countera. flow node counter node Figure 5: Message passing on a bipartite graph with flow nodes and counter nodes. � μai: Conveys countera’s guess of flowi’s size based on information received from neighboring flows other than flowi. � νia: Guess by flowi of its own size, based on the information received from neighboring counters other than countera. 10
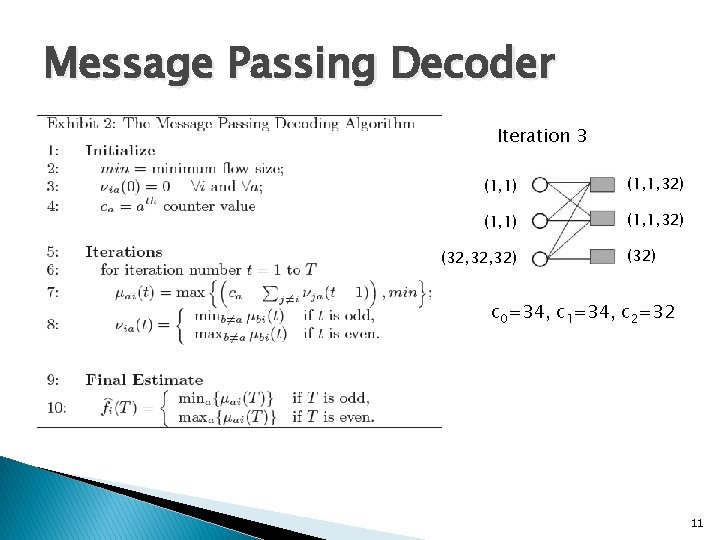
Message Passing Decoder Iteration 3 1 2 Initialize (0, 0) (34, 34) (1, 1) (34, 34, 34) (1, 1, 32) (1, 1, 1) (0, 0, 0) (32, 32) (32, 34) (32, 1) (32) c 0=34, c 1=34, c 2=32 11
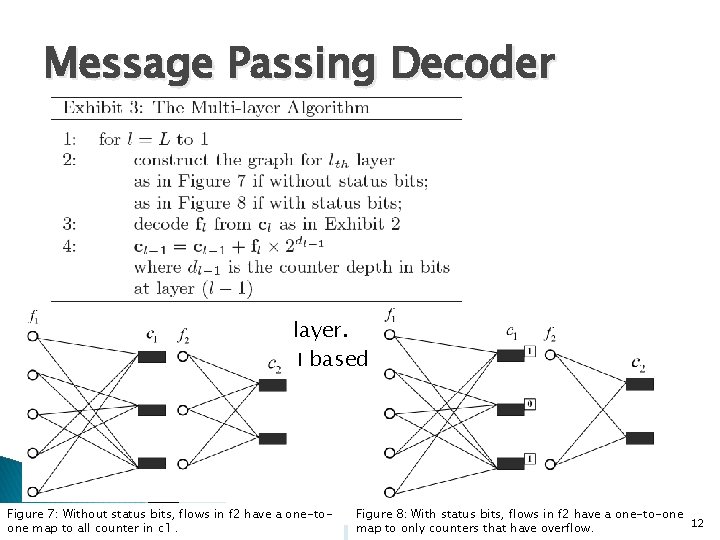
Message Passing Decoder ◦ Start from topmost layer. ◦ Construct fl at layer l based on the counters at layer l-1. Figure 7: Without status bits, flows in f 2 have a one-toone map to all counter in c 1. Figure 8: With status bits, flows in f 2 have a one-to-one 12 map to only counters that have overflow.
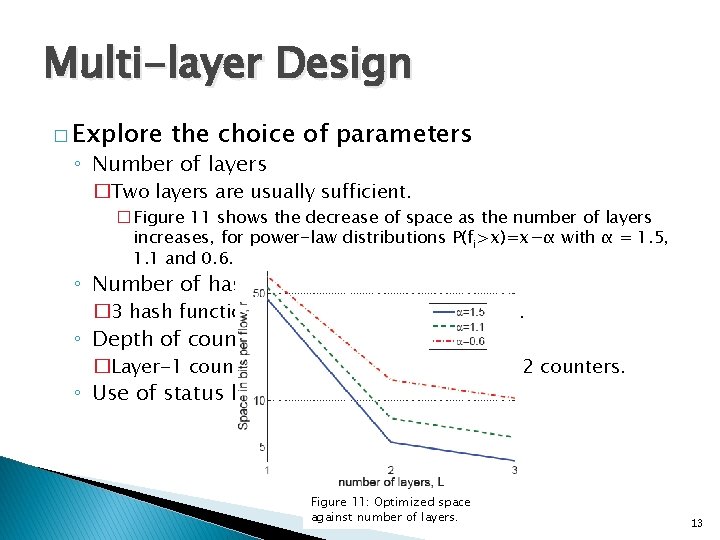
Multi-layer Design � Explore the choice of parameters ◦ Number of layers �Two layers are usually sufficient. �Figure 11 shows the decrease of space as the number of layers increases, for power-law distributions P(fi>x)=x−α with α = 1. 5, 1. 1 and 0. 6. ◦ Number of hash function in each layer � 3 hash functions is optimal for two-layer CB. ◦ Depth of counters in each layer �Layer-1 counter depth and number of layer-2 counters. ◦ Use of status bits. Figure 11: Optimized space against number of layers. 13
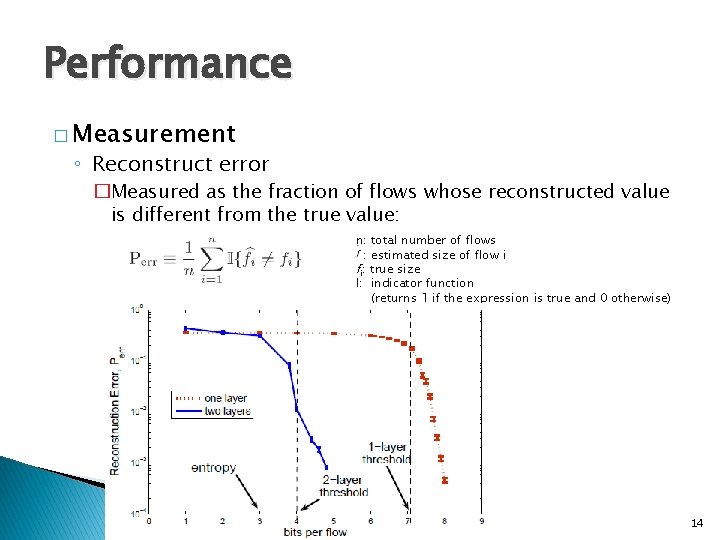
Performance � Measurement ◦ Reconstruct error �Measured as the fraction of flows whose reconstructed value is different from the true value: n: total number of flows : estimated size of flow i fi: true size I: indicator function (returns 1 if the expression is true and 0 otherwise) 14
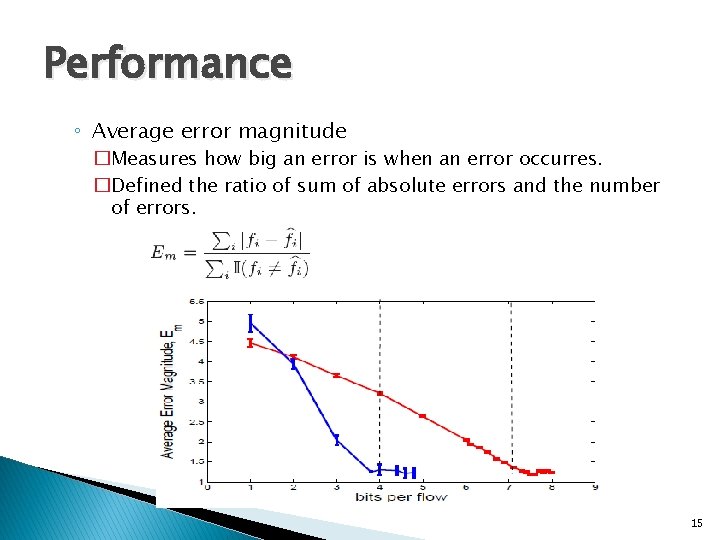
Performance ◦ Average error magnitude �Measures how big an error is when an error occurres. �Defined the ratio of sum of absolute errors and the number of errors. 15
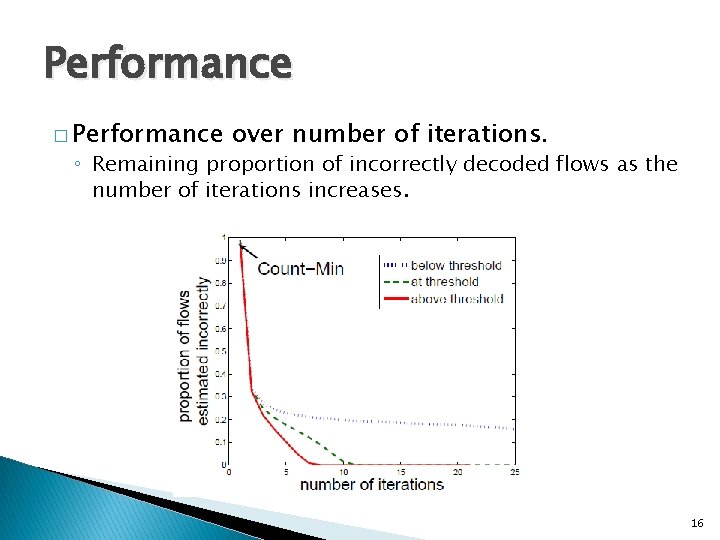
Performance � Performance over number of iterations. ◦ Remaining proportion of incorrectly decoded flows as the number of iterations increases. 16
Future work � Save counter space to combine the counts collected at different routers. � “lossy compression” problem ◦ Recover if the amount space is less than the requirement 17
- Slides: 17