Controlled Algebras and GIIs Ronald L Rivest MIT
Controlled Algebras and GII’s Ronald L. Rivest MIT CSAIL IPAM Workshop October 9, 2006
Outline u. Controlled algebras u. Trapdoor discrete log groups u. Black box & pseudo-free groups u. Groups with infeasible inverses u. Transitive signatures u. Trapdoor pairings
Algebra u( S 1 , S 2 , op 1 , op 2, …, opn ) u Algebra is set(s) with operation(s). u Abstract algebra is mathematical object. u Instantiation is computational object: – Each element of set has one or more representations. – Each operation has associated computational procedure.
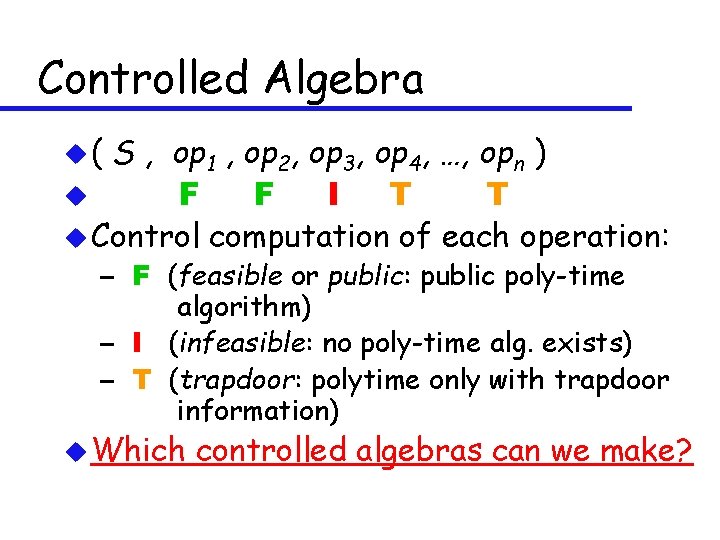
Controlled Algebra u( S , op 1 , op 2, op 3, op 4, …, opn ) u F F I T T u Control computation of each operation: – F (feasible or public: public poly-time algorithm) – I (infeasible: no poly-time alg. exists) – T (trapdoor: polytime only with trapdoor information) u Which controlled algebras can we make?
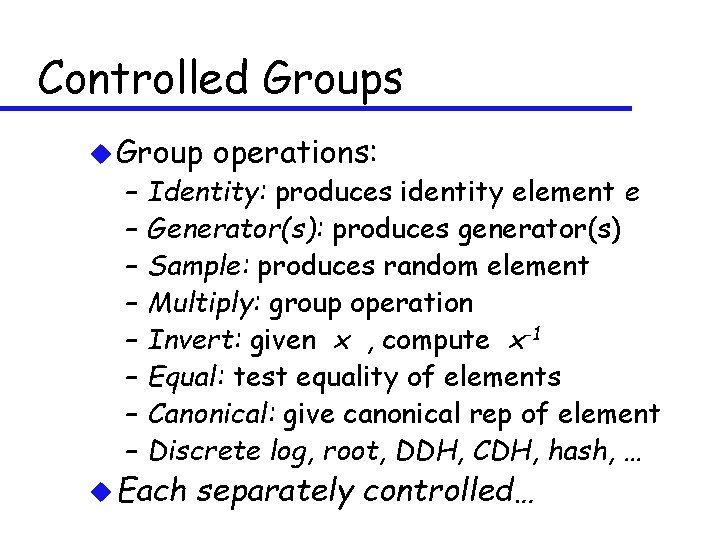
Controlled Groups u Group – – – – operations: Identity: produces identity element e Generator(s): produces generator(s) Sample: produces random element Multiply: group operation Invert: given x , compute x-1 Equal: test equality of elements Canonical: give canonical rep of element Discrete log, root, DDH, CDH, hash, … u Each separately controlled…
Analogy: gene expression u One of the marvelous features of the way DNA works is that the semantics of the gene (i. e. , what protein is made) is decoupled from the control of its expression. Semantics and control may evolve separately. control protein
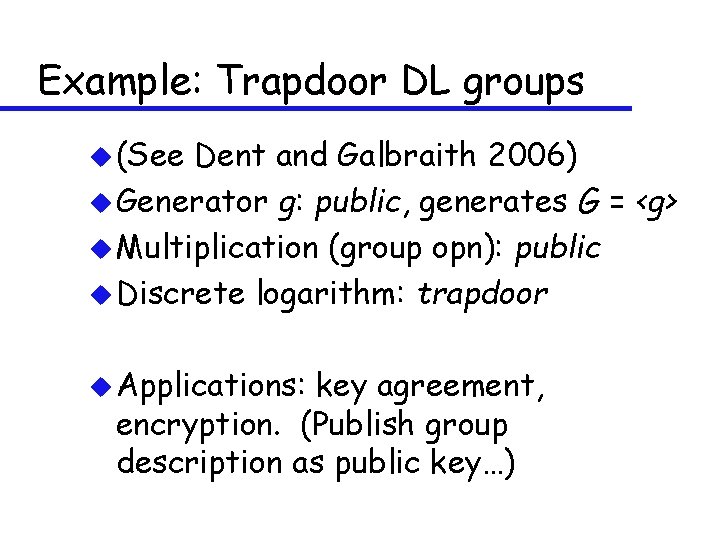
Example: Trapdoor DL groups u (See Dent and Galbraith 2006) u Generator g: public, generates G = <g> u Multiplication (group opn): public u Discrete logarithm: trapdoor u Applications: key agreement, encryption. (Publish group description as public key…)
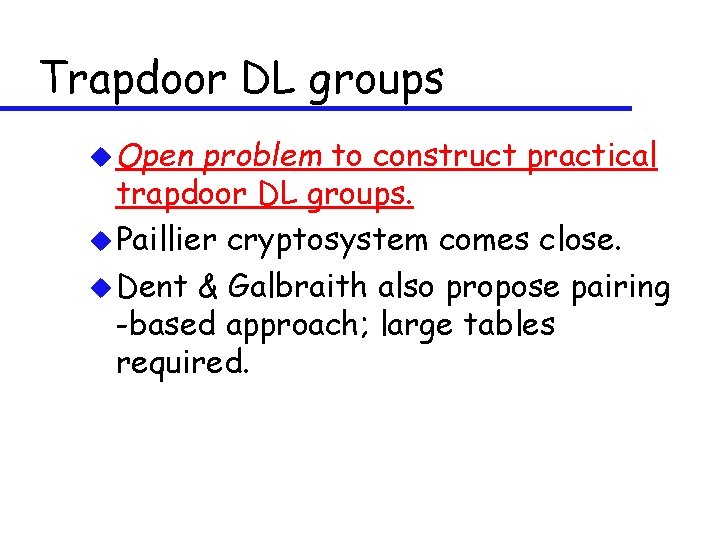
Trapdoor DL groups u Open problem to construct practical trapdoor DL groups. u Paillier cryptosystem comes close. u Dent & Galbraith also propose pairing -based approach; large tables required.
Black box group u Controlled group related to notion of black box group (group operation efficient; others, such as discrete log, may not be) which is “essentially the same” as (“just”) the mathematical object. u Some attempts to have “computational black box group” (Frey; Galbraith) via “disguised elliptic curves” or other techniques, for specific groups.
“Pseudo-free” Group u Notion introduced by Hohenberger (2003), refined by Rivest (2004). u Group is (strongly) “pseudo-free” if adversary can’t find solution to any “non-trivial” equation (i. e. one that has no solution in free group). u Micciancio (2005) showed that Zn* where n=pq is pseudo-free (given “strong RSA assumption”).
Groups with Infeasible Inverses (GII’s) u Want group operation to be easy, but computing inverses to be hard (for everyone). u GII’s introduced by Susan Hohenberger in her MS thesis; also studied by David Molnar, Vinod Vaikuntanathan. u Open problem to make GII’s under reasonable assumptions.
GII’s imply Key Agreement u (Hohenberger; Rabi/Sherman) u Alice draws random elts: x, y u Alice sends Bob: xy, y u Bob draws random elt: z u Bob sends Alice yz u Both compute K = (xy)z = x(yz)
![Security Argument [H] u An Eve who can guess K=xyz from (xy, y, yz) Security Argument [H] u An Eve who can guess K=xyz from (xy, y, yz)](http://slidetodoc.com/presentation_image/e6c839c5c97fb34f35377eeda10e038d/image-13.jpg)
Security Argument [H] u An Eve who can guess K=xyz from (xy, y, yz) can invert random elts. u Choose a at random u Give Eve xy = ai , y = aj , yz = ak where i-j+k=-1. u Then K = ai-j+k = a-1.
Strongly Associative OWF’s u (Introduced by Rabi/Sherman) u Associative function f(. , . ) on set S u Easy to compute f(x, y) given x, y u Given f(x, y) and y , hard to compute any x’ such that f(x’, y) = f(x, y). u Hemaspaandra and Rothe show that SAOWF and OWF are black-box equivalent on non-structured domains. u But on a group, SAOWF = GII’s.
Trapdoor GII’s (TGII’s) u GII except some trapdoor information allows computation of inverses. u Any finite GII is really TGII, since knowing group order allows computation of inverses. However, it may be possible to generate a GII without anyone knowing group order…
Applications of TGII’s u Vaikuntanathan (2003) has shown how to implement IBE using any TGII that has an efficient algorithm for sampling a random element together with its inverse. u Is this only known sufficient condition for IBE outside of bilinear maps?
Vaikuntanathan’s IBE construction u Let G be a TGII, h 1 h 2 hash functions. u Given ID, define g. ID = h 1(ID) u Define sk. ID = g. ID-1 (using trapdoor) u To encrypt m, pick r randomly, then: C = (r g. ID, m h 2(r)) u To decrypt (s, t) compute m = t h 2(s sk. ID) u (Sampling of pairs (a, a-1) needed, but only in reduction proof, for ID-CPA security. )
How to construct GII or TGII? ? u Order of group must be hidden. u RSA group (Zn*) has hidden order, but inverses are unfortunately easy. u Maybe use “trusted oracle” to provide interface for composition / sampling / comparing elements, but not inversion. All reps are encrypted. (Saxena and Soh) u Open problem!
Transitive Signatures u (due to Micali/Rivest) u Signature scheme on pairs of elts (think of σ(a, b) as sig on edge (a, b) ) u DTS (Directed Transitive Signatures) Given σ(a, b) and σ(b, c) , anyone can compute σ(a, c) u UTS (Undirected TS) Given σ(a, b), easy to compute σ(b, a)
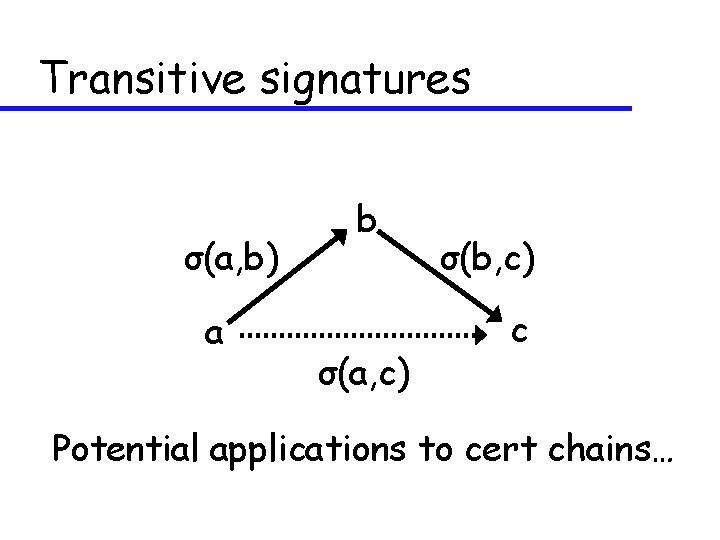
Transitive signatures σ(a, b) a b σ(a, c) σ(b, c) c Potential applications to cert chains…
![Some relationships (see [H]) TDP OT PKE TDL BM TGII DTS GII KA OWF Some relationships (see [H]) TDP OT PKE TDL BM TGII DTS GII KA OWF](http://slidetodoc.com/presentation_image/e6c839c5c97fb34f35377eeda10e038d/image-21.jpg)
Some relationships (see [H]) TDP OT PKE TDL BM TGII DTS GII KA OWF SDS UTS
Constructing a DTS from TGII u Simple way to build a directed transitive signature scheme from a TGII: – Signature on (a, b) is just a/b u But is this secure? ? ?
Trapdoor pairings u. A group with a bilinear map, except that one needs trapdoor information to compute the pairing function. (Rivest (2004), Dent & Galbraith (2006))
Applications of trapdoor pairings u ID scheme (Dent & Galbraith): Alice is only one who can correctly compute DDH results on challenges (ga, gb, gab) or (ga, gb, gc) u Making various flavors of signature schemes (ID-based, aggregate, ring, …) into “designated verifier” schemes
Construction of trapdoor pairings u Use elliptic curve over Zn where n=pq (Dent & Galbraith 2006) u “Disguised elliptic curves” (Dent & Galbraith, Galbraith 2006) Parameters may have to be extremely large…
Summary – Open problems 1. 2. 3. 4. Construct practical trapdoor DL groups. Make groups with infeasible inversion (GII’s), under reasonable assumptions. Make better trapdoor pairings. Prove that simple TGII---->DTS construction is secure (or fix it).
Acknowledgments u Thanks to Susan Hohenberger, David Molnar, and Vinod Vaikuntanathan for helpful suggestions and comments….
(The End)
- Slides: 28