COMP 3371 Cyber Security Richard Henson University of
COMP 3371 Cyber Security Richard Henson University of Worcester October 2019
Week 2: “Defensive Security” Strategies for securing data held within digital systems n Objectives: Ø Explain tensions in key principles of maintaining data confidentiality, integrity, availability Ø Devise a security strategy for users in terms of using technical controls to protect access to resources, services and information Ø Explain that total security is a myth; people are people, and computer technology is constantly evolving…
CIA in practice… (1) n Generally about… ØC = confidentiality ØA = Availability Secure it! Want it NOW! Data
CIA in Practice…(2) n Massive Tension… Ønetwork managers: responsibility to keep data secure (CONFIDENTIALITY) Øusers: just want data… NOW!!! » AVAILABILITY » security controls just get in the way
The “I” in the middle Maintaining Data: Integrity n Enforced by Law… Øpersonal or sensitive data MUST be protected against copying/modifying n Recently tightened up (GDPR) » big fines possible! Øusers need to be aware of the data/information dichotomy!
IS Policy and CIA (1) n As CIA is the key to good cyber security… ØAll three aspects should be basic to IS policy » C… good security of network data » I… as above… » A… backend systems should work efficiently with desktops and have excellent backups
IS Policy and CIA (2) Data needs to be looked after!! n Technical responsibility… n Ønetwork engineers needs to make sure data is looked after by systems Ø boundaries need to be protected against malicious data n Management responsibility Øneed to make sure data is looked after by appropriately trained people
Policy and Strategy… plans for the future n Policy… the means for implementing the strategy n n To manage CIA properly… ØStrategy must come first! ØPolicy should follow…
Strategy: (1) Protects Data (2) Enables users to do their jobs n Up to the organisation to choose how to do this… ØLogin or each user ESSENTIAL » necessary for accountability » immediate issue for “start ups” ØESSENTIAL for users to get appropriate system access to do their job… n Who decides what is appropriate? How?
Implementing Strategy… n Usual technical option… Ønetwork devices linked together Øprovide access to the Internet for all linked devices through a server (Internet Gateway) n Software (either/or): ØWindows networks ØSome form of Unix/Linux

Principle of security “controls” n Any method used to protect organisational data against being compromised… Øtechnical controls use hardware and software to protect data Øpeople controls provide procedures for people to follow to protect data Ømanagement controls provide procedures for those managing data users
Technical Controls n Ways to protect the data once users have logged in… ØLog in is a management control implemented through technical means! ØPassword use is a user control, which is assisted by technical rules (e. g. length and “complexity” of password)
Client-server or Peer-peer? n Client-Server essential unless small number of devices (<8) Ømay be happy to just use the Microsoft domain model… » but have in mind the weakness that “read only” files could be changed (!) Øessential to monitor for changes via server logging (event viewer) » makes users accountable
Features of Client-Server LANs n Centralised server(s) Øcontrol user access via login » to system » to the organisational resources they need… n Client end can still hold resources in memory and secondary storage Øa lot (workstation) Ønot much (thin client)
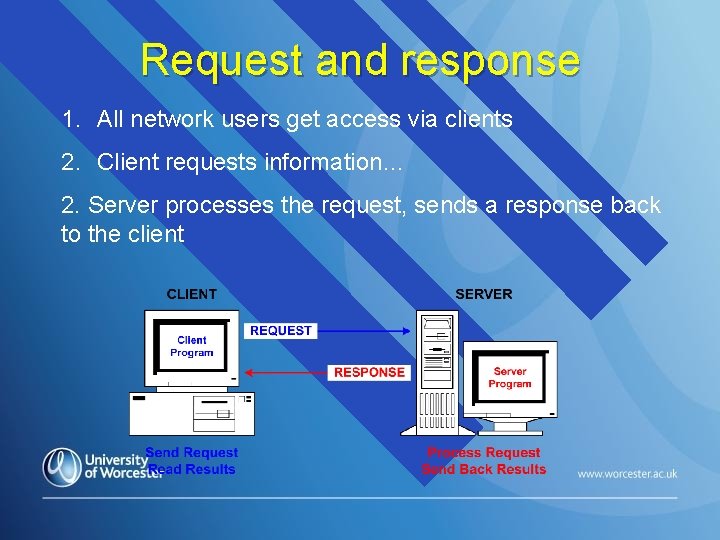
Request and response 1. All network users get access via clients 2. Client requests information… 2. Server processes the request, sends a response back to the client
Technical Controls on Data n Technologies for safe Øtransport… wired or wireless Øprocessing… secure CPU/memory Østorage… n Purpose: Øprotect network resources from attacks and accidental loss of data
Domains: basic hardware infrastructure n Basic principle… resources and security controlled via server(s) Øand accessible to all Øeverything needs at least one back up n Plan hardware and connectivity first… Øsoftware could be Windows or Unix/Linux
Microsoft Implementation n Microsoft domains… Øserver(s) set up first Øclients attached physically & logically to server ØUsers controlled through policy files on server(s)
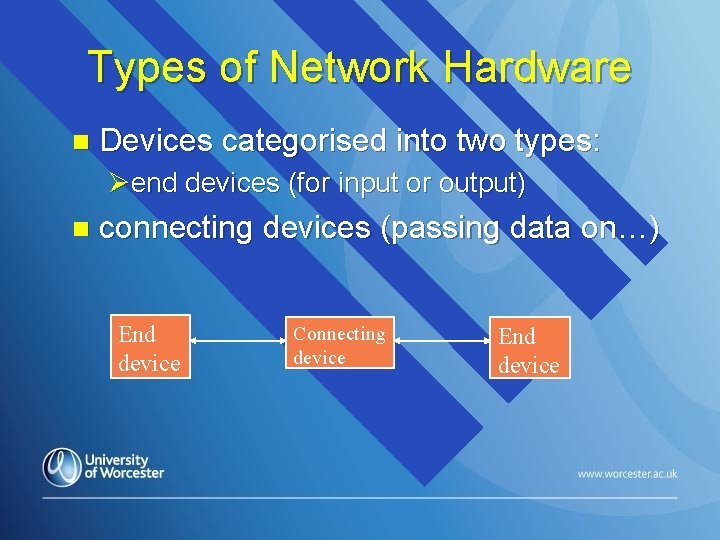
Types of Network Hardware n Devices categorised into two types: Øend devices (for input or output) n connecting devices (passing data on…) End device Connecting device End device
Addressing and Network Devices n Addressing possible at two of the OSI software levels/layers: ØHardware-compatible layer uses MAC addresses ØInternet-compatible layer uses IP addresses ØARP (Address Resolution Protocol) converts addresses from IP to MAC
End Devices Computers n Dumb Terminals n Printers n VOIP phones n Scanners n Anything that inputs or outputs… n
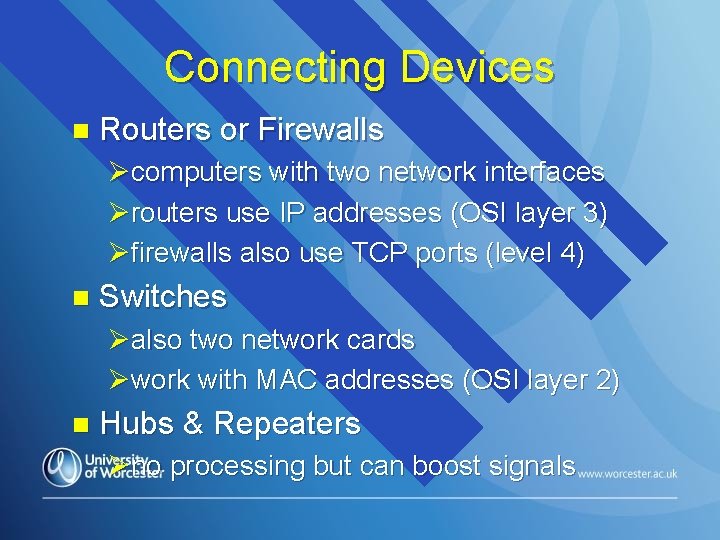
Connecting Devices n Routers or Firewalls Øcomputers with two network interfaces Ørouters use IP addresses (OSI layer 3) Øfirewalls also use TCP ports (level 4) n Switches Øalso two network cards Øwork with MAC addresses (OSI layer 2) n Hubs & Repeaters Øno processing but can boost signals
Switches n Handle network traffic efficiently within a LAN Øprovide cabled connectivity between server/router and user device Øsoftware control using IEEE 802. 3 (Ethernet) standard » physical layer… transfer of electrical signals » MAC addresses and transporting data frames
Routers n Provide connectivity between LANs and LAN segments Øtwo network interfaces (“internal”, “external”) Øneeds same protocol as Internet (IP addressing) Ømay control LAN IP addresses using DHCP protocol Ømay be ethernet or wireless (IEEE 802. 11 x) for internal interface
IP addresses n For packets to move between devices, each device must have an IP address Øe. g. 192. 168. 2. 22 n Three ways to allocate an IP address to a Windows PC: Ømanually… just type it into client interface Øfrom DHCP server/router (between fixed range) Øthrough autoconfig (randomly allocated from a range of IP addresses)
Switches and IP addresses Switches (and routers) link devices together n By default, a switch will create a virtual LAN (VLAN) n Øallows communication between devices on allocated IP address (e. g. 192. 168. 1. 0 -63) Øfine for small networks Øregular cause of lack of connectivity!
Configuring Switches Have an operating system (Cisco i. OS) n Come with default configurations for VLANs n Ømay need changing… Øuse a CLI n IP address needs to be consistent with devices being connected Øneed IP addresses on the same subnet
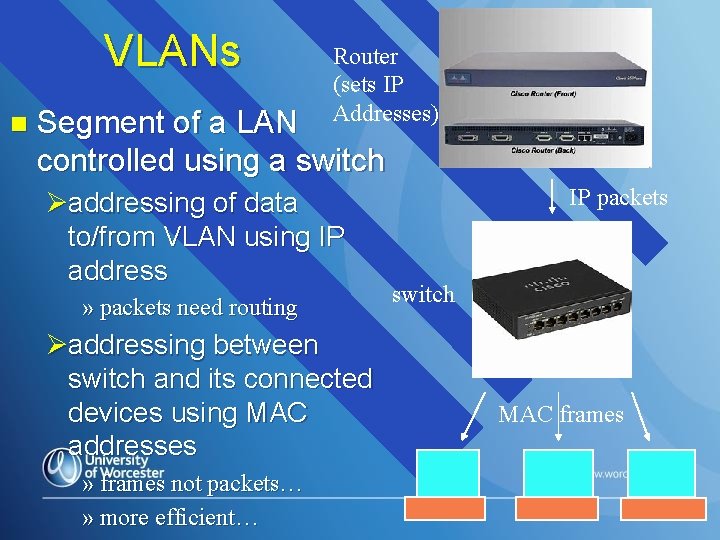
VLANs n Router (sets IP Addresses) Segment of a LAN controlled using a switch Øaddressing of data to/from VLAN using IP address » packets need routing Øaddressing between switch and its connected devices using MAC addresses » frames not packets… » more efficient… IP packets switch MAC frames
Malvern Innovation Festival: Cyber Security n Annual event… ØThursday focuses on cyber security Øaspects of each LO will be covered n Cyber security academics and practitioners present Ølots of opportunities for final year students Ødress: smart casual Øwhy not brush up your cv?
Encryption ØThree potentially vulnerable places for hackers to capture organisational data: » physically stored e. g. hard disk, CD, USB » system stored e. g. memory of computer, router, or other intermediate device » on the move e. g. through cables or the air ØHackers want information, not data without context! » useless to them if stored & sent in scrambled form…
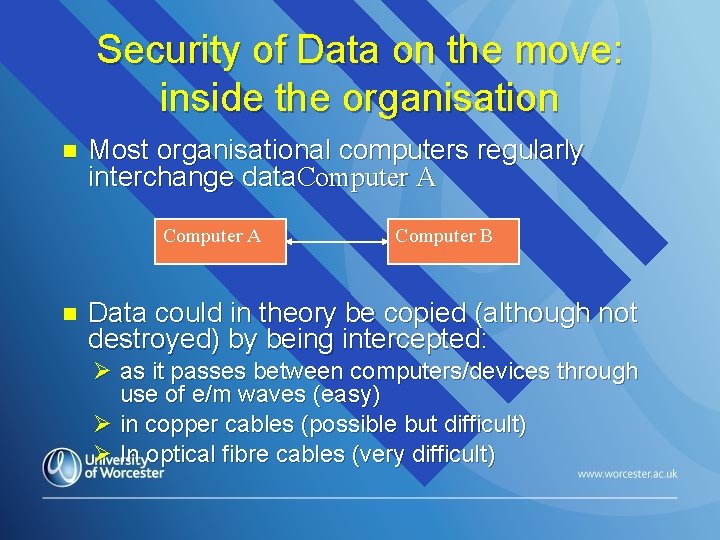
Security of Data on the move: inside the organisation n Most organisational computers regularly interchange data. Computer A n Computer B Data could in theory be copied (although not destroyed) by being intercepted: Ø as it passes between computers/devices through use of e/m waves (easy) Ø in copper cables (possible but difficult) Ø In optical fibre cables (very difficult)
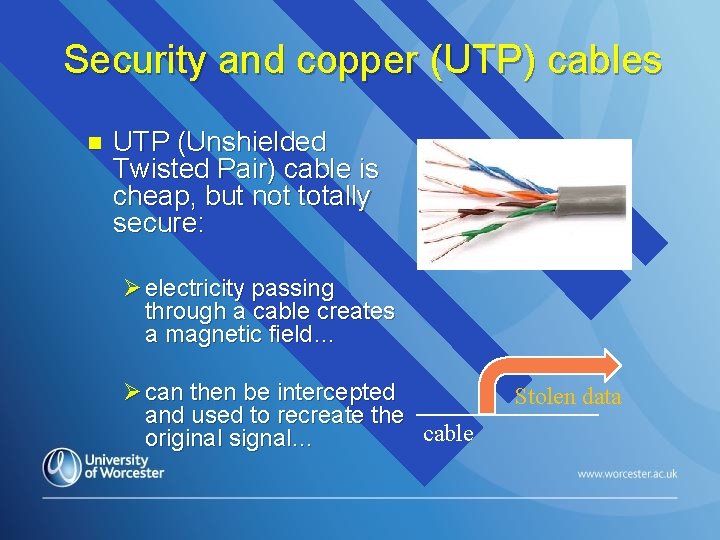
Security and copper (UTP) cables n UTP (Unshielded Twisted Pair) cable is cheap, but not totally secure: Ø electricity passing through a cable creates a magnetic field… Ø can then be intercepted and used to recreate the cable original signal… Stolen data
Security and copper cables: STP n Apart from security concerns, UTP is also vulnerable to stray electro-magnetic waves (e. g. nearby electric motor) n Shielding stops the magnetic field spreading out and stray fields getting in Ø STP (Shielded Twisted Pair) cabling recommended or vulnerable environments Ø but more expensive… ØSECURITY ALWAYS HAS A PRICE!
Security, cost and Fibre Optic Cables n Fibre more secure than even shielded copper Ø digital data transmitted as a high intensity light beam Ø no associated magnetic field; data can’t be “tapped” n Can carry much more data than twisted pair Ø but: » cost… of cables… of installation…
Discussion n Which to choose, UTP, STP, optical fibre? Ø cost v risk balancing act small network e. g. home/microbusiness n medium size network e. g. business 50 employees n large network, with multisite operation n
Using Radio Waves… n Ideal? Øno unsightly cables Ømobile availability Øcheap! n Standard radio waves don’t carry much data (i. e. low bandwidth) Øneed to be high frequency… Øclose to microwave frequency
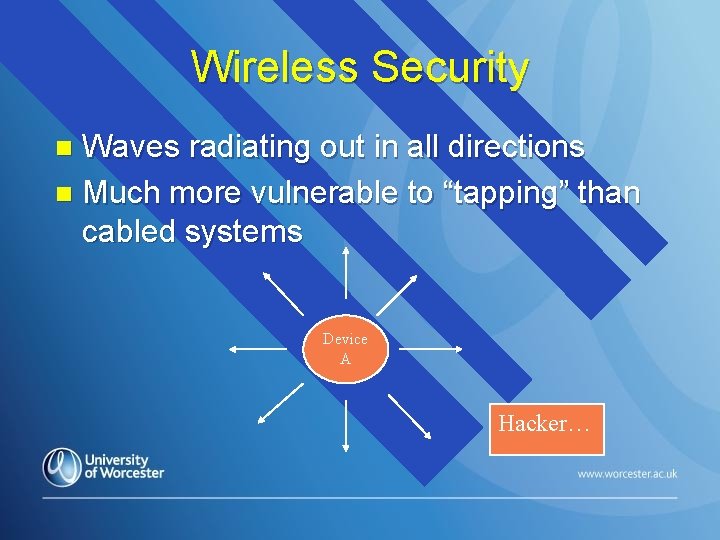
Wireless Security Waves radiating out in all directions n Much more vulnerable to “tapping” than cabled systems n Device A Hacker…
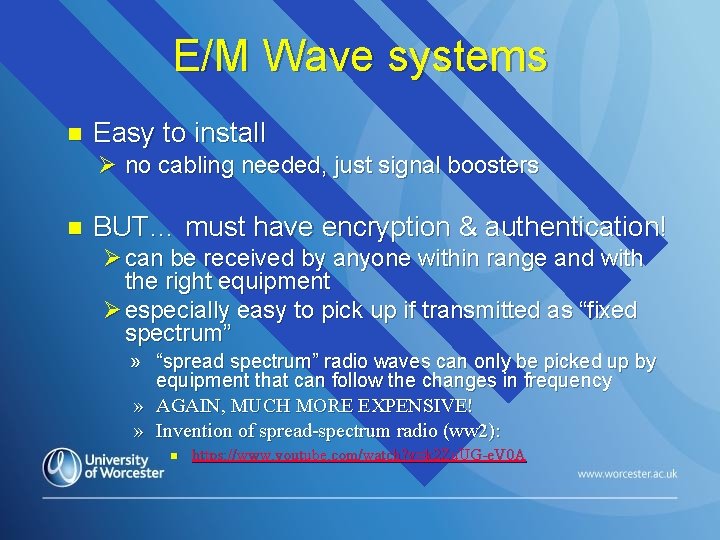
E/M Wave systems n Easy to install Ø no cabling needed, just signal boosters n BUT… must have encryption & authentication! Ø can be received by anyone within range and with the right equipment Ø especially easy to pick up if transmitted as “fixed spectrum” » “spread spectrum” radio waves can only be picked up by equipment that can follow the changes in frequency » AGAIN, MUCH MORE EXPENSIVE! » Invention of spread-spectrum radio (ww 2): n https: //www. youtube. com/watch? v=k 2 Zu. UG-e. V 0 A
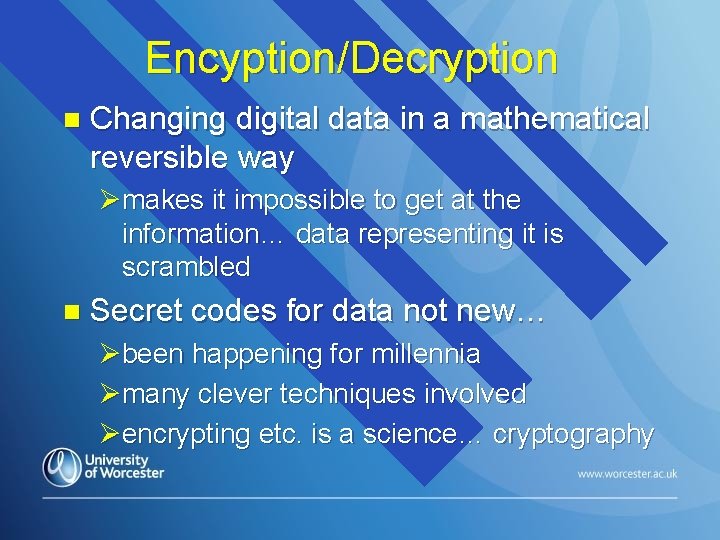
Encyption/Decryption n Changing digital data in a mathematical reversible way Ømakes it impossible to get at the information… data representing it is scrambled n Secret codes for data not new… Øbeen happening for millennia Ømany clever techniques involved Øencrypting etc. is a science… cryptography
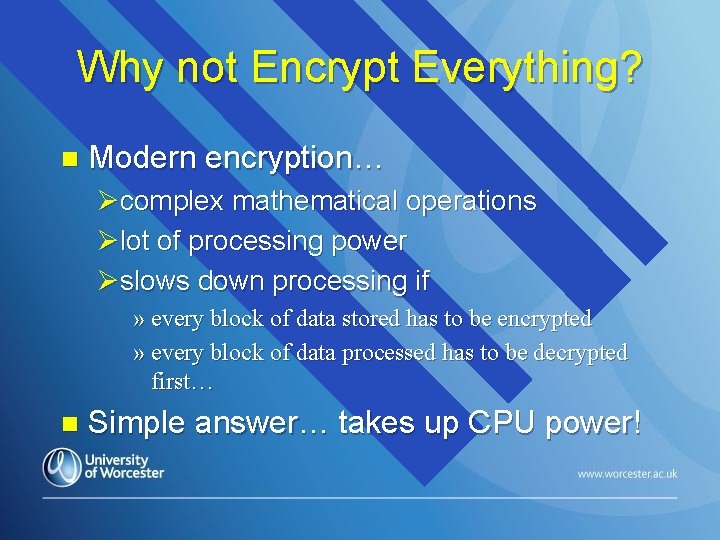
Why not Encrypt Everything? n Modern encryption… Øcomplex mathematical operations Ølot of processing power Øslows down processing if » every block of data stored has to be encrypted » every block of data processed has to be decrypted first… n Simple answer… takes up CPU power!
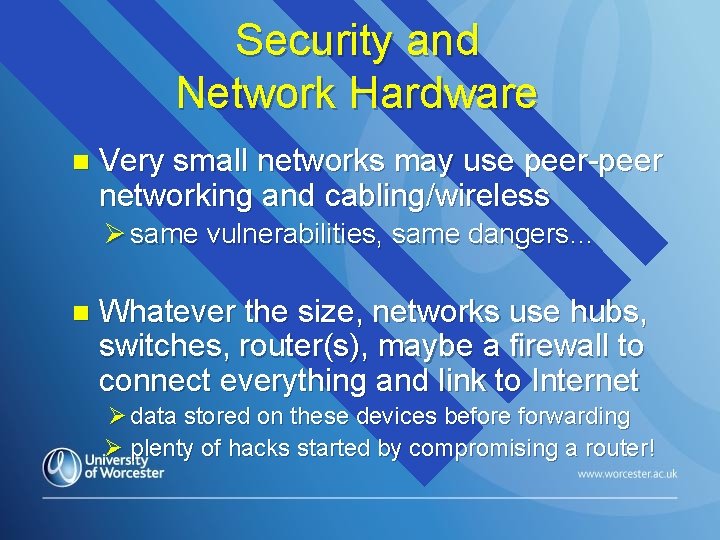
Security and Network Hardware n Very small networks may use peer-peer networking and cabling/wireless Ø same vulnerabilities, same dangers… n Whatever the size, networks use hubs, switches, router(s), maybe a firewall to connect everything and link to Internet Ø data stored on these devices before forwarding Ø plenty of hacks started by compromising a router!
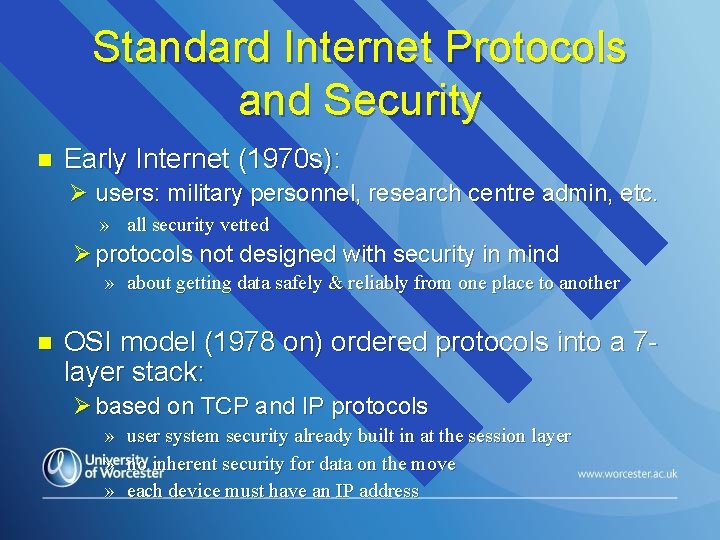
Standard Internet Protocols and Security n Early Internet (1970 s): Ø users: military personnel, research centre admin, etc. » all security vetted Ø protocols not designed with security in mind » about getting data safely & reliably from one place to another n OSI model (1978 on) ordered protocols into a 7 layer stack: Ø based on TCP and IP protocols » user system security already built in at the session layer » no inherent security for data on the move » each device must have an IP address
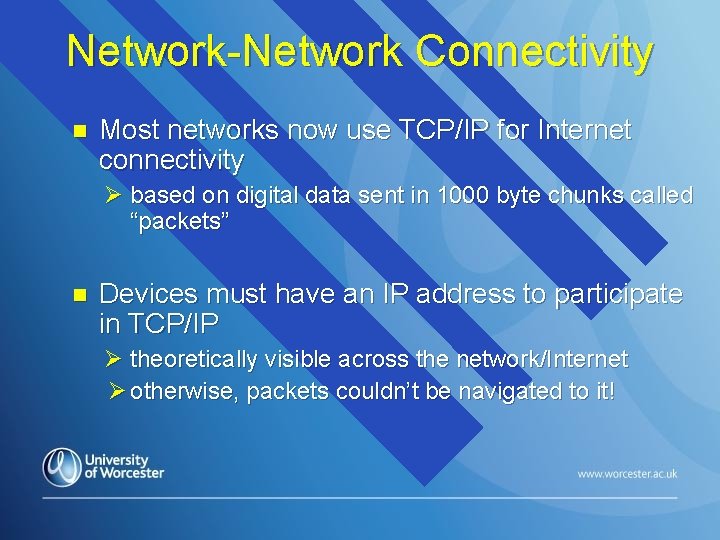
Network-Network Connectivity n Most networks now use TCP/IP for Internet connectivity Ø based on digital data sent in 1000 byte chunks called “packets” n Devices must have an IP address to participate in TCP/IP Ø theoretically visible across the network/Internet Ø otherwise, packets couldn’t be navigated to it!
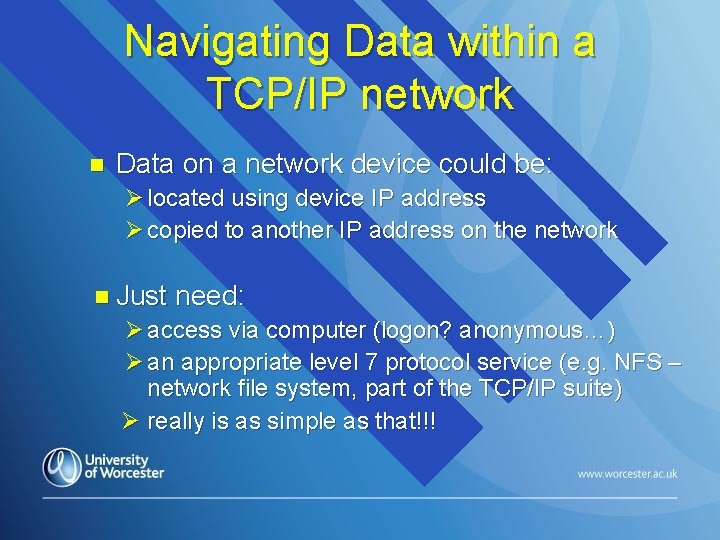
Navigating Data within a TCP/IP network n Data on a network device could be: Ø located using device IP address Ø copied to another IP address on the network n Just need: Ø access via computer (logon? anonymous…) Ø an appropriate level 7 protocol service (e. g. NFS – network file system, part of the TCP/IP suite) Ø really is as simple as that!!!
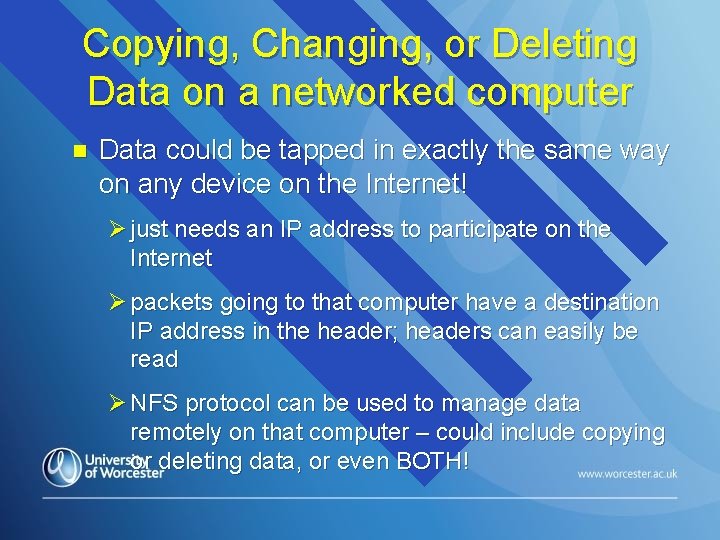
Copying, Changing, or Deleting Data on a networked computer n Data could be tapped in exactly the same way on any device on the Internet! Ø just needs an IP address to participate on the Internet Ø packets going to that computer have a destination IP address in the header; headers can easily be read Ø NFS protocol can be used to manage data remotely on that computer – could include copying or deleting data, or even BOTH!
Connecting Devices & Configuration One of the keys to security… n Routers & Switches often configured via Windows interface n Ø fine for small, simple changes ØMore complex changes need a command line interface (CLI)
The Virtual Private Network n Secure sending of data through the Internet Ø Only use a restricted and very secure set of Internet routers Ø No IP address broadcasting needed… all packets use the same route! Ø IP tunnelling protocol encapsulates data » normal Internet users will therefore not be able to see the sending, receiving, or intermediate IP addresses Ø data sent is encrypted n Potential hackers don’t get a look in!
Simulating a Network CISCO software: Packet Tracer n Drag and drop tool used for planning and implementing networks n Øvery useful also for finding out about network infrastructure and connectivity! Øpractical after the break…
Download a copy of the latest CISCO Packet Tracer for your own use from netacad. com…
- Slides: 49