Coolaid Debugging Compilers with Untrusted Code Verification BorYuh
Coolaid: Debugging Compilers with Untrusted Code Verification Bor-Yuh Evan Chang with George Necula, Robert Schneck, and Kun Gao May 14, 2003 OSQ Retreat
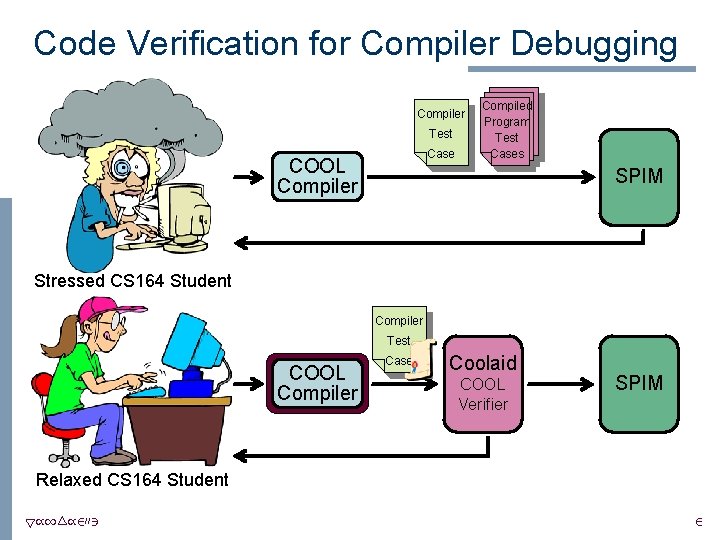
Code Verification for Compiler Debugging Compiler Test Case COOL Compiler Compiled Program Test Cases SPIM Stressed CS 164 Student Compiler Test COOL Compiler Case Coolaid COOL Verifier SPIM Relaxed CS 164 Student 5/14/2003 2
Code Verification for Compiler Debugging • COOL’s type system ensures certain safety properties, such as memory safety • Unverifiable code is either – not from a certifying COOL compiler; – from a compiler with a code generation scheme confusing to the verifier; or • e. g. offset an address by indexing into a table – from a broken COOL compiler • e. g. did not emit null pointer check 5/14/2003 3
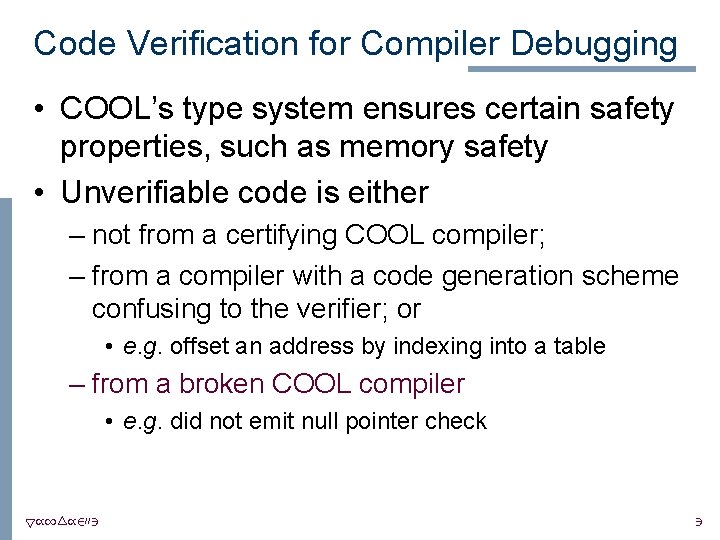
Coolaid vs. JVML Bytecode Verifier Similarities • Abstract interpreter over types for each register (roughly) • “Execute” a method by proceeding assuming the effect as dictated by the method type • Take least upper bound for each register at join points • Stop when a fixed point is reached Differences • Coolaid verifies low-level assembly • Need to store some intermediate information – e. g. a pointer is not null – e. g. class tag for some object • Need equivalence classes of values – i. e. not only that r 1 : A and r 2 : A, but that r 1 = r 2 – null checks • Some code generation sensitivity 5/14/2003 4
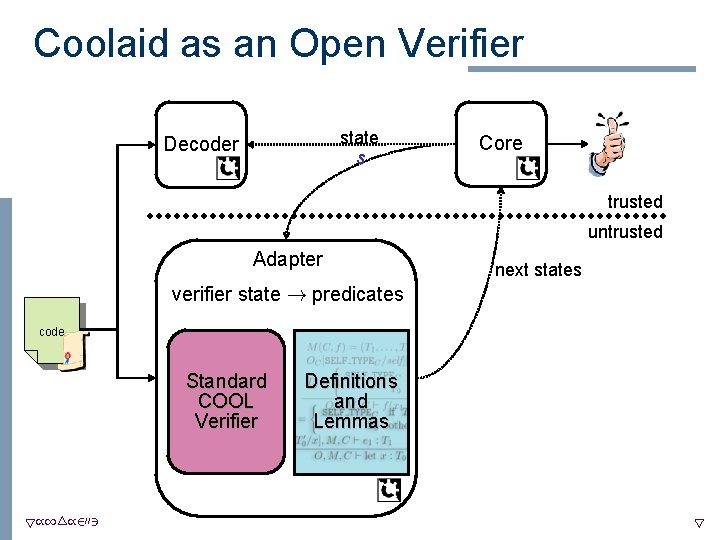
Coolaid as an Open Verifier state s Decoder Core trusted untrusted Adapter next states verifier state ! predicates code Extension Standard Definitions COOL and Verifier Lemmas 5/14/2003 5
![Summary • COOL [Aiken et al. ] – more compilers than programs! – small Summary • COOL [Aiken et al. ] – more compilers than programs! – small](http://slidetodoc.com/presentation_image/59ba77631fcf06bb0901876ebaee5f6f/image-6.jpg)
Summary • COOL [Aiken et al. ] – more compilers than programs! – small language but with realistic challenges, e. g. , dynamic dispatch – ideal testbed for open verifier project • COOL Open Verifier – test our ideas for an open verification architecture for proof-carrying code – provide students with a helpful debugging tool 5/14/2003
- Slides: 6