Computer Networks Why Computer Networks Sharing Resources Sharing

- Slides: 68
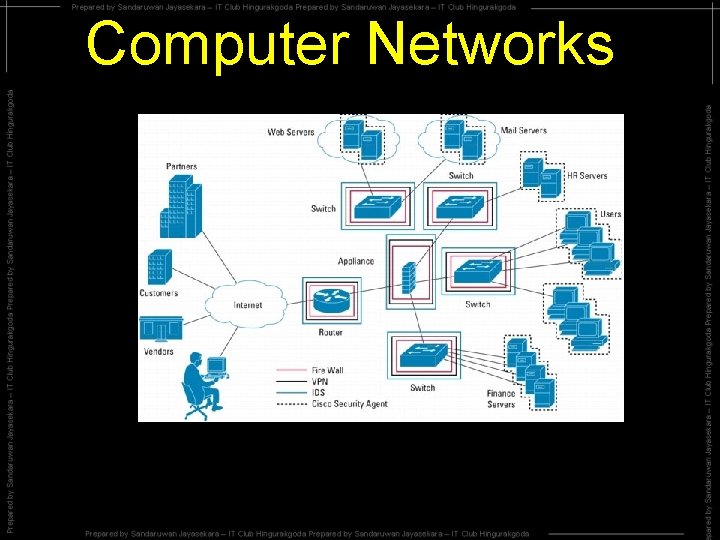
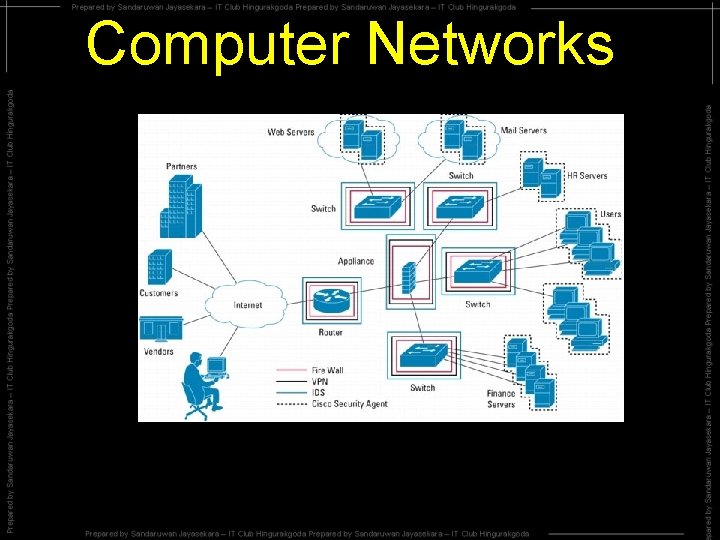
Computer Networks
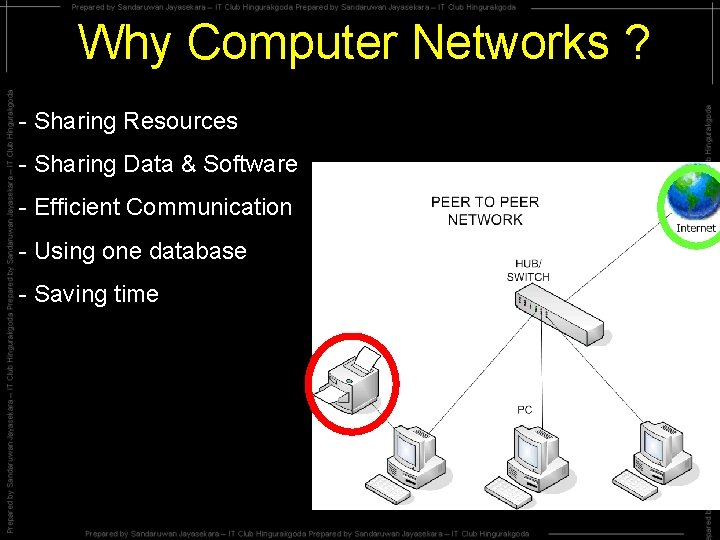
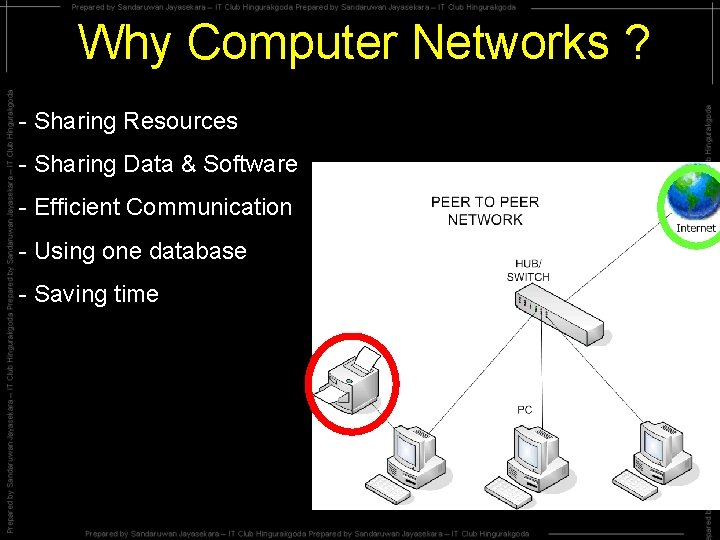
Why Computer Networks ? - Sharing Resources - Sharing Data & Software - Efficient Communication - Using one database - Saving time
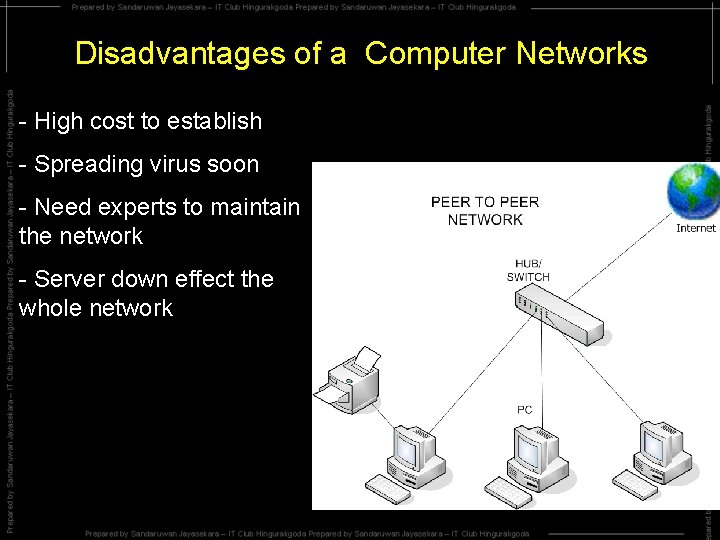
Disadvantages of a Computer Networks - High cost to establish - Spreading virus soon - Need experts to maintain the network - Server down effect the whole network
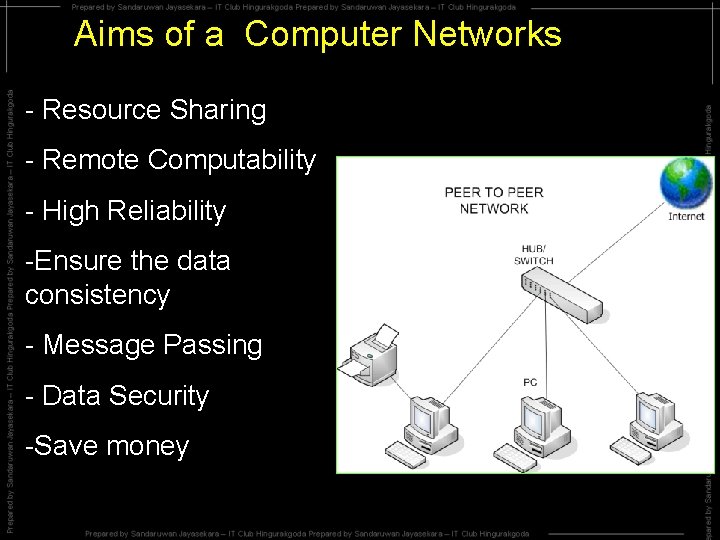
Aims of a Computer Networks - Resource Sharing - Remote Computability - High Reliability -Ensure the data consistency - Message Passing - Data Security -Save money
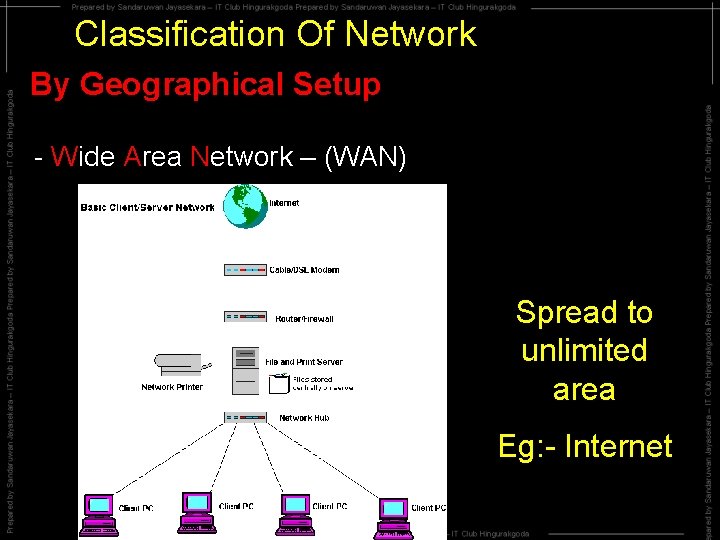
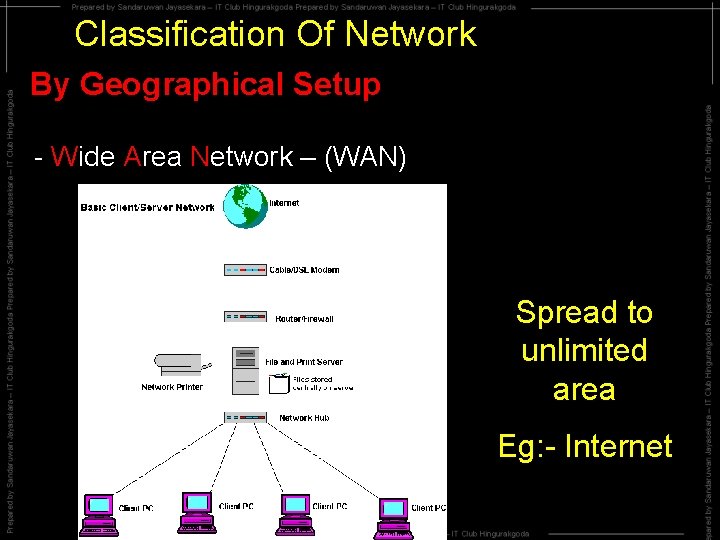
Classification Of Network By Geographical Setup - Wide Area Network – (WAN) Spread to unlimited area Eg: - Internet
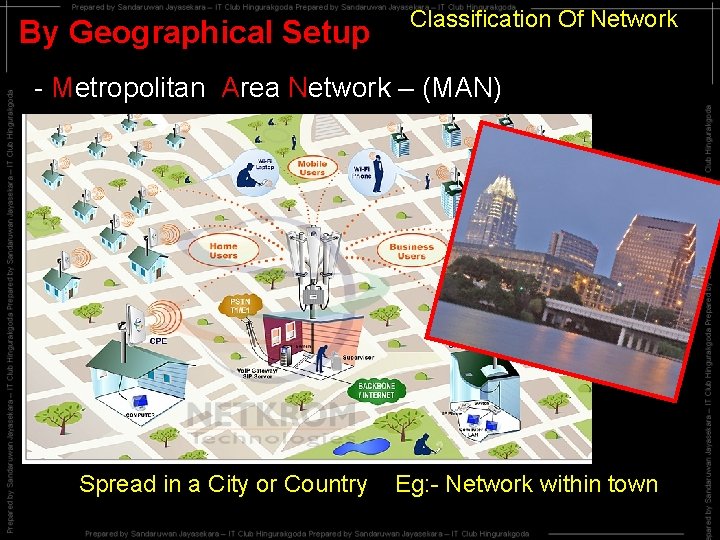
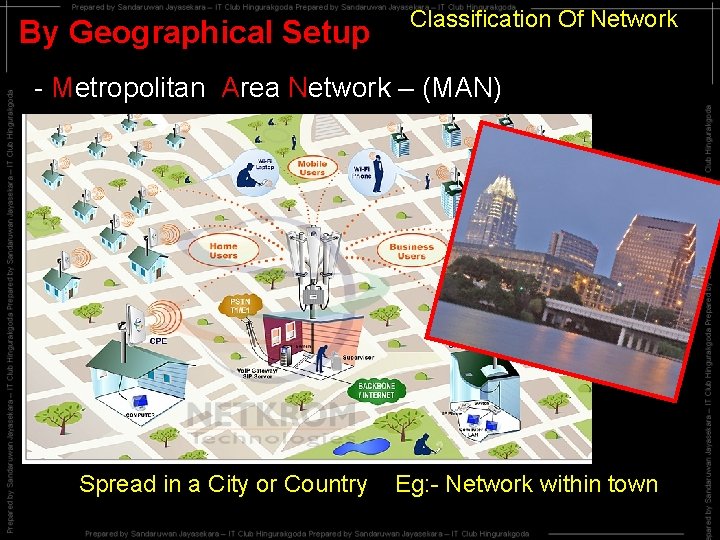
By Geographical Setup Classification Of Network - Metropolitan Area Network – (MAN) Spread in a City or Country Eg: - Network within town
By Geographical Setup Classification Of Network - Campus Area Network – (CAN) Spread in a site like School, Campus Eg: Network within a school
By Geographical Setup Classification Of Network - Local Area Network – (LAN) Spread in a Building Eg: - Network within a Building
By Geographical Setup Classification Of Network - Home Area Network – (HAN) Spread in a House Eg: - Network within a home
By Geographical Setup Classification Of Network - Personal Area Network – (PAN) Computer and its components
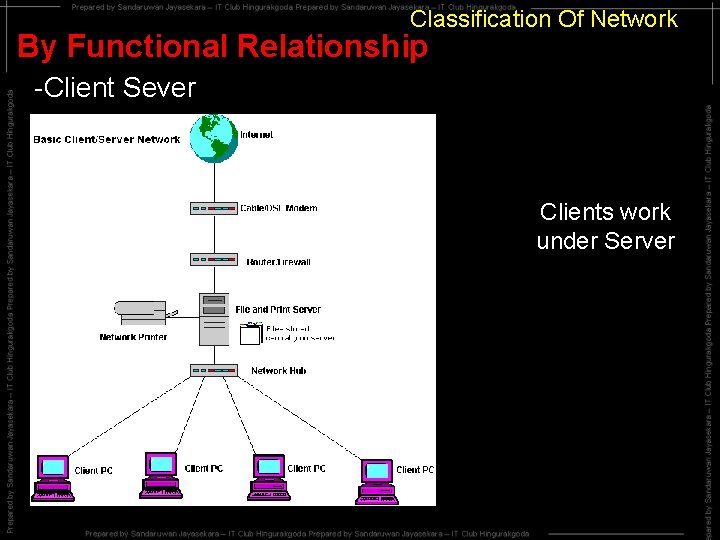
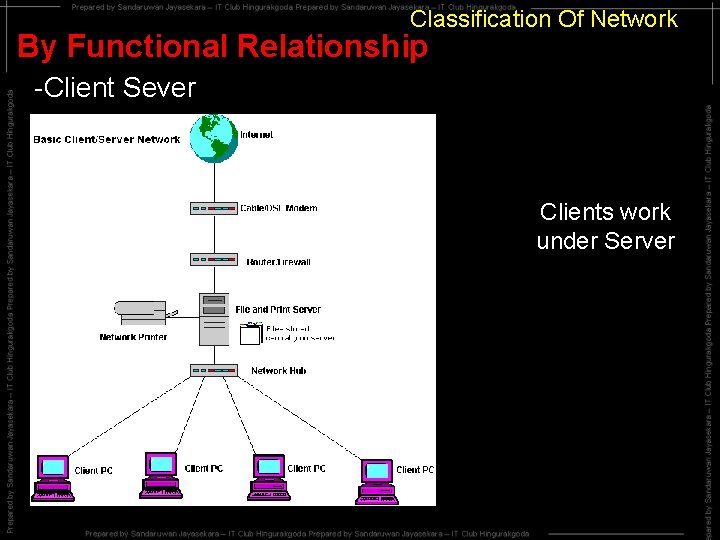
Classification Of Network By Functional Relationship -Client Sever Clients work under Server
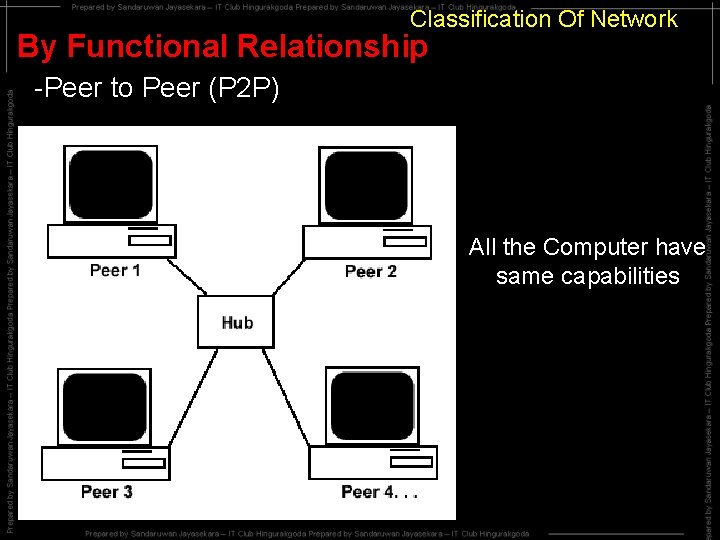
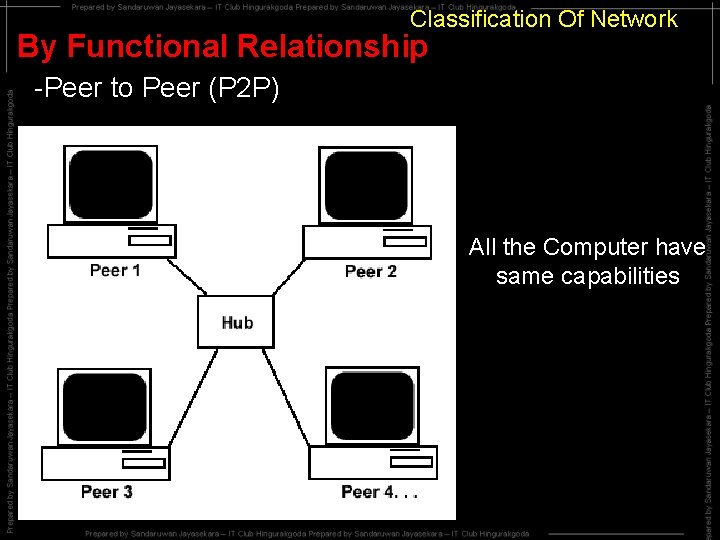
Classification Of Network By Functional Relationship -Peer to Peer (P 2 P) All the Computer have same capabilities
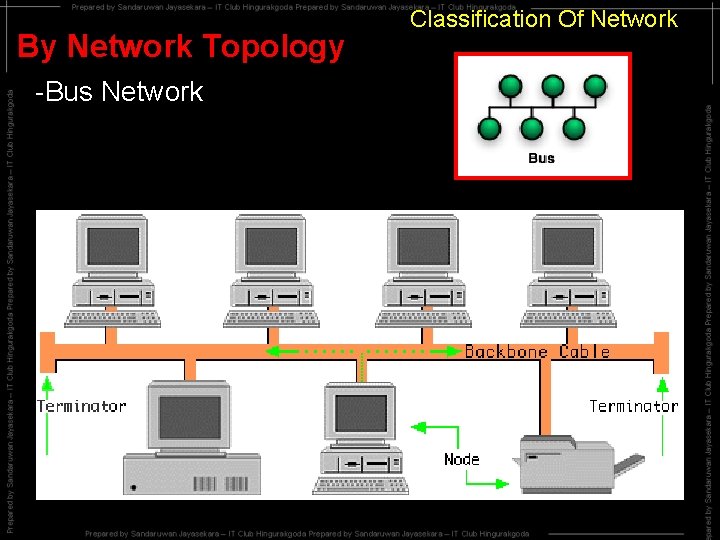
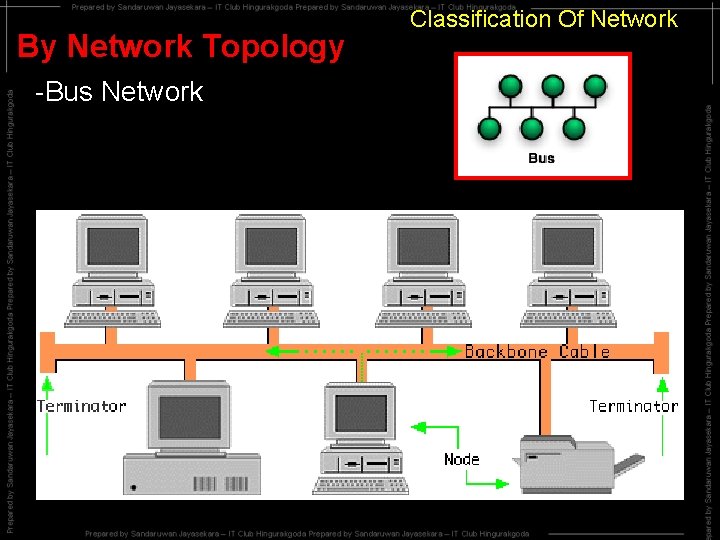
By Network Topology -Bus Network Classification Of Network
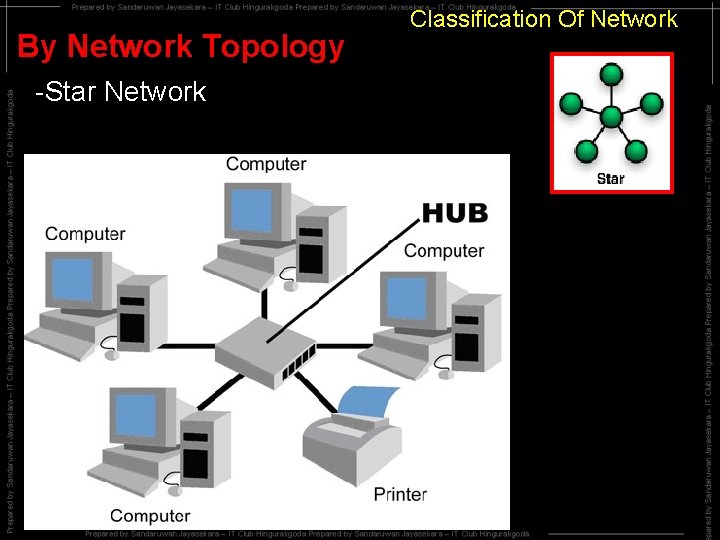
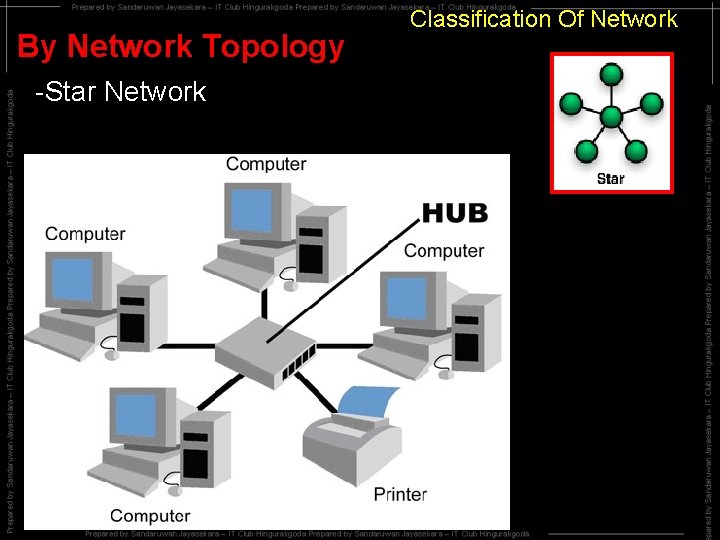
By Network Topology -Star Network Classification Of Network
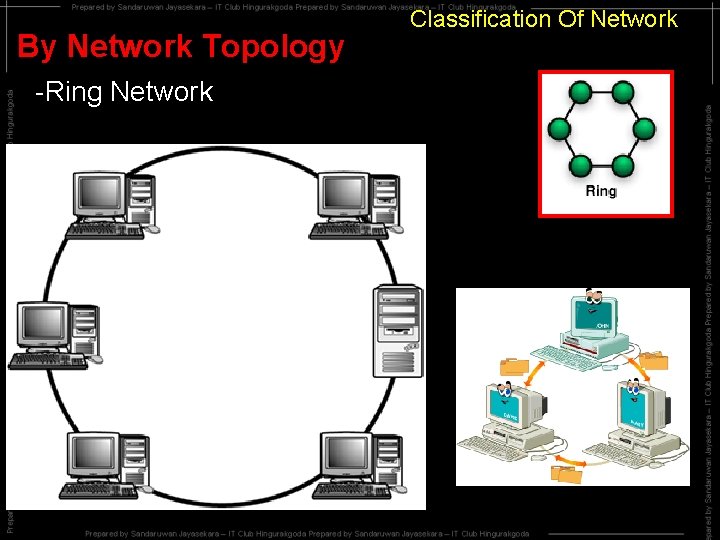
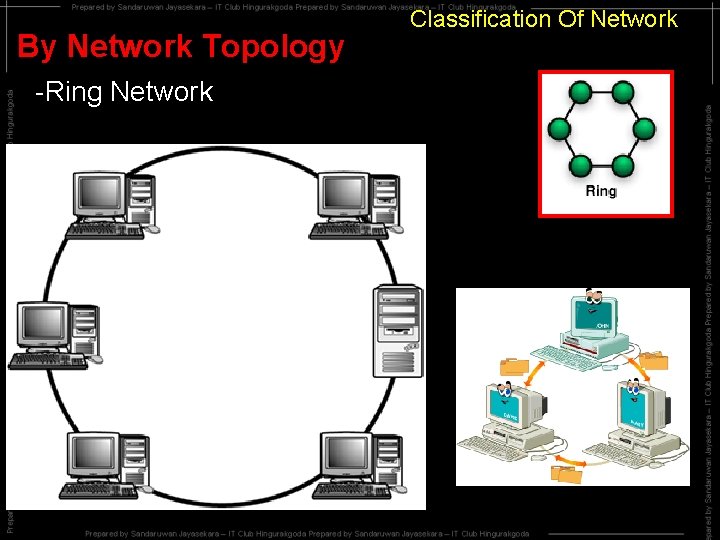
By Network Topology -Ring Network Classification Of Network
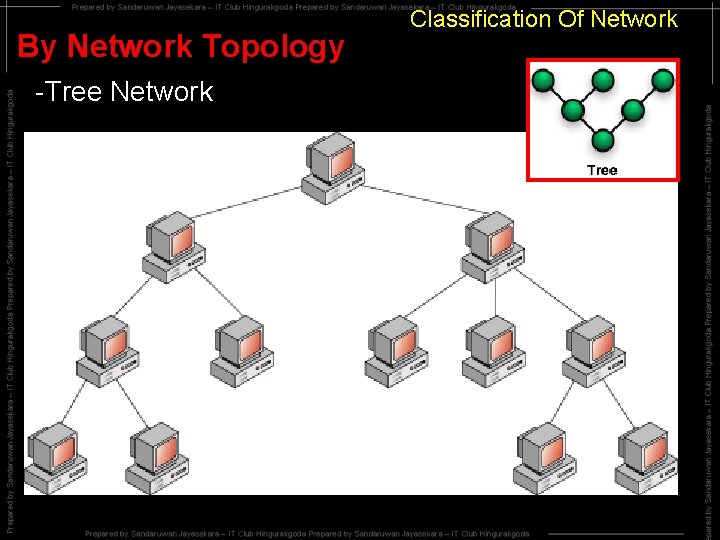
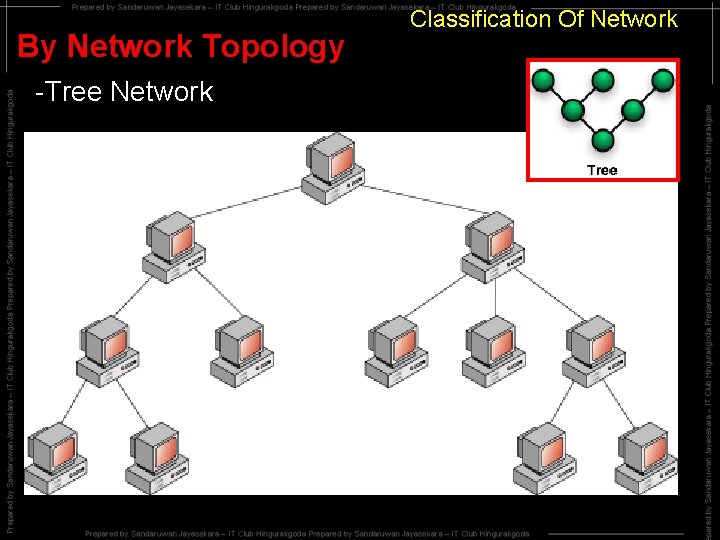
By Network Topology -Tree Network Classification Of Network
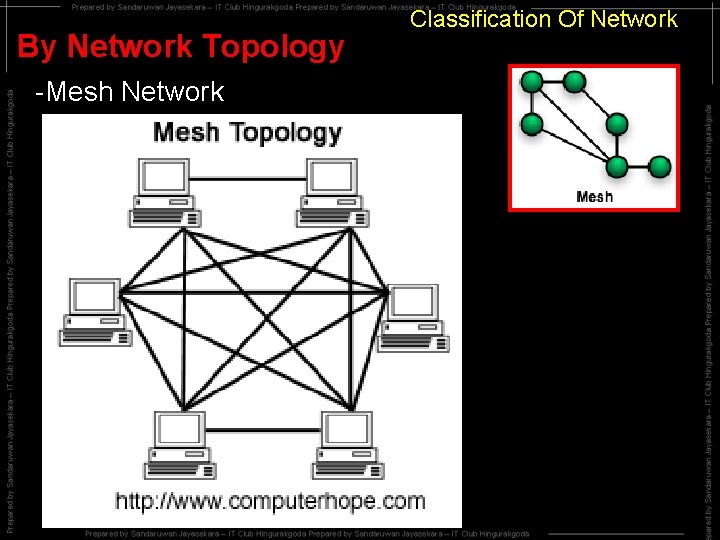
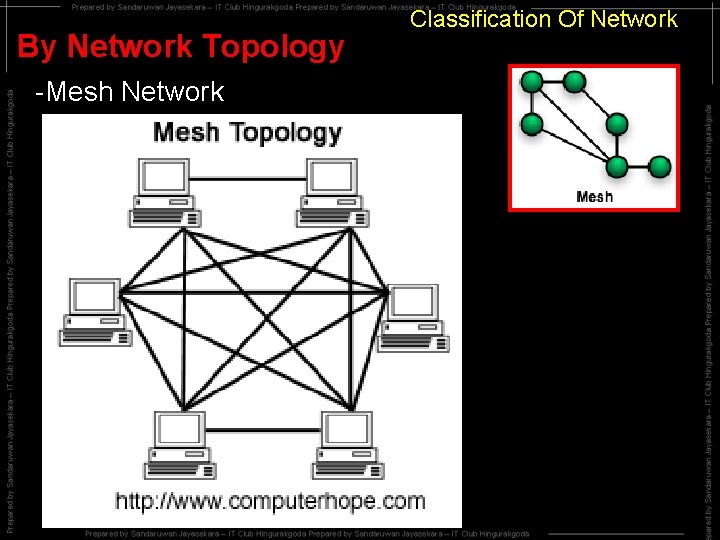
By Network Topology -Mesh Network Classification Of Network
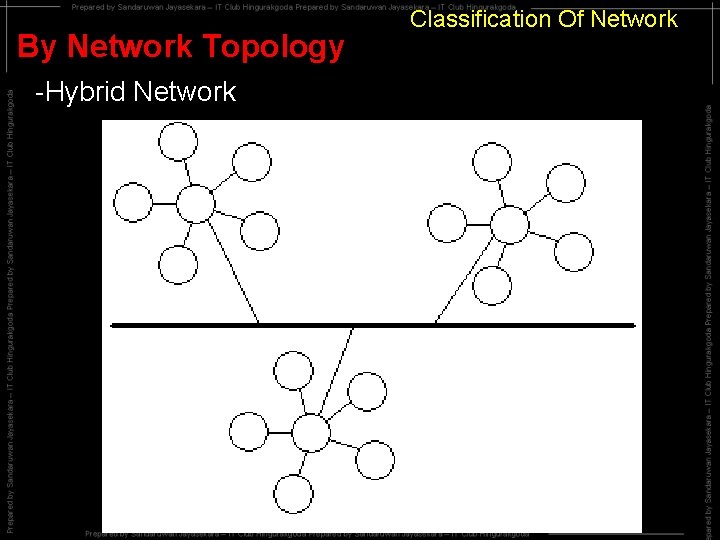
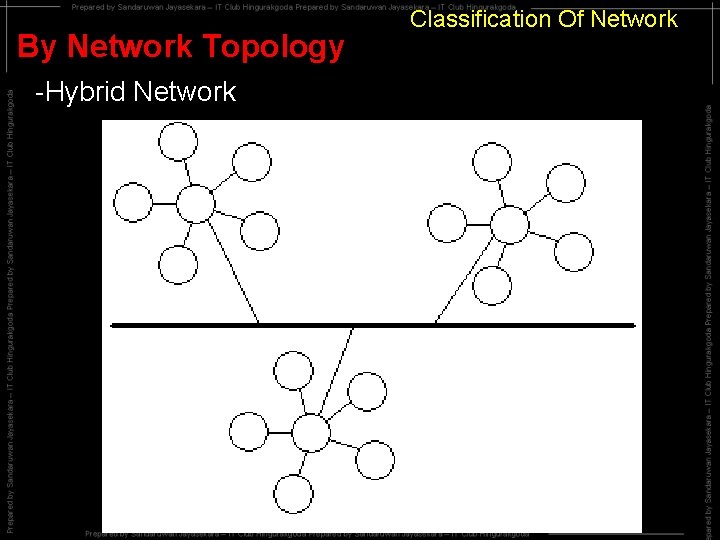
By Network Topology -Hybrid Network Classification Of Network
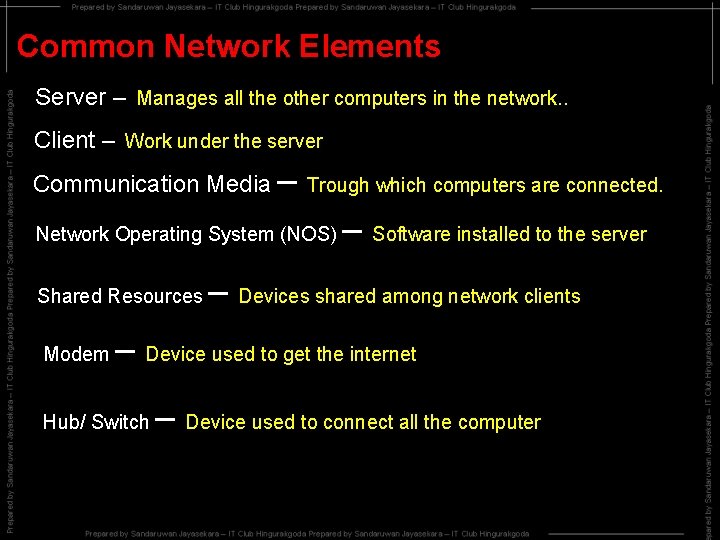
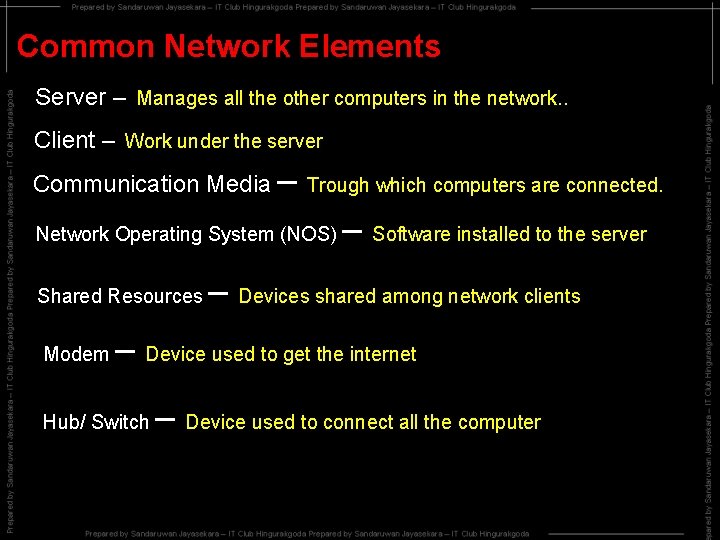
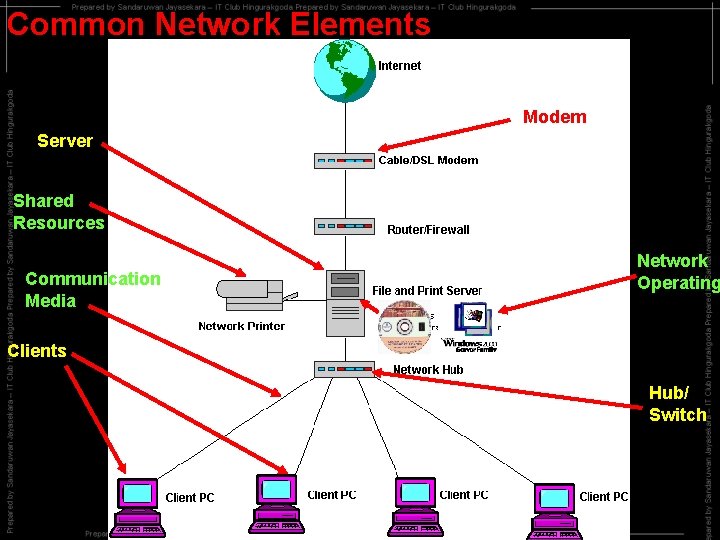
Common Network Elements Server – Manages all the other computers in the network. . Client – Work under the server Communication Media – Trough which computers are connected. Network Operating System (NOS) Shared Resources Modem – Software installed to the server – Devices shared among network clients – Device used to get the internet Hub/ Switch – Device used to connect all the computer
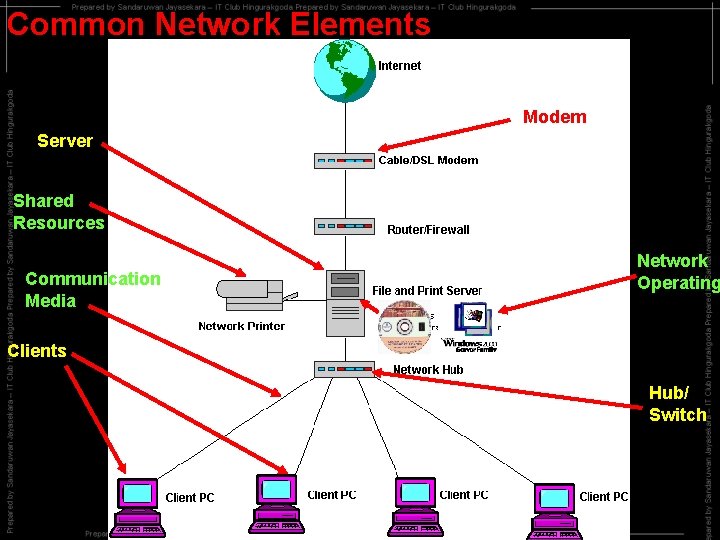
Common Network Elements Modem Server Shared Resources Communication Media Network Operating Clients Hub/ Switch
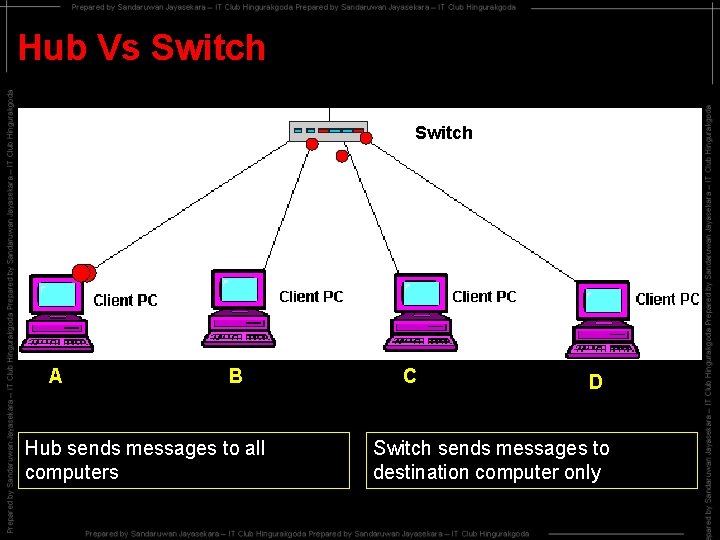
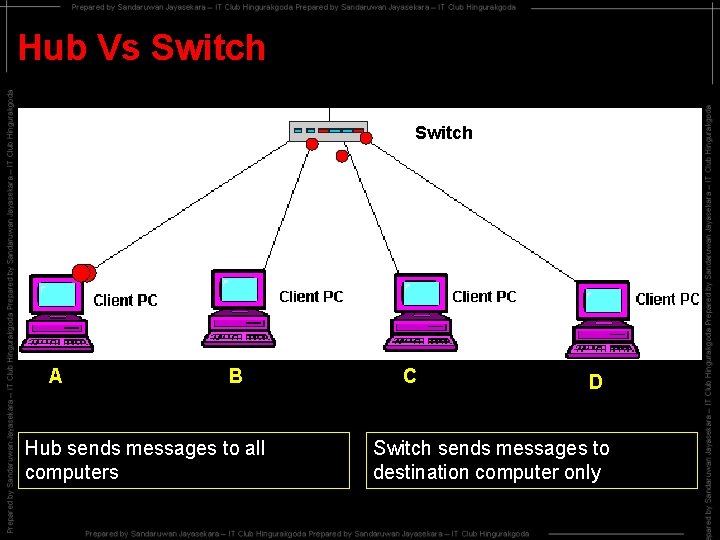
Hub Vs Switch Hub A B Hub sends messages to all computers C D Switch sends messages to destination computer only
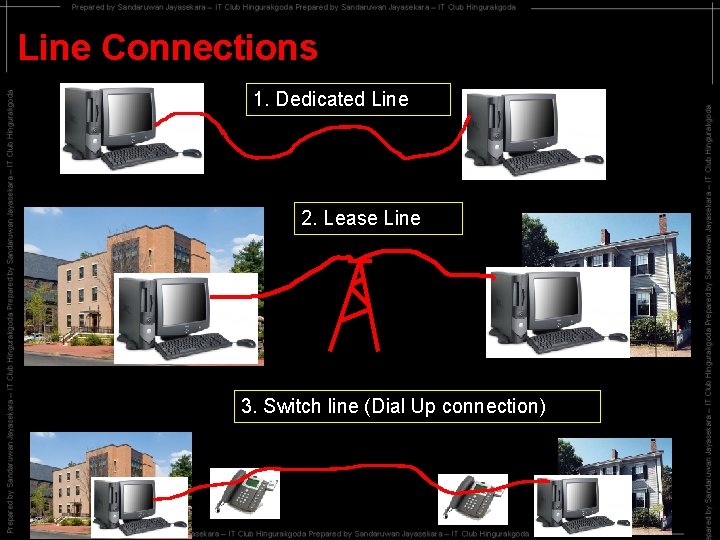
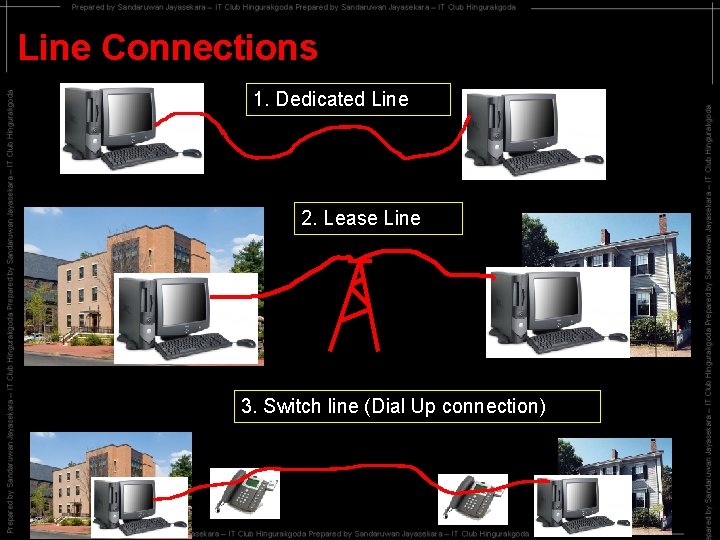
Line Connections 1. Dedicated Line 2. Lease Line 3. Switch line (Dial Up connection)
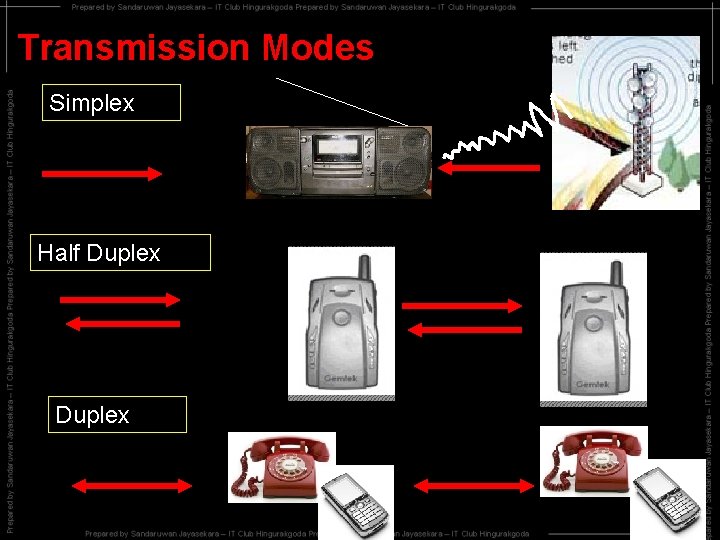
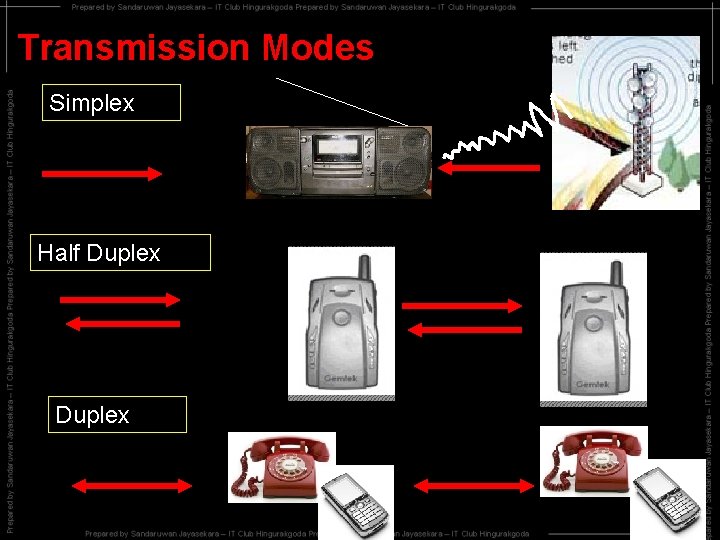
Transmission Modes Simplex Half Duplex
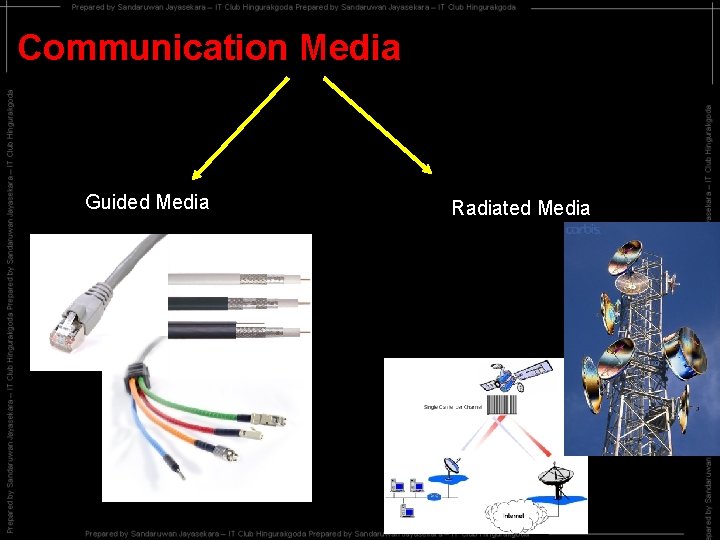
Communication Media Guided Media Radiated Media
Guided Media
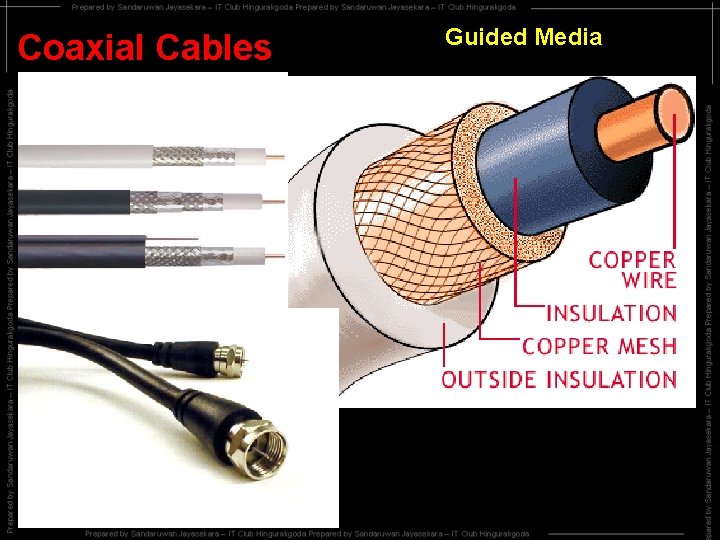
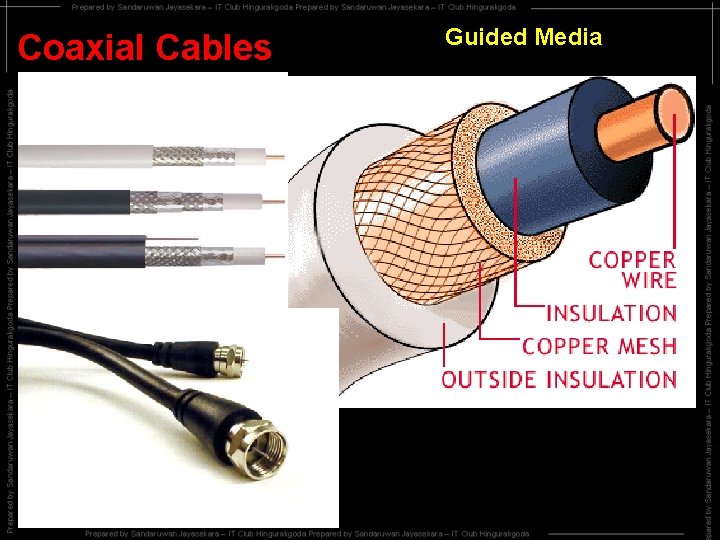
Coaxial Cables Guided Media
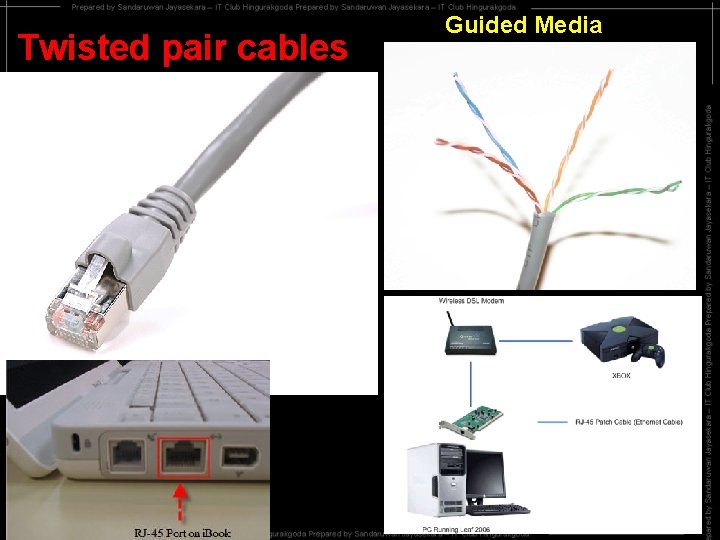
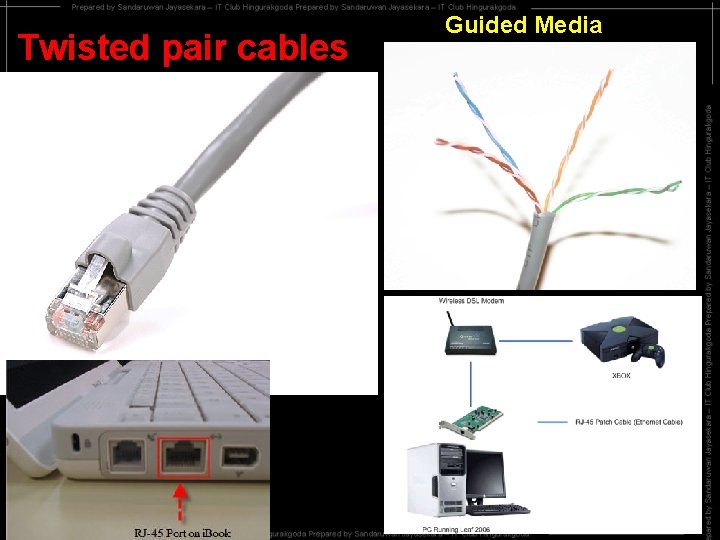
Twisted pair cables Guided Media
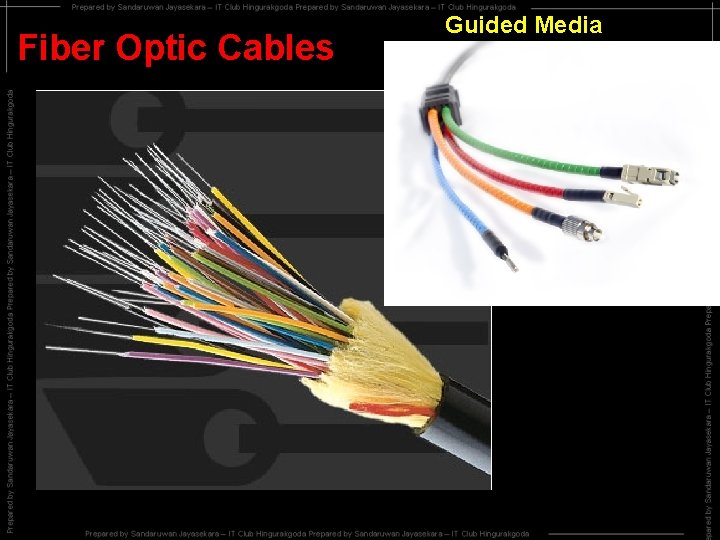
Fiber Optic Cables Guided Media
Radiated Media
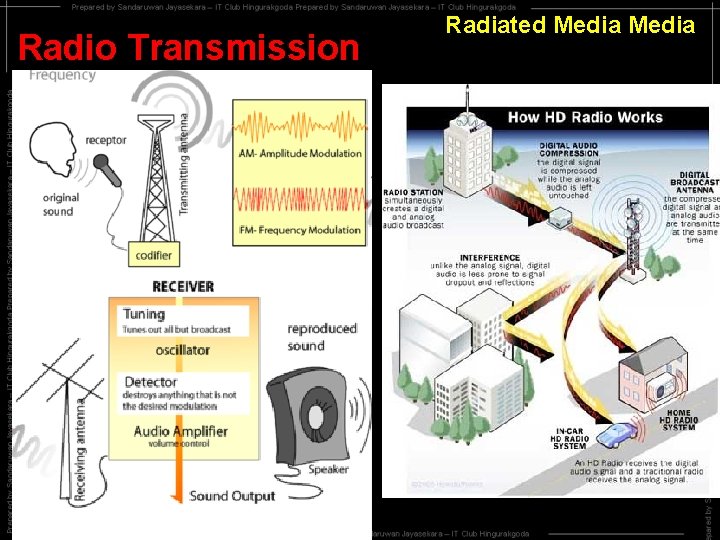
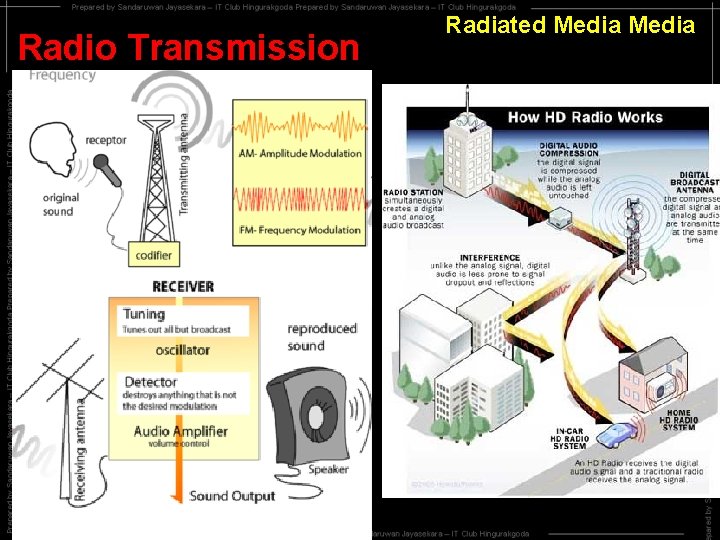
Radio Transmission Radiated Media
Infrared Transmission Radiated Media
Microwave Transmission Radiated Media
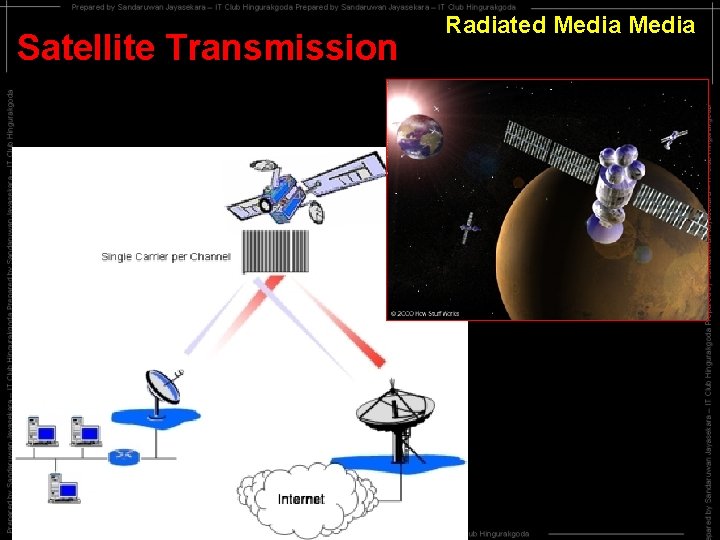
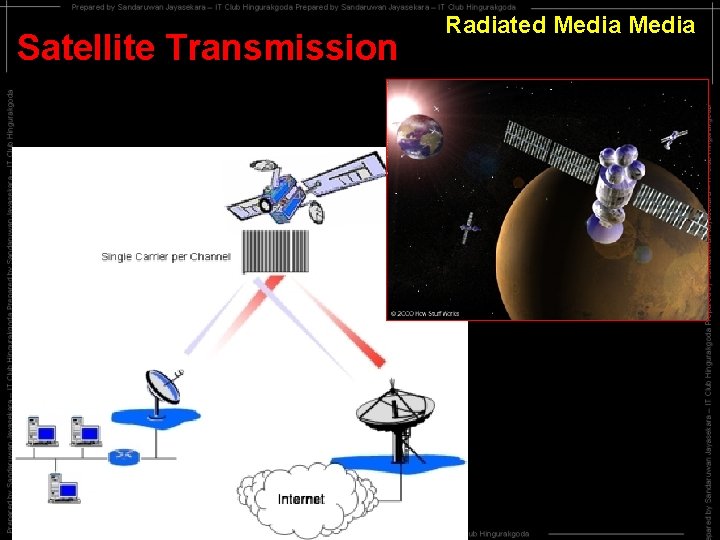
Satellite Transmission Radiated Media
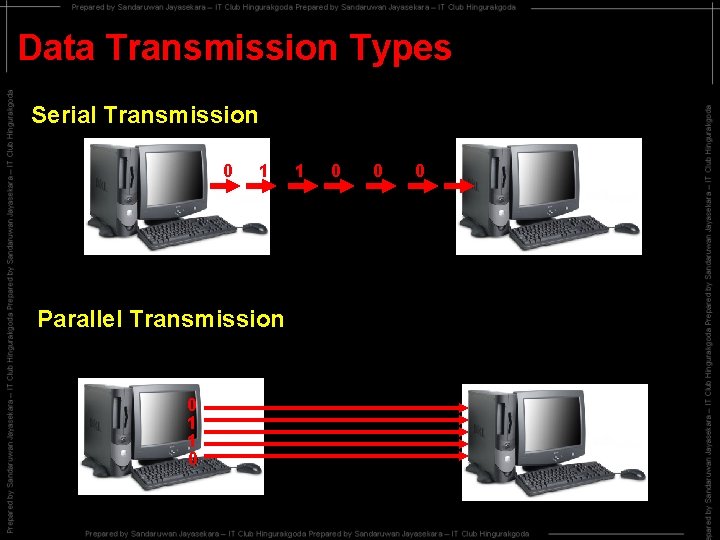
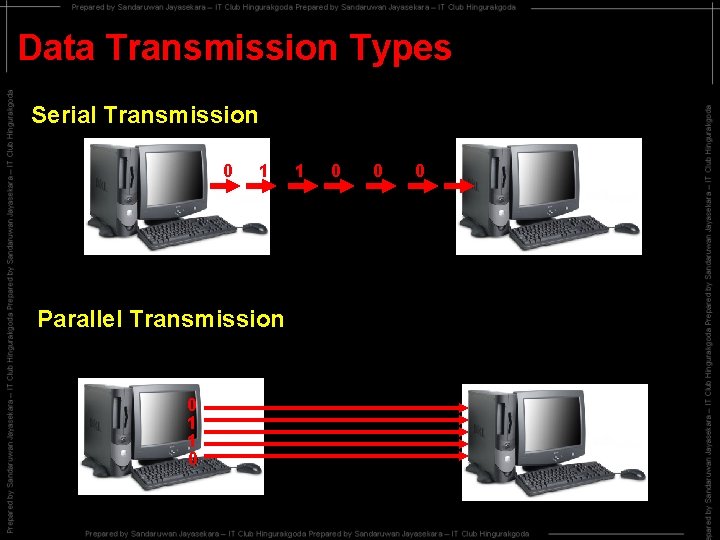
Data Transmission Types Serial Transmission 0 1 Parallel Transmission 0 1 1 0 0 0
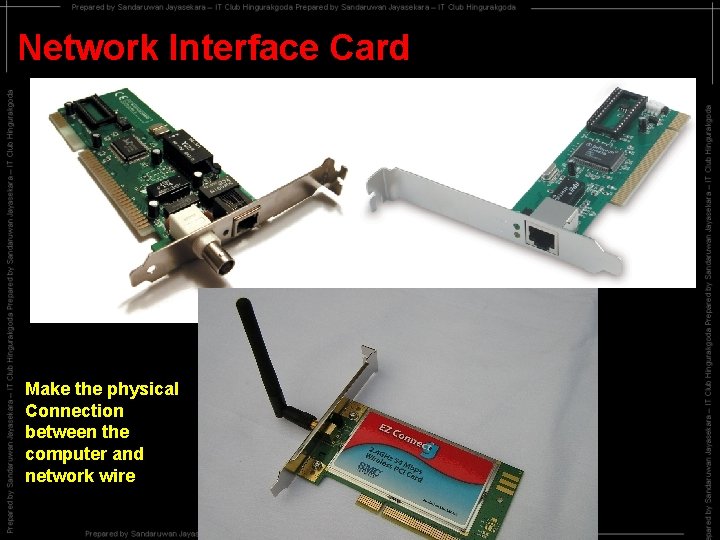
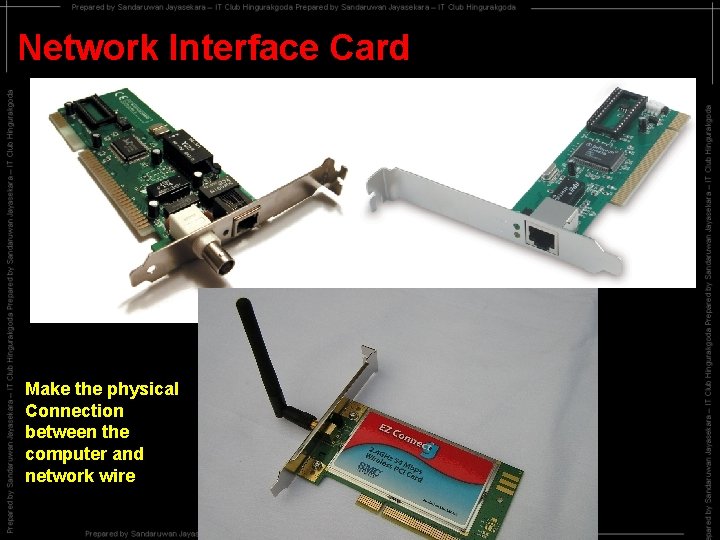
Network Interface Card Make the physical Connection between the computer and network wire
What is a Network Protocol ? It is an agreement on transferring Data between computers in a network Eg: TCP/IP, IPX/SPX, X. 25
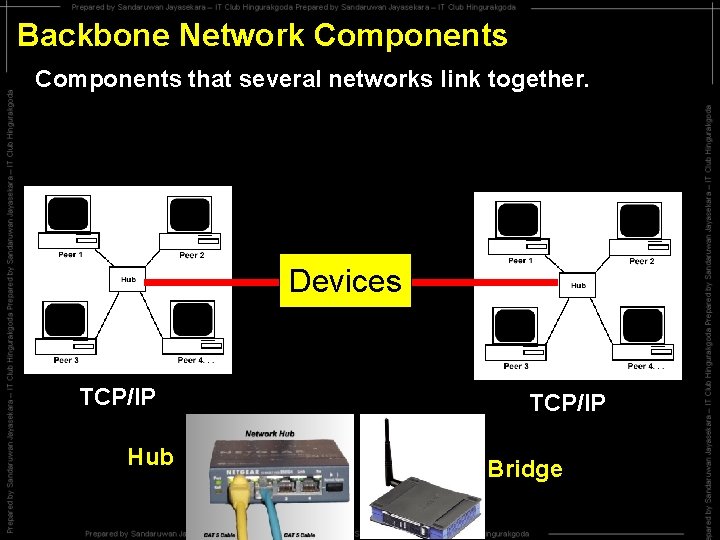
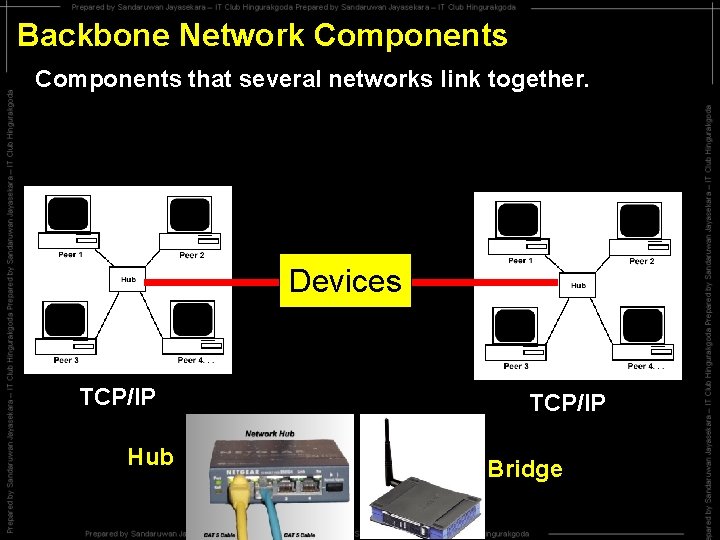
Backbone Network Components that several networks link together. Devices TCP/IP Hub TCP/IP Bridge
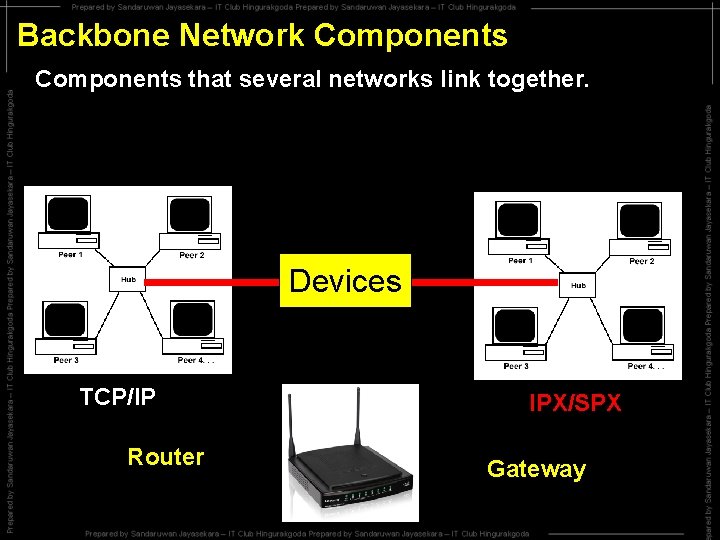
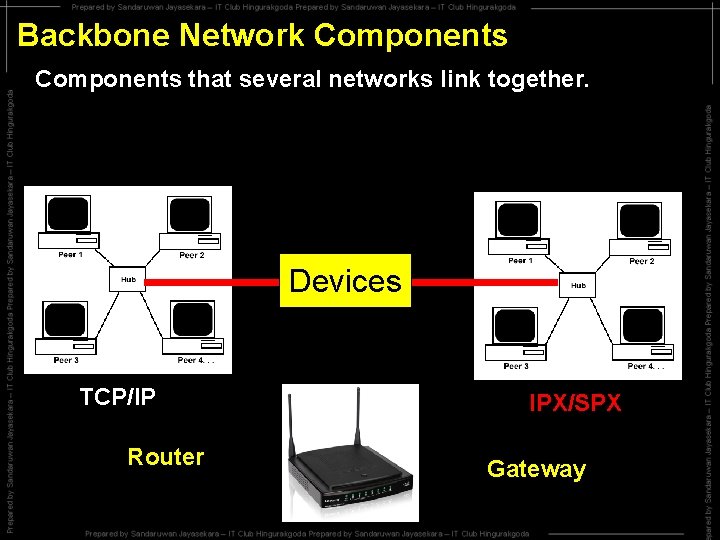
Backbone Network Components that several networks link together. Devices TCP/IP Router IPX/SPX Gateway
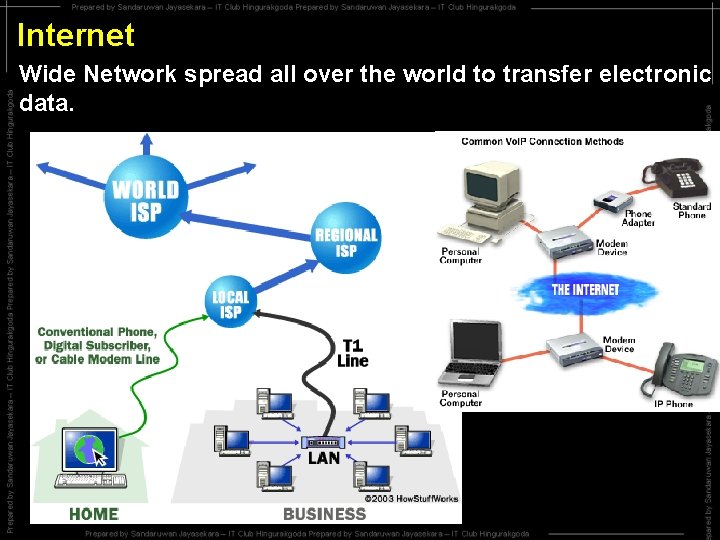
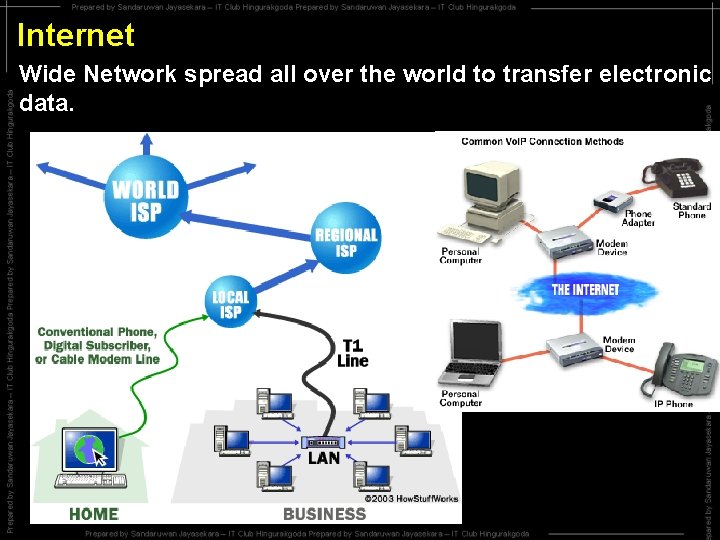
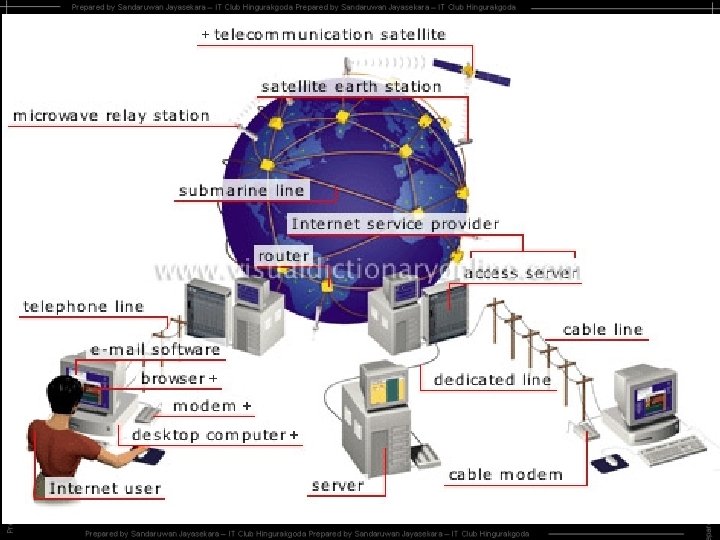
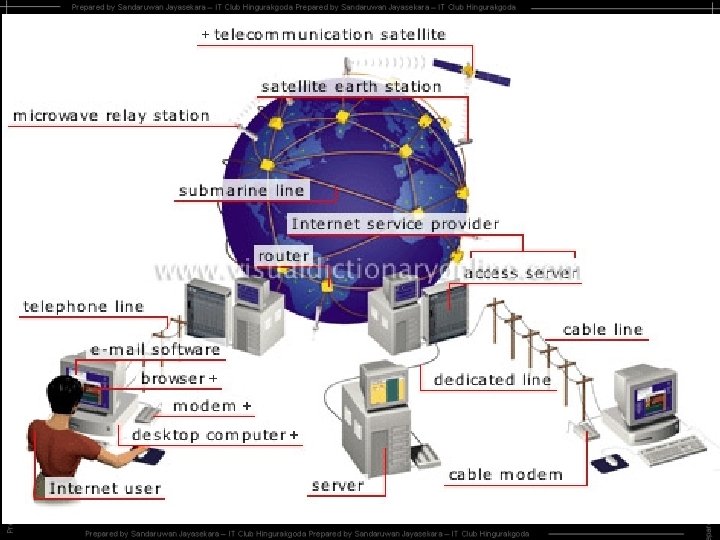
Internet Wide Network spread all over the world to transfer electronic data.
Today Internet is used for…. Business, Education, communication
Resources in the internet Information, Pictures, Sounds, Vedio, on line exams, Games, Chatting
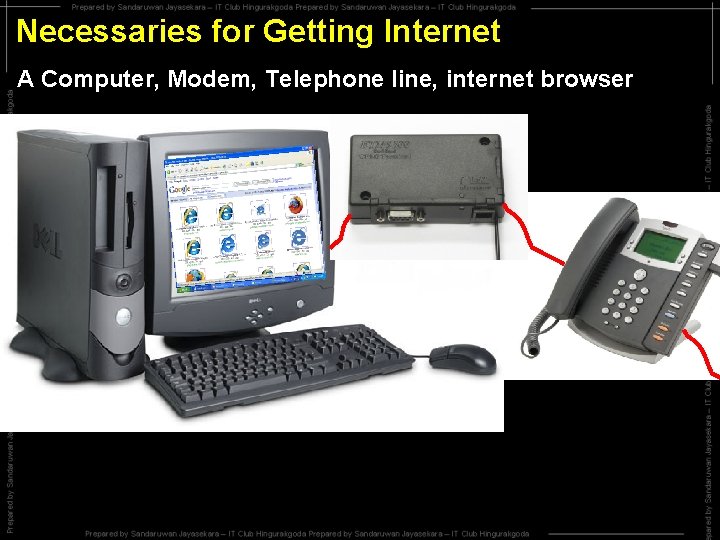
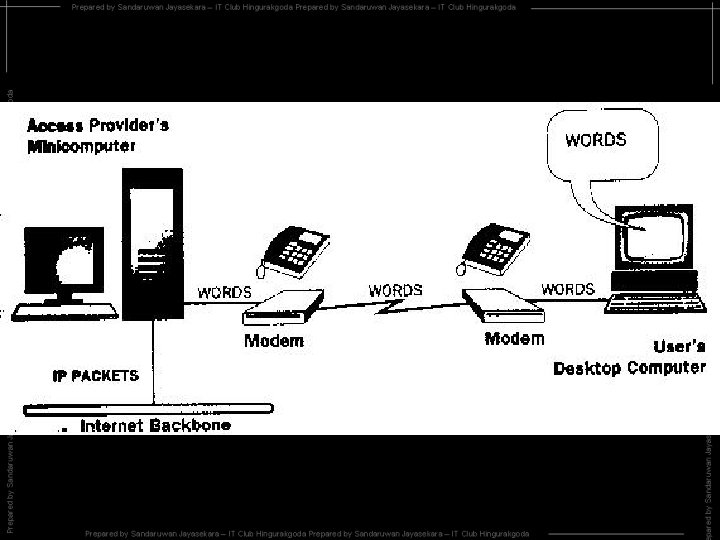
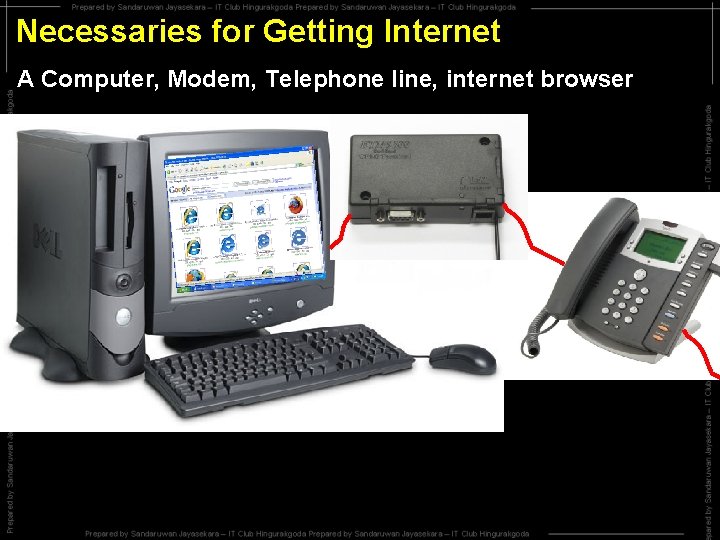
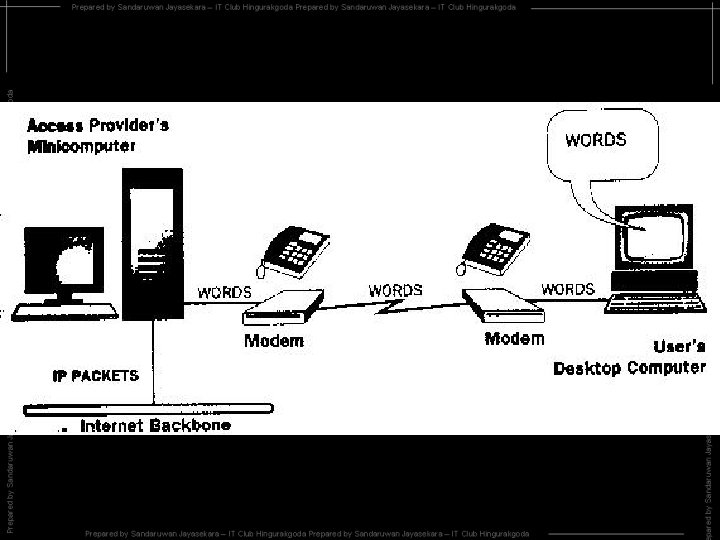
Necessaries for Getting Internet A Computer, Modem, Telephone line, internet browser
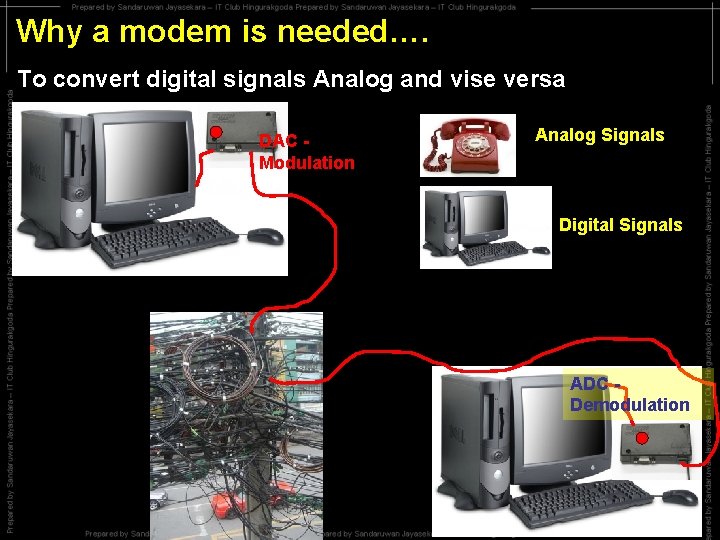
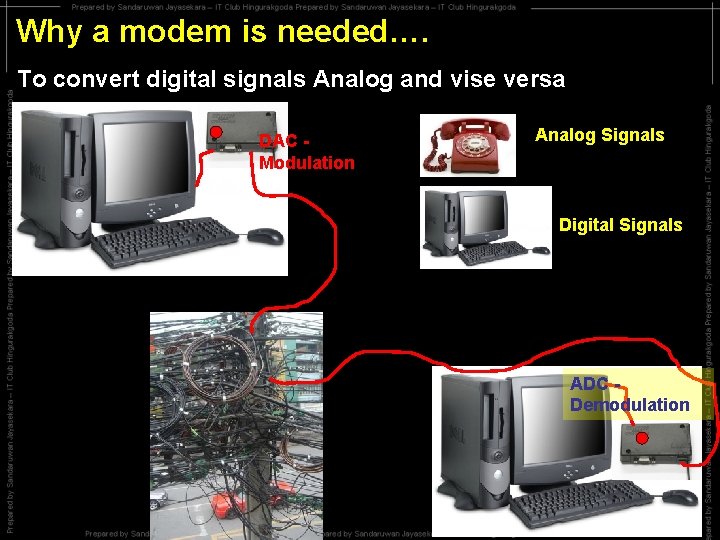
Why a modem is needed…. To convert digital signals Analog and vise versa DAC Modulation Analog Signals Digital Signals ADC Demodulation
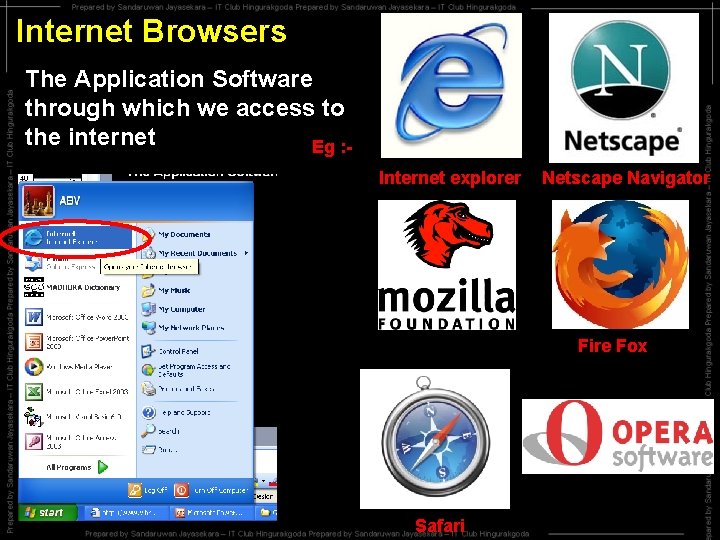
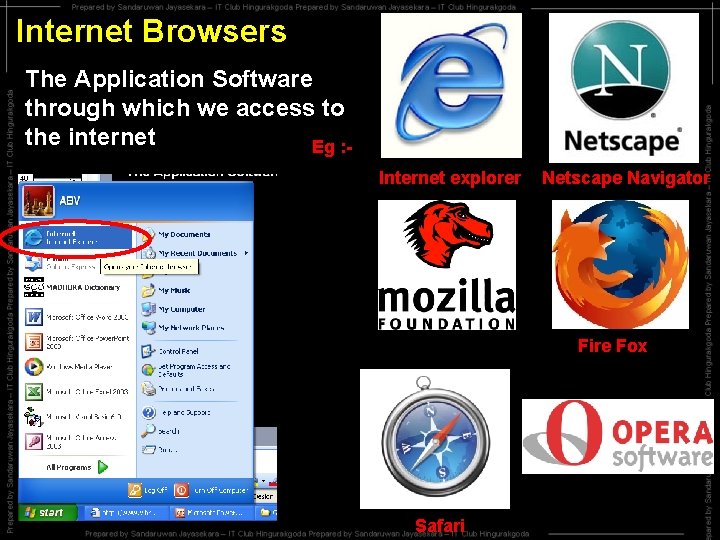
Internet Browsers The Application Software through which we access to the internet Eg : Internet explorer Netscape Navigator Fire Fox Safari
World Wide Web (WWW) Collection of Web pages throughout the world www. Rupavahini. lk WWW. Defence. lk
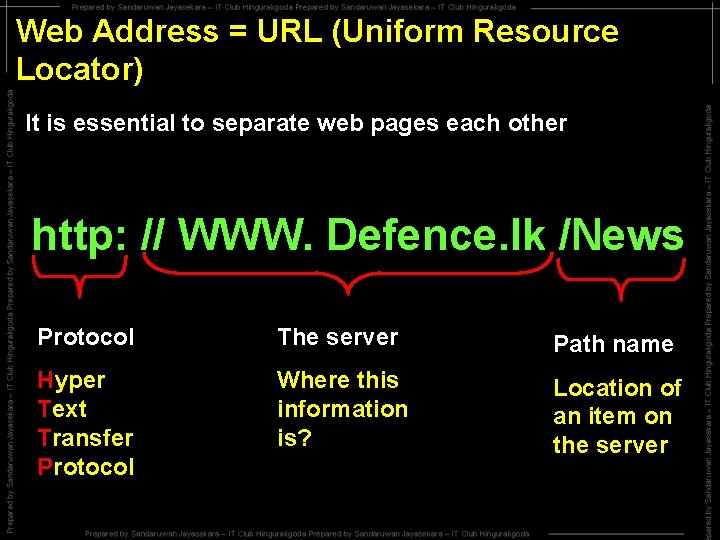
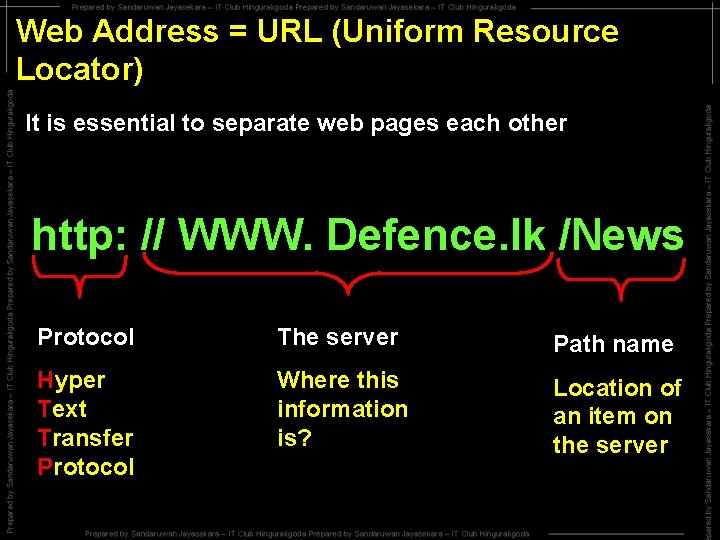
Web Address = URL (Uniform Resource Locator) It is essential to separate web pages each other http: // WWW. Defence. lk /News Protocol The server Path name Hyper Text Transfer Protocol Where this information is? Location of an item on the server
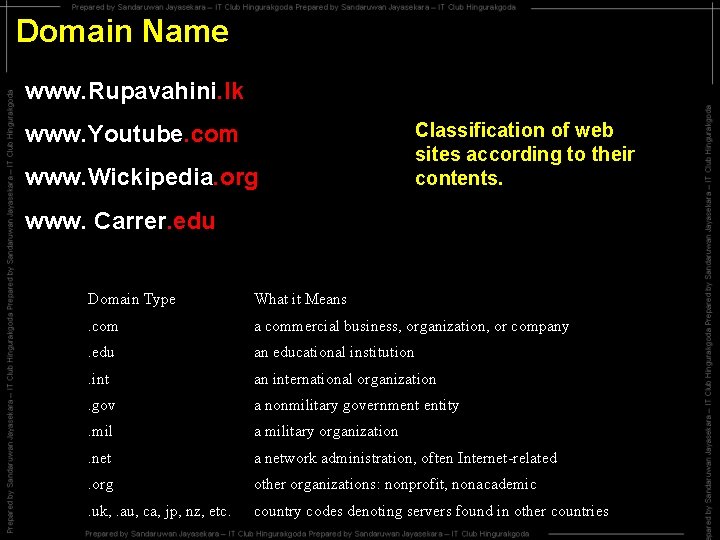
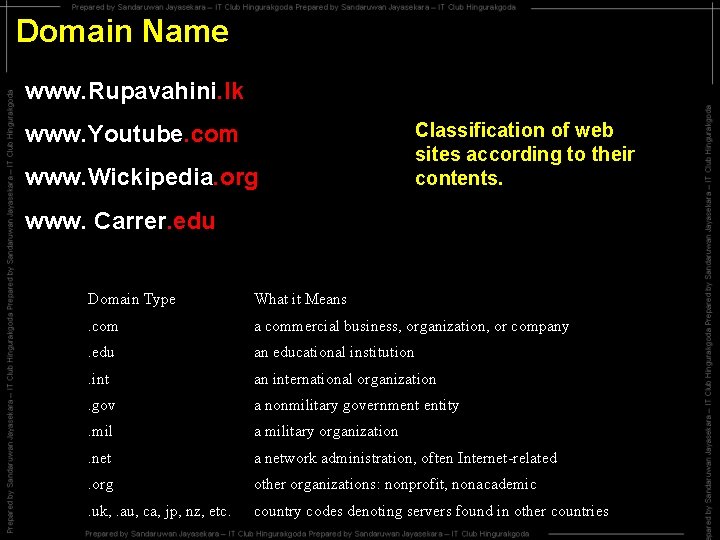
Domain Name www. Rupavahini. lk www. Youtube. com www. Wickipedia. org Classification of web sites according to their contents. www. Carrer. edu Domain Type What it Means . com a commercial business, organization, or company . edu an educational institution . int an international organization . gov a nonmilitary government entity . mil a military organization . net a network administration, often Internet-related . org other organizations: nonprofit, nonacademic . uk, . au, ca, jp, nz, etc. country codes denoting servers found in other countries
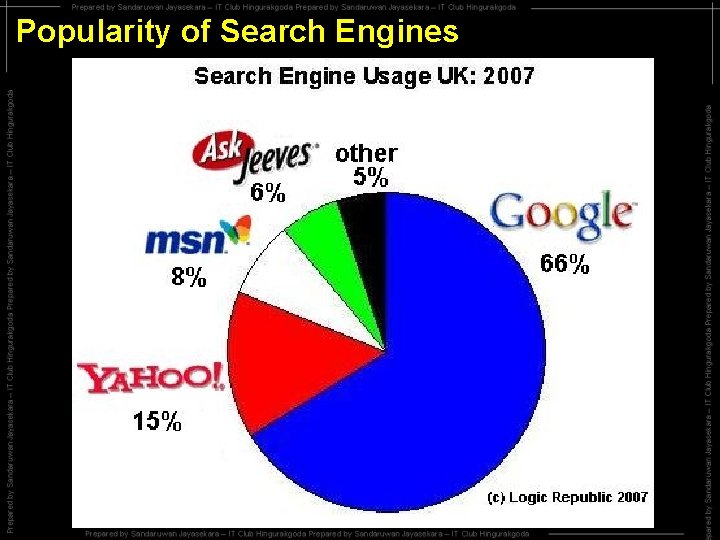
Search Engines A web page that helps us to find information on web pages when we don’t know the exact name of the Web. Eg: - WWW. Google. com, Yahoo. com ….
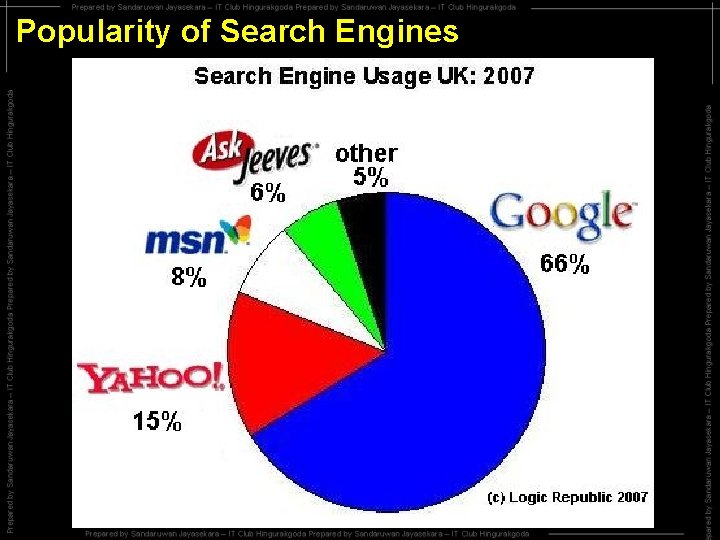
Popularity of Search Engines
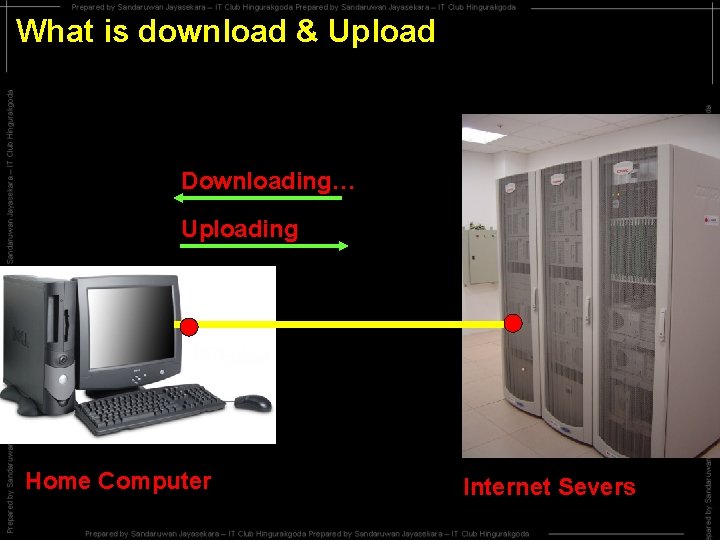
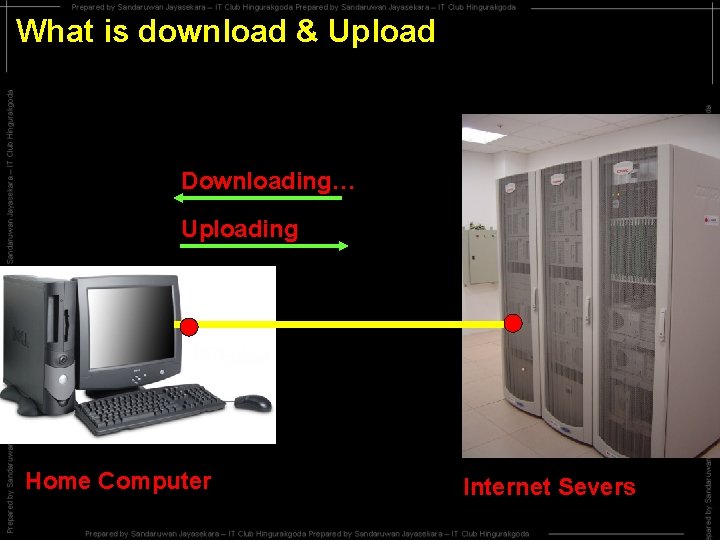
What is download & Upload Downloading… Uploading Home Computer Internet Severs
Computer Virus
Computer Virus It is a software that is very harm to computer. • Replicate itself • Join with another programs • Do unintended actions
Why Virus ? • Hacking • Avoid of copying software • Revenge • To break security systems • to defeat competitors Etc…. .
How Virus enter ?
Characteristics of Virus ? • If computer take long time than normal to open a program • If it Read the hard disks, Floppy disks often • If Unknown files are visible • If unnecessary beep codes activate • If Unnecessary messages & pictures visible
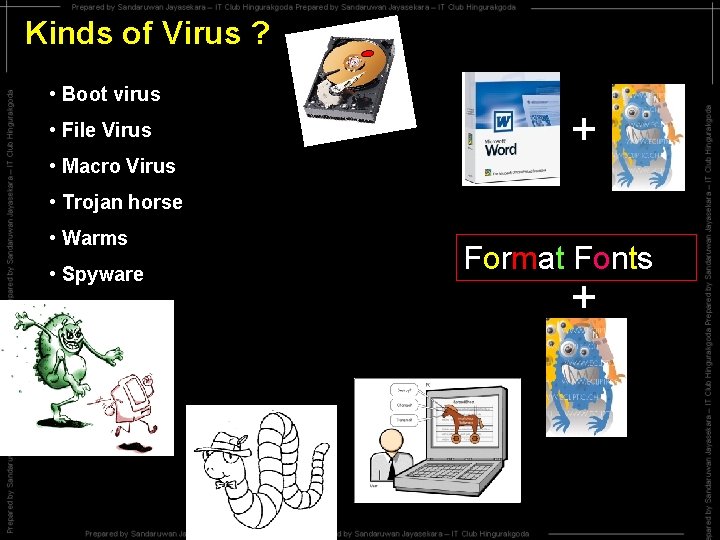
Kinds of Virus ? • Boot virus • File Virus • Macro Virus + • Trojan horse • Warms • Spyware Format Fonts +
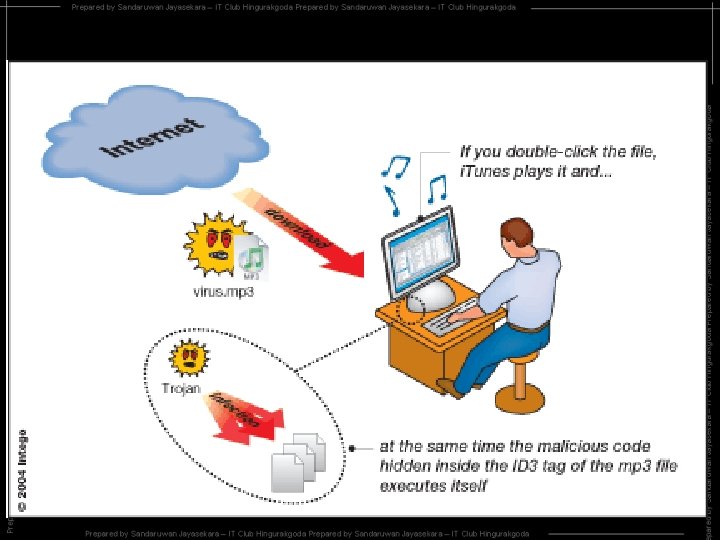
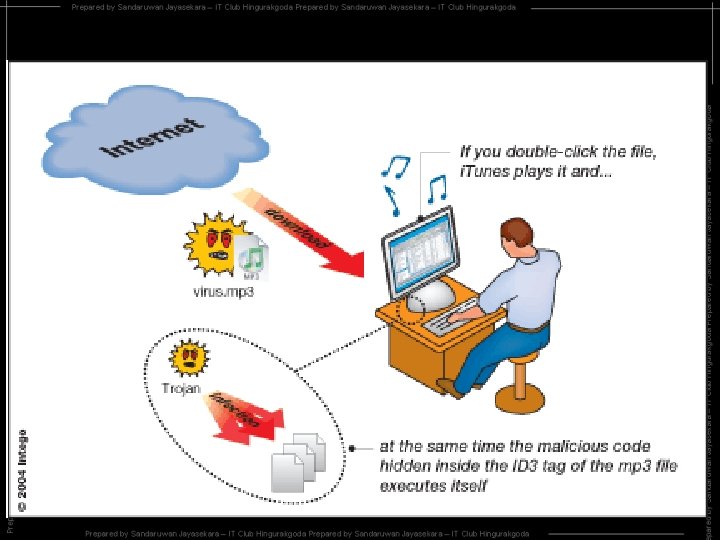
• Spam Unsolicited email, often of a commercial nature, sent indiscriminately to multiple mailing lists or individuals. • Spyware This is software that secretly gathers information about a user while he/she navigates the Internet. This information is normally used for advertising purposes. Spyware can also gather information about email addresses and even passwords and credit card numbers. • Trojan horse This is a program that disguises itself as another program. Similar to a virus, these programs are hidden and cause an unwanted effect. They differ from viruses because they are normally not designed to replicate like a virus. • Virus A computer virus is a piece of code that is secretly introduced into a system in order to corrupt it or destroy data. Often viruses are hidden in other programs or documents and when opened, the virus is let loose. • Worm This is a special type of virus that spreads without any user interaction, typically by exploiting a flaw in popular software.
Prevent from virus ? • Use Anti virus Software
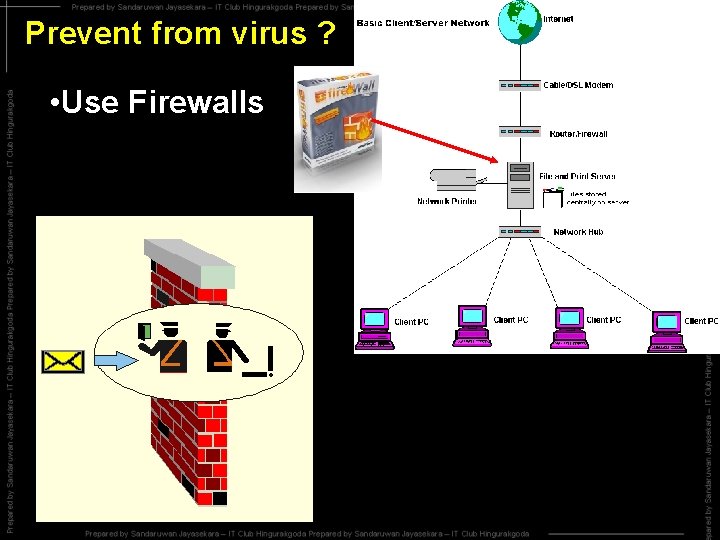
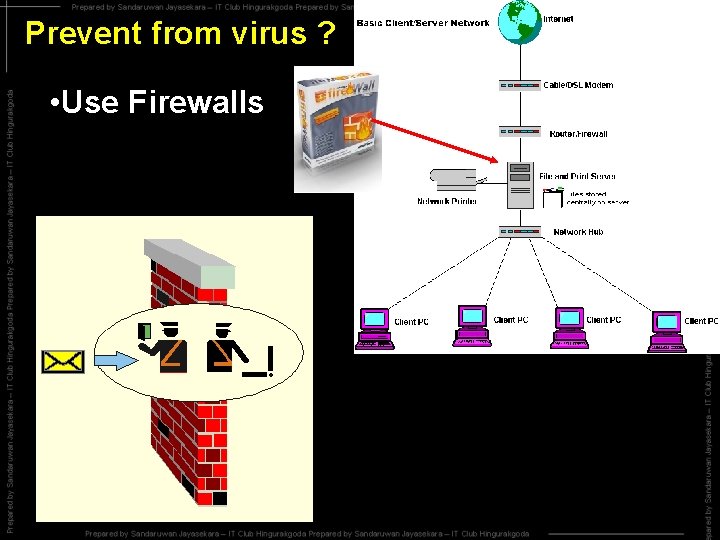
Prevent from virus ? • Use Firewalls
Prevent from virus ? • Avoiding of using unexamined CD, Floppy, Software us Vir Gu ard
E-mail (Electronic Mail) • Sending electronic data by using a network
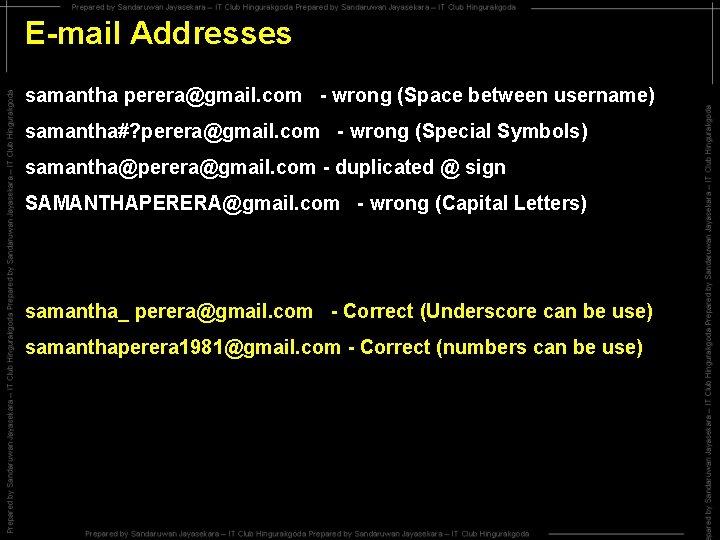
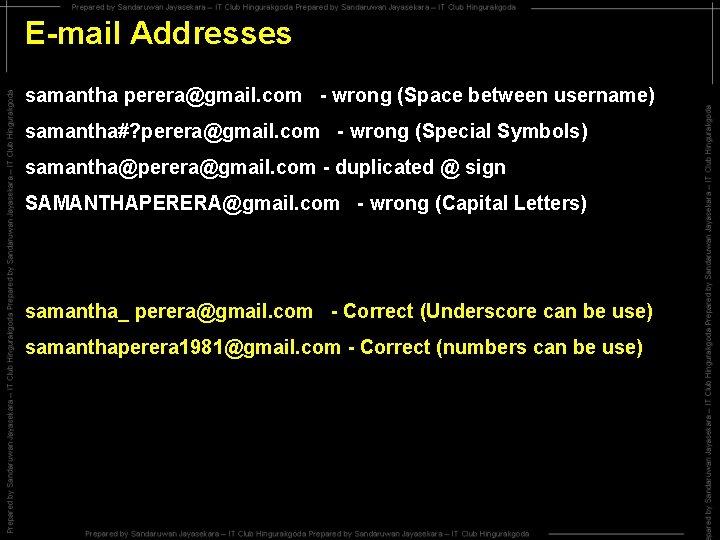
E-mail Addresses samantha perera@gmail. com - wrong (Space between username) samantha#? perera@gmail. com - wrong (Special Symbols) samantha@perera@gmail. com - duplicated @ sign SAMANTHAPERERA@gmail. com - wrong (Capital Letters) samantha_ perera@gmail. com - Correct (Underscore can be use) samanthaperera 1981@gmail. com - Correct (numbers can be use)

E-mail Addresses samantha@gmail. com We can create email accounts through…. www. google. com – username@gmail. com www. yahoo. com – username@yahoo. com www. esrilanka. lk – username@esrilanka. lk Through Telecom – username@slt. lk