Computer Forensics Definition What is Computer Forensics Computer

- Slides: 82
Computer Forensics
Definition • What is Computer Forensics? ? – Computer forensics involves the preservation, identification, extraction, documentation, and interpretation of computer media for evidentiary and/or root cause analysis. – Evidence might be required for a wide range of computer crimes and misuses – Multiple methods of • Discovering data on computer system • Recovering deleted, encrypted, or damaged file information • Monitoring live activity • Detecting violations of corporate policy – Information collected assists in arrests, prosecution, termination of employment, and preventing future illegal activity
The Field of Computer Forensics What is Computer Forensics? ðScientific process of preserving, identifying, extracting, documenting, and interpreting data on computer ðUsed to obtain potential legal evidence
COMPUTER FORENSICS CAN BE MANY THINGS • Corporate or University internal investigation • FBI or (unlikely) Sheriff investigation • Computer Security Research • Post Mortem or Damage Assessment § § Child Pornography Fraud Espionage & Treason Corporate or University Policy Violation § Honey-pots Computer Forensics ultimately support or refute a case someone cares to make.
History of Computer Forensics Michael Anderson ð“Father of computer forensics” ðspecial agent with IRS Meeting in 1988 (Portland, Oregon) ðcreation of IACIS, the International Association of Computer Investigative Specialists ðthe first Seized Computer Evidence Recovery Specialists (SCERS) classes held
Certification for Computer Investigative Specialists CEECS (Certified Electronic Evidence Collection Specialist Certification) ð Awarded to individuals who complete the CEECS regional certification course ð Also awarded to individuals in the Certified Forensic Computer Examiner course that successfully pass the written test

Certification for Forensic Computer Examiner Internal Certification Training Program ð Must successfully complete two week training course offered by IACIS and correspondence proficiency problems External Certification Testing Process ð Not a training course ð Testing process Active Law Enforcement Individuals qualified for IACIS membership Recertification ð Every three years must complete recertification process Must be in good standing with IACIS Complete proficiency test
Collecting Evidence Make Exact copies of all hard drives & disks using computer software ð Date and Time stamped on each file; used for timeline Protect the Computer system ð Avoid deletion, damage, viruses and corruption Discover files ð ð ð Normal Files Deleted Files Password Protected Files Hidden Files Encrypted Files Reveal all contents of hidden files used by application and operating system Access contents of password protected files if legally able to do so Analyze data Print out analysis ð Computer System ð All Files and data ð Overall opinion Provide expert
How Evidence is Protected A Computer Forensic Specialist promises to: Not delete, damage or alter any evidence Protect the computer and files against a virus Handle all evidence properly to prevent any future damage Keep a log of all work done and by whom Keep any Client-Attorney information that is gained confidential
Advantages of Computer Forensics Ability to search through a massive amount of data ðQuickly ðThoroughly ðIn any language
Disadvantages of Computer Forensics Digital evidence accepted into court ð must prove that there is no tampering ð all evidence must be fully accounted for ð computer forensic specialists must have complete knowledge of legal requirements, evidence handling and storage and documentation procedures
Disadvantages of Computer Forensics Costs ðproducing electronic records & preserving them is extremely costly Sattar vs. Motorola Inc Presents the potential for exposing privileged documents Legal practitioners must have extensive computer knowledge
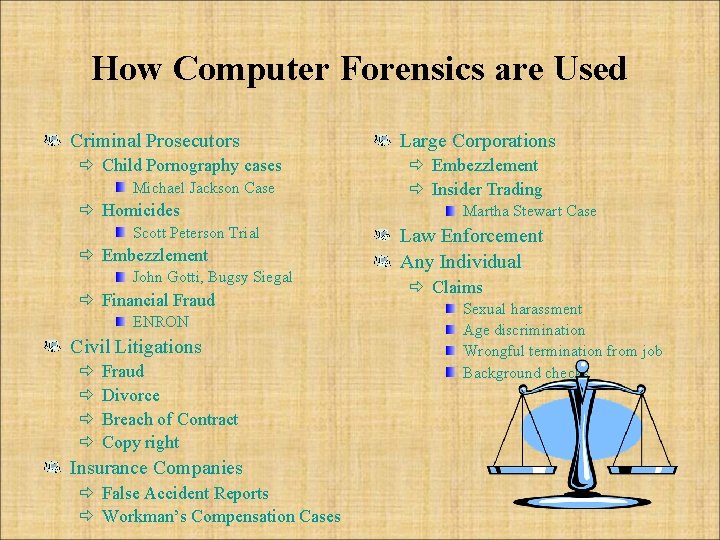
How Computer Forensics are Used Criminal Prosecutors ð Child Pornography cases Michael Jackson Case ð Homicides Scott Peterson Trial ð Embezzlement John Gotti, Bugsy Siegal ð Financial Fraud ENRON Civil Litigations ð ð Fraud Divorce Breach of Contract Copy right Insurance Companies ð False Accident Reports ð Workman’s Compensation Cases Large Corporations ð Embezzlement ð Insider Trading Martha Stewart Case Law Enforcement Any Individual ð Claims Sexual harassment Age discrimination Wrongful termination from job Background checks
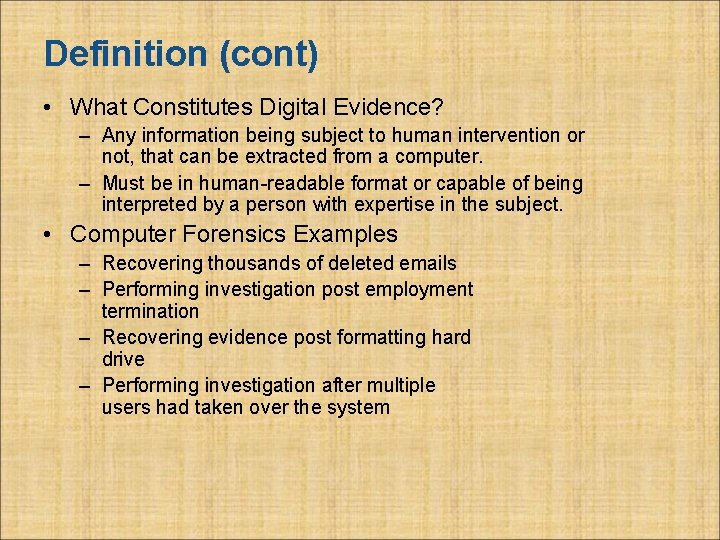
Definition (cont) • What Constitutes Digital Evidence? – Any information being subject to human intervention or not, that can be extracted from a computer. – Must be in human-readable format or capable of being interpreted by a person with expertise in the subject. • Computer Forensics Examples – Recovering thousands of deleted emails – Performing investigation post employment termination – Recovering evidence post formatting hard drive – Performing investigation after multiple users had taken over the system
Computer Forensics …. Mostly a success story - < 14 years • Data from computers can be reliably preserved and presented in court • Deleted data can be recovered • Events can be reconstructed • Intentions can be inferred Lots of good products and procedures to support …. (c)Peter Sommer 2002
(c)Peter Sommer 2002
(c)Peter Sommer 2002
Computer Forensics …. deployed in: • • hacking fraud paedophiliac rings defamation immigration fraud narcotics trafficking credit card cloning software piracy • • electoral law obscene publication perjury forgery murder sexual harassment data theft – industrial espionage • divorce (c)Peter Sommer 2002
Computer Forensics …. But this has been mostly about DISK forensics, specifically disks in PCs What about: • evidence from large systems? • evidence from remote sites? • evidence from networks? • evidence from data eavesdropped in transmission? (c)Peter Sommer 2002
Computer Forensics …. Are the very high standards now existing for disk forensics creating unrealistic expectations for all other forms of computer-derived evidence? (c)Peter Sommer 2002
Science vs Forensic Science vs What Courts Do • Science: providing generalised descriptions which reduce the chaos of the observable world – major discoveries – minor discoveries • Forensic science: (almost) a series of technologies to aid legal process – major discoveries – minor discoveries (c)Peter Sommer 2002
Science vs Forensic Science vs What Courts Do • Forensic science, like regular science, advances by means of peer-reviewed publication (c)Peter Sommer 2002
Science vs Forensic Science vs What Courts Do • In court: the decisions to be made are not “scientific” - judges and juries decide on: – was a contract broken? – was there a breach of duty of care? – was some-one defamed? – were the tests for a specific criminal offence satisfied? (c)Peter Sommer 2002
Science vs Forensic Science vs What Courts Do • Tests in court: – balance of probabilities – beyond a reasonable doubt • Evidence from “scientists” and “experts” only part of the overall mix (c)Peter Sommer 2002
Science vs Forensic Science vs What Courts Do • Legal proof is what is demonstrated before the court • Legal proof is about arriving at a conclusion from a specific set of circumstances • Limits of Scientific Evidence: R v Adams, R v Dohenny (1996) AC – DNA evidence, Bayesian probabilities (c)Peter Sommer 2002
Reasons For Evidence • Wide range of computer crimes and misuses – Non-Business Environment: evidence collected by Federal, State and local authorities for crimes relating to: • • • Theft of trade secrets Fraud Extortion Industrial espionage Position of pornography SPAM investigations Virus/Trojan distribution Homicide investigations Intellectual property breaches Unauthorized use of personal information Forgery Perjury
Reasons For Evidence (cont) • Computer related crime and violations include a range of activities including: – Business Environment: • Theft of or destruction of intellectual property • Unauthorized activity • Tracking internet browsing habits • • • Reconstructing Events Inferring intentions Selling company bandwidth Wrongful dismissal claims Sexual harassment Software Piracy
Who Uses Computer Forensics? • Criminal Prosecutors – Rely on evidence obtained from a computer to prosecute suspects and use as evidence • Civil Litigations – Personal and business data discovered on a computer can be used in fraud, divorce, harassment, or discrimination cases • Insurance Companies – Evidence discovered on computer can be used to mollify costs (fraud, worker’s compensation, arson, etc) • Private Corporations – Obtained evidence from employee computers can be used as evidence in harassment, fraud, and embezzlement cases
Who Uses Computer Forensics? (cont) • Law Enforcement Officials – Rely on computer forensics to backup search warrants and post-seizure handling • Individual/Private Citizens – Obtain the services of professional computer forensic specialists to support claims of harassment, abuse, or wrongful termination from employment
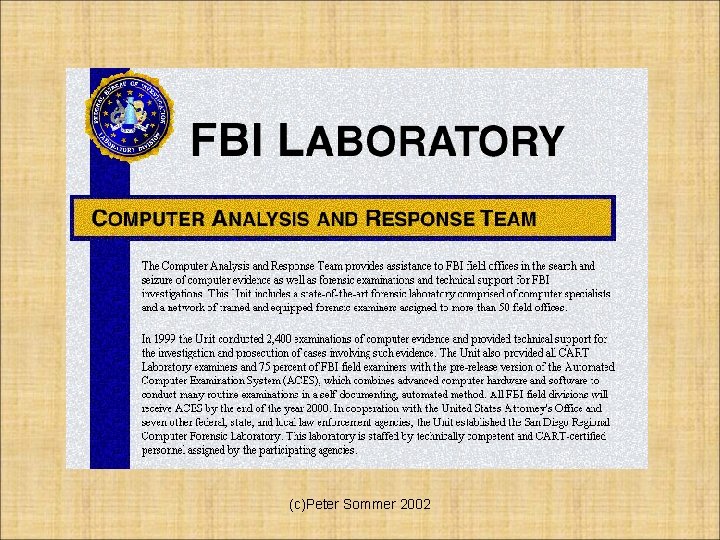
FBI Computer Forensic Services • • • Content Comparison again known data Transaction sequencing Extraction of data Recovering deleted data files Format conversion Keyword searching Decrypting passwords Analyzing and comparing limited source code
Steps Of Computer Forensics • According to many professionals, Computer Forensics is a four (4) step process – Acquisition • Physically or remotely obtaining possession of the computer, all network mappings from the system, and external physical storage devices – Identification • This step involves identifying what data could be recovered and electronically retrieving it by running various Computer Forensic tools and software suites – Evaluation • Evaluating the information/data recovered to determine if and how it could be used again the suspect for employment termination or prosecution in court
Steps Of Computer Forensics (cont) – Presentation • This step involves the presentation of evidence discovered in a manner which is understood by lawyers, non-technically staff/management, and suitable as evidence as determined by United States and internal laws
Handling Evidence • Admissibility of Evidence – Legal rules which determine whether potential evidence can be considered by a court – Must be obtained in a manner which ensures the authenticity and validity and that no tampering had taken place • No possible evidence is damaged, destroyed, or otherwise compromised by the procedures used to search the computer • Preventing viruses from being introduced to a computer during the analysis process • Extracted / relevant evidence is properly handled and protected from later mechanical or electromagnetic damage
Handling Evidence (cont) • Establishing and maintaining a continuing chain of custody • Limiting the amount of time business operations are affected • Not divulging and respecting any ethically [and legally] client-attorney information that is inadvertently acquired during a forensic exploration
Evidence Recovery • The process of evidence extraction can be easy or complicated depending on the nature of the incident and the type of computer or network upon which the incident took place. • What do I extract and What do I leave behind? - Extract and collect as much as you can
Candidates for Evidence Extraction • Computers, printers, scanners, network connectors, modem, routers, hubs, switches, system programs, logs, application software, etc, scrap paers, documents, persons, backup tapes, disks
An investigator should start the job only when the items are at hand • • • Forensic toolkit – forensic workstation A search kit Search and evidence forms and sketch plan sheets Evidence bag Stil, digital, etc cameras Disk boxes Mobile phone Empty disks Flash light Evidence container Etc
Gather evidence by following the steps • Arrange interviews with all parties • Fillout the evidence form • Copy the digital evidence disk by making a bit-stream copy or bit-by-bit copy
Preserving Evidence • Catalog and package evidence in a secure bags or containers • Back pu the original data including doing a disk imaging of all suspected media. • Document and timestamp • Implement a credible control access system • Encryptions • Trusted tools to be used • Validate and authenticate the data
Transporitng Evidence
Initiating An Investigation • DO NOT begin by exploring files on system randomly • Establish evidence custodian - start a detailed journal with the date and time and date/information discovered • If possible, designate suspected equipment as “off-limits” to normal activity. This includes backups, remotely or locally scheduled house-keeping, and configuration changes • Collect email, DNS, and other network service logs
Initiating An Investigation (cont) • Capture exhaustive external TCP and UDP port scans of the host – Could present a problem if TCP is wrapped • Contact security personnel [CERT], management, Federal and local enforcement, as well as affected sites or persons
Incidence Response • Identify, designate, or become evidence custodian • Review any existing journal of what has been done to system already and/or how intrusion was detected • Begin new or maintain existing journal • Install monitoring tools (sniffers, port detectors, etc. ) • Without rebooting or affecting running processes, perform a copy of physical disk • Capture network information
Incidence Response (cont) • Capture processes and files in use (e. g. dll, exe) • Capture config information • Receipt and signing of data
Handling Information • Information and data being sought after and collected in the investigation must be properly handled • Volatile Information – Network Information • Communication between system and the network – Active Processes • Programs and daemons currently active on the system – Logged-on Users • Users/employees currently using system – Open Files • Libraries in use; hidden files; Trojans (rootkit) loaded in system
Handling Information (cont) • Non-Volatile Information – This includes information, configuration settings, system files and registry settings that are available after reboot – Accessed through drive mappings from system – This information should investigated and reviewed from a backup copy
Computer Forensic Requirements • Hardware – Familiarity with all internal and external devices/components of a computer – Thorough understanding of hard drives and settings – Understanding motherboards and the various chipsets used – Power connections – Memory • BIOS – Understanding how the BIOS works – Familiarity with the various settings and limitations of the BIOS
Computer Forensic Requirements • Operation Systems – – – Windows 3. 1/95/98/ME/NT/2000/2003/XP DOS UNIX LINUX VAX/VMS • Software – Familiarity with most popular software packages such as Office • Forensic Tools – Familiarity with computer forensic techniques and the software packages that could be used (cont)
Anti-Forensics • Software that limits and/or corrupts evidence that could be collected by an investigator • Performs data hiding and distortion • Exploits limitations of known and used forensic tools • Works both on Windows and LINUX based systems • In place prior to or post system acquisition
Evidence Processing Guidelines • New Technologies Inc. recommends following 16 steps in processing evidence • They offer training on properly handling each step – Step 1: Shut down the computer • Considerations must be given to volatile information • Prevents remote access to machine and destruction of evidence (manual or ant-forensic software) – Step 2: Document the Hardware Configuration of The System • Note everything about the computer configuration prior to re-locating
Evidence Processing Guidelines (cont) – Step 3: Transport the Computer System to A Secure Location • Do not leave the computer unattended unless it is locked in a secure location – Step 4: Make Bit Stream Backups of Hard Disks and Floppy Disks – Step 5: Mathematically Authenticate Data on All Storage Devices • Must be able to prove that you did not alter any of the evidence after the computer came into your possession – Step 6: Document the System Date and Time – Step 7: Make a List of Key Search Words – Step 8: Evaluate the Windows Swap File
Evidence Processing Guidelines (cont) – Step 9: Evaluate File Slack • File slack is a data storage area of which most computer users are unaware; a source of significant security leakage. – Step 10: Evaluate Unallocated Space (Erased Files) – Step 11: Search Files, File Slack and Unallocated Space for Key Words – Step 12: Document File Names, Dates and Times – Step 13: Identify File, Program and Storage Anomalies – Step 14: Evaluate Program Functionality – Step 15: Document Your Findings – Step 16: Retain Copies of Software Used
Methods Of Hiding Data • Covert Channels – Hiding in Transmission – Take advantage of timing or shared storage to pass data through unsuspected channel • EXAMPLE: IP datagram – Header Redundancy – Known Maximum Transfer Unit (MTU) • A datagram (IP) is encapsulated into frame (header, datagram, trailer). MTU is the max total size of this datagram. • To make IP independent of physical network, MTU = 65, 535 bytes to give it more efficiency. • If the physical layer doesn’t support that MTU, the datagram must be fragmented
Methods Of Hiding Data (cont) • EXAMPLE: Continued… – Flags: 3 bits • 1 st bit: reserved (always 0) • 2 nd bit: Do not fragment (DF): if 1, can’t be fragmented. If it is too large to pass through any available physical network, it is discarded • 3 rd bit: More fragment (MF): if 1, the datagram is not the last fragment of the original datagram, if 0, it is last one or there is only 1 fragment (the original datagram)
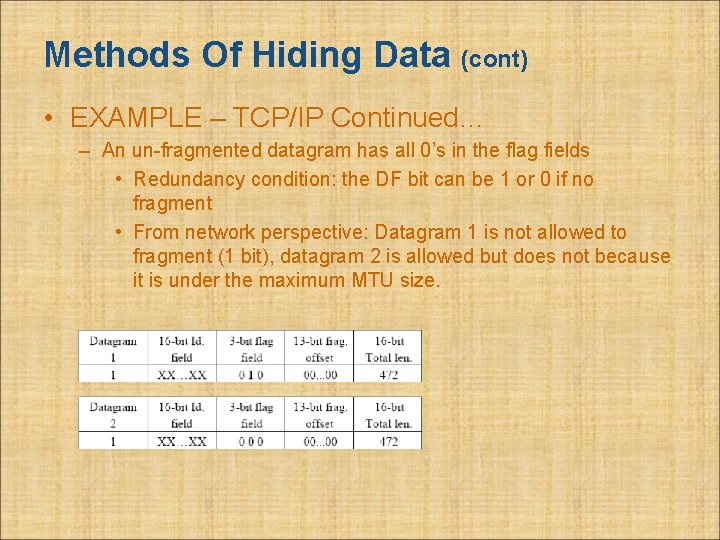
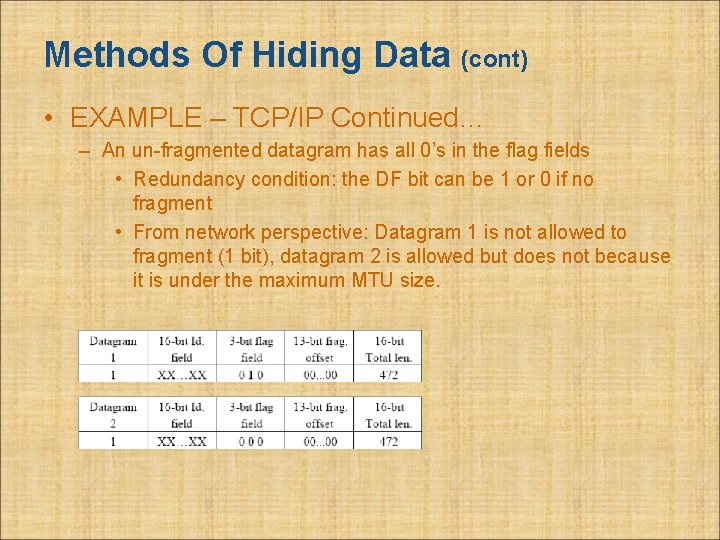
Methods Of Hiding Data (cont) • EXAMPLE – TCP/IP Continued… – An un-fragmented datagram has all 0’s in the flag fields • Redundancy condition: the DF bit can be 1 or 0 if no fragment • From network perspective: Datagram 1 is not allowed to fragment (1 bit), datagram 2 is allowed but does not because it is under the maximum MTU size.
Methods Of Hiding Data (cont) • To human eyes, data usually contains known forms, like images, e-mail, sounds, and text. Most Internet data naturally includes gratuitous headers, too. These are media exploited using new controversial logical encodings: steganography and marking. • Steganography: The art of storing information in such a way that the existence of the information is hidden.
Methods Of Hiding Data (cont) • To human eyes, data usually contains known forms, like images, e-mail, sounds, and text. Most Internet data naturally includes gratuitous headers, too. These are media exploited using new controversial logical encodings: steganography and marking. • The duck flies at midnight. Tame uncle Sam – Simple but effective when done well
Methods Of Hiding Data (cont) • Watermarking: Hiding data within data – Information can be hidden in almost any file format. – File formats with more room for compression are best • Image files (JPEG, GIF) • Sound files (MP 3, WAV) • Video files (MPG, AVI) – The hidden information may be encrypted, but not necessarily – Numerous software applications will do this for you: Many are freely available online
Methods Of Hiding Data (cont) • Hard Drive/File System manipulation – Slack Space is the space between the logical end and the physical end of file and is called the file slack. The logical end of a file comes before the physical end of the cluster in which it is stored. The remaining bytes in the cluster are remnants of previous files or directories stored in that cluster. • Slack space can be accessed and written to directly using a hex editor. • This does not add any “used space” information to the drive – Partition waste space is the rest of the unused track which the boot sector is stored on – usually 10 s, possibly 100 s of sectors skipped • After the boot sector, the rest of the track is left empty
Methods Of Hiding Data (cont) • Hard Drive/File System manipulation cont… – Hidden drive space is non-partitioned space inbetween partitions • The File Allocation Table (FAT) is modified to remove any reference to the non-partitioned space • The address of the sectors must be known in order to read/write information to them – Bad sectors occur when the OS attempts to read info from a sector unsuccessfully. After a (specified) # of unsuccessful tries, it copies (if possible) the information to another sector and marks (flags) the sector as bad so it is not read from/written to again • users can control the flagging of bad sectors • Flagged sectors can be read to /written from with direct reads and writes using a hex editor
Methods Of Hiding Data (cont) • Hard Drive/File System manipulation cont… – Extra Tracks: most hard disks have more than the rated # of tracks to make up for flaws in manufacturing (to keep from being thrown away because failure to meet minimum #). • Usually not required or used, but with direct (hex editor) reads and writes, they can be used to hide/read data – Change file names and extensions – i. e. rename a. doc file to a. dll file
Methods Of Hiding Data (cont) • Other Methods – Manipulating HTTP requests by changing (unconstrained) order of elements • The order of elements can be preset as a 1 or 0 bit • No public software is available for use yet, but the government uses this method for its agents who wish to transfer sensitive information online • Undetectable because there is no standard for the order of elements and it is, in essence, just normal web browsing – Encryption: The problem with this is that existence of data is not hidden, instead it draws attention to itself. • With strong enough encryption, it doesn’t matter if its existence is known
Methods Of Detecting/Recovering Data • Steganalysis - the art of detecting and decoding hidden data – Hiding information within electronic media requires alterations of the media properties that may introduce some form of degradation or unusual characteristics – The pattern of degradation or the unusual characteristic of a specific type of steganography method is called a signature – Steganalysis software can be trained to look for a signature
Methods Of Detecting/Recovering Data (cont) • Steganalysis Methods - Detection – Human Observation • Opening a text document in a common word processor may show appended spaces and “invisible” characters • Images and sound/video clips can be viewed or listened to and distortions may be found – Generally, this only occurs if the amount of data hidden inside the media is too large to be successfully hidden within the media (15% rule) – Software analysis • Even small amounts of processing can filter out echoes and shadow noise within an audio file to search for hidden information • If the original media file is available, hash values can easily detect modifications
Methods Of Detecting/Recovering Data (cont) • Steganalysis Methods – Detection cont. . . – Disk analysis utilities can search the hard drive for hidden tracks/sectors/data – RAM slack is the space from the end of the file to the end of the containing sector. Before a sector is written to disk, it is stored in a buffer somewhere in RAM. If the buffer is only partially filled with information before being committed to disk, remnants from the end of the buffer will be written to disk. In this way, information that was never "saved" can be found in RAM slack on disk. – Firewall/Routing filters can be applied to search for hidden or invalid data in IP datagram headers
Methods Of Detecting/Recovering Data (cont) • Steganalysis Methods – Detection cont. . . – Statistical Analysis • Most steganographic algorithms that work on images assume that the Least Significant Bit (LSB) is random • If a filter is applied to an image, the LSB bits will produce a recognizable image, so the assumption is wrong • After inserting hidden information into an image, the LSB is no longer non-random (especially with encrypted data). If you apply the same filter, it will no longer produce a recognizable image • Statistical analysis of the LSB will tell you if the LSB bits are random or not • Can be applied to audio files as well (using LSB) – Frequency scanning • Software can search for high, inaudible frequencies
Methods Of Detecting/Recovering Data (cont) • Steganalysis Methods – Recovery of watermarked data is extremely hard • Currently, there are very few methods to recover hidden, encrypted data. – Data hidden on disk is much easier to find. Once found, if unencrypted, it is already recovered – Deleted data can be reconstructed (even on hard drives that have been magnetically wiped) – Check swap files for passwords and encryption keys which are stored in the clear (unencrypted) – Software Tools • Scan for and reconstruct deleted data • Break encryption • Destroy hidden information (overwrite)
Preparing a Computer Investigation • Role of computer forensics professional: gather evidence to prove a suspect committed a crime or violated a company policy • Collect evidence that can be offered in court or at a corporate inquiry – Investigate the suspect’s computer – Preserve the evidence on a different computer 68
Preparing a Computer Investigation (continued) • Follow an accepted procedure to prepare a case • The U. S. Department of Justice has a document you can download that reviews proper acquisition of electronic evidence • Searching and Seizing Computers • Chain of custody – Route the evidence takes from the time you find it until the case is closed or goes to court 69
Examining a Computer Crime • Computers can contain information that helps law enforcement determine: – Chain of events leading to a crime – Evidence that can lead to a conviction • Law enforcement officers should follow proper procedure when acquiring the evidence – Digital evidence can be easily altered by an overeager investigator 70
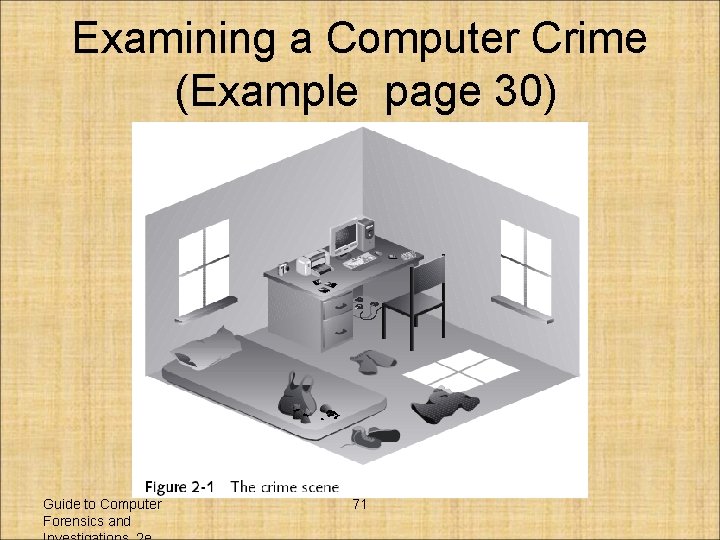
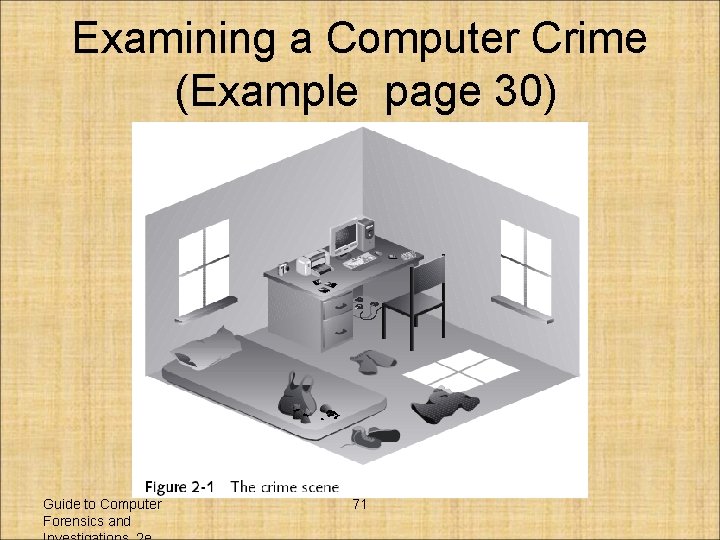
Examining a Computer Crime (Example page 30) Guide to Computer Forensics and 71
Examining a Company Policy Violation • Companies often establish policies for computer use by employees. • Employees misusing resources can cost companies millions of dollars • Misuse includes: – Surfing the Internet – Sending personal e-mails – Using company computers for personal tasks 72
Taking a Systematic Approach • Steps for problem solving: – Make an initial assessment about the type of case you are investigating – Determine a preliminary design or approach to the case – Create a detailed design – Determine the resources you need – Obtain and copy an evidence disk drive Guide to Computer Forensics and 73
Taking a Systematic Approach (continued) • Steps for problem solving (continued): – Identify the risks – Mitigate or minimize the risks – Test the design – Analyze and recover the digital evidence – Investigate the data you recovered – Complete the case report – Critique the case Guide to Computer Forensics and 74
Assessing the Case • Systematically outline the case details: – Situation – Nature of the case – Specifics about the case – Type of evidence – OS – Known disk format – Location of evidence Guide to Computer Forensics and 75
Assessing the Case (continued) • Based on case details, you can determine the case requirements: – Type of evidence – Computer forensics tools – Special OSs Guide to Computer Forensics and 76
Planning your Investigation • A basic investigation plan should include the following activities: – Acquire the evidence – Complete an evidence form and establish a chain of custody – Transport evidence to a computer forensics lab – Secure evidence in an approved secure container Guide to Computer Forensics and 77
Planning your Investigation (continued) • A basic investigation plan (continued): – Prepare a forensics workstation – Obtain the evidence from the secure container – Make a forensic copy of the evidence – Return the evidence to the secure container – Process the copied evidence with computer forensics tools Guide to Computer Forensics and 78
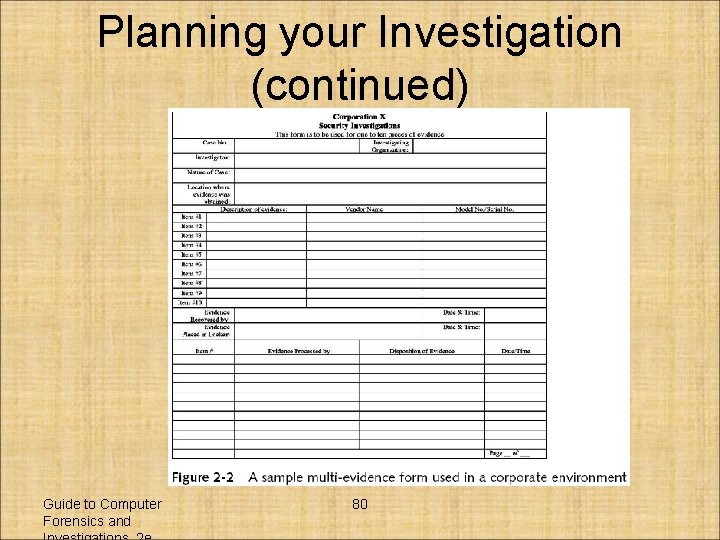
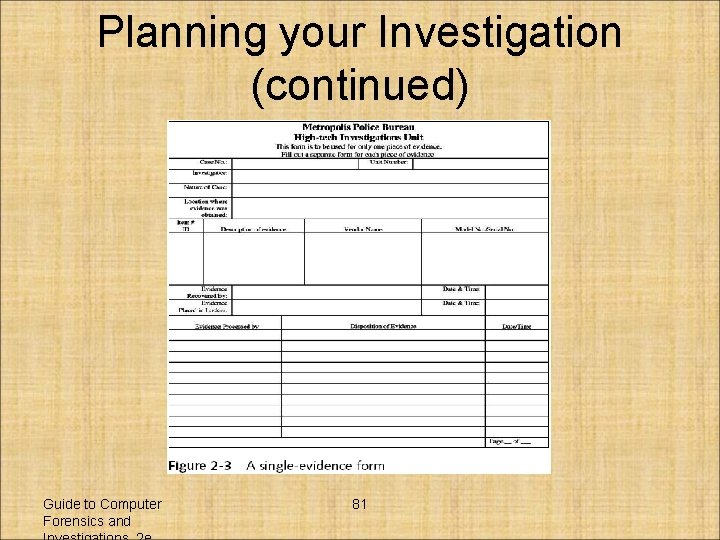
Planning your Investigation (continued) • An evidence custody form helps you document what has been done with the original evidence and its forensics copies • There are two types: – Single-evidence form – Multi-evidence form Guide to Computer Forensics and 79
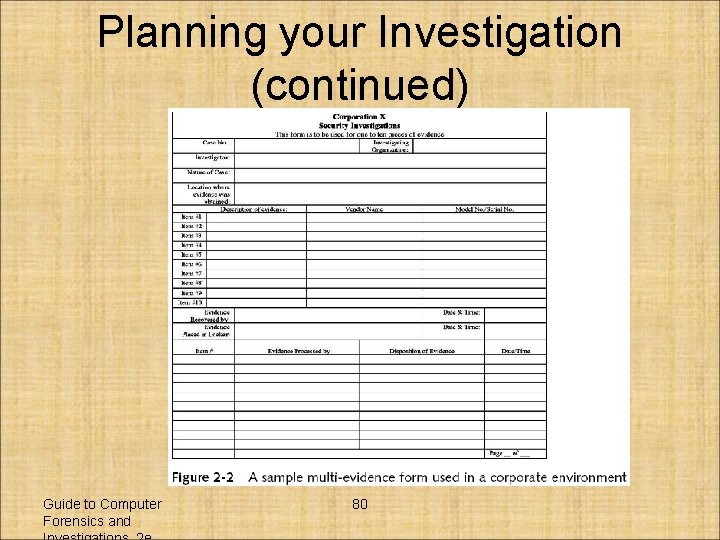
Planning your Investigation (continued) Guide to Computer Forensics and 80
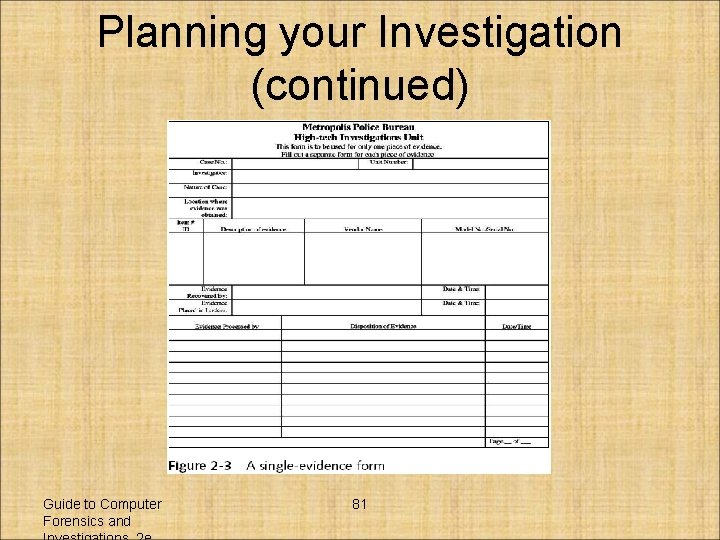
Planning your Investigation (continued) Guide to Computer Forensics and 81