Composing Quantum Protocols Dominic Mayers Universit de Sherbrooke
Composing Quantum Protocols Dominic Mayers Université de Sherbrooke Joint Work with Michael Ben-Or
Overview • Basic Quantum Mechanics • Models for quantum protocols and attacks. • Canetti`s security definition and composability theorem in the quantum world • Composability of Quantum Key Distribution (joint work with Michael Ben-Or, Michal Horodecki, Debbie Leung and Jonathan Oppenheim) • Generalization of Ideal protocols (pro and con) X • Briefly mention application to relativistic bit commitment X
Basic Quantum Mechanics Classically, we believe that, in principle, if we are very careful, we can always extract a property of a system without disturbing the system. If we have two properties (e. g. momemtum and position), we can make a measurement to extract the first property and another measurement to extract the second property. Quantum Mechanics uses the non abelian properties of operators on Hilbert space to model the fact that two measurements are not always compatible. The execution of one measurement (say momemtum) fundamentally interfers with the other (say position).
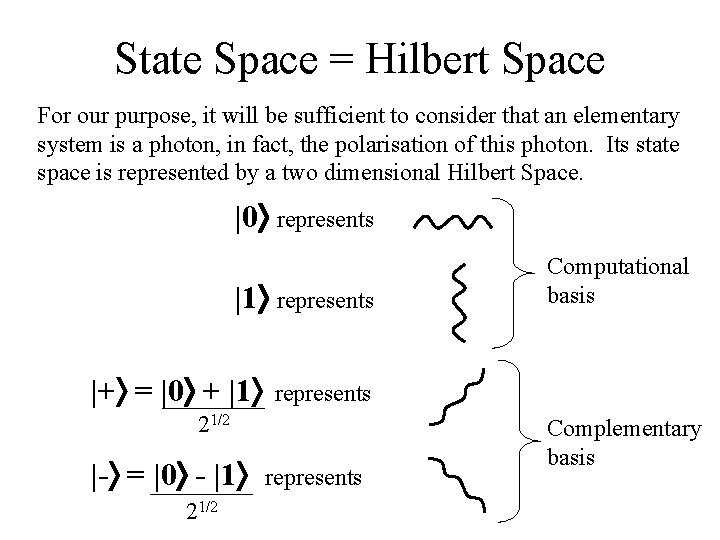
State Space = Hilbert Space For our purpose, it will be sufficient to consider that an elementary system is a photon, in fact, the polarisation of this photon. Its state space is represented by a two dimensional Hilbert Space. |0 represents |1 represents |+ = |0 + |1 represents 21/2 |- = |0 - |1 21/2 Computational basis represents Complementary basis
General state and transformation The general state is |0 + |1 where and are complex numbers with | |2 + | |2 = 1. Global phase (multiplication by a complex number) does not change the physical state. The valid transformations are unitary transformations on the Hilbert space. This extends to tensor products of Hilbert Space. For example, |00 |01 |10 |11 is a basis for two photons.
Classical Vs Quantum Many quantum observable have a classical counterpart. The polarisation of a photon is an example. Its classical counterpart is the polarisation of a classical laser beam. The polarisation of a classical laser beam can be observed without disturbing it. This is not true for the (quantum) polarisation of a photon.
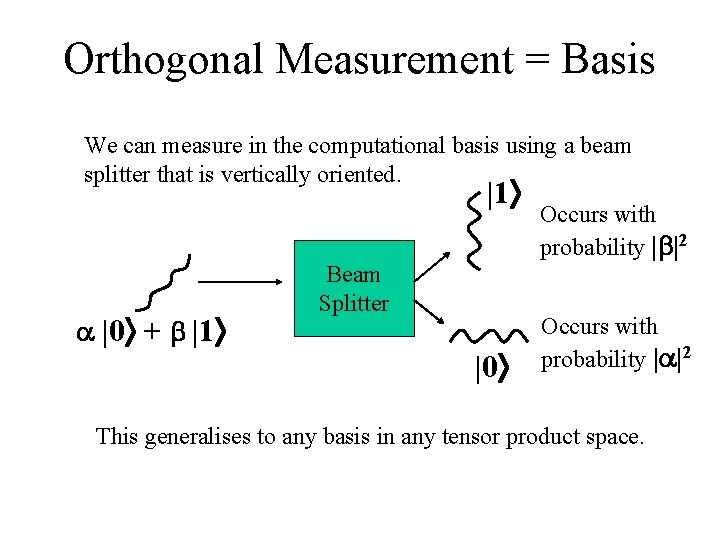
Orthogonal Measurement = Basis We can measure in the computational basis using a beam splitter that is vertically oriented. |1 |0 + |1 Beam Splitter |0 Occurs with probability | |2 This generalises to any basis in any tensor product space.
Models for Quantum Protocols A protocol is specified by an initial state for each party and a sequence of quantum circuits: where each circuit is controled by a single party. Communication occurs through registers that are transferred from one party to another. This is not enough. We also need to specify what is a subprotocol and how communication occurs between a protocol and its sub-protocols.
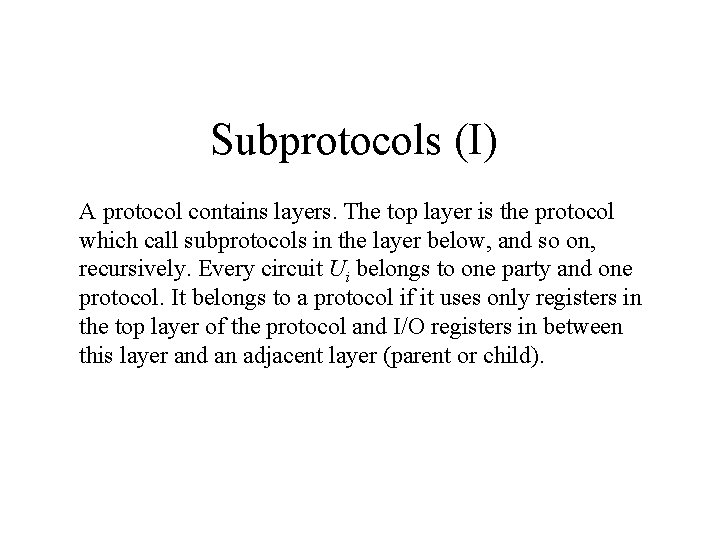
Subprotocols (I) A protocol contains layers. The top layer is the protocol which call subprotocols in the layer below, and so on, recursively. Every circuit Ui belongs to one party and one protocol. It belongs to a protocol if it uses only registers in the top layer of the protocol and I/O registers in between this layer and an adjacent layer (parent or child).
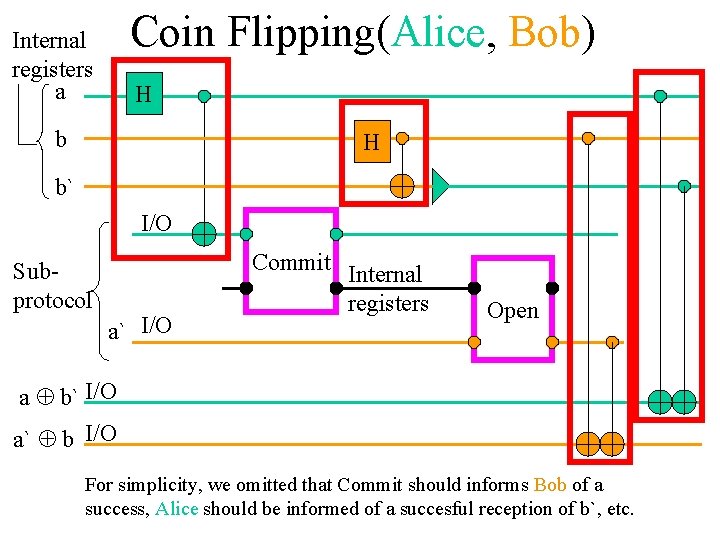
Coin Flipping(Alice, Bob) Internal registers a H b` I/O Subprotocol Commit a` I/O Internal registers Open a b` I/O a` b I/O For simplicity, we omitted that Commit should informs Bob of a success, Alice should be informed of a succesful reception of b`, etc.
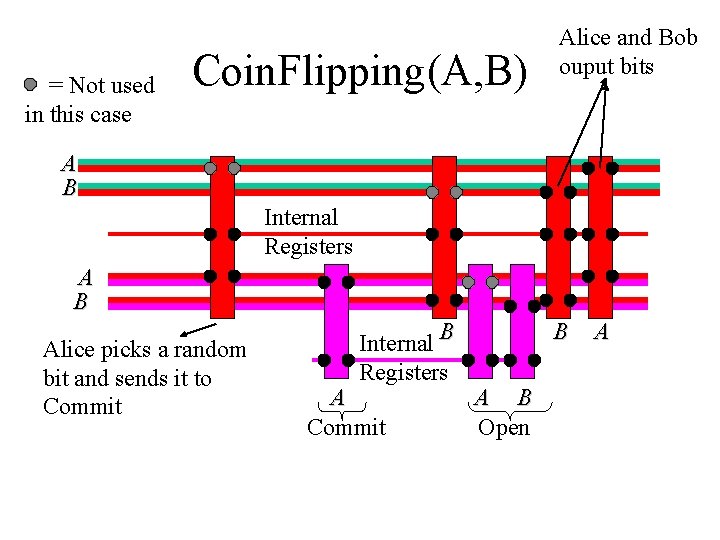
= Not used in this case Coin. Flipping(A, B) Alice and Bob ouput bits A B Internal Registers A B Alice picks a random bit and sends it to Commit Internal B Registers A Commit B A B Open A
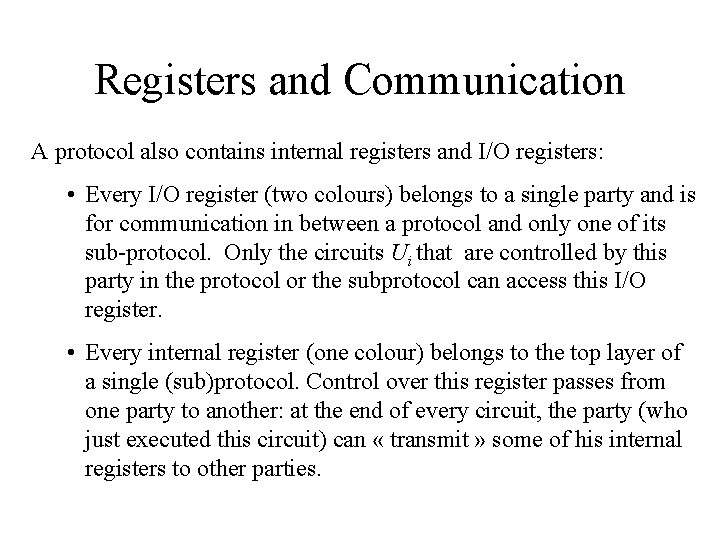
Registers and Communication A protocol also contains internal registers and I/O registers: • Every I/O register (two colours) belongs to a single party and is for communication in between a protocol and only one of its sub-protocol. Only the circuits Ui that are controlled by this party in the protocol or the subprotocol can access this I/O register. • Every internal register (one colour) belongs to the top layer of a single (sub)protocol. Control over this register passes from one party to another: at the end of every circuit, the party (who just executed this circuit) can « transmit » some of his internal registers to other parties.
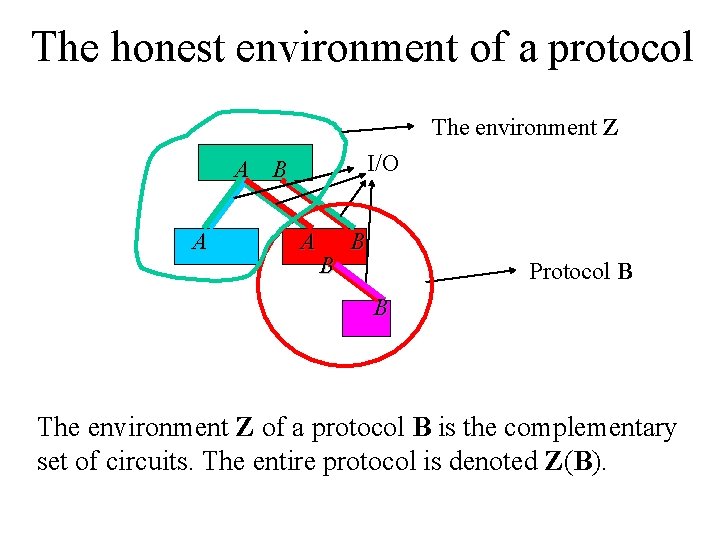
The honest environment of a protocol The environment Z I/O A B A A B B Protocol B B The environment Z of a protocol B is the complementary set of circuits. The entire protocol is denoted Z(B).
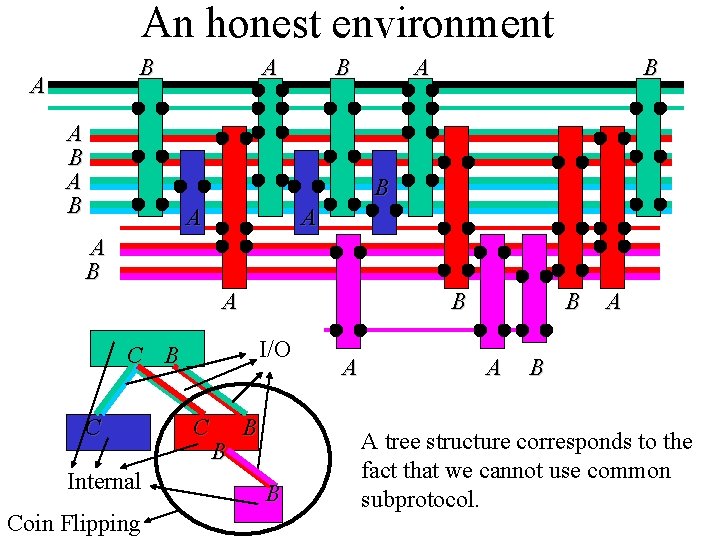
An honest environment B A A B A B B A A A B I/O C B C Internal Coin Flipping C B B B A A B A tree structure corresponds to the fact that we cannot use common subprotocol.
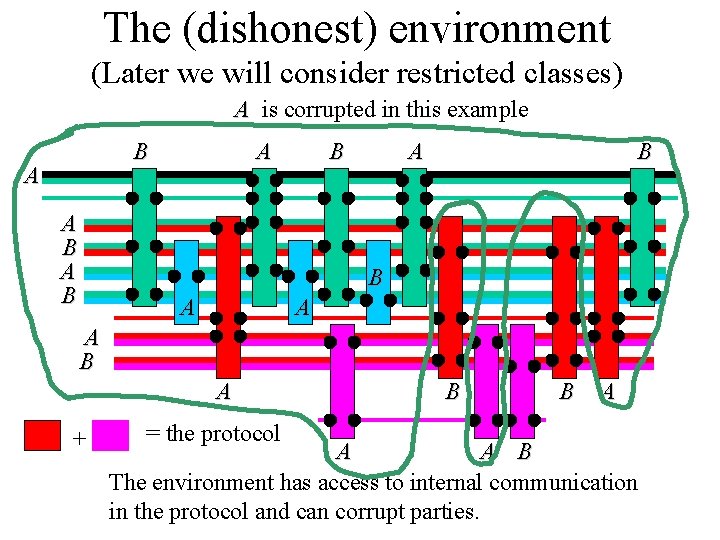
The (dishonest) environment (Later we will consider restricted classes) A is corrupted in this example B A A B A B B A A A B A + = the protocol B B A A A B The environment has access to internal communication in the protocol and can corrupt parties.
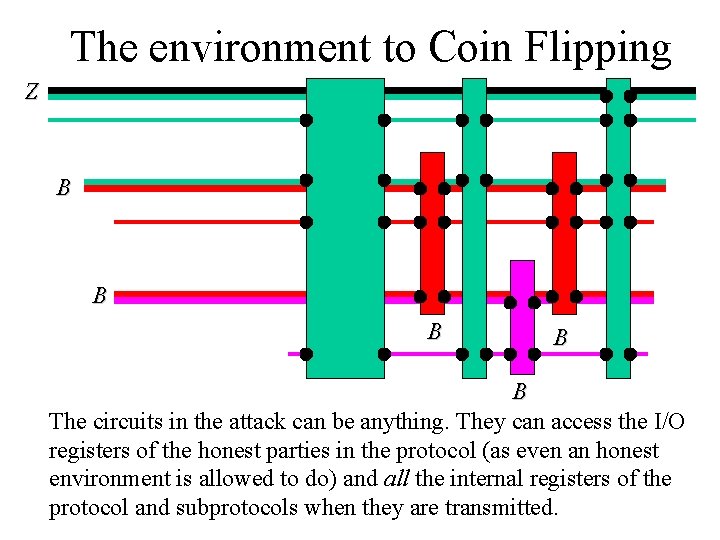
The environment to Coin Flipping Z B B B The circuits in the attack can be anything. They can access the I/O registers of the honest parties in the protocol (as even an honest environment is allowed to do) and all the internal registers of the protocol and subprotocols when they are transmitted.
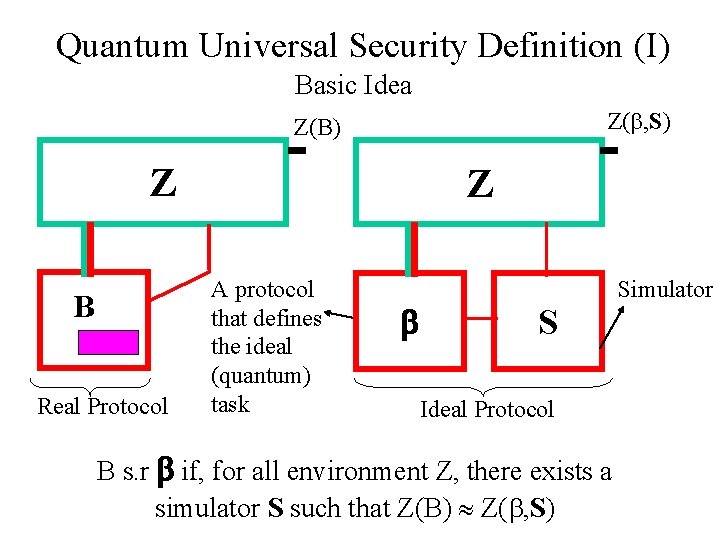
Quantum Universal Security Definition (I) Basic Idea Z( , S) Z(B) Z B Real Protocol Z A protocol that defines the ideal (quantum) task S Simulator Ideal Protocol B s. r if, for all environment Z, there exists a simulator S such that Z(B) Z( , S)
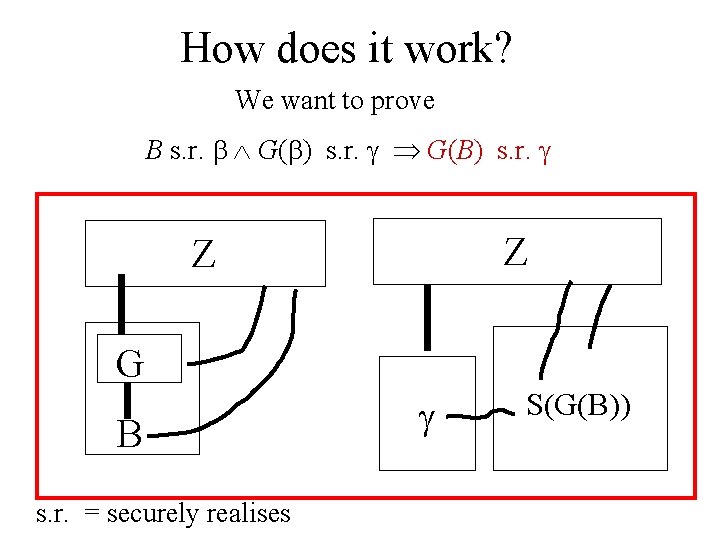
How does it work? We want to prove B s. r. G( ) s. r. G(B) s. r. Z Z G B s. r. = securely realises S(G(B))
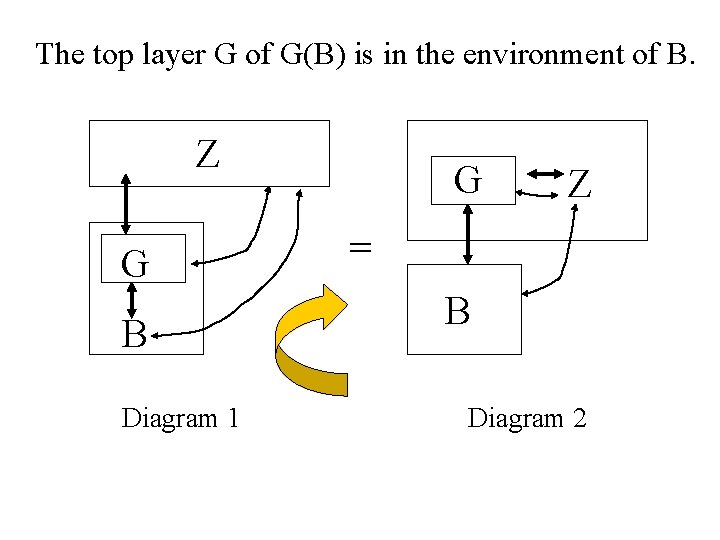
The top layer G of G(B) is in the environment of B. Z G B Diagram 1 G Z = B Diagram 2
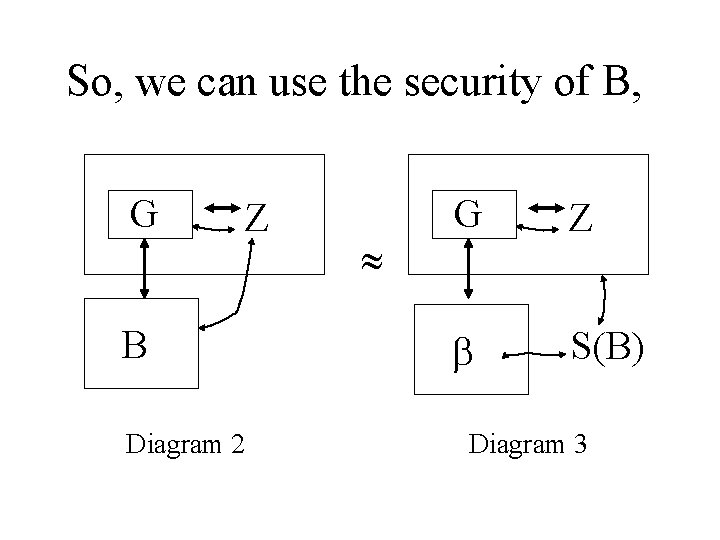
So, we can use the security of B, G Z B Diagram 2 G Z S(B) Diagram 3
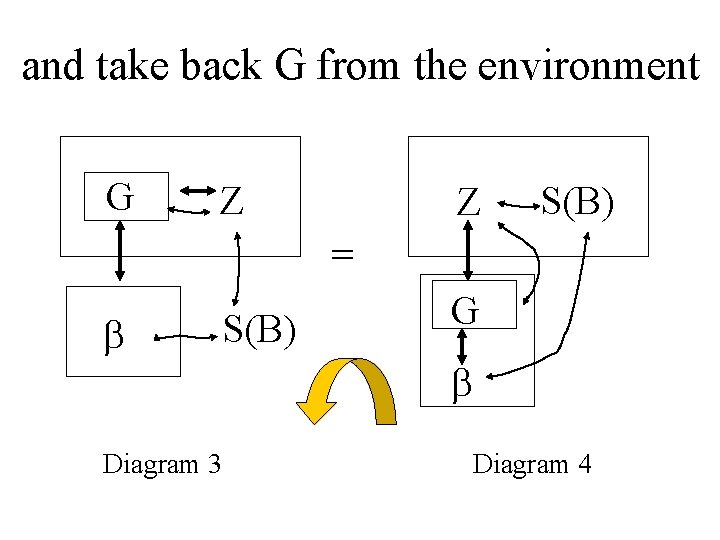
and take back G from the environment G Z Z S(B) = S(B) Diagram 3 G Diagram 4
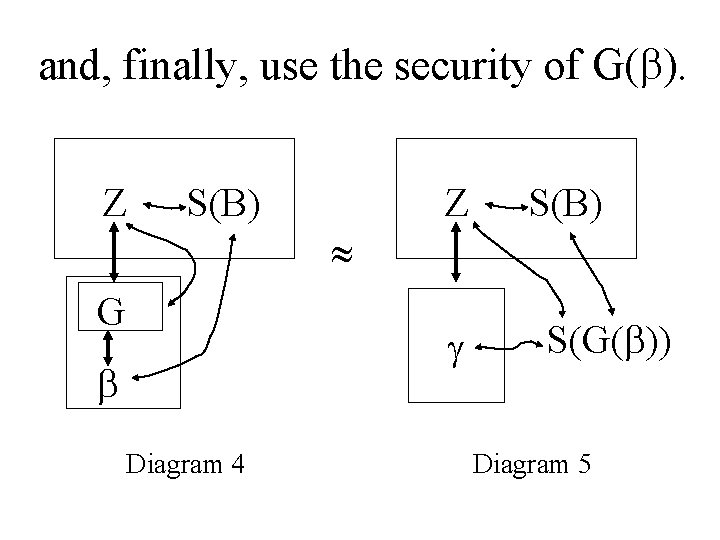
and, finally, use the security of G( ). Z S(B) G Diagram 4 S(G( )) Diagram 5
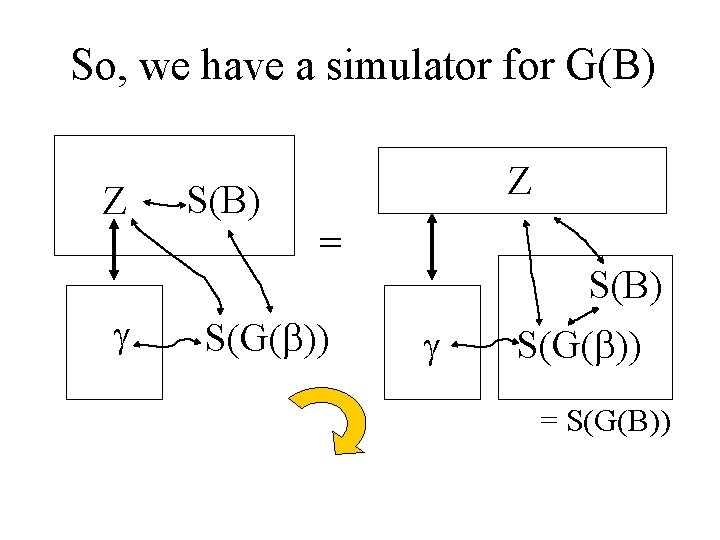
So, we have a simulator for G(B) Z S(B) Z = S(G( )) S(B) S(G( )) = S(G(B))
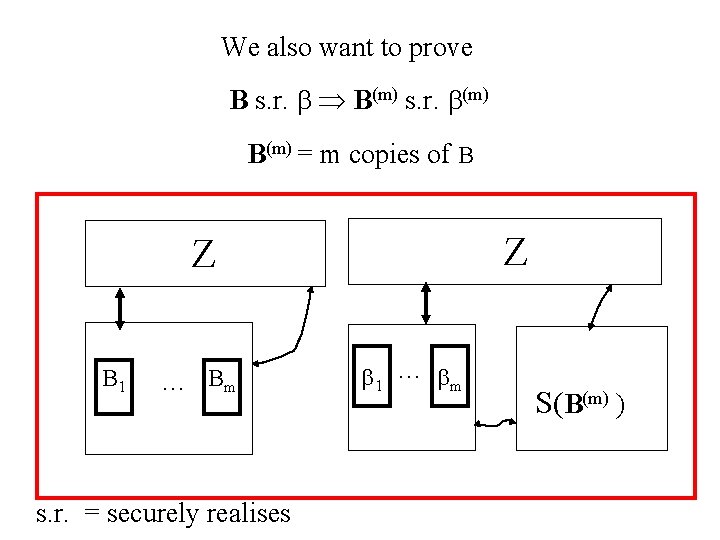
We also want to prove B s. r. B(m) s. r. (m) B(m) = m copies of B Z Z B 1 … Bm s. r. = securely realises 1 … m S(B(m) )
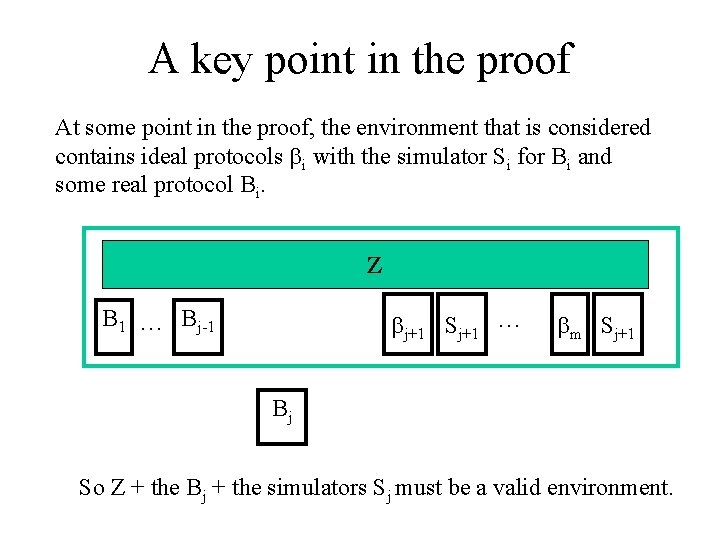
A key point in the proof At some point in the proof, the environment that is considered contains ideal protocols i with the simulator Si for Bi and some real protocol Bi. Z B 1 … Bj-1 j+1 Sj+1 … m Sj+1 Bj So Z + the Bj + the simulators Sj must be a valid environment.
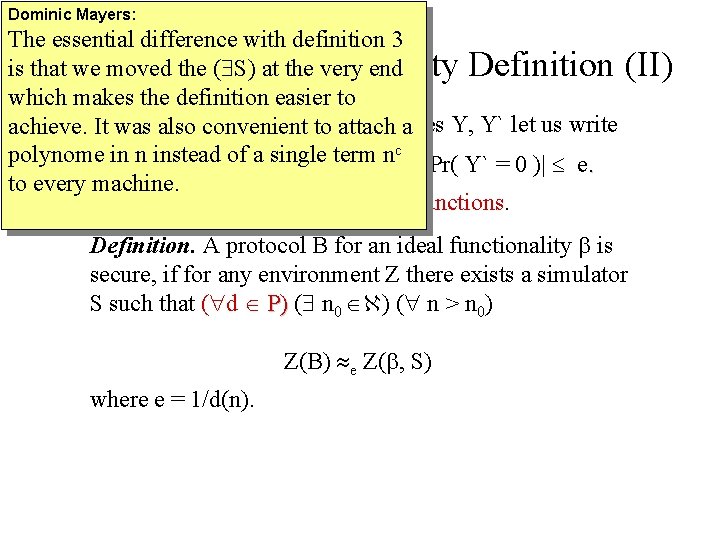
Dominic Mayers: The essential difference with definition 3 is that we moved the ( S) at the very end Quantum Universal Security Definition (II) which makes the definition easier to For any two random binary variables Y, Y` let us write achieve. It was also convenient to attach a c polynome in n instead of a single term n Y e Y` if | Pr( Y = 0 ) - Pr( Y` = 0 )| e. . to every machine. Let P be the set of all polynomial functions. Definition. A protocol B for an ideal functionality is secure, if for any environment Z there exists a simulator S such that ( d P) ( n P) 0 ) ( n > n 0) Z(B) e Z( , S) where e = 1/d(n).
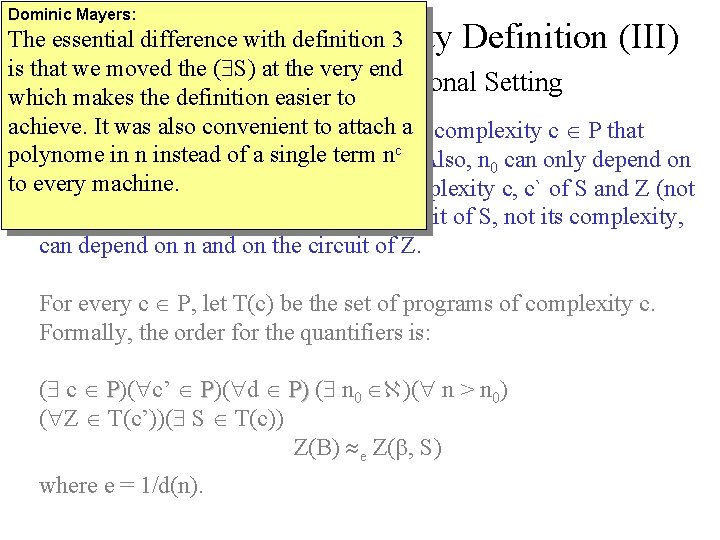
Dominic Mayers: The essential difference with definition 3 Quantum Universal Security Definition (III) is that we moved the ( S) at the very end About the Computational Setting which makes the definition easier to achieve. It was also convenient to attach a The simulator S must have a polynomial complexity c P that polynome in n instead of a single term n depends only on B (i. e. not on Z or n 0 c). Also, n 0 can only depend on to every machine. d and on the respective polynomial complexity c, c` of S and Z (not on their actual circuits). The actual circuit of S, not its complexity, can depend on n and on the circuit of Z. For every c P, let T(c) be the set of programs of complexity c. Formally, the order for the quantifiers is: ( c P)( c’ P)( d P) ( n P) 0 )( n > n 0) ( Z T(c’))( S T(c)) Z(B) e Z( , S) where e = 1/d(n).
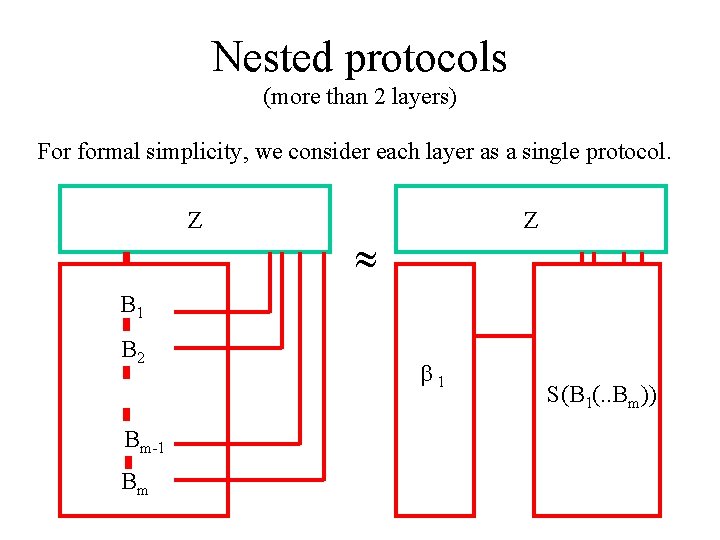
Nested protocols (more than 2 layers) For formal simplicity, we consider each layer as a single protocol. Z Z B 1 B 2 Bm-1 Bm 1 S(B 1(. . Bm))
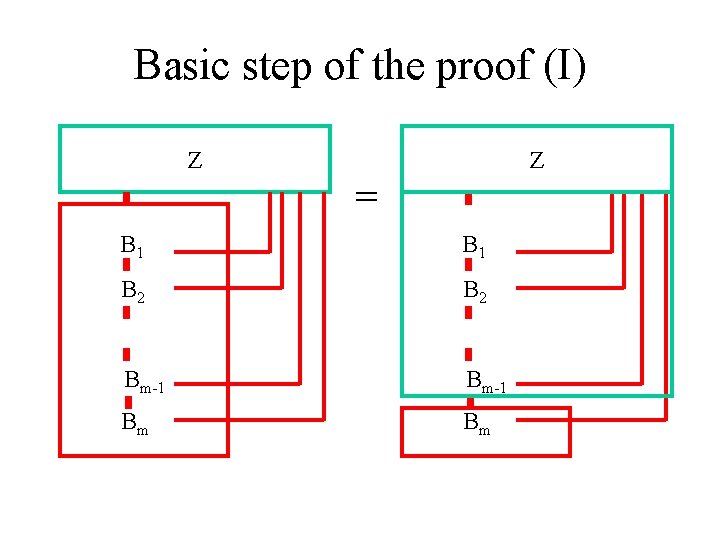
Basic step of the proof (I) Z Z = B 1 B 2 Bm-1 Bm Bm
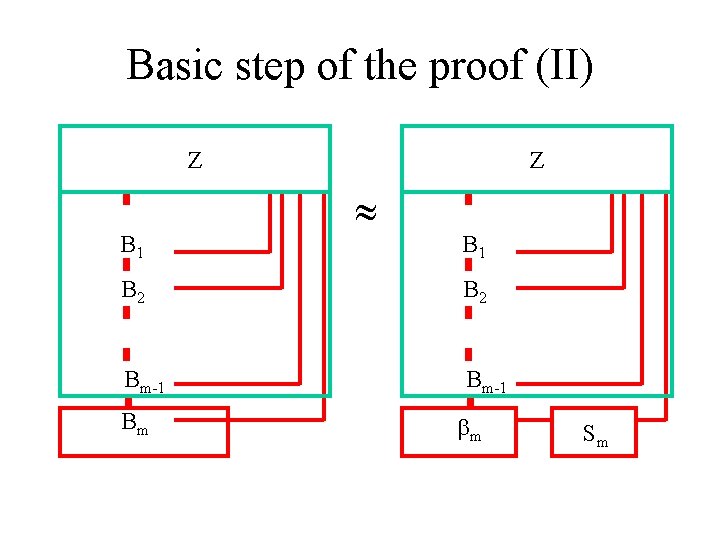
Basic step of the proof (II) Z B 1 B 2 Bm-1 Bm m Sm
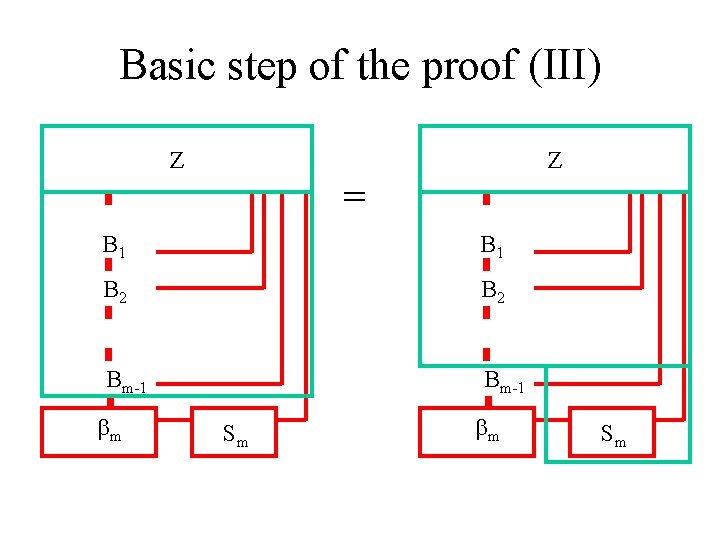
Basic step of the proof (III) Z Z = B 1 B 2 Bm-1 m Sm
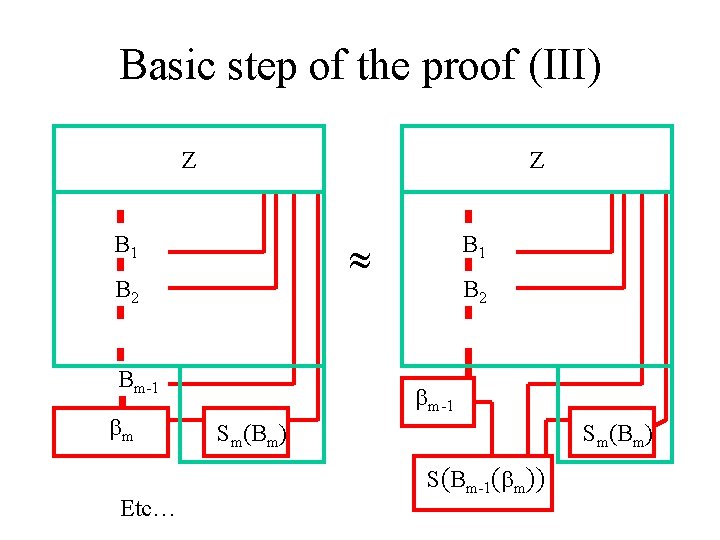
Basic step of the proof (III) Z Z B 1 B 2 Bm-1 m Etc… B 1 B 2 m-1 Sm(Bm) S(Bm-1( m))
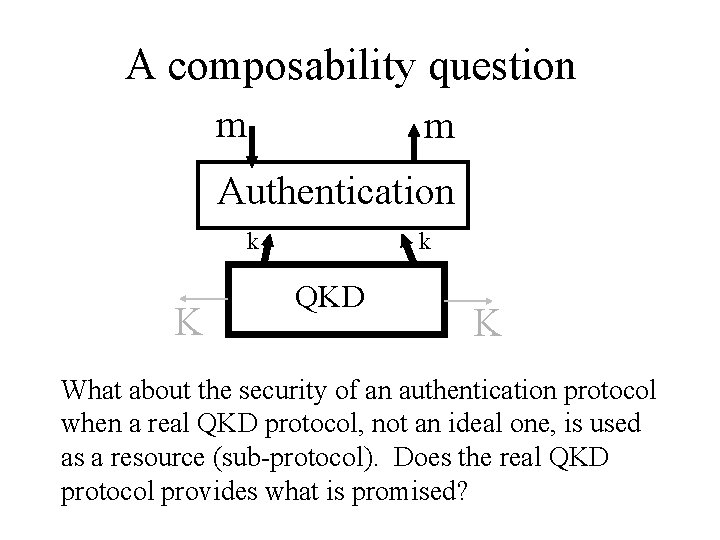
A composability question m m Authentication k K k QKD K What about the security of an authentication protocol when a real QKD protocol, not an ideal one, is used as a resource (sub-protocol). Does the real QKD protocol provides what is promised?
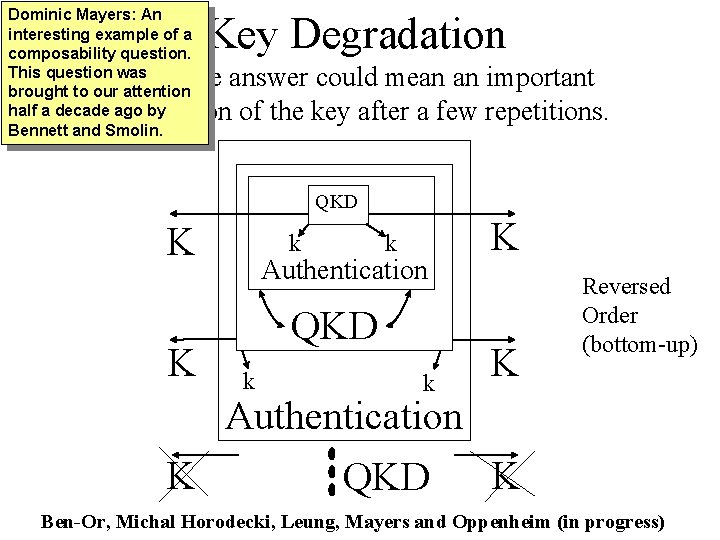
Dominic Mayers: An interesting example of a composability question. This question was brought to our attention half a decade ago by Bennett and Smolin. Key Degradation A negative answer could mean an important degradation of the key after a few repetitions. QKD K K k k Authentication QKD k K QKD K Reversed Order (bottom-up) Authentication K Ben-Or, Michal Horodecki, Leung, Mayers and Oppenheim (in progress)
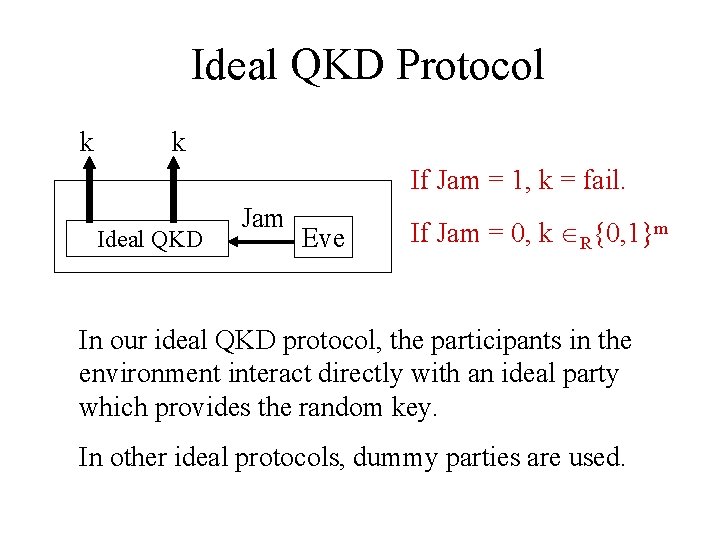
Ideal QKD Protocol k k If Jam = 1, k = fail. Ideal QKD Jam Eve If Jam = 0, k R{0, 1}m In our ideal QKD protocol, the participants in the environment interact directly with an ideal party which provides the random key. In other ideal protocols, dummy parties are used.
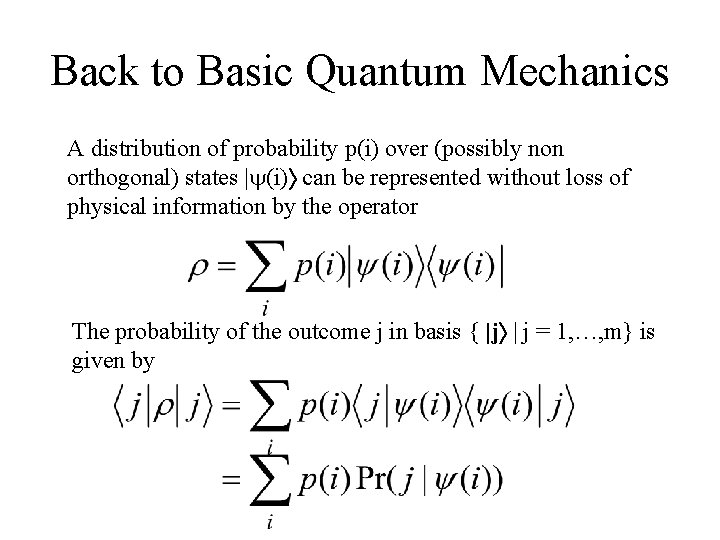
Back to Basic Quantum Mechanics A distribution of probability p(i) over (possibly non orthogonal) states | (i) can be represented without loss of physical information by the operator The probability of the outcome j in basis { |j | j = 1, …, m} is given by
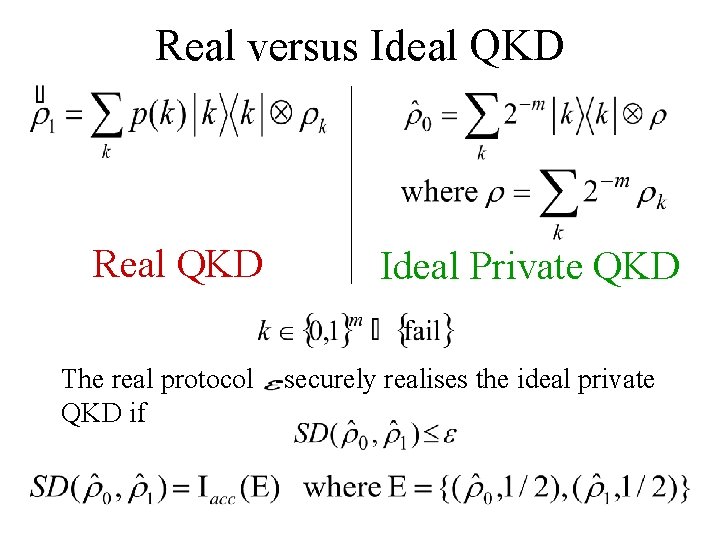
Real versus Ideal QKD Real QKD Ideal Private QKD The real protocol -securely realises the ideal private QKD if
How comes there is a single key k for Alice and Bob on the real side? The known security results for QKD give us that Alice`s key and Bob’s key are almost always identical. For simplicity, we will assume that we are only interested about the privacy of Alice`s key.
Uniformity Vs Privacy The security of QKD is not only a small mutual information. We must also require a priori uniformity, i. e. , in the ideal case, for all k, p(k | Jam = 0) = 2 -m.
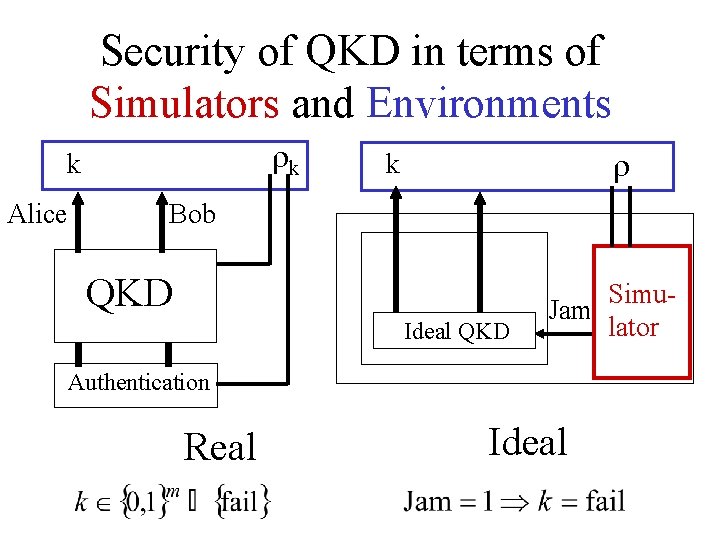
Security of QKD in terms of Simulators and Environments k k Alice k Bob QKD Ideal QKD ? Simu. Jam lator Authentication Real Ideal
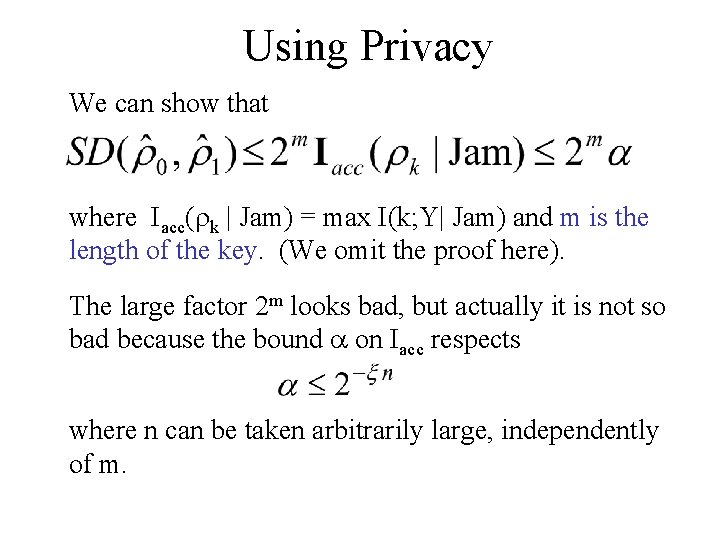
Using Privacy We can show that where Iacc( k | Jam) = max I(k; Y| Jam) and m is the length of the key. (We omit the proof here). The large factor 2 m looks bad, but actually it is not so bad because the bound on Iacc respects where n can be taken arbitrarily large, independently of m.
What about the known QKD protocols • Mayers and Shor-Preskill security proofs can be adapted for composability without the large factor 2 m. • We do not know if B 92 is composable without this large factor (since there is no security proof).
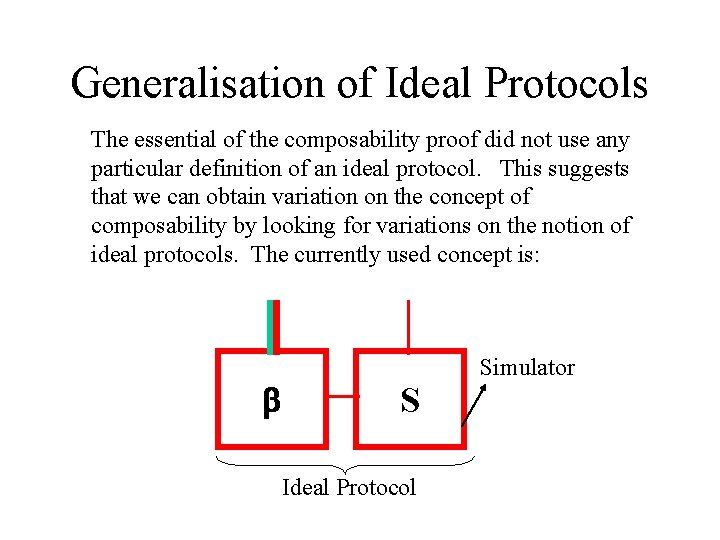
Generalisation of Ideal Protocols The essential of the composability proof did not use any particular definition of an ideal protocol. This suggests that we can obtain variation on the concept of composability by looking for variations on the notion of ideal protocols. The currently used concept is: S Ideal Protocol Simulator
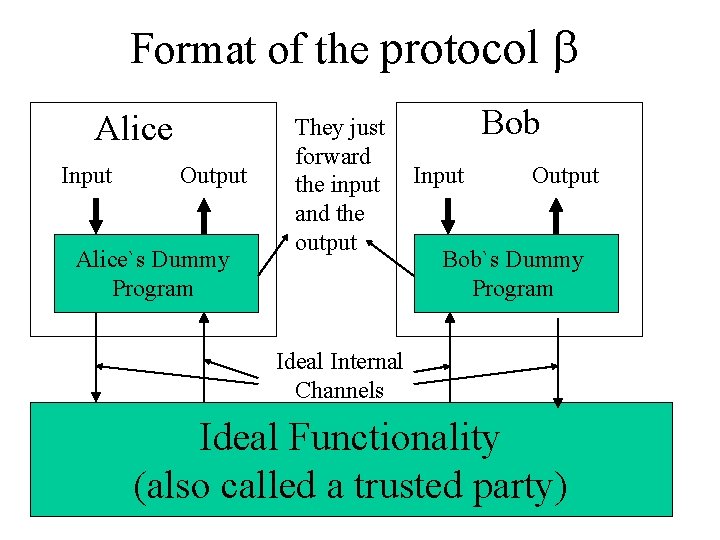
Format of the protocol Alice Input Output Alice`s Dummy Program They just forward the input and the output Bob Input Output Bob`s Dummy Program Ideal Internal Channels Ideal Functionality (also called a trusted party)
A possible variation (I) First, note that simulator depends on the environment. So, in the view point that we have adopted, we already accepted the principle that the ideal protocol can depend on the environment. An ideal protocol is any protocol, including protocols that use unrestricted circuits. However, the final state after every circuit in the ideal protocol should be with high fidelity close to a state that would be obtained with a valid circuit.
A possible variation (II) Of course, we must also specify which properties are satisfied by this « ideal protocol » . For example, there might be measurements that compute the inputs of the corrupted parties in a way that is perfectly consistent with the desired task and the input/output of the honest parties, and commutes with the measurement of these honest input/output.
Composable relativistic bit commitment We have obtained a “composable” relativistic bit commitmen in the following sense: If Alice is corrupted, there exists a measurement that computes the bit that will be open later in the opening phase. This measurement needs only to access the registers that are used by Alice in the commit phase. In particular, this measurement cannot access the register that are kept private by Bob until after the commit phase. The protocol is perfectly concealing against Bob.
Conclusion The quantum composability theorem is useful to provide an adequate angle to prove the security of quantum protocols with subprotocols. The key degradation problem is an example. Many quantum protocols will not respect the “standard” univeral security definition (the one based on simulator and trusted party). Yet, variations on this standard definition can still provide a useful angle.
- Slides: 48