Congestion Control in Software Define Data Center Network
- Slides: 32
Congestion Control in Software Define Data Center Network Speaker : Cheng-Yu Chang Advisor : Dr. Kai-Wei Ke Date : Dec. 3 2015 1
Outline • Software Define Network (SDN) • TCP/IP Congestion Control • Data Center Network (DCN) • Methodology • Implementation • Future Directions • References 2
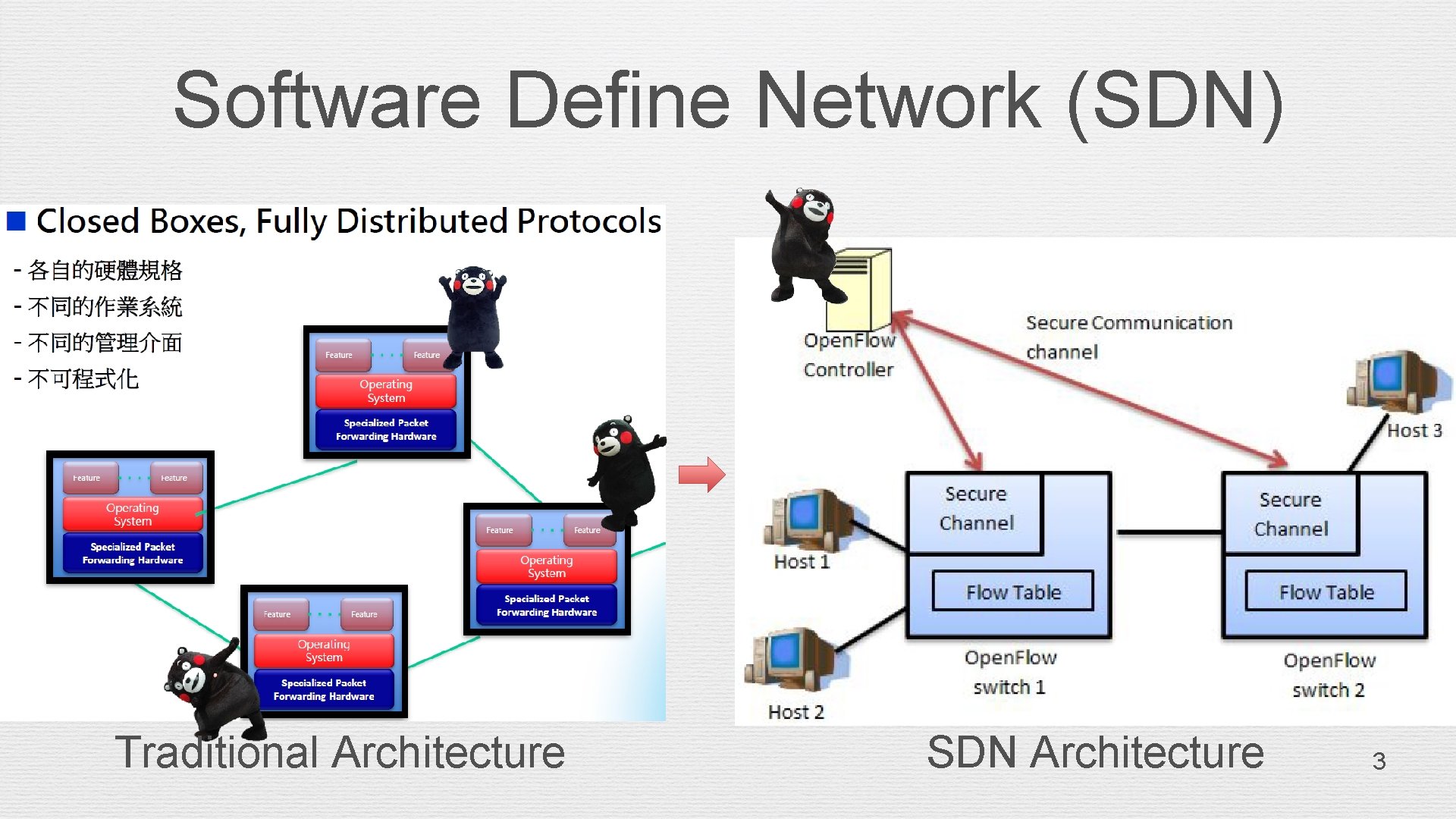
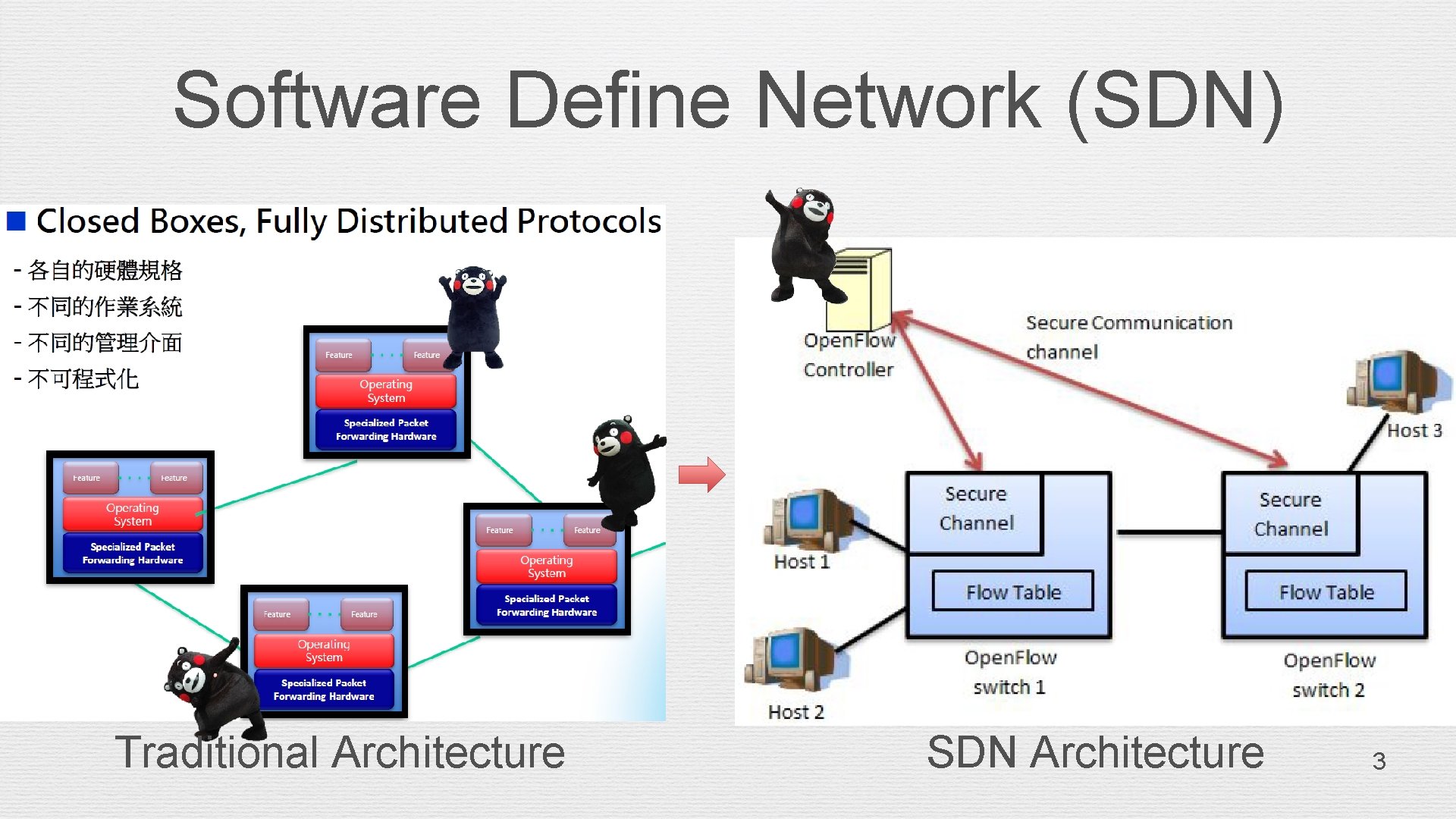
Software Define Network (SDN) Traditional Architecture SDN Architecture 3
TCP/IP Congestion Control 4
TCP/IP Congestion Control • Explicit Congestion Notification (ECN) in TCP/IP • Notify congestion to end nodes • Sender reduce sending rate • Operation of ECN with ü IP ü TCP 5
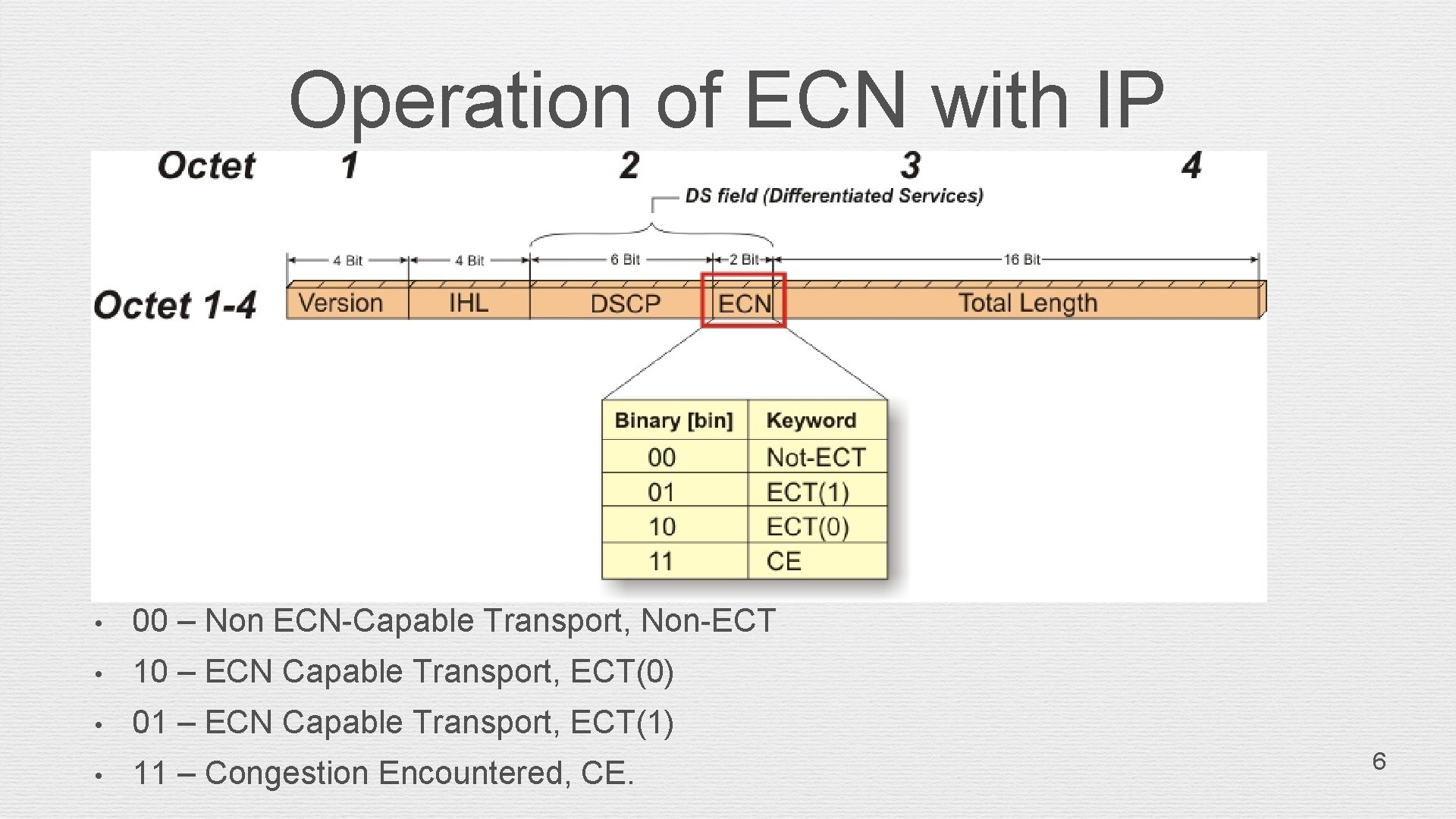
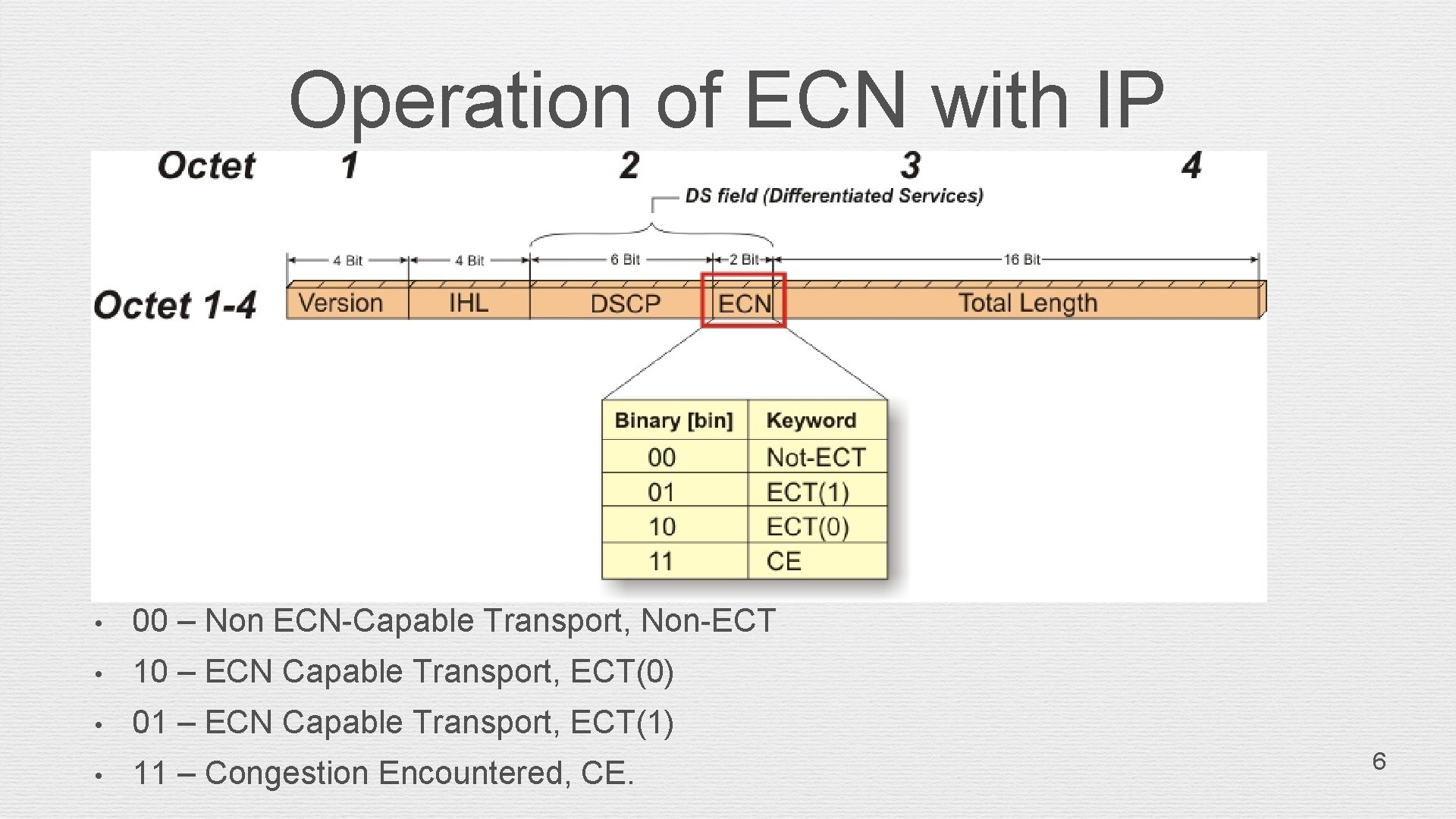
Operation of ECN with IP • 00 – Non ECN-Capable Transport, Non-ECT • 10 – ECN Capable Transport, ECT(0) • 01 – ECN Capable Transport, ECT(1) • 11 – Congestion Encountered, CE. 6
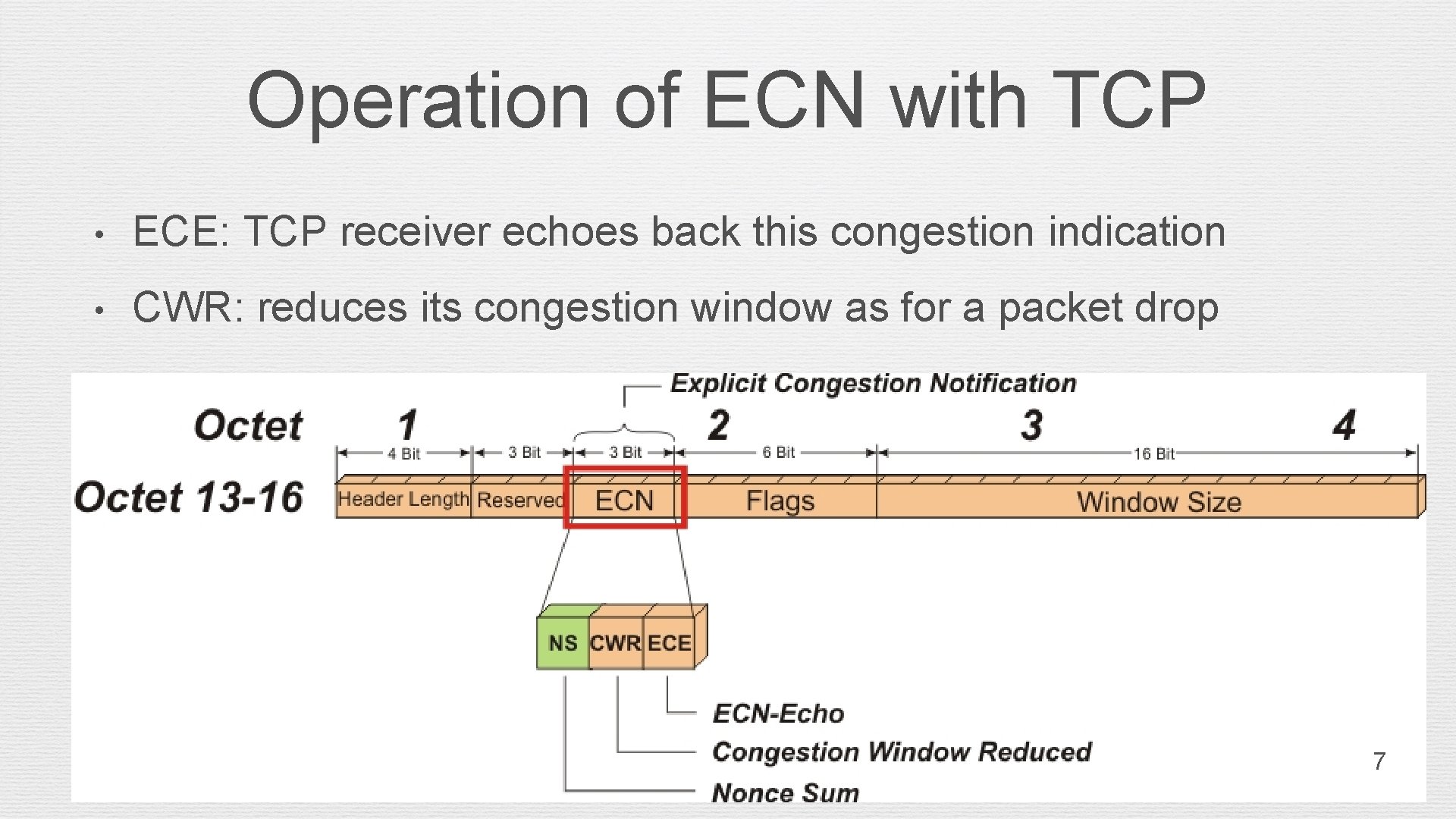
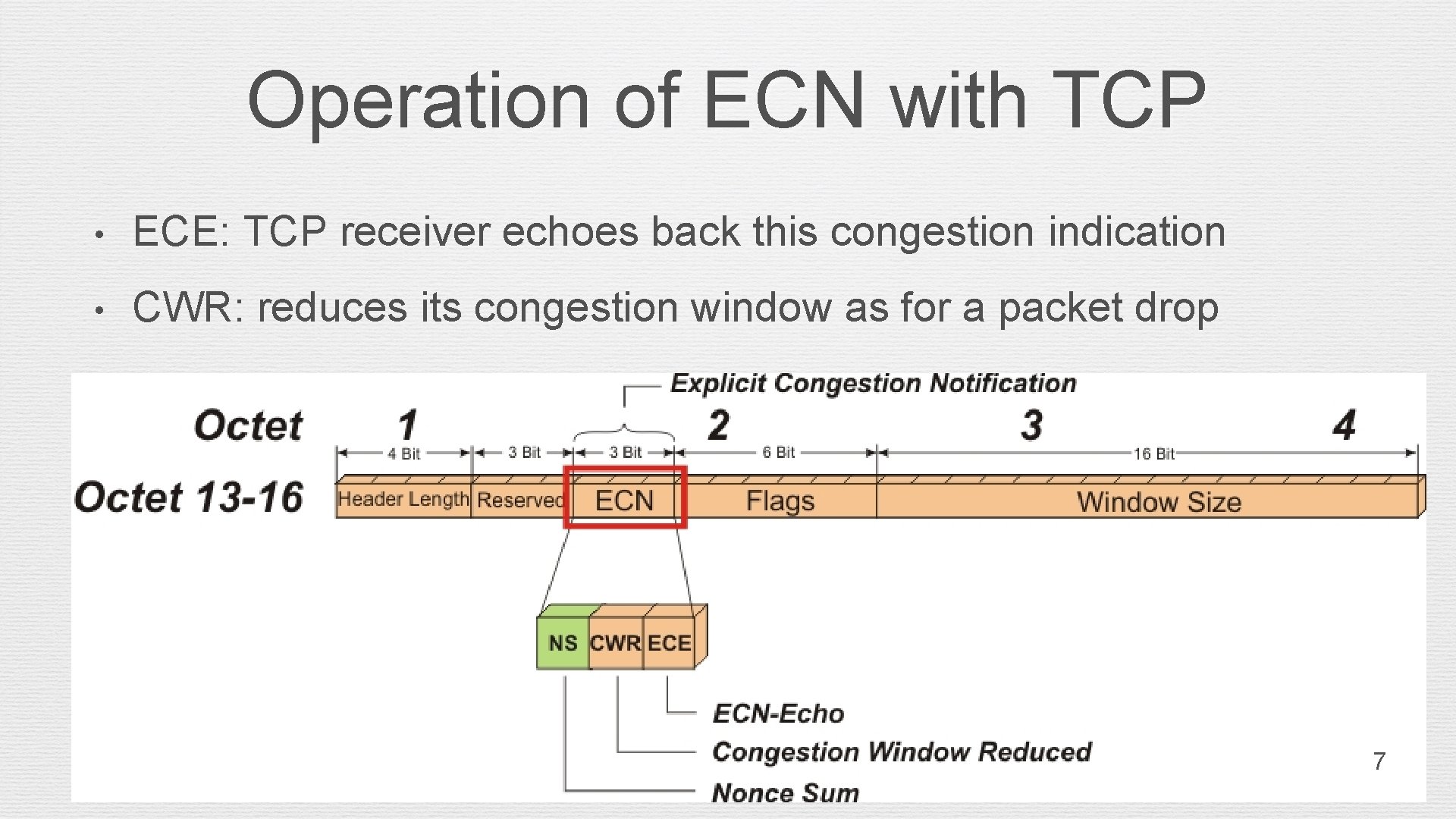
Operation of ECN with TCP • ECE: TCP receiver echoes back this congestion indication • CWR: reduces its congestion window as for a packet drop 7
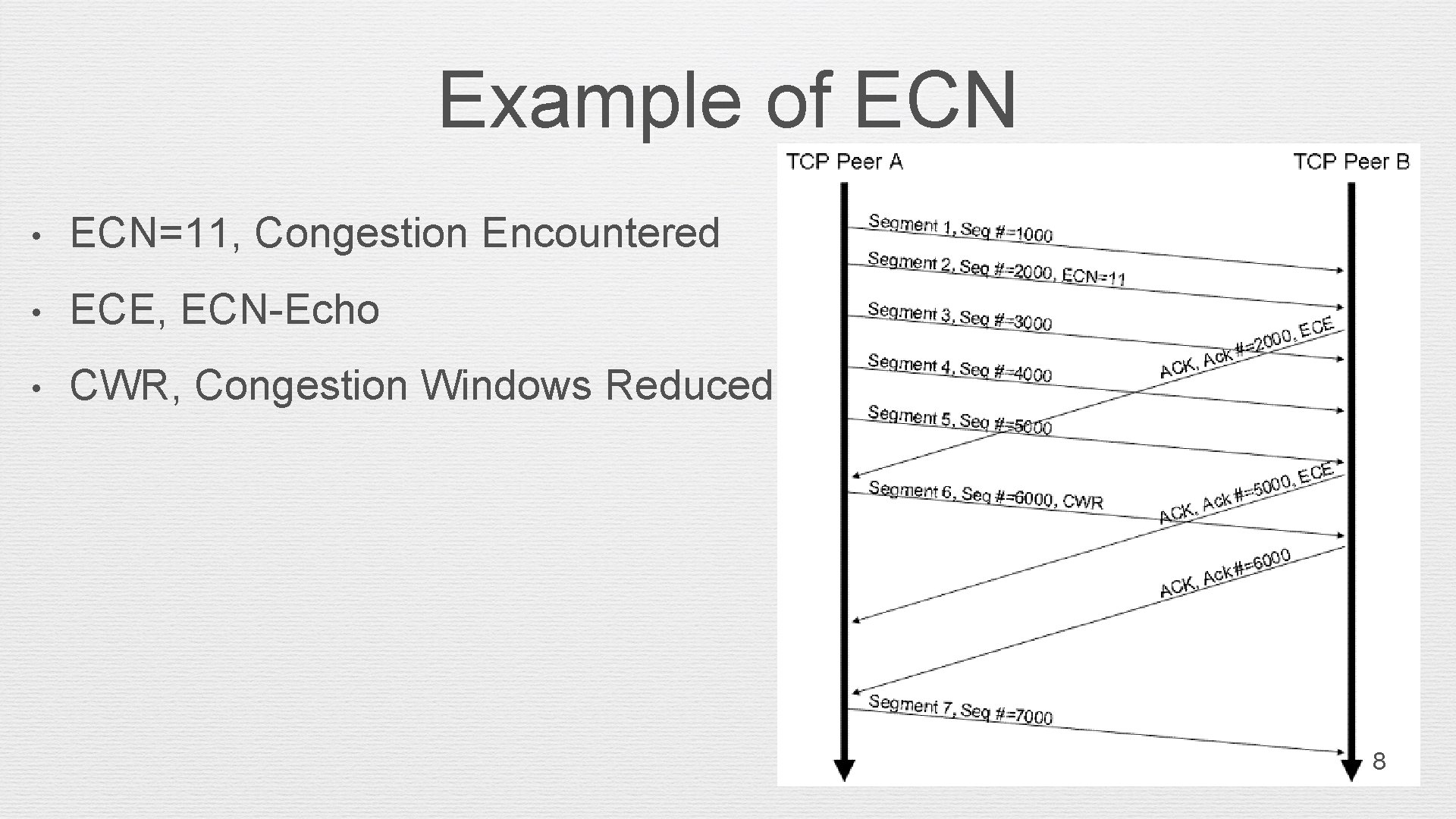
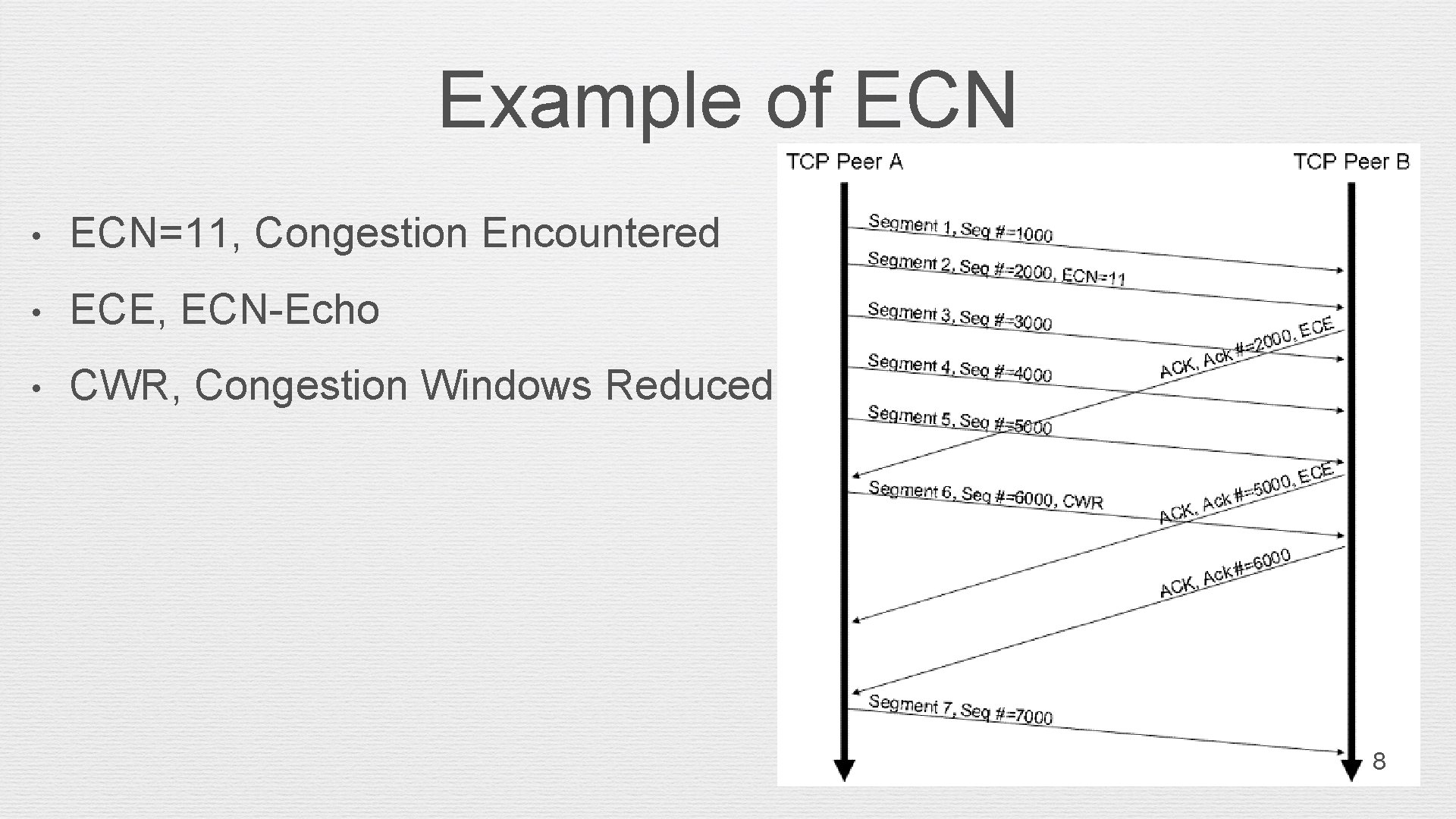
Example of ECN • ECN=11, Congestion Encountered • ECE, ECN-Echo • CWR, Congestion Windows Reduced 8
Data Center Network (DCN) • Topology • Elephant/Mice Flow • TCP Incast 9
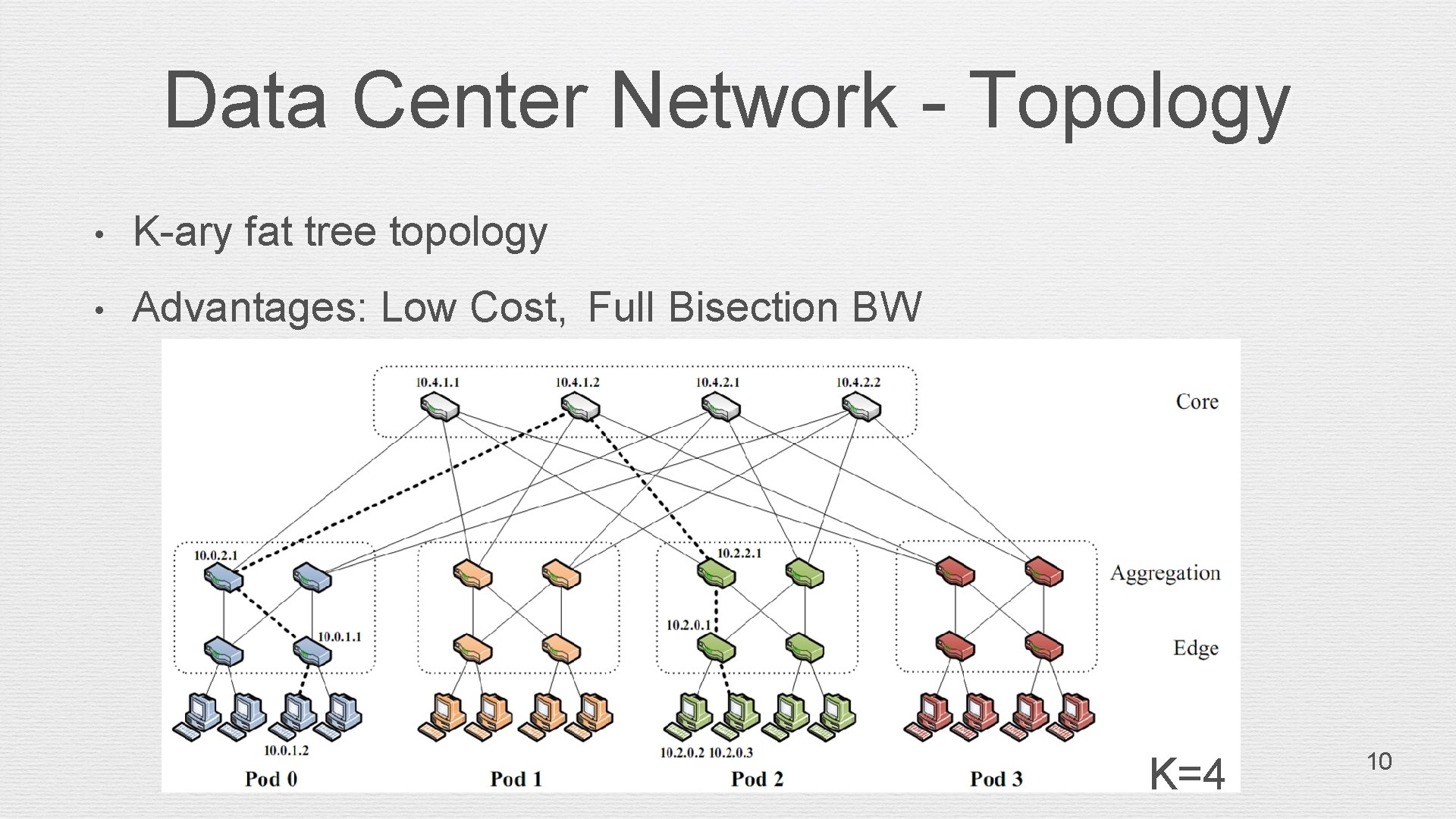
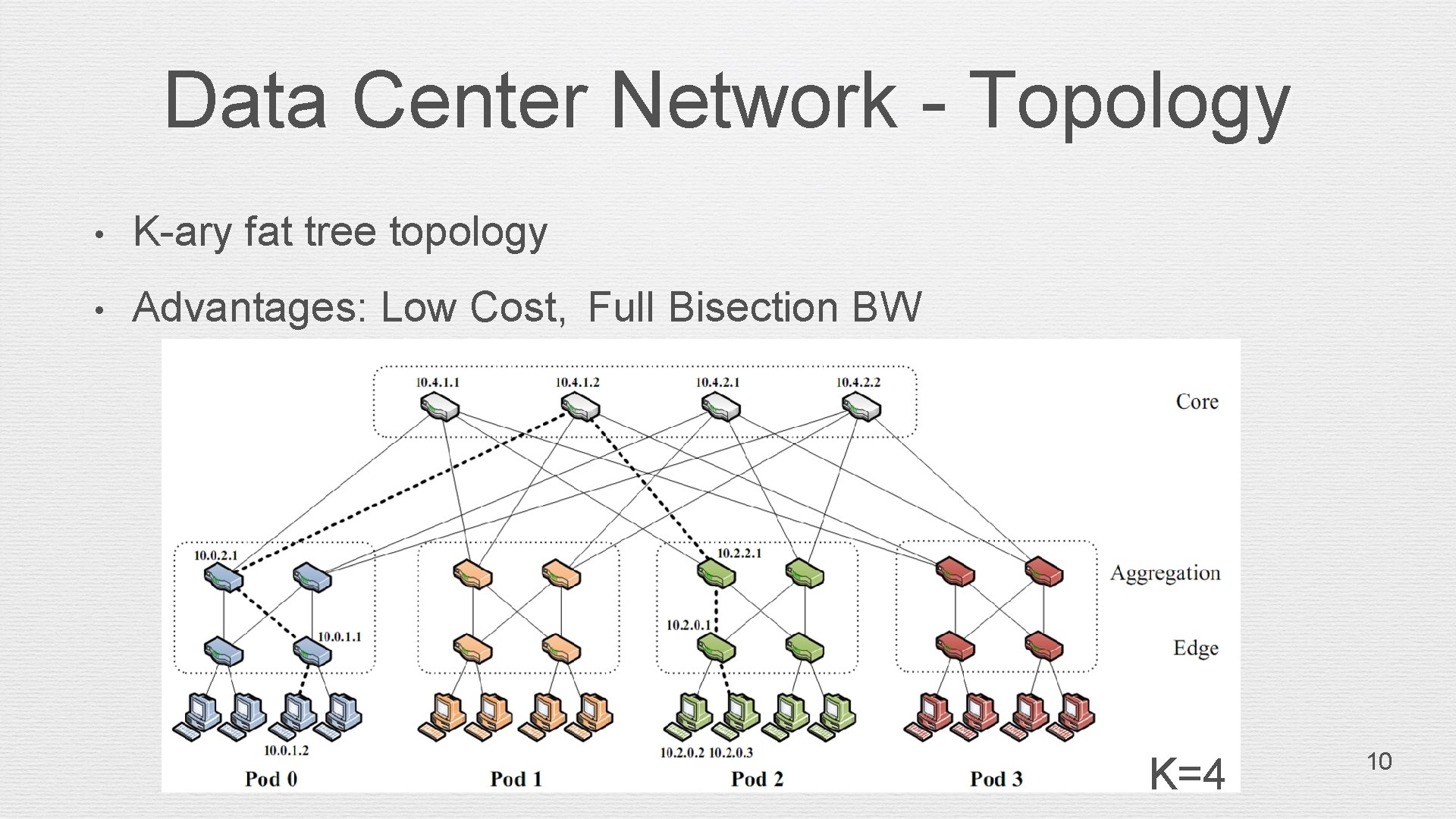
Data Center Network - Topology • K-ary fat tree topology • Advantages: Low Cost, Full Bisection BW K=4 10
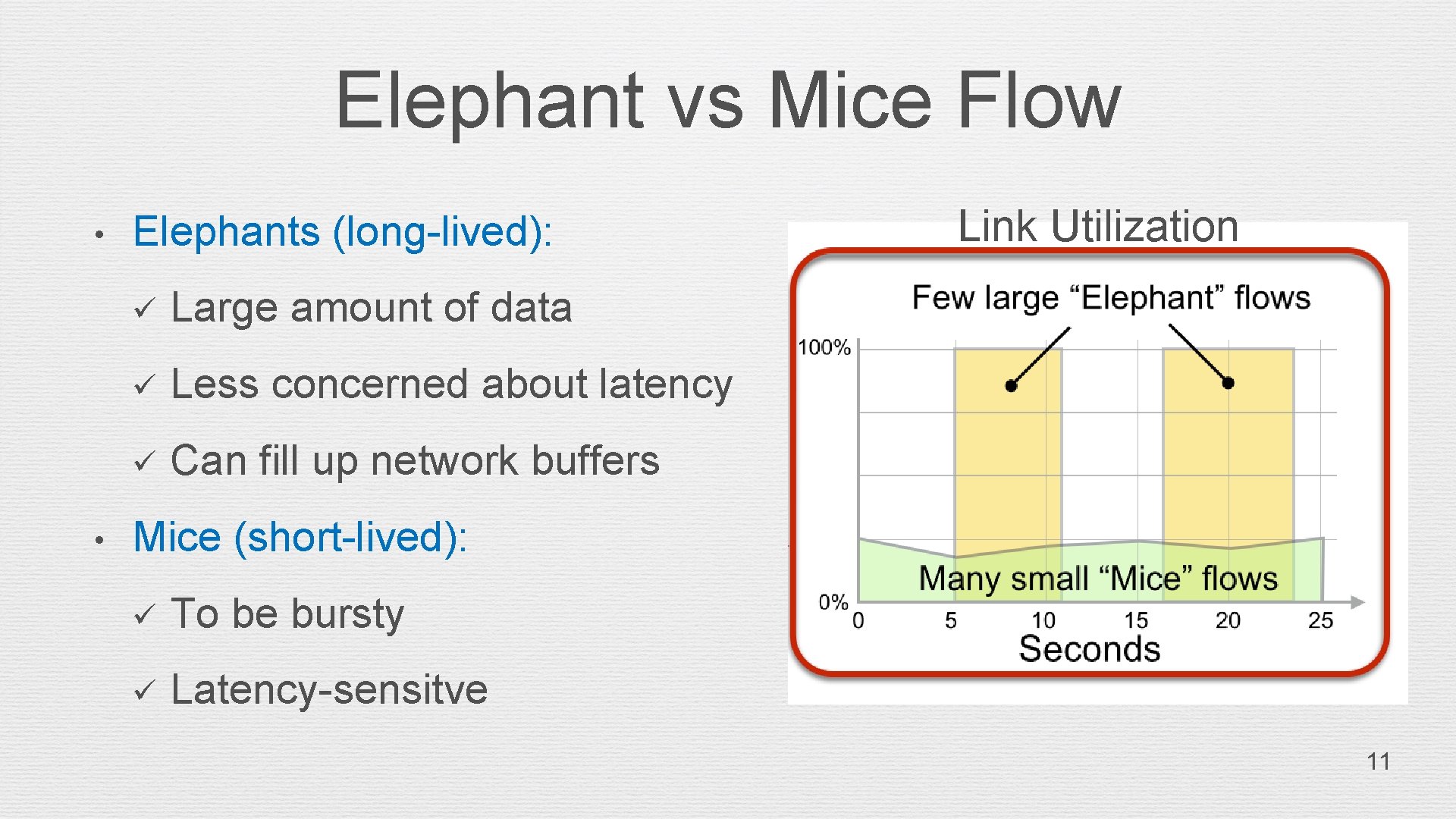
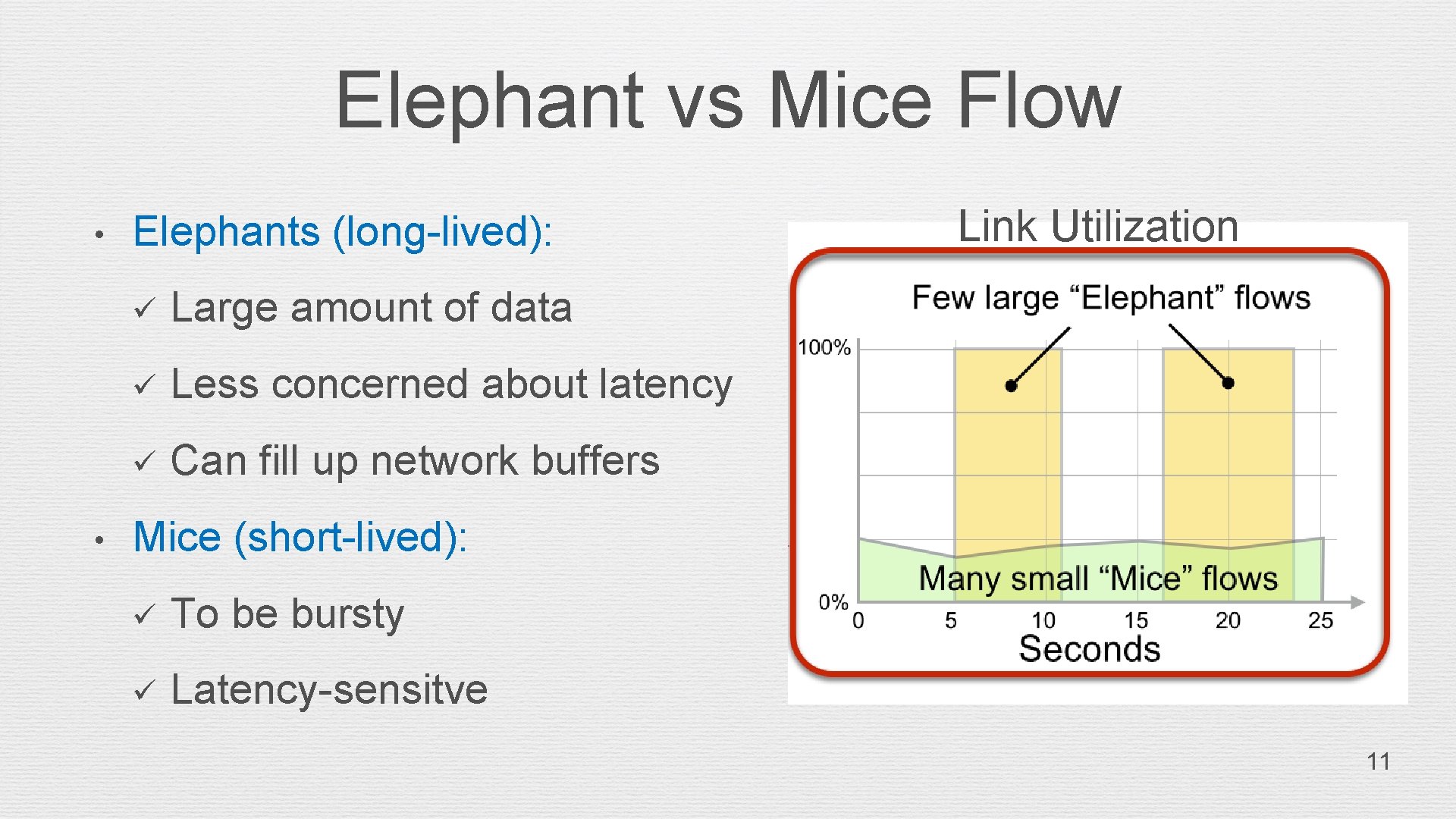
Elephant vs Mice Flow • • Elephants (long-lived): ü Large amount of data ü Less concerned about latency ü Can fill up network buffers Link Utilization Mice (short-lived): ü To be bursty ü Latency-sensitve 11
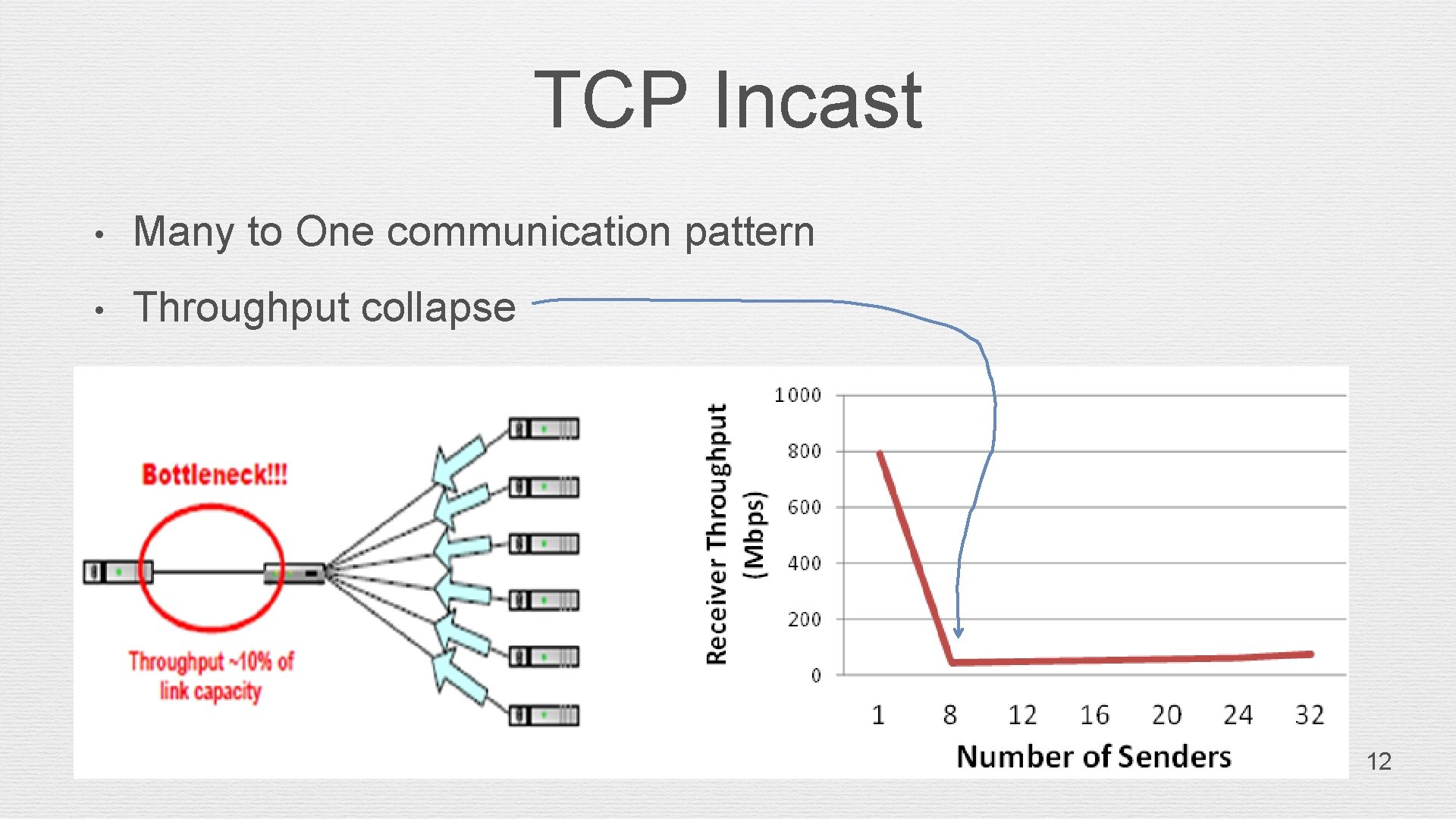
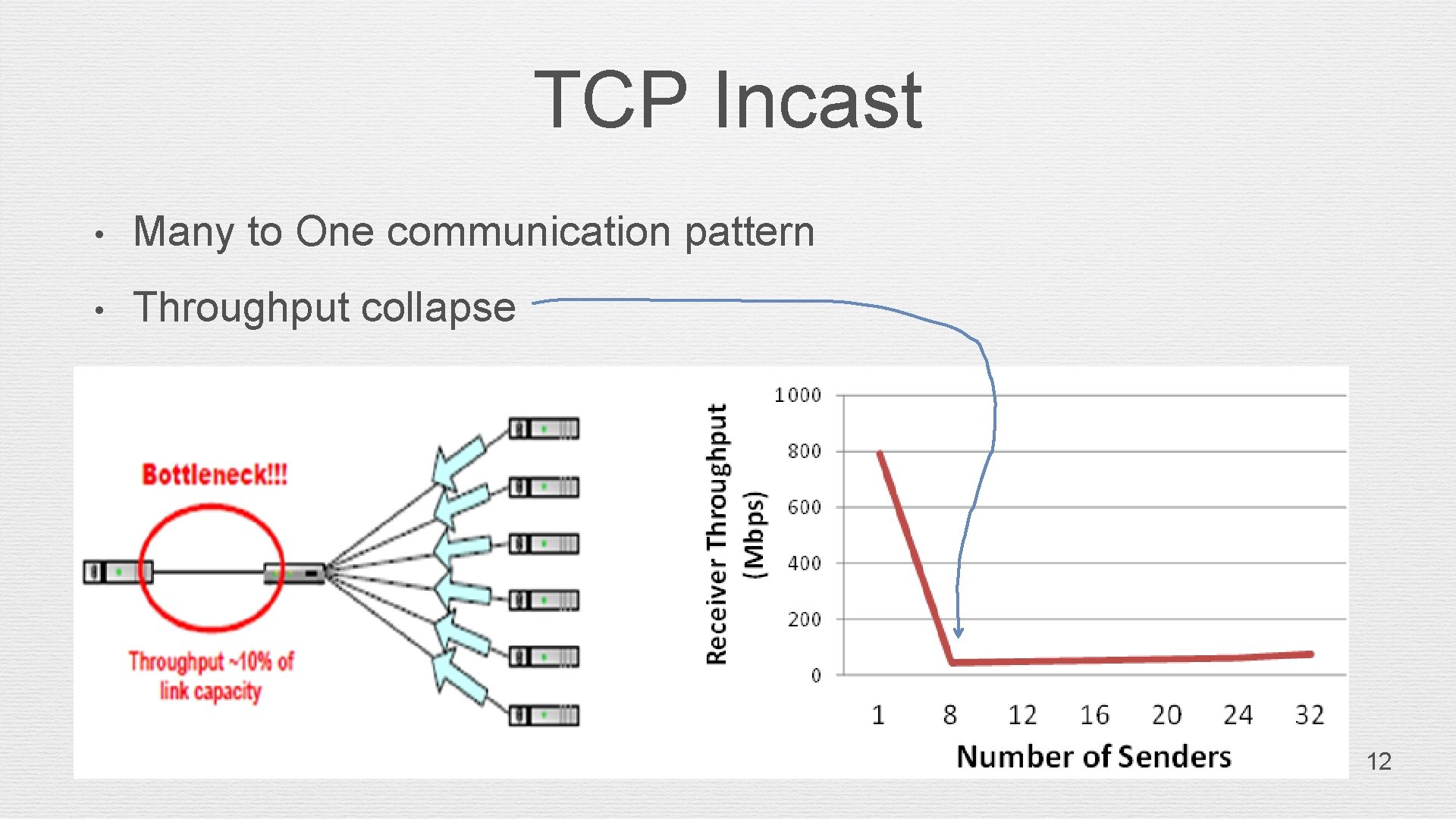
TCP Incast • Many to One communication pattern • Throughput collapse 12
Congestion Control Methodology • Detection Method • Control Method 13
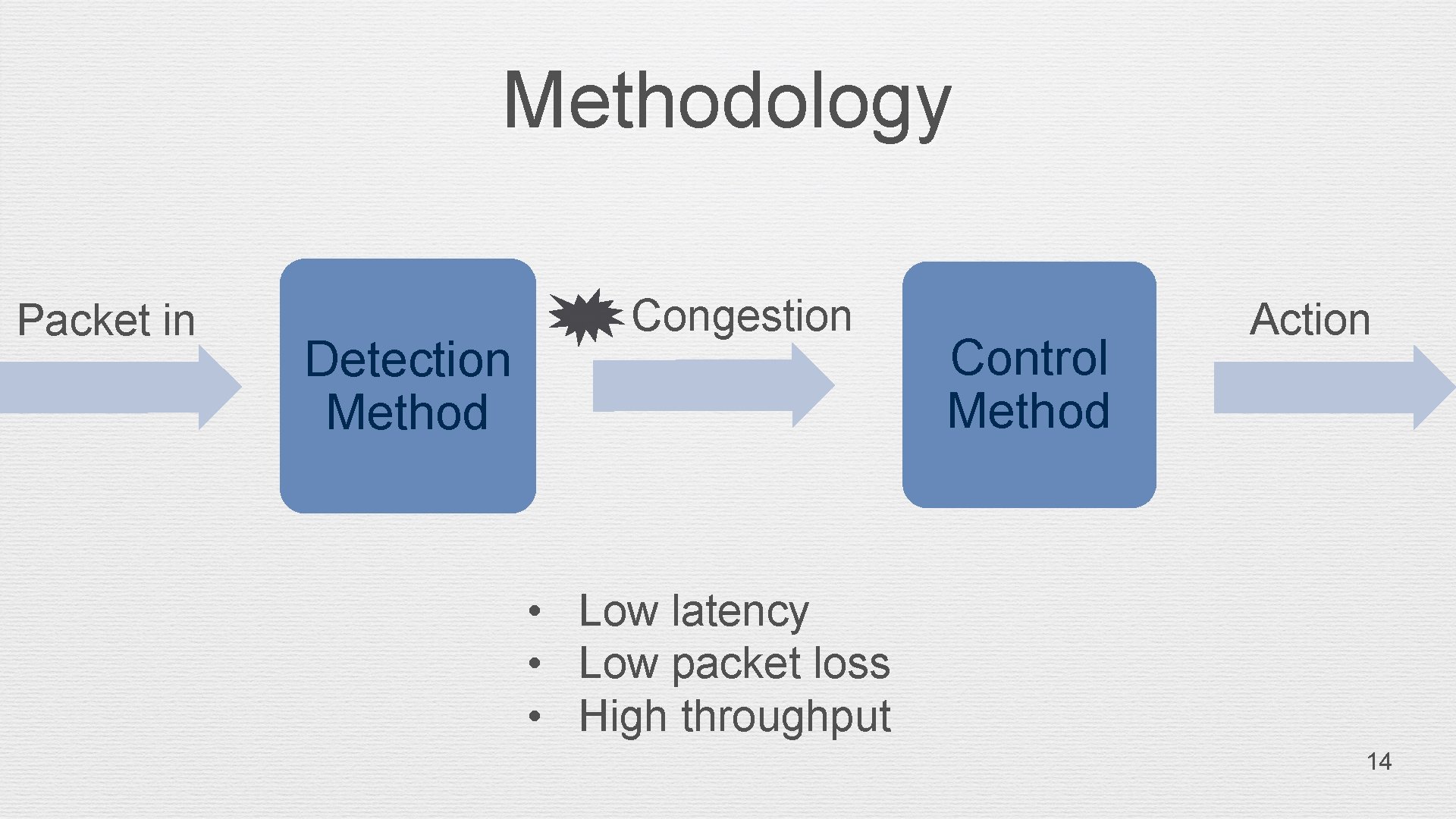
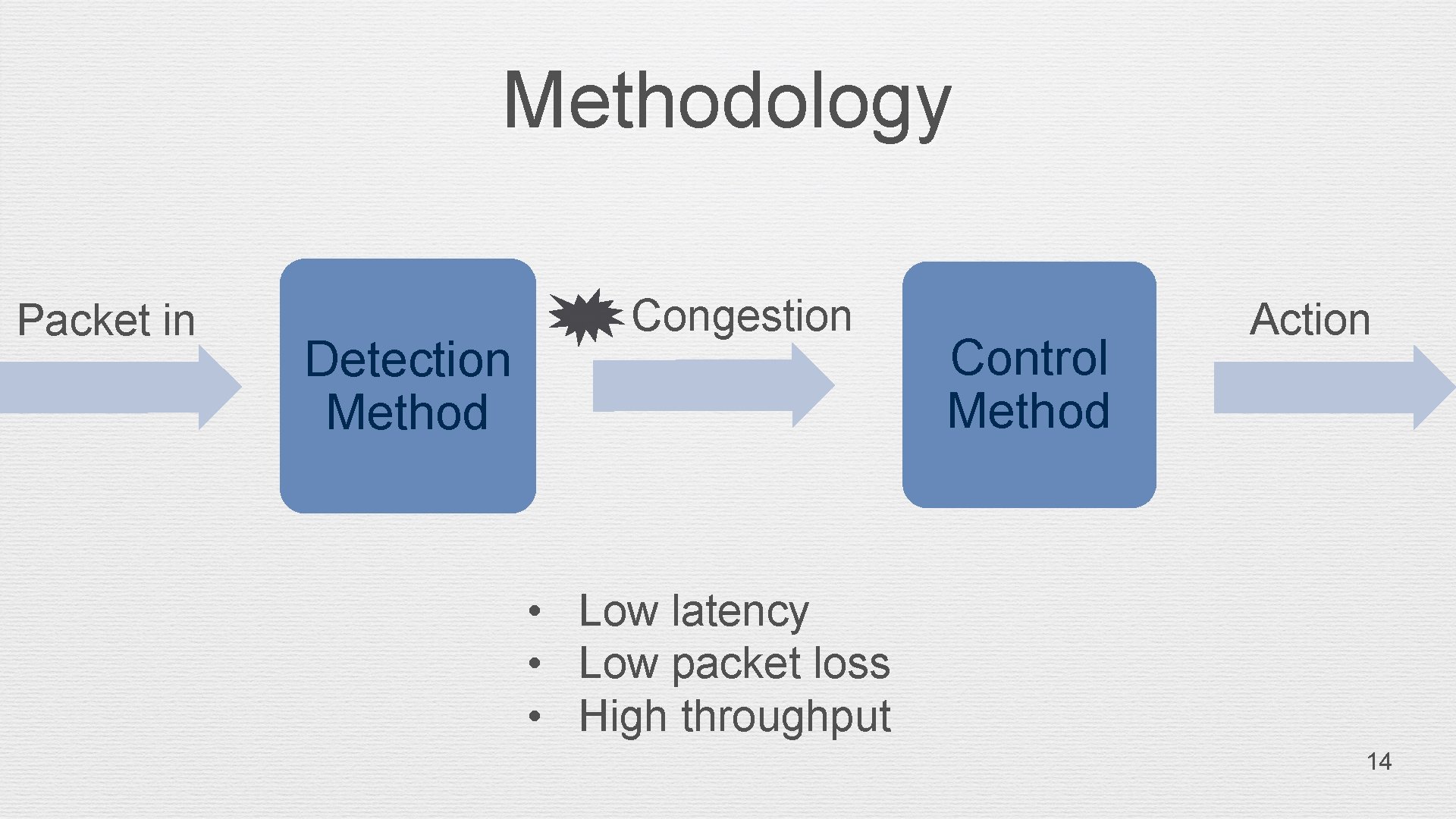
Methodology Packet in Detection Method Congestion Control Method Action • Low latency • Low packet loss • High throughput 14
Detection Method • Purpose: Detect the network congestion • Method (per table/per flow/per port): ü Queue size ü Packet drop rate ü Bandwidth ü Link captaincy (Link load) 15
Control Method • Purpose: Action to reduce congestion • Method 1: Modify the host • ü TCP Stack Modify - RWIN, ACK interval ü Admission Control - Bandwidth allocation Method 2: host no modify ü Reroute - chose less congestion path, with DLBMP ü Switch ECN setting modify 16
Implementation 17
Implementation • Under TCP Congestion/Incast in Data Center Network • Architecture: 1. Congestion Detection 2. Target flow identification 3. Congestion Control modification 18
Congestion Detection • TCP Incast in the DCN case throughput collapse • Detection Method: ü The queue size more than threshold ü Available bandwidth less than threshold ü Port/Flow load more than link capacity threshold 19
Target flow identification • Use the DSCP for identification • Detect the Elephant/Mice use • ü rate and time ü large segments Elephant flow: more sensitive and commonly affected (Target) 20
Congestion Control modification - part 1 • Method: use different queues/paths/congestion control • Example of different queues: ü Elephant flow: queue 1 ü Mice flow: queue 2 • Congestion Different queues • No congestion Same queue 21
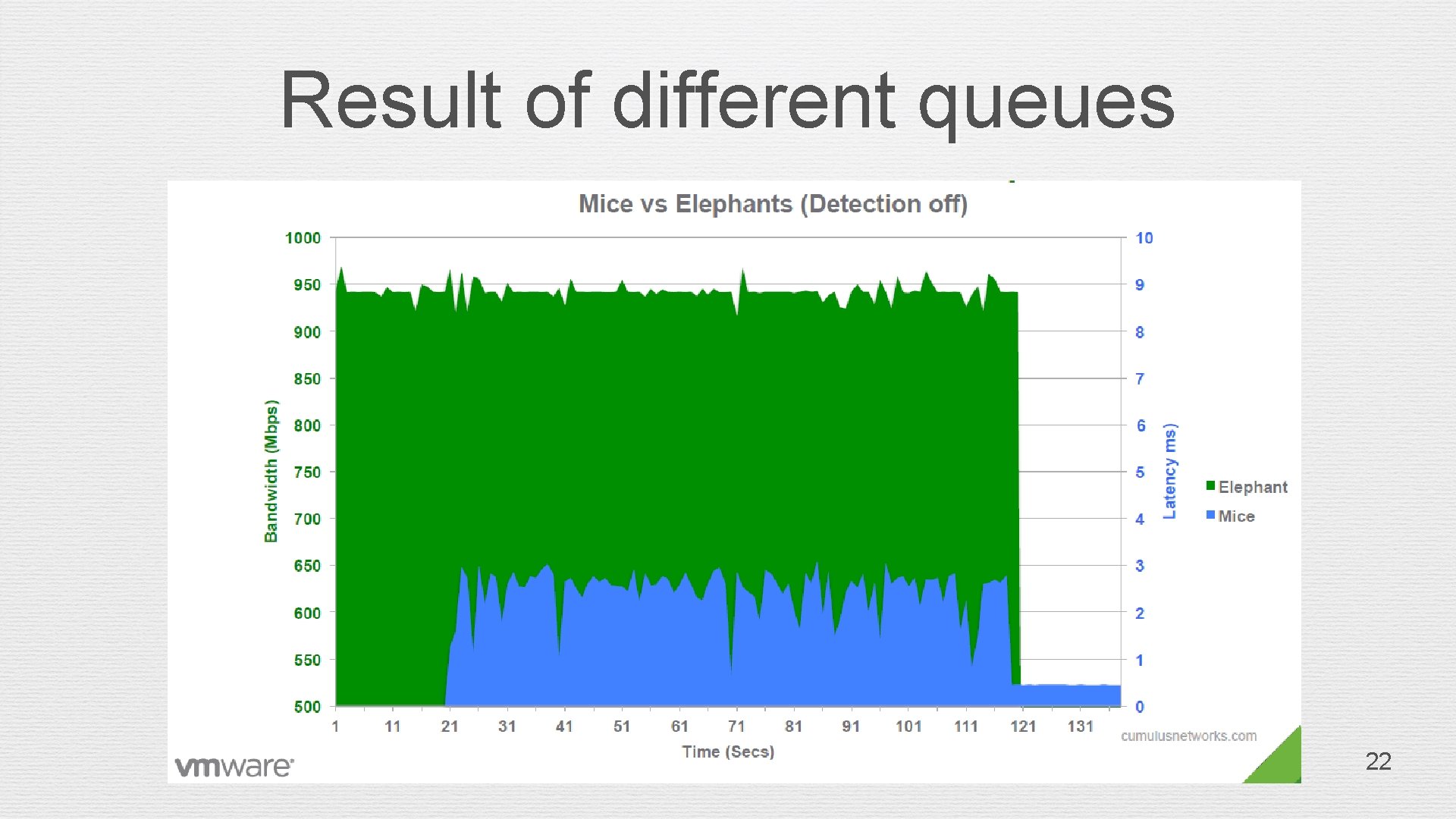
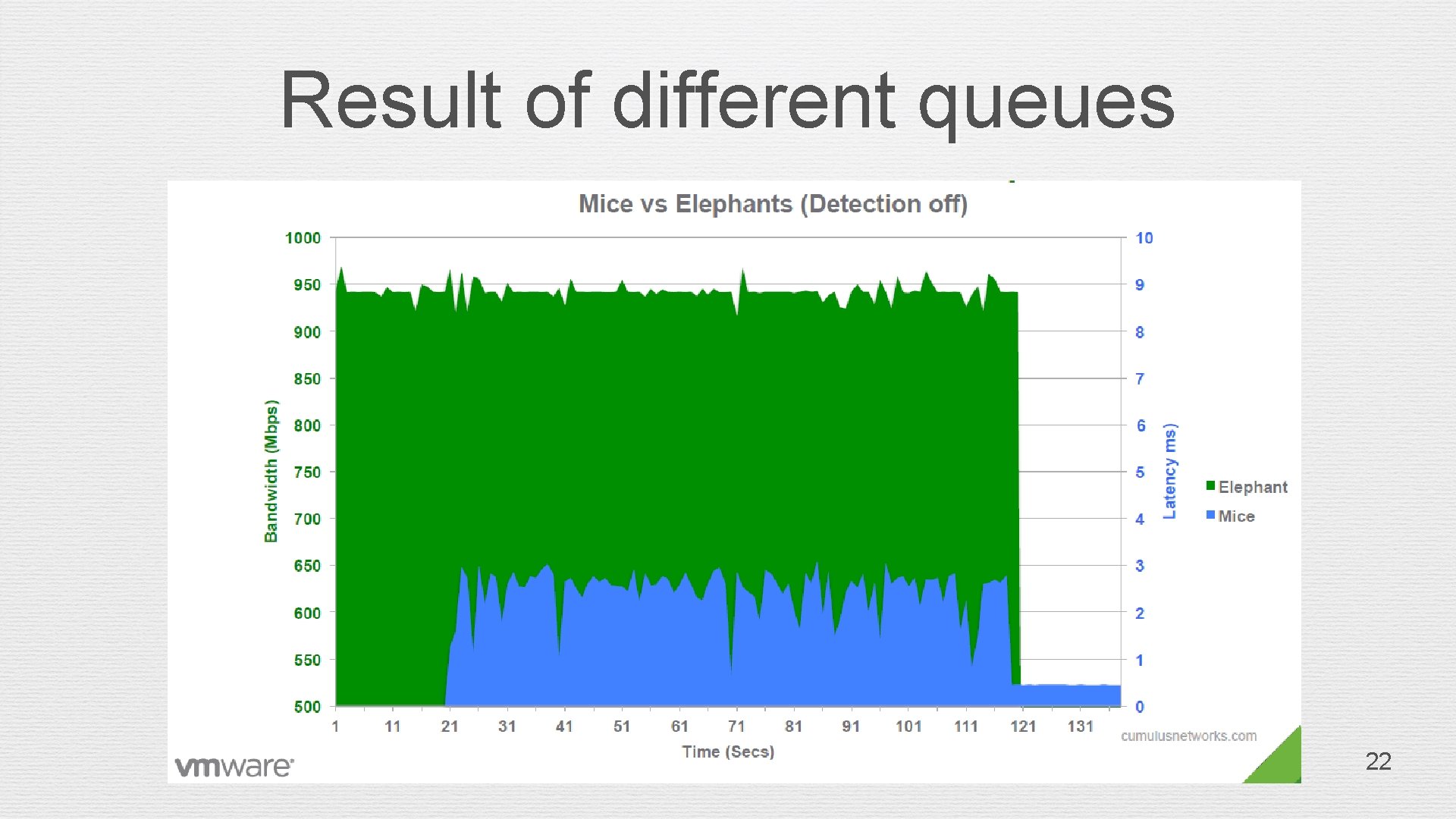
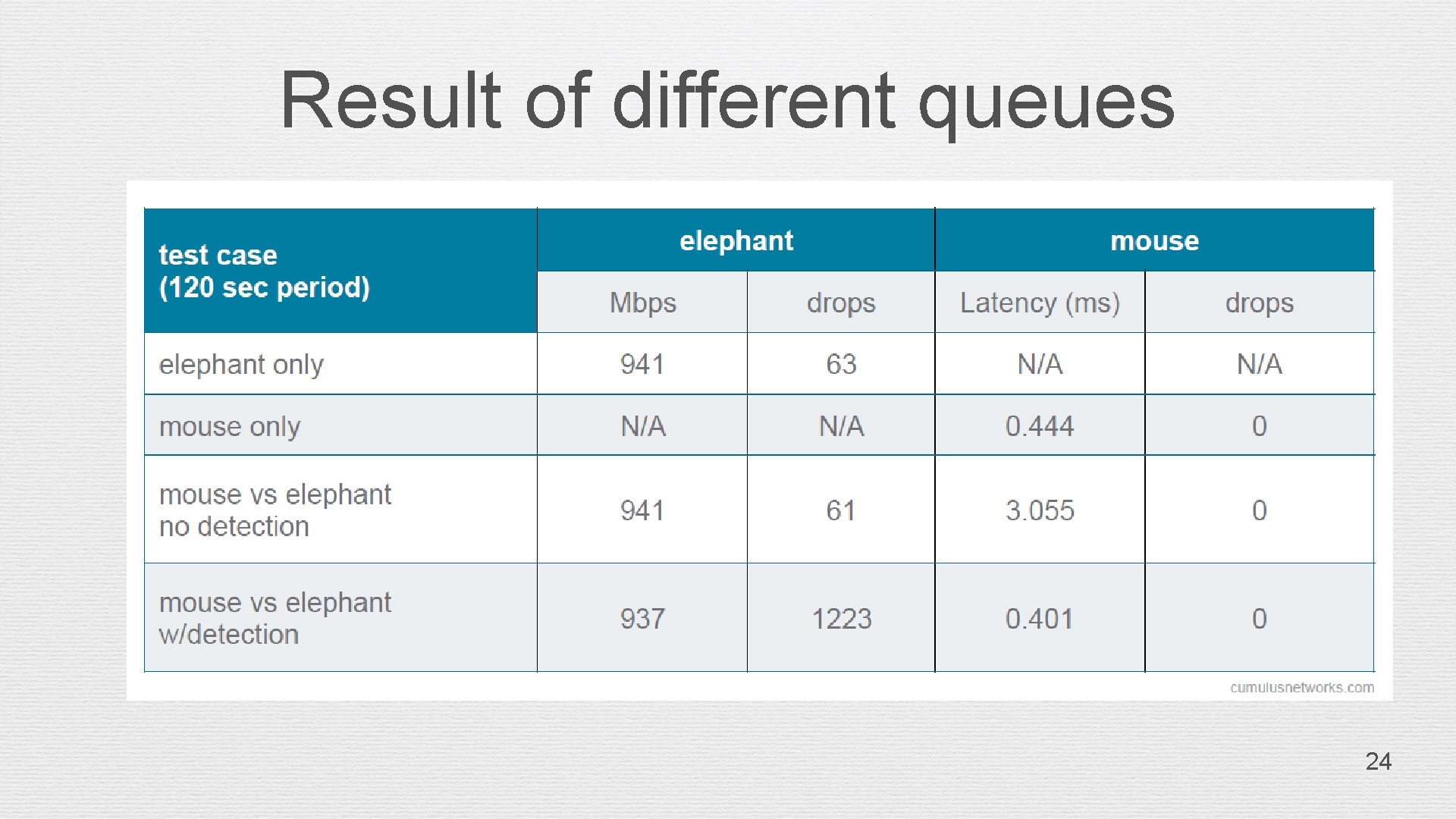
Result of different queues 22
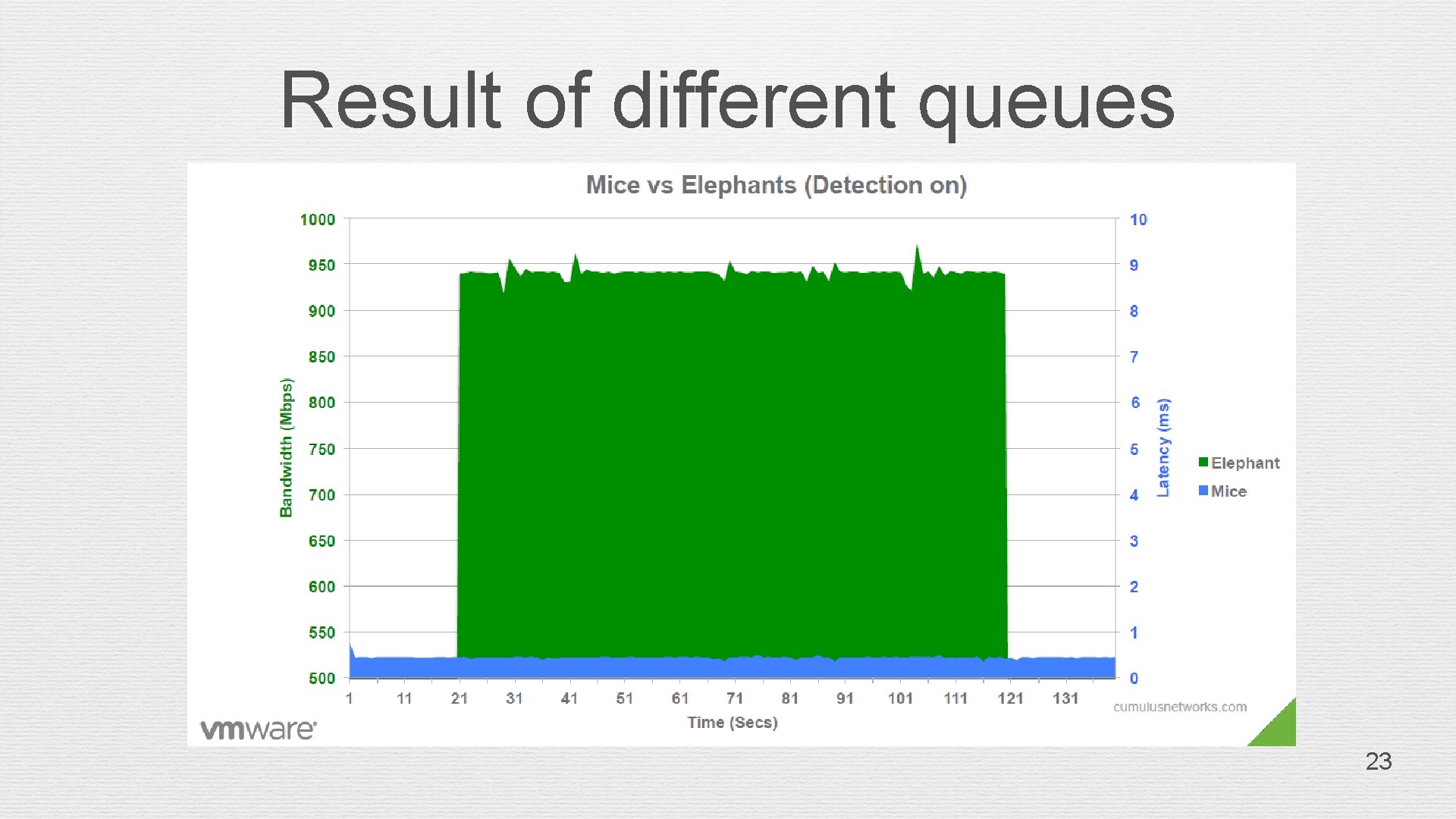
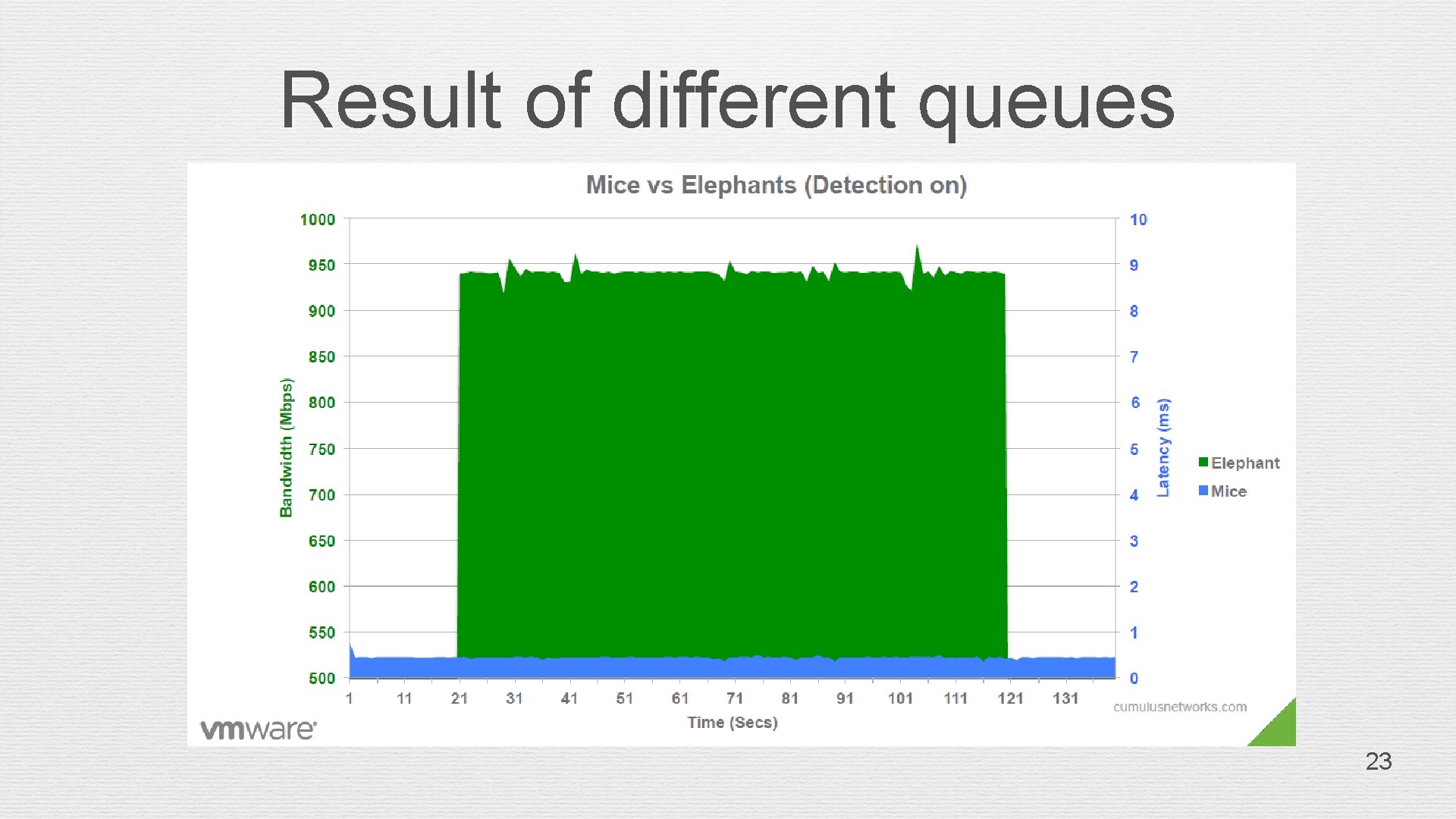
Result of different queues 23
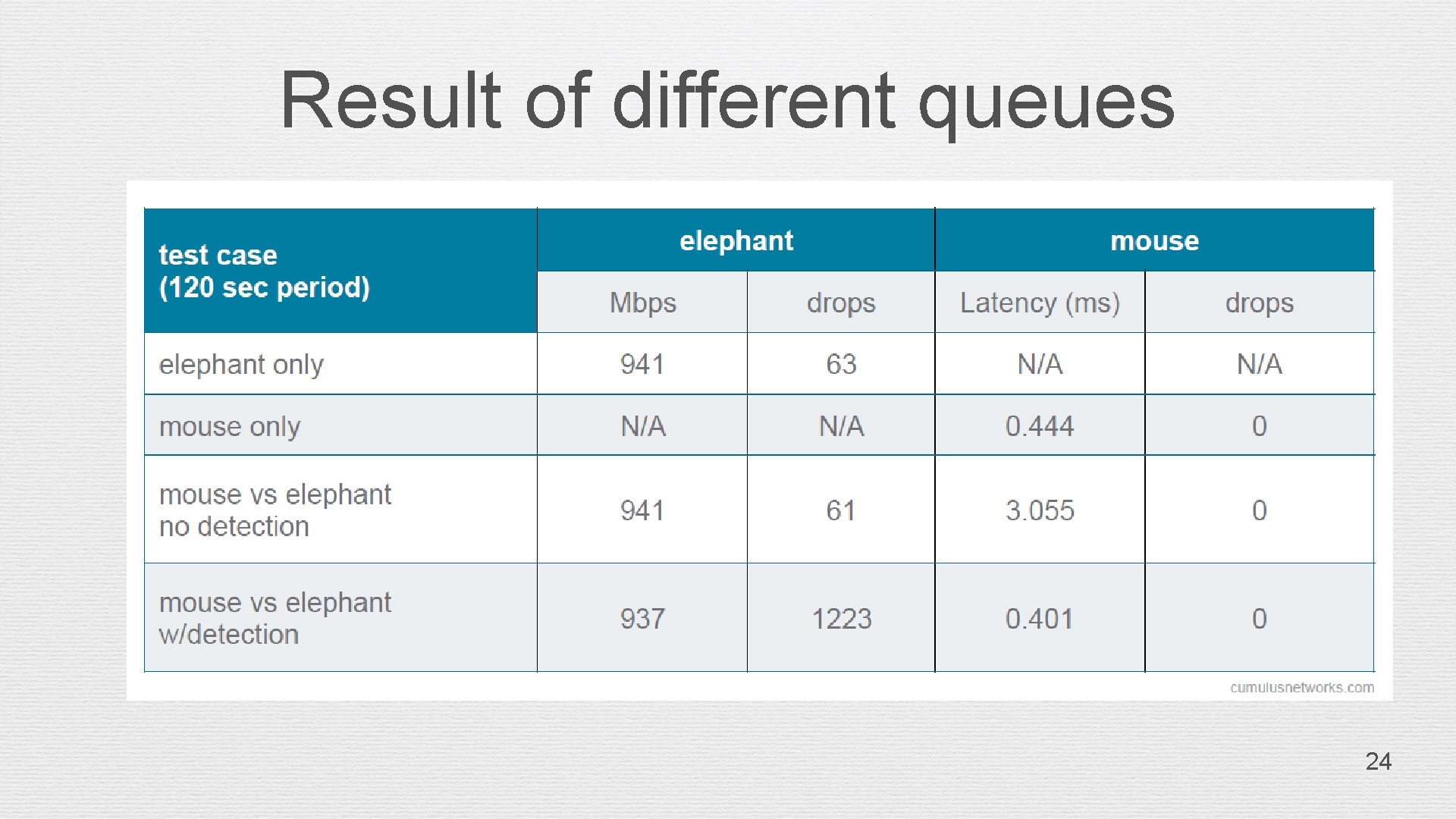
Result of different queues 24
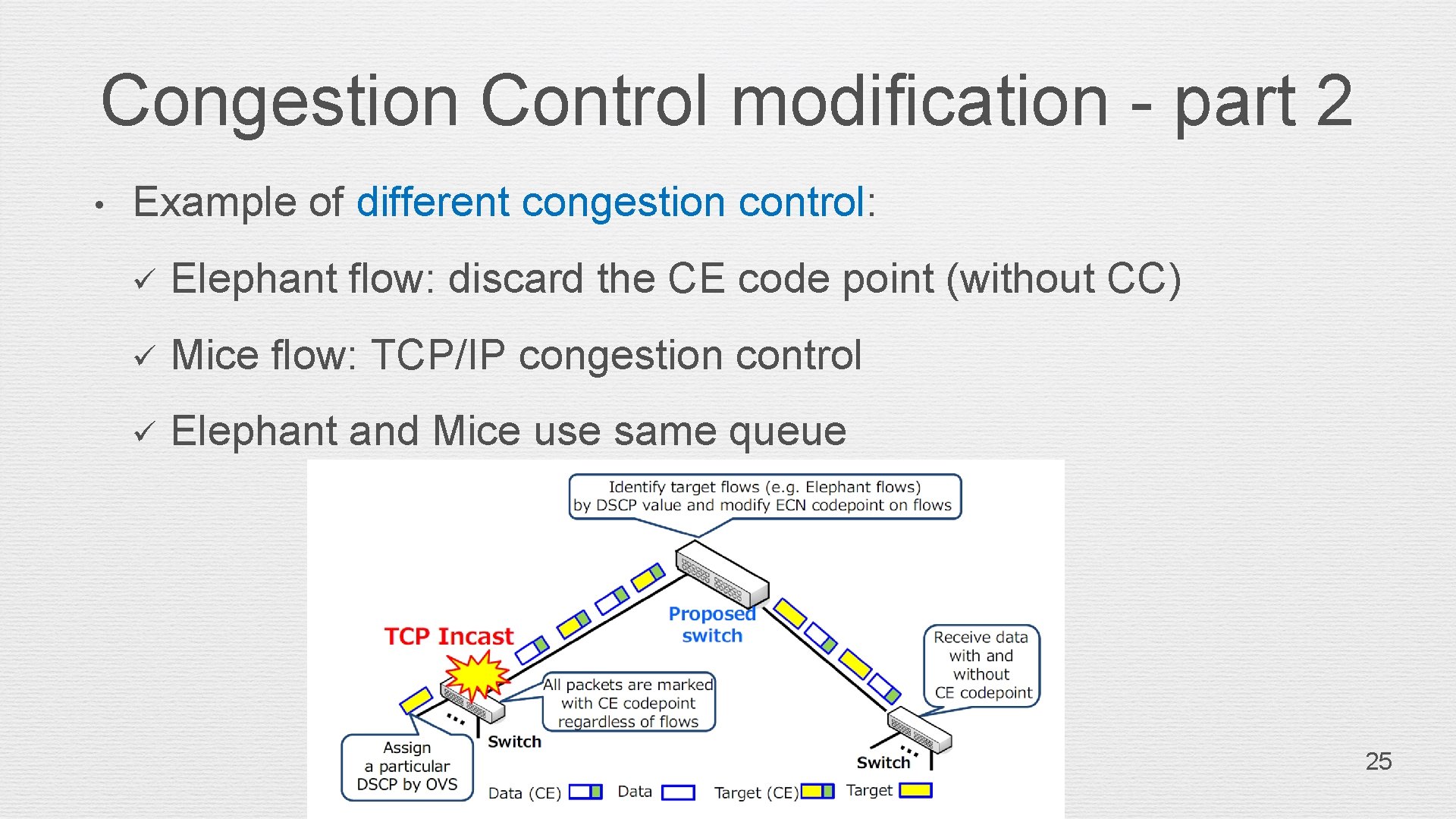
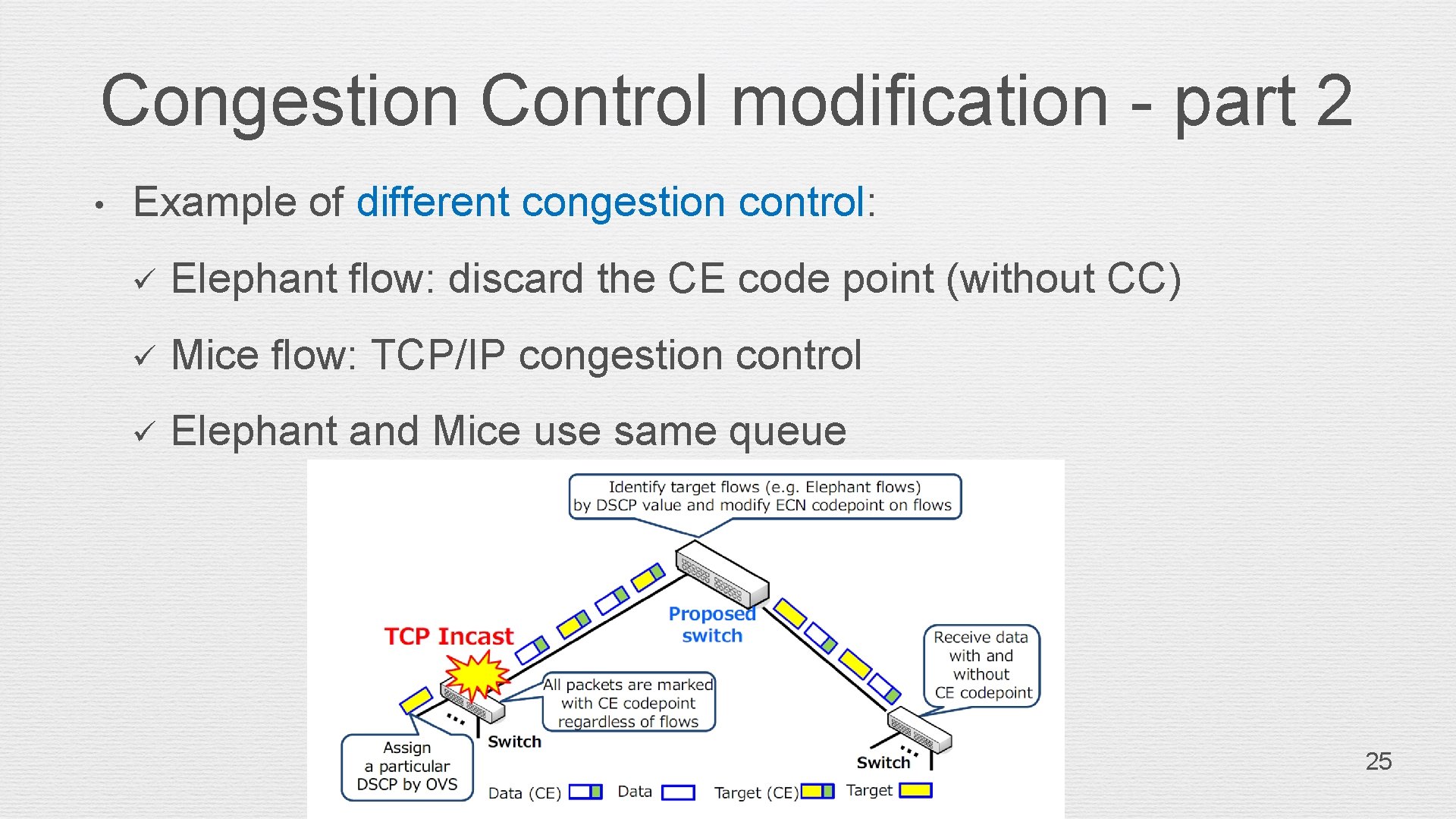
Congestion Control modification - part 2 • Example of different congestion control: ü Elephant flow: discard the CE code point (without CC) ü Mice flow: TCP/IP congestion control ü Elephant and Mice use same queue 25
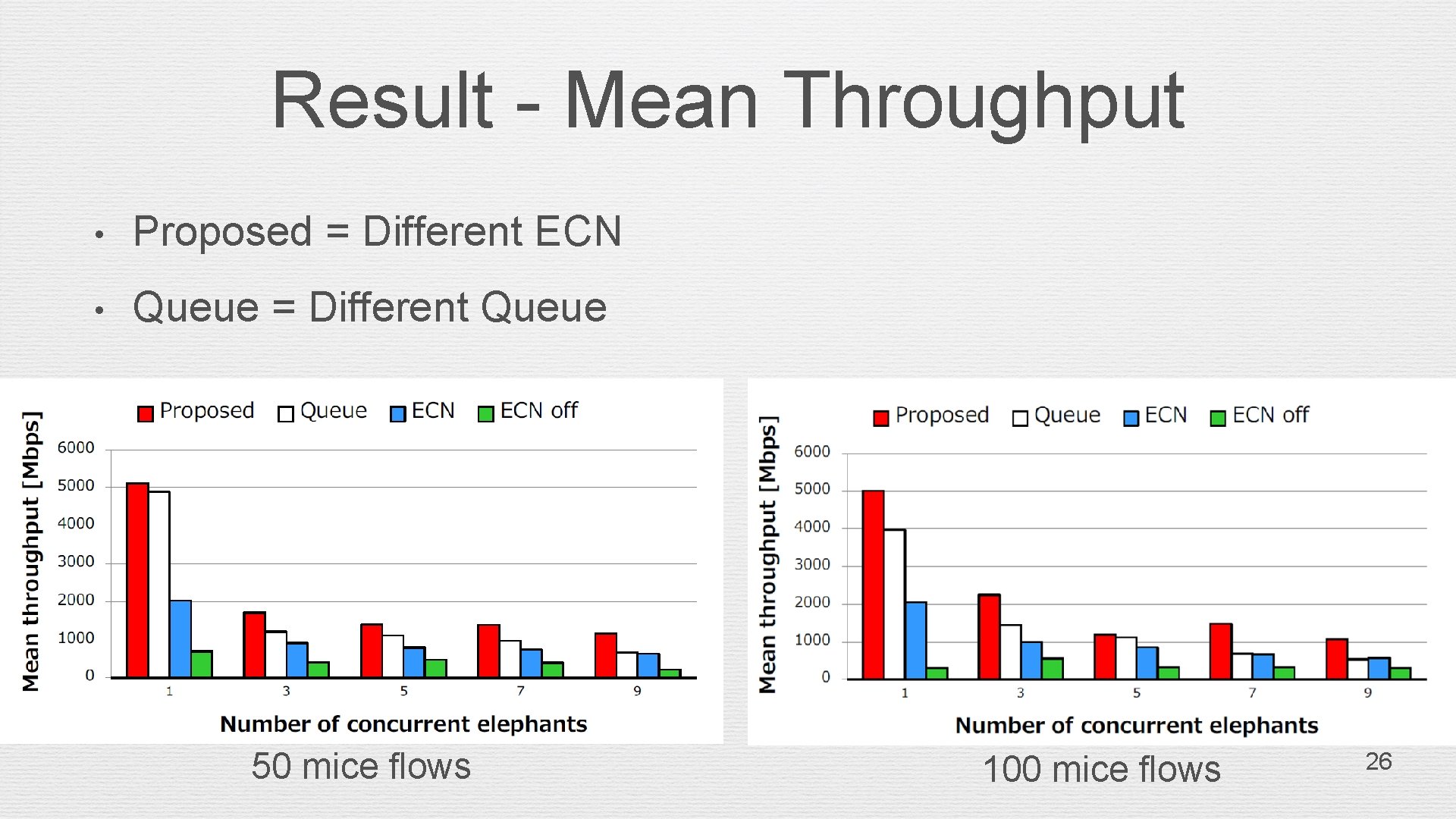
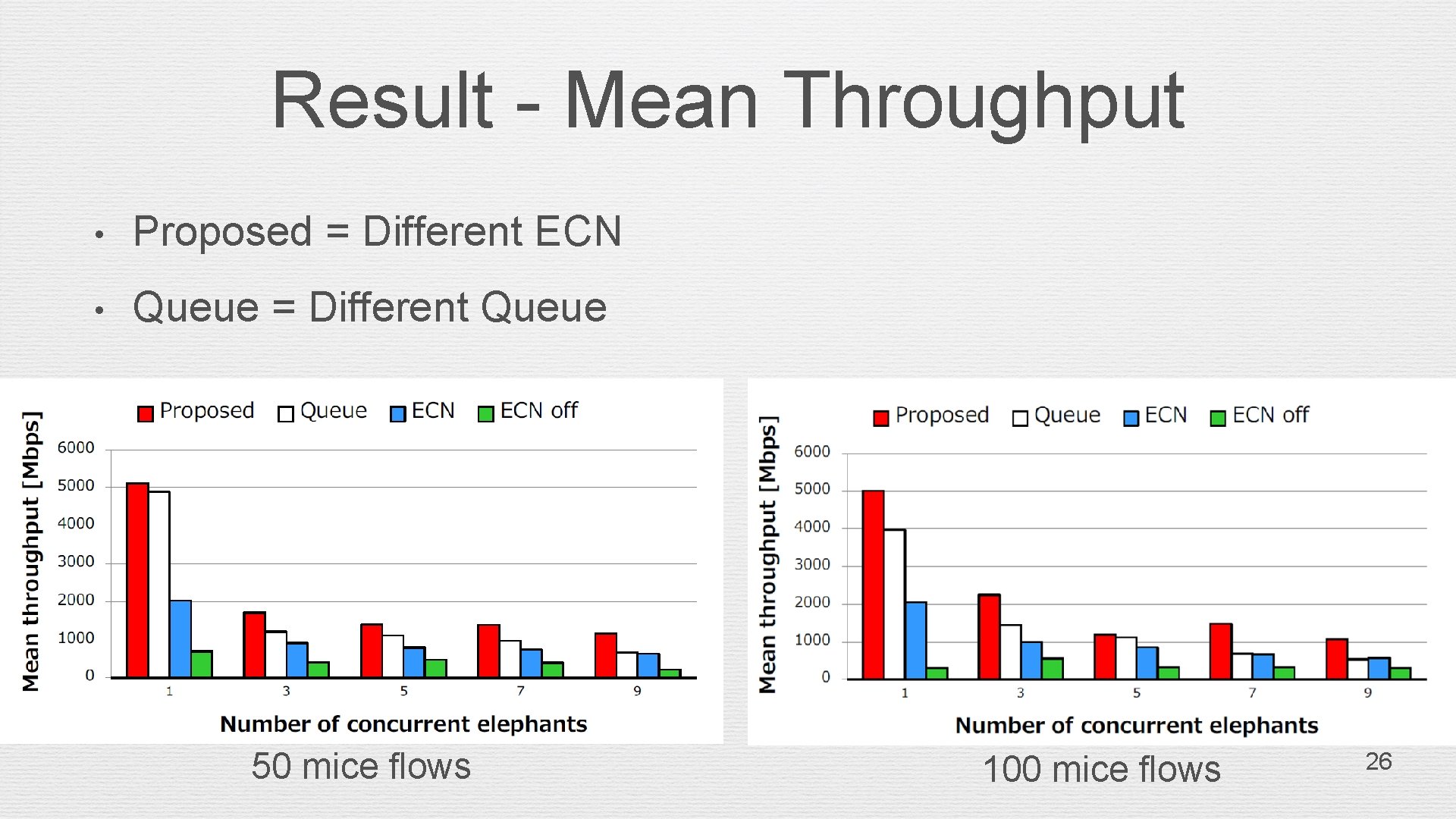
Result - Mean Throughput • Proposed = Different ECN • Queue = Different Queue 50 mice flows 100 mice flows 26
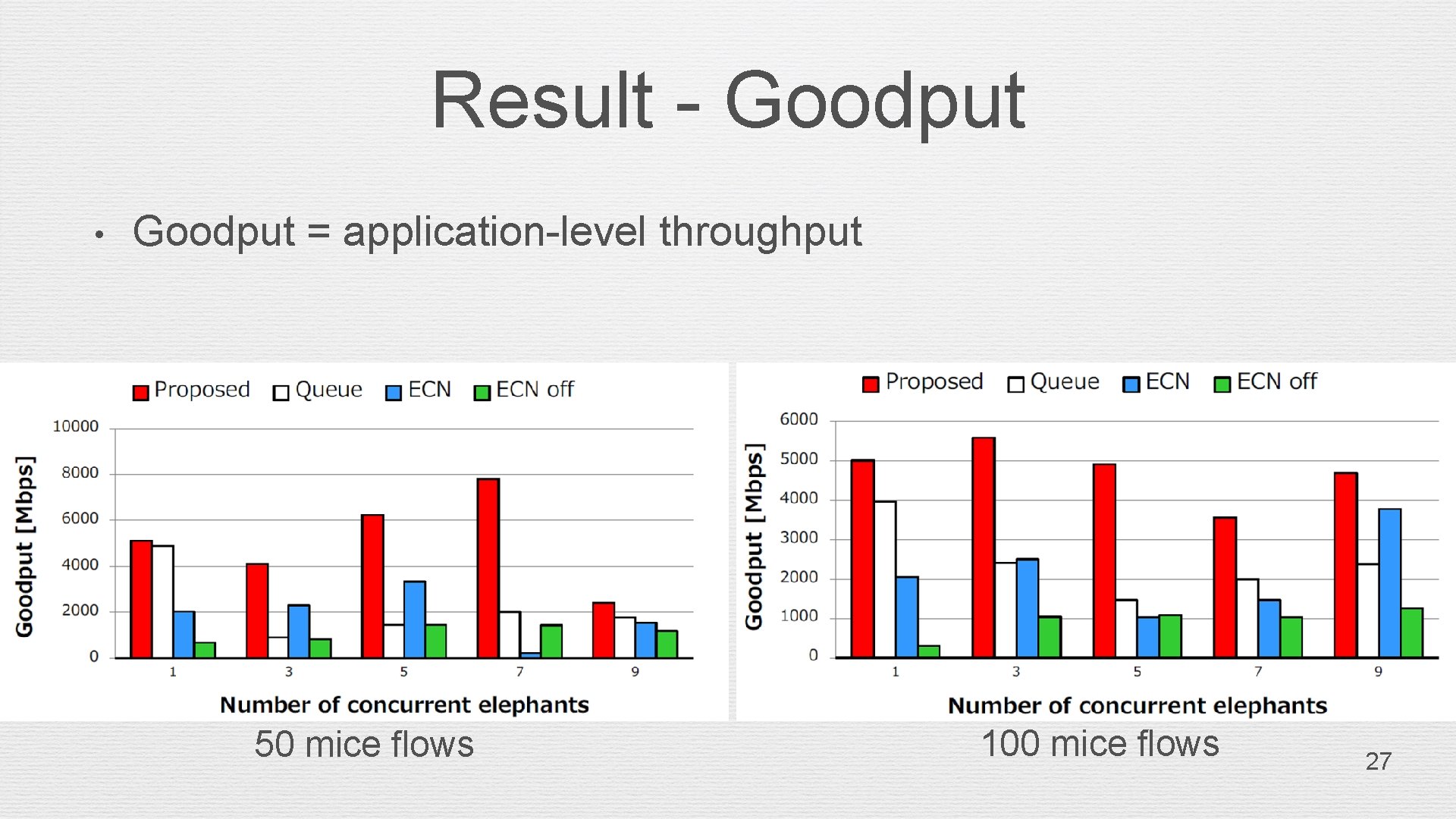
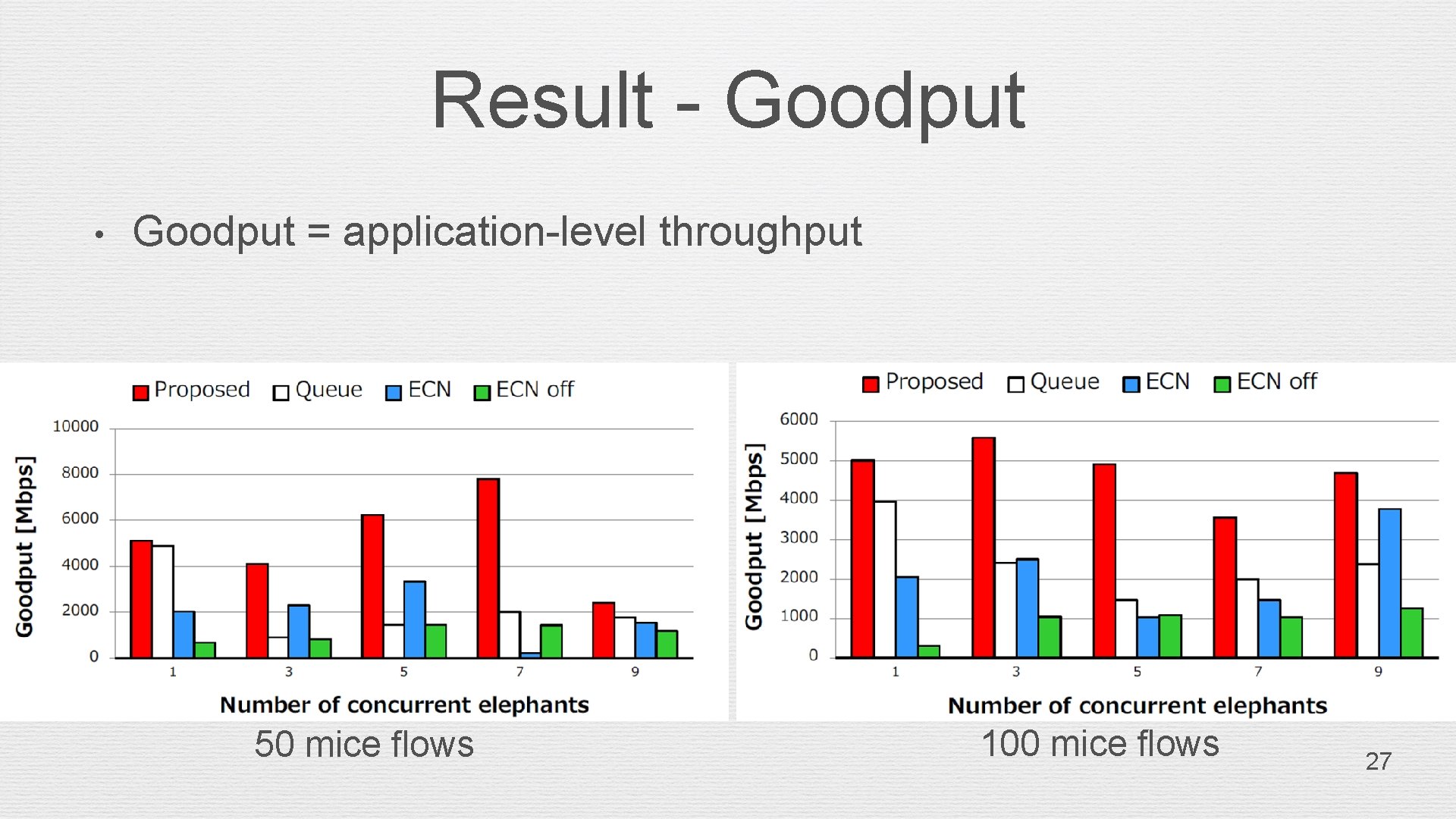
Result - Goodput • Goodput = application-level throughput 50 mice flows 100 mice flows 27
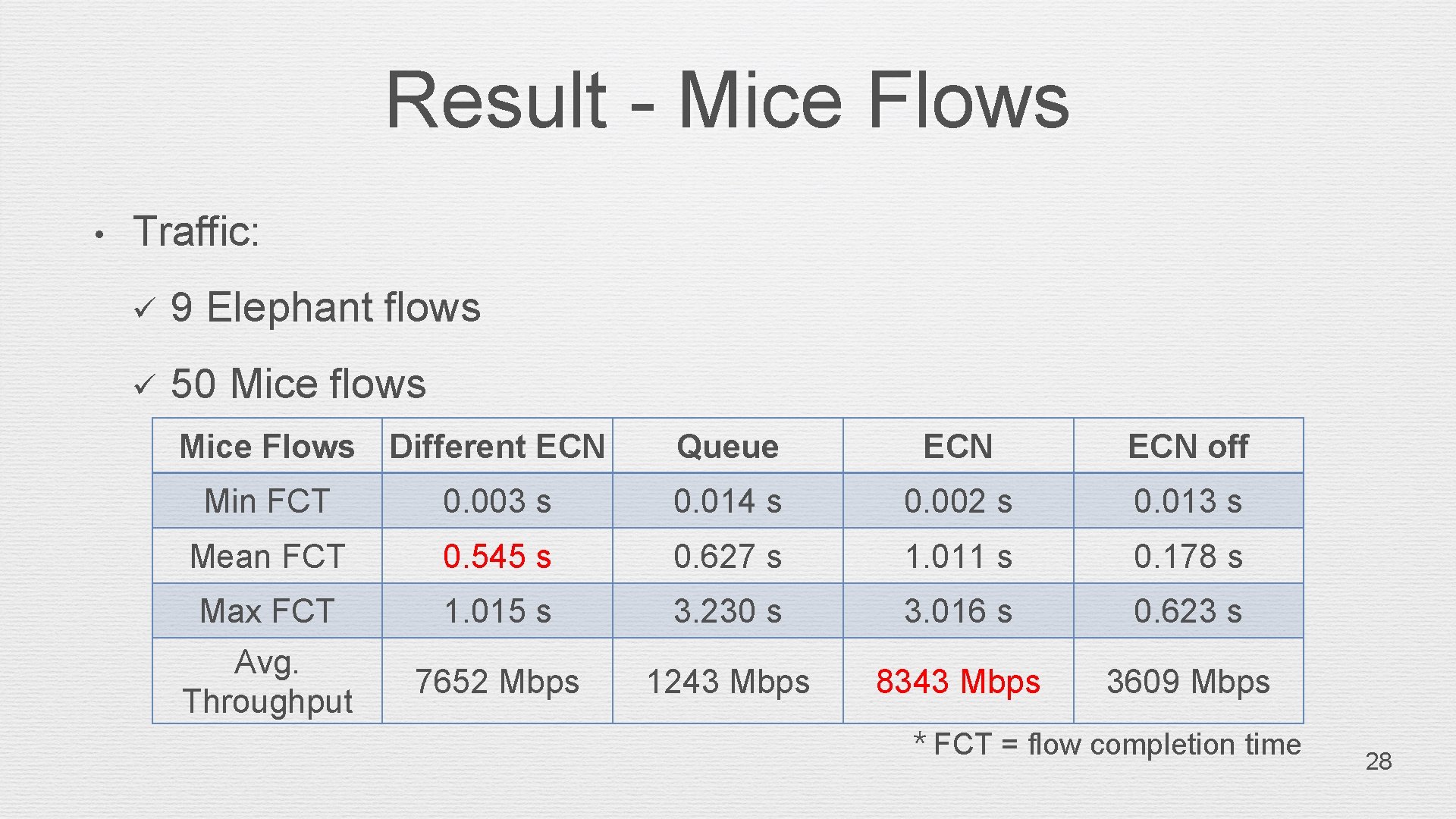
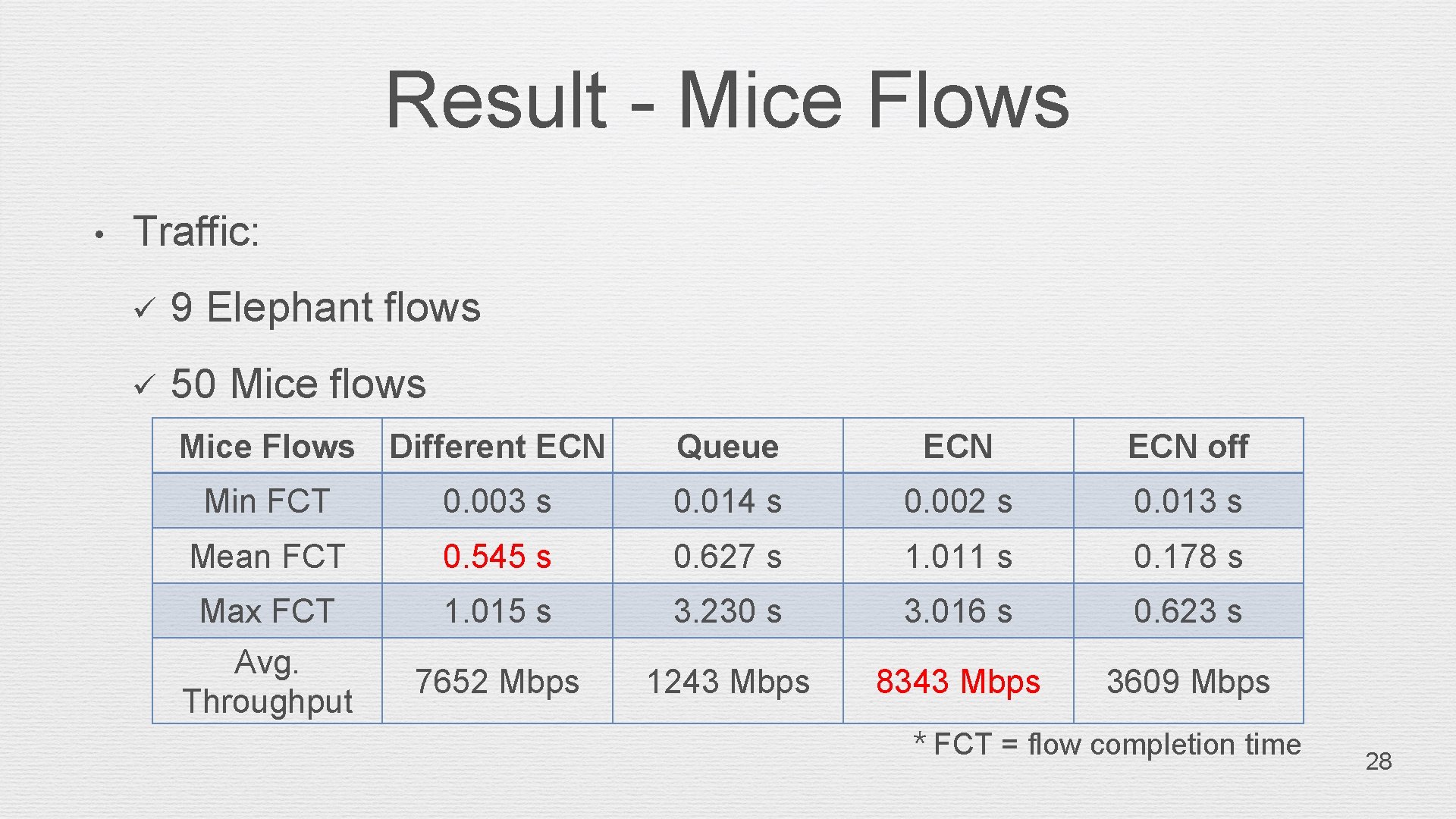
Result - Mice Flows • Traffic: ü 9 Elephant flows ü 50 Mice flows Mice Flows Different ECN Queue ECN off Min FCT 0. 003 s 0. 014 s 0. 002 s 0. 013 s Mean FCT 0. 545 s 0. 627 s 1. 011 s 0. 178 s Max FCT 1. 015 s 3. 230 s 3. 016 s 0. 623 s Avg. Throughput 7652 Mbps 1243 Mbps 8343 Mbps 3609 Mbps * FCT = flow completion time 28
Result (Cont. ) Elephant flow • Throughput: Different ECN > Queue > ECN off Mice flow • Mean of FCT: ECN off > Different ECN > Queue > ECN • Average throughput: ECN > Different ECN > ECN off > Queue 29
Future Directions • With Qo. S mechanism • Congestion Control and Qo. S use rerouting first. • If path load is full than: ü Elephant flow with Qo. S without Congestion control ü Mice flow with congestion control 30
References • Lee, Chunghan, et al. "Flow-Aware Congestion Control to Improve Throughput under TCP Incast in Datacenter Networks, “ in Computer Software and Applications Conference (COMPSAC), 2015, pp. 155 -162. • Gholami, M. , & Akbari, B. “Congestion Control in Software Defined Data Center Networks Through Flow Rerouting, ” in 2015 23 rd Iranian Conference on Electrical Engineering (ICEE), 2015, pp. 654 -657. • S. Fang, Y. Yu, C. H. Foh and K. M. M. Aung. “A loss-free multipathing solution for data center network using software-defined networking approach, ” IEEE Trans. Magn. , vol. 49, no. 6, pp. 2723 -2730, Jun. , 2013. • M. F. Bari, S. R. Chowdhury, R. Ahmed, and R. Boutaba, “Policy. Cop: An autonomic Qo. S policy enforcement framework for software defined networks, ” in Proc. IEEE SDN Future Netw. Serv. (SDN 4 FNS), Nov. 2013, pp. 1– 7 31
References • Open v. Switch and the Intelligent Edge, http: //openvswitch. org/pipermail/announce/2014 -May/000066. html. 32