Continuous Monitoring with the 20 Critical Security Controls

- Slides: 46
Continuous Monitoring with the 20 Critical Security Controls SESSION ID: SPO 1 -W 02 Wolfgang Kandek CTO
We called 2013 the year of the data breach… #RSAC 2
…but 2014 started in much the same spirit… #RSAC 3
Background u Open System Administration Channels u Default and Weak Passwords u End-user has Admin Privileges u Outdated Software Versions #RSAC 4
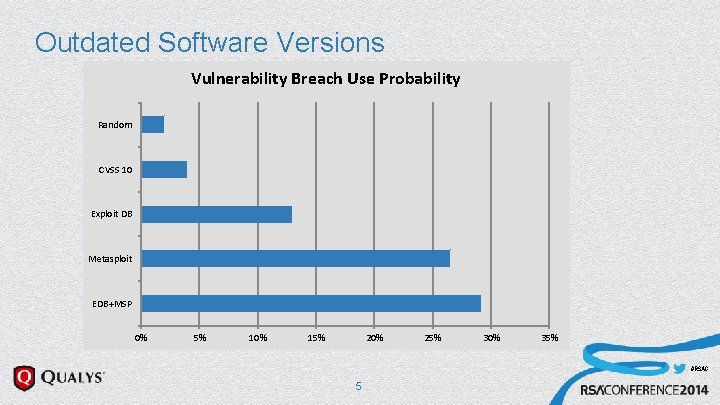
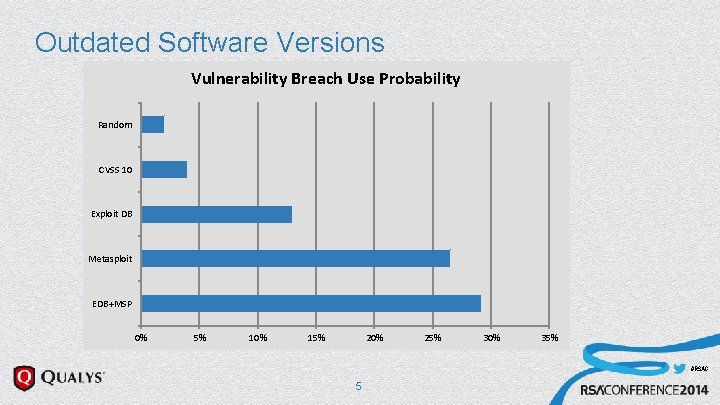
Outdated Software Versions Vulnerability Breach Use Probability Random CVSS 10 Exploit DB Metasploit EDB+MSP 0% 5% 10% 15% 20% 25% 30% 35% #RSAC 5
Background u Open System Administration Channels u Default and Weak Passwords u End-user has Admin Privileges u Outdated Software Versions u Non-Hardened Configurations => Flaws in System Administration #RSAC 6
Solution u 20 Critical Security Controls u What works in Security? #RSAC 7
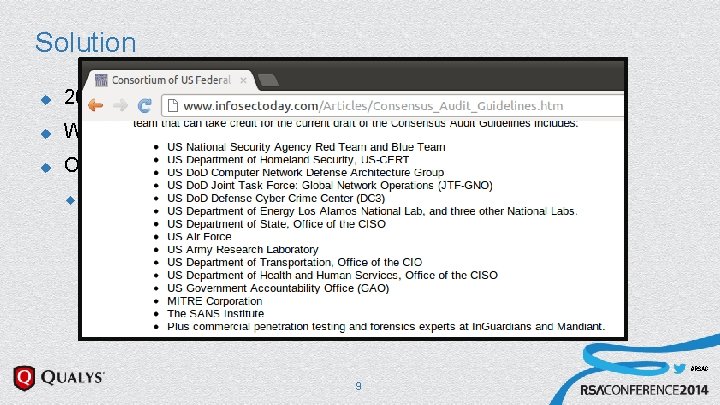
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input #RSAC 8
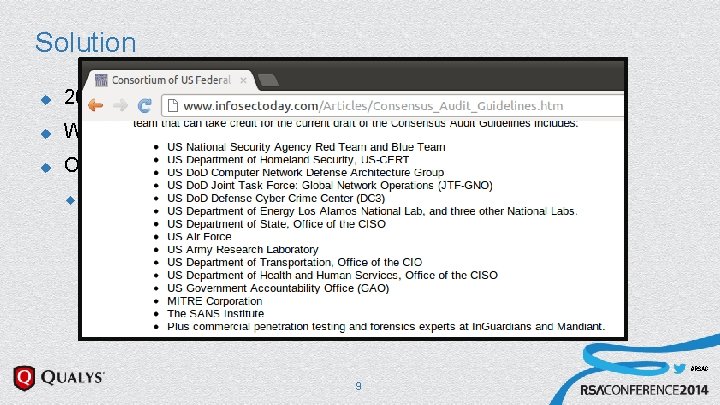
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industryexpert input #RSAC 9
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input u International Participation #RSAC 10
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input u International Participation #RSAC 11

Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industryexpert input u International Participation #RSAC 12
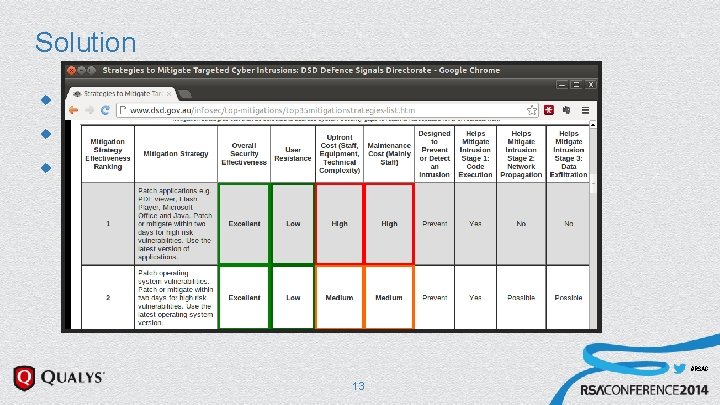
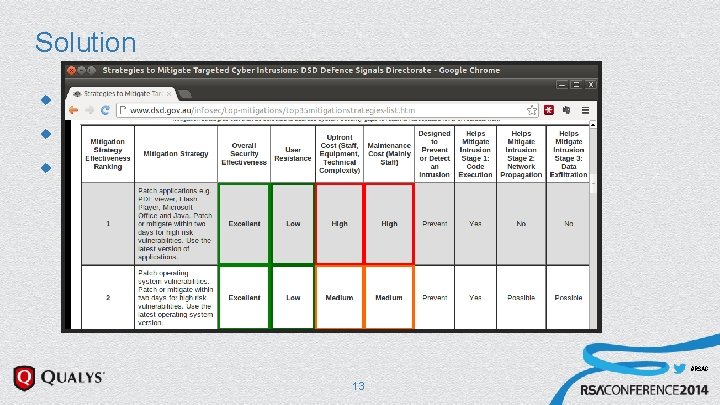
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industryexpert input u International Participation #RSAC 13
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u u With widespread industry expert input u International Participation 5 Tenets #RSAC 14
5 Tenets 20 CSC u Offense informs Defense u Prioritization u Metrics u Continuous Diagnostics and Mitigation u Automation #RSAC 15
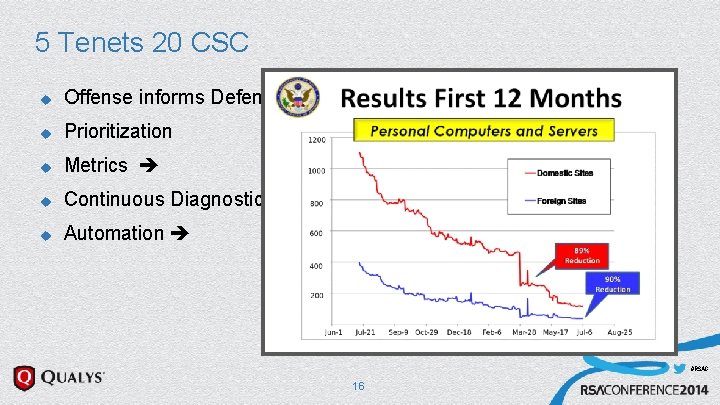
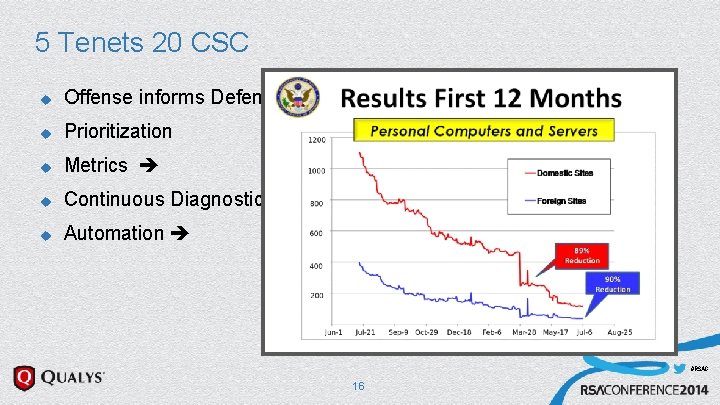
5 Tenets 20 CSC u Offense informs Defense u Prioritization u Metrics u Continuous Diagnostics and Mitigation u Automation #RSAC 16
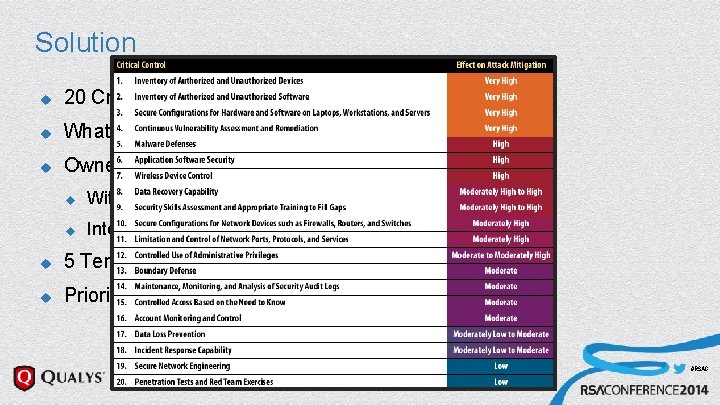
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input u International Participation u 5 Tenets u Prioritized #RSAC 17
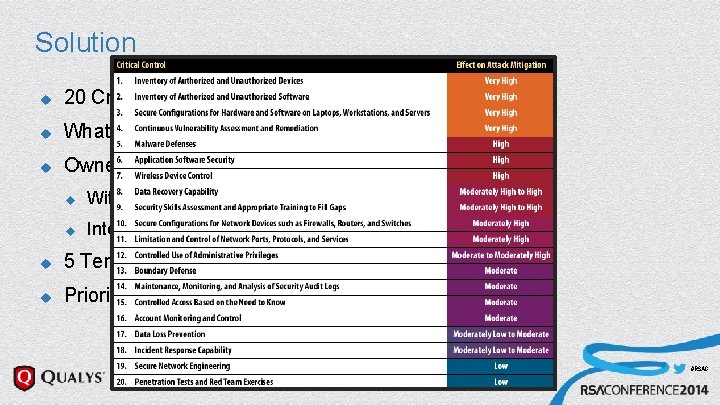
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input u International Participation u 5 Tenets u Prioritized #RSAC 18
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input u International Participation u 5 Tenets u Prioritized u Implementation Guidelines #RSAC 19
Solution u 20 Critical Security Controls u What works in Security? u Owned by the Council on Cybersecurity u With widespread industry expert input u International Participation u 5 Tenets u Prioritized u Implementation Guidelines = Quick Wins, Visibility/Attribution, Configuration/Hygiene, Advanced 20 #RSAC
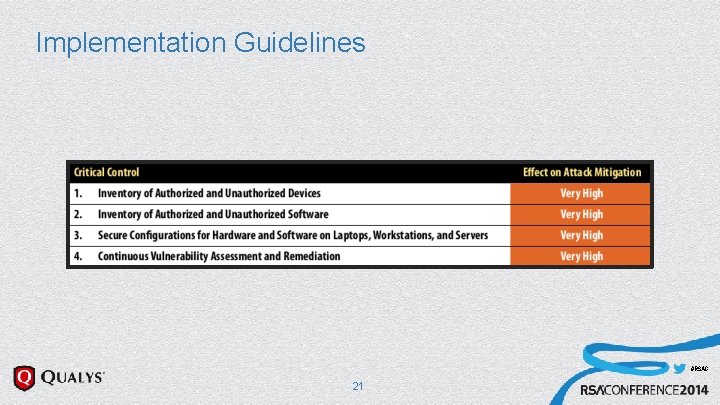
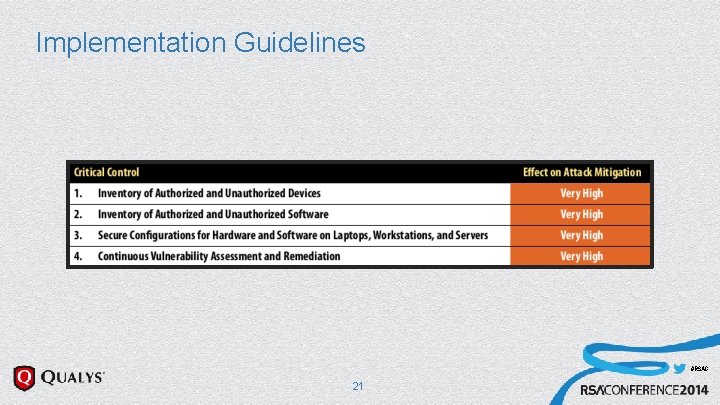
Implementation Guidelines #RSAC 21
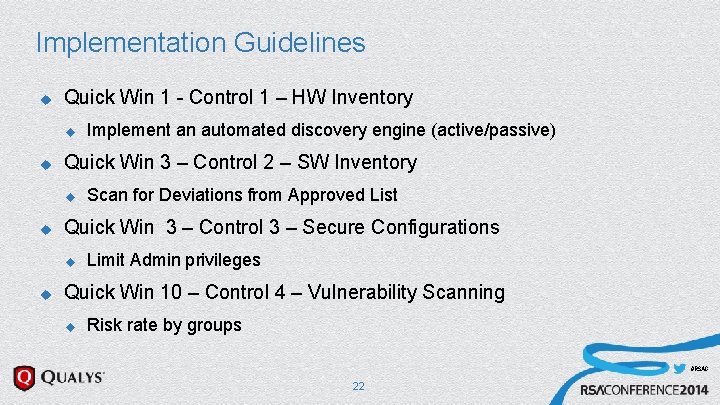
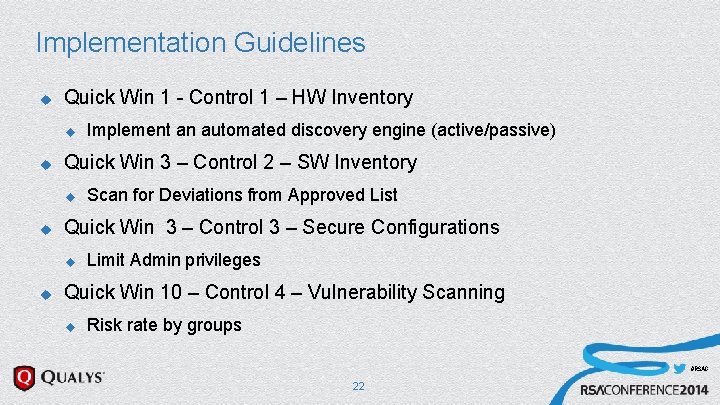
Implementation Guidelines u Quick Win 1 - Control 1 – HW Inventory u u Quick Win 3 – Control 2 – SW Inventory u u Scan for Deviations from Approved List Quick Win 3 – Control 3 – Secure Configurations u u Implement an automated discovery engine (active/passive) Limit Admin privileges Quick Win 10 – Control 4 – Vulnerability Scanning u Risk rate by groups #RSAC 22
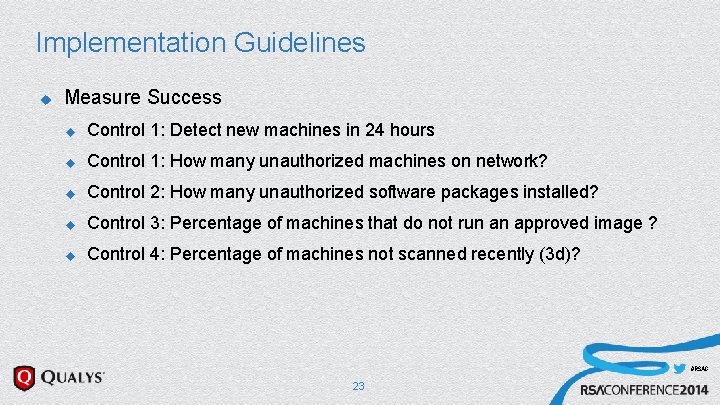
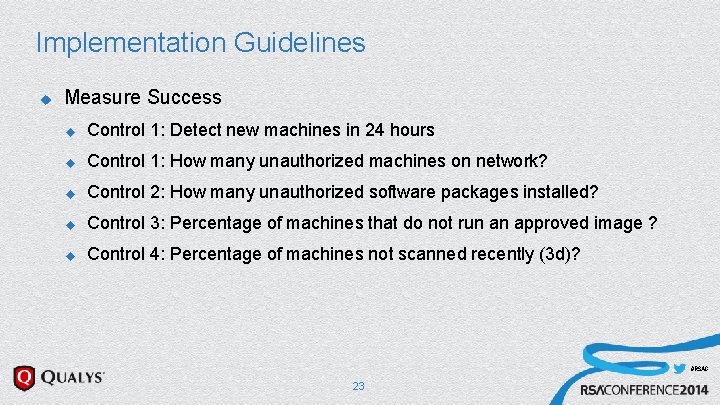
Implementation Guidelines u Measure Success u Control 1: Detect new machines in 24 hours u Control 1: How many unauthorized machines on network? u Control 2: How many unauthorized software packages installed? u Control 3: Percentage of machines that do not run an approved image ? u Control 4: Percentage of machines not scanned recently (3 d)? #RSAC 23
Implementing Quick Wins - Prototype u Qualys. Guard, API, PERL, Splunk u Daily Authenticated Scan of Network u Scripted API Access and Load #RSAC 24
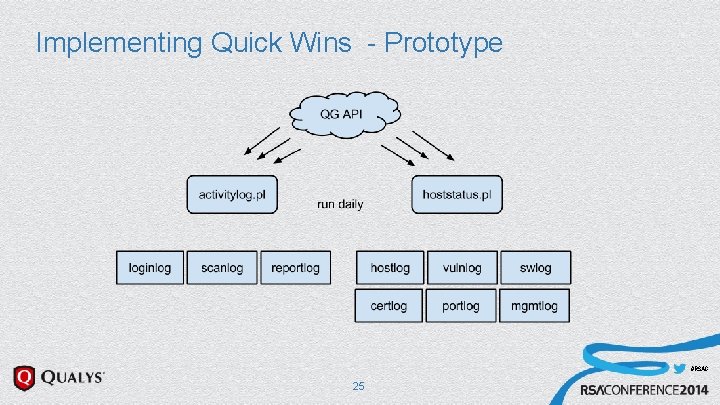
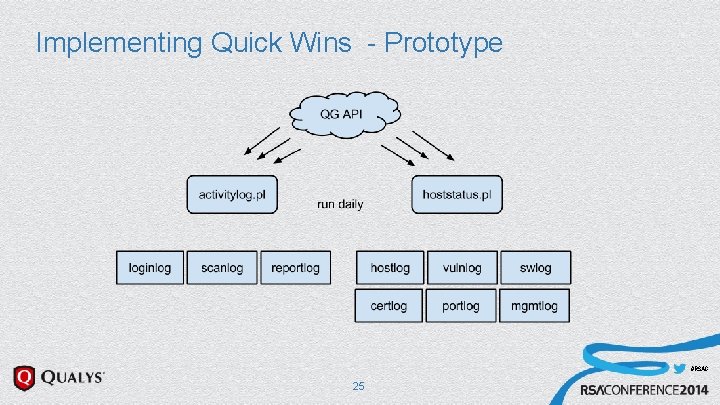
Implementing Quick Wins - Prototype #RSAC 25
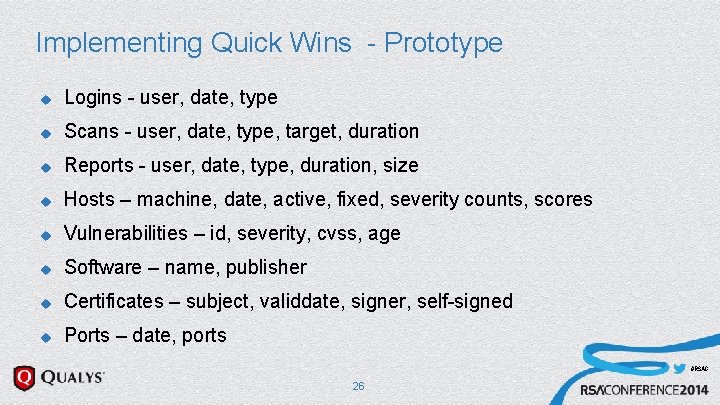
Implementing Quick Wins - Prototype u Logins - user, date, type u Scans - user, date, type, target, duration u Reports - user, date, type, duration, size u Hosts – machine, date, active, fixed, severity counts, scores u Vulnerabilities – id, severity, cvss, age u Software – name, publisher u Certificates – subject, validdate, signer, self-signed u Ports – date, ports #RSAC 26
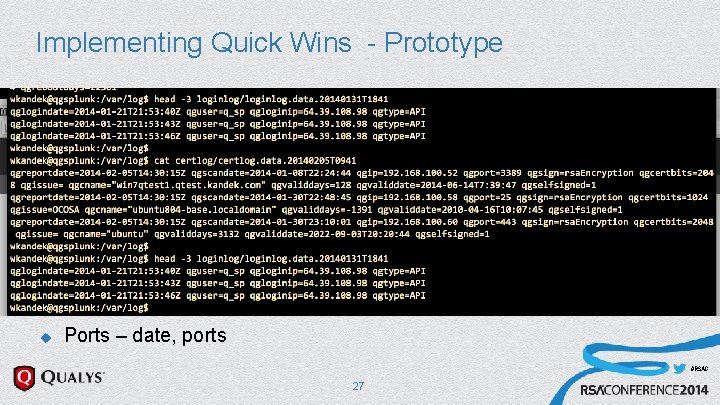
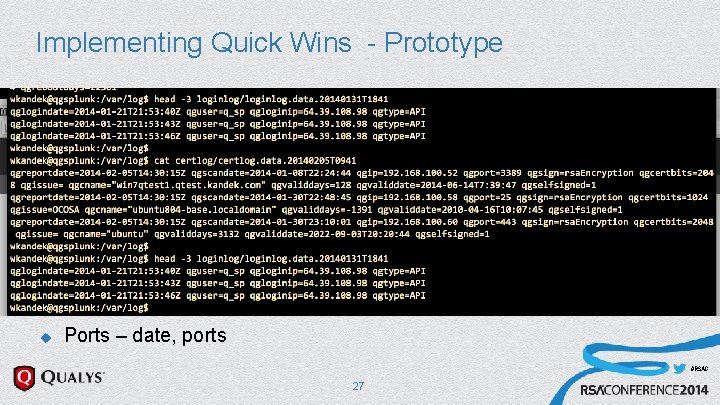
Implementing Quick Wins - Prototype u Logins - user, date, type u Scans - user, date, type, target, duration u Reports - user, date, type, duration, size u Hosts – machine, date, active, fixed, severity counts, scores u Vulnerabilities – id, severity, cvss, age u Software – name, publisher u Certificates – subject, validdate, signer, self-signed u Ports – date, ports #RSAC 27
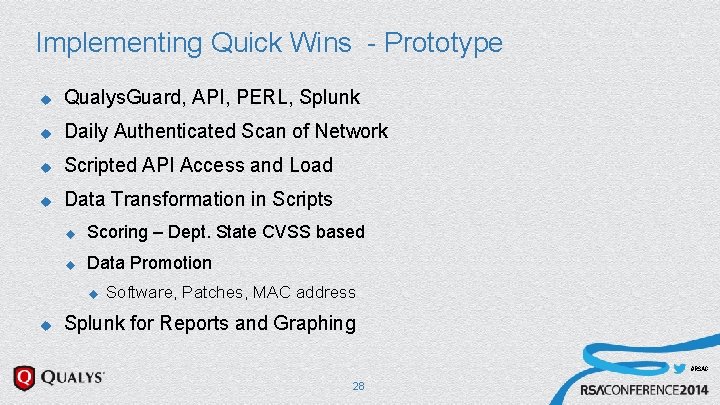
Implementing Quick Wins - Prototype u Qualys. Guard, API, PERL, Splunk u Daily Authenticated Scan of Network u Scripted API Access and Load u Data Transformation in Scripts u Scoring – Dept. State CVSS based u Data Promotion u u Software, Patches, MAC address Splunk for Reports and Graphing #RSAC 28
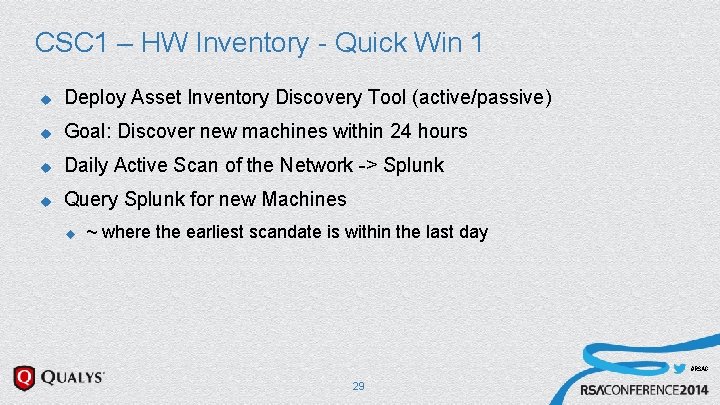
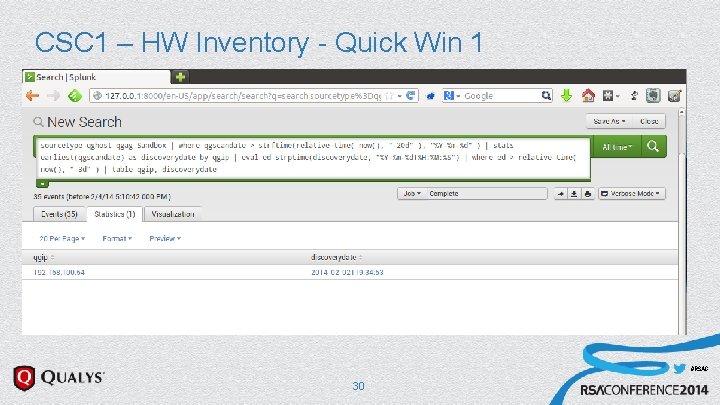
CSC 1 – HW Inventory - Quick Win 1 u Deploy Asset Inventory Discovery Tool (active/passive) u Goal: Discover new machines within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for new Machines u ~ where the earliest scandate is within the last day #RSAC 29
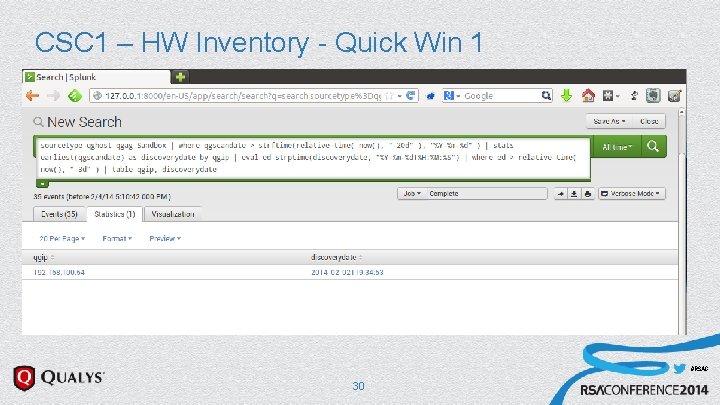
CSC 1 – HW Inventory - Quick Win 1 u Asset Inventory Discovery Tool (active/passive) u Discover new machines within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for new Machines #RSAC 30
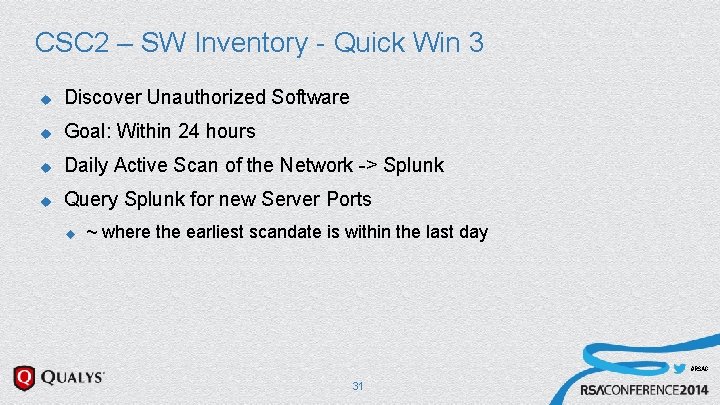
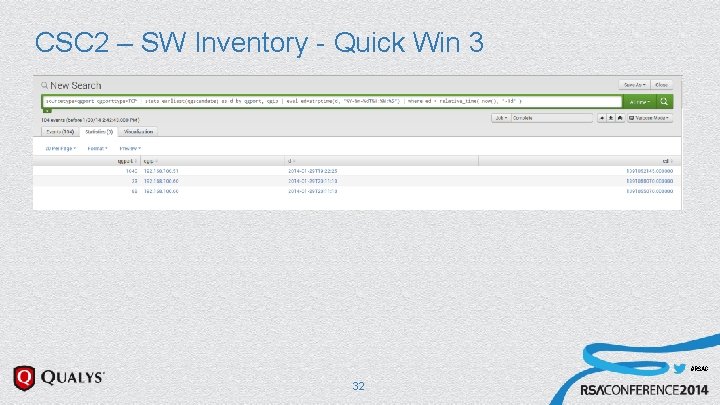
CSC 2 – SW Inventory - Quick Win 3 u Discover Unauthorized Software u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for new Server Ports u ~ where the earliest scandate is within the last day #RSAC 31
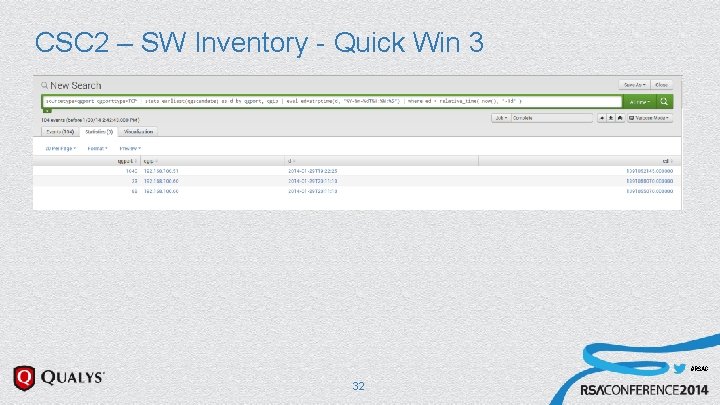
CSC 2 – SW Inventory - Quick Win 3 u Discover Unauthorized Software u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk #RSAC 32
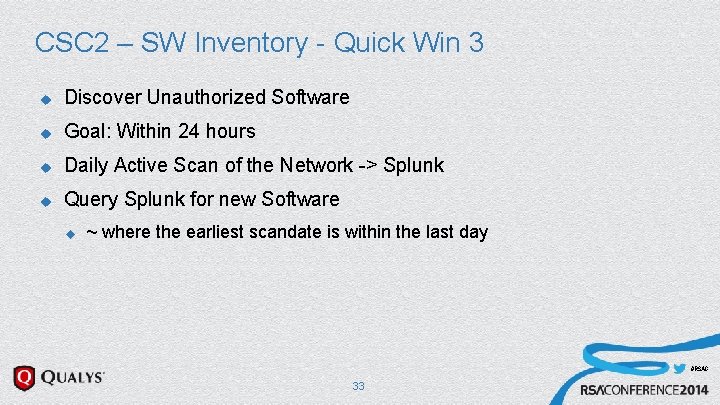
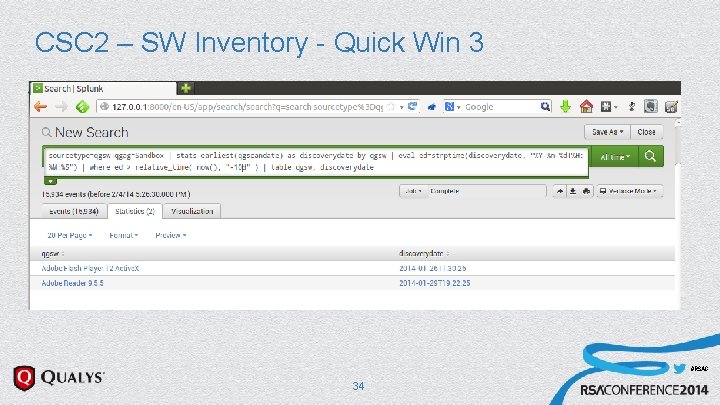
CSC 2 – SW Inventory - Quick Win 3 u Discover Unauthorized Software u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for new Software u ~ where the earliest scandate is within the last day #RSAC 33
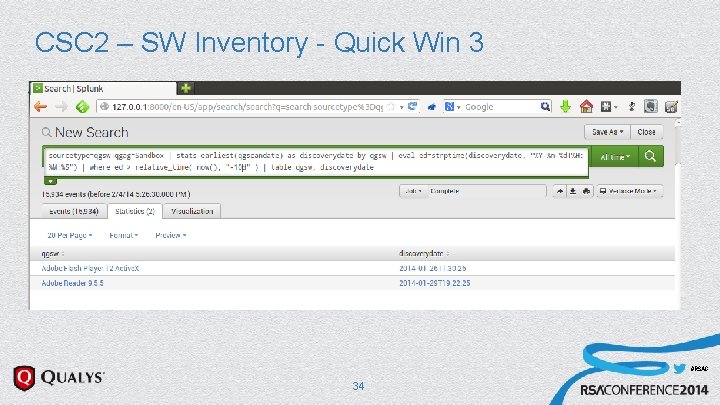
CSC 2 – SW Inventory - Quick Win 3 u Discover Unauthorized Software u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for new Server Ports u u ~ where the earliest scandate is within the last day Query Splunk for new Software #RSAC 34
CSC 2 – SW Inventory - Quick Win 3 u Discover Unauthorized Software u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for new Software u u ~ where the earliest scandate is within the last day Can be Alerted On #RSAC 35
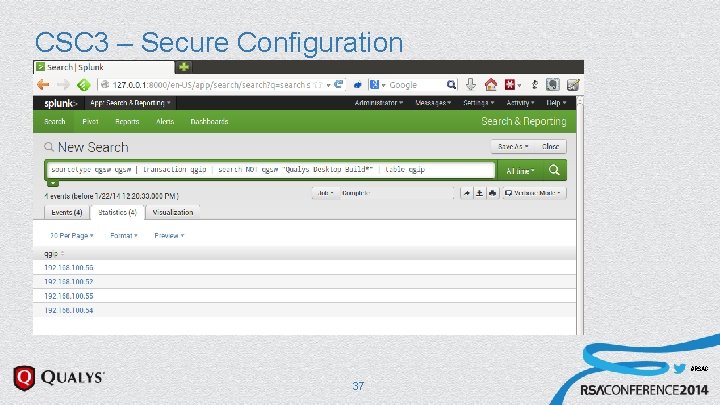
CSC 3 – Secure Configuration u Automation: Discover Non Standard Setups u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for certain Software. Marker u Here: “Qualys Desktop Build” – which is a custom SW package that identifies our IT standard builds #RSAC 36
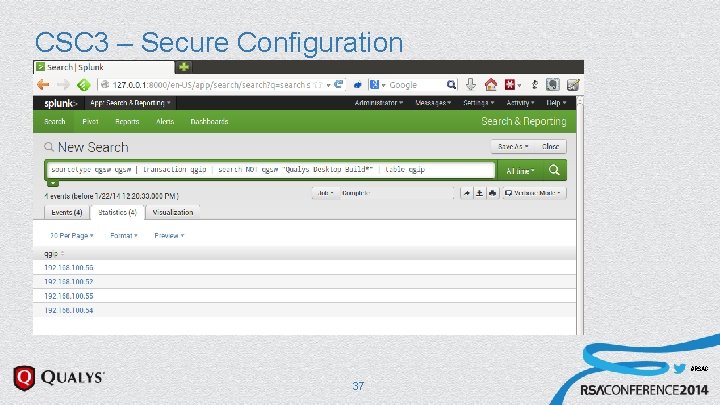
CSC 3 – Secure Configuration u Automation: Discover Non Standard Setups u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for certain Software. Marker u Here: “Qualys Desktop Build” – which is a custom SW packag that identifies out IT standard builds #RSAC 37
CSC 3 – Secure Configuration u Automation: Discover Non Standard Setups u Goal: Within 24 hours u Daily Active Scan of the Network -> Splunk u Query Splunk for certain Software Marker u u Here: “Qualys Desktop Build” – which is a custom SW package that identifies out IT standard builds Can be Alerted On #RSAC 38
Further Uses and Projects u Plot Progress for a Machine #RSAC 39
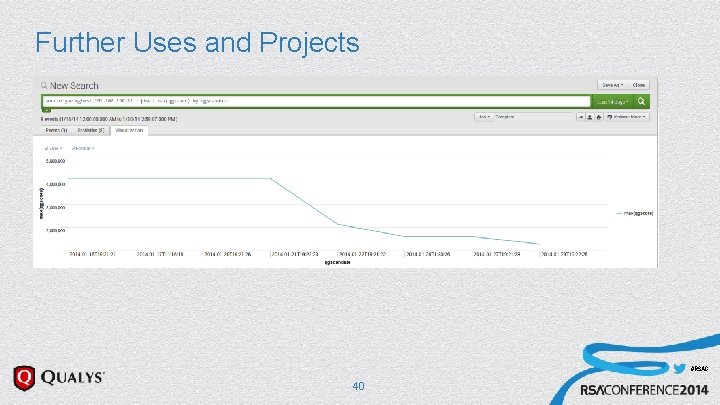
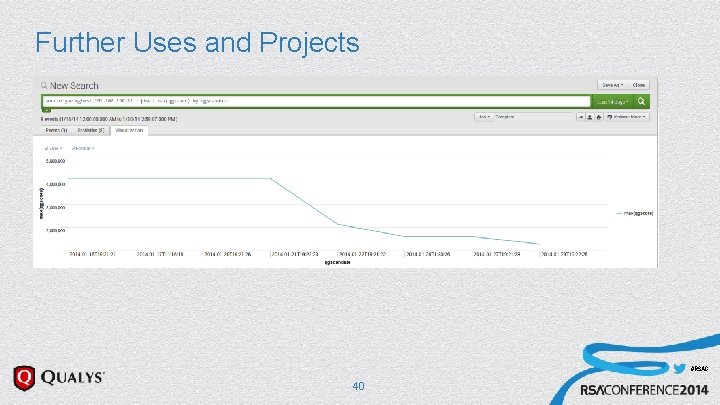
Further Uses and Projects u Plot Progress for a Machine #RSAC 40
Further Uses and Projects u Plot Progress for a Machine u Plot Progress for a Network #RSAC 41
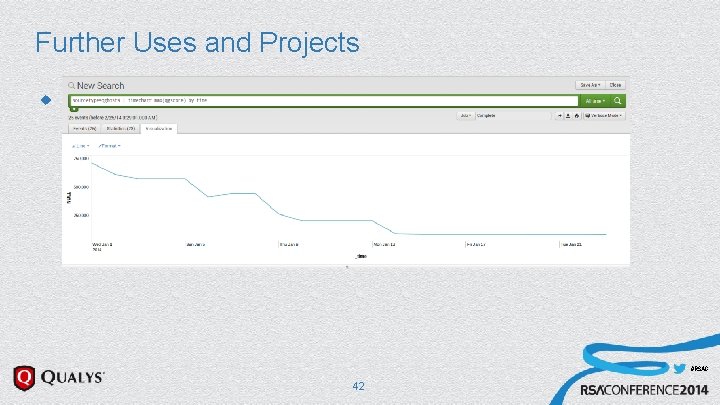
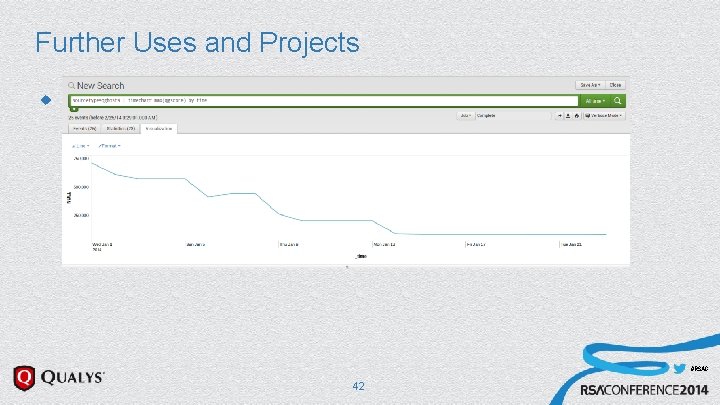
Further Uses and Projects u Plot Progress for a Machine #RSAC 42
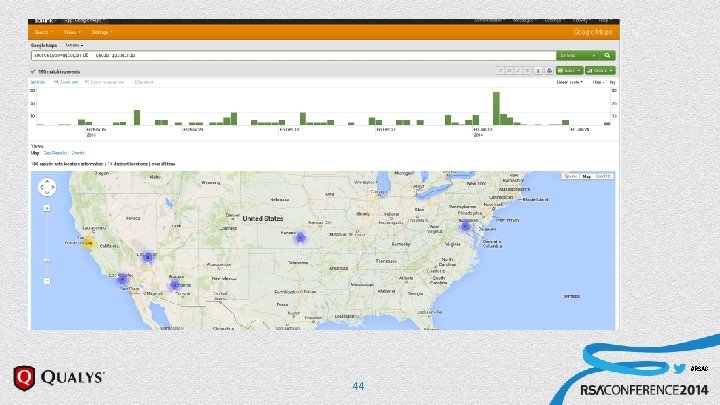
Other Operational Reports u Usage Reporting u User Logins u API Logins u Reports u Anomaly Detection u Geo. IP #RSAC 43
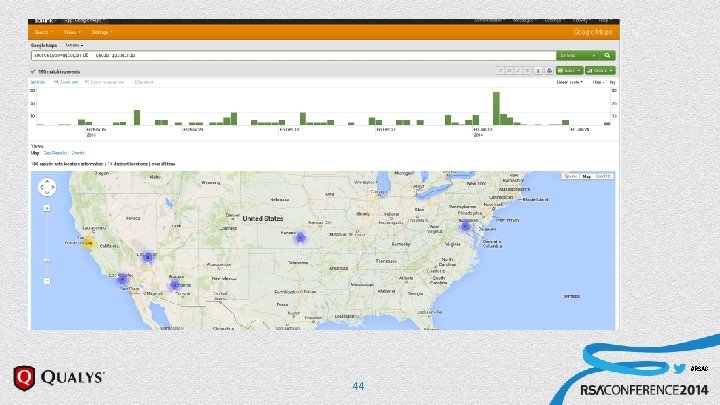
Other Operational Reports u Usage Reporting u User Logins u API Logins u Reports u Anomaly Detection u Geo. IP #RSAC 44
Beyond Prototyping u Continuous Monitoring u Alert on Additions & Changes u u Machines u Vulnerabilities u Ports u Certificates Simple Configuration #RSAC 45
Questions? wkandek@qualys. com @wkandek http: //laws. qualys. com