Computer Forensics CS 407 MW 10 30 12
- Slides: 37
Computer Forensics CS 407 MW 10: 30 – 12: 30 Texts: File System Forensic Analysis, Brian Carrier Windows Forensics Analysis, 2 nd editiion, Harlan Carvey Supplementary Texts: Digital Evidence and Computer Crime, Eoghan Casey Guide to Computer Forensics and Investigations, Nelson, et al Web site: ackler. csrl. sou. edu/
More Texts: Electronic Crime Scene Investigation: A Guide for First Responders, Second Edition, http: //www. ncjrs. gov/pdffiles 1/nij/187736. pdf Forensic Examination of Digital Evidence: A Guide for Law Enforcement Series, http: //www. ncjrs. gov/pdffiles 1/nij/199408. pdf Best Practices for Seizing Electronic Evidence V 2 www. fletc. gov/training/programs/legal-division/downloads-articles-and faqs/downloads/other/bestpractices. pdf/view
Advanced Computer Forensics A New Realm Responsiblities Ethical Legal Technical Three Course Sequence 1. File system Forensics 2. Network Forensics 3. Memory Forensics ACE Certification Preparation for CCE Certification, ISFCE
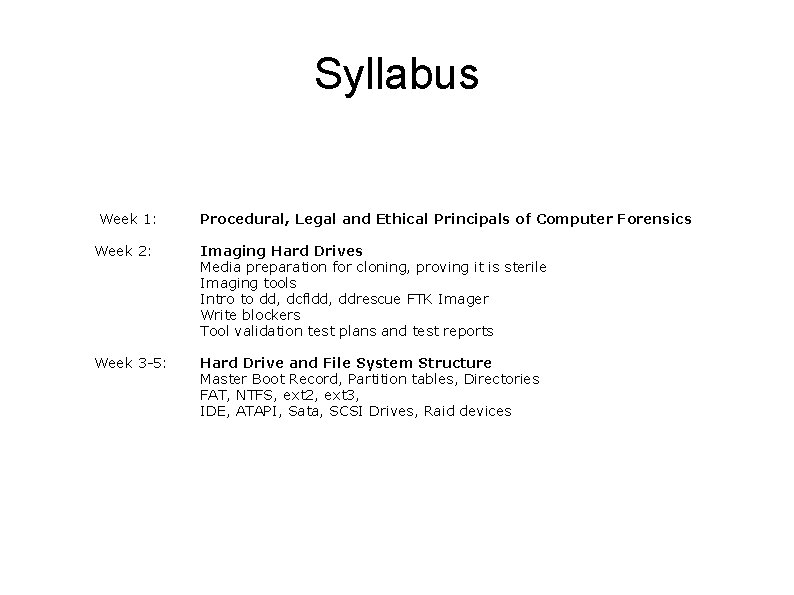
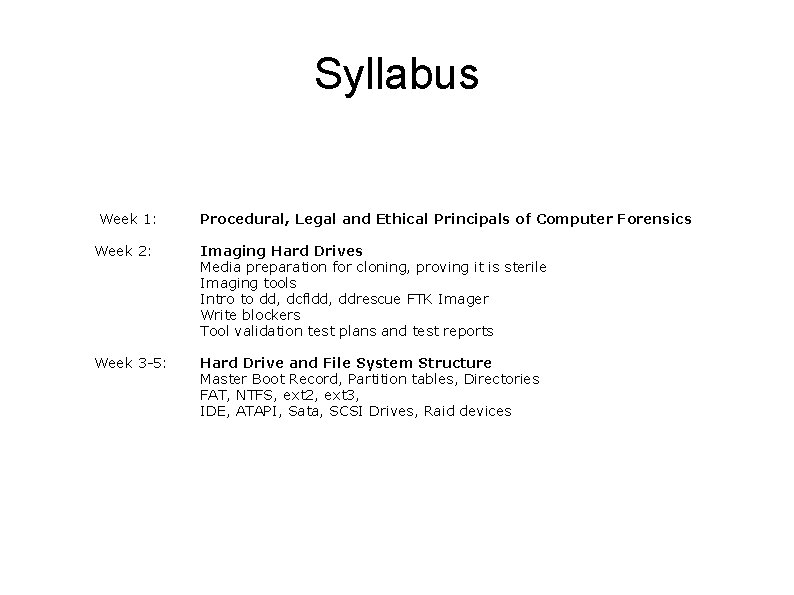
Syllabus Week 1: Week 2: Week 3 -5: Procedural, Legal and Ethical Principals of Computer Forensics Imaging Hard Drives Media preparation for cloning, proving it is sterile Imaging tools Intro to dd, dcfldd, ddrescue FTK Imager Write blockers Tool validation test plans and test reports Hard Drive and File System Structure Master Boot Record, Partition tables, Directories FAT, NTFS, ext 2, ext 3, IDE, ATAPI, Sata, SCSI Drives, Raid devices
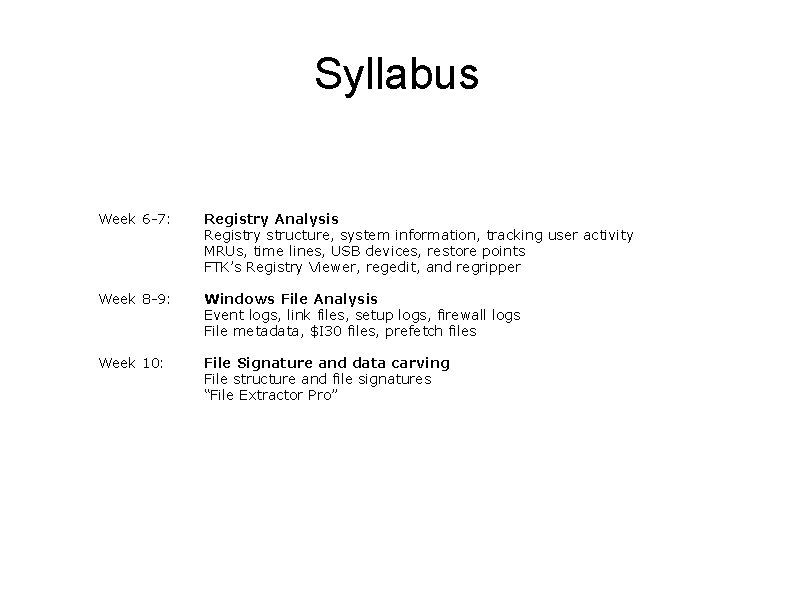
Syllabus Week 6 -7: Week 8 -9: Week 10: Registry Analysis Registry structure, system information, tracking user activity MRUs, time lines, USB devices, restore points FTK’s Registry Viewer, regedit, and regripper Windows File Analysis Event logs, link files, setup logs, firewall logs File metadata, $I 30 files, prefetch files File Signature and data carving File structure and file signatures “File Extractor Pro”
Computer Forensics As in all endeavors: “Blame always falls some where. ” Rule: “Let it not be in your lap. ”
Computer Forensics Discovery and recovery of digital evidence Usually post facto Sometimes real time Types of forensic investigations Liturgical Going to court Crimes, etc. Non-Liturgical Administrative adjudication Industry
Purpose Prove or disprove criminal activity Prove or disprove policy violation Prove or disprove malicious behavior to or by the computer/user If the evidence is there, the case is yours to lose with very little effort.
Today Ethical issues Privacy issues Evidence Association of suspect with evidence Chain of custody Seizing electronic evidence
Ethical issues Evidence All of it Emphasis on exculpatory Respect for suspects privacy and rights Beware of collateral damage Proper use of dual use technology All tools can be used to commit crime All procedures can be used to hide crime
Business Issues No interruption of business Know the policies of the business Sensitive to the business costs during an investigation
Privacy Issues Rights of the suspect Liabilities of the investigator Public versus private storage of information Expectation of privacy
Search and Seize With and without a warrant Not for the computer forensics expert Residences Private Sector-workplaces Public Sector-workplaces “In plain sight” issues
Subpoenas Person to testify Present to the court computers, records, documents Authentication issues Record alteration Usually for computer based business records Often a snapshot of ongoing record keeping
Search Warrants Show up and take away Court approved with probable cause Good for computers Records, etc. Sneak & peek Compelling reason Notify within 7 – 45 days For stored communications and records Caution: third party information
Electronic Storage Any temporary or intermediate storage of a wire or electronic communication incidental to the electronic transmission of the communications And backup for the restoration of the electronic communication service (not for future use)
Wire Communications Telephone communications mostly Specifically the communication must contain the human voice At any point from the point of origin to the point of reception Must be on a wire somewhere Wire communication in “temporary or incidental” electronic storage is covered by Title III Causes confusion Unopened voice mail is covered Opened voice mail is not
Electronic Communications Internet communications mostly Signs, signals, writing, images, sounds, data, or intelligence transmitted electronically BUT does not include Wire or oral communications Tone-only paging device Cannot be characterized as containing the human voice
Communications Intercept Acquisition contemporaneous with transmission Content Addressing information
Electronic surveillance Pen/Trap Statue Collection of addressing information for wire and electronic communications Title III of the Omnibus Crime Control and Safe Streets Act of 1968 Collection of content of wire and electronic communications
Pen/Trap Statue Collection of addressing information Phone is different from Internet Application for a Pen/Trap order Who wants it Where do they work State their belief the info is relevant to an ongoing criminal investigation Application is easy Violation is severe
Title III - 1968 Assumption: any interception of private communication between two parties is illegal. Title III order is required when Intercepted communication is protected under Title III The proposed surveillance is an interception oc communications Is there a statutory exception
Title III Wire Taps Court approved upon probable cause Feds need Do. J approval Good for 30 days Can apply for non-notification Usually used for “wire communications” Very dicey area between “wire communication” and “electronic communication”
Title III - 2001 Voice intercept authorized in computer hacking investigations Electronic storage of wire communications is now covered by same rules as stored electronic communications (only need a search warrant) Session times, addresses only requires a subpoena not a Pen/Trap order Warrants for e-mail are now nationwide
Title III - Today NSA surveillance puts all in disarray
NSLs Specifically enabled in the USA PATRIOT Act Requires FBI supervisor approval No judicial oversight Disclosure is forbidden
Evidence Demonstrative Documentary Testimonial Circumstantial Hearsay
Demonstrative Evidence Physical evidence that one can see and inspect Does not play a direct part in the incident Of probative value Sometimes referred to as real evidence
Documentary Evidence supplied by a writing or other document Must be authenticated to be admissible
Testimonial Evidence A person’s testimony Offered to prove the truth of the matter
Hearsay Evidence “Hearsay is a statement offered in evidence to prove the truth of the matter asserted” Federal Rules of Evidence, § 801 There are many exceptions to hearsay evidence. Most forensic evidence must be shown to be excepted from hearsay
Computer Evidence Two broad classes Computer generated records Computer stored records Computer data contains potential hearsay evidence To be admissible, a hearsay exception must be established Unless it can be shown that the data are reliable, trustworthy, material and authentic.
Computer Generated Data Computer generated records Data untouched by human hands. Phone logs ISP logs syslogs The data contains no hearsay evidence To be admissible, it must be shown that the data are reliable, trustworthy, material and authentic. Reliability of the computer programs
Computer Stored Data Computer stored records Data potentially contains hearsay Photo graphs Results of Excel spreadsheets A printout of an e-mail is considered to be an original. However, to connect the e-mail to the defendant one must tie the computer system to the defendant. The ISP records of the e-mail server are business records and only require testimony of the ISP.
Computer Stored Business Records Business records Data generated in the usual course of business Done regularly A satisfies a hearsay exception.
Evidence Admissible Reliable the real thing, not a replica Complete has not been tainted (changed) since acquisition Authentic must be legally obtained and relevant includes any exculpatory evidence Believable lawyers, judge & jury can understand it
Chain of Custody The evidence must be accounted for at all times after seizure Very prone to violation with digital evidence Can’t take it home to work on! Sometimes it is hard to say where the evidence is. Fortunately the courts accept hash codes Not for long MD 5 collisions in less than a minute