Computer Forensics Principles and Practices by Volonino Anzaldua
Computer Forensics Principles and Practices by Volonino, Anzaldua, and Godwin © Pearson Education Computer Forensics: Chapter 2: Computer Principles and Practices Forensics and Digital Detective Work
Objectives n n Recognize the role e-evidence plays in physical, or violent, and computer crimes Describe the basic steps in a computer forensics investigation Identify the legal and ethical issues affecting evidence search and seizure Identify the types of challenges to the admissibility of e-evidence © Pearson Education Computer Forensics: Principles and Practices 2
Objectives (Cont. ) n n n Understand how criminals’ motives can help in crime detection and investigation Explain chain of custody Explain why acceptable methods for computer forensics investigations and ediscovery are still emerging © Pearson Education Computer Forensics: Principles and Practices 3
Introduction Computer forensics investigators are “detectives of the digital world. ” This chapter introduces you to the generally accepted methods used in computer forensics; computer architecture, the Internet, and digital devices, and the types of evidence these trails leave behind. © Pearson Education Computer Forensics: Principles and Practices 4
E-Evidence Trails and Hidden Files n n Computers are routinely used to plan and coordinate many types of crimes Computer activities leave e-evidence trails q q n File-wiping software can be used to delete data File-wiping process takes time and expertise Many e-evidence traces can be found by showing hidden files on a computer © Pearson Education Computer Forensics: Principles and Practices 5
Knowing What to Look For n n Technical knowledge of how data and metadata are stored will determine what eevidence is found For this reason, technical knowledge of investigators must keep pace with evolving data storage devices © Pearson Education Computer Forensics: Principles and Practices 6
Knowing What to Look for (Cont. ) n Three cases illustrate importance of technical knowledge: q q q Dr. Harold Shipman modified medical records to hide evidence of murder; date stamp revealed records were fraudulent Employees made online purchases with customer credit cards; hidden HTML code revealed fraud Neil Entwhistle killed his wife and child; cache showed Internet sites that described how to kill people © Pearson Education Computer Forensics: Principles and Practices 7
The Five Ws n Answering the 5 Ws helps in criminal investigations: q q q Who What Where When Why © Pearson Education Computer Forensics: Principles and Practices 8
In Practice: PDA Forensics n n PDA forensics are being used frequently in homicide investigations and white collar crimes Examples: q q Danielle van Dam murder, February 2002 Falsely billing for Medicaid and Medicare patients that were never seen © Pearson Education Computer Forensics: Principles and Practices 9
Preserving Evidence n n Preserving evidence is critical in order to use the evidence in a legal defense or prosecution Scientific methods must be used in order to preserve the integrity of the evidence collected © Pearson Education Computer Forensics: Principles and Practices 10
Computer Forensics Science n n Consistent with other scientific research, a computer forensics investigation is a process There are five stages to the process: q q q Intelligence Hypothesis or Theory Formulation Evidence Collection Testing Conclusion © Pearson Education Computer Forensics: Principles and Practices 11
Admissibility of Evidence n n Goal of an investigation: collect evidence using accepted methods so that the evidence is accepted in the courtroom and admitted as evidence in the trial Judge’s acceptance of evidence is called admission of evidence © Pearson Education Computer Forensics: Principles and Practices 12
Admissibility of Evidence (Cont. ) n n Evidence admissibility requires legal search and seizure and chain of custody Chain of custody must include: q q q n Where the evidence was stored Who had access to the evidence What was done to the evidence In some cases, it may be more important to protect operations than obtain admissible evidence © Pearson Education Computer Forensics: Principles and Practices 13
In Practice: CD Universe Prosecution Failure n n n Attempted extortion involving credit card numbers by “Maxim” Six months after the incident, Maxim still could not be found Evidence was compromised by FBI and security firms who may have used original data rather than a forensic copy © Pearson Education Computer Forensics: Principles and Practices 14
Digital Signatures and Profiling n Digital signature left by serial killer q q n Dennis L. Rader revealed as “BTK” Hidden electronic code on disk led to church where he had access to a computer Digital profiling of crime suspects q q E-evidence can supply patterns of behavior or imply motives Evidence can include information stored on computers, e-mail, cell phone data, and wiretaps © Pearson Education Computer Forensics: Principles and Practices 15
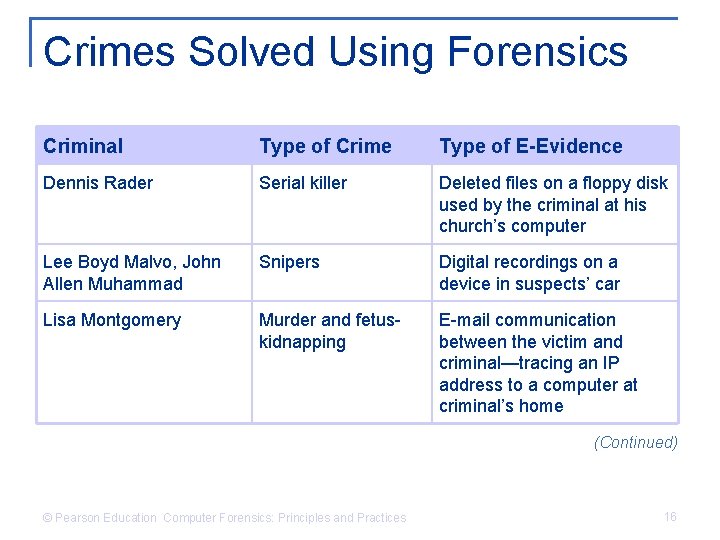
Crimes Solved Using Forensics Criminal Type of Crime Type of E-Evidence Dennis Rader Serial killer Deleted files on a floppy disk used by the criminal at his church’s computer Lee Boyd Malvo, John Allen Muhammad Snipers Digital recordings on a device in suspects’ car Lisa Montgomery Murder and fetuskidnapping E-mail communication between the victim and criminal—tracing an IP address to a computer at criminal’s home (Continued) © Pearson Education Computer Forensics: Principles and Practices 16
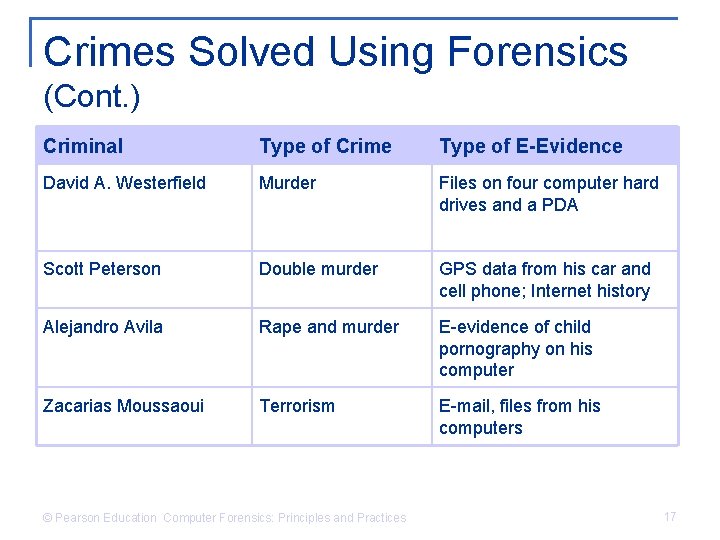
Crimes Solved Using Forensics (Cont. ) Criminal Type of Crime Type of E-Evidence David A. Westerfield Murder Files on four computer hard drives and a PDA Scott Peterson Double murder GPS data from his car and cell phone; Internet history Alejandro Avila Rape and murder E-evidence of child pornography on his computer Zacarias Moussaoui Terrorism E-mail, files from his computers © Pearson Education Computer Forensics: Principles and Practices 17
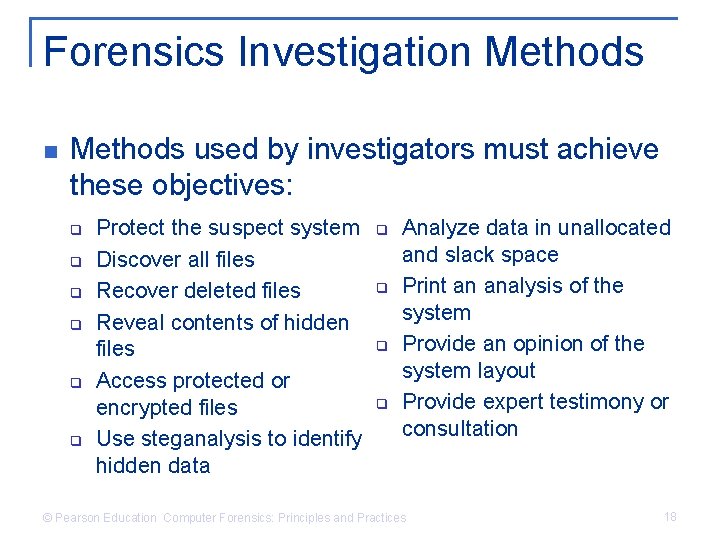
Forensics Investigation Methods used by investigators must achieve these objectives: q q q Protect the suspect system Discover all files Recover deleted files Reveal contents of hidden files Access protected or encrypted files Use steganalysis to identify hidden data q q Analyze data in unallocated and slack space Print an analysis of the system Provide an opinion of the system layout Provide expert testimony or consultation © Pearson Education Computer Forensics: Principles and Practices 18
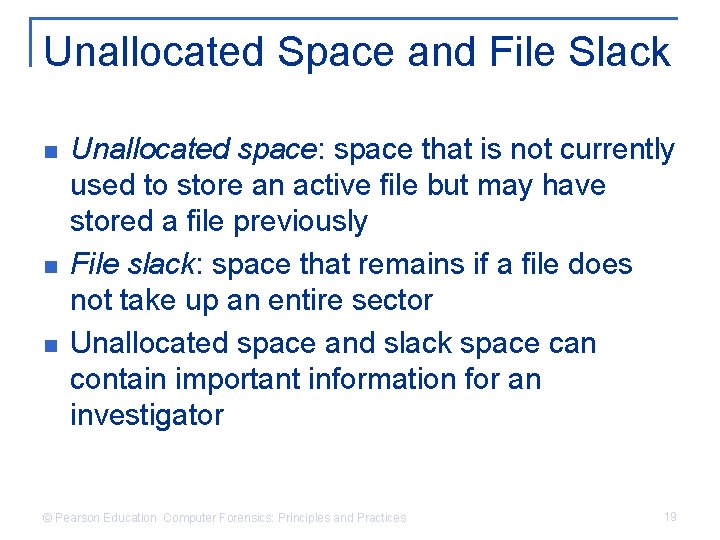
Unallocated Space and File Slack n n n Unallocated space: space that is not currently used to store an active file but may have stored a file previously File slack: space that remains if a file does not take up an entire sector Unallocated space and slack space can contain important information for an investigator © Pearson Education Computer Forensics: Principles and Practices 19
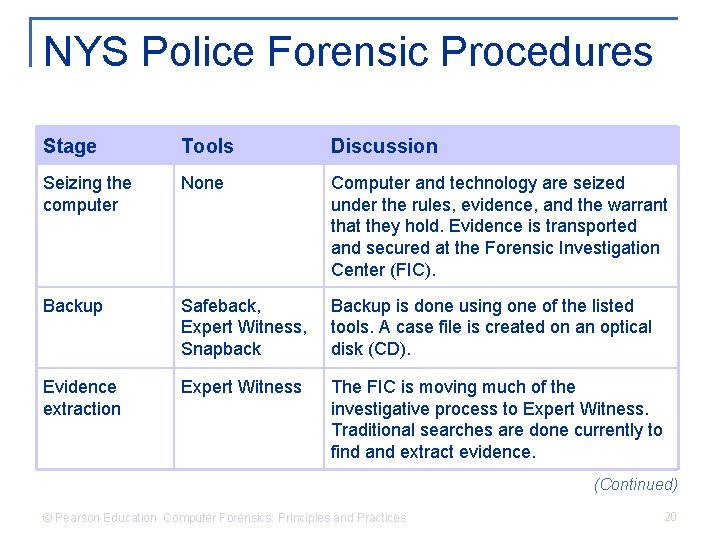
NYS Police Forensic Procedures Stage Tools Discussion Seizing the computer None Computer and technology are seized under the rules, evidence, and the warrant that they hold. Evidence is transported and secured at the Forensic Investigation Center (FIC). Backup Safeback, Expert Witness, Snapback Backup is done using one of the listed tools. A case file is created on an optical disk (CD). Evidence extraction Expert Witness The FIC is moving much of the investigative process to Expert Witness. Traditional searches are done currently to find and extract evidence. (Continued) © Pearson Education Computer Forensics: Principles and Practices 20
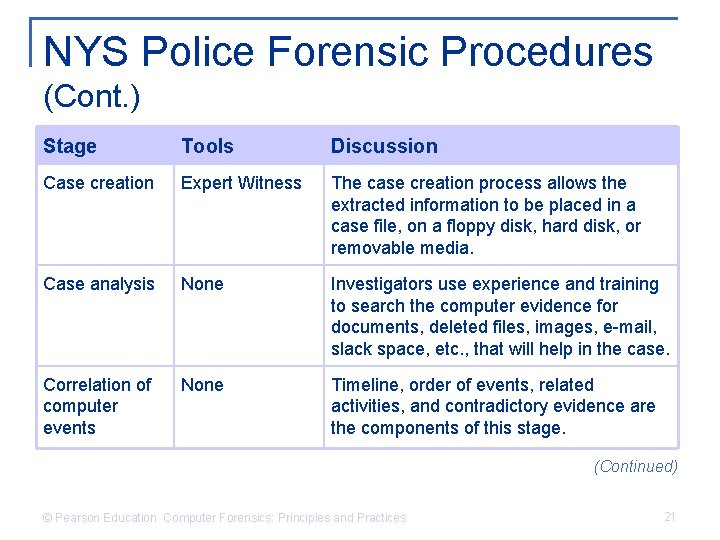
NYS Police Forensic Procedures (Cont. ) Stage Tools Discussion Case creation Expert Witness The case creation process allows the extracted information to be placed in a case file, on a floppy disk, hard disk, or removable media. Case analysis None Investigators use experience and training to search the computer evidence for documents, deleted files, images, e-mail, slack space, etc. , that will help in the case. Correlation of computer events None Timeline, order of events, related activities, and contradictory evidence are the components of this stage. (Continued) © Pearson Education Computer Forensics: Principles and Practices 21
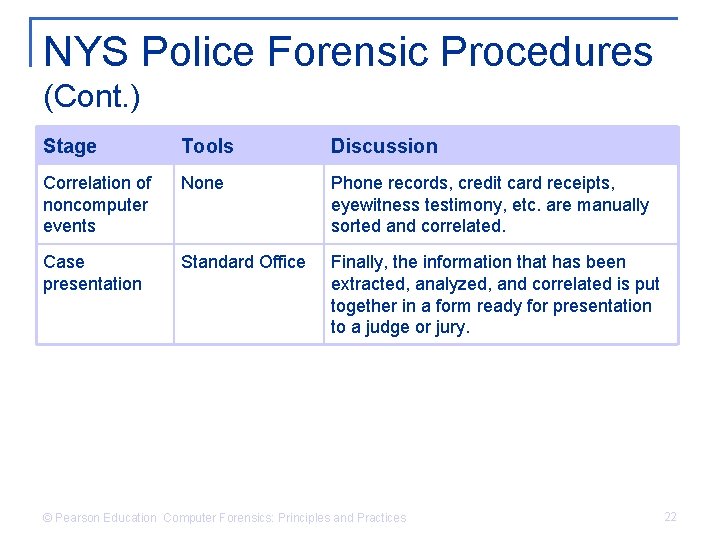
NYS Police Forensic Procedures (Cont. ) Stage Tools Discussion Correlation of noncomputer events None Phone records, credit card receipts, eyewitness testimony, etc. are manually sorted and correlated. Case presentation Standard Office Finally, the information that has been extracted, analyzed, and correlated is put together in a form ready for presentation to a judge or jury. © Pearson Education Computer Forensics: Principles and Practices 22
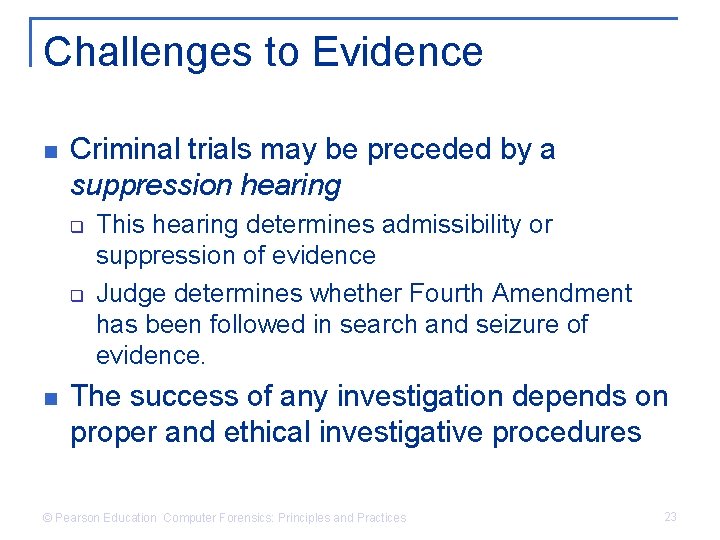
Challenges to Evidence n Criminal trials may be preceded by a suppression hearing q q n This hearing determines admissibility or suppression of evidence Judge determines whether Fourth Amendment has been followed in search and seizure of evidence. The success of any investigation depends on proper and ethical investigative procedures © Pearson Education Computer Forensics: Principles and Practices 23
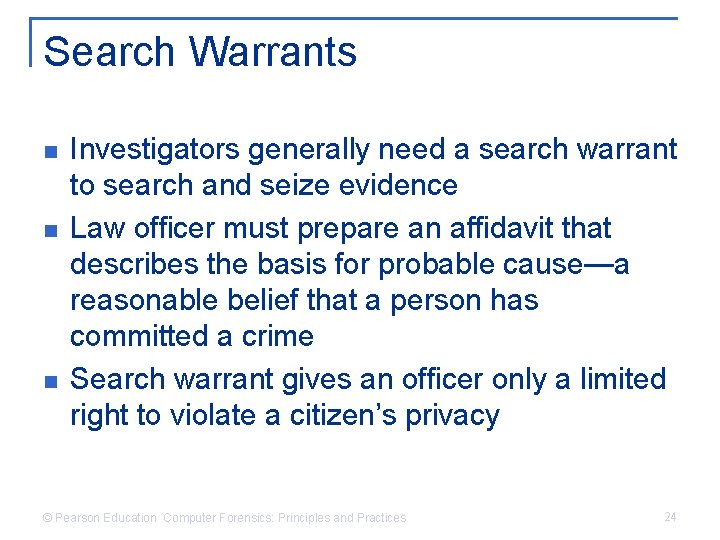
Search Warrants n n n Investigators generally need a search warrant to search and seize evidence Law officer must prepare an affidavit that describes the basis for probable cause—a reasonable belief that a person has committed a crime Search warrant gives an officer only a limited right to violate a citizen’s privacy © Pearson Education Computer Forensics: Principles and Practices 24
Search Warrants (Cont. ) n Two reasons a search can take place without a search warrant: q q The officer may search for and remove any weapons that the arrested person may use to escape or resist arrest The officer may seize evidence in order to prevent its destruction or concealment © Pearson Education Computer Forensics: Principles and Practices 25
In Practice: A Terrorist’s Trial n n FBI agents attempted to get permission to search Moussaoui’s laptop but permission was denied on grounds they had not proved probable cause Events on September 11 provided enough evidence for a search warrant, but by this time it was too late to access e-mail accounts that might have provided important data © Pearson Education Computer Forensics: Principles and Practices 26
Motives for Cybercrimes n n Finding the motive—the “why” of the crime— can help in an investigation Possible motives: q q q Financial gain, including extortion and blackmail Cover up a crime Remove incriminating information or correspondence Steal goods or services without having to pay for them Industrial espionage © Pearson Education Computer Forensics: Principles and Practices 27
Categories of Cybercrimes n n Computer is the crime target Computer is the crime instrument Computer is incidental to traditional crimes New crimes generated by the prevalence of computers © Pearson Education Computer Forensics: Principles and Practices 28
Chain of Custody Procedures n n Handling of e-evidence must follow the three C’s of evidence: care, control, and chain of custody Chain of custody procedures q q q Keep an evidence log that shows when evidence was received and seized, and where it is located Record dates if items are released to anyone Restrict access to evidence Place original hard drive in an evidence locker Perform all forensics on a mirror-image copy, never on the original data © Pearson Education Computer Forensics: Principles and Practices 29
Report Procedures n n n All reports of the investigation should be prepared with the understanding that they will be read by others The investigator should never comment on the guilt or innocence of a suspect or suspects or their affiliations Only the facts of the investigation should be presented; opinions should be avoided © Pearson Education Computer Forensics: Principles and Practices 30
Computer Forensics Investigator’s Responsibilities n n Investigate and/or review current computer and computer-mediated crimes Maintain objectivity when seizing and investigating computers, suspects, and support staff Conduct all forensics investigations consistently with generally accepted procedures and federal rules of evidence and discovery Keep a log of activities undertaken to stay current in the search, seizure, and processing of e-evidence © Pearson Education Computer Forensics: Principles and Practices 31
Summary n n n Computers and the Internet have contributed to traditional and computer crimes Effective forensic investigation requires any technology that tracks what was done, who did it, and when Images or exact copies of the digital media being investigated need to be examined by trained professionals © Pearson Education Computer Forensics: Principles and Practices 32
Summary (Cont. ) n n There are several legal and ethical issues of evidence seizure, handling, and investigation New federal rules and laws regulate forensic investigations The need for e-evidence has led to a new area of criminal investigation, namely computer forensics This field is less than 15 years old © Pearson Education Computer Forensics: Principles and Practices 33
Summary (Cont. ) n n n Computer forensics depends on an understanding of technical and legal issues Greatest legal issue in computer forensics is the admissibility of evidence in criminal cases Computer forensics investigators identify, gather, extract, protect, preserve, and document computer and other e-evidence using acceptable methods © Pearson Education Computer Forensics: Principles and Practices 34
Summary (Cont. ) n n Laws of search and seizure, as they relate to electronic equipment, must be followed Failure to follow proper legal procedure will result in evidence being ruled inadmissible in court © Pearson Education Computer Forensics: Principles and Practices 35
- Slides: 35