Computer Security Privacy Brandon Boyd Information Technology Specialist
Computer Security & Privacy Brandon Boyd Information Technology Specialist Bboyd@westervillelibrary. org

Getting Started 100% security is not possible Focus: Vulnerability management Goal: Unattractiveness
The Basics 1. Get a firewall 2. Practice patch management 3. Use Antivirus & Antispyware software 4. Practice ‘Safe Surfing’ 5. BACK UP!
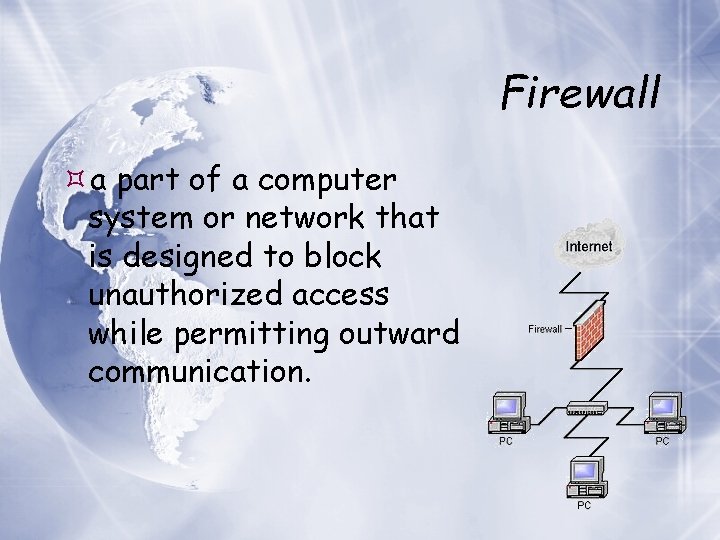
Firewall a part of a computer system or network that is designed to block unauthorized access while permitting outward communication.
Firewall Enable Windows Firewall Zone. Alarm
Patch Management an area of systems management that involves acquiring, testing, and installing patches (code changes) to an administered computer system. Patches are released to fix some issue that could allow a hacker to exploit your machine

Patch Management
Patch Management It is best practice to download and install updates at least weekly Windows: windowsupdate. microsoft. com OS X: Apple -> Software Update Application Updates Make sure you have most update to date version of all software you use
Viruses, Worms, Trojan Horses, and Spyware a piece of code that is capable of copying itself and typically has a detrimental effect, such as corrupting the system or destroying data software that self-installs on computers and tracks the user's Internet use, mainly for marketing purposes
Anti-Virus & Anti-Spyware Software For Anti-Virus AVG Anti-Virus Free Edition For Anti-Spyware Ad-Aware SE Personal Edition Microsoft Windows Defender
Phishing the activity of defrauding an online account holder of financial information by posing as a legitimate company
Phishing Best Protection: NEVER click a link in an email that claims to be from a financial institution, no matter how legitimate it seems. Instead, call the financial institution, use your web browser to visit the site, or simply ignore the email.
Phishing The newest versions of Internet Explorer 7 and Firefox 2 have built in anti-phishing technologies Additional Protection: Netcraft Anti. Phishing Toolbar
Wireless Networking allows computers to share printers, files or an internet connection without any wires between them. Uses radio frequencies to transmit information between the individual computers; each computer requires a wireless network adapter. A wireless network hub or router is used to bridge the wireless network to traditional Ethernet or home phone line networks, or provide a shared internet connection.

Wireless Networking
Wireless Networking Change your SSID and password Disabled SSID broadcast? Set up MAC filtering Gives you control over who may access your network and who may not Encrypt!! Use WPA encryption (if available) and a strong key
Content Filtering A facility to block or allow Internet sites and content from being accessed and viewed by an individual, a group of individuals, or all the connected users.

Content Filtering K 9 Web Protection Prevents the computer user from viewing Web sites that contain unwanted content. It can block more than 55 different categories of content, including pornography, hate speech and sites that promote violence or permit gambling.

Backup
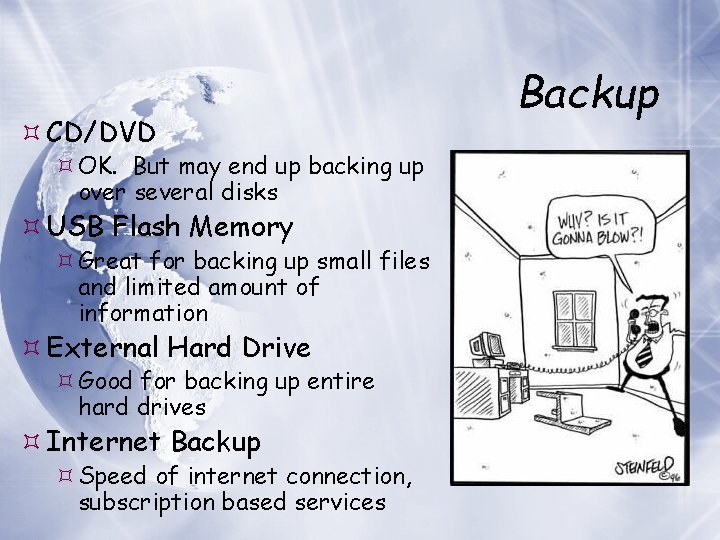
CD/DVD OK. But may end up backing up over several disks USB Flash Memory Great for backing up small files and limited amount of information External Hard Drive Good for backing up entire hard drives Internet Backup Speed of internet connection, subscription based services Backup

All In One Solution Norton 360 $80
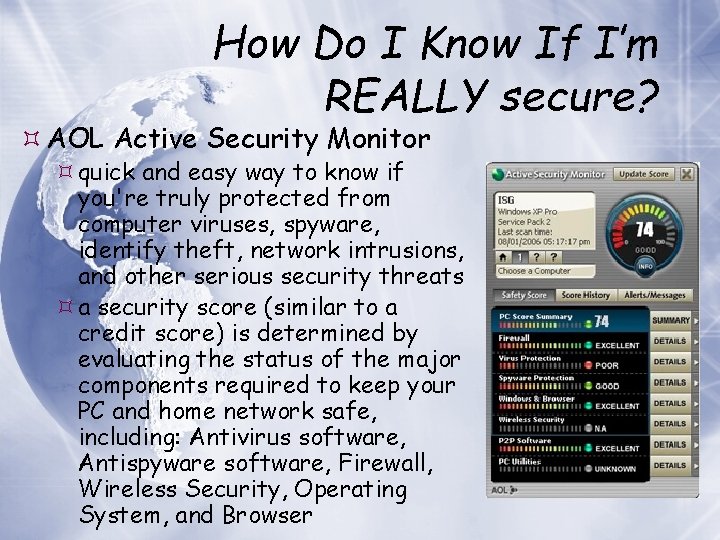
How Do I Know If I’m REALLY secure? AOL Active Security Monitor quick and easy way to know if you're truly protected from computer viruses, spyware, identify theft, network intrusions, and other serious security threats a security score (similar to a credit score) is determined by evaluating the status of the major components required to keep your PC and home network safe, including: Antivirus software, Antispyware software, Firewall, Wireless Security, Operating System, and Browser
Review 1. Get a firewall 2. Practice patch management 3. Use Antivirus & Antispyware software 4. Practice ‘Safe Surfing’ 5. BACK UP!

Questions?
- Slides: 24