CONNECTING THE DOTS FROM BUSINESS ARCHITECTURE TO IT
CONNECTING THE DOTS: FROM BUSINESS ARCHITECTURE TO IT NUTS AND BOLTS Dave Goiffon, Enterprise Architect The Business Architecture Summit December 1, 2016 Confidential and proprietary. Blue Cross® and Blue Shield ® of Minnesota and Blue Plus ® are nonprofit independent licensees of the Blue Cross and Blue Shield Association.
PRESENTATION GOAL IS TO SHOW: The progression • from using business architecture for planning major business transformations • to using whole IT lifecycle management for implementing IT changes to enable major business transformations • by tightly coupling business architecture to physical applications, components and infrastructure. Confidential and proprietary.
CONTENTS • Background • Business Capability Planning Framework • Business Capability Model and Capability Application Model • Capability Model transformation analysis tools • Physical applications* and IT configuration management • Mapping business architecture to physical applications and configurations • Forecasting and tracking application and component lifecycle changes * Hosted in our data center, not in the Cloud. Confidential and proprietary.
BACKGROUND: FRAMEWORKS WITH TOP-BOTTOM AND BOTTOM-TOP MAPS • • • NIST Enterprise Architecture Model - 1989 Zachman Framework for Enterprise Architecture - 1992 Department of Defense (Do. D) Architecture Framework (Do. DAF) - 1995 The Open Group Architecture Framework (TOGAF) - 1995 Federal Enterprise Architecture Framework - 1999 Confidential and proprietary. 4
BACKGROUND: BCBSMN • Origins of the company go back to the early 1930’s in St. Paul • Information technology at Blue Cross Blue Shield began in late 1950’s • Information systems and infrastructure (“IT”) incrementally grew and evolved in proportion to company growth and change • Optimizing business operations became a high priority in 2014 • Multiple year program to enable support of new business strategies • Usual incremental operating performance and platform improvements could limit planned business changes • Realizing this goal requires EXTENSIVE architecture-IT top-bottom & bottom-top Confidential and proprietary. 5
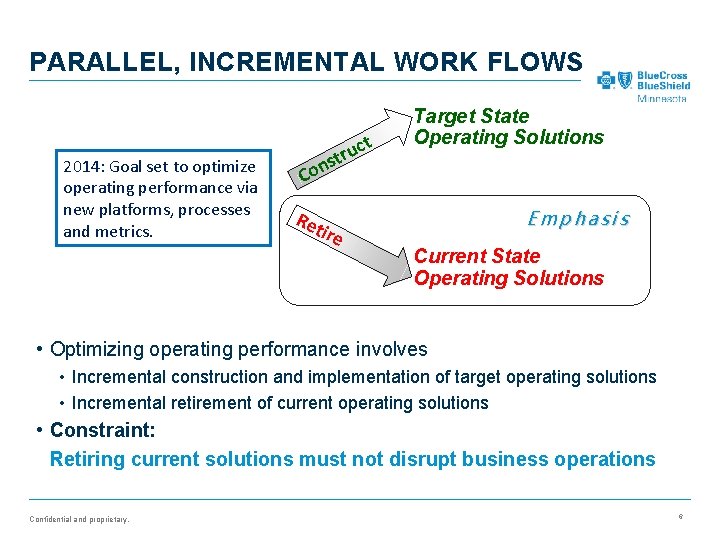
PARALLEL, INCREMENTAL WORK FLOWS 2014: Goal set to optimize operating performance via new platforms, processes and metrics. t uc r t s Con Target State Operating Solutions Emphasis Ret ire Current State Operating Solutions • Optimizing operating performance involves • Incremental construction and implementation of target operating solutions • Incremental retirement of current operating solutions • Constraint: Retiring current solutions must not disrupt business operations Confidential and proprietary. 6
CONTENTS • Background • Business Capability Planning Framework • Business Capability Model and Capability Application Model • Capability Model transformation analysis tools • Physical applications and IT configuration management • Mapping business architecture to physical applications and configurations • Forecasting and tracking application and component lifecycle changes Confidential and proprietary.
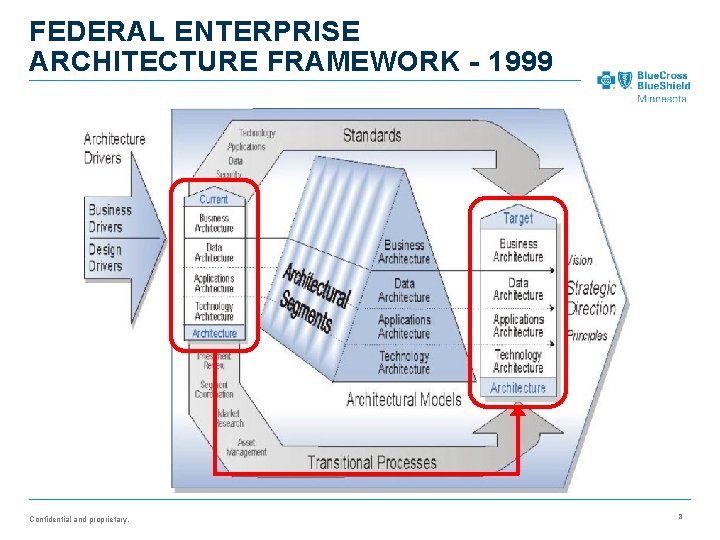
FEDERAL ENTERPRISE ARCHITECTURE FRAMEWORK - 1999 Confidential and proprietary. 8
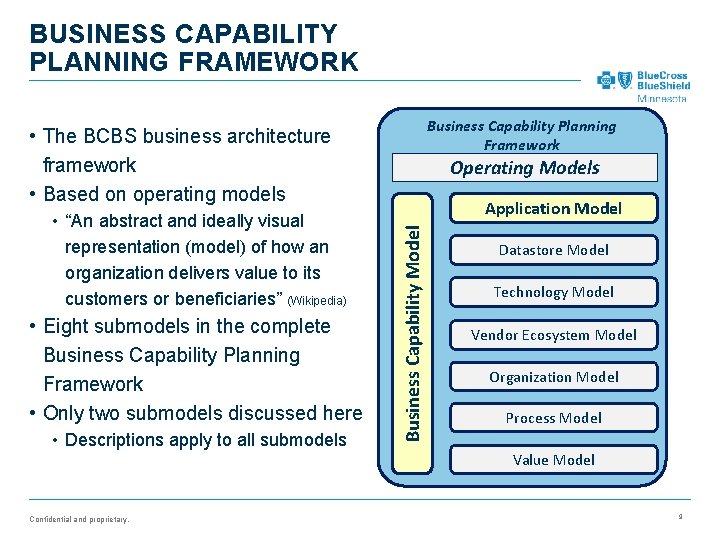
BUSINESS CAPABILITY PLANNING FRAMEWORK Business Capability Planning Framework • The BCBS business architecture framework • Based on operating models • Eight submodels in the complete Business Capability Planning Framework • Only two submodels discussed here • Descriptions apply to all submodels Confidential and proprietary. Application Model Business Capability Model • “An abstract and ideally visual representation (model) of how an organization delivers value to its customers or beneficiaries” (Wikipedia) Operating Models Datastore Model Technology Model Vendor Ecosystem Model Organization Model Process Model Value Model 9
QUESTIONS ANSWERED BY BUSINESS CAPABILITY PLANNING FRAMEWORK 1. As a company, what business capabilities do we have? Confidential and proprietary. 10
BUSINESS CAPABILITY PLANNING FRAMEWORK Business Capability Planning Framework Business Capability Model Operating Models Confidential and proprietary. 11
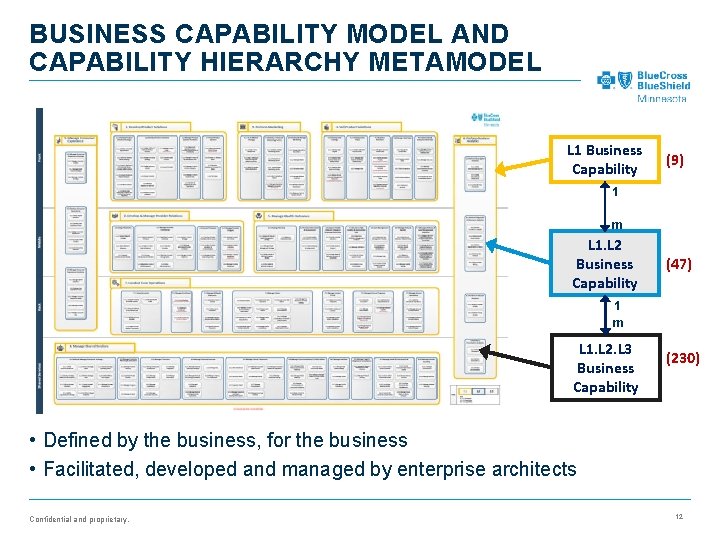
BUSINESS CAPABILITY MODEL AND CAPABILITY HIERARCHY METAMODEL L 1 Business Capability (9) 1 m L 1. L 2 Business Capability (47) 1 m L 1. L 2. L 3 Business Capability (230) • Defined by the business, for the business • Facilitated, developed and managed by enterprise architects Confidential and proprietary. 12
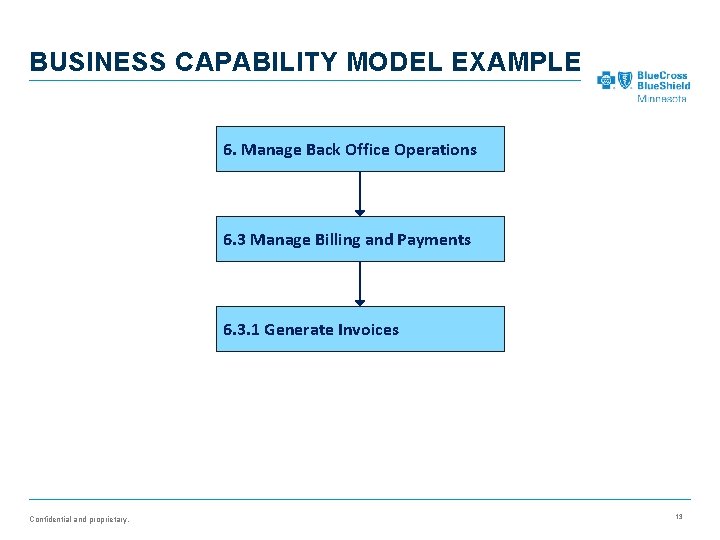
BUSINESS CAPABILITY MODEL EXAMPLE 6. Manage Back Office Operations 6. 3 Manage Billing and Payments 6. 3. 1 Generate Invoices Confidential and proprietary. 13
QUESTIONS ANSWERED BY BUSINESS CAPABILITY PLANNING FRAMEWORK 1. As a company, what business capabilities do we have? 2. What applications enable business capabilities to operate? • Current Application Model and Target Application Model Confidential and proprietary. 14
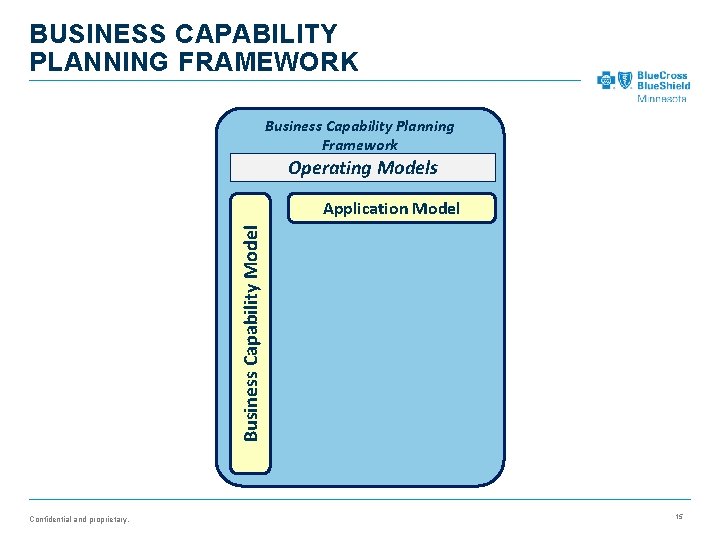
BUSINESS CAPABILITY PLANNING FRAMEWORK Business Capability Planning Framework Operating Models Business Capability Model Application Model Confidential and proprietary. 15
OPERATING MODEL LAYER: APPLICATION MODEL Confidential and proprietary. 16
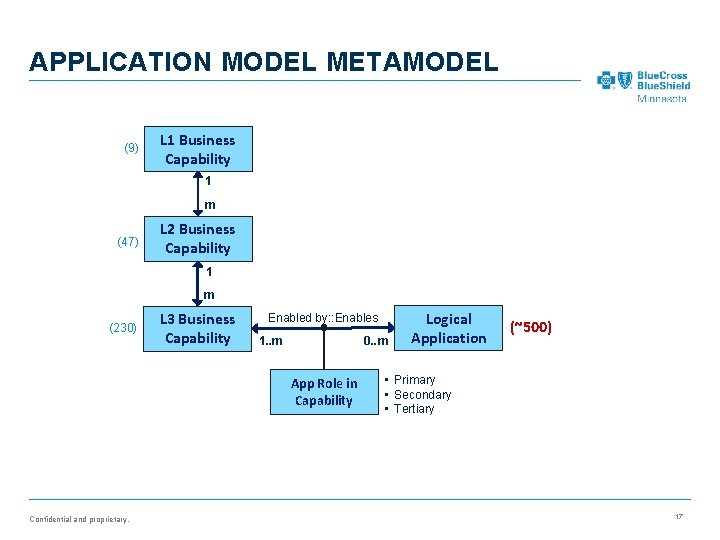
APPLICATION MODEL METAMODEL (9) L 1 Business Capability 1 m (47) L 2 Business Capability 1 m (230) L 3 Business Capability Enabled by: : Enables 0. . m 1. . m App Role in Capability Confidential and proprietary. Logical Application (~500) • Primary • Secondary • Tertiary 17
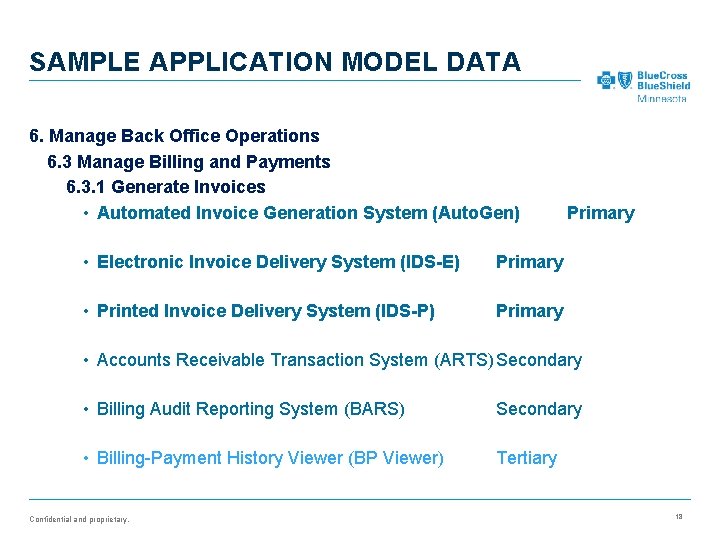
SAMPLE APPLICATION MODEL DATA 6. Manage Back Office Operations 6. 3 Manage Billing and Payments 6. 3. 1 Generate Invoices • Automated Invoice Generation System (Auto. Gen) • Electronic Invoice Delivery System (IDS-E) Primary • Printed Invoice Delivery System (IDS-P) Primary • Accounts Receivable Transaction System (ARTS)Secondary • Billing Audit Reporting System (BARS) Secondary • Billing-Payment History Viewer (BP Viewer) Tertiary Confidential and proprietary. 18
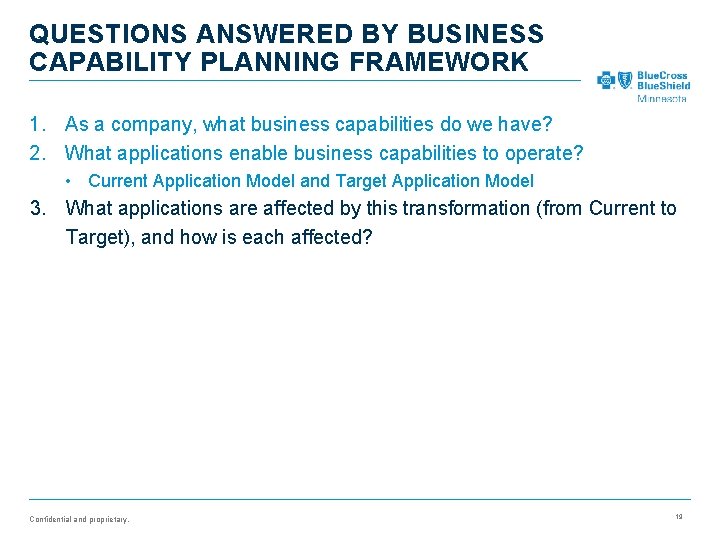
QUESTIONS ANSWERED BY BUSINESS CAPABILITY PLANNING FRAMEWORK 1. As a company, what business capabilities do we have? 2. What applications enable business capabilities to operate? • Current Application Model and Target Application Model 3. What applications are affected by this transformation (from Current to Target), and how is each affected? Confidential and proprietary. 19
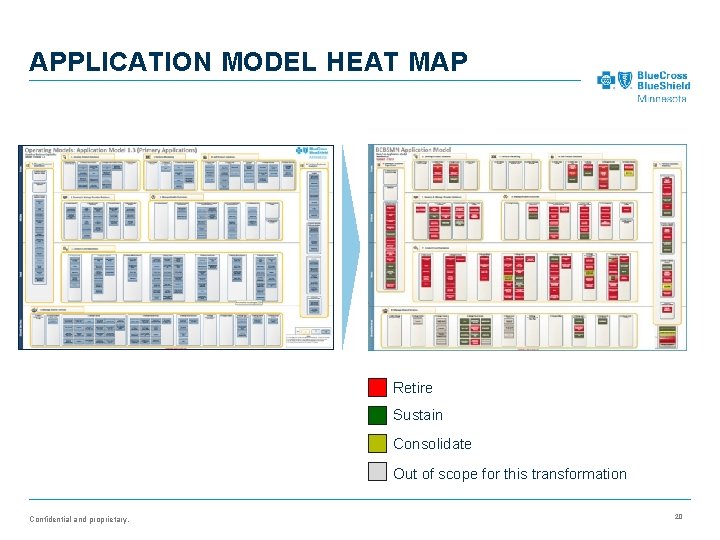
APPLICATION MODEL HEAT MAP Retire Sustain Consolidate Out of scope for this transformation Confidential and proprietary. 20
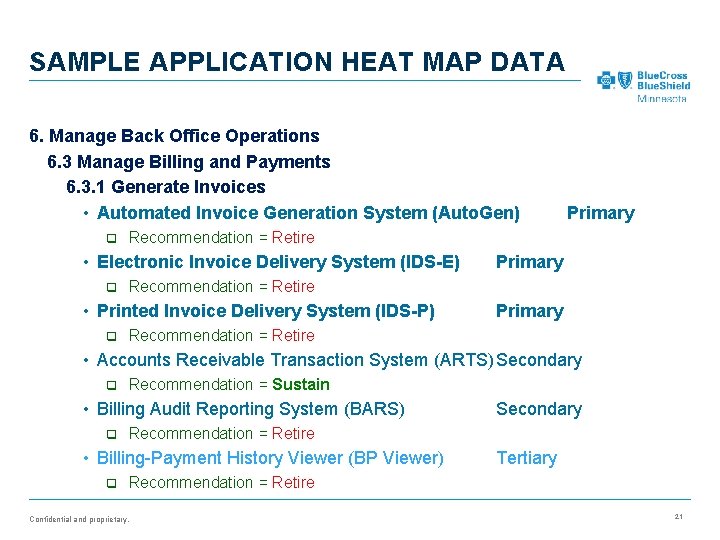
SAMPLE APPLICATION HEAT MAP DATA 6. Manage Back Office Operations 6. 3 Manage Billing and Payments 6. 3. 1 Generate Invoices • Automated Invoice Generation System (Auto. Gen) q Recommendation = Retire • Electronic Invoice Delivery System (IDS-E) q Primary Recommendation = Retire • Printed Invoice Delivery System (IDS-P) q Primary Recommendation = Retire • Accounts Receivable Transaction System (ARTS)Secondary q Recommendation = Sustain • Billing Audit Reporting System (BARS) q Recommendation = Retire • Billing-Payment History Viewer (BP Viewer) q Secondary Tertiary Recommendation = Retire Confidential and proprietary. 21
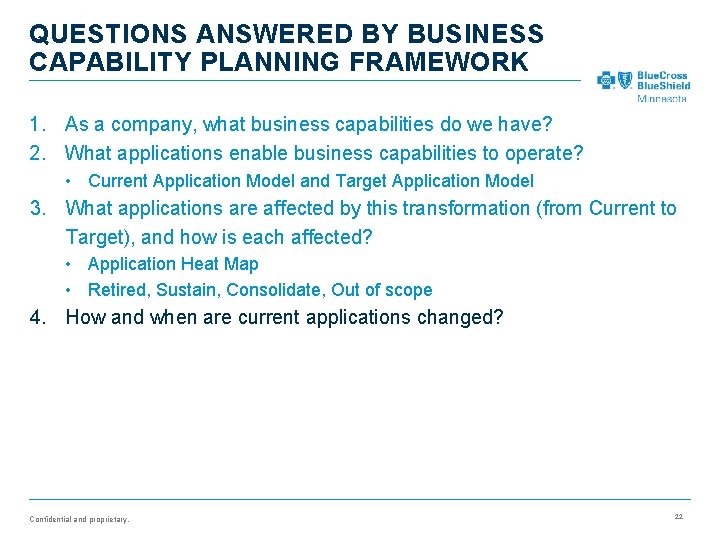
QUESTIONS ANSWERED BY BUSINESS CAPABILITY PLANNING FRAMEWORK 1. As a company, what business capabilities do we have? 2. What applications enable business capabilities to operate? • Current Application Model and Target Application Model 3. What applications are affected by this transformation (from Current to Target), and how is each affected? • Application Heat Map • Retired, Sustain, Consolidate, Out of scope 4. How and when are current applications changed? Confidential and proprietary. 22
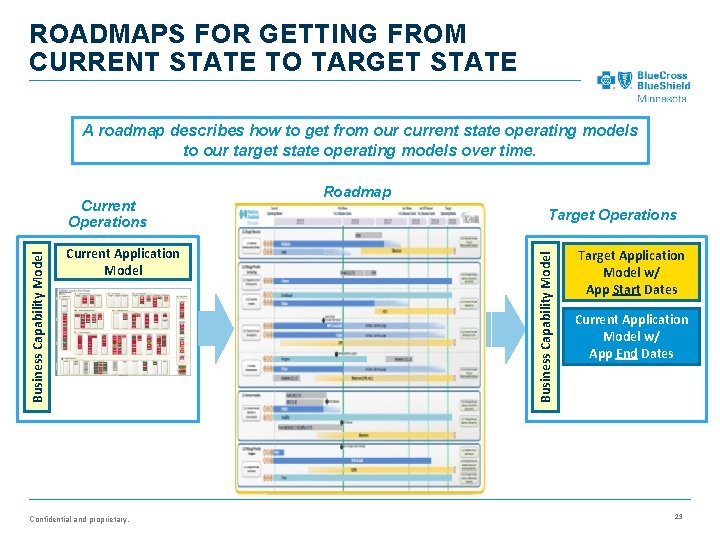
ROADMAPS FOR GETTING FROM CURRENT STATE TO TARGET STATE A roadmap describes how to get from our current state operating models to our target state operating models over time. Current Application Model Confidential and proprietary. Roadmap Target Operations Business Capability Model Current Operations Target Application Model w/ App Start Dates Current Application Model w/ App End Dates 23
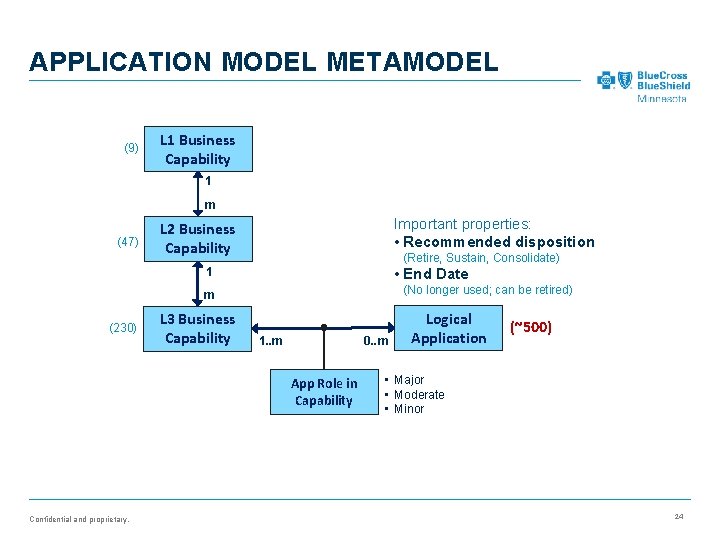
APPLICATION MODEL METAMODEL (9) L 1 Business Capability 1 m (47) Important properties: • Recommended disposition L 2 Business Capability (Retire, Sustain, Consolidate) 1 • End Date (No longer used; can be retired) m (230) L 3 Business Capability 0. . m 1. . m App Role in Capability Confidential and proprietary. Logical Application (~500) • Major • Moderate • Minor 24
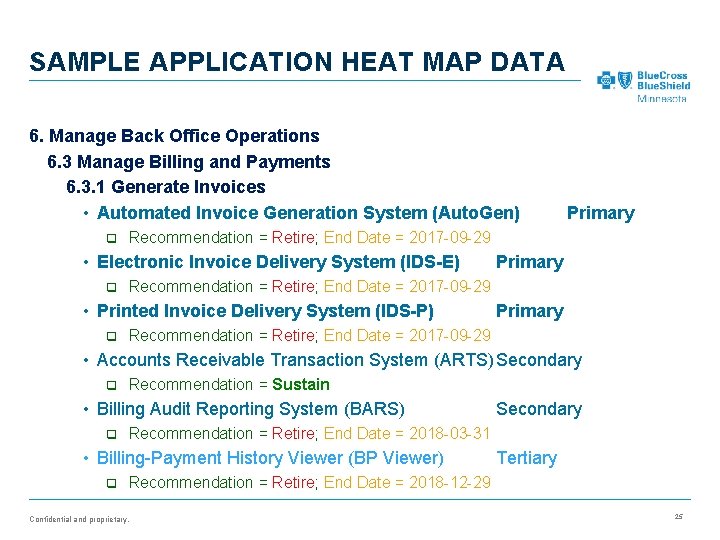
SAMPLE APPLICATION HEAT MAP DATA 6. Manage Back Office Operations 6. 3 Manage Billing and Payments 6. 3. 1 Generate Invoices • Automated Invoice Generation System (Auto. Gen) q Recommendation = Retire; End Date = 2017 -09 -29 • Electronic Invoice Delivery System (IDS-E) q Primary Recommendation = Retire; End Date = 2017 -09 -29 • Printed Invoice Delivery System (IDS-P) q Primary Recommendation = Retire; End Date = 2017 -09 -29 • Accounts Receivable Transaction System (ARTS)Secondary q Recommendation = Sustain • Billing Audit Reporting System (BARS) q Recommendation = Retire; End Date = 2018 -03 -31 • Billing-Payment History Viewer (BP Viewer) q Secondary Tertiary Recommendation = Retire; End Date = 2018 -12 -29 Confidential and proprietary. 25
CONTENTS • Background • Business Capability Planning Framework • Business Capability Model and Capability Application Model • Capability Model transformation analysis tools • Physical applications and IT configuration management • Mapping business architecture to physical applications and configurations • Forecasting and tracking application and component lifecycle changes Confidential and proprietary. 26
FROM PLANS TO EXECUTION Business architecture operating models work very well for planning and communicating • High level, not IT implementation details • Business terms, not IT language • Logical, not physical However IT cannot execute on operating models • IT needs to know the implemented details • Logical applications need to be mapped to physical applications • Plans for logical applications need to be transferred to physical applications Confidential and proprietary. 27
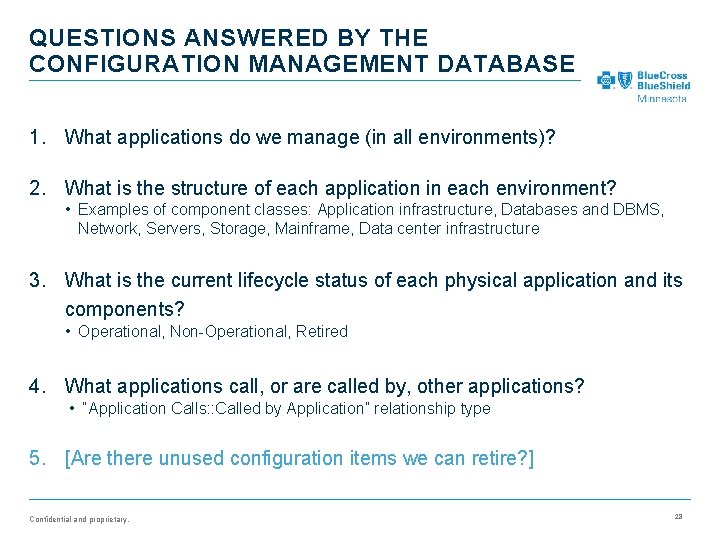
QUESTIONS ANSWERED BY THE CONFIGURATION MANAGEMENT DATABASE 1. What applications do we manage (in all environments)? 2. What is the structure of each application in each environment? • Examples of component classes: Application infrastructure, Databases and DBMS, Network, Servers, Storage, Mainframe, Data center infrastructure 3. What is the current lifecycle status of each physical application and its components? • Operational, Non-Operational, Retired 4. What applications call, or are called by, other applications? • “Application Calls: : Called by Application” relationship type 5. [Are there unused configuration items we can retire? ] Confidential and proprietary. 28
LESSON LEARNED FROM EARLY LOGICAL-PHYSICAL MAPPING EFFORT The utility value of the logical-physical cross references depends heavily on the of the completeness and accuracy of the physical configuration information in the first place. • Incomplete or inaccurate physical application information • Causes cross reference rework (!) • Increases the risk of disrupting business operations caused by unexpected consequences of undocumented applications or dependencies • Software development and support management needs to make configuration management a priority • Complete and correct application configurations are performance objectives for every app owner and group manager Confidential and proprietary. 29
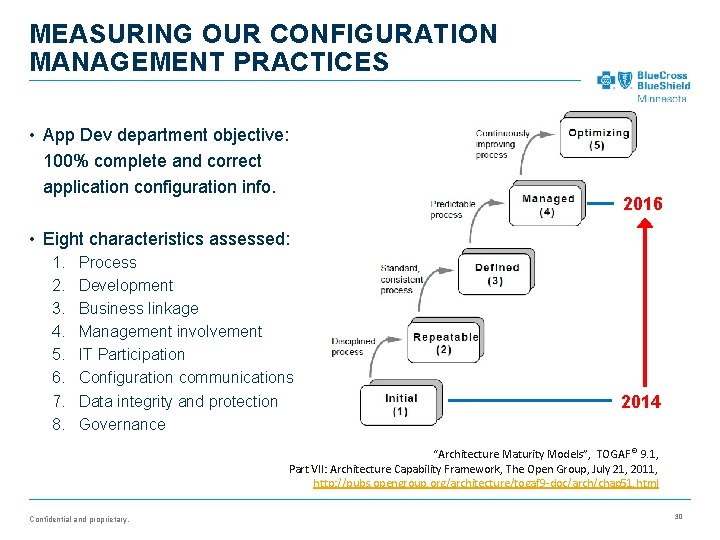
MEASURING OUR CONFIGURATION MANAGEMENT PRACTICES • App Dev department objective: 100% complete and correct application configuration info. 2016 • Eight characteristics assessed: 1. 2. 3. 4. 5. 6. 7. 8. Process Development Business linkage Management involvement IT Participation Configuration communications Data integrity and protection Governance 2014 “Architecture Maturity Models”, TOGAF ® 9. 1, Part VII: Architecture Capability Framework, The Open Group, July 21, 2011, http: //pubs. opengroup. org/architecture/togaf 9 -doc/arch/chap 51. html Confidential and proprietary. 30
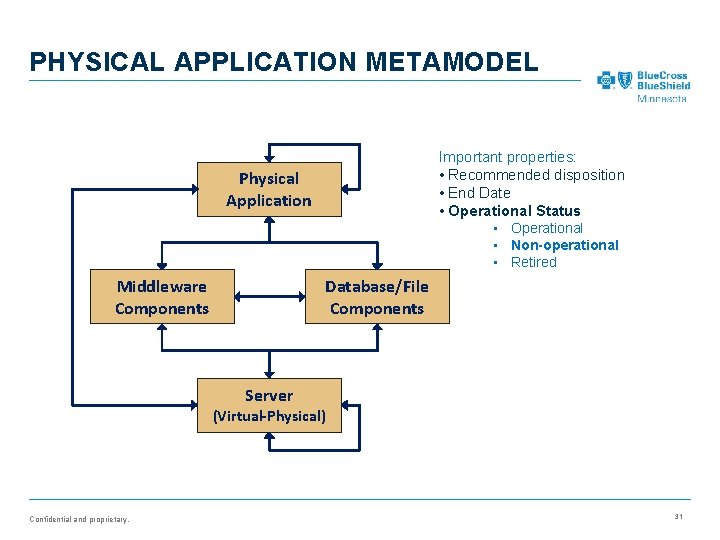
PHYSICAL APPLICATION METAMODEL Important properties: • Recommended disposition • End Date • Operational Status • Operational • Non-operational • Retired Physical Application Middleware Components Database/File Components Server (Virtual-Physical) Confidential and proprietary. 31
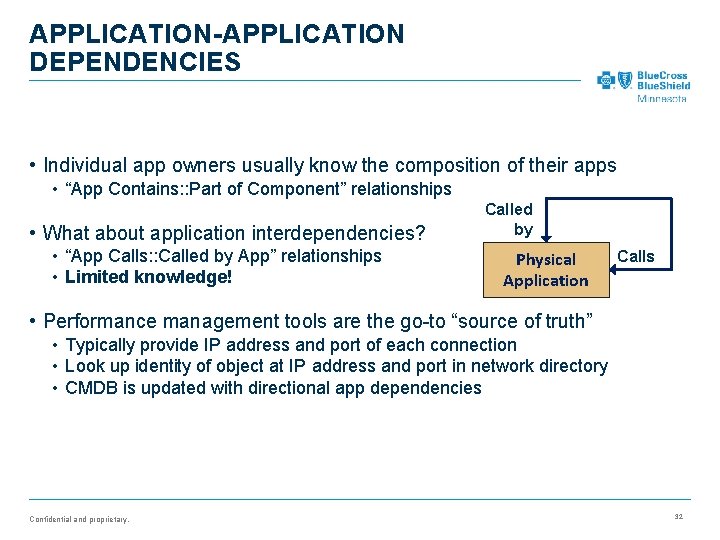
APPLICATION-APPLICATION DEPENDENCIES • Individual app owners usually know the composition of their apps • “App Contains: : Part of Component” relationships • What about application interdependencies? • “App Calls: : Called by App” relationships • Limited knowledge! Called by Physical Application Calls • Performance management tools are the go-to “source of truth” • Typically provide IP address and port of each connection • Look up identity of object at IP address and port in network directory • CMDB is updated with directional app dependencies Confidential and proprietary. 32
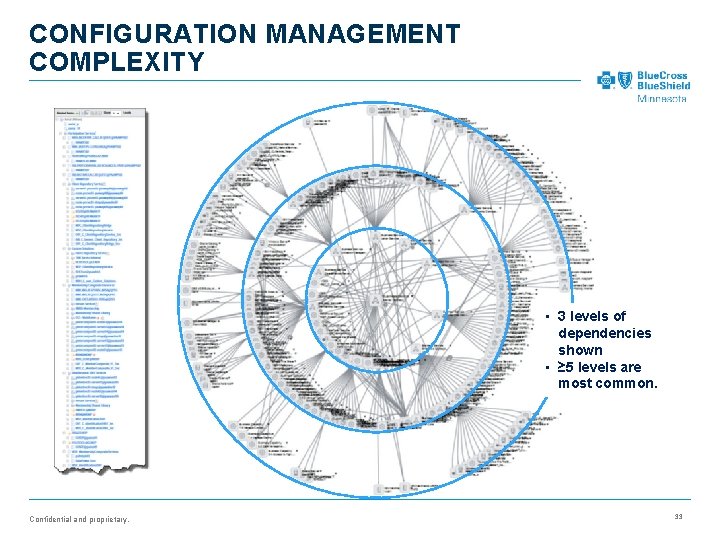
CONFIGURATION MANAGEMENT COMPLEXITY • 3 levels of dependencies shown • ≥ 5 levels are most common. Confidential and proprietary. 33
CONTENTS • Background • Business Capability Planning Framework • Business Capability Model and Capability Application Model • Capability Model transformation analysis tools • Physical applications and IT configuration management • Mapping business architecture to physical applications and configurations • Forecasting and tracking application and component lifecycle changes Confidential and proprietary.
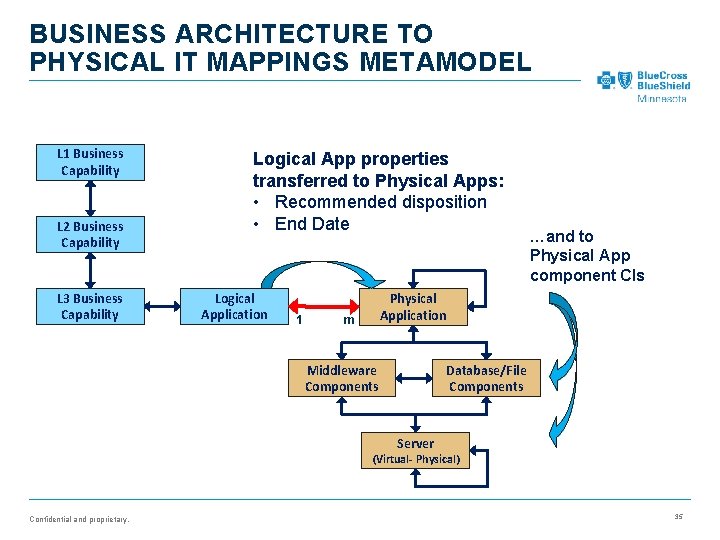
BUSINESS ARCHITECTURE TO PHYSICAL IT MAPPINGS METAMODEL L 1 Business Capability L 2 Business Capability L 3 Business Capability Logical App properties transferred to Physical Apps: • Recommended disposition • End Date Logical Application 1 …and to Physical App component CIs Physical Application m Database/File Components Middleware Components Server (Virtual- Physical) Confidential and proprietary. 35
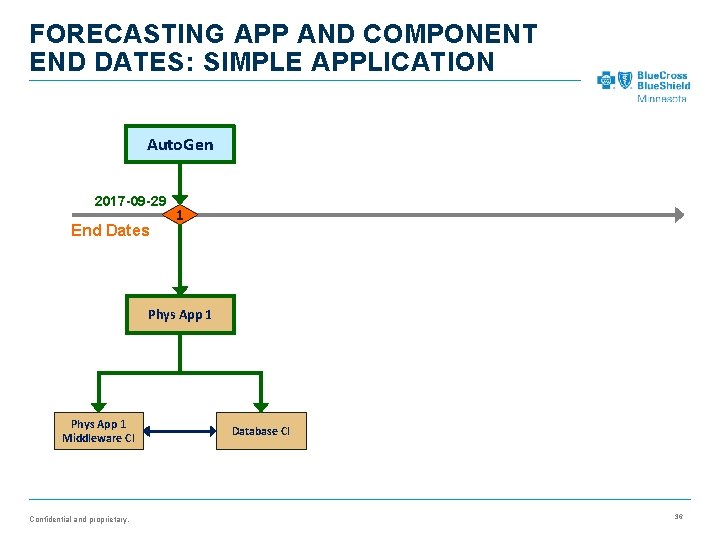
FORECASTING APP AND COMPONENT END DATES: SIMPLE APPLICATION Auto. Gen 2017 -09 -29 End Dates 1 Phys App 1 Middleware CI Confidential and proprietary. Database CI 36
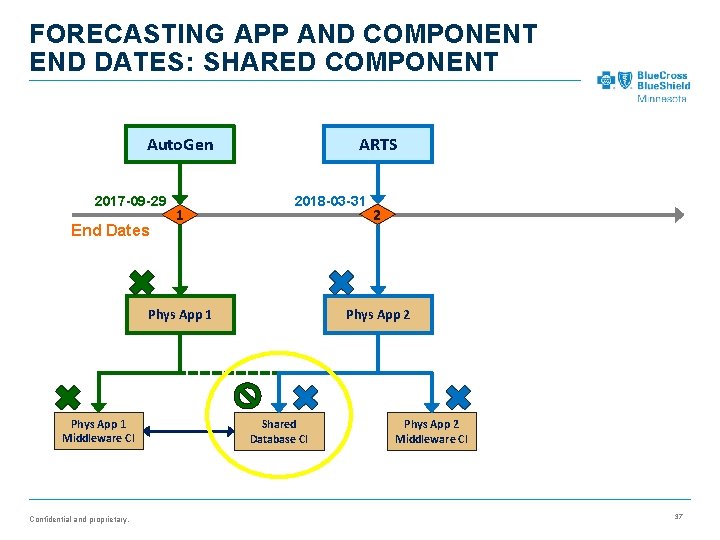
FORECASTING APP AND COMPONENT END DATES: SHARED COMPONENT ARTS Auto. Gen 2017 -09 -29 End Dates 1 2018 -03 -31 Phys App 2 Phys App 1 Middleware CI Confidential and proprietary. 2 Shared Database CI Phys App 2 Middleware CI 37
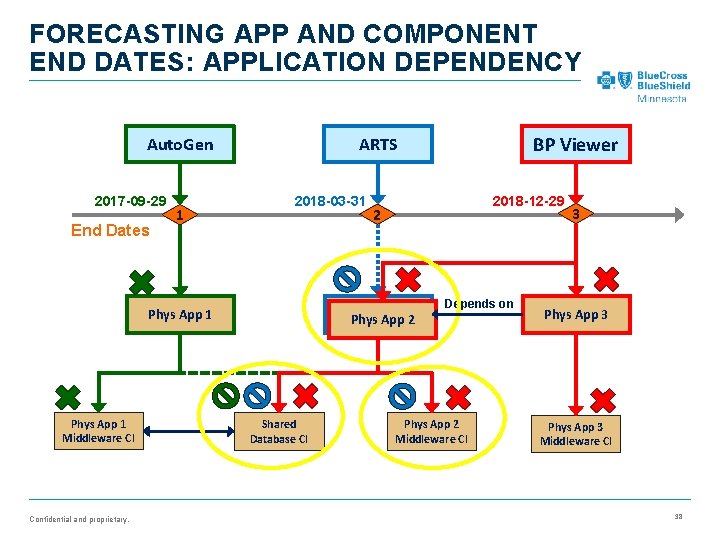
FORECASTING APP AND COMPONENT END DATES: APPLICATION DEPENDENCY 2017 -09 -29 End Dates 1 2018 -03 -31 Confidential and proprietary. 2018 -12 -29 2 Phys. App 22 Phys App 1 Middleware CI BP Viewer ARTS Auto. Gen Shared Database CI Depends on Phys App 2 Middleware CI 3 Phys App 3 Middleware CI 38
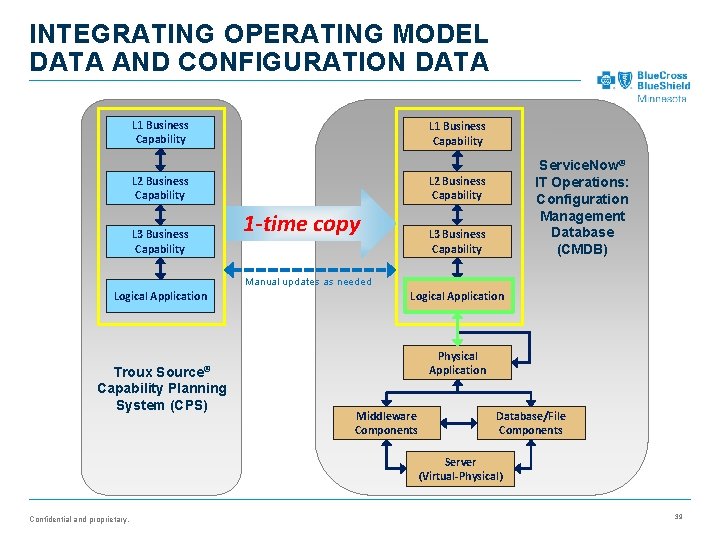
INTEGRATING OPERATING MODEL DATA AND CONFIGURATION DATA L 1 Business Capability L 2 Business Capability L 3 Business Capability Service. Now® IT Operations: Configuration Management Database (CMDB) 1 -time copy L 3 Business Capability Manual updates as needed Logical Application Troux Source® Capability Planning System (CPS) Logical Application Physical Application Middleware Components Database/File Components Server (Virtual-Physical) Confidential and proprietary. 39
CONTENTS • Background • Business Capability Planning Framework • Business Capability Model and Capability Application Model • Capability Model transformation analysis tools • Physical applications and IT configuration management • Mapping business architecture to physical applications and configurations • Forecasting and tracking application and component lifecycle changes Confidential and proprietary.
FORECASTING AND TRACKING: LARGE AUDIENCES FOR BOTH • Many audiences need or want to know when application lifecycles are planned to change • Operational “point of no return” • Access to legacy data if needed • Other audiences need to know when application lifecycles changes are complete • IT resources can be re-allocated or released • For use as an indicator of progress towards operating goal(s) • Generated reports are primary means of communicating operating solution changes (planned or actual) • Process and methods for ad hoc queries are required too • Most reports are in Excel and summarized in presentations with Excel charts Confidential and proprietary. 41
![APP LIFECYCLE PLANNING AND TRACKING REPORTING Capability Planning System (CPS) [Troux® by Planview] Service. APP LIFECYCLE PLANNING AND TRACKING REPORTING Capability Planning System (CPS) [Troux® by Planview] Service.](http://slidetodoc.com/presentation_image_h/ec6d75e068e67731f358a2c021bf5e4a/image-42.jpg)
APP LIFECYCLE PLANNING AND TRACKING REPORTING Capability Planning System (CPS) [Troux® by Planview] Service. Now Reports & Tables Configuration Management System [Service. Now IT Operations Management] SQL Server Repository Perspectium Service. Now Replicator Troux Link (Custom SQL Server app) ® IT Data Warehouse BI Tools Confidential and proprietary. 42
SUMMARY • The BCBSMN Business Capability Planning Framework and similar business architecture frameworks are highly effective tools for planning business transformations. • Executing business architecture transformations requires changes to the software and systems that enable the business capabilities affected by the transformations. • For large business transformations, extensive relationships between business architecture and IT solutions and solution components reduce the time and risk of IT changes to support the business transformations. Confidential and proprietary. 43

THANK YOU. Dave Goiffon, Enterprise Architect, Blue Cross Blue Shield of Minnesota 651 -662 -1687 David. Goiffon@Bluecrossmn. com Confidential and proprietary. Blue Cross® and Blue Shield ® of Minnesota and Blue Plus ® are nonprofit independent licensees of the Blue Cross and Blue Shield Association.
- Slides: 44