Computer Transport Layer F Manages communication between two
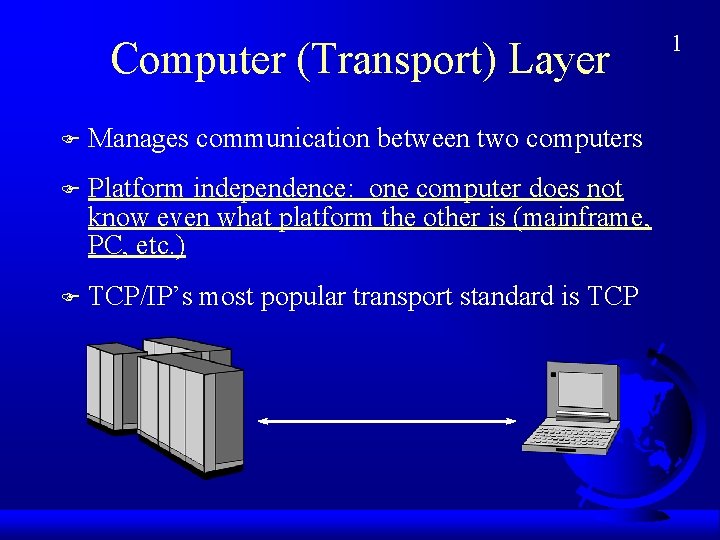
Computer (Transport) Layer F Manages communication between two computers F Platform independence: one computer does not know even what platform the other is (mainframe, PC, etc. ) F TCP/IP’s most popular transport standard is TCP 1
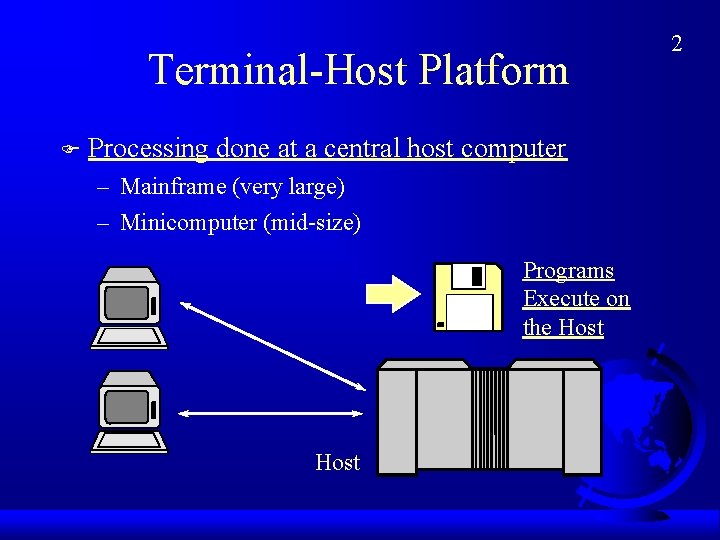
Terminal-Host Platform F Processing done at a central host computer – Mainframe (very large) – Minicomputer (mid-size) Programs Execute on the Host 2
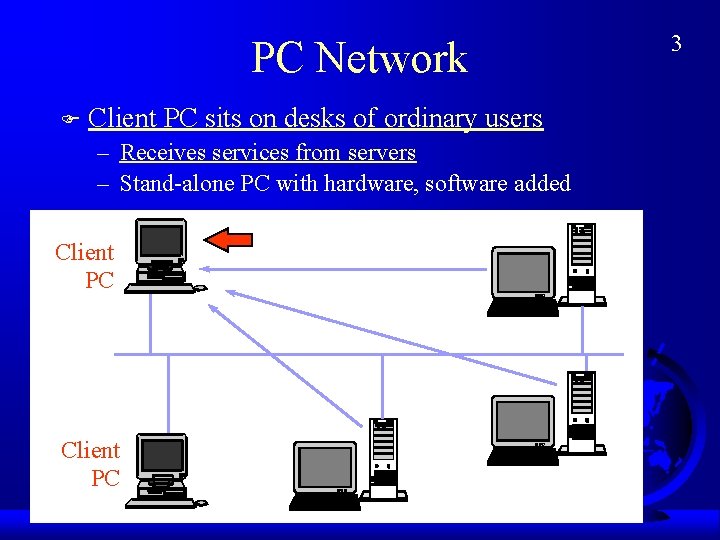
PC Network F Client PC sits on desks of ordinary users – Receives services from servers – Stand-alone PC with hardware, software added Client PC 3
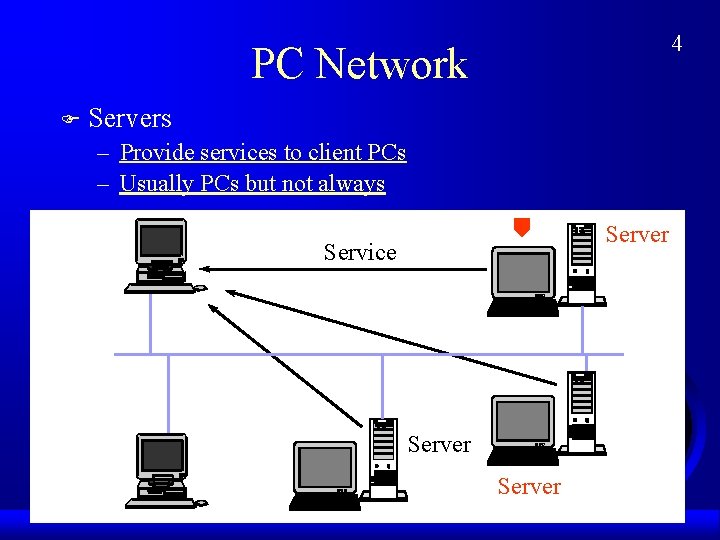
4 PC Network F Servers – Provide services to client PCs – Usually PCs but not always Server Service Server
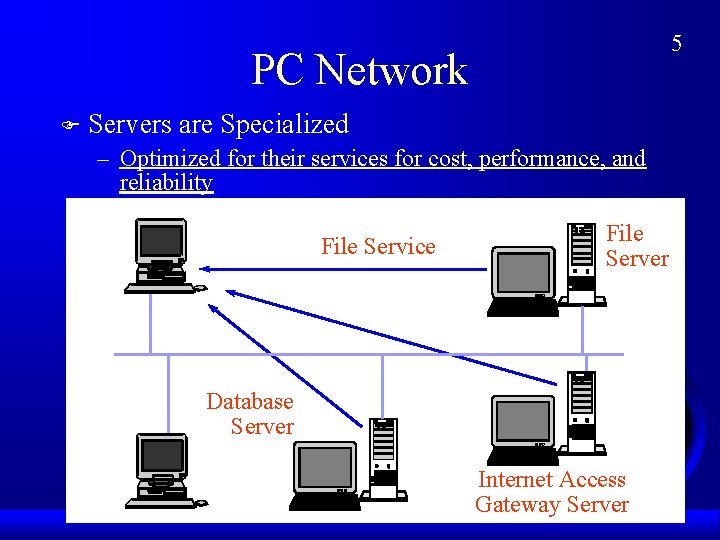
5 PC Network F Servers are Specialized – Optimized for their services for cost, performance, and reliability File Service File Server Database Server Internet Access Gateway Server
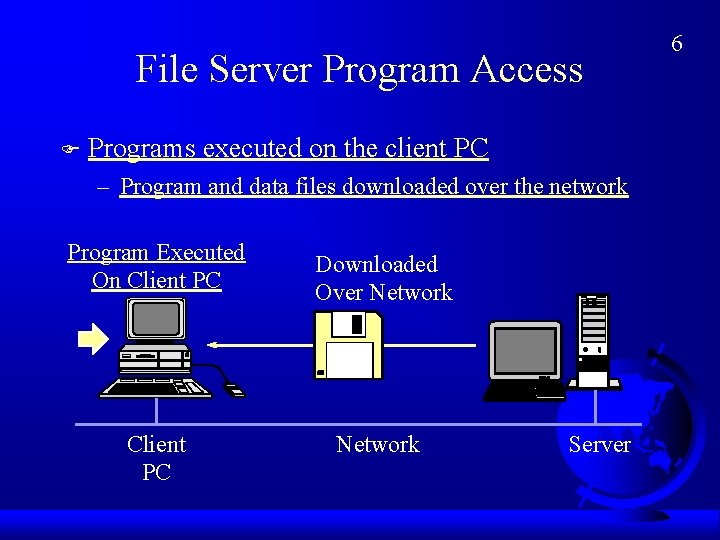
File Server Program Access F Programs executed on the client PC – Program and data files downloaded over the network Program Executed On Client PC Downloaded Over Network Client PC Network Server 6
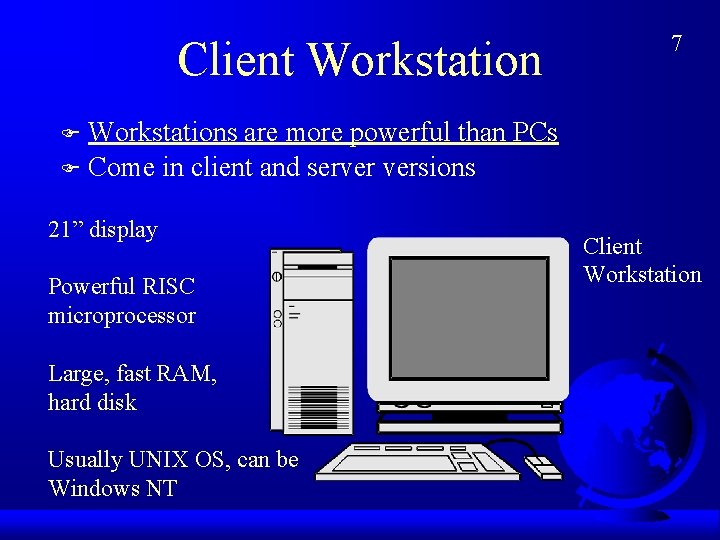
Client Workstation 7 Workstations are more powerful than PCs F Come in client and server versions F 21” display Powerful RISC microprocessor Large, fast RAM, hard disk Usually UNIX OS, can be Windows NT Client Workstation
Networked PC F The Dominant Computer Platform Today is the Networked PC – High penetration of PCs on desktops – Most are already networked F “Legacy” Systems Must be Maintained – Mainframe terminal-host systems – Minicomputer terminal-host systems – Many are being “downsized” to PC networking 8
Managed PCs F Designed to be Managed Remotely – Slashes maintenance costs – Slashes software upgrade costs – Users have less control over their machines – Company can search for illegal games – Management standards are still immature – Eventually, all networked PCs will be managed 9
Net. PC F Standard Pushed by Microsoft, Intel – Closed box with limited upgradability – Should ease maintenance by reducing incompatibilities and add-in problems – Will users be content? – Remote management built in 10
Network Computers (NCs) F Designed for Use on the Internet (Java) – Little or no local disk drive storage – Programs downloaded over Internet when needed (or from corporate servers using Internet standards) – User always gets the latest version of the software – Downloading can take time; small applications would load faster but might lack functionality – When the network is down, so are you The Internet 11
Low-Cost PCs for the Home F Web. TV 12 (Microsoft) – Uses TV for its display – User only needs $500 box – Problem: TV display resolution is far lower than that of a TV screen; webpages look bad – Problem: Need special Internet service provider who cannot work with your regular PC – Problem: No printing – Problem: Limited to WWW and email F Sub $1, 000 PCs
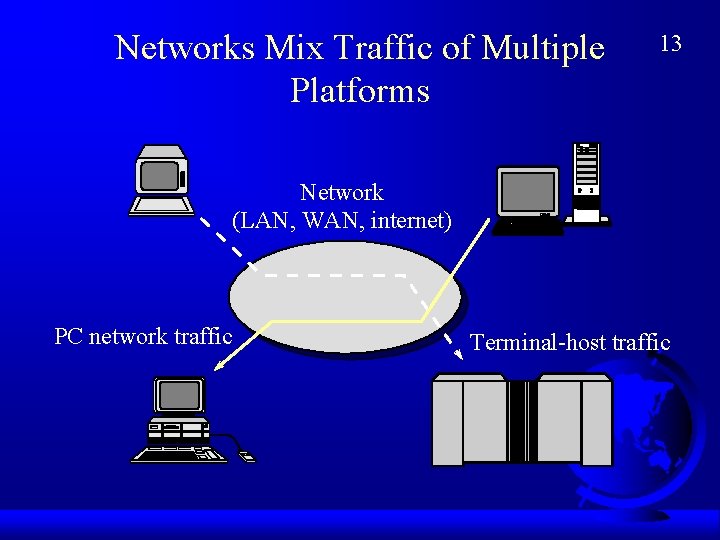
Networks Mix Traffic of Multiple Platforms 13 Network (LAN, WAN, internet) PC network traffic Terminal-host traffic
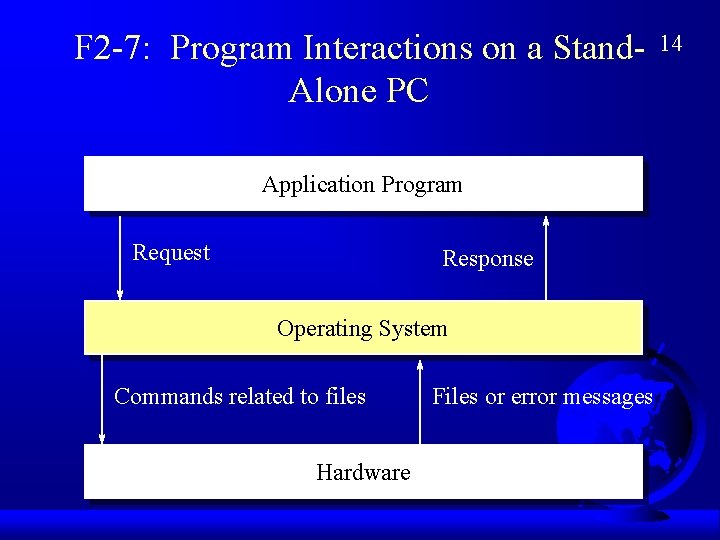
F 2 -7: Program Interactions on a Stand. Alone PC Application Program Request Response Operating System Commands related to files Hardware Files or error messages 14
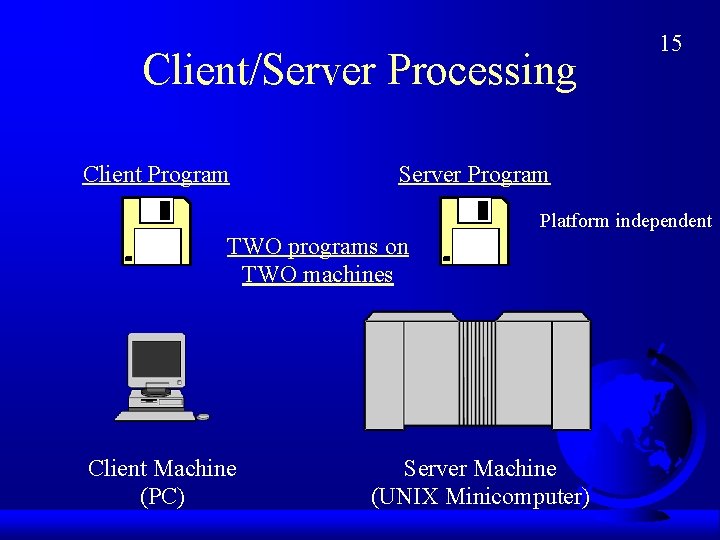
Client/Server Processing Client Program 15 Server Program Platform independent TWO programs on TWO machines Client Machine (PC) Server Machine (UNIX Minicomputer)
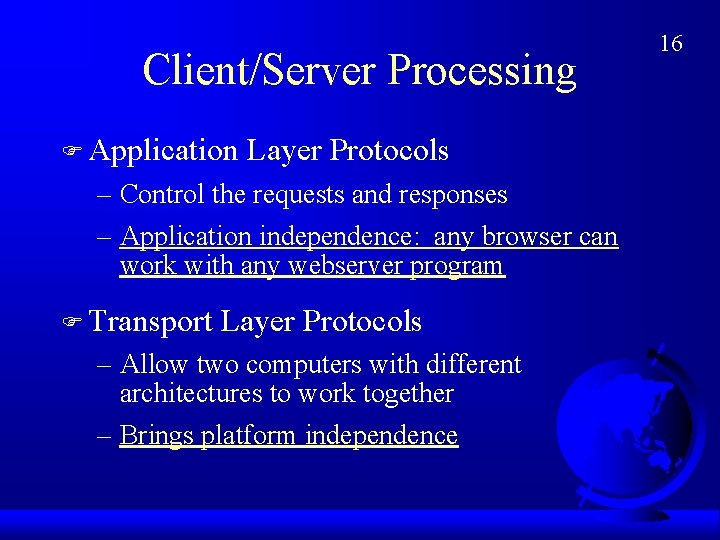
Client/Server Processing F Application Layer Protocols – Control the requests and responses – Application independence: any browser can work with any webserver program F Transport Layer Protocols – Allow two computers with different architectures to work together – Brings platform independence 16
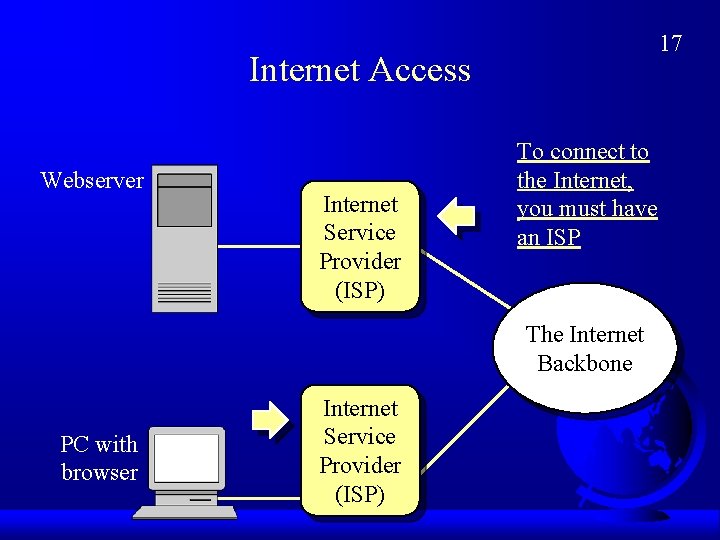
17 Internet Access Webserver Internet Service Provider (ISP) To connect to the Internet, you must have an ISP The Internet Backbone PC with browser Internet Service Provider (ISP)
Internet Service Provider (ISP) F Basic Service: Links You to the Internet – Provides a connection – Pays for your use. (The Internet is NOT Free. ) F Most Provide Additional Services – E-mail – World Wide Web Homepage Hosting – Premium Providers have Specialized Services (America Online, Compu. Serv, MSN) 18
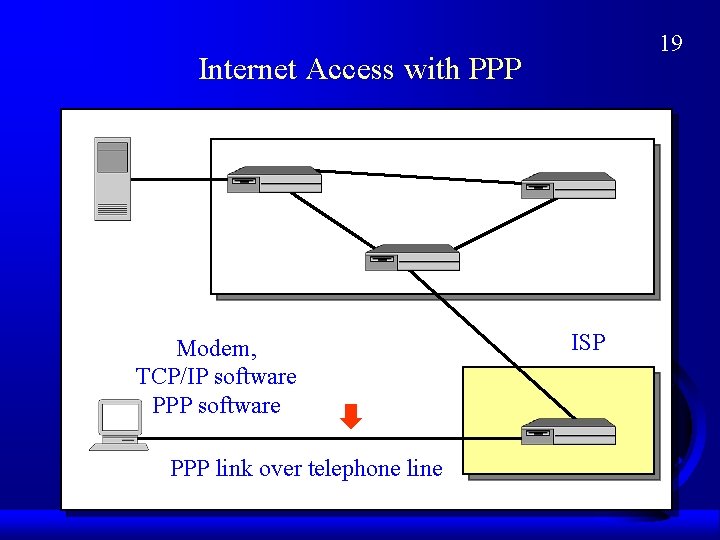
19 Internet Access with PPP Modem, TCP/IP software PPP link over telephone line ISP
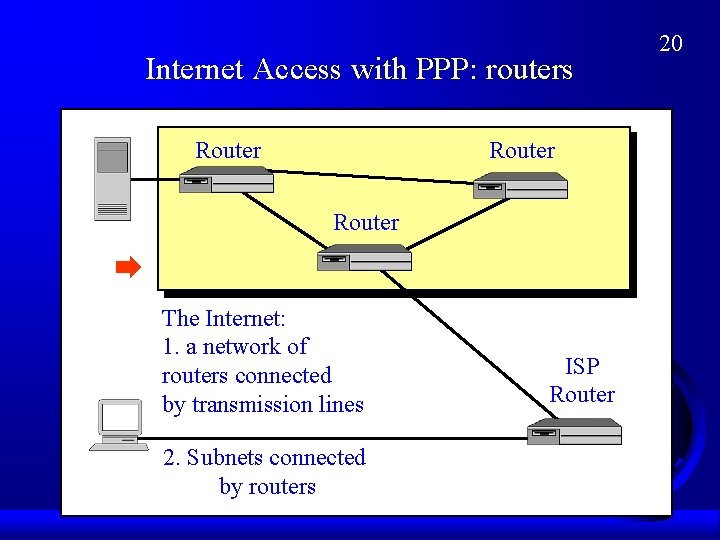
Internet Access with PPP: routers Router The Internet: 1. a network of routers connected by transmission lines 2. Subnets connected ISP by routers ISP Router 20
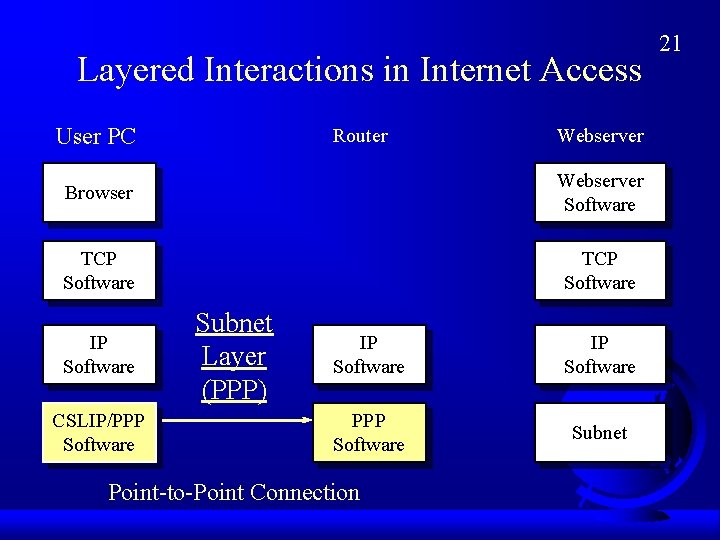
Layered Interactions in Internet Access User PC Router Webserver Browser Webserver Software TCP Software IP Software CSLIP/PPP Software Subnet Layer (PPP) IP Software PPP Software Subnet Point-to-Point Connection 21
Point-to-Point Connection F Physical Layer – Serial Port – Modem – Telephone Transmission F Data Link Layer – Packaging of data for delivery over line – Error detection and correction – CSLIP or PPP standard 22
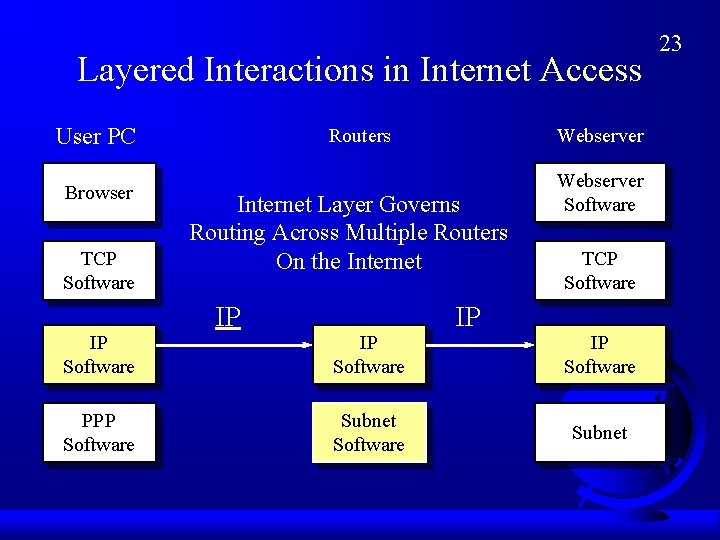
Layered Interactions in Internet Access User PC Browser TCP Software IP Software PPP Software Routers Webserver Internet Layer Governs Routing Across Multiple Routers On the Internet IP IP Software Subnet Software IP Webserver Software TCP Software IP Software Subnet 23
Routing Across the Internet F Routing – Message (packet) must travel over a network of routers – The user PC tells the first router the destination address of the webserver (e. g. , voyager. cba. hawaii. edu) – Working together, routers route the packet to its destination host 24
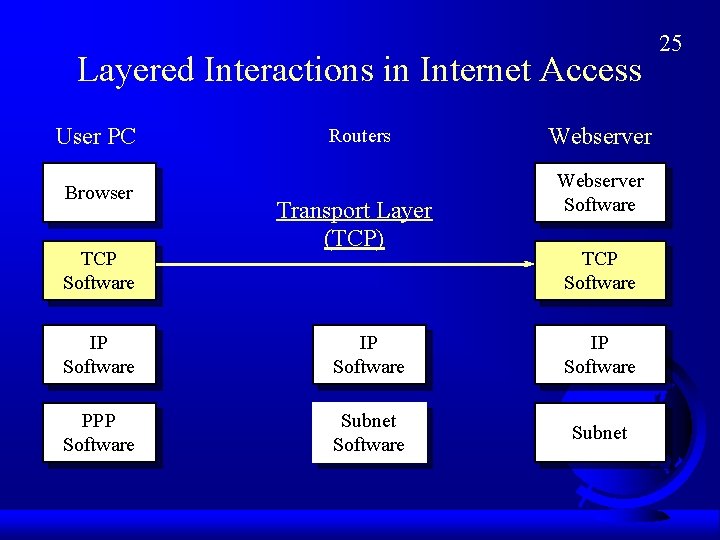
Layered Interactions in Internet Access User PC Browser TCP Software Routers Transport Layer (TCP) Webserver Software TCP Software IP Software PPP Software Subnet 25
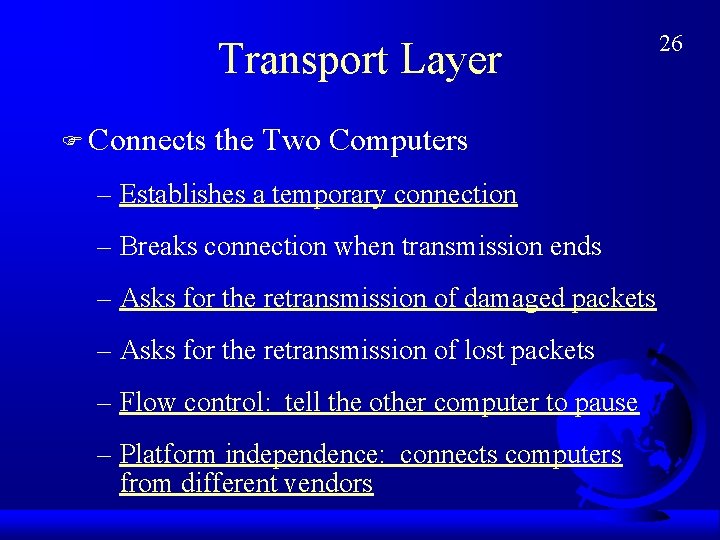
Transport Layer F Connects the Two Computers – Establishes a temporary connection – Breaks connection when transmission ends – Asks for the retransmission of damaged packets – Asks for the retransmission of lost packets – Flow control: tell the other computer to pause – Platform independence: connects computers from different vendors 26
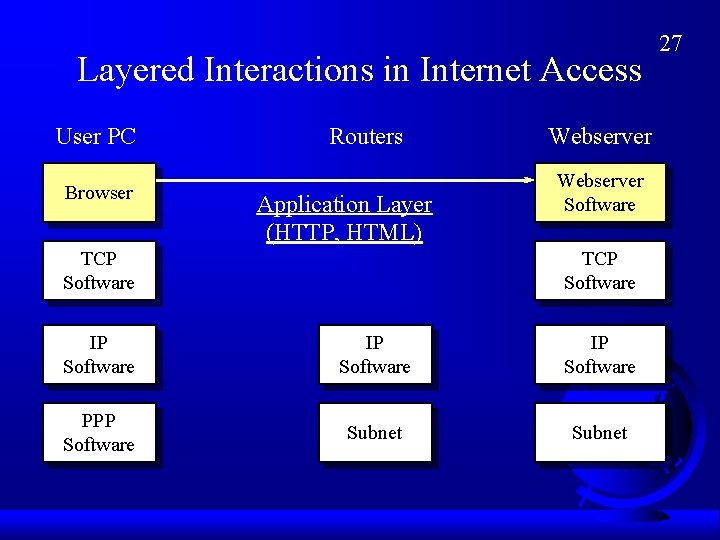
Layered Interactions in Internet Access User PC Browser Routers Application Layer (HTTP, HTML) TCP Software Webserver Software TCP Software IP Software PPP Software Subnet 27
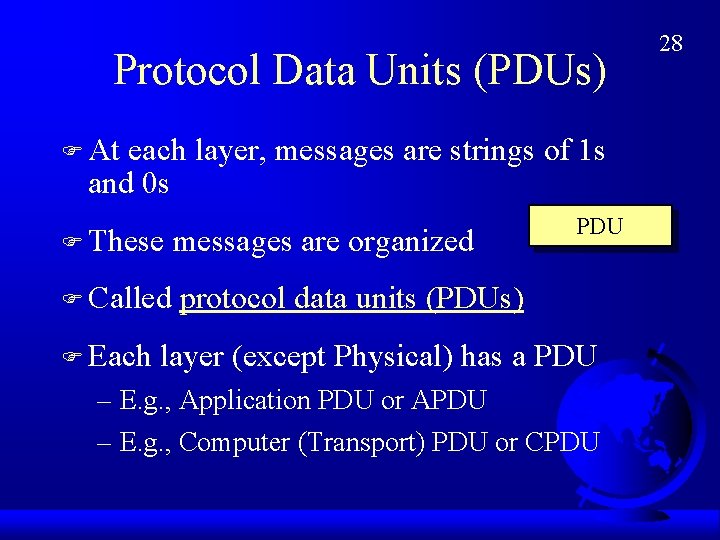
Protocol Data Units (PDUs) F At each layer, messages are strings of 1 s and 0 s F These messages are organized F Called protocol data units (PDUs) F Each PDU layer (except Physical) has a PDU – E. g. , Application PDU or APDU – E. g. , Computer (Transport) PDU or CPDU 28
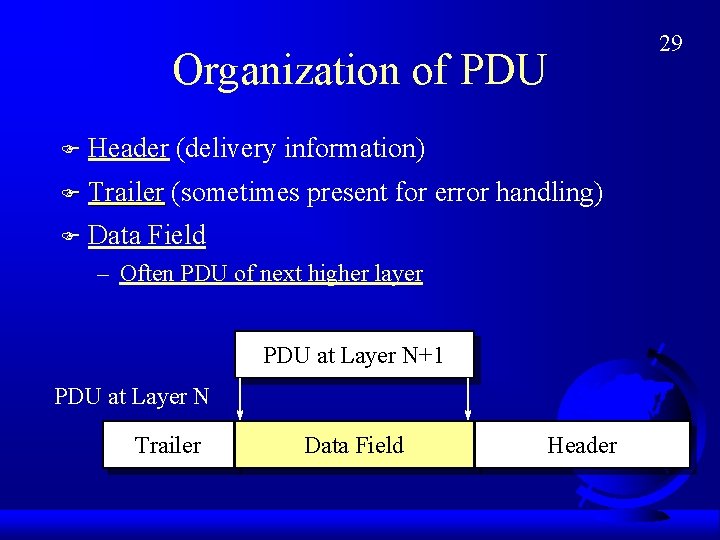
Organization of PDU F Header (delivery information) F Trailer (sometimes F present for error handling) Data Field – Often PDU of next higher layer PDU at Layer N+1 PDU at Layer N Trailer Data Field Header 29
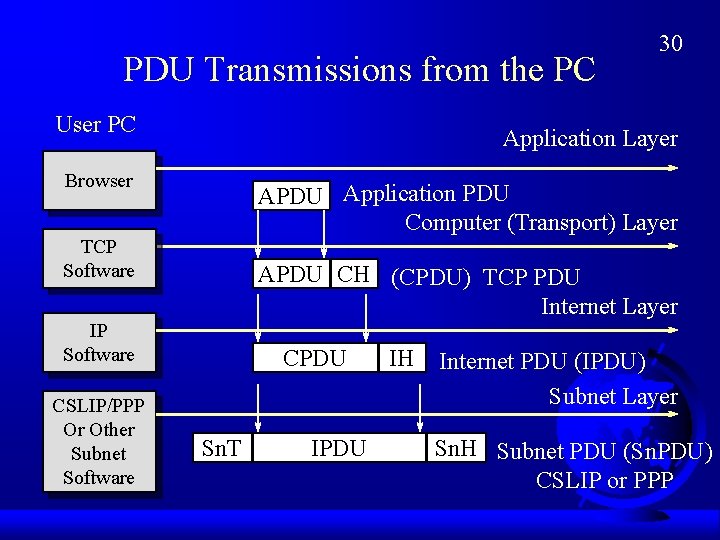
PDU Transmissions from the PC User PC Application Layer Browser APDU Application PDU Computer (Transport) Layer TCP Software APDU CH (CPDU) TCP PDU Internet Layer IP Software CSLIP/PPP Or Other Subnet Software 30 CPDU Sn. T IPDU IH Internet PDU (IPDU) Subnet Layer Sn. H Subnet PDU (Sn. PDU) CSLIP or PPP
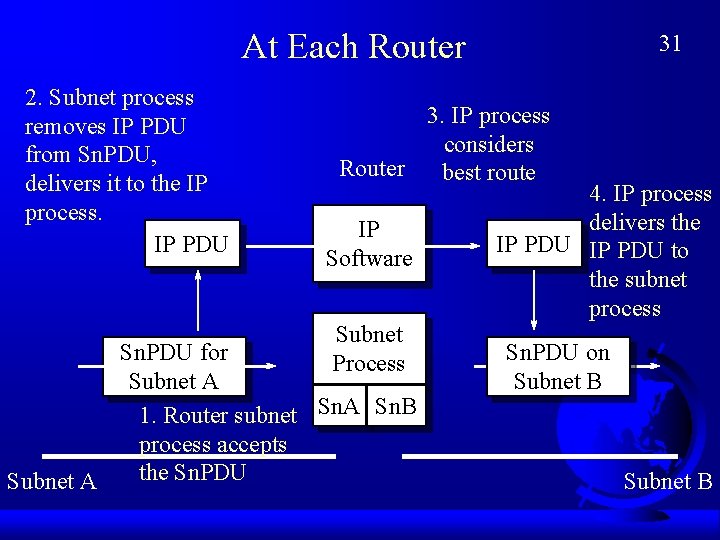
At Each Router 2. Subnet process removes IP PDU from Sn. PDU, delivers it to the IP process. IP PDU 31 3. IP process considers Router best route IP Software Subnet Process Sn. PDU for Subnet A 1. Router subnet Sn. A Sn. B process accepts the Sn. PDU Subnet A 4. IP process delivers the IP PDU to the subnet process Sn. PDU on Subnet B
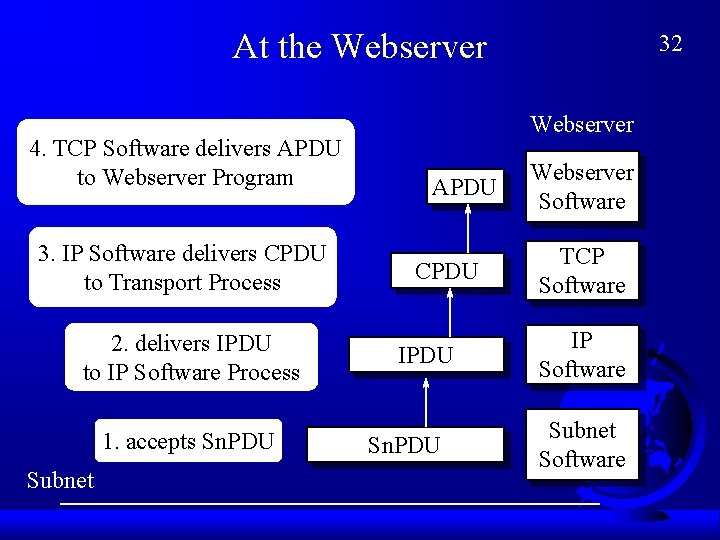
At the Webserver 4. TCP Software delivers APDU to Webserver Program 3. IP Software delivers CPDU to Transport Process 2. delivers IPDU to IP Software Process 1. accepts Sn. PDU Subnet 32 Webserver APDU CPDU IPDU Sn. PDU Webserver Software TCP Software IP Software Subnet Software
Intranets F Use of Internet Technology within Firms – Standards are mature – Standards for many applications – Security is good for internal use – Platform independent: No need to create separate applications for PCs, Macs, Unix – Browser runs software: no need to install software on PCs – Major concern of corporations today 33
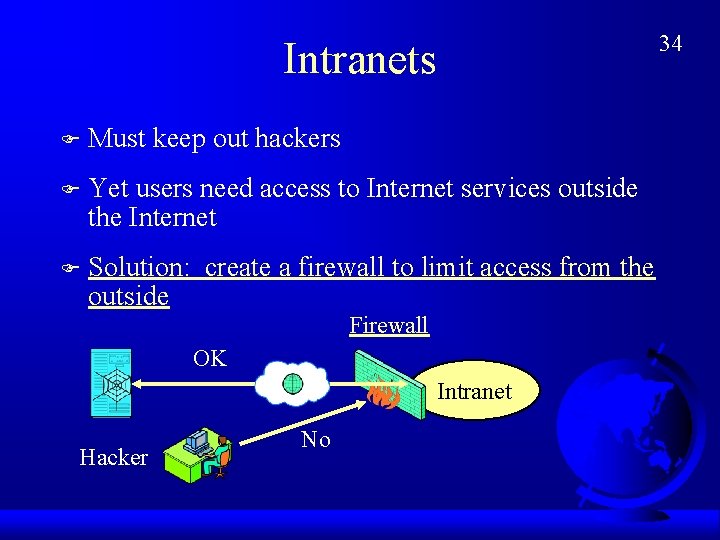
Intranets F Must keep out hackers F Yet users need access to Internet services outside the Internet F Solution: create a firewall to limit access from the outside Firewall OK Intranet Hacker No 34
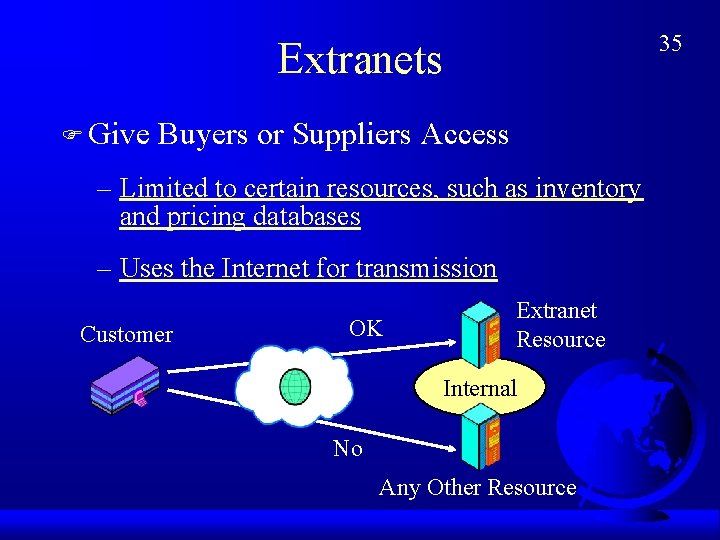
35 Extranets F Give Buyers or Suppliers Access – Limited to certain resources, such as inventory and pricing databases – Uses the Internet for transmission Customer OK Extranet Resource Internal No Any Other Resource
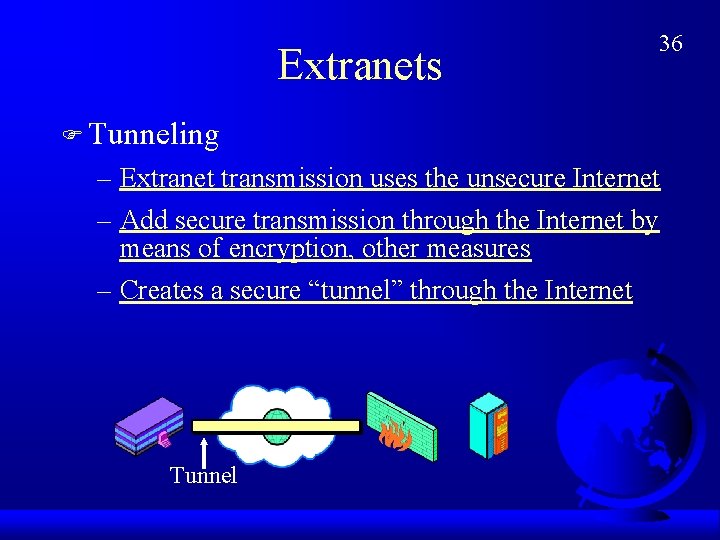
Extranets 36 F Tunneling – Extranet transmission uses the unsecure Internet – Add secure transmission through the Internet by means of encryption, other measures – Creates a secure “tunnel” through the Internet Tunnel
- Slides: 36