Computer science revision 1 Convert 72 to hexadecimal
- Slides: 20
Computer science revision 1
Convert 72 to hexadecimal (1 mark) • 48
Explain how images are stored in binary (3 marks) • Image broken up into pixels • Each pixel is a colour • Each colour is represented by an individual binary value
List six types of input validation (6 marks) • Range check • Presence check • Length check • Picture check/formatting check • Lookup table • Check digit
What are the 3 different types of test data? (3 marks) • Valid • Invalid • Erroneous – wrong data types
List 3 features of an IDE • Code editor • Debugger • Auto documentation
Define the term input sanitation • Sanitization modifies the input to ensure that it is valid. For example changing input to uppercase
What are the four steps of a binary search algorithm? • The binary search will split the database in half, and compare the midpoint (the middle name) to the search item’. • It will see whether the midpoint comes before or after it and will throw away the set of records that doesn’t contain the search item. • It will keep dividing the records in that way until it reaches two records left, one of which is the search item. • It will then throw away the other record and output the search item
What are the four stages of computational thinking? • Decomposition • Pattern recognition • Abstraction • algorithm
What is meant by the term ‘decomposition’? • Breaking a large problem down into sub problems
What is meant by the term ‘abstraction’ • Abstraction is the process of filtering out – ignoring - the characteristics of patterns that we don't need in order to concentrate on those that we do.
What are the benefits of using pseudocode? (2 marks) • Don’t have to worry about syntax errors • Can be understood by any programmer
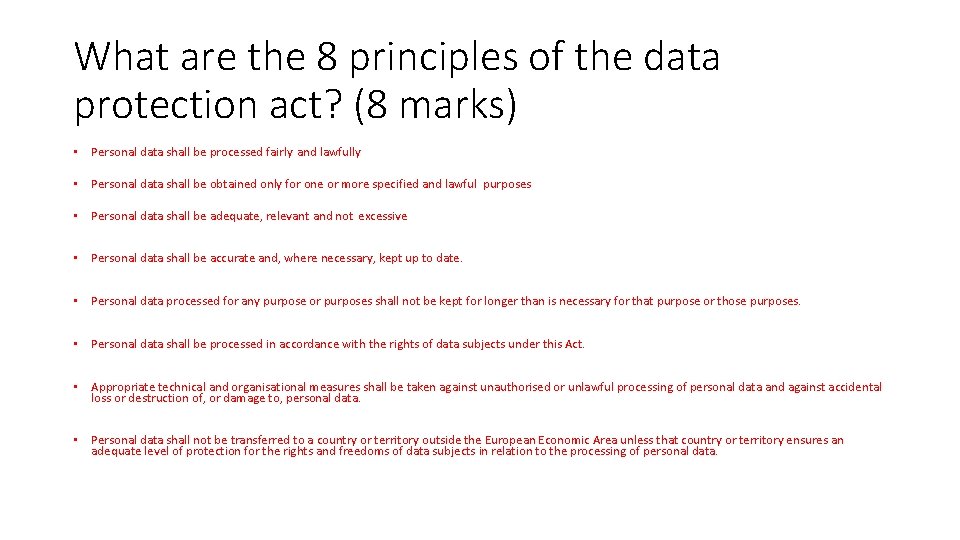
What are the 8 principles of the data protection act? (8 marks) • Personal data shall be processed fairly and lawfully • Personal data shall be obtained only for one or more specified and lawful purposes • Personal data shall be adequate, relevant and not excessive • Personal data shall be accurate and, where necessary, kept up to date. • Personal data processed for any purpose or purposes shall not be kept for longer than is necessary for that purpose or those purposes. • Personal data shall be processed in accordance with the rights of data subjects under this Act. • Appropriate technical and organisational measures shall be taken against unauthorised or unlawful processing of personal data and against accidental loss or destruction of, or damage to, personal data. • Personal data shall not be transferred to a country or territory outside the European Economic Area unless that country or territory ensures an adequate level of protection for the rights and freedoms of data subjects in relation to the processing of personal data.
Give 3 examples of natural resources which are used to make computers • Gold • Copper • Aluminium • Silicon • zinc
Give 3 reasons for why a digital divide exists • age • Education • poverty
What is the definition of a protocol? • a protocol is a standard used to define a method of exchanging data over a computer network
Explain how an SQL injection works • SQL injection usually occurs when you ask a user for input, like their username/userid, and instead of a name/id, the user gives you an SQL statement that you will unknowingly run on your database.
List the four layers of the network stack • Application • Transport • Internet • network
What are the 3 main parts of the CPU? • Arithmetic Logic Unit • Control unit • Immediate access store
What is sequential programming? • Programming statements are set out one after the other and carried out in turn