Core Scope Graph Mining Using kCore Analysis Patterns
![Research Questions • Question 1 [Patterns] What are common patterns regarding k-cores occurring across Research Questions • Question 1 [Patterns] What are common patterns regarding k-cores occurring across](https://slidetodoc.com/presentation_image/29c0095047ad5342c5e794f889f32076/image-3.jpg)
![Mirror Pattern: Question: What is the key factor determining the coreness of nodes? [Reminder] Mirror Pattern: Question: What is the key factor determining the coreness of nodes? [Reminder]](https://slidetodoc.com/presentation_image/29c0095047ad5342c5e794f889f32076/image-7.jpg)
![Core-Triangle Pattern: Question: What is the key factor determining degeneracy? [Reminder] Degeneracy of a Core-Triangle Pattern: Question: What is the key factor determining degeneracy? [Reminder] Degeneracy of a](https://slidetodoc.com/presentation_image/29c0095047ad5342c5e794f889f32076/image-21.jpg)
- Slides: 44
Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms Kijung Shin Tina Eliassi-Rad Christos Faloutsos Carnegie Mellon University Northeastern University Carnegie Mellon University
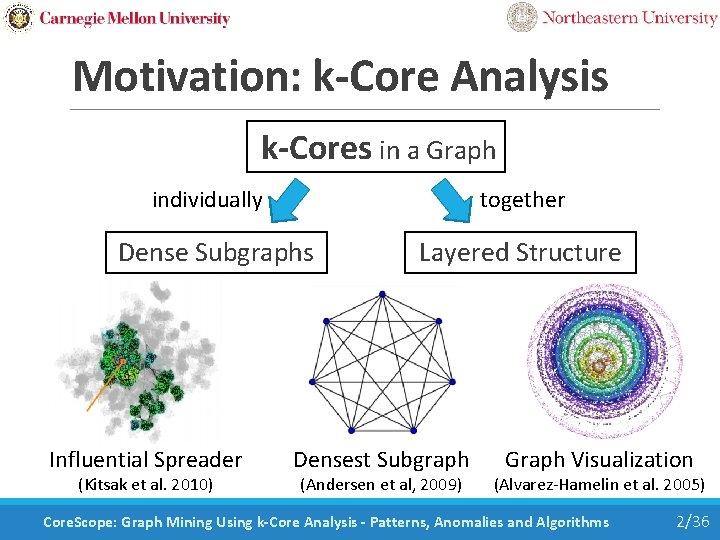
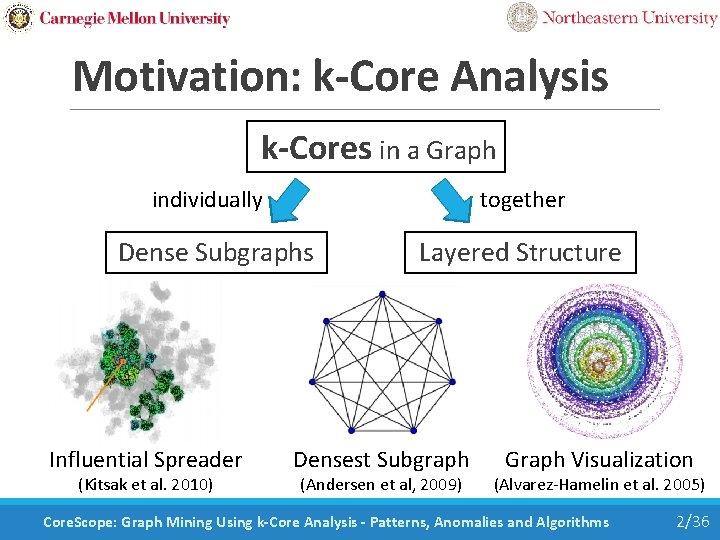
Motivation: k-Core Analysis k-Cores in a Graph individually together Dense Subgraphs Influential Spreader (Kitsak et al. 2010) Layered Structure Densest Subgraph (Andersen et al, 2009) Graph Visualization (Alvarez-Hamelin et al. 2005) Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 2/36
![Research Questions Question 1 Patterns What are common patterns regarding kcores occurring across Research Questions • Question 1 [Patterns] What are common patterns regarding k-cores occurring across](https://slidetodoc.com/presentation_image/29c0095047ad5342c5e794f889f32076/image-3.jpg)
Research Questions • Question 1 [Patterns] What are common patterns regarding k-cores occurring across graphs in diverse domains? (e. g. , ) • Question 2 [Anomalies] What are anomalies deviating from these patterns? • Question 3 [Algorithms] How can these patterns and anomalies be used for designing algorithms? Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 3/36
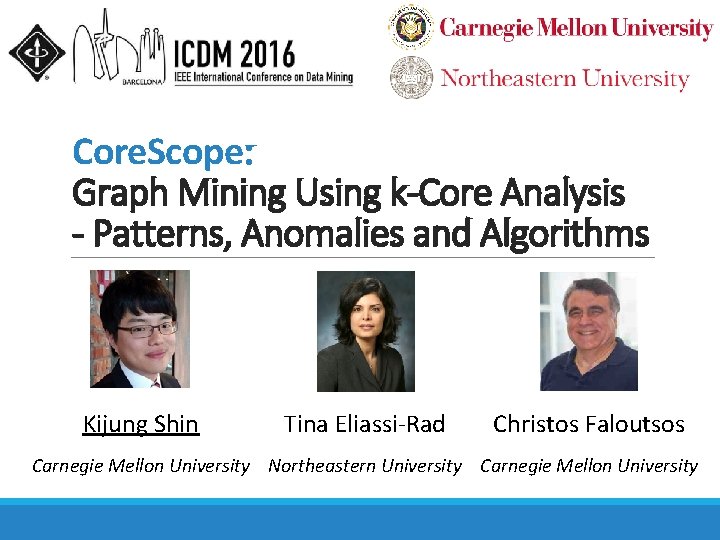
Road Map • Introduction • Definition of K-Cores << • Pattern 1: “Mirror Pattern” • Pattern 2: “Core-Triangle Pattern” • Pattern 3: “Structural-Core Pattern” • Conclusion Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 4/36
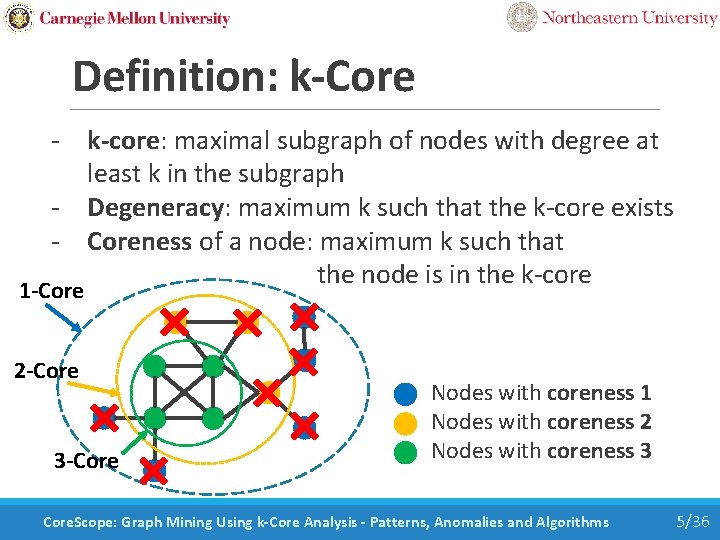
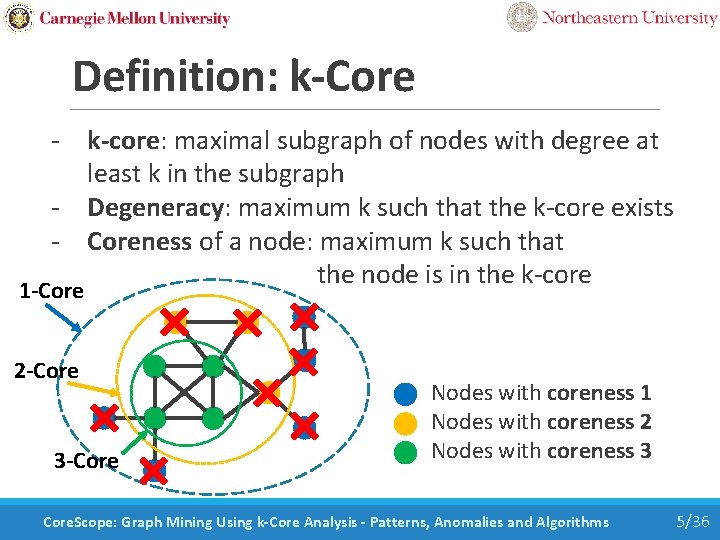
Definition: k-Core - k-core: maximal subgraph of nodes with degree at least k in the subgraph - Degeneracy: maximum k such that the k-core exists - Coreness of a node: maximum k such that the node is in the k-core 1 -Core 2 -Core 3 -Core Nodes with coreness 1 Nodes with coreness 2 Nodes with coreness 3 Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 5/36
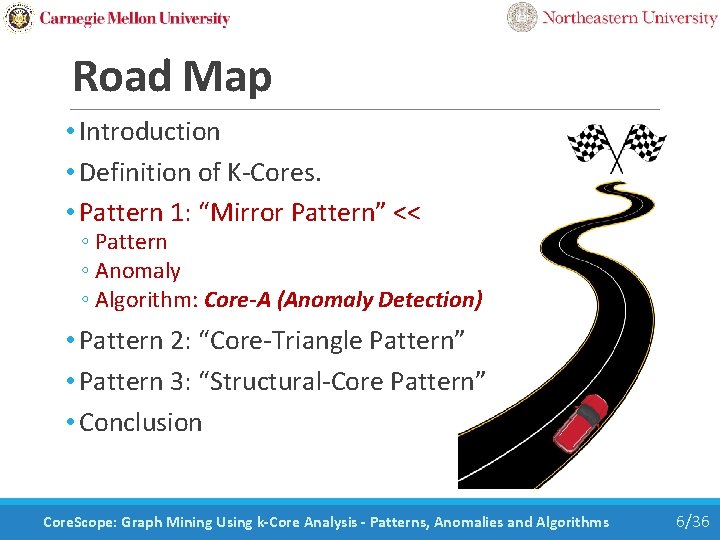
Road Map • Introduction • Definition of K-Cores. • Pattern 1: “Mirror Pattern” << ◦ Pattern ◦ Anomaly ◦ Algorithm: Core-A (Anomaly Detection) • Pattern 2: “Core-Triangle Pattern” • Pattern 3: “Structural-Core Pattern” • Conclusion Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 6/36
![Mirror Pattern Question What is the key factor determining the coreness of nodes Reminder Mirror Pattern: Question: What is the key factor determining the coreness of nodes? [Reminder]](https://slidetodoc.com/presentation_image/29c0095047ad5342c5e794f889f32076/image-7.jpg)
Mirror Pattern: Question: What is the key factor determining the coreness of nodes? [Reminder] Coreness of a node is the highest k value such that the node is in the k-core Coreness Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 7/36
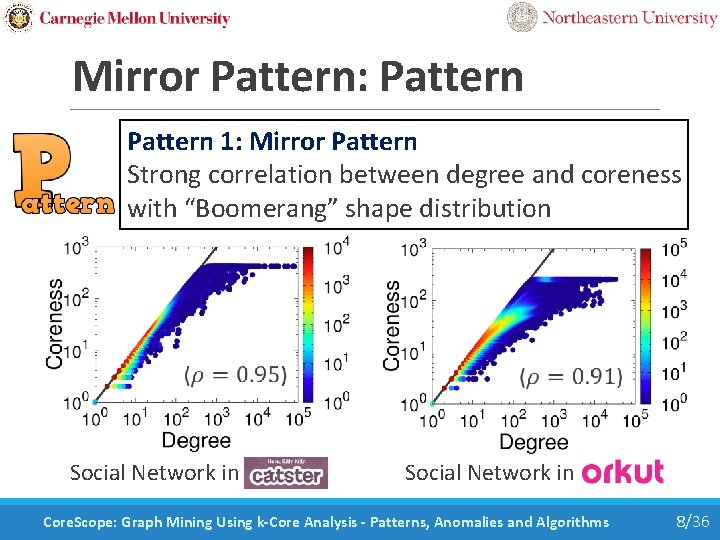
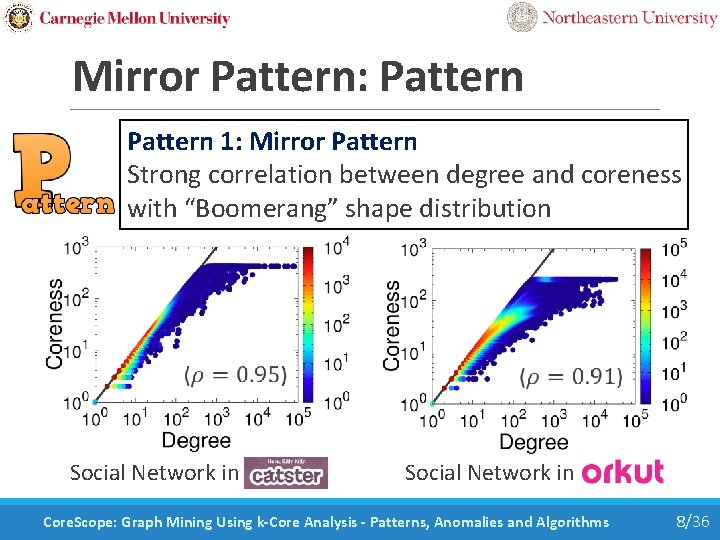
Mirror Pattern: Pattern 1: Mirror Pattern Strong correlation between degree and coreness with “Boomerang” shape distribution Social Network in Catster Social Network in Orkut Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 8/36
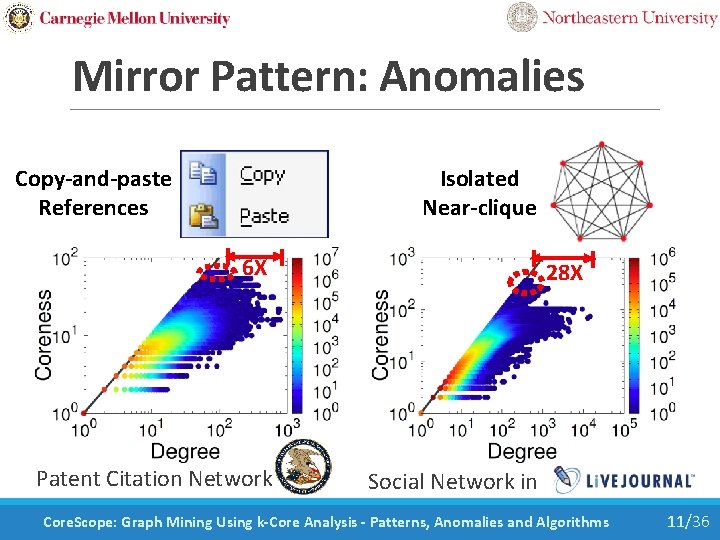
Mirror Pattern: Anomalies Question: Do all nodes follow this pattern? Answer: No! Nodes deviating from the pattern are interesting anomalies. Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 9/36
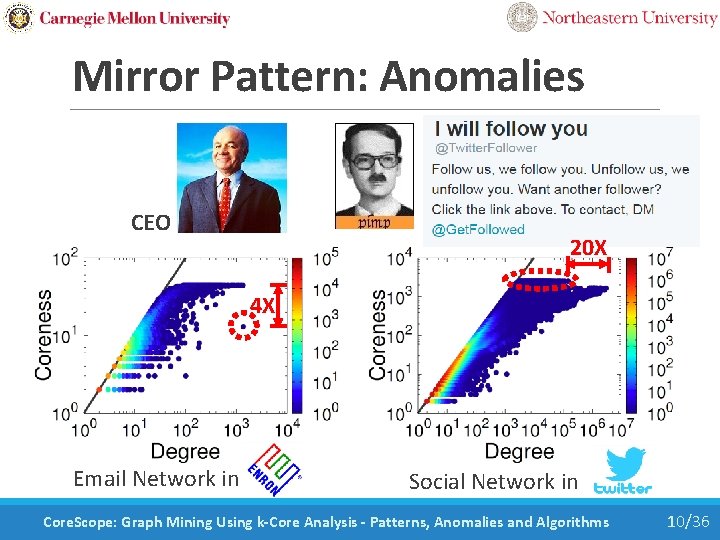
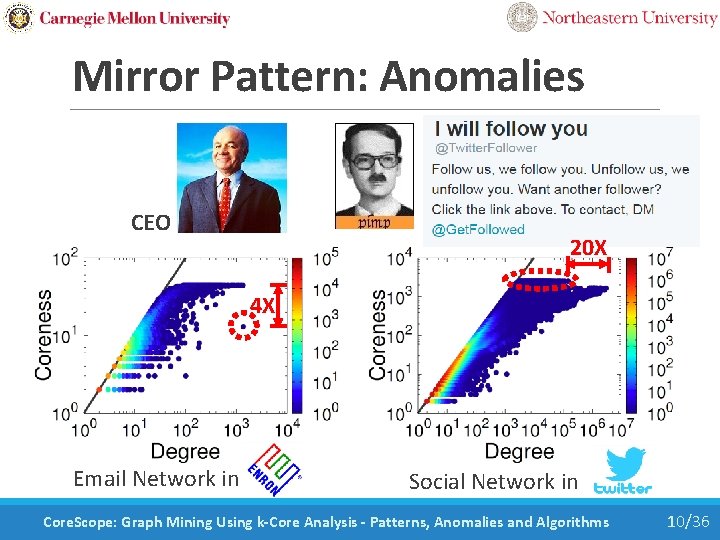
Mirror Pattern: Anomalies CEO 20 X 4 X Email Network in Social Network in Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 10/36
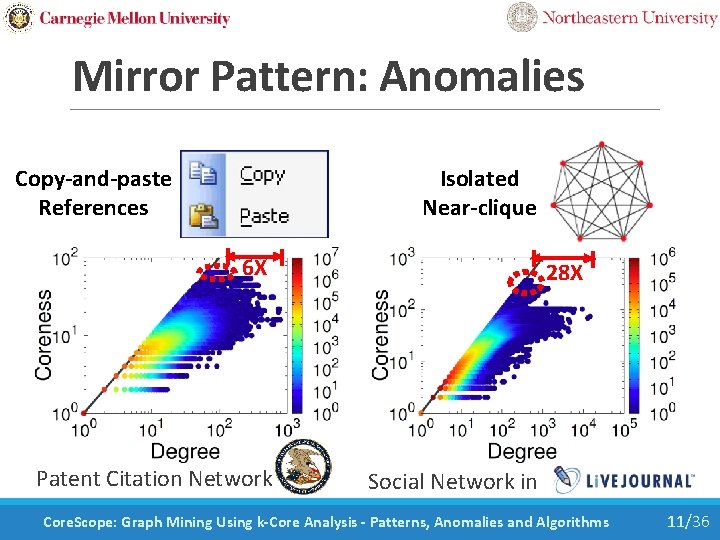
Mirror Pattern: Anomalies Isolated Near-clique Copy-and-paste References 6 X Patent Citation Network 28 X Social Network in Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 11/36
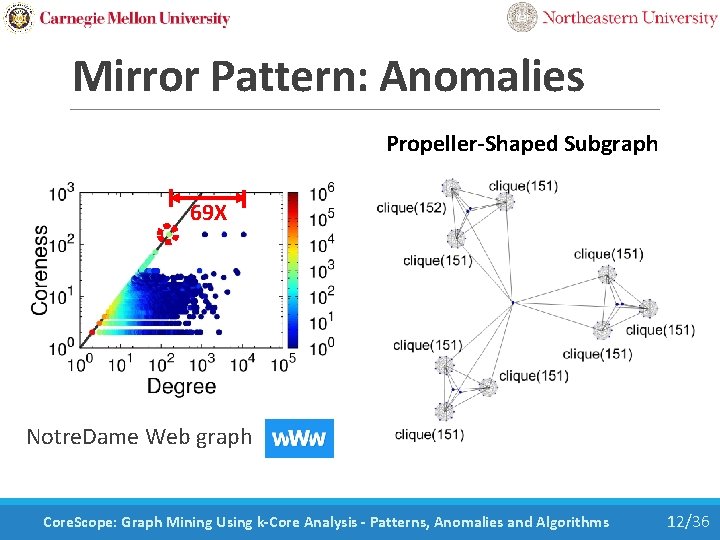
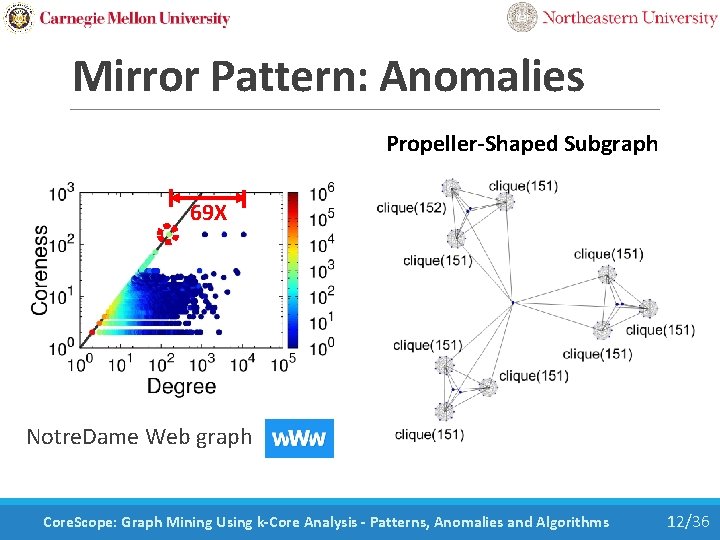
Mirror Pattern: Anomalies Propeller-Shaped Subgraph 69 X Notre. Dame Web graph Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 12/36
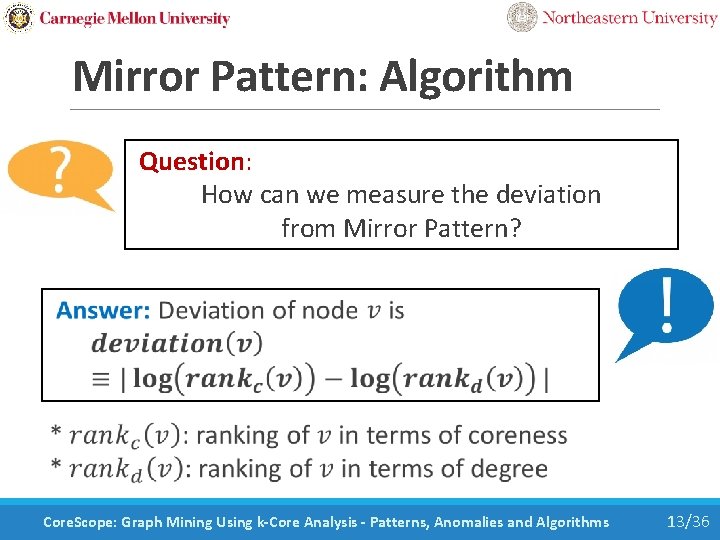
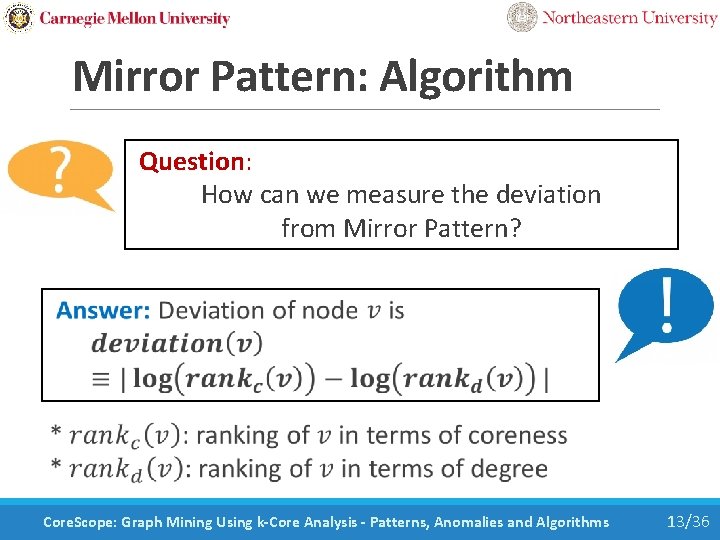
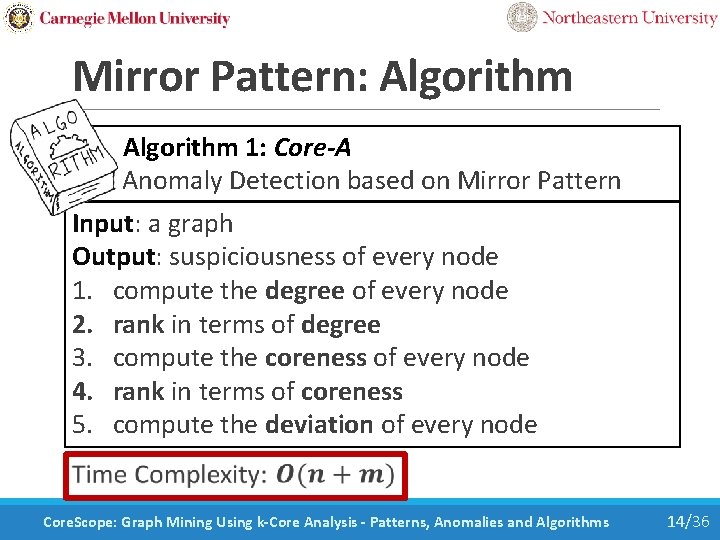
Mirror Pattern: Algorithm Question: How can we measure the deviation from Mirror Pattern? Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 13/36
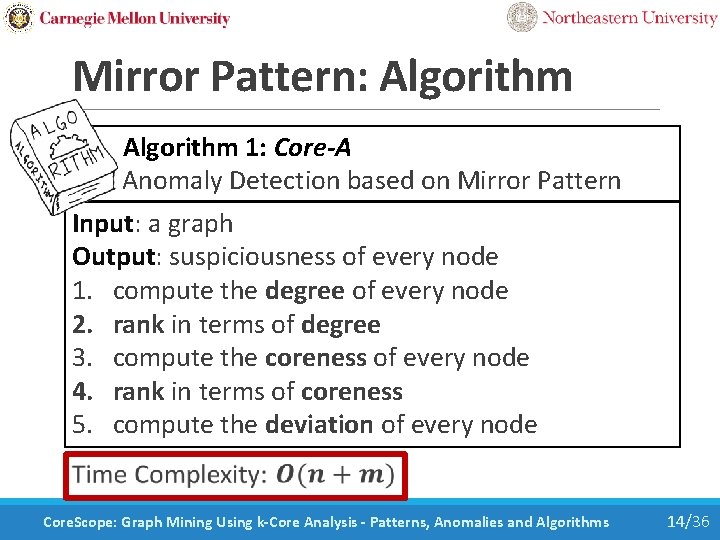
Mirror Pattern: Algorithm 1: Core-A Anomaly Detection based on Mirror Pattern Input: a graph Output: suspiciousness of every node 1. compute the degree of every node 2. rank in terms of degree 3. compute the coreness of every node 4. rank in terms of coreness 5. compute the deviation of every node Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 14/36
Mirror Pattern: Experiment Question: Does Core-A detect different anomalies with other dense-subgraph based algorithms? Answer: Yes, they are complementary Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 15/36
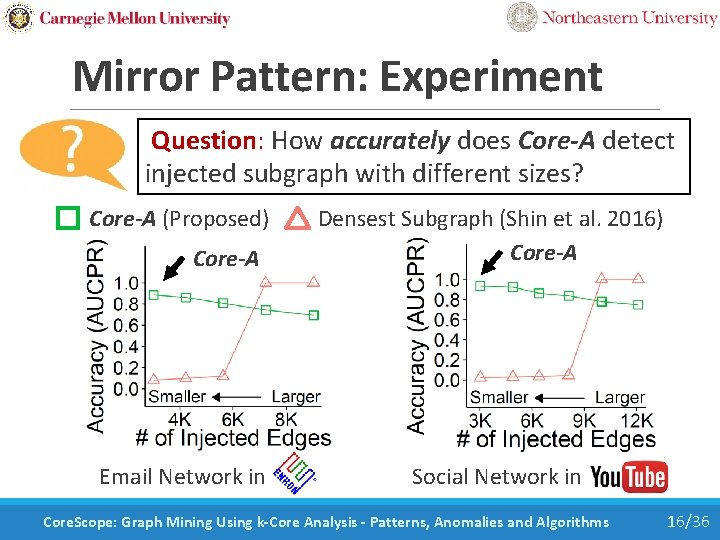
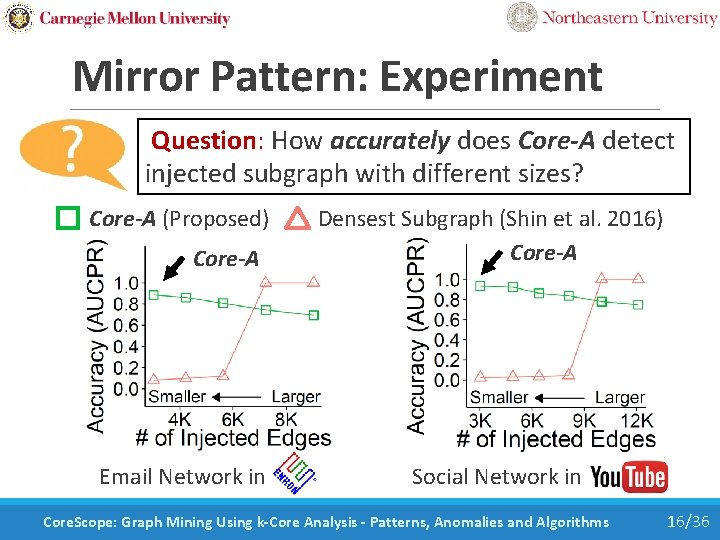
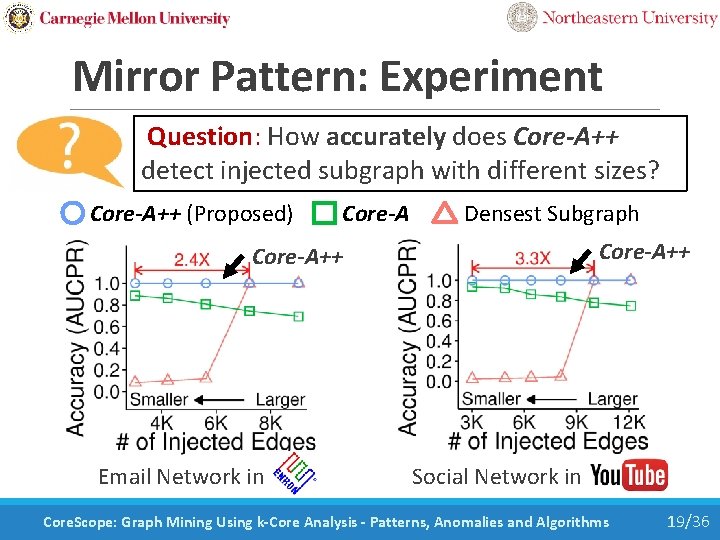
Mirror Pattern: Experiment Question: How accurately does Core-A detect injected subgraph with different sizes? Core-A (Proposed) Densest Subgraph (Shin et al. 2016) Core-A Email Network in Social Network in Youtube Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 16/36
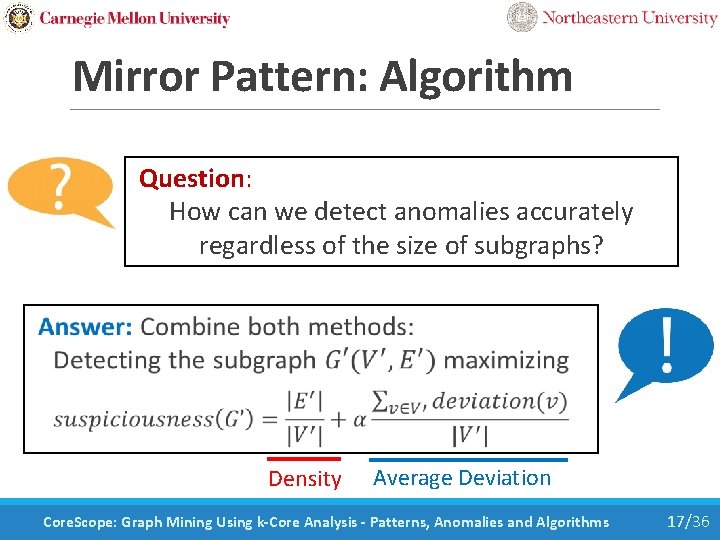
Mirror Pattern: Algorithm Question: How can we detect anomalies accurately regardless of the size of subgraphs? Density Average Deviation Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 17/36
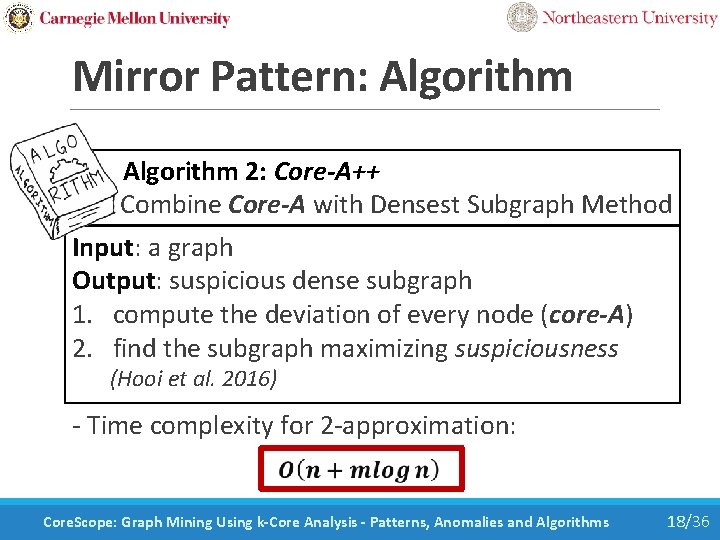
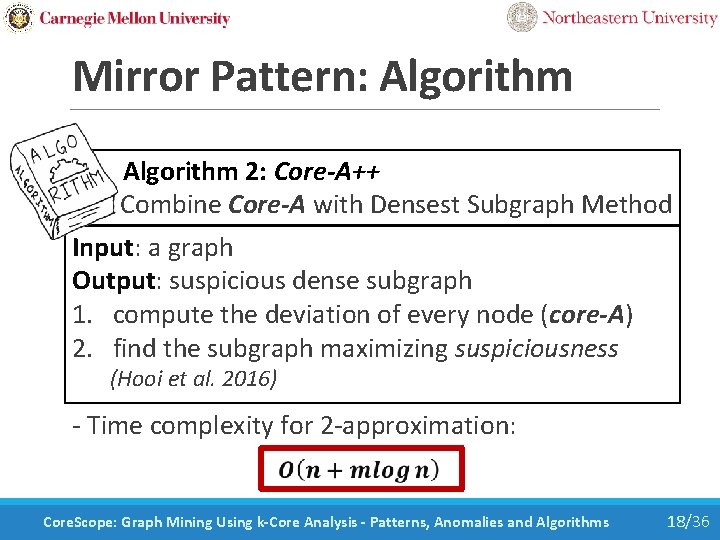
Mirror Pattern: Algorithm 2: Core-A++ Combine Core-A with Densest Subgraph Method Input: a graph Output: suspicious dense subgraph 1. compute the deviation of every node (core-A) 2. find the subgraph maximizing suspiciousness (Hooi et al. 2016) - Time complexity for 2 -approximation: Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 18/36
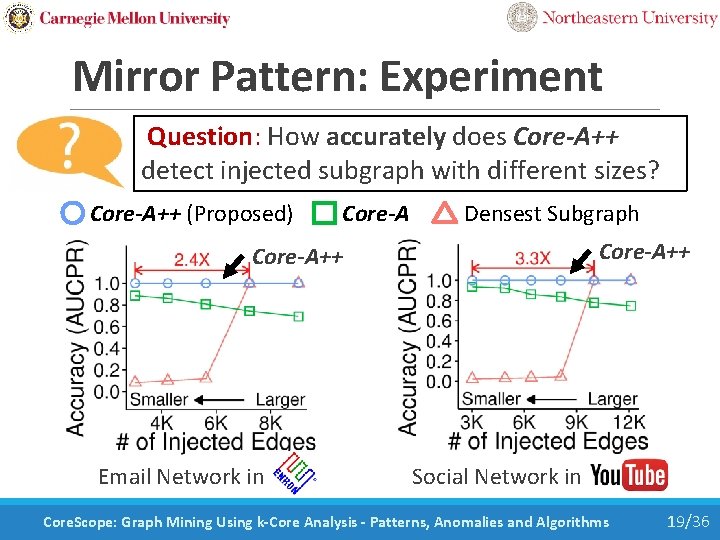
Mirror Pattern: Experiment Question: How accurately does Core-A++ detect injected subgraph with different sizes? Core-A++ (Proposed) Core-A Densest Subgraph Core-A++ Email Network in Core-A++ Social Network in Youtube Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 19/36
Road Map • Introduction • Definition of K-Cores • Pattern 1: “Mirror Pattern” • Pattern 2: “Core-Triangle Pattern” << ◦ Pattern ◦ Analysis ◦ Algorithm: Core-D (Degeneracy in Graph Stream) • Pattern 3: “Structural-Core Pattern” • Conclusion Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 20/36
![CoreTriangle Pattern Question What is the key factor determining degeneracy Reminder Degeneracy of a Core-Triangle Pattern: Question: What is the key factor determining degeneracy? [Reminder] Degeneracy of a](https://slidetodoc.com/presentation_image/29c0095047ad5342c5e794f889f32076/image-21.jpg)
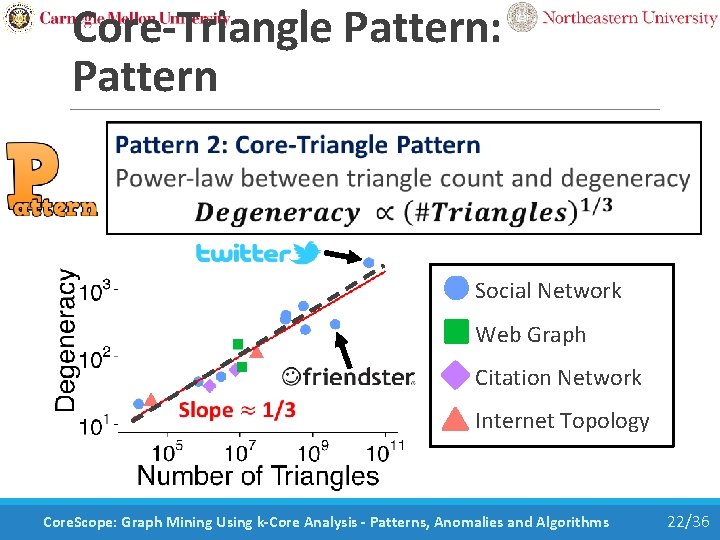
Core-Triangle Pattern: Question: What is the key factor determining degeneracy? [Reminder] Degeneracy of a graph is the highest value k such that the k-core exists Degeneracy Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 21/36
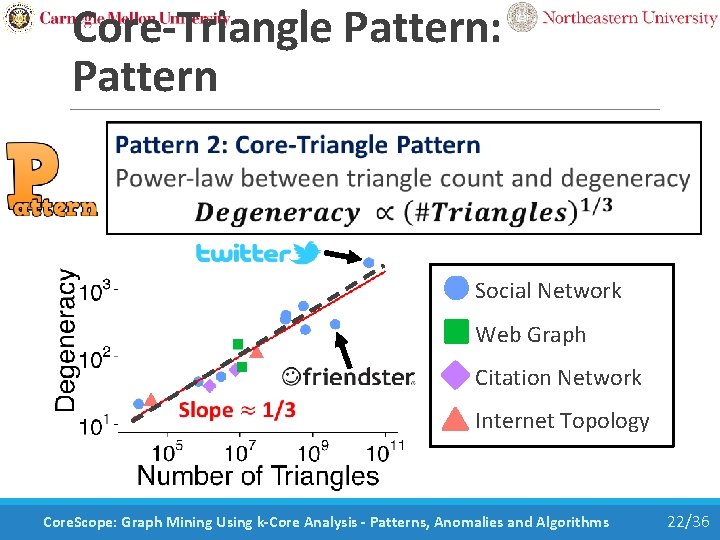
Core-Triangle Pattern: Pattern Social Network Web Graph Citation Network Internet Topology Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 22/36
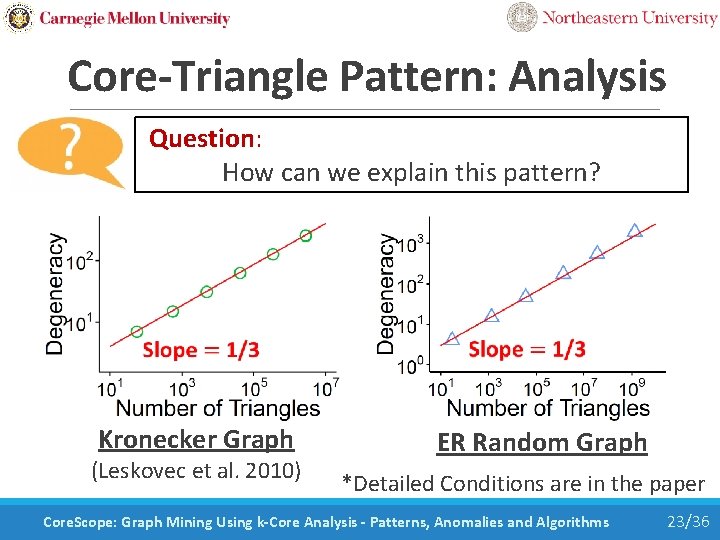
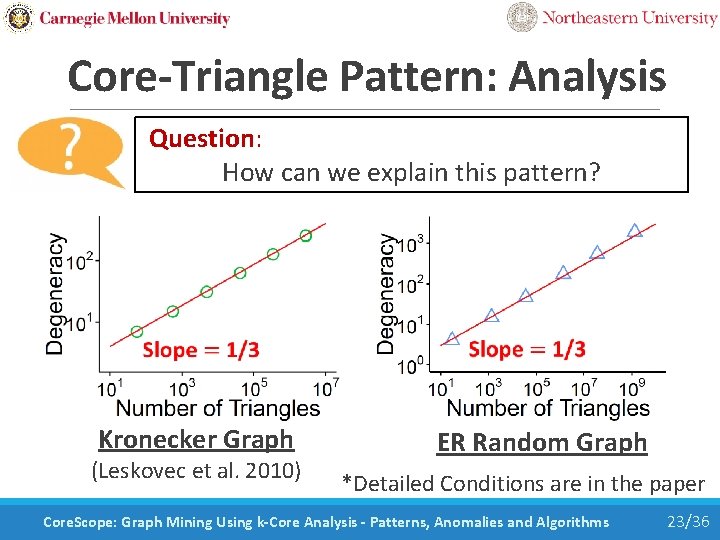
Core-Triangle Pattern: Analysis Question: How can we explain this pattern? Kronecker Graph (Leskovec et al. 2010) ER Random Graph *Detailed Conditions are in the paper Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 23/36
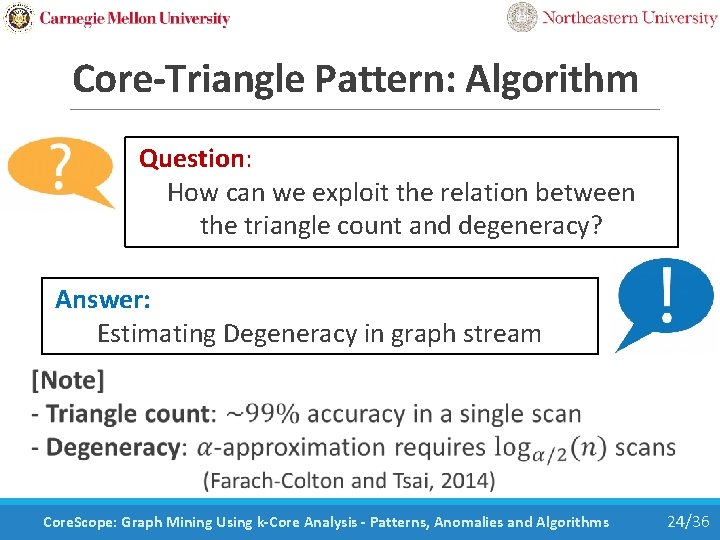
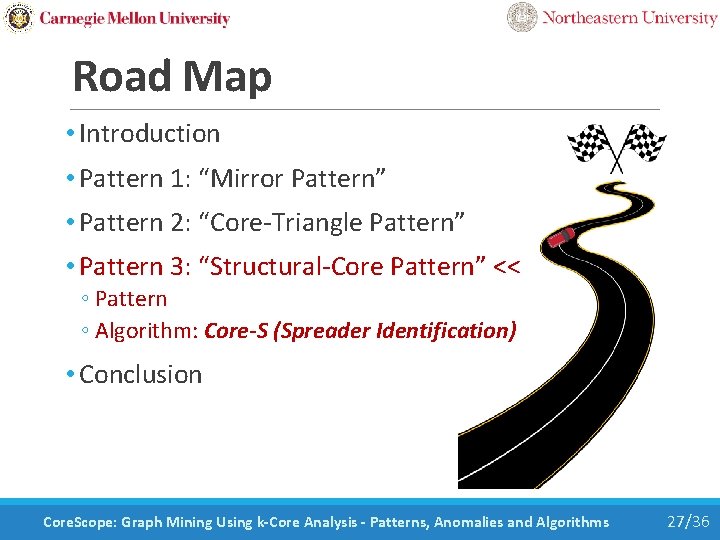
Core-Triangle Pattern: Algorithm Question: How can we exploit the relation between the triangle count and degeneracy? Answer: Estimating Degeneracy in graph stream Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 24/36
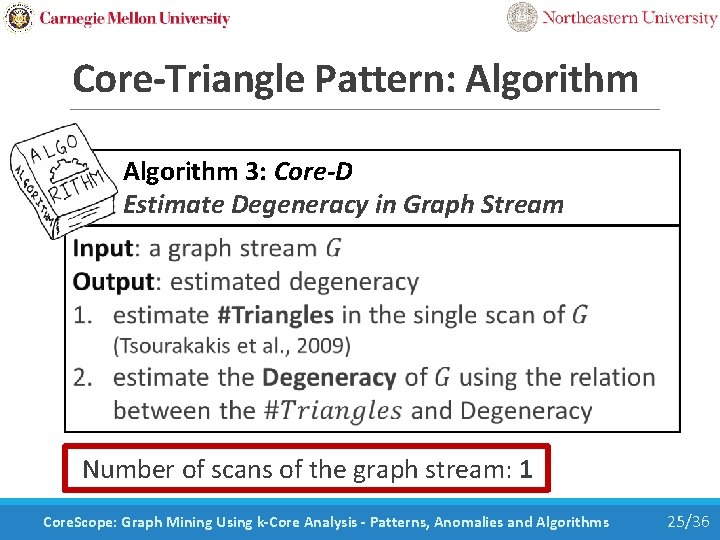
Core-Triangle Pattern: Algorithm 3: Core-D Estimate Degeneracy in Graph Stream Number of scans of the graph stream: 1 Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 25/36
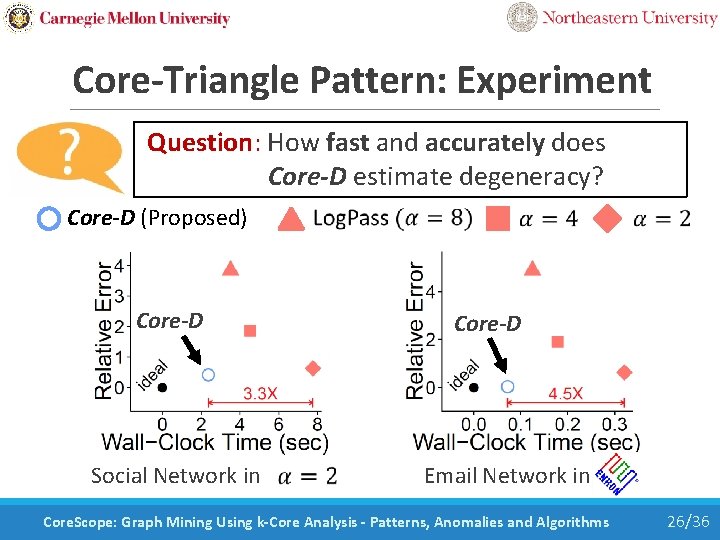
Core-Triangle Pattern: Experiment Question: How fast and accurately does Core-D estimate degeneracy? Core-D (Proposed) Core-D Social Network in Core-D Email Network in Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 26/36
Road Map • Introduction • Pattern 1: “Mirror Pattern” • Pattern 2: “Core-Triangle Pattern” • Pattern 3: “Structural-Core Pattern” << ◦ Pattern ◦ Algorithm: Core-S (Spreader Identification) • Conclusion Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 27/36
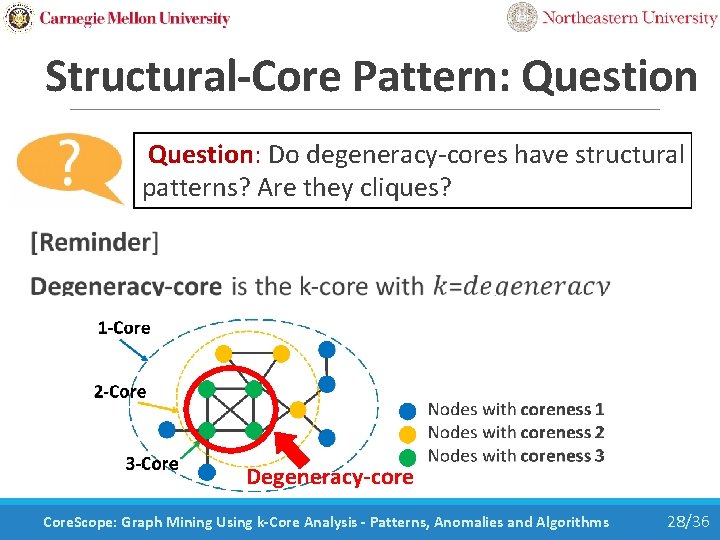
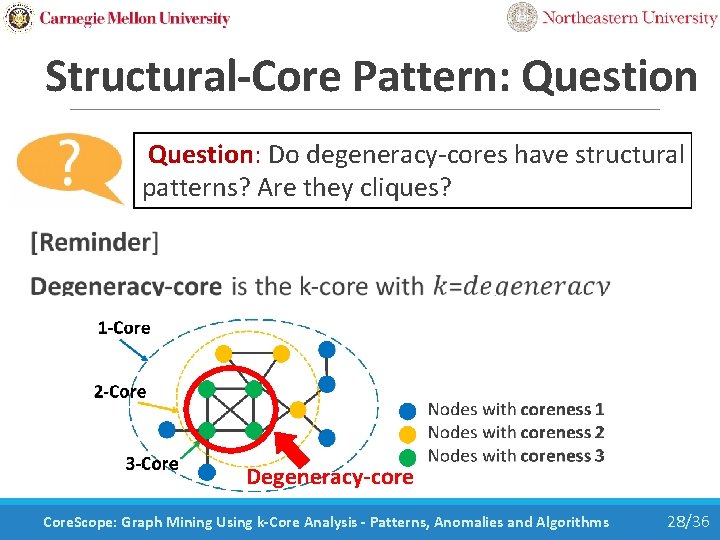
Structural-Core Pattern: Question: Do degeneracy-cores have structural patterns? Are they cliques? Degeneracy-core Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 28/36
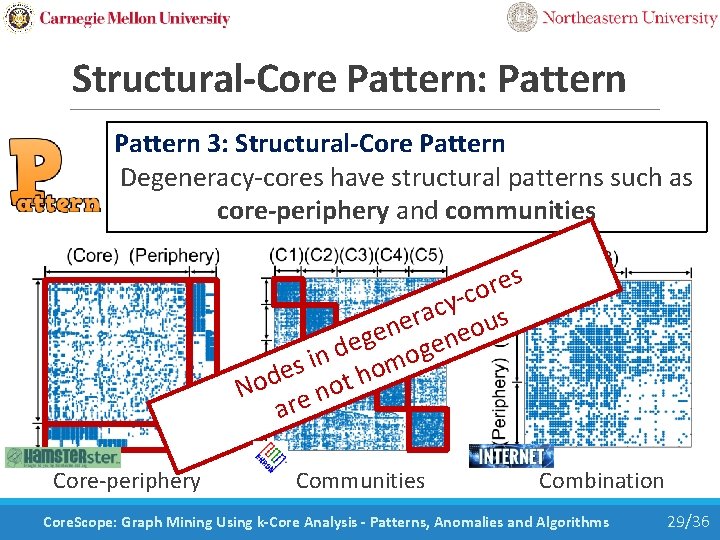
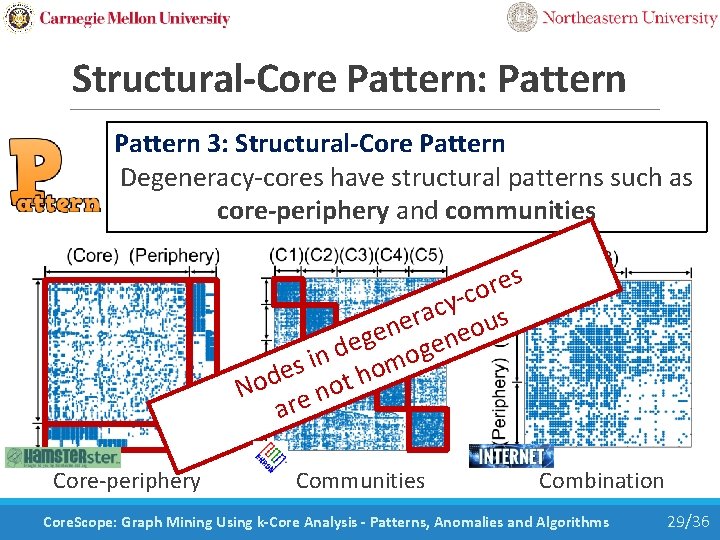
Structural-Core Pattern: Pattern 3: Structural-Core Pattern Degeneracy-cores have structural patterns such as core-periphery and communities s e r o -c y c a r s e u n o e e g n e e d mog n i s o e h d t o o N n e ar Core-periphery Communities Combination Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 29/36
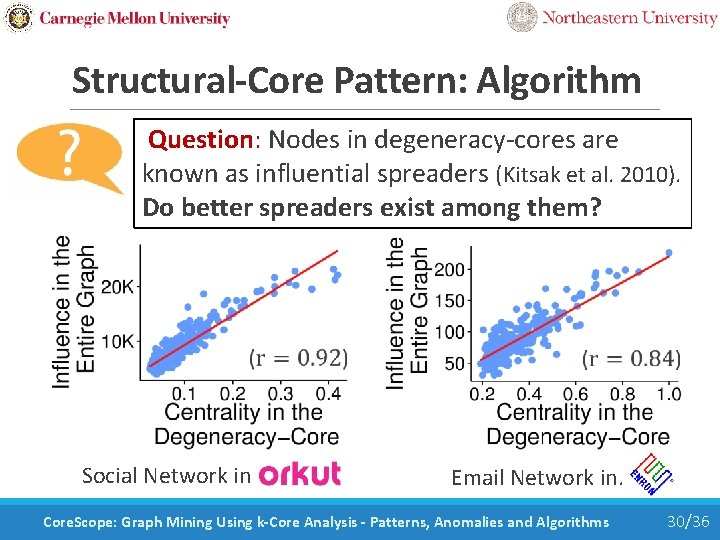
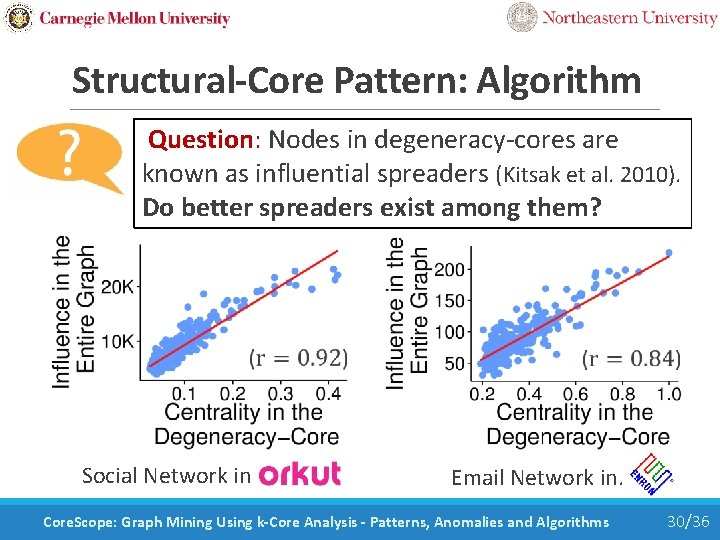
Structural-Core Pattern: Algorithm Question: Nodes in degeneracy-cores are known as influential spreaders (Kitsak et al. 2010). Do better spreaders exist among them? Social Network in Orkut Email Network in. Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 30/36
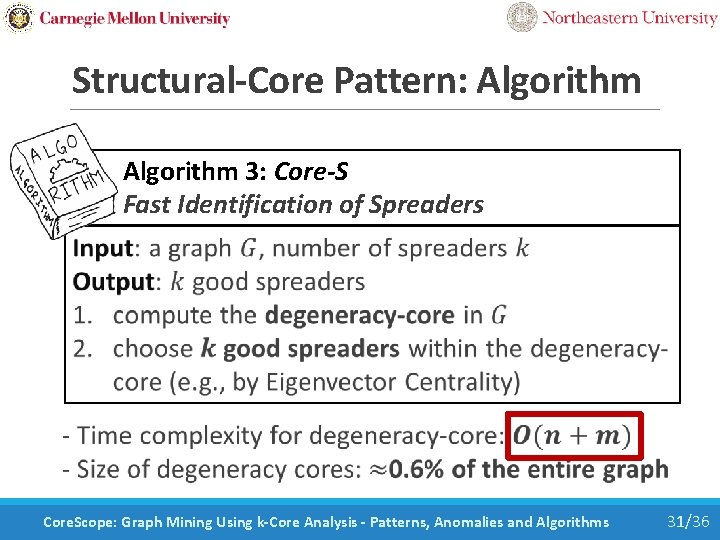
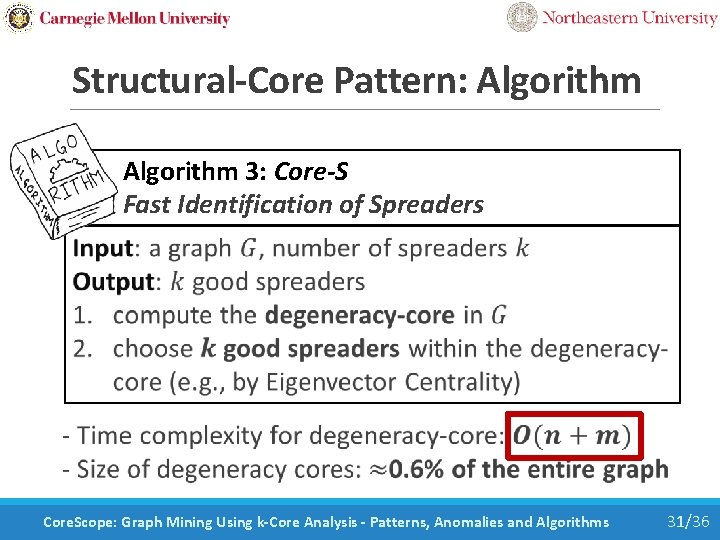
Structural-Core Pattern: Algorithm 3: Core-S Fast Identification of Spreaders Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 31/36
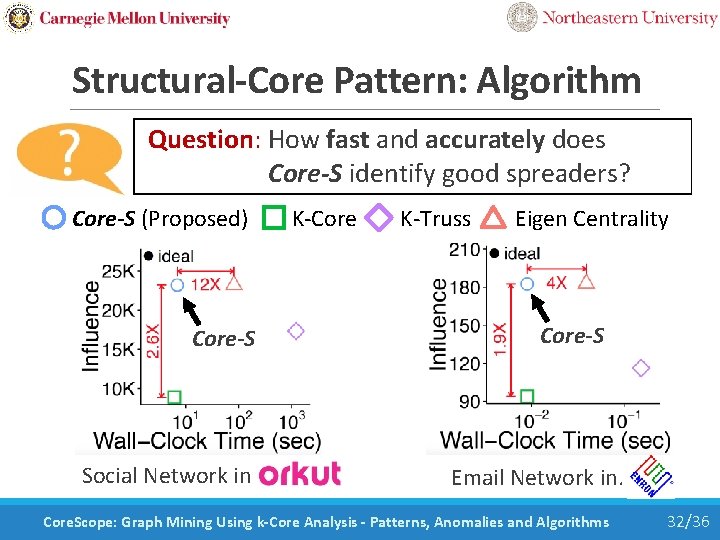
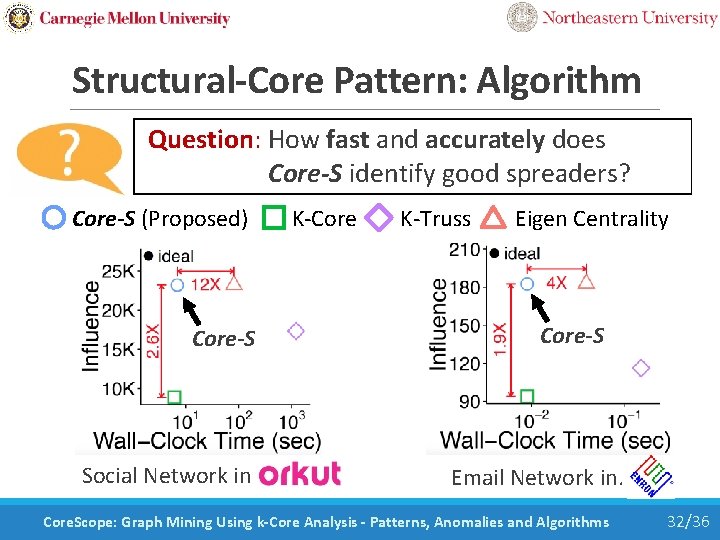
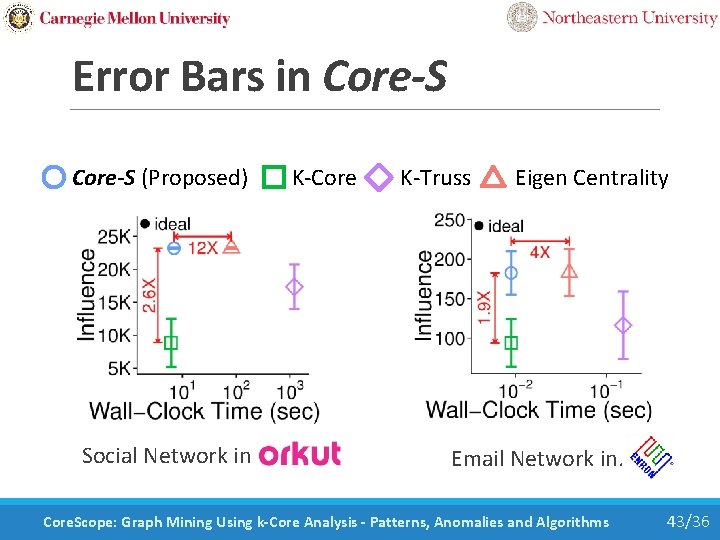
Structural-Core Pattern: Algorithm Question: How fast and accurately does Core-S identify good spreaders? Core-S (Proposed) K-Core K-Truss Eigen Centrality Core-S Social Network in Orkut Core-S Email Network in. Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 32/36
Road Map • Introduction • Definition of K-Cores • Pattern 1: “Mirror Pattern” • Pattern 2: “Core-Triangle Pattern” • Pattern 3: “Structural-Core Pattern” • Conclusion << Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 33/36
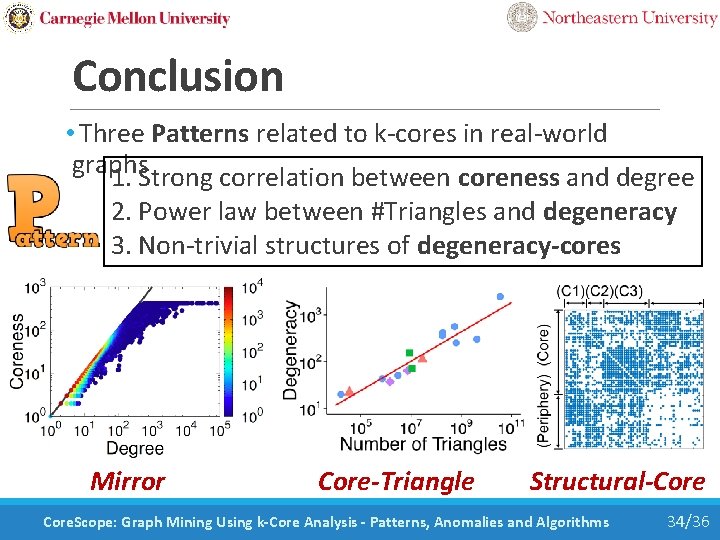
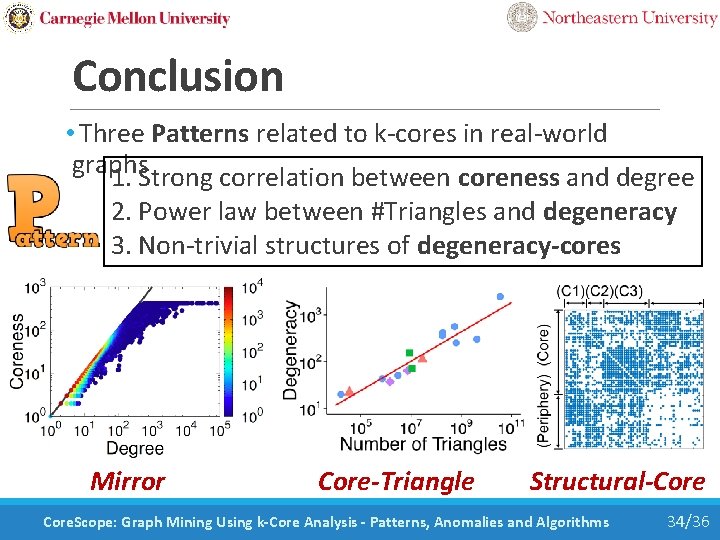
Conclusion • Three Patterns related to k-cores in real-world graphs 1. Strong correlation between coreness and degree 2. Power law between #Triangles and degeneracy 3. Non-trivial structures of degeneracy-cores Mirror Core-Triangle Structural-Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 34/36
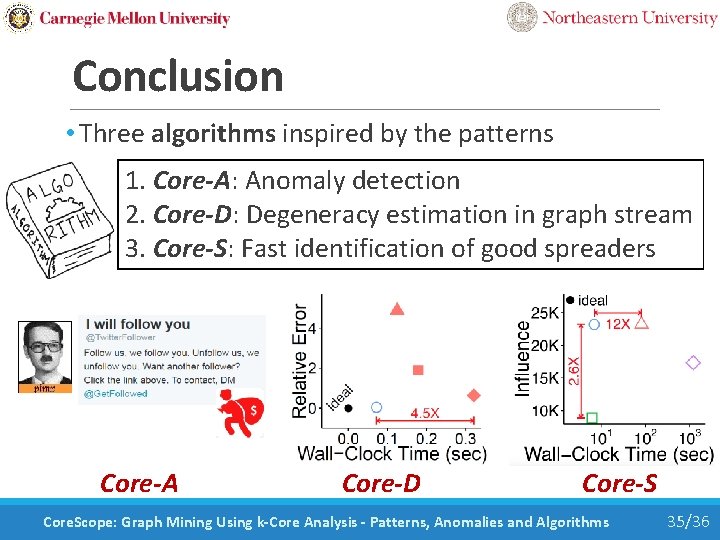
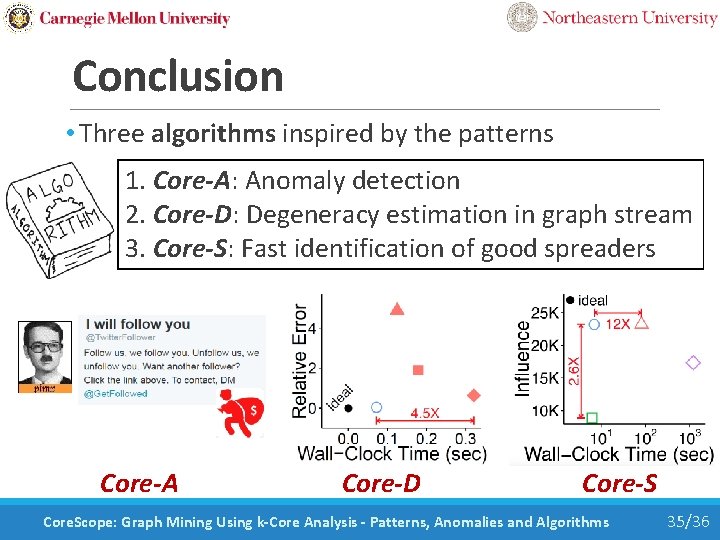
Conclusion • Three algorithms inspired by the patterns 1. Core-A: Anomaly detection 2. Core-D: Degeneracy estimation in graph stream 3. Core-S: Fast identification of good spreaders Core-A Core-D Core-S Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 35/36
Thank you! • Source codes and datasets used in the paper are available at https: //github. com/kijungs/corescope M-Zoom: Fast Dense-Block Detection in Tensors with Quality Guarantees 36/36
Backup Slides Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 37/36
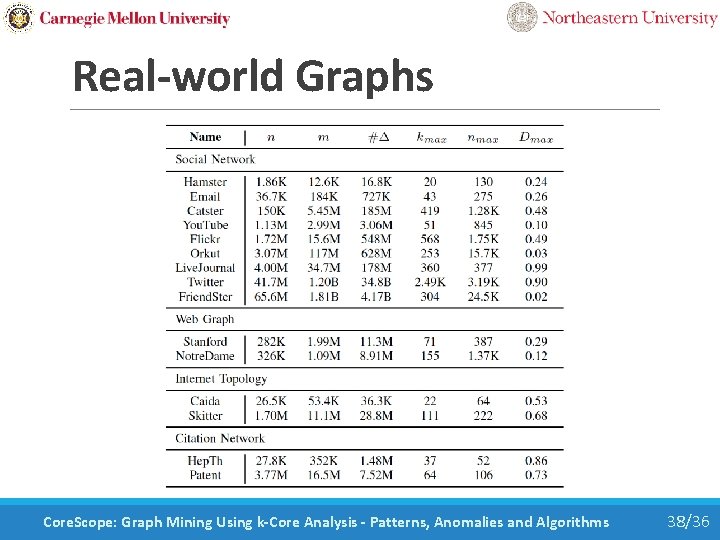
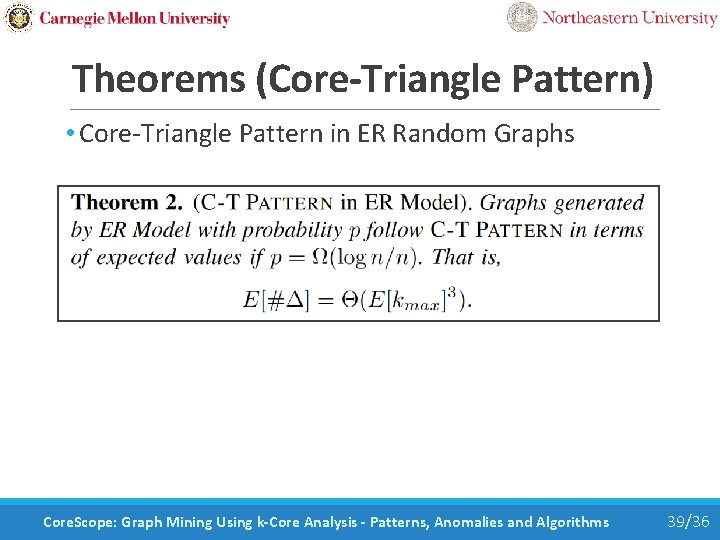
Real-world Graphs Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 38/36
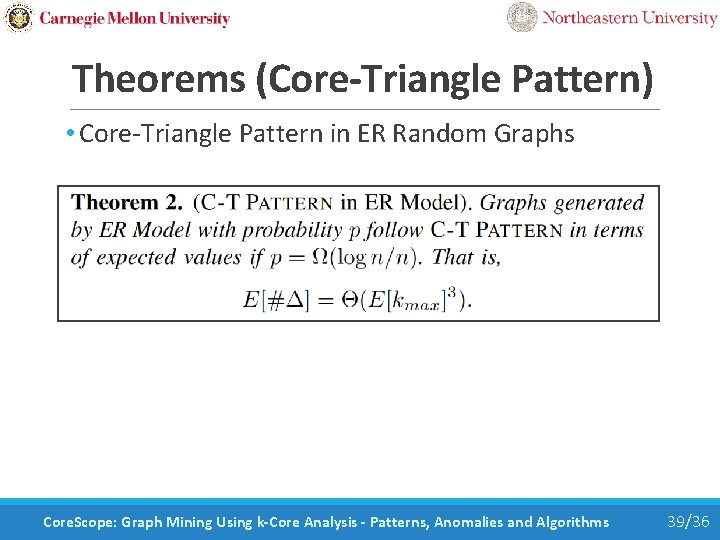
Theorems (Core-Triangle Pattern) • Core-Triangle Pattern in ER Random Graphs Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 39/36
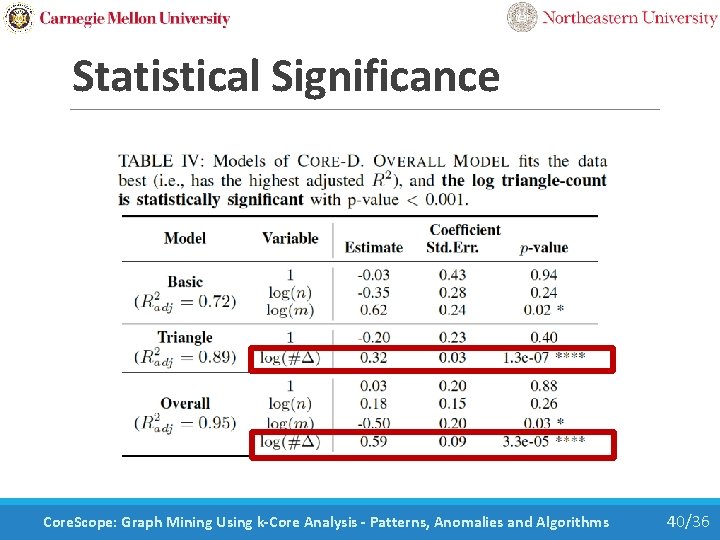
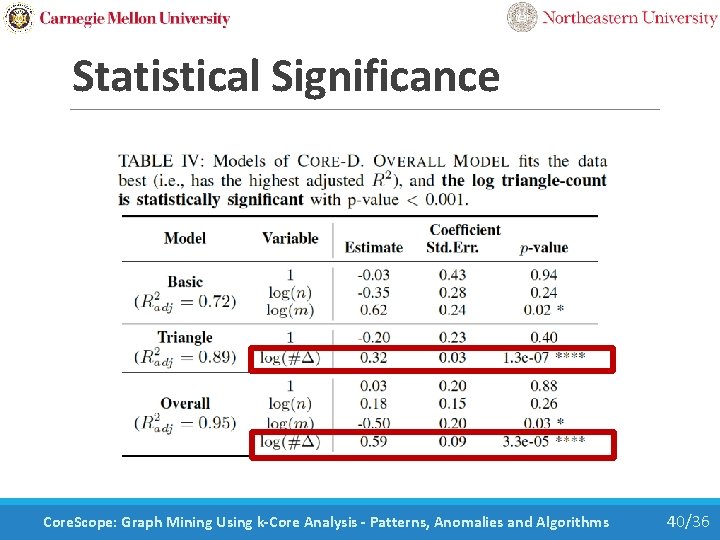
Statistical Significance Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 40/36
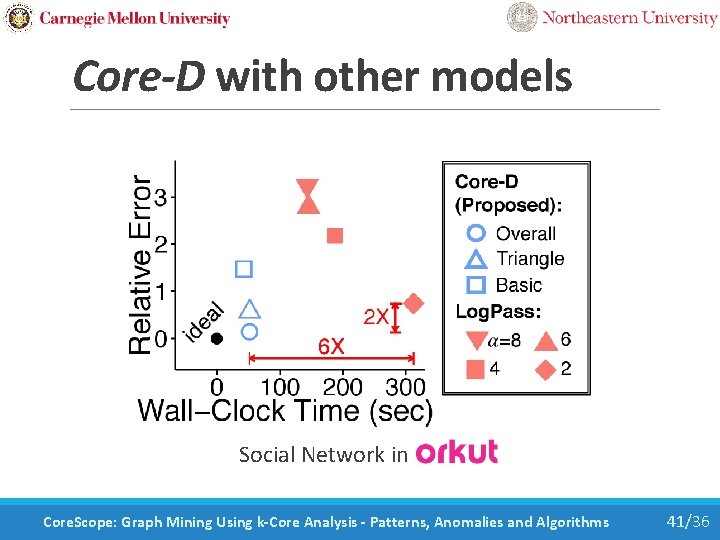
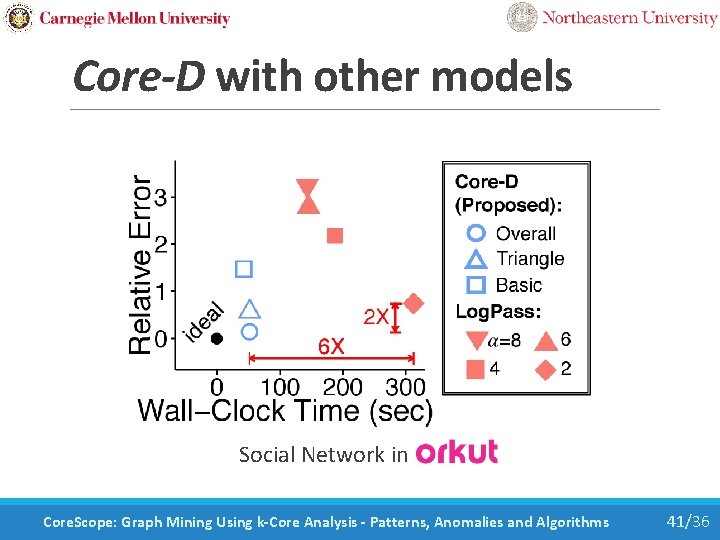
Core-D with other models Social Network in Orkut Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 41/36
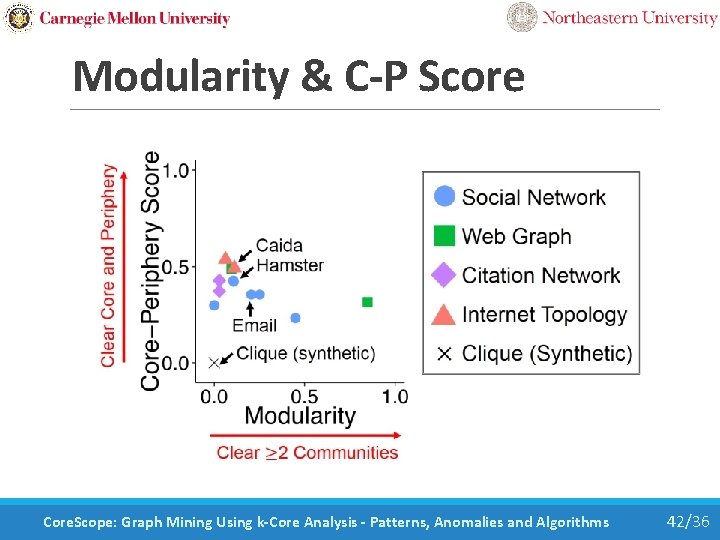
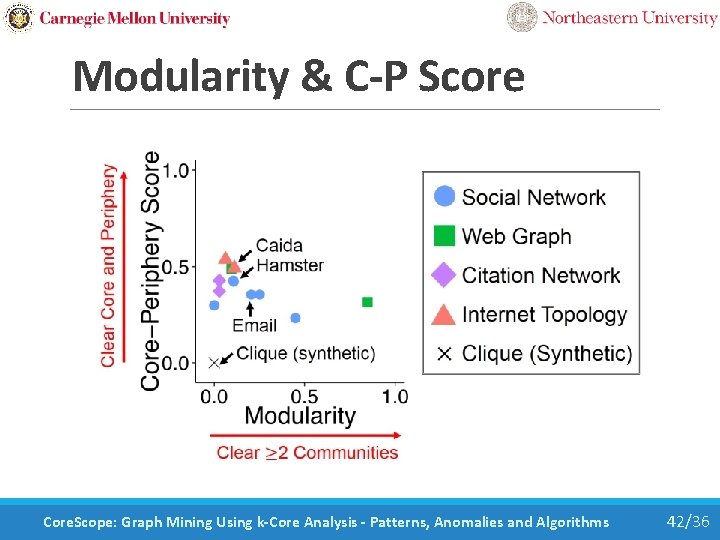
Modularity & C-P Score Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 42/36
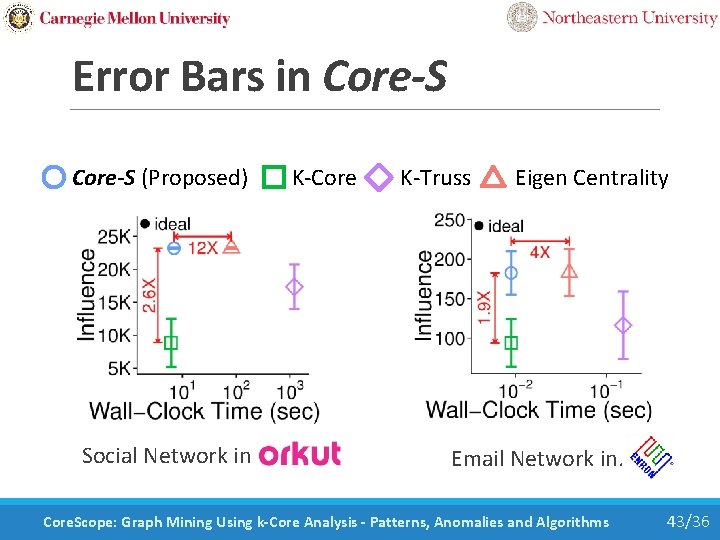
Error Bars in Core-S (Proposed) K-Core K-Truss Eigen Centrality Social Network in Orkut Email Network in. Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 43/36
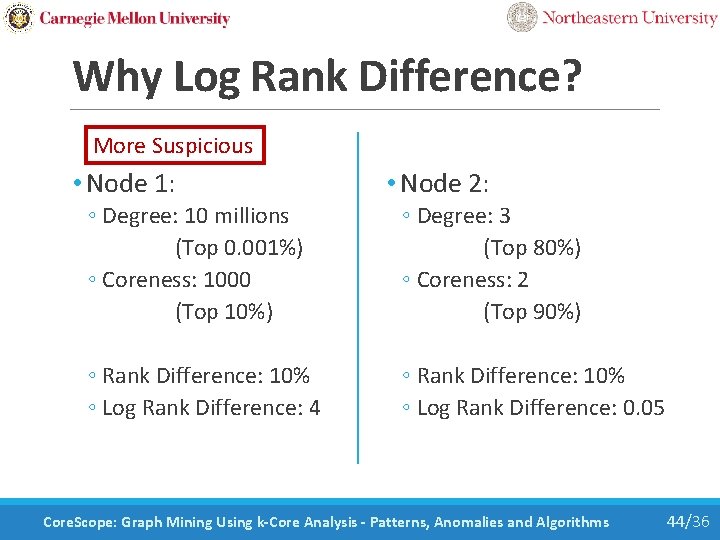
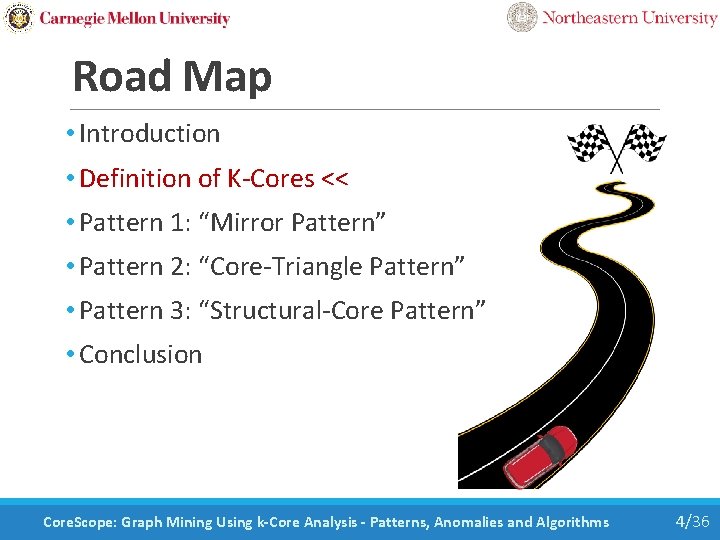
Why Log Rank Difference? More Suspicious • Node 1: • Node 2: ◦ Degree: 10 millions (Top 0. 001%) ◦ Coreness: 1000 (Top 10%) ◦ Degree: 3 (Top 80%) ◦ Coreness: 2 (Top 90%) ◦ Rank Difference: 10% ◦ Log Rank Difference: 4 ◦ Rank Difference: 10% ◦ Log Rank Difference: 0. 05 Core. Scope: Graph Mining Using k-Core Analysis - Patterns, Anomalies and Algorithms 44/36