Computer and Network Security Rabie A Ramadan Lecture
Computer and Network Security Rabie A. Ramadan Lecture 5
More Math …. 2
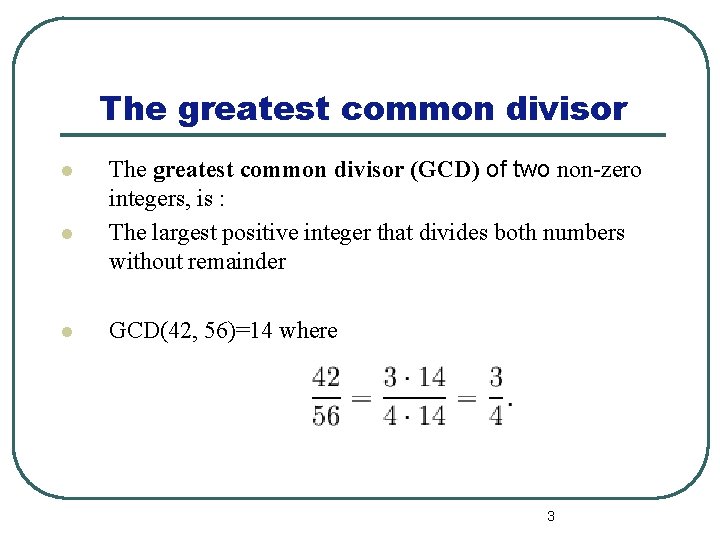
The greatest common divisor l l l The greatest common divisor (GCD) of two non-zero integers, is : The largest positive integer that divides both numbers without remainder GCD(42, 56)=14 where 3
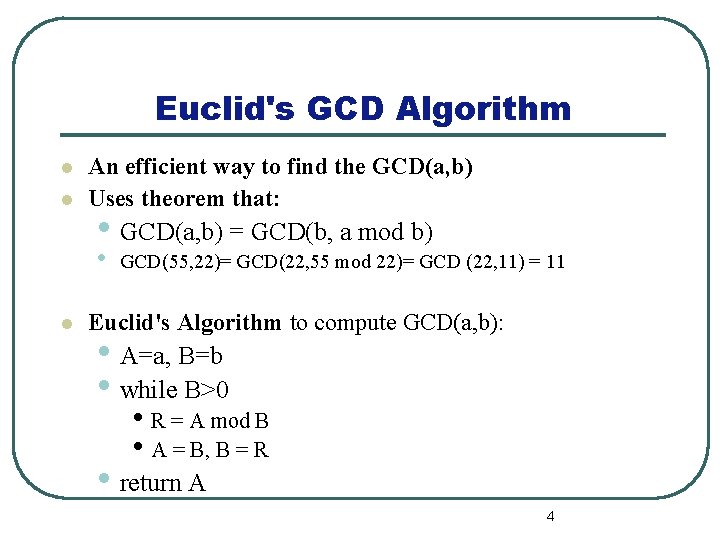
Euclid's GCD Algorithm l l An efficient way to find the GCD(a, b) Uses theorem that: • GCD(a, b) = GCD(b, a mod b) • l GCD(55, 22)= GCD(22, 55 mod 22)= GCD (22, 11) = 11 Euclid's Algorithm to compute GCD(a, b): • A=a, B=b • while B>0 • R = A mod B • A = B, B = R • return A 4
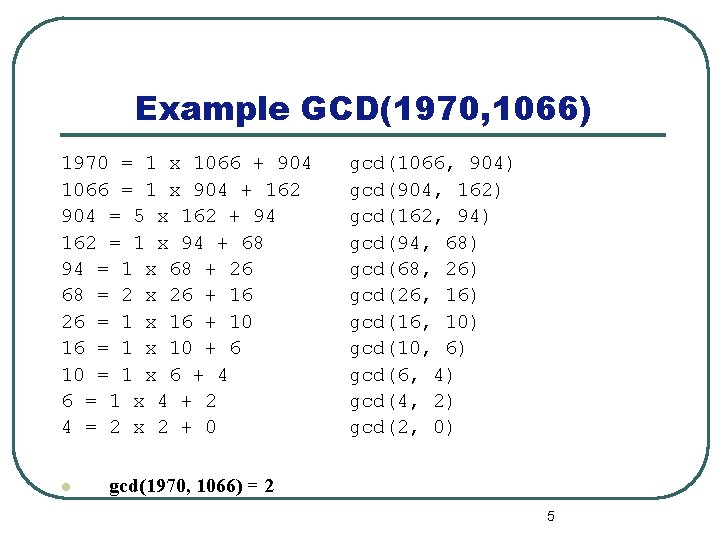
Example GCD(1970, 1066) 1970 = 1 x 1066 + 904 1066 = 1 x 904 + 162 904 = 5 x 162 + 94 162 = 1 x 94 + 68 94 = 1 x 68 + 26 68 = 2 x 26 + 16 26 = 1 x 16 + 10 16 = 1 x 10 + 6 10 = 1 x 6 + 4 6 = 1 x 4 + 2 4 = 2 x 2 + 0 l gcd(1066, 904) gcd(904, 162) gcd(162, 94) gcd(94, 68) gcd(68, 26) gcd(26, 16) gcd(16, 10) gcd(10, 6) gcd(6, 4) gcd(4, 2) gcd(2, 0) gcd(1970, 1066) = 2 5
Polynomial Arithmetic l Can compute using polynomials l Several alternatives available • ordinary polynomial arithmetic • poly arithmetic with coords mod p
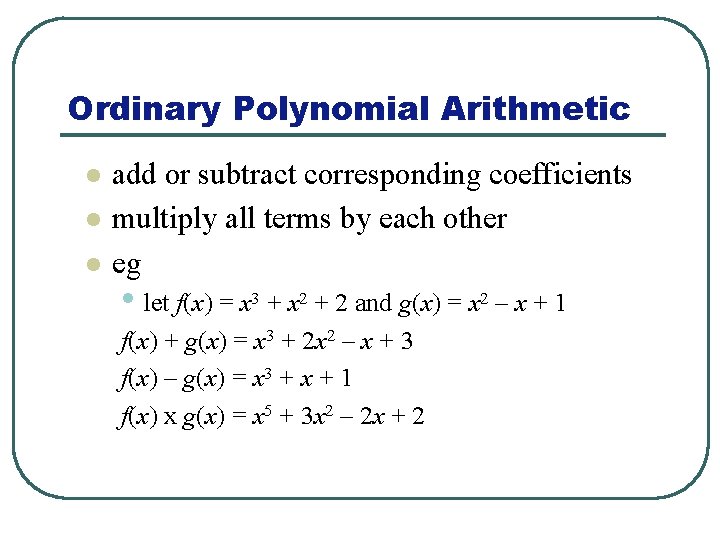
Ordinary Polynomial Arithmetic l l l add or subtract corresponding coefficients multiply all terms by each other eg • let f(x) = x 3 + x 2 + 2 and g(x) = x 2 – x + 1 f(x) + g(x) = x 3 + 2 x 2 – x + 3 f(x) – g(x) = x 3 + x + 1 f(x) x g(x) = x 5 + 3 x 2 – 2 x + 2
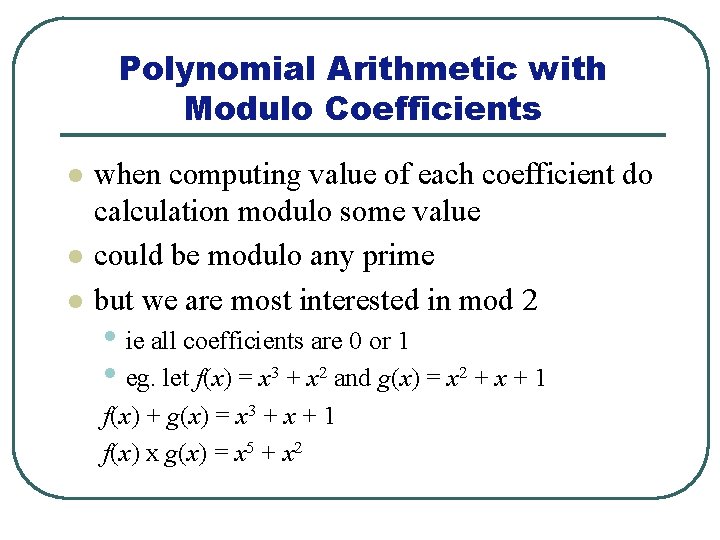
Polynomial Arithmetic with Modulo Coefficients l l l when computing value of each coefficient do calculation modulo some value could be modulo any prime but we are most interested in mod 2 • ie all coefficients are 0 or 1 • eg. let f(x) = x 3 + x 2 and g(x) = x 2 + x + 1 f(x) + g(x) = x 3 + x + 1 f(x) x g(x) = x 5 + x 2
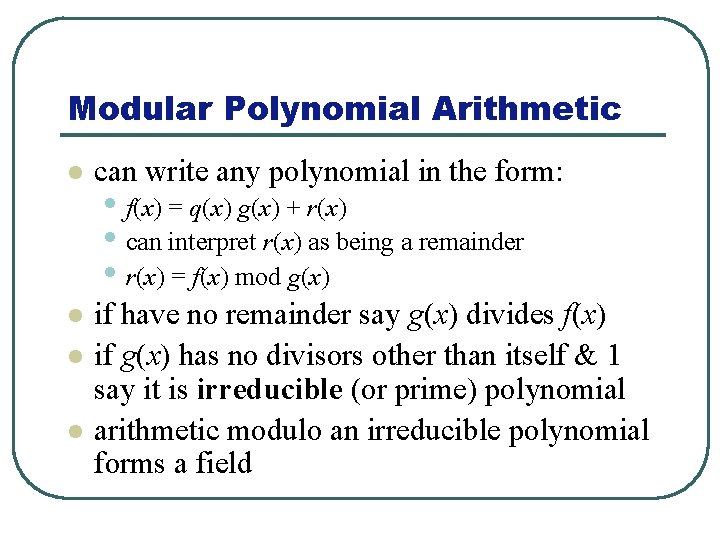
Modular Polynomial Arithmetic l can write any polynomial in the form: l if have no remainder say g(x) divides f(x) if g(x) has no divisors other than itself & 1 say it is irreducible (or prime) polynomial arithmetic modulo an irreducible polynomial forms a field l l • f(x) = q(x) g(x) + r(x) • can interpret r(x) as being a remainder • r(x) = f(x) mod g(x)
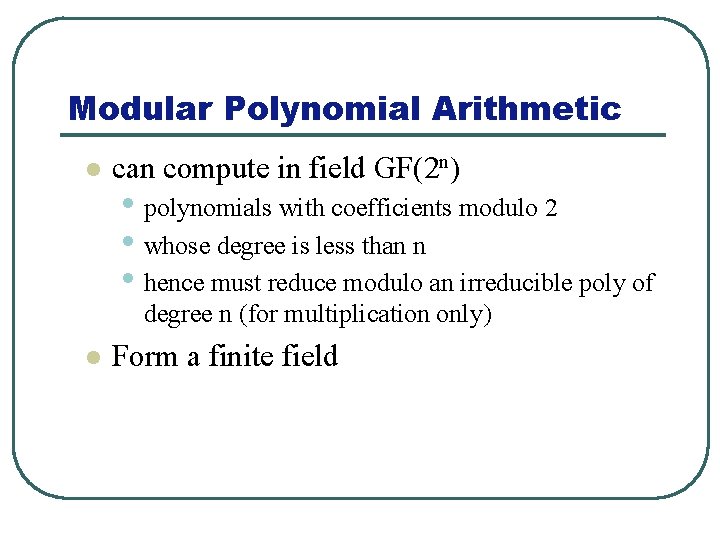
Modular Polynomial Arithmetic l can compute in field GF(2 n) • polynomials with coefficients modulo 2 • whose degree is less than n • hence must reduce modulo an irreducible poly of degree n (for multiplication only) l Form a finite field
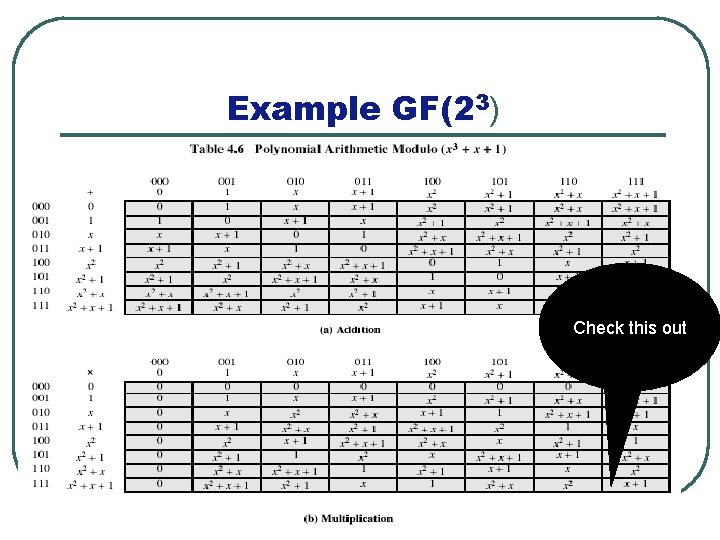
Example GF(23) Check this out
Group Activity Find the results of (x 5+x 2+x) * (x 7+x 4+x 3+x 2+x ) in GF(28) with irreducible polynomial x 8+x 4+x 3+x+1 l
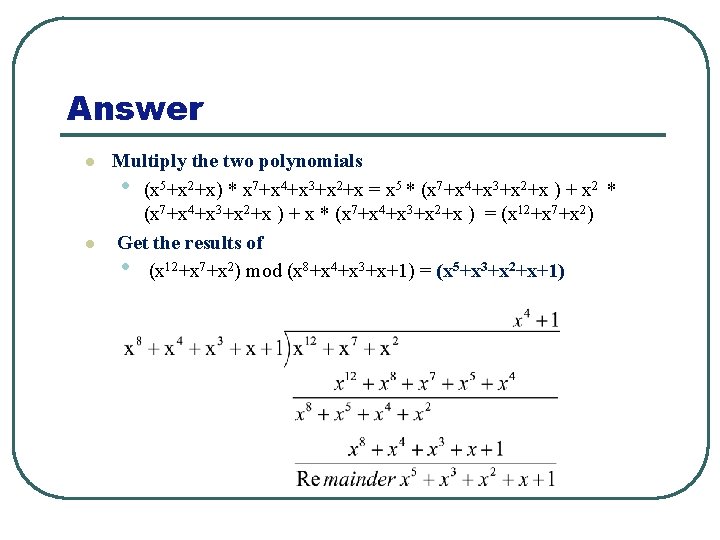
Answer l l Multiply the two polynomials • (x 5+x 2+x) * x 7+x 4+x 3+x 2+x = x 5 * (x 7+x 4+x 3+x 2+x ) + x 2 * (x 7+x 4+x 3+x 2+x ) + x * (x 7+x 4+x 3+x 2+x ) = (x 12+x 7+x 2) Get the results of • (x 12+x 7+x 2) mod (x 8+x 4+x 3+x+1) = (x 5+x 3+x 2+x+1)
Advanced Encryption Standard (AES) 14
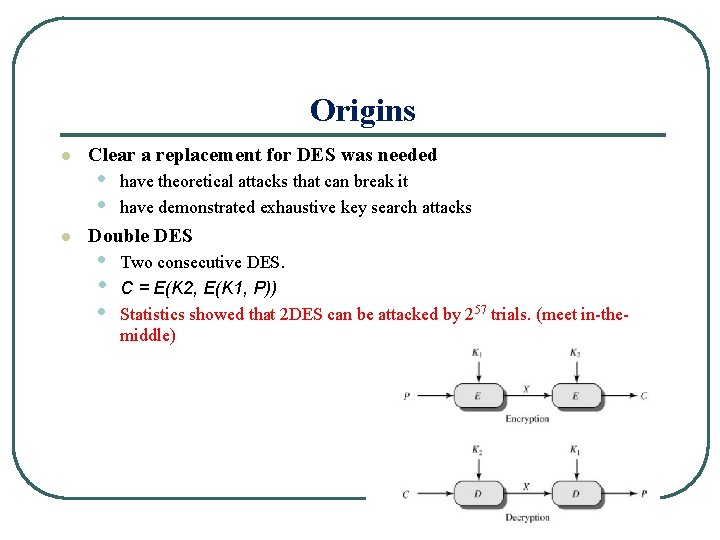
Origins l l Clear a replacement for DES was needed • • have theoretical attacks that can break it have demonstrated exhaustive key search attacks Double DES • • • Two consecutive DES. C = E(K 2, E(K 1, P)) Statistics showed that 2 DES can be attacked by 257 trials. (meet in-themiddle) 15
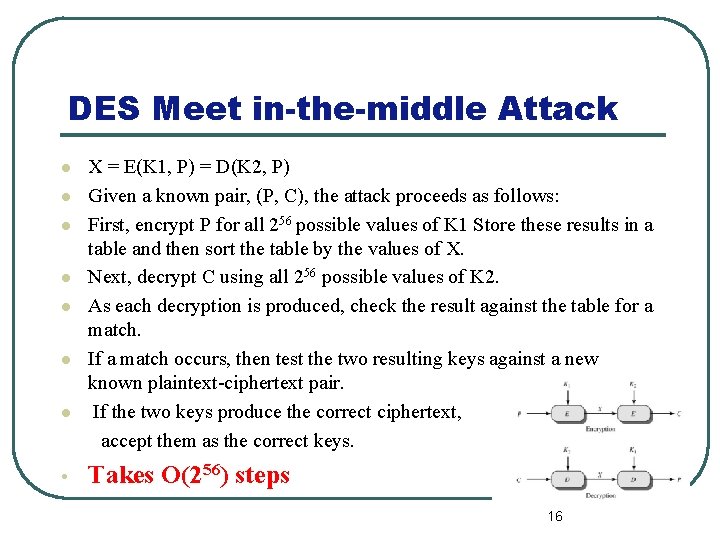
DES Meet in-the-middle Attack l l l l • X = E(K 1, P) = D(K 2, P) Given a known pair, (P, C), the attack proceeds as follows: First, encrypt P for all 256 possible values of K 1 Store these results in a table and then sort the table by the values of X. Next, decrypt C using all 256 possible values of K 2. As each decryption is produced, check the result against the table for a match. If a match occurs, then test the two resulting keys against a new known plaintext-ciphertext pair. If the two keys produce the correct ciphertext, accept them as the correct keys. Takes O(256) steps 16
Triple-DES with Two-Keys l Hence must use 3 encryptions l But can use 2 keys with E-D-E sequence l Standardized in ISO 8732 No current known practical attacks l • would seem to need 3 distinct keys • C = EK 1[DK 2[EK 1[P]]] • encrypt & decrypt equivalent in security • if K 1=K 2 then can work with single DES
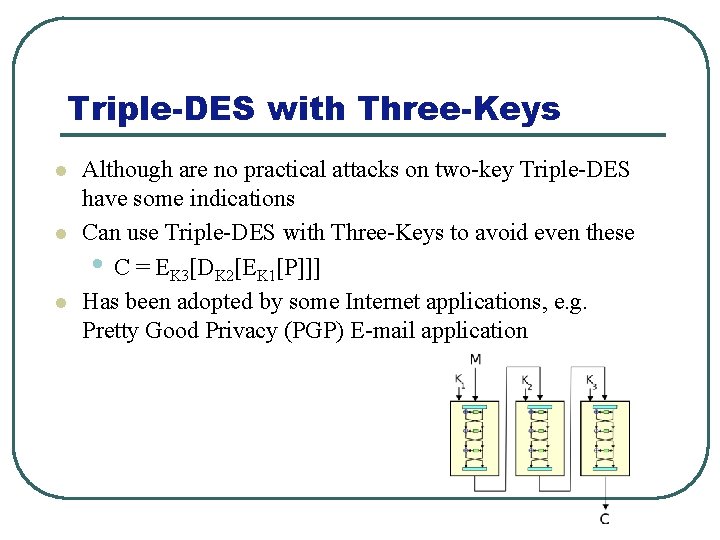
Triple-DES with Three-Keys l l l Although are no practical attacks on two-key Triple-DES have some indications Can use Triple-DES with Three-Keys to avoid even these • C = EK 3[DK 2[EK 1[P]]] Has been adopted by some Internet applications, e. g. Pretty Good Privacy (PGP) E-mail application
Viruses, Worms, Zombies, and others 19
What is Computer Security? 20
What is Computer Security? l Computer Security is the protection of computing systems and the data that they store or access 21
Why is Computer Security Important? l Computer Security allows the University to carry out its mission by: • Enabling people to carry out their jobs, education, and research. • Supporting critical business processes • Protecting personal and sensitive information 22
Why do I need to learn about Computer Security? Isn’t this just an IT Problem? 23
l Good Security Standards follow the “ 90 / 10” Rule: • 10% of security safeguards are technical • 90% of security safeguards rely on the computer user (“YOU”) to adhere to good computing practices 24
What Does This Mean for Me? l This means that everyone who uses a computer or mobile device needs to understand how to keep their computer, device and data secure. • Information Technology Security is everyone’s responsibility 25
What’s at Stake? Kinds of damage caused by insecurity • Nuisance: spam, … • Data erased, corrupted, or held hostage • Valuable information stolen • (credit card numbers, trade secrets, etc. ) Services made unavailable (email and web site outages, lost business) 26
Breaking into a Computer 27
Breaking into a Computer What? • Run unauthorized software How? • Trick the user into running bad software • (“social engineering”) Exploit software bugs to run bad software without the user’s help 28
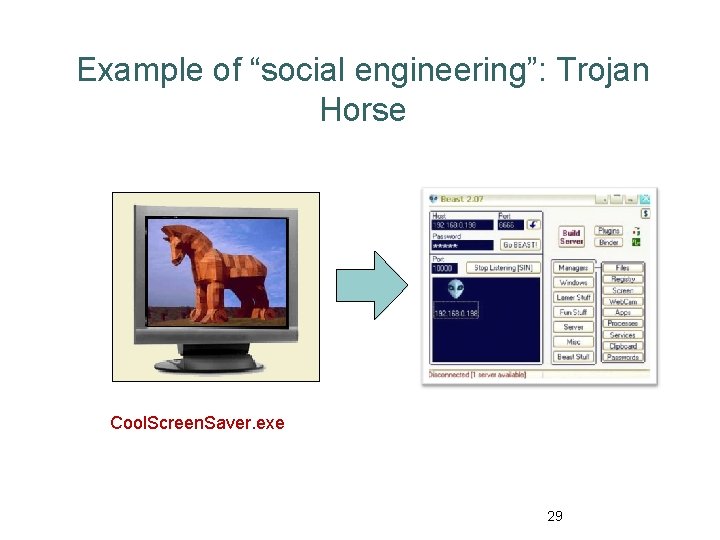
Example of “social engineering”: Trojan Horse Cool. Screen. Saver. exe 29
Viruses and Worms l Automated ways of breaking in; Use self-replicating programs l (Recall self-replicating programs: Print the following line twice, the second time in quotes. “Print the following line twice, the second time in quotes. ” ) 30
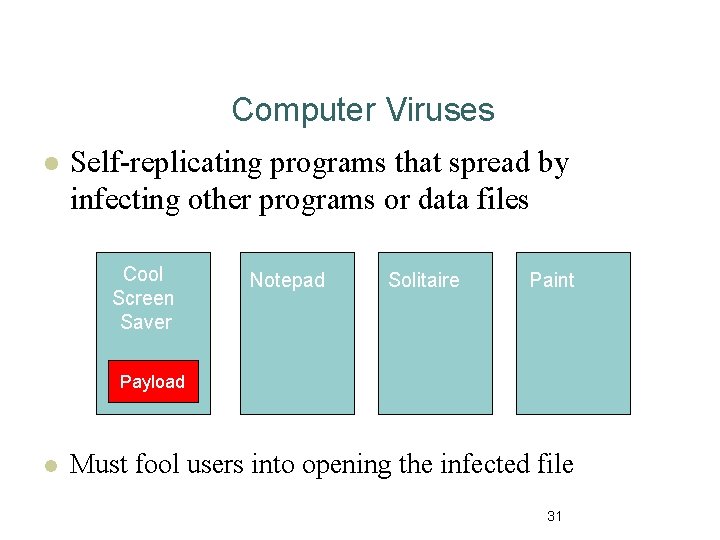
Computer Viruses l Self-replicating programs that spread by infecting other programs or data files Cool Screen Saver Notepad Solitaire Paint Payload l Must fool users into opening the infected file 31
Email Viruses l l Infected program, screen saver, or Word document launches virus when opened Use social engineering to entice you to open the virus attachment Self-spreading: after you open it, automatically emails copies to everyone in your address book Other forms of social engineering: downloadable software/games, P 2 P software, etc. 32
The Melissa Virus (1999) l l l Social engineering: Email says attachment contains porn site passwords Self-spreading: Random 50 people from address book Traffic forced shutdown of many email servers $80 million damage 20 months and $5000 fine David L. Smith Aberdeen, NJ 33
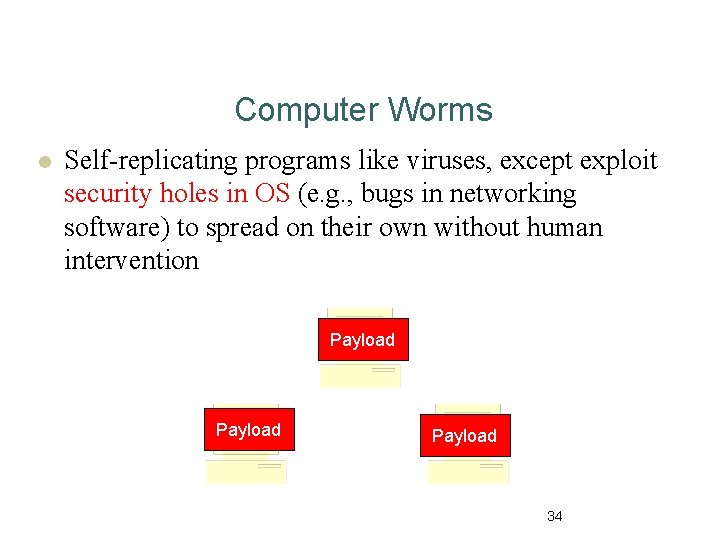
Computer Worms l Self-replicating programs like viruses, except exploit security holes in OS (e. g. , bugs in networking software) to spread on their own without human intervention Payload 34
Robert Tappan Morris First Internet worm l Created by student at Cornell l Exploited holes in email servers, other programs l Infected ~10% of the net l Spawned multiple copies, crippling infected servers l Sentenced to 3 years probation, $10, 000 fine, 400 hours community service l Robert Tappan Morris 35
![“Can we just develop software to detect a virus/worm? ” [Adleman’ 88] This task “Can we just develop software to detect a virus/worm? ” [Adleman’ 88] This task](http://slidetodoc.com/presentation_image_h2/1ef4f6d004e6829757ed5ca6ea82b944/image-36.jpg)
“Can we just develop software to detect a virus/worm? ” [Adleman’ 88] This task is undecidable. (so no software can work with 100% guarantee) Current methods: (i) Look for snippets of known virus programs on hard drive (ii) maintain log of activities such as network requests, read/writes to hard-drive and look for “suspicious” trends (iii) look for changes to OS code. No real guarantee 36
Spyware/Adware Hidden but not self-replicating l Tracks web activity for marketing, shows popup ads, etc. Usually written by businesses: Legal gray area l l 37
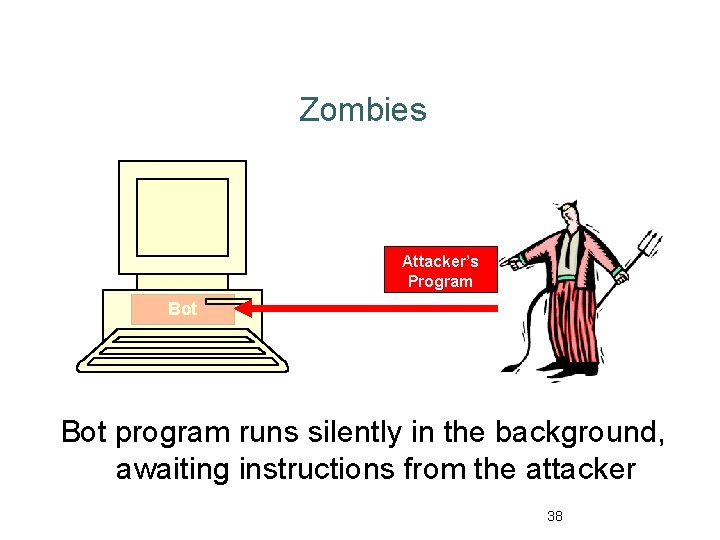
Zombies Attacker’s Program Bot program runs silently in the background, awaiting instructions from the attacker 38
Can we stop computer crime? Probably not! l Wild West nature of the Internet l Software will always have bugs l Rapid exponential spread of attacks But we can take steps to reduce risks… 39
Protecting Your Computer Six easy things you can do… Keep your software up-to-date l Use safe programs to surf the ‘net Run anti-virus and anti-spyware regularly l Add an external firewall l Back up your data l Learn to be “street smart” online l l 40
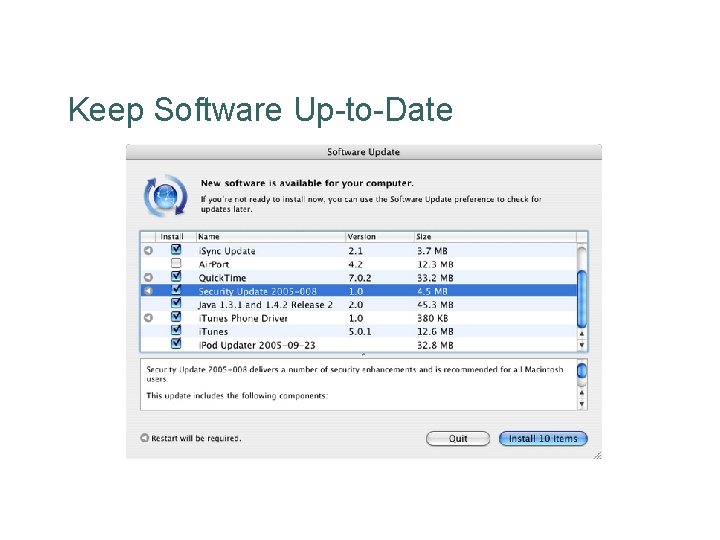
Keep Software Up-to-Date

Use Safe Software to Go Online Firefox (web browser) Thunderbird (email)
Anti-virus / Anti-spyware Scans Symantec Antivirus (Free from OIT) Spybot Search & Destroy (Free download)
Add an External Firewall Provides layered security (think: castle walls, moat) (Recent operating systems have built-in firewall features)
Back Up Your Data Tivoli Storage Manager (Free from OIT)
Learn Online “Street Smarts” l Be aware of your surroundings l Don’t accept candy from strangers • Is the web site being spoofed? • How do you know an attachment or download isn’t a virus, Trojan, or spyware? l Don’t believe everything you read • Email may contain viruses or phishing attack – remember, bad guys can forge email from your friends
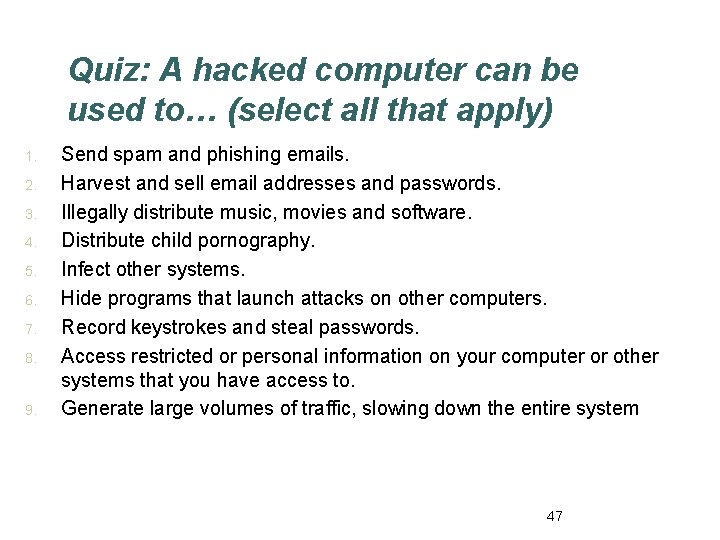
Quiz: A hacked computer can be used to… (select all that apply) 1. 2. 3. 4. 5. 6. 7. 8. 9. Send spam and phishing emails. Harvest and sell email addresses and passwords. Illegally distribute music, movies and software. Distribute child pornography. Infect other systems. Hide programs that launch attacks on other computers. Record keystrokes and steal passwords. Access restricted or personal information on your computer or other systems that you have access to. Generate large volumes of traffic, slowing down the entire system 47
Next time is an exam l Assignment 3 • Survey some of viruses and security incidents that ha been found in the last five years ? 48
Advanced Encryption Standard (AES) "It is very simple. But if you don't know what the key is it's virtually indecipherable. " —Talking to Strange Men, Ruth Rendell 49
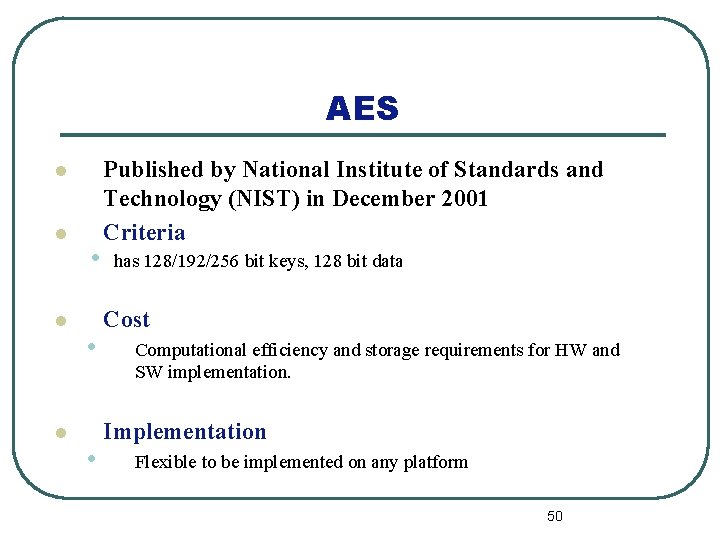
AES l l • • • Published by National Institute of Standards and Technology (NIST) in December 2001 Criteria has 128/192/256 bit keys, 128 bit data Cost Computational efficiency and storage requirements for HW and SW implementation. Implementation Flexible to be implemented on any platform 50
AES l An iterative rather than feistel cipher l Designed to be: • treats data in 4 groups of 4 bytes • operates an entire block in every round • resistant against known attacks • speed and code compactness on many CPUs • design simplicity 51
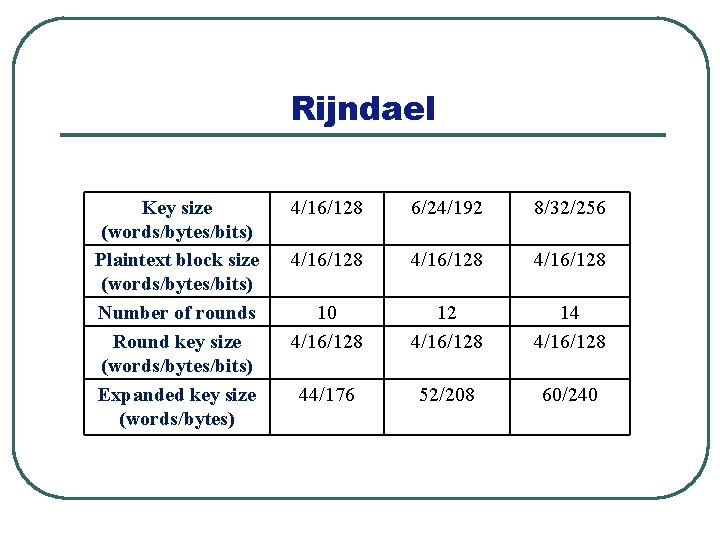
Rijndael Key size (words/bytes/bits) Plaintext block size (words/bytes/bits) Number of rounds Round key size (words/bytes/bits) Expanded key size (words/bytes) 4/16/128 6/24/192 8/32/256 4/16/128 10 4/16/128 12 4/16/128 14 4/16/128 44/176 52/208 60/240
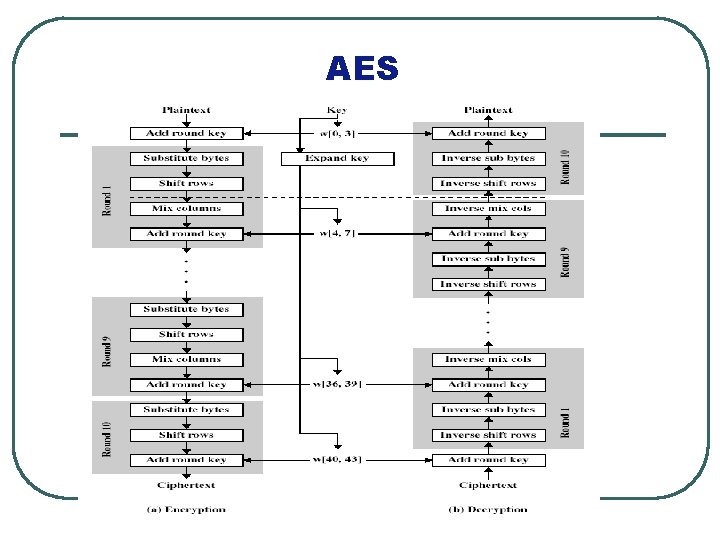
AES 53
AES Encryption Round 54
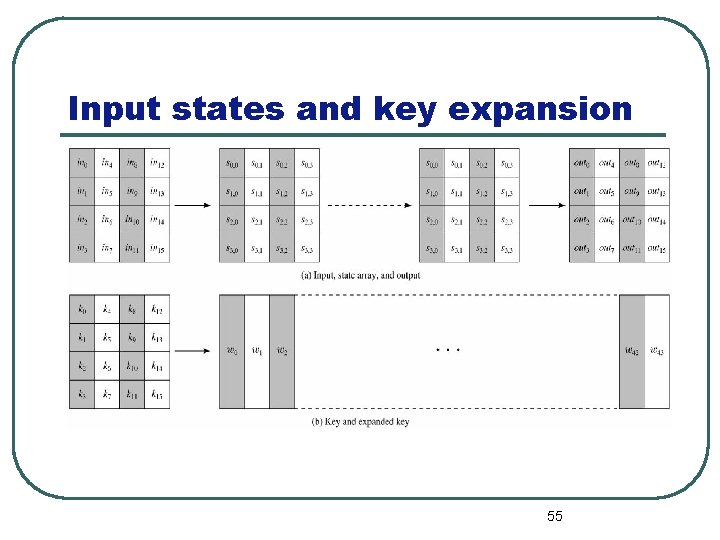
Input states and key expansion 55
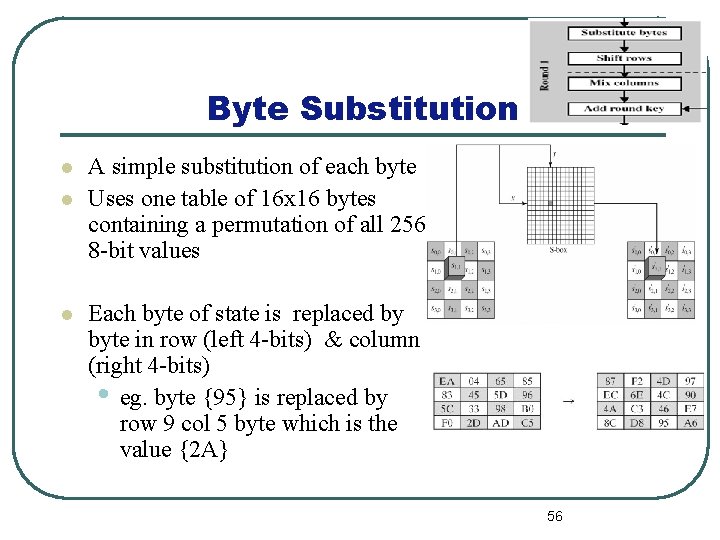
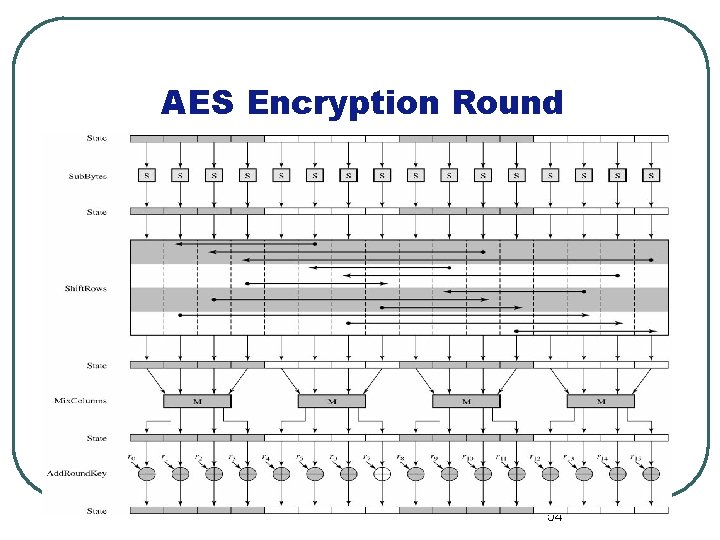
Byte Substitution l l l A simple substitution of each byte Uses one table of 16 x 16 bytes containing a permutation of all 256 8 -bit values Each byte of state is replaced by byte in row (left 4 -bits) & column (right 4 -bits) • eg. byte {95} is replaced by row 9 col 5 byte which is the value {2 A} 56
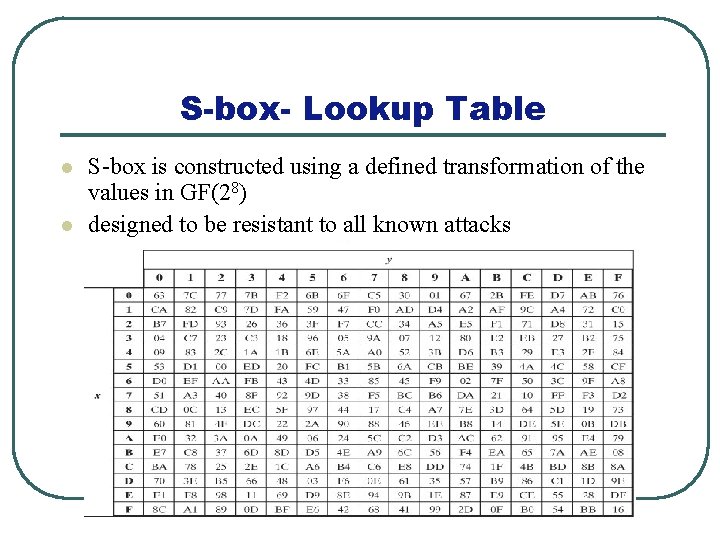
S-box- Lookup Table l l S-box is constructed using a defined transformation of the values in GF(28) designed to be resistant to all known attacks 57
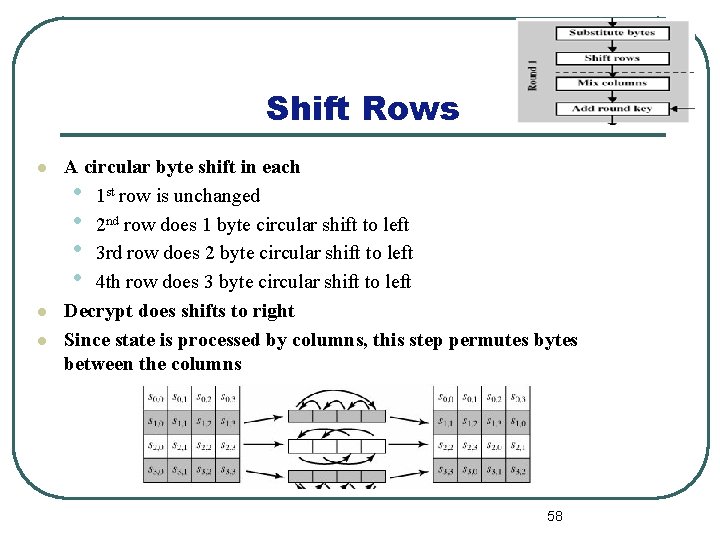
Shift Rows l l l A circular byte shift in each • 1 st row is unchanged • 2 nd row does 1 byte circular shift to left • 3 rd row does 2 byte circular shift to left • 4 th row does 3 byte circular shift to left Decrypt does shifts to right Since state is processed by columns, this step permutes bytes between the columns 58
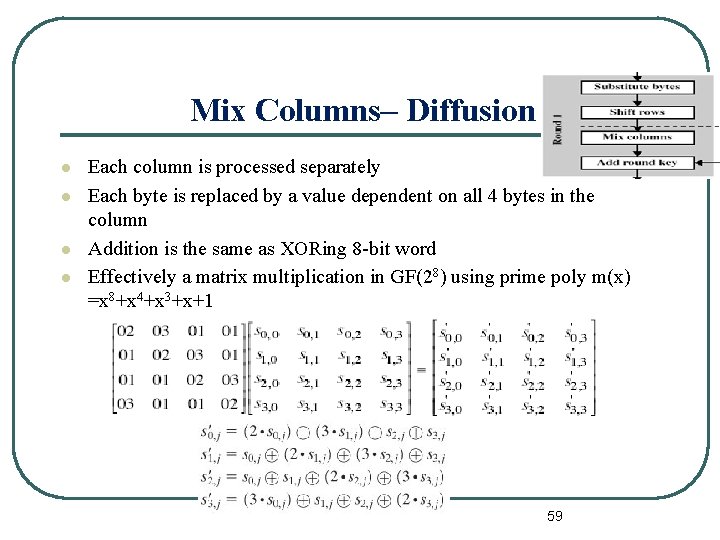
Mix Columns– Diffusion l l Each column is processed separately Each byte is replaced by a value dependent on all 4 bytes in the column Addition is the same as XORing 8 -bit word Effectively a matrix multiplication in GF(28) using prime poly m(x) =x 8+x 4+x 3+x+1 59
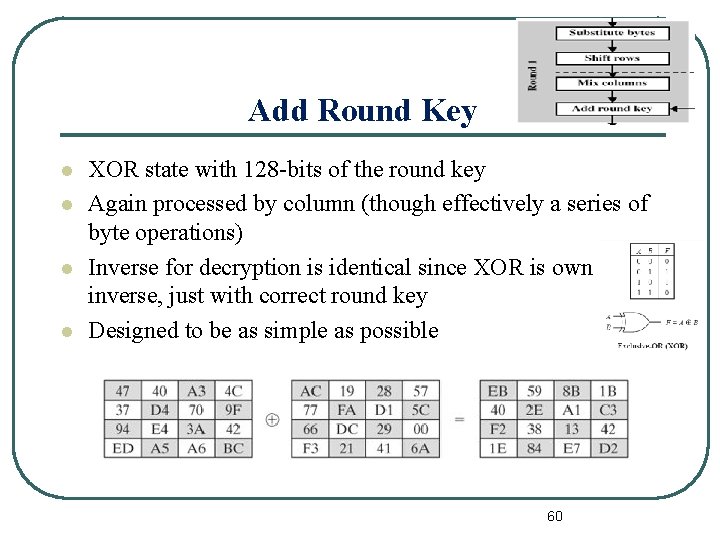
Add Round Key l l XOR state with 128 -bits of the round key Again processed by column (though effectively a series of byte operations) Inverse for decryption is identical since XOR is own inverse, just with correct round key Designed to be as simple as possible 60
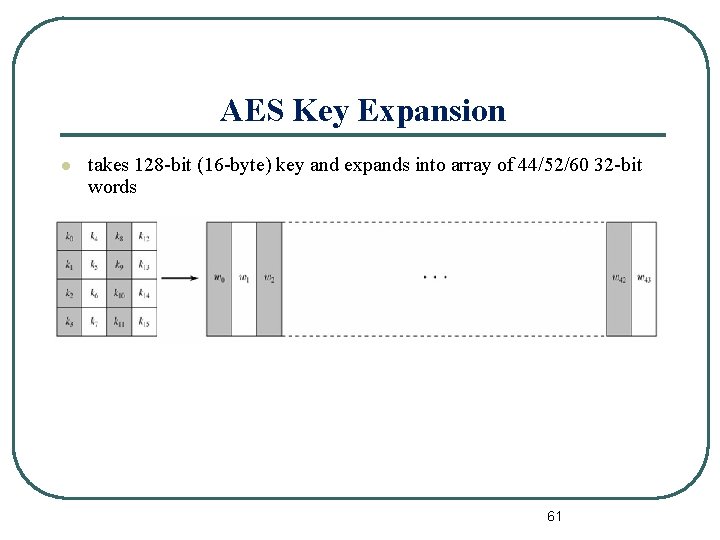
AES Key Expansion l takes 128 -bit (16 -byte) key and expands into array of 44/52/60 32 -bit words 61
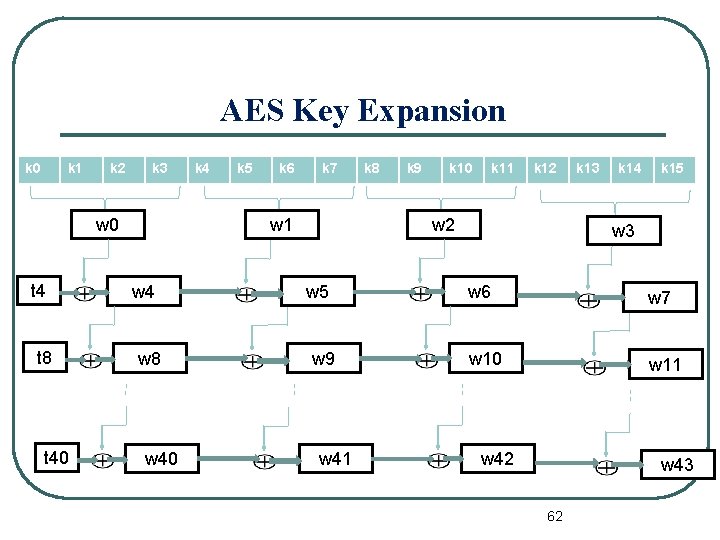
AES Key Expansion k 0 k 1 k 2 k 3 w 0 t 4 t 8 t 40 k 4 k 5 k 6 k 7 w 1 w 4 w 8 w 40 k 8 k 9 k 10 k 11 k 12 w 5 w 9 w 41 k 13 k 14 k 15 w 3 w 6 w 7 w 10 w 11 w 42 w 43 62
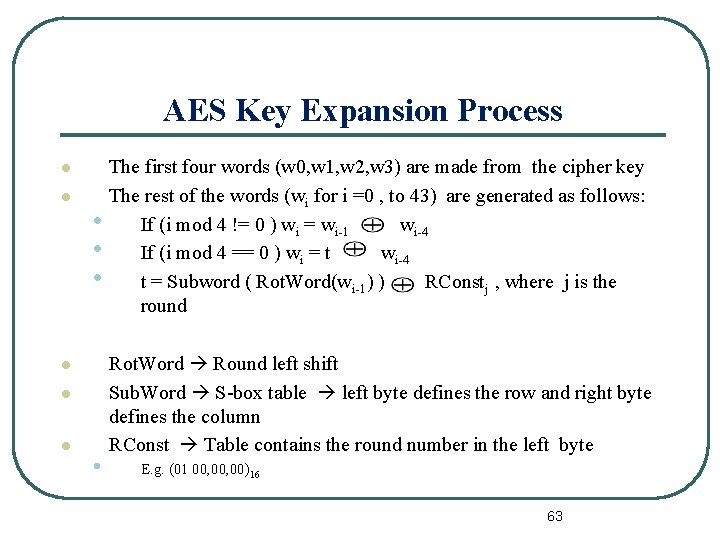
AES Key Expansion Process l l The first four words (w 0, w 1, w 2, w 3) are made from the cipher key The rest of the words (wi for i =0 , to 43) are generated as follows: • If (i mod 4 != 0 ) wi = wi-1 wi-4 • If (i mod 4 == 0 ) wi = t wi-4 • t = Subword ( Rot. Word(wi-1) ) RConstj , where j is the round l l l • Rot. Word Round left shift Sub. Word S-box table left byte defines the row and right byte defines the column RConst Table contains the round number in the left byte E. g. (01 00, 00)16 63
- Slides: 63