Configurable computing for highsecurityhighperformance ambient systems 1 Guy
Configurable computing for high-security/high-performance ambient systems 1 Guy Gogniat, Lilian Bossuet, Wayne Burleson, LESTER Laboratory, University of South Britanny (UBS), Lorient, France guy. gogniat@univ-ubs. fr; lilian. bossuet@univ-ubs. fr 1 This Department of Electrical and Computer Engineering, University of Massachusetts, Amherst, MA 01003 -9284 USA burleson@ecs. umass. edu research This work is supported by the French DGA DSP/SREA under contract no. ERE 0460 00 010 Department of Electrical and Computer Engineering
Outline § Attacks and countermeasures on embedded systems § Reconfigurable architectures § Security and reconfigurable architectures § AES case study § Conclusions Department of Electrical and Computer Engineering 2
Outline § Attacks and countermeasures on embedded systems § § Reconfigurable architectures Security and reconfigurable architectures AES case study Conclusions Department of Electrical and Computer Engineering 3
Security and attacks § Security Objectives • § Security is required in order to guaranty: • The protection of private data (typically key, PIN, secret or confidential data) • The protection of the design (typically some IPs) • The protection of the system (typically its functionality, so that nobody else can control the system) Attack Objectives • Attacks aim to break security in order to get access to: • Private data so that changing some values, copying the data or destroying the data • The design so that changing some modules, copying the design or destroying the design • The system so that changing its behavior or destroying the system Department of Electrical and Computer Engineering 4
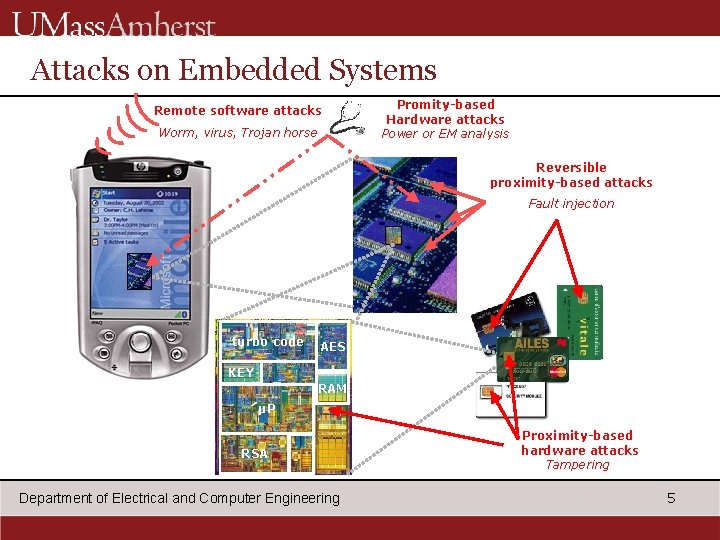
Attacks on Embedded Systems Remote software attacks Worm, virus, Trojan horse Promity-based Hardware attacks Power or EM analysis Reversible proximity-based attacks Fault injection turbo code AES KEY RAM µP RSA RAM Department of Electrical and Computer Engineering Proximity-based hardware attacks Tampering 5
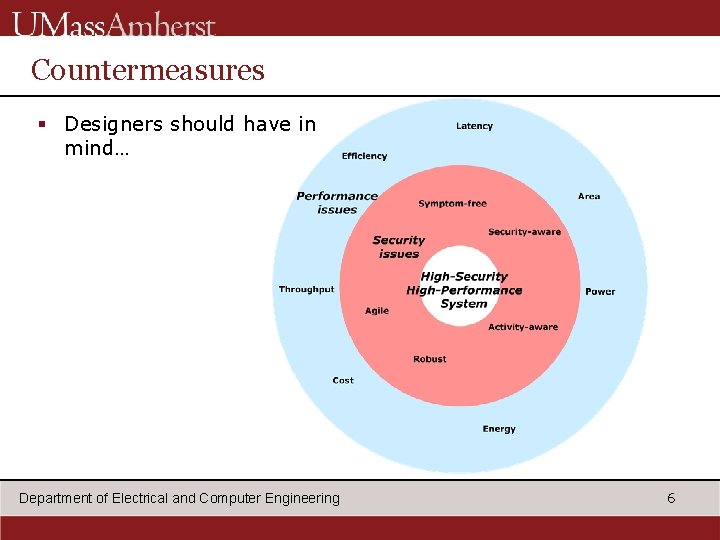
Countermeasures § Designers should have in mind… Department of Electrical and Computer Engineering 6
Outline § Attacks and countermeasures on embedded systems § Reconfigurable architectures § Security and reconfigurable architectures § AES case study § Conclusions Department of Electrical and Computer Engineering 7
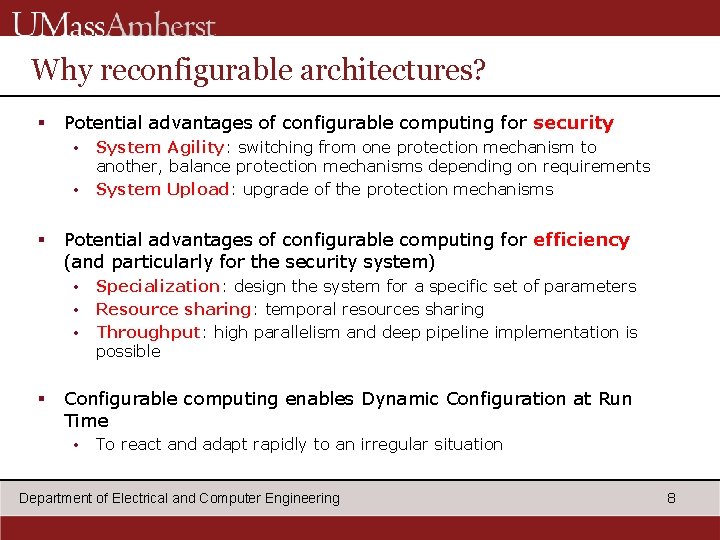
Why reconfigurable architectures? § Potential advantages of configurable computing for security • • § Potential advantages of configurable computing for efficiency (and particularly for the security system) • • • § System Agility: switching from one protection mechanism to another, balance protection mechanisms depending on requirements System Upload: upgrade of the protection mechanisms Specialization: design the system for a specific set of parameters Resource sharing: temporal resources sharing Throughput: high parallelism and deep pipeline implementation is possible Configurable computing enables Dynamic Configuration at Run Time • To react and adapt rapidly to an irregular situation Department of Electrical and Computer Engineering 8
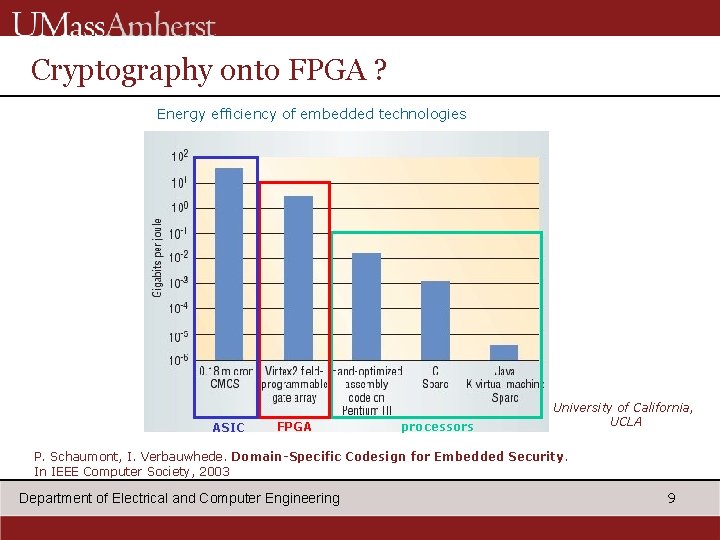
Cryptography onto FPGA ? Energy efficiency of embedded technologies ASIC FPGA processors University of California, UCLA P. Schaumont, I. Verbauwhede. Domain-Specific Codesign for Embedded Security. In IEEE Computer Society, 2003 Department of Electrical and Computer Engineering 9
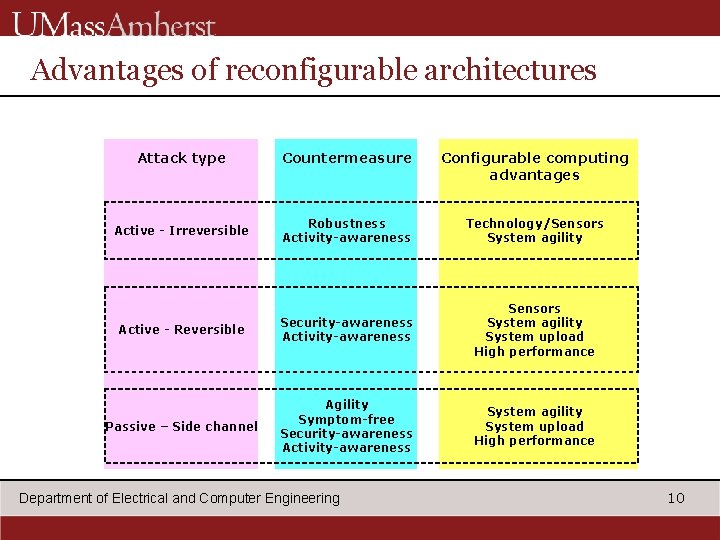
Advantages of reconfigurable architectures Attack type Countermeasure Configurable computing advantages Active - Irreversible Robustness Activity-awareness Technology/Sensors System agility Active - Reversible Security-awareness Activity-awareness Sensors System agility System upload High performance Passive – Side channel Agility Symptom-free Security-awareness Activity-awareness System agility System upload High performance Department of Electrical and Computer Engineering 10
Outline § Attacks and countermeasures on embedded systems § Reconfigurable architectures § Security and reconfigurable architectures § AES case study § Conclusions Department of Electrical and Computer Engineering 11
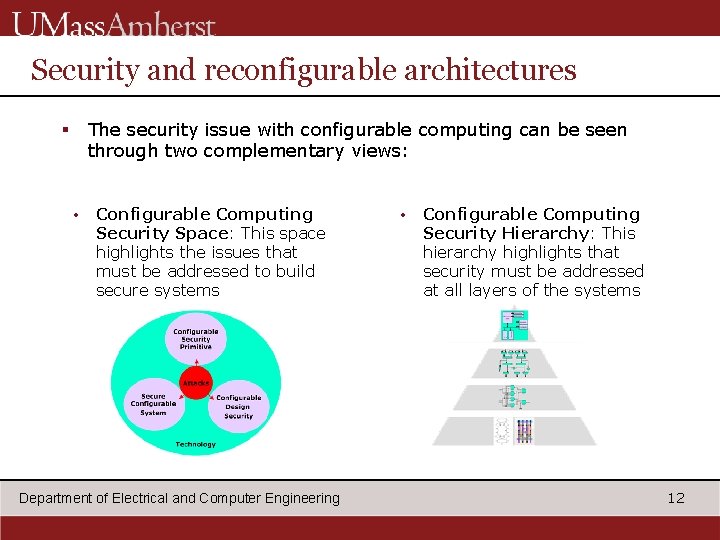
Security and reconfigurable architectures The security issue with configurable computing can be seen through two complementary views: § • Configurable Computing Security Space: This space highlights the issues that must be addressed to build secure systems Department of Electrical and Computer Engineering • Configurable Computing Security Hierarchy: This hierarchy highlights that security must be addressed at all layers of the systems 12
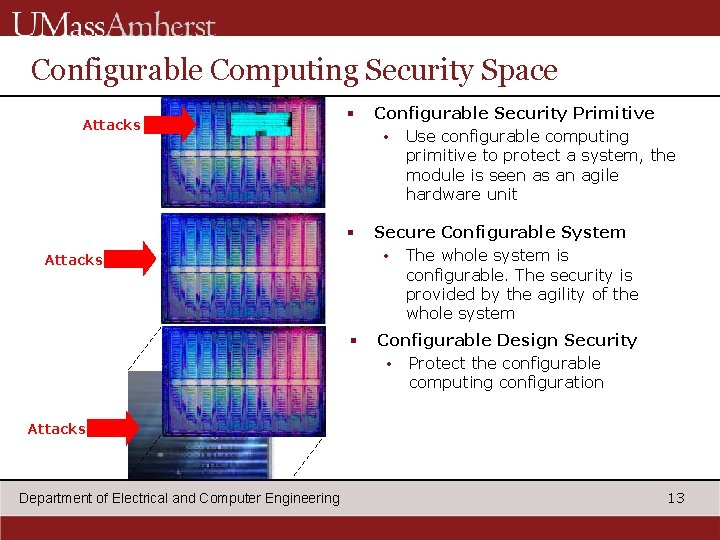
Configurable Computing Security Space Attacks § Configurable Security Primitive • Use configurable computing primitive to protect a system, the module is seen as an agile hardware unit § Secure Configurable System • The whole system is configurable. The security is provided by the agility of the whole system § Configurable Design Security • Protect the configurable computing configuration Attacks Department of Electrical and Computer Engineering 13
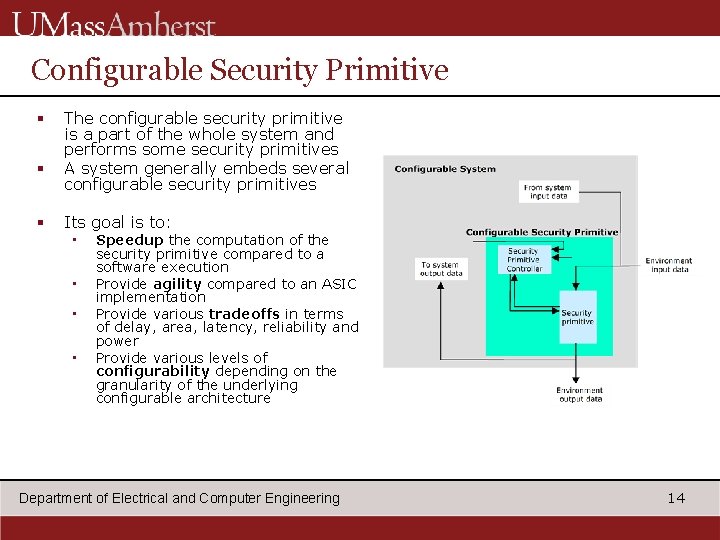
Configurable Security Primitive § § § The configurable security primitive is a part of the whole system and performs some security primitives A system generally embeds several configurable security primitives Its goal is to: • • Speedup the computation of the security primitive compared to a software execution Provide agility compared to an ASIC implementation Provide various tradeoffs in terms of delay, area, latency, reliability and power Provide various levels of configurability depending on the granularity of the underlying configurable architecture Department of Electrical and Computer Engineering 14
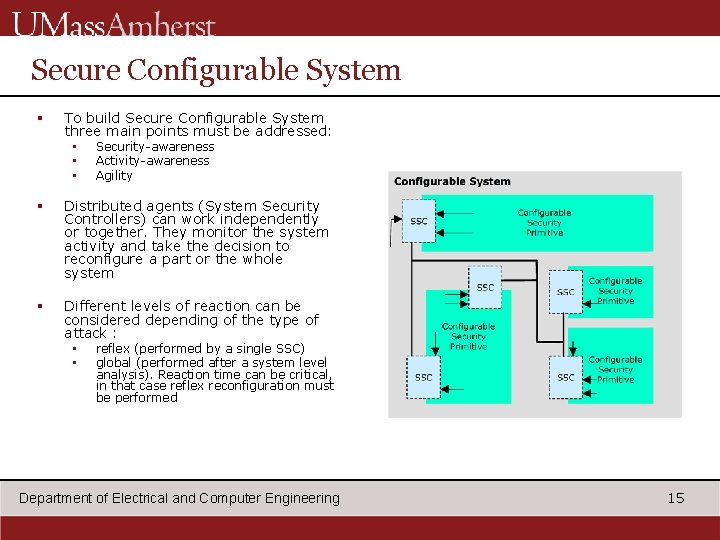
Secure Configurable System § To build Secure Configurable System three main points must be addressed: • • • Security-awareness Activity-awareness Agility § Distributed agents (System Security Controllers) can work independently or together. They monitor the system activity and take the decision to reconfigure a part or the whole system § Different levels of reaction can be considered depending of the type of attack : • • reflex (performed by a single SSC) global (performed after a system level analysis). Reaction time can be critical, in that case reflex reconfiguration must be performed Department of Electrical and Computer Engineering 15
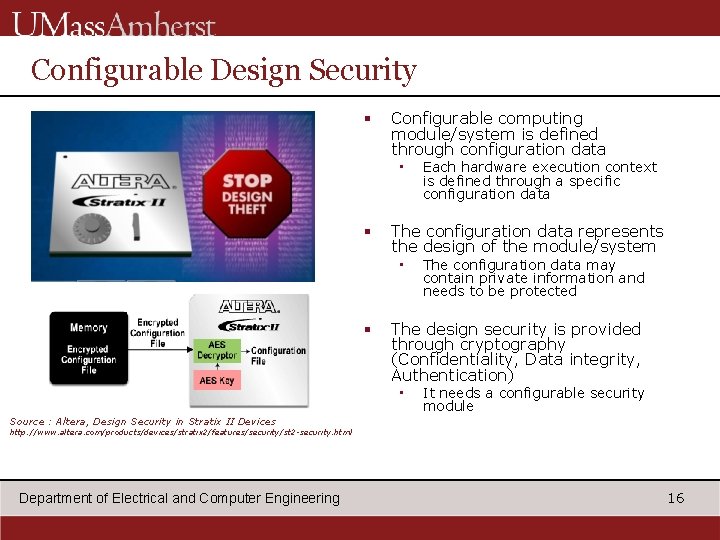
Configurable Design Security § Configurable computing module/system is defined through configuration data • § The configuration data represents the design of the module/system • § Each hardware execution context is defined through a specific configuration data The configuration data may contain private information and needs to be protected The design security is provided through cryptography (Confidentiality, Data integrity, Authentication) • It needs a configurable security module Source : Altera, Design Security in Stratix II Devices http: //www. altera. com/products/devices/stratix 2/features/security/st 2 -security. html Department of Electrical and Computer Engineering 16
Outline § § Attacks on embedded systems Countermeasures Reconfigurable architectures Security and reconfigurable architectures § AES case study § Conclusions Department of Electrical and Computer Engineering 17
Agility leverages security § At the system and architectural level (Secure Configurable System and Configurable security module) agility is provided through reconfiguration § How can it be performed? Need to deal with these points: • • Self-reconfiguration or Remote-reconfiguration Partial or full reconfiguration, Dynamic or static reconfiguration Predefined configuration data or dynamic configuration data Reconfiguration time Configuration memory Communication links Configuration controller (what is the policy? ) Department of Electrical and Computer Engineering 18
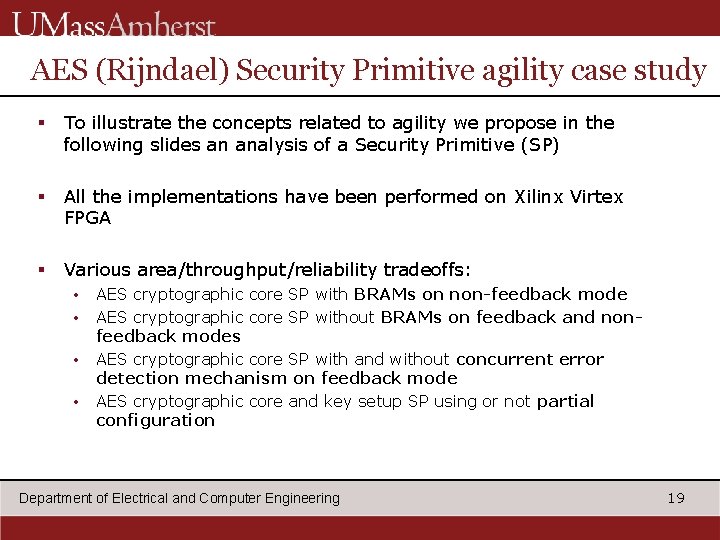
AES (Rijndael) Security Primitive agility case study § To illustrate the concepts related to agility we propose in the following slides an analysis of a Security Primitive (SP) § All the implementations have been performed on Xilinx Virtex FPGA § Various area/throughput/reliability tradeoffs: • • AES cryptographic core SP with BRAMs on non-feedback mode AES cryptographic core SP without BRAMs on feedback and nonfeedback modes AES cryptographic core SP with and without concurrent error detection mechanism on feedback mode AES cryptographic core and key setup SP using or not partial configuration Department of Electrical and Computer Engineering 19
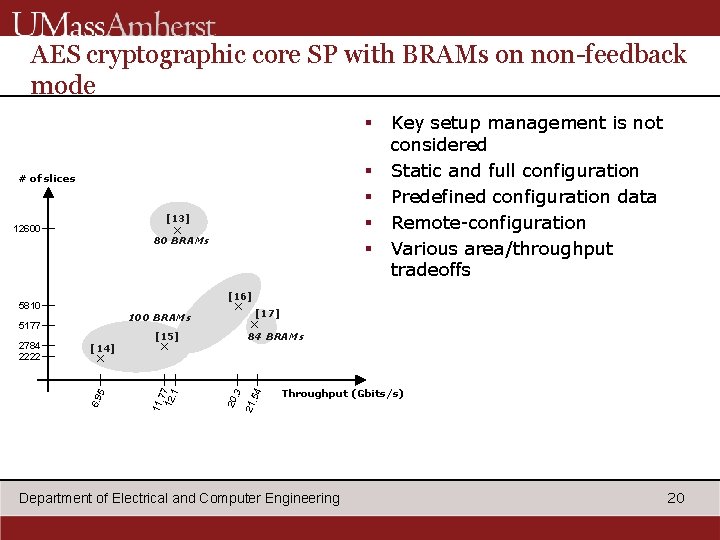
AES cryptographic core SP with BRAMs on non-feedback mode § § § # of slices [13] × 12600 80 BRAMs [16] [15] 84 BRAMs × . 54 6. 9 5 × [17] × . 3 [14] 11. 7 12 7. 1 5177 × Throughput (Gbits/s) 21 100 BRAMs 20 5810 2784 2222 Key setup management is not considered Static and full configuration Predefined configuration data Remote-configuration Various area/throughput tradeoffs Department of Electrical and Computer Engineering 20
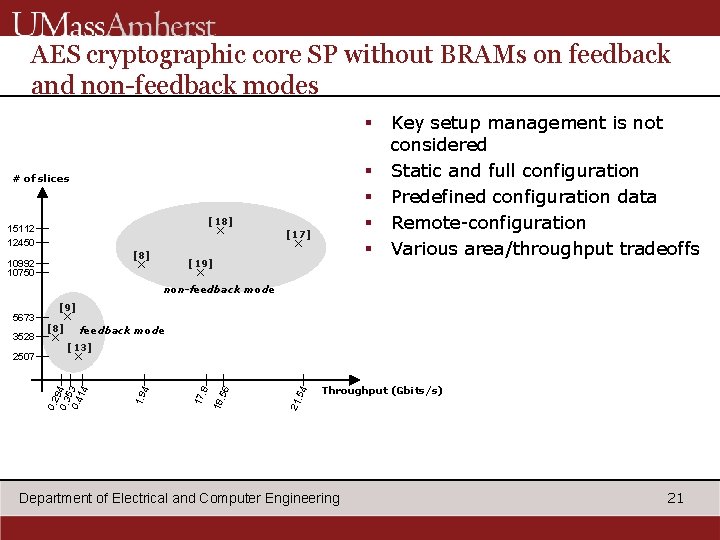
AES cryptographic core SP without BRAMs on feedback and non-feedback modes § § § # of slices [18] × 15112 12450 [8] × 10992 10750 [17] × [19] Key setup management is not considered Static and full configuration Predefined configuration data Remote-configuration Various area/throughput tradeoffs × non-feedback mode × feedback mode [13] . 54 Throughput (Gbits/s) 21 . 56 18 17 . 8 × 0. 2 9 0. 3 4 53 0. 4 14 2507 × [8] 4 3528 [9] 1. 9 5673 Department of Electrical and Computer Engineering 21
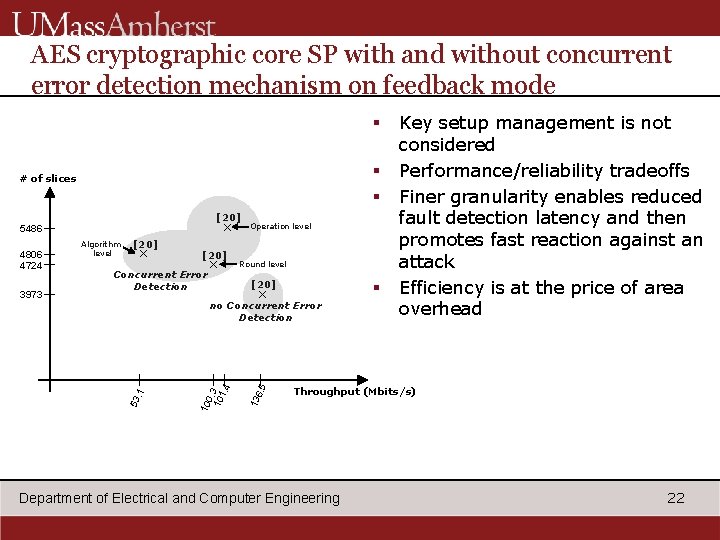
AES cryptographic core SP with and without concurrent error detection mechanism on feedback mode § § § # of slices [20] × 5486 [20] × Concurrent Error Detection Round level § [20] × Throughput (Mbits/s) 13 53 6. 5 no Concurrent Error Detection . 1 3973 Algorithm level 10 0. 10 3 1. 4 4806 4724 Operation level Key setup management is not considered Performance/reliability tradeoffs Finer granularity enables reduced fault detection latency and then promotes fast reaction against an attack Efficiency is at the price of area overhead Department of Electrical and Computer Engineering 22
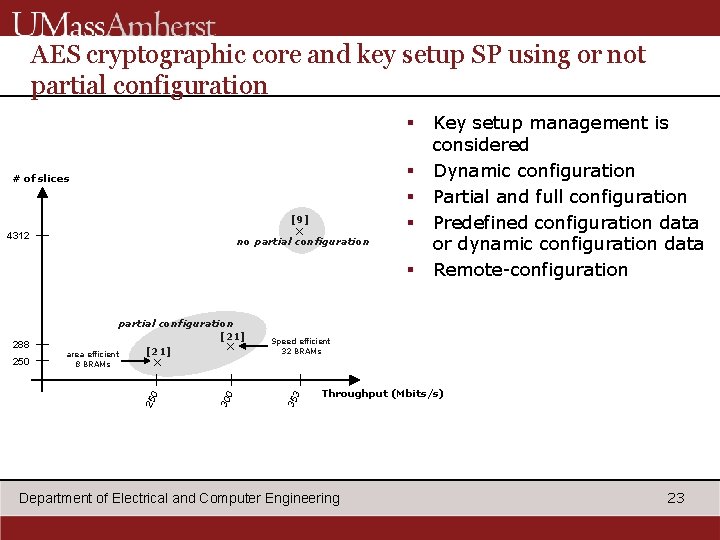
AES cryptographic core and key setup SP using or not partial configuration § § # of slices [9] × 4312 no partial configuration § 25 3 Speed efficient 32 BRAMs 35 × 0 8 BRAMs 0 250 30 288 partial configuration [21] × [21] area efficient Key setup management is considered Dynamic configuration Partial and full configuration Predefined configuration data or dynamic configuration data Remote-configuration Throughput (Mbits/s) Department of Electrical and Computer Engineering 23
Outline § § § Attacks on embedded systems Countermeasures Reconfigurable architectures Security and reconfigurable architectures AES case study § Conclusions Department of Electrical and Computer Engineering 24
Conclusions § Configurable computing presents significant features to target high-security/high performance ambient systems § It is time to extend the vision of security using configurable computing (Configurable computing is not just hardware accelerators for security primitives) § Two complementary views to guide the designer when facing with the difficult problem of system security § Key aspects related to agility are presented and illustrated through the AES security primitive § There are still many issues to make security commonplace dealing with configurable computing and to define the overhead costs that imply security mechanisms at the hardware level Department of Electrical and Computer Engineering 25
- Slides: 25