Computer and Information Security Chapter 1 Introduction Slides
![Fundamental threats [Mc. Gibney 04] • Information leakage – Disclosure to unauthorized parties – Fundamental threats [Mc. Gibney 04] • Information leakage – Disclosure to unauthorized parties –](https://slidetodoc.com/presentation_image_h2/62e007e18213767d1b06e1d841a04b1e/image-29.jpg)
- Slides: 48
Computer and Information Security Chapter 1 Introduction Slides by H. Johnson & S. Malladi. Modified by SJF-S'06 1
Overview • • • Security Goals The need for security OSI Security Architecture Attacks, services and mechanisms Security attacks Security services Methods of Defense A model for Internetwork Security Internet standards and RFCs
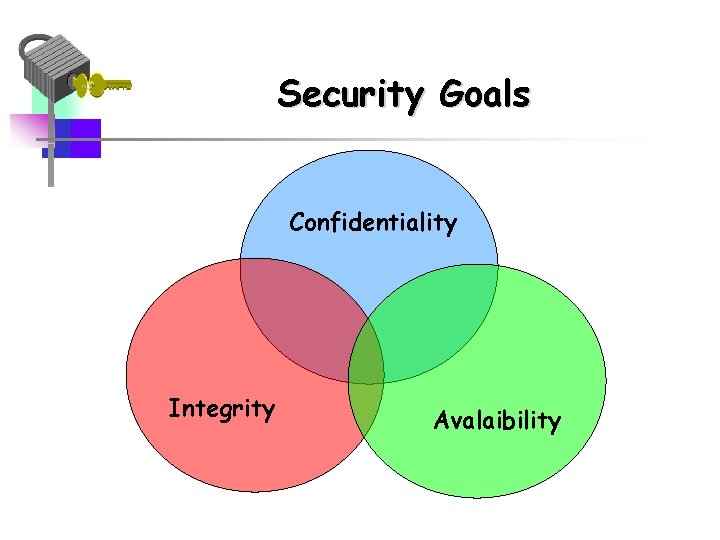
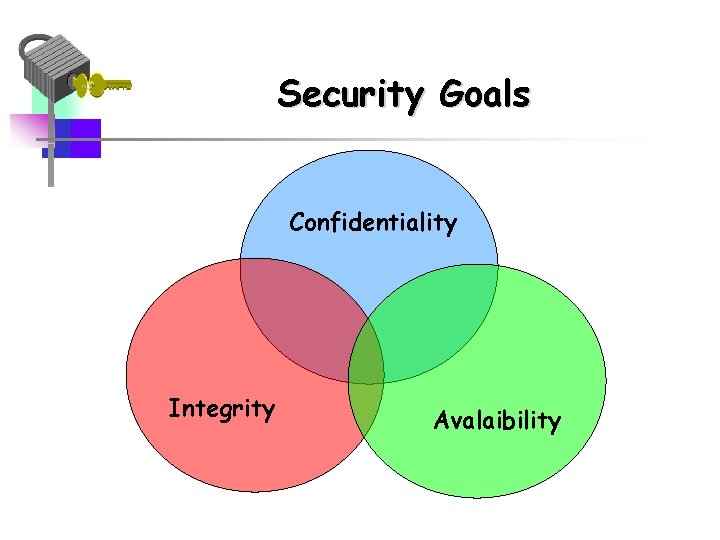
Security Goals Confidentiality Integrity Avalaibility
Security Goals • Confidentiality – Concealment of information or resources • Integrity – Trustworthiness of data or resources • Availability – Ability to use information or resources
Confidentiality • Need for keeping information secret arises from use of computers in sensitive fields such as government and industry • Access mechanisms, such as cryptography, support confidentiality – Example: encrypting income tax return
Integrity • Often requires preventing unauthorized changes • Includes data integrity (content) and origin integrity ( source of data also called authentication) • Include prevention mechanisms and detection mechanisms – Example: Newspaper prints info leaked from White House and gives wrong source • Includes both correctness and trustworthiness
Availability • Is an aspect of reliability and system design • Attempts to block availability, called denial of service attacks are difficult to detect – Example: bank with two servers –one is blocked, the other provides false information
The Need for Security • Computer Security - the collection of tools designed – to protect data and – to thwart hackers • Network security or internet security- security measures needed to protect data during their transmission
Security • Motivation: Why do we need security? • Increased reliance on Information technology with or with out the use of networks • The use of IT has changed our lives drastically. • We depend on E-mail, Internet banking, and several other governmental activities that use IT • Increased use of E-Commerce and the World wide web on the Internet as a vast repository of various kinds of information (immigration databases, flight tickets, stock markets etc. )
Security Concerns • Damage to any IT-based system or activity can result in severe disruption of services and losses • Systems connected by networks are more prone to attacks and also suffer more as a result of the attacks than stand-alone systems (Reasons? ) • Concerns such as the following are common – How do I know the party I am talking on the network is really the one I want to talk? – How can I be assured that no one else is listening and learning the data that I send over a network – Can I ever stay relaxed that no hacker can enter my network and play havoc?
Concerns continued… • Is the web site I am downloading information from a legitimate one, or a fake? • How do I ensure that the person I just did a financial transaction denies having done it tomorrow or at a later time? • I want to buy some thing online, but I don’t want to let them charge my credit card before they deliver the product to me
That is why… • . . we need security – To safeguard the confidentiality, integrity, authenticity and availability of data transmitted over insecure networks – Internet is not the only insecure network in this world – Many internal networks in organizations are prone to insider attacks – In fact, insider attacks are greater both in terms of likelihood of happening and damage caused
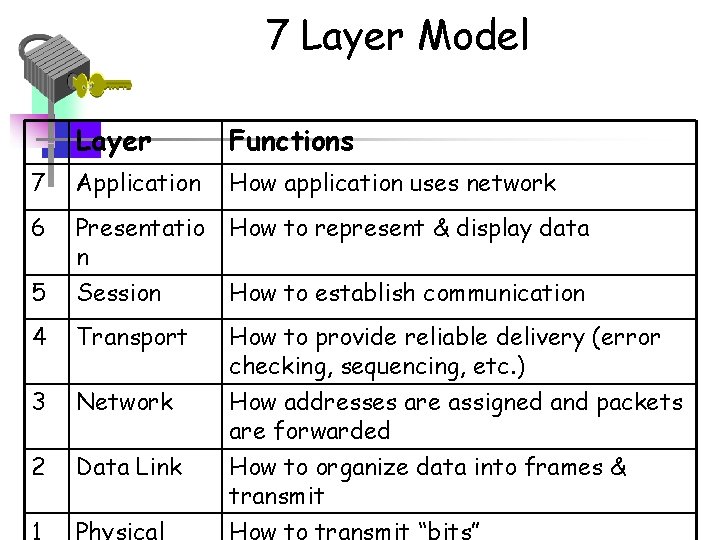
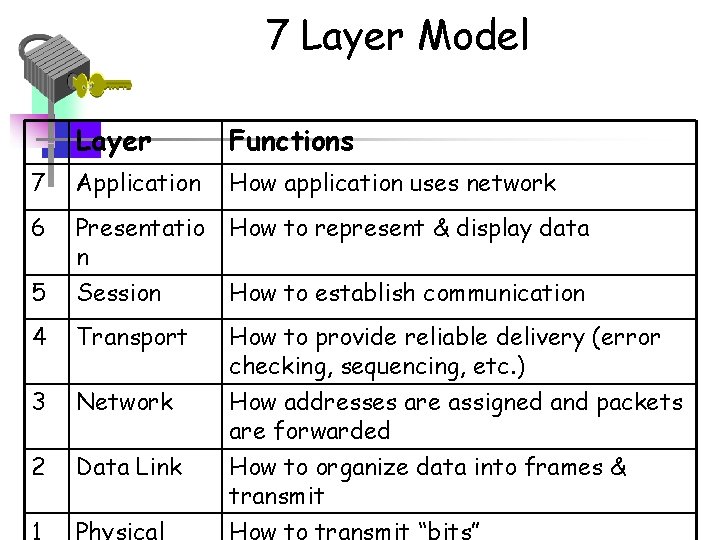
7 Layer Model Layer Functions 7 Application How application uses network 6 Presentatio n How to represent & display data 5 Session How to establish communication 4 Transport How to provide reliable delivery (error checking, sequencing, etc. ) 3 Network 2 Data Link 1 Physical How addresses are assigned and packets are forwarded How to organize data into frames & transmit How to transmit “bits”
Attacks, Services and Mechanisms • Security Attack: Any action that compromises the security of information. • Security Mechanism: A mechanism that is designed to detect, prevent, or recover from a security attack. • Security Service: A service that enhances the security of data processing systems and information transfers. A security service makes use of one or more security mechanisms
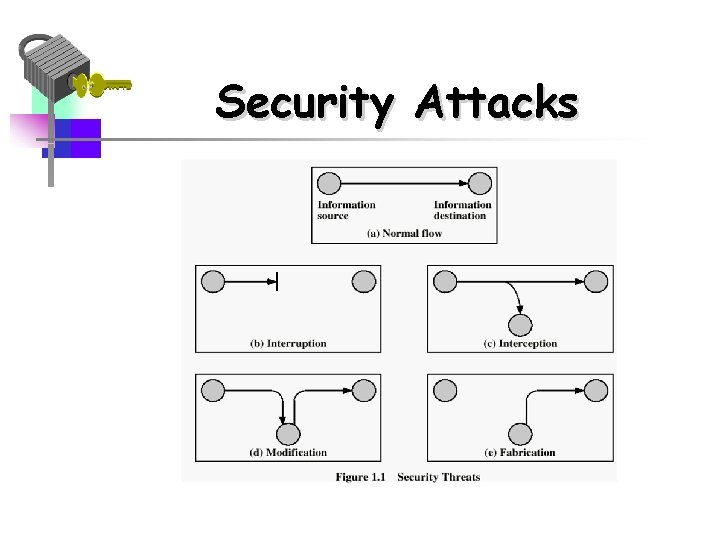
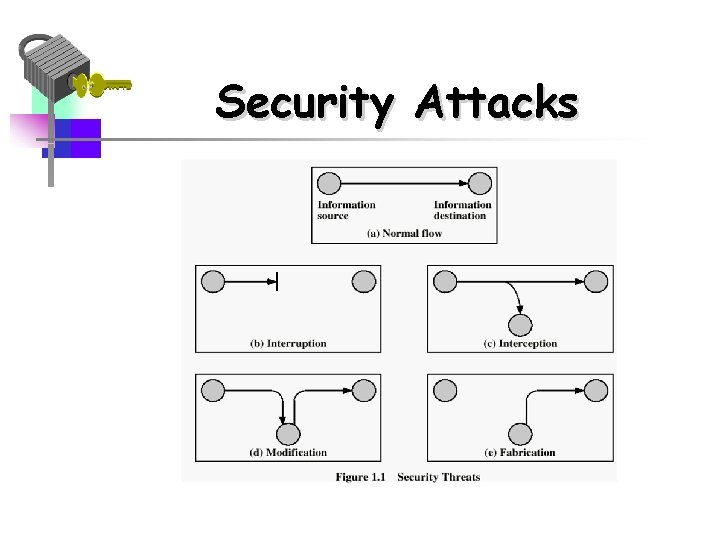
Security Attacks
Security Attacks • Interruption: This is an attack on availability – Disrupting traffic – Physically breaking communication line • Interception: This is an attack on confidentiality – Overhearing, eavesdropping over a communication line
Security Attacks (continued) • Modification: This is an attack on integrity – Corrupting transmitted data or tampering with it before it reaches its destination • Fabrication: This is an attack on authenticity – Faking data as if it were created by a legitimate and authentic party
Threats and Attacks • Threat - a potential for violation of security or a possible danger that might exploit a vulnerability • Attack - an assault on system security- an intelligent act that is a deliberate attempt to evade security services and violate the security policy of a system. • Attack (or exploit). An action taken to harm an asset
Threats • Disclosure – unauthorized access to information • Deception – acceptance of false data • Disruption- interruption or prevention of correct operation • Usurpation- unauthorized control of some part of a system
Examples of Threats • Snooping intercepting information (“passive” wiretapping) • Modification or alteration of information by “active” wiretapping • Masquerading or spoofing • Repudiation of origin • Delay or denial of service
Safeguards and Vulnerabilities • A Safeguard is a countermeasure to protect against a threat • A weakness in a safeguard is called a vulnerability
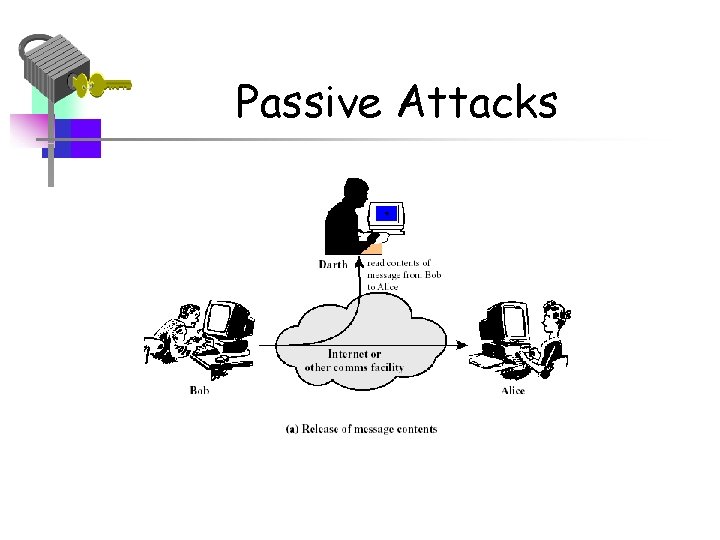
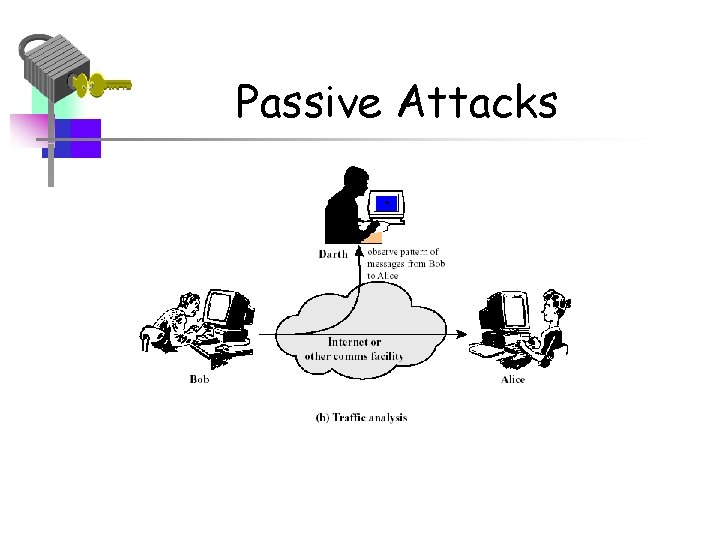
Passive and active attacks • Passive attacks – No modification of content or fabrication – Eavesdropping to learn contents or other information (transfer patterns, traffic flows etc. ) • Active attacks – Modification of content and/or participation in communication to • Impersonate legitimate parties • Modify the content in transit • Launch denial of service attacks
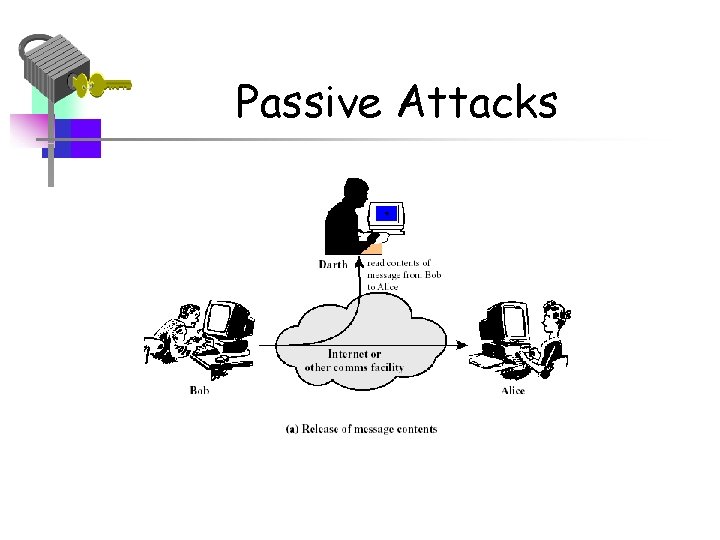
Passive Attacks
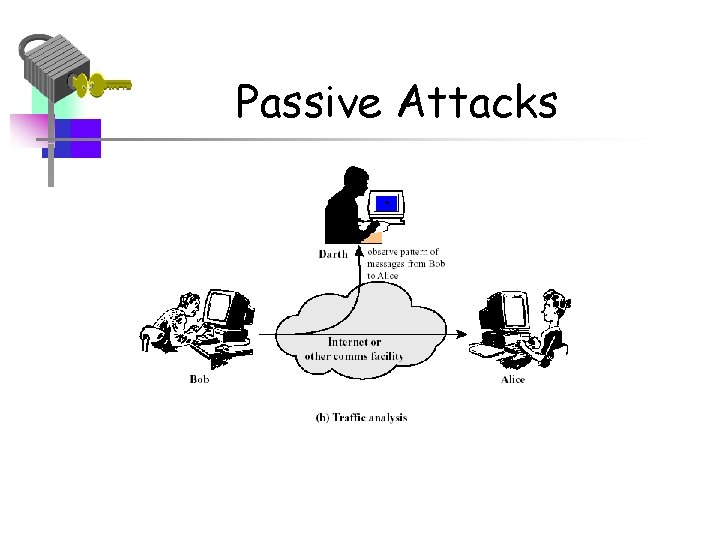
Passive Attacks
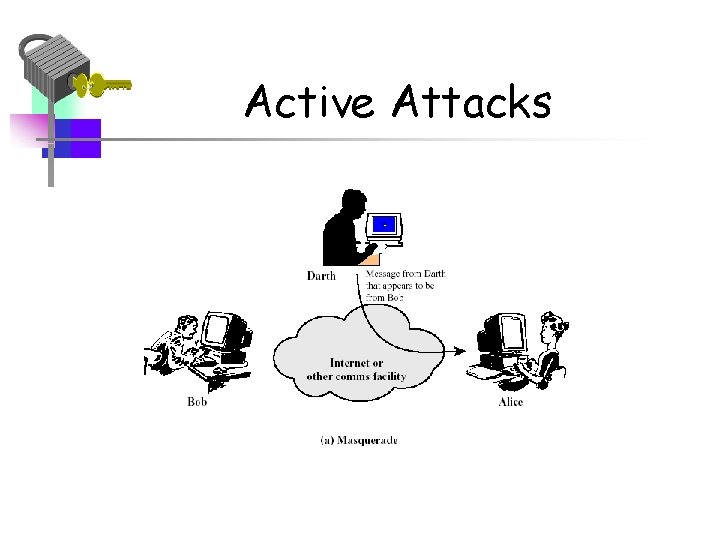
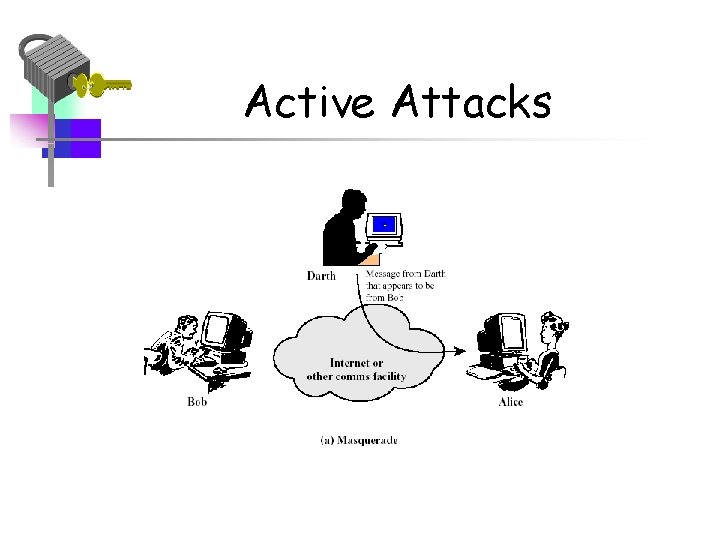
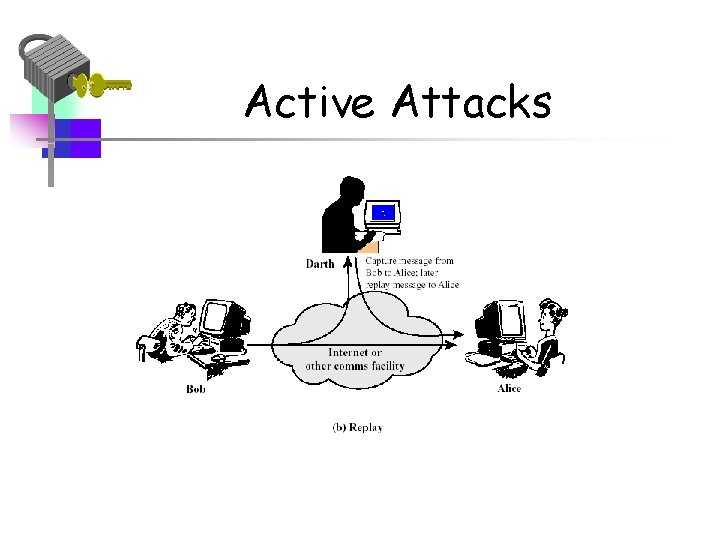
Active Attacks
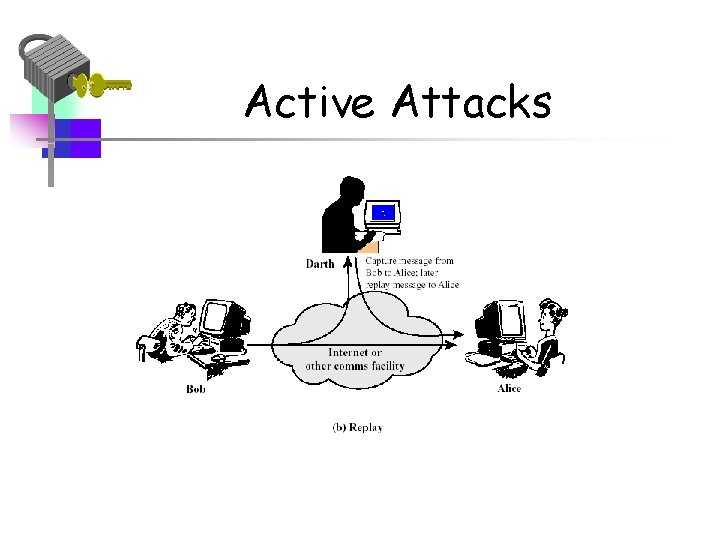
Active Attacks
Two types of threats • Information access threats – Intercept or modify data on behalf of users who should not have access to that data. – E. g. corruption of data by injecting malicious code • Service threats – Exploit service flaws in computers to inhibit use by legitimate uses. – E. g. disabling authentication
![Fundamental threats Mc Gibney 04 Information leakage Disclosure to unauthorized parties Fundamental threats [Mc. Gibney 04] • Information leakage – Disclosure to unauthorized parties –](https://slidetodoc.com/presentation_image_h2/62e007e18213767d1b06e1d841a04b1e/image-29.jpg)
Fundamental threats [Mc. Gibney 04] • Information leakage – Disclosure to unauthorized parties – Prince Charles mobile phone calls, 1993 • Integrity violation – Corruption of data or loss of data – Coca-Cola website defaced with slogans, 1997 • Denial of service – Unavailability of system/service/network Illegitimate use – Morris Internet worm spread to 5% of machines on the Internet, 1988
Services and Mechanisms • A security policy is a statement of what is and what is not allowed. • A security service is a measure to address a threat – E. g. authenticate individuals to prevent unauthorized access • A security mechanism is a means to provide a service – E. g. encryption, cryptographic protocols
Security Services • A security service is a service provided by the protocol layer of a communicating system (X. 800) • 5 Categories – – – Authentication Access Control Data confidentiality Data Integrity Nonrepudiation (and Availability)
Authentication • The authentication service is concerning with assuring that a communication is authentic: • The recipient of the message should be sure that the message came from the source that it claims to be • All communicating parties should be sure that the connection is not interfered with by unauthorized party. Example: consider a person, using online banking service. Both the user and the bank should be assured in identities of each other
Access control • This service controls • who can have access to a resource; • under what conditions access can occur; • what those accessing are allowing to do. Example: in online banking a user may be allowed to see his balance, but not allowed to make any transactions for some of his accounts.
Data confidentiality • The protection of data from unauthorized disclosure (from passive attacks). • Connection confidentiality • Connectionless confidentiality • Selective field confidentiality • Traffic-Flow Confidentiality
Data Integrity • The assurance that data received are exactly as sent by an authorized entity, i. e. contain • no modification • no insertion • no deletion • no replay • Protection from active attacks It may be • integrity with recovery, or • Integrity without recovery (detection only)
Nonrepudiation • Protection against denial by one of the entities involved in a communication of having participated in the communication. Nonrepudiation can be related to • Origin: proof that the message was sent by the specified party • Destination: proof that the message was received by the specified party • Example: Imagine a user of online banking who has made a transaction, but later denied that. How the bank can protect itself in a such situation?
Availability service • Protects a system to ensure its availability • Particularly, it addresses denial-ofservice attacks • Depends on other security services: access control, authentication, etc
Security Services • Authentication (who created or sent the data) • Access control (prevent misuse of resources) • Confidentiality (privacy) • Integrity (has not been altered) • Non-repudiation (the order is final) • Availability (permanence, non-erasure) – Denial of Service Attacks – Virus that deletes files
Security Services Examples • Authentication – Ensuring the proper identification of entities and origins of data before communication • Access control – Preventing unauthorized access to system resources • Data confidentiality – Preventing disclosure to unauthorized parties • Data integrity – Preventing corruption of data • Non-repudiation – Collecting proof to prevent denial of participation in transaction or communication • Availability – Protection against denial-of-service
Security Mechanisms Examples • Two types – Specific mechanisms existing to provide certain security services • E. g. encryption used for authentication – Pervasive mechanisms which are general mechanisms incorporated into the system and not specific to a service • E. g. security audit trail
Model for Network Security • Basic tasks – Design an algorithm that opponent cannot defeat – Generate the secret information to be used with the algorithm – Develop methods for distributing secret information – Specify a protocol to be used • May need a trusted third part to assist
Model for Network Access Security • • using this model requires us to: 1. select appropriate gatekeeper functions to identify users 2. implement security controls to ensure only authorised users access designated information or resources trusted computer systems may be useful to help implement this model
Methods of Defense • Encryption • Software Controls – (access limitations in a data base, in operating system protect each user from other users) • Hardware Controls – (smartcard) • Policies – (frequent changes of passwords) • Physical Controls
Internet standards and RFCs • The Internet society – Internet Architecture Board (IAB) – Internet Engineering Task Force (IETF) – Internet Engineering Steering Group (IESG)
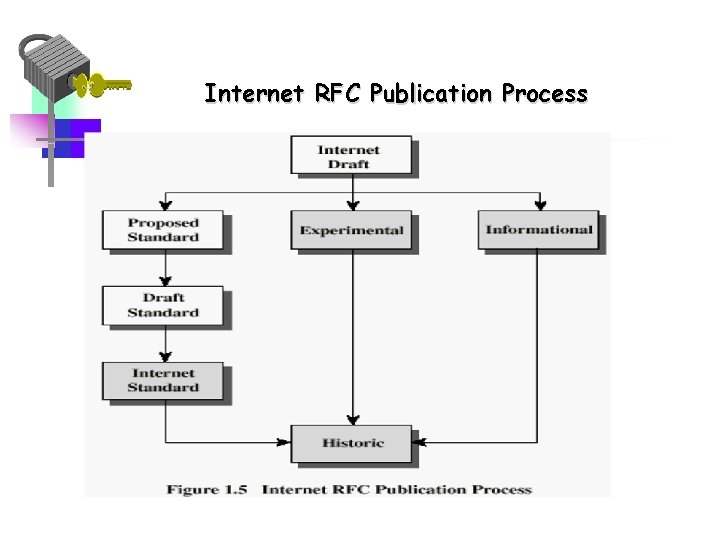
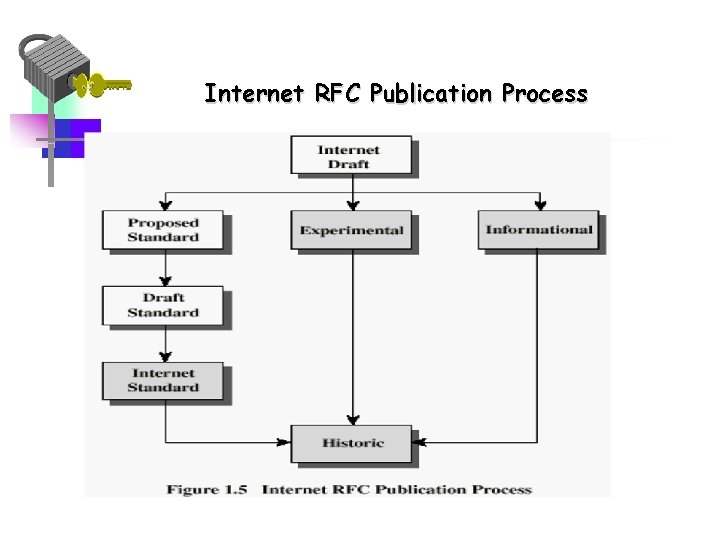
Internet RFC Publication Process
Recommended Reading • Pfleeger, C. Security in Computing. Prentice Hall, 1997. • Mel, H. X. Baker, D. Cryptography Decrypted. Addison Wesley, 2001. • Rita Summers, Secure Computing: Threats and Safe Guards, Mc. Graw. Hill. • Peter Ryan and Steve Schneider, Modeling and analysis of security protocols, Addison Wesley. • V. Shmatikov, Network security and privacy, University of Texas, Austin, TX. • Jimmy Mc. Gibney, IT Security 2004/2005, WIT.