ComputerUserInput Behavioral Biometrics Dr Charles C Tappert Seidenberg
Computer-User-Input Behavioral Biometrics Dr. Charles C. Tappert Seidenberg School of CSIS, Pace University http: //csis. pace. edu/~ctappert/ SUBTITLE Gen. Cybersecurity Workshop at Pace University
Cybersecurity Affects Governments, Companies, and even Individuals Cybersecurity Threats 2018 Cyber Security, Terrorism, and Beyond How the Internet of Things (Io. T) Is Changing the Cybersecurity Landscape How Cyber Attacks Affect Individuals and How You can Help Keep them Safe Russian interference in the 2016 United States elections Cyberwarfare by Russia U. S. , Britain blame Russia for global cyber attack U. S. -U. K. Warning on Cyberattacks Includes Private Homes List of data breaches and cyber attacks in March 2018 Gen. Cybersecurity Workshop at Pace University
University Research and Projects in Cybersecurity University research and projects are typically on a considerably smaller scale than those undertaken by governments and companies However, there are some areas of cybersecurity where universities can make contributions In the area of biometrics we focus at Pace University on the less-studied biometrics because they have not been as extensively explored as the wellknown biometrics One of these areas is computer-user-input behavioral biometrics Gen. Cybersecurity Workshop at Pace University
What are Computer-User-Input Behavioral Biometrics Authentication or identification of individuals based on the unique way they interact with computer devices With desktop/laptop computers, it is the way people input text (motor control of keystroke input), the words and syntax they use (stylometry), the intent (semantics) of the input, as well as the way they move a mouse With smartphones, and to some extent tablets, it concerns all of the above, and everything from how the user holds the phone to how they swipe the screen to which keyboard or gestural shortcuts they use Of the various biometrics we focus on these at Pace University because they have not been as extensively studied as the well-known biometrics Gen. Cybersecurity Workshop at Pace University
Importance of Computer-Input Biometrics to Identify or Authenticate Computer Users DARPA: Active Authentication – Do. D wants to continually authenticate all gov’t computer users Phase 1: 2010 and 2012 – authenticate users on desktops/laptops 2: 2013 and 2015 – authenticate users on mobile devices 3: 2016 - implementation DARPA: Enhanced Attribution – Do. D wants technology to attribute actions in cyberspace to individuals 2016 -2020 – network behavior and activity tracking of individuals, fusing generated data for predictive analysis Gen. Cybersecurity Workshop at Pace University
Importance of Computer-Input Biometrics to Identify or Authenticate Computer Users U. S. Higher Education Opportunity Act of 2008 Concerns authentication of students taking online tests Universities are using more online courses Requires institutions of higher learning to adopt new identification technologies as they become available To assure students of record are those accessing the systems and taking the exams in online courses Gen. Cybersecurity Workshop at Pace University
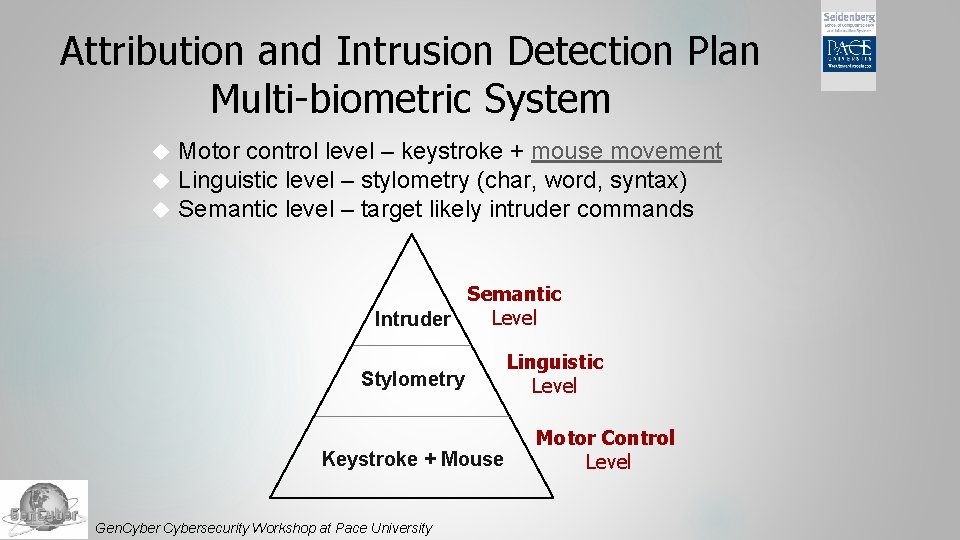
Attribution and Intrusion Detection Plan Multi-biometric System Motor control level – keystroke + mouse movement Linguistic level – stylometry (char, word, syntax) Semantic level – target likely intruder commands Semantic Level Intruder Stylometry Keystroke + Mouse Gen. Cybersecurity Workshop at Pace University Linguistic Level Motor Control Level

Keystroke Biometrics Based on idea that generated patterns are unique to individuals and difficult to duplicate Appeal of keystroke over other biometrics Not intrusive, inexpensive, continual user verification The keystroke biometric is one of the less-studied behavioral biometrics Gen. Cybersecurity Workshop at Pace University
Pace Univ. Keystroke Biometric Studies Most literature studies have been on short input of a few seconds Pace University studies on desktop/laptop mechanical keyboards Commercial products on hardening passwords Short input of few seconds Vinnie Monaco, now at ARL, entered 2016 contest: we have World’s Best System Phone number – similar to CMU study (Ned Bakelman and Vinnie Monaco) Long text input of several minutes Online test taking (Mary Villani, John Stewart, Vinnie Monaco, Steve Kim) Impaired users – left hand, right hand, and both hands input (Gonzalo Perez) Pace University studies on mobile device touchscreens Numeric input – phone # – similar to CMU study (Mike Coakley) Features – pressure & location/area of finger press on keys, acceleration & gyroscope information Gen. Cybersecurity Workshop at Pace University Names are doctoral students
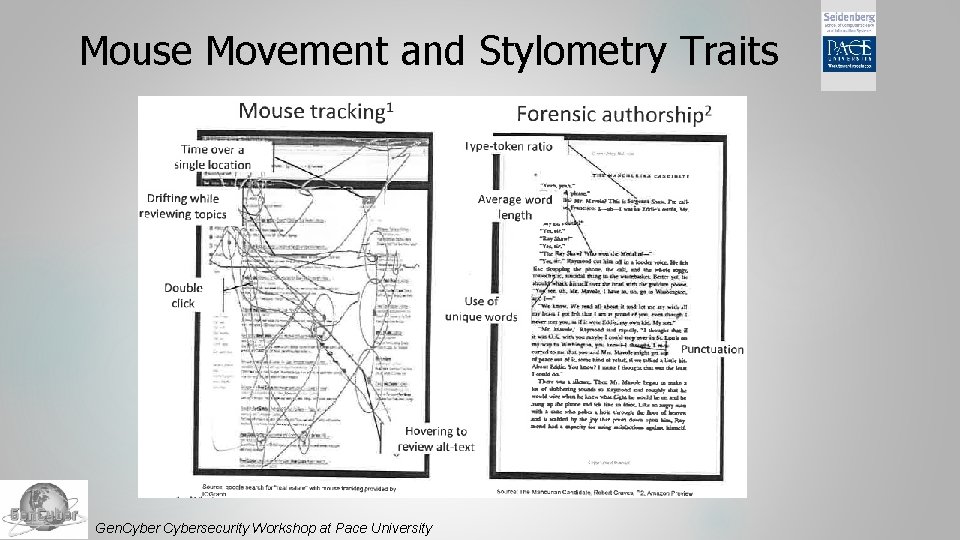
Mouse Movement and Stylometry Traits Gen. Cybersecurity Workshop at Pace University
Pace Univ. Mouse & Stylometry Studies Combining keystroke/stylometry info: John Stewart Stylometry can compliment keystroke analysis The correct student may be keying in the test answers provided by a coach, with the student merely typing the coach’s words This But would not be discovered via keystroke analysis potentially could through stylometry analysis Stylometry analysis of Facebook postings Dissertation study by Jenny Li Gen. Cybersecurity Workshop at Pace University
Interesting Related Videos IBM Trusteer Car Driving Biometric (2 min) AT&T: Cybersecurity for today’s digital world (7 min) The Five Most Dangerous New Attack Techniques – RSA Conf 2018 (44 min) Remarks by Secretary of Department Homeland Security – RSA Conf 2018 (35 min) Other Keynote presentations – RSA Conf 2018 RSA A View of the Future of Cyber. Security – RSA Conf 2017 (2 min) Kahn Academy Cybersecurity 101 Another keystroke biometric demo Gen. Cybersecurity Workshop at Pace University
Pace Univ. Dissertations and Papers Research 2018 Research Day Conference Analyzing 2017 The Expert Cybersecurity Twitter Accounts by Using Thesaurus Methods for Text Analytics Research Day Conference – stylometry examples below Correlation between the Topic and Emotion of Tweets through Machine Learning Sentiment Doctoral DPS Day Conference Proceedings Analysis of Twitter Messages Using Word 2 Vec of Professional Studies (DPS) program Doctoral Dissertations. Gen. Cybersecurity Workshop at Pace University
Copyright for Material Reuse This materials are developed under the support of the Gen. Cyber program of the National Security Agency and the Cyber. Corps program of the National Science Foundation. Copyright© 2018 Charles Tappert (ctappert@pace. edu), Pace University. Please properly acknowledge the source for any reuse of the materials as below. Charles Tappert, 2018 Gen. Cybersecurity Workshop, Pace University Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1. 3 or any later version published by the Free Software Foundation. A copy of the license is available at http: //www. gnu. org/copyleft/fdl. html. Gen. Cybersecurity Workshop at Pace University
Acknowledgment The authors would like to acknowledge the support from the Gen. Cyber program of the National Security Agency and the Cyber. Corps program of the National Science Foundation. Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author(s) and do not necessarily reflect the views of the National Science Foundation, the National Security Agency or the U. S. government. Gen. Cybersecurity Workshop at Pace University
- Slides: 15