Compliance and Robustness Rules for Windows Media DRM
Compliance and Robustness Rules for Windows Media DRM Implementations Microsoft Corporation
Definitions Compliance Rules specify the required behaviors of the Windows Media DRM implementation and any applications accessing the implementation Compliance Rules include definitions of specific WMDRM license rights Compliance Rules include WMDRM device requirements Robustness Rules specify the Windows Media DRM assets and different levels of robustness required to protect each asset type 2 Copyright 2004 by Microsoft Corporation
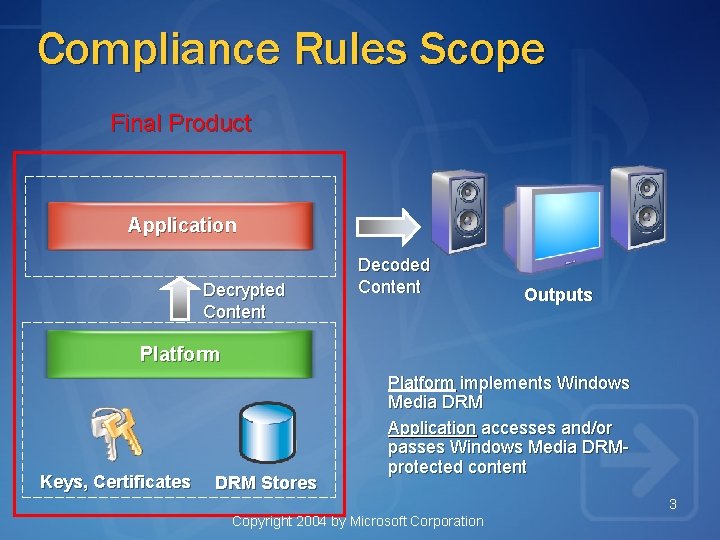
Compliance Rules Scope Final Product Application Decrypted Content Decoded Content Outputs Platform Keys, Certificates DRM Stores Platform implements Windows Media DRM Application accesses and/or passes Windows Media DRMprotected content 3 Copyright 2004 by Microsoft Corporation
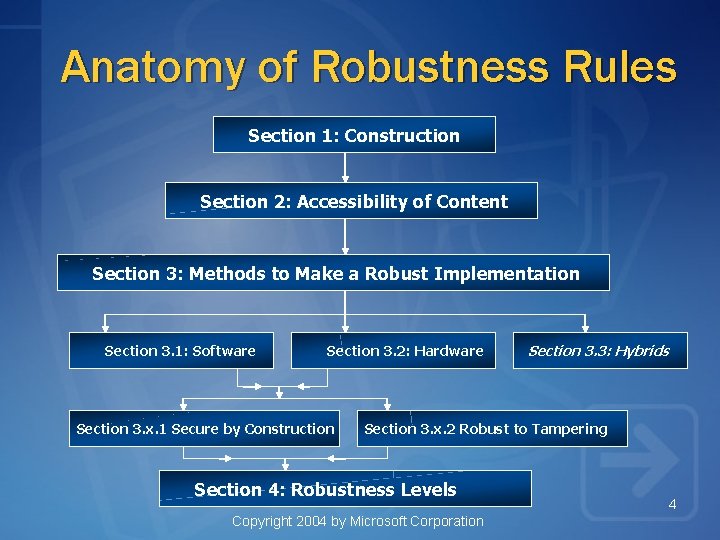
Anatomy of Robustness Rules Section 1: Construction Section 2: Accessibility of Content Section 3: Methods to Make a Robust Implementation Section 3. 1: Software Section 3. 2: Hardware Section 3. x. 1 Secure by Construction Section 3. 3: Hybrids Section 3. x. 2 Robust to Tampering Section 4: Robustness Levels Copyright 2004 by Microsoft Corporation 4

Assets and Security Levels Level 1 Assets • Immune to Widely Available & Specialized Tools Device Key Level 2 Assets • Immune to Widely Available Tools • Resistant to Specialized Tools Content Key Level 3 Assets • Resistant to Widely Available & Specialized Tools Profiling data Widely Available Tools general purpose, easy to use: screwdrivers, clips, file editors, etc. Specialized Tools reasonable price; some skill required: debuggers, memory scanners, etc. Professional Tools high price; professional use ICE, logic analyzers 5 Copyright 2004 by Microsoft Corporation
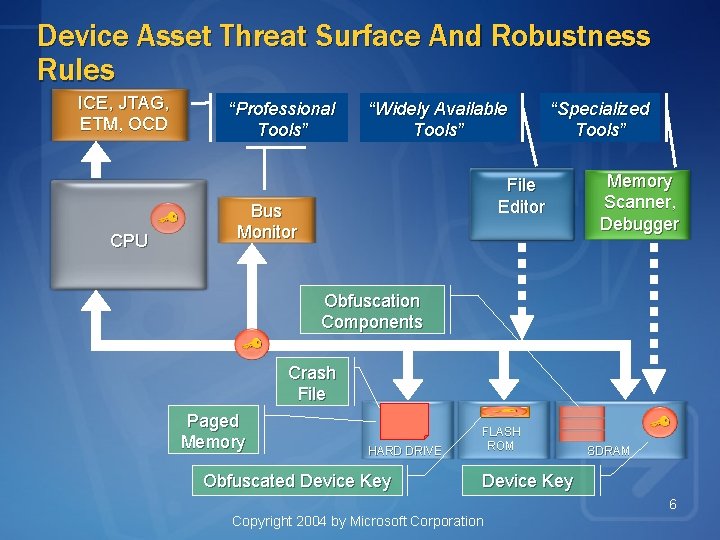
Device Asset Threat Surface And Robustness Rules ICE, JTAG, ETM, OCD CPU “Professional Tools” “Widely Available Tools” “Specialized Tools” File Editor Bus Monitor Memory Scanner, Debugger Obfuscation Components Crash File Paged Memory HARD DRIVE Obfuscated Device Key FLASH ROM SDRAM Device Key 6 Copyright 2004 by Microsoft Corporation
Producing a Robust Solution Understand the Robustness Rules Secured assets on your device Protected content and user accessible bus Widely available, specialized & professional tools Threat model your design For each asset-tool pair, define attack path Evaluate how easily this attack would be done Compare Results to Robustness Rules Does your design meet the minimum standard? 7 Copyright 2004 by Microsoft Corporation
Appendix
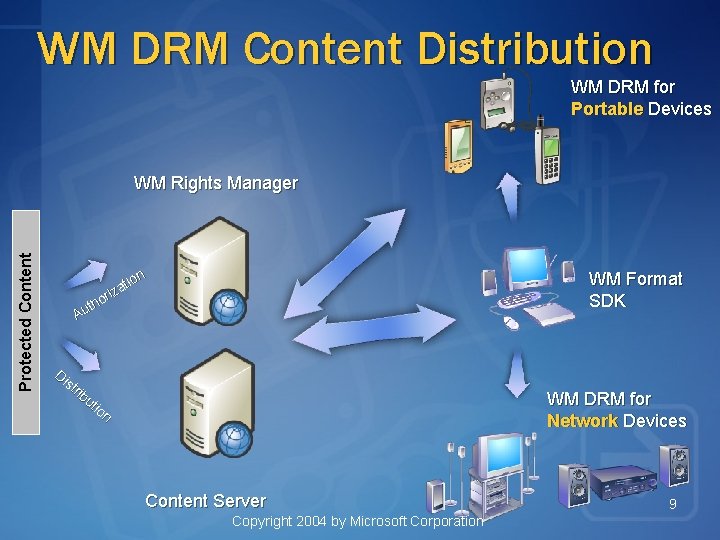
WM DRM Content Distribution WM DRM for Portable Devices Protected Content WM Rights Manager n tio a z ori h t Au WM Format SDK Di st rib ut io n WM DRM for Network Devices Content Server Copyright 2004 by Microsoft Corporation 9
- Slides: 9