Conveying Trust Serge Egelman CMU Usable Privacy and
Conveying Trust Serge Egelman CMU Usable Privacy and Security Laboratory http: //cups. cmu. edu/
Portal to The Interweb n Threats to privacy: • Phishing • Information interception • Fraudulent sites n Web browser is central • Email • IM n Detection must occur here • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
In The Beginning… n Man-in-the-middle n Sniffing n SSL solved these n Browser SSL indicators • • Locks Keys Borders URL bar • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
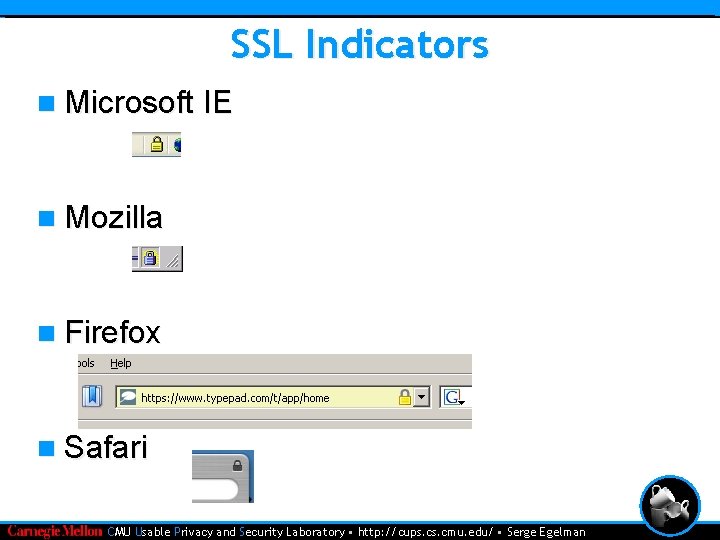
SSL Indicators n Microsoft IE n Mozilla n Firefox n Safari • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
But What About Phishing? n Toolbars n User notification • Audio • Pop-ups • Indicators n Community ratings n Heuristics • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
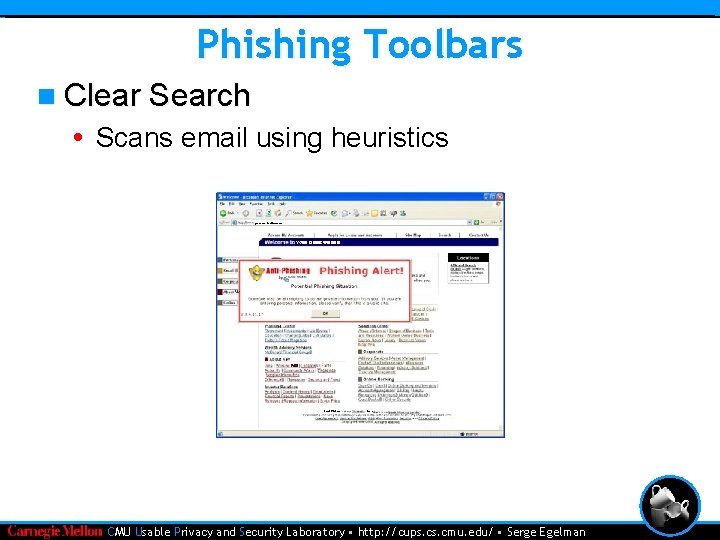
Phishing Toolbars n Clear Search • Scans email using heuristics • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
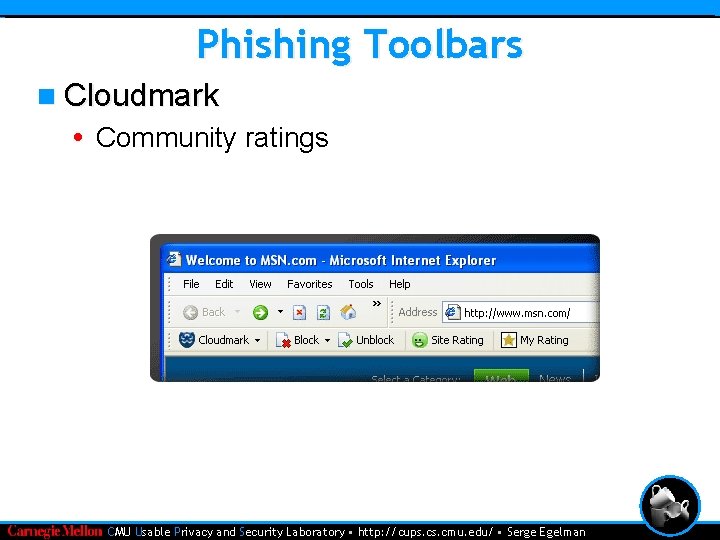
Phishing Toolbars n Cloudmark • Community ratings • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
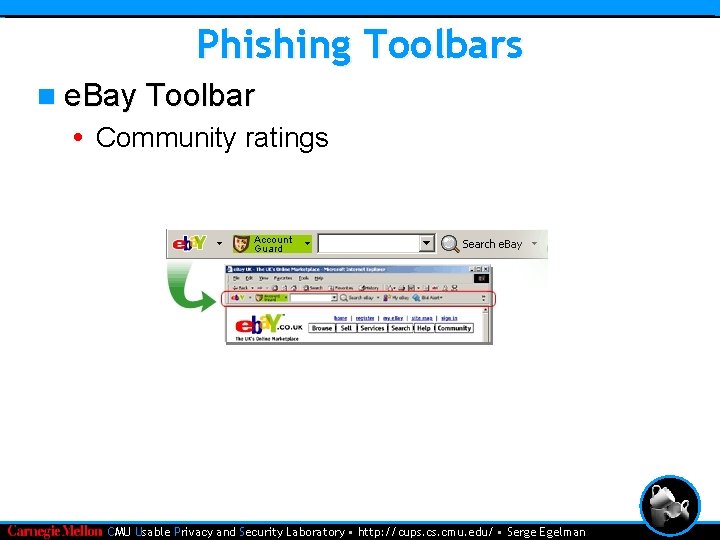
Phishing Toolbars n e. Bay Toolbar • Community ratings • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
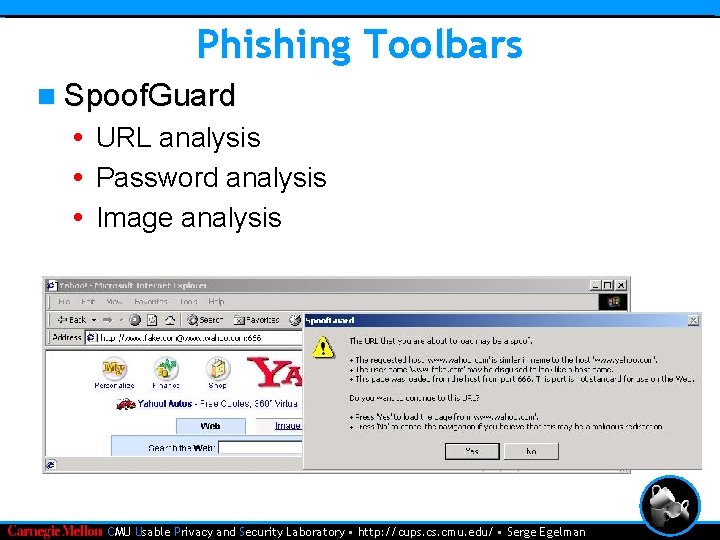
Phishing Toolbars n Spoof. Guard • URL analysis • Password analysis • Image analysis • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
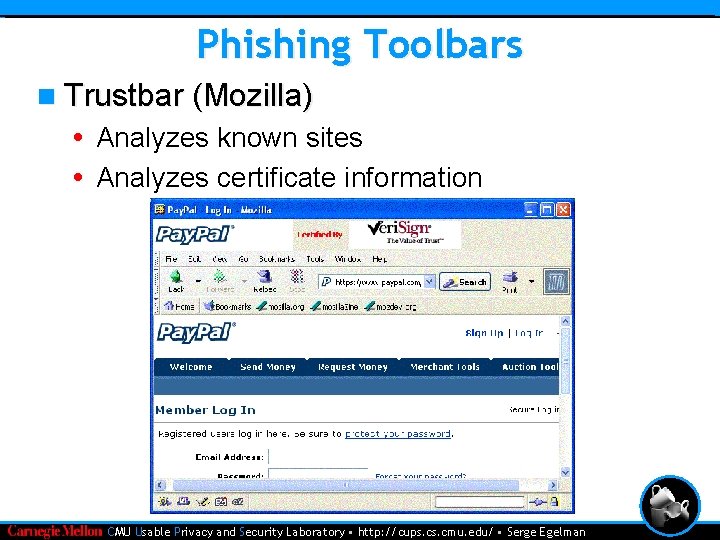
Phishing Toolbars n Trustbar (Mozilla) • Analyzes known sites • Analyzes certificate information • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
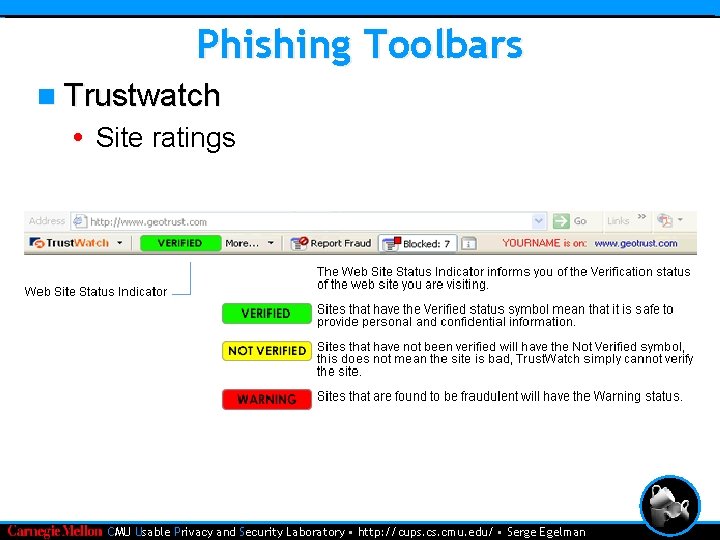
Phishing Toolbars n Trustwatch • Site ratings • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
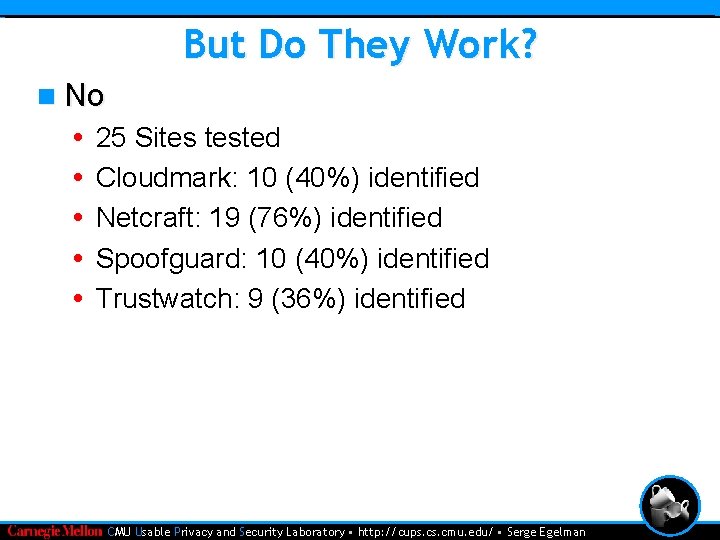
But Do They Work? n No • • • 25 Sites tested Cloudmark: 10 (40%) identified Netcraft: 19 (76%) identified Spoofguard: 10 (40%) identified Trustwatch: 9 (36%) identified • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Activity #1 n Download a phishing toolbar: • • • http: //www. cloudmark. com/desktop/download/ http: //pages. ebay. com/ebay_toolbar/ http: //crypto. stanford. edu/Spoof. Guard/ http: //trustbar. mozdev. org/ http: //toolbar. trustwatch. com/ http: //toolbar. netcraft. com/ n Pros? Cons? n Is it usable? n How could it be circumvented? • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Other Browser Plugins n Previously mentioned toolbars • Phishing • Fraudulent sites • Limited intelligence • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Password Hashing n Many users use same passwords • One compromise leads to many • Knowing real password doesn’t help n Hashing solves this • Passwords hashed automatically with domain name • User doesn’t know the difference n Mozilla extension • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Dynamic Security Skins n User remembers one image • Trusted window n User remembers one password • Ease of use • Sites get hashed password n Matches two patterns to trust server • Generated using a shared secret • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
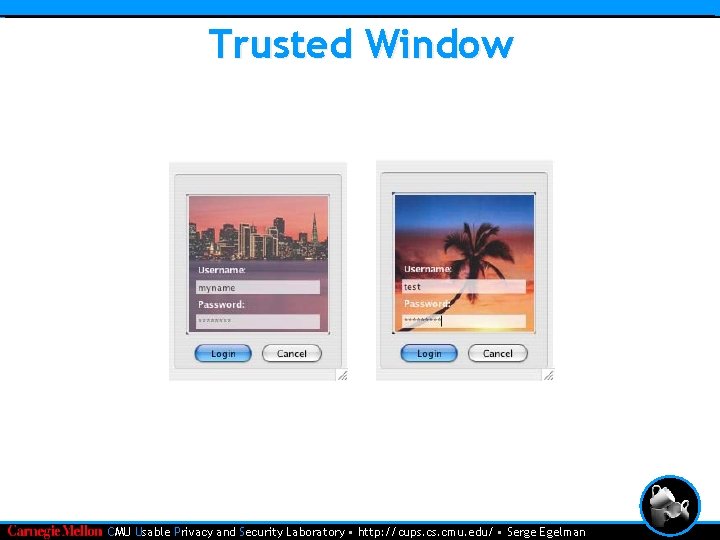
Trusted Window • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
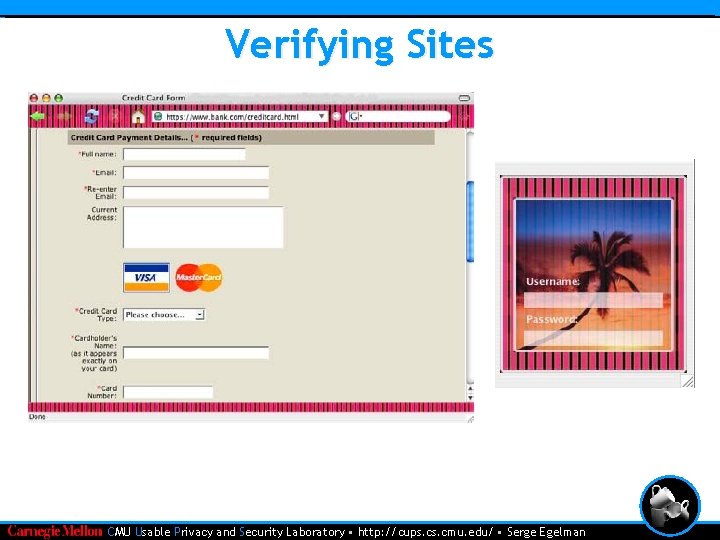
Verifying Sites • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Using Tokens n Two factor authentication • Something you have • Usually cryptographic n Secure. ID n Smart cards n Random cryptographic tokens n Scratch cards • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Using Phones n Client side certificates • Private keys generated/stored on phone • New key for each phone n Keys linked to domain names n Key generated upon new connection n Bluetooth n No server modifications • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Current Browser Support n Hardware drivers • Crappy browser support • Example n Simple text box n Make using the device unobtrusive n Activity #2 • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
False Sense of Security n Java. Script tricks • ING example • MITM • Spyware n Stored images • Bank of America example • MITM • Spyware n CAPTCHAs • MITM • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
Activity #3 n What security features really need to be prominent? • CMU Usable Privacy and Security Laboratory • http: //cups. cmu. edu/ • Serge Egelman
- Slides: 23